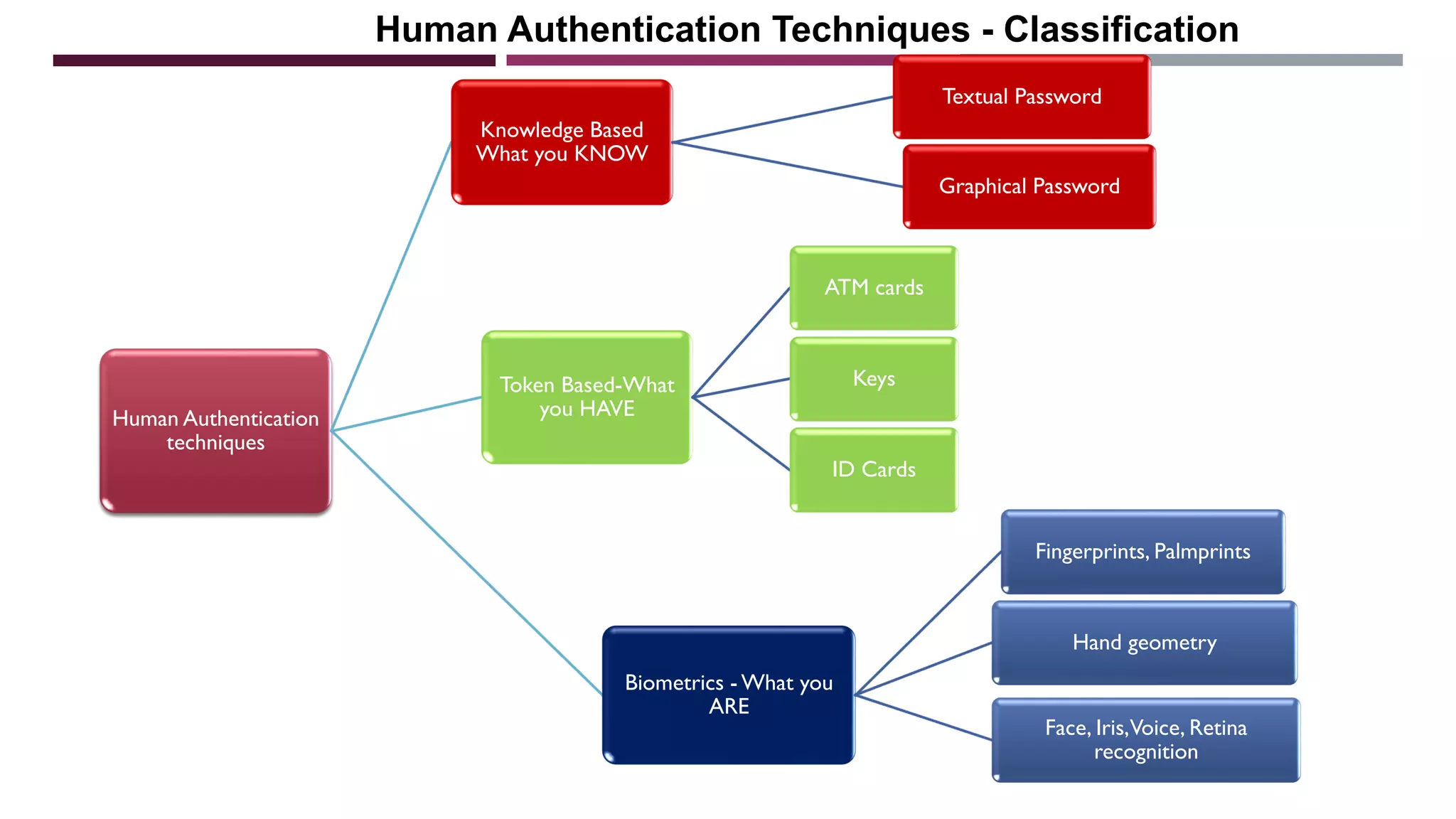
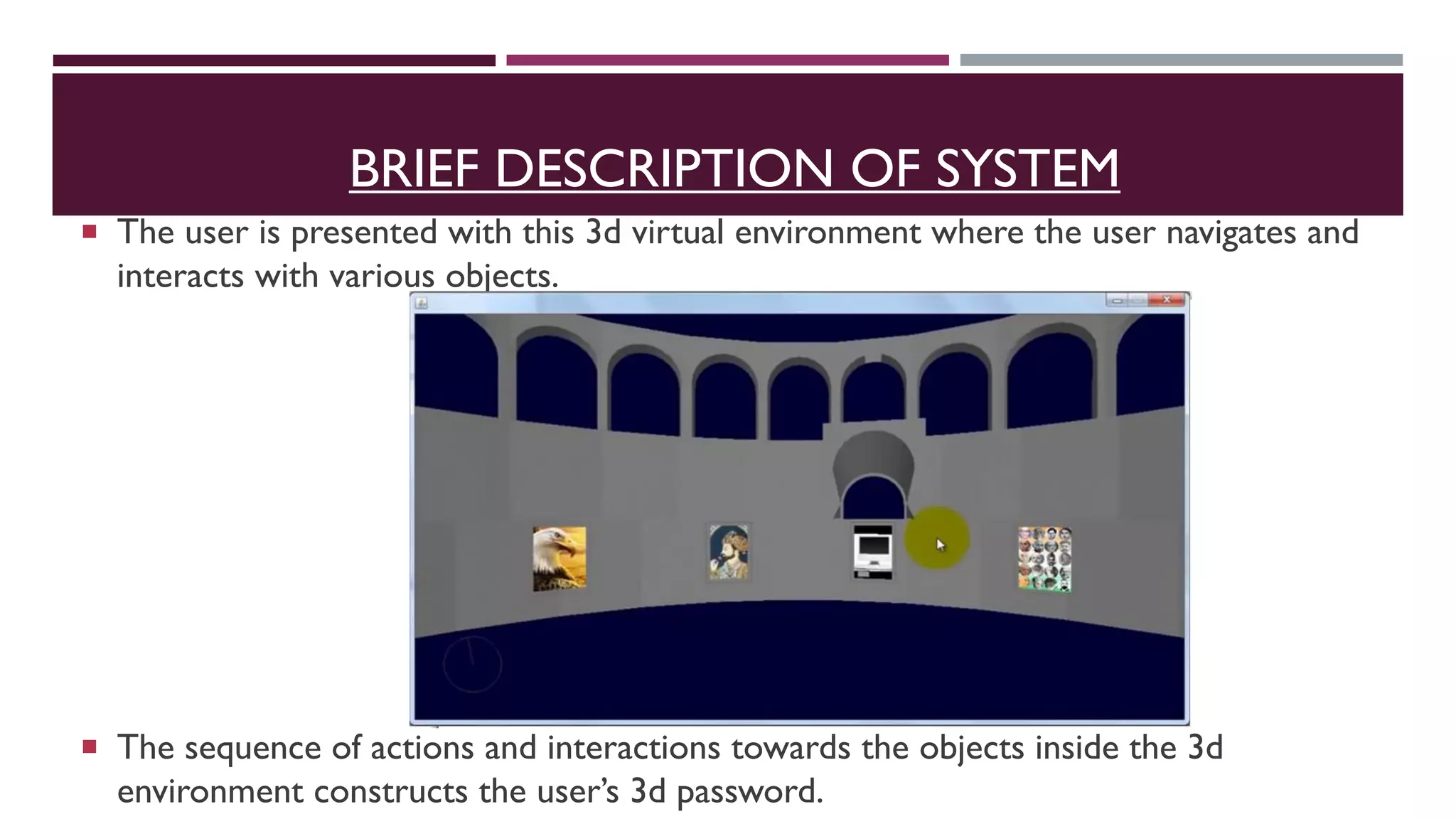
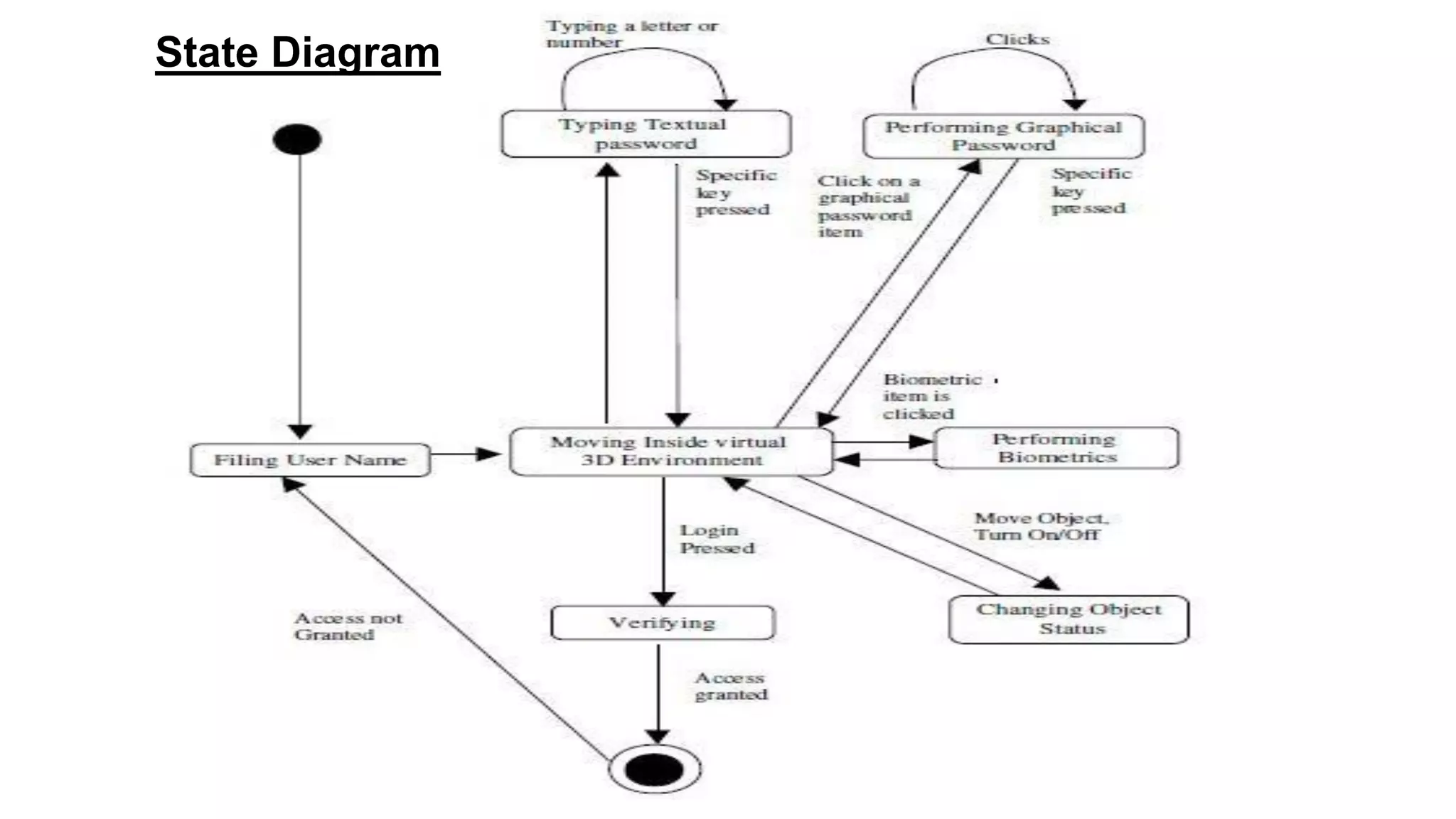
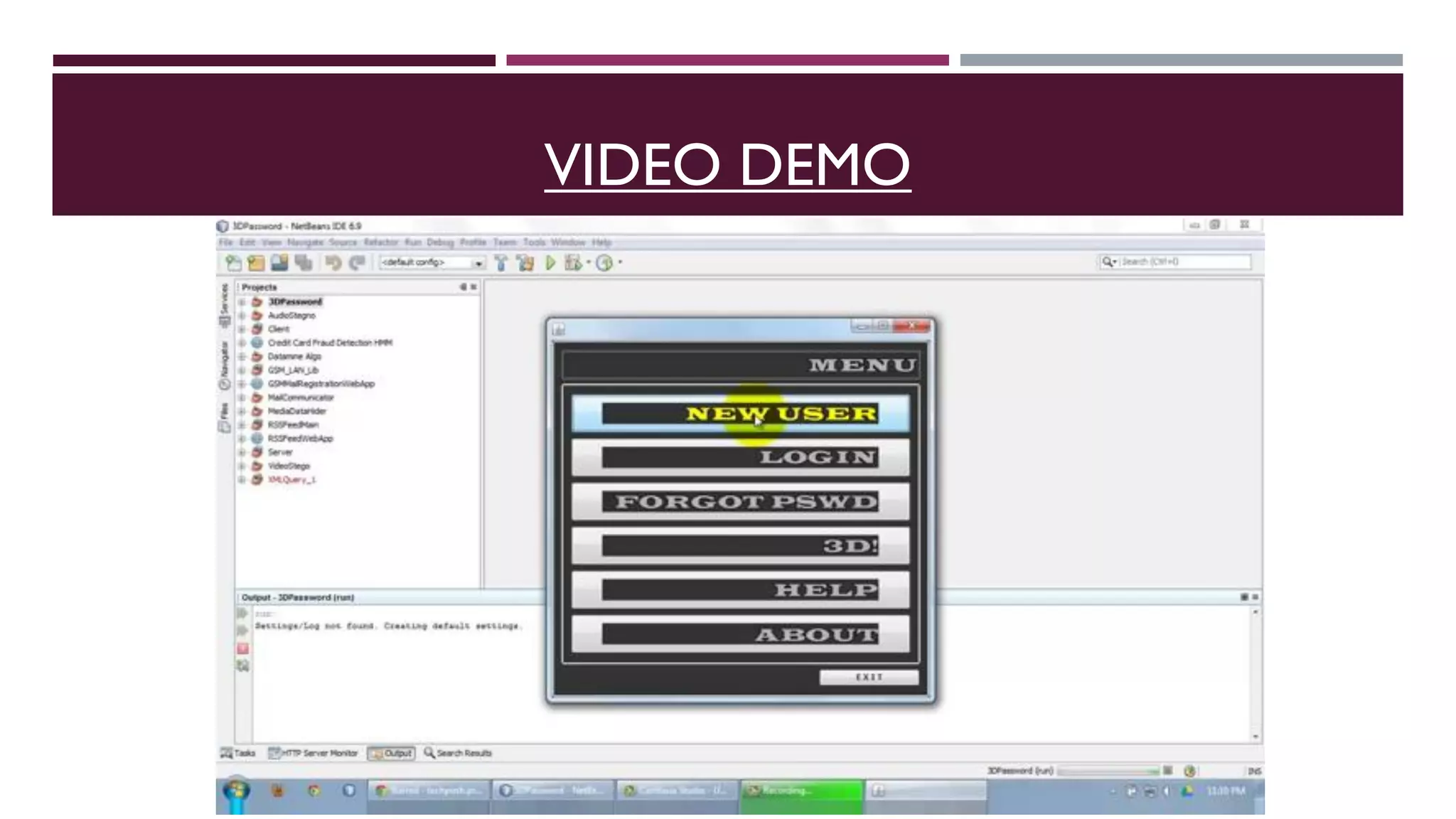
The 3D password is a multifactor authentication scheme that combines various traditional authentication methods within a 3D virtual environment, allowing users to interact with objects to construct their password through specific sequences of actions. This system enhances security by integrating biometric, token, and recall-based validation, making it difficult for unauthorized users to replicate. Applications include critical systems like military facilities and ATM machines, and while it faces potential attacks, its design aims to be robust against common threats.