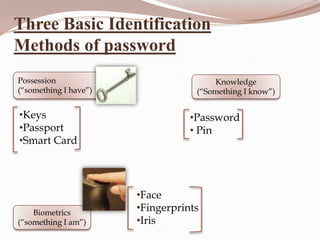
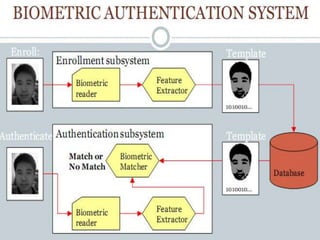
Authentication validates a user's identity by using something they know, have, or are. Common authentication methods include passwords which are something known, tokens like keys which are something had, and biometrics like fingerprints which are something a user is. A 3D password aims to improve authentication security by combining recognition, recall, tokens, and biometrics within a virtual 3D environment that requires users to interact with objects in a specific sequence.