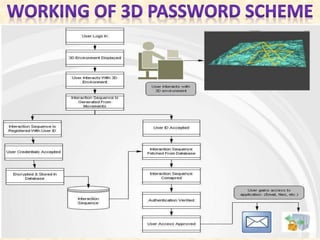
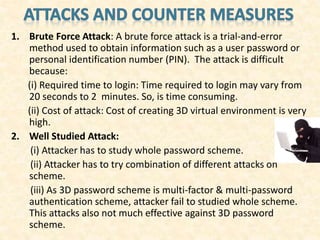
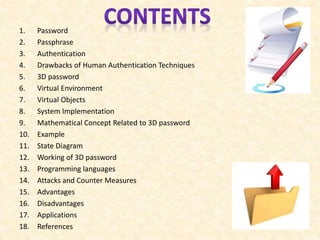
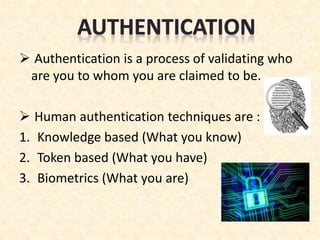
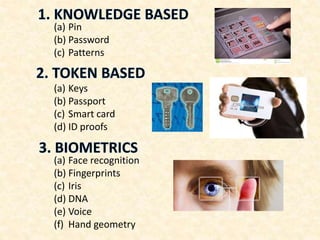
This document describes 3D passwords as a multifactor authentication method that combines knowledge-based, token-based, and biometric authentication in a virtual 3D environment. A 3D password records a user's interactions with virtual objects in the environment, such as opening a door or typing on a computer, creating a unique sequence. Implementation requires programming languages like C++ and OpenGL to create the 3D virtual world. Attacks are difficult due to the complexity of reproducing all factors, but 3D passwords provide very high security and flexibility compared to traditional passwords.


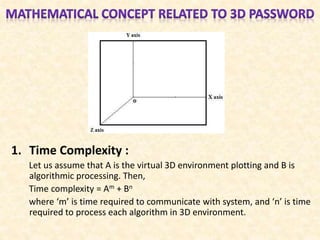
![• Let us consider a 3D virtual environment space
of size G x G x G. The 3D environment space is
represented by the coordinates (x,y,z) ϵ [1,…,G] x
[1,…,G] x [1,…,G].
• The objects are distributed in the 3D virtual
environment with unique (x,y,z) coordinates. We
assume that the user can navigate into the 3D
virtual environment and interact with the
objects using any input device such as a mouse,
keyboard, fingerprint scanner, iris scanner, card
readers, microphones, stylus, etc.](https://image.slidesharecdn.com/3dpasswordppt1-150125050948-conversion-gate01/85/3d-password-ppt-17-320.jpg)