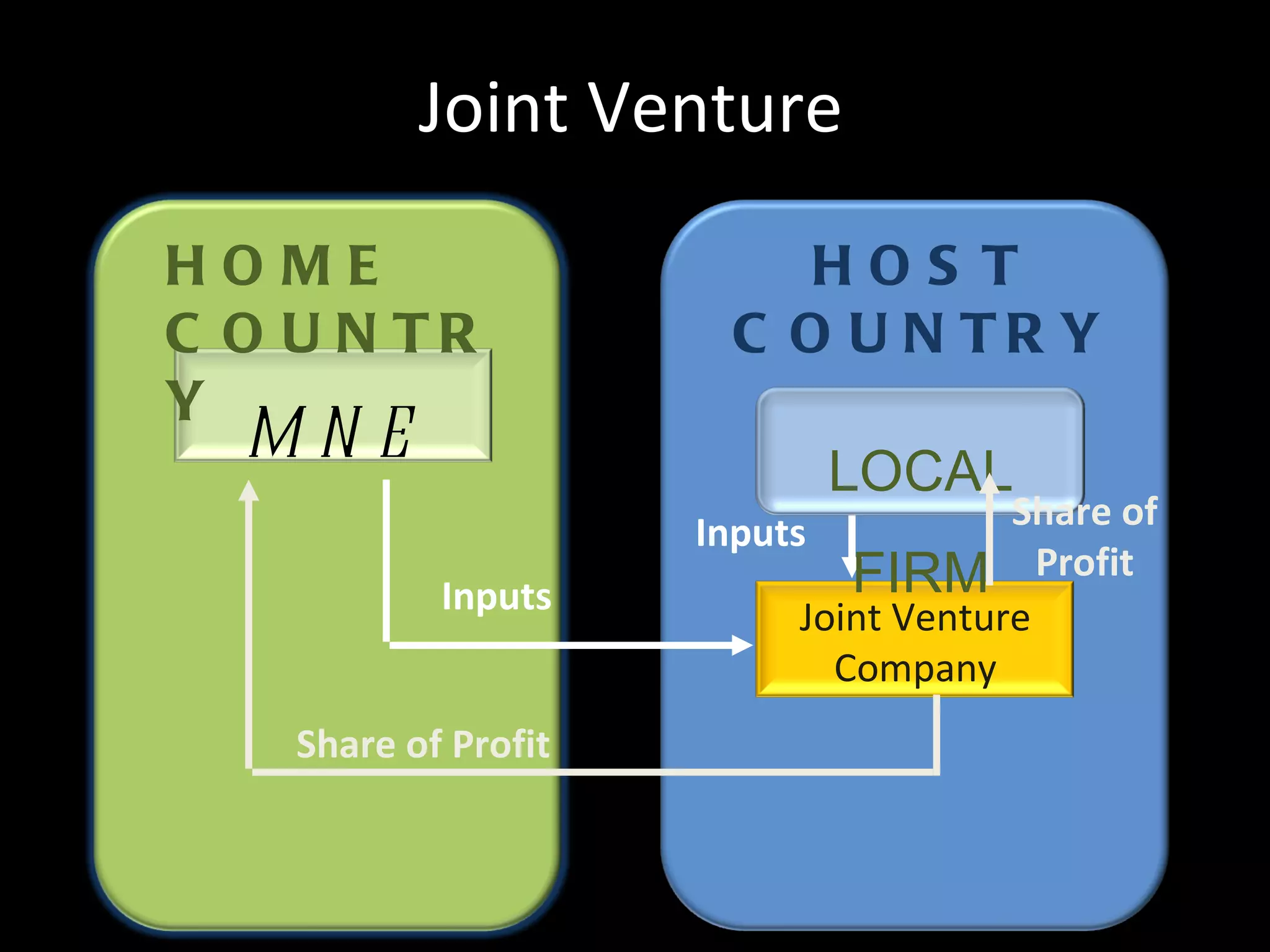
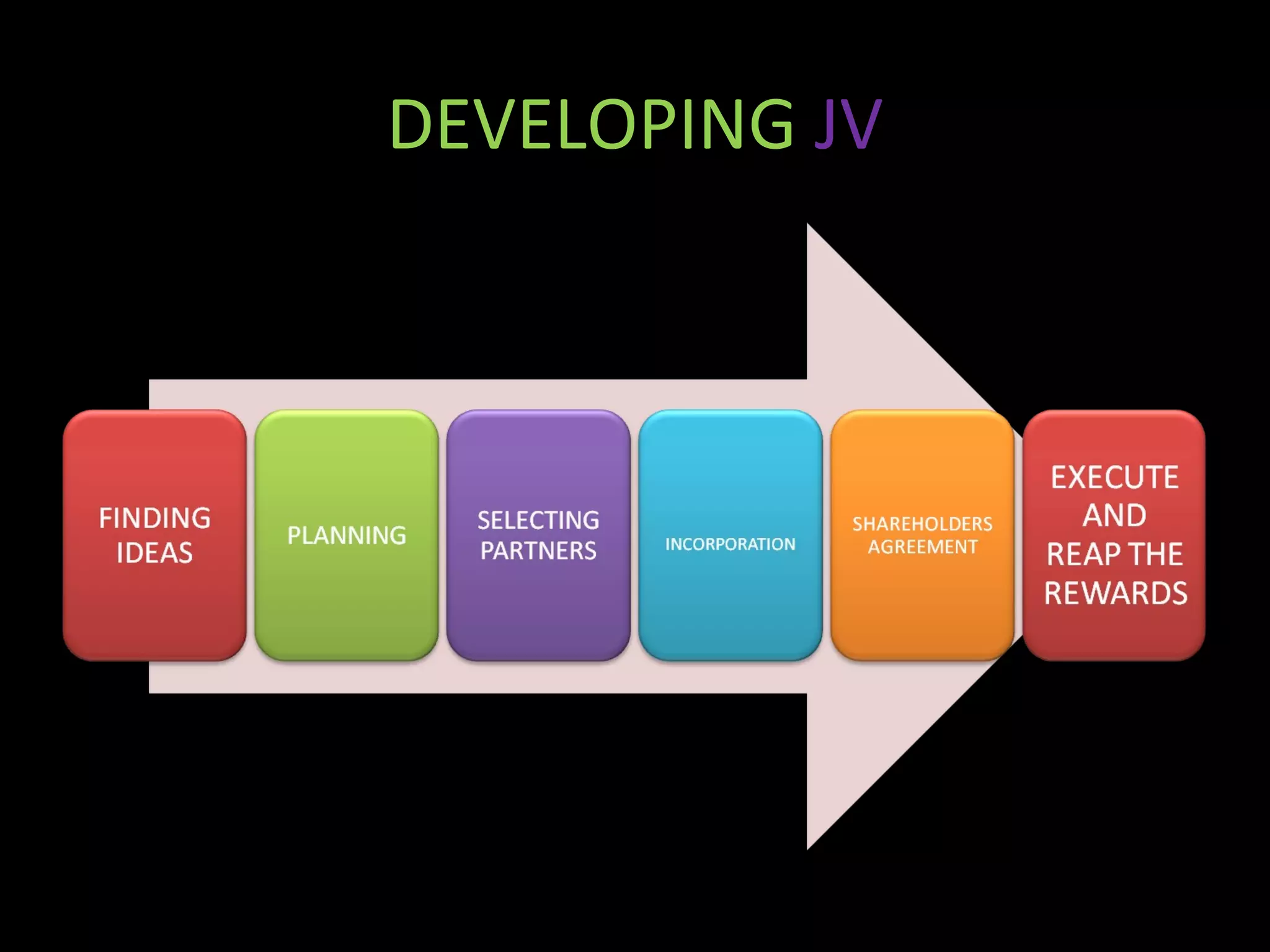
The document discusses technology exports and joint ventures. It provides details on different types of technology exports, including transfers of intellectual property rights and licensing agreements. It also outlines the objectives and needs for technology exports, such as earning royalties and accessing technical knowledge. Joint ventures are described as strategic partnerships between two or more companies, where they share resources to achieve common goals. Successful factors for joint ventures include partner selection, access to financing, adopting modern practices, and technology transfers. Examples provided include the Shanghai BOC industrial gases joint venture and the Sony-Ericsson mobile phone partnership.