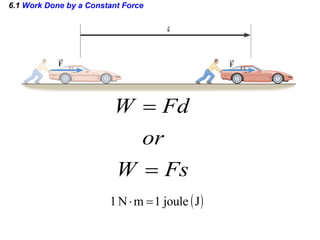
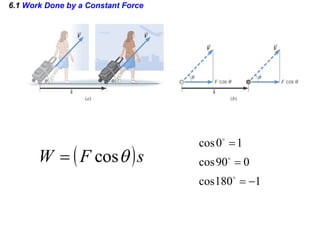
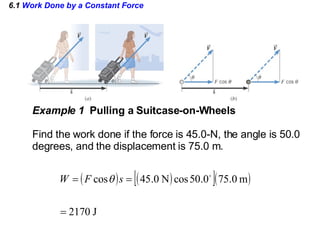
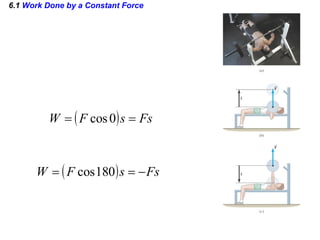
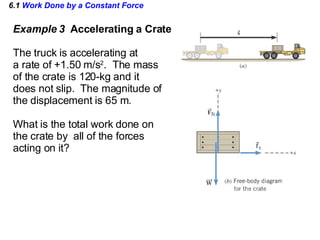
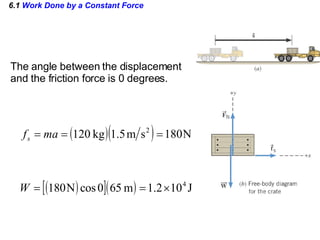
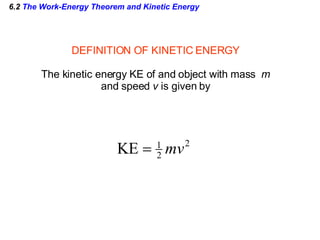
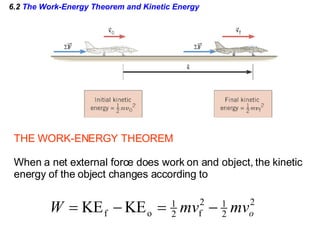
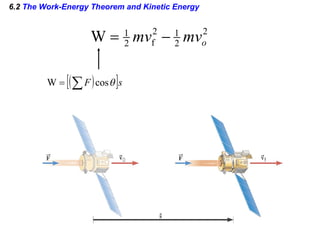
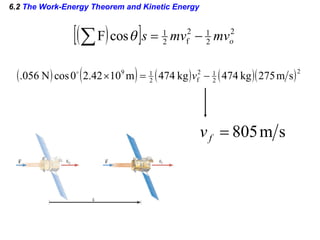
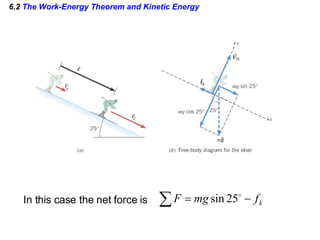
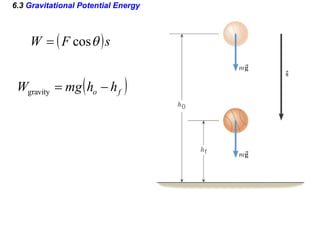
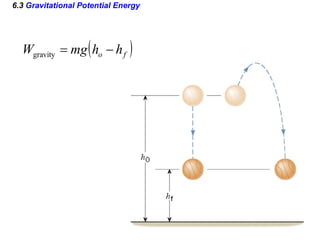
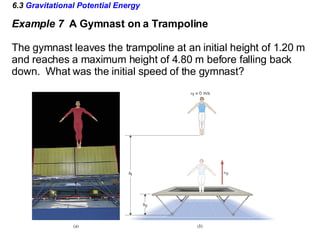
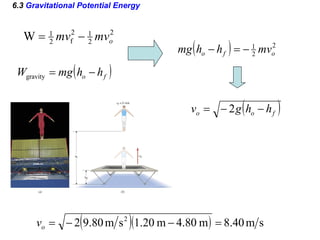
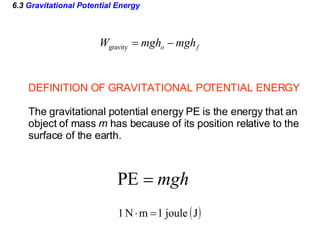
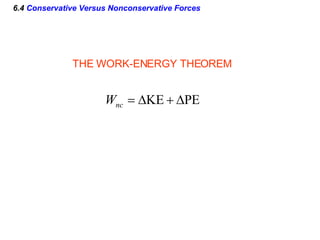
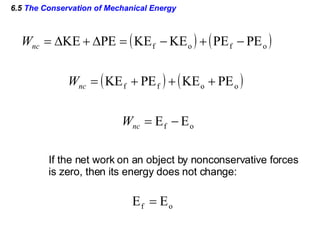
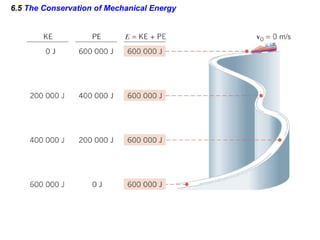
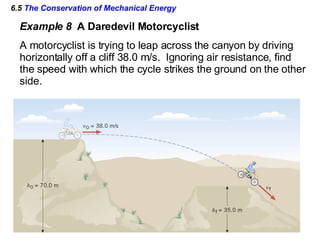
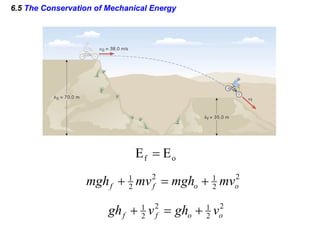
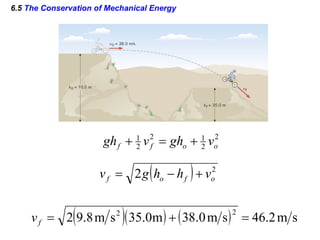
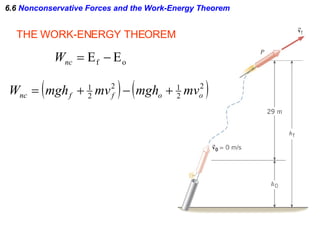
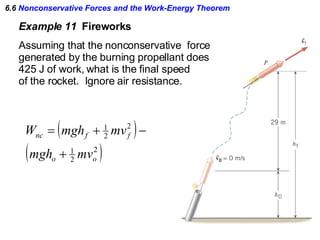
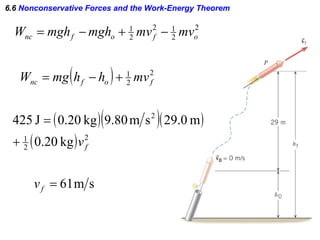
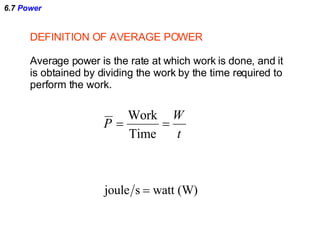
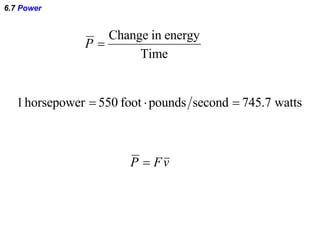
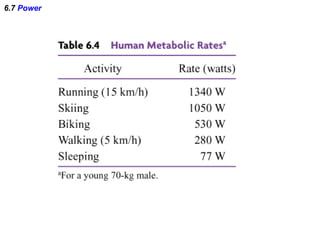
This document discusses work, energy, and power. It defines work, kinetic energy, gravitational potential energy, and average power. It describes the work-energy theorem, the principle of conservation of mechanical energy, and how energy can be transferred between different forms but not created or destroyed based on the principle of conservation of energy. Examples are provided to demonstrate how to calculate work, kinetic energy, gravitational potential energy, and changes in speed and energy based on these principles.