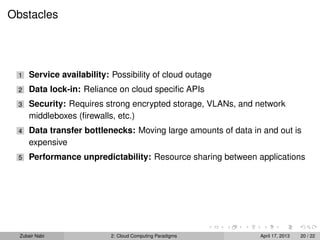
This document discusses cloud computing paradigms. It outlines the history and growth of cloud computing, driven by large internet companies developing scalable infrastructure and data centers. It describes advantages for both service providers and end users, such as simplified installation and maintenance, centralized updates, and on-demand scaling. New applications like mobile and analytics are discussed. Cloud providers operate under a utility computing model of low commitment and pay-as-you-go services.