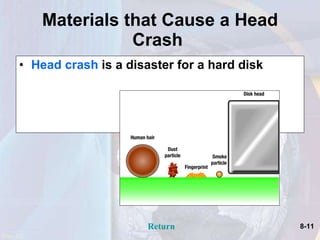
The document discusses various types of secondary storage devices. It describes floppy disks, hard disks, optical disks, solid-state storage, internet drives, magnetic tape, and mass storage devices. It explains the characteristics and capabilities of each type of storage including capacity, access speed, portability and applications used. The document also discusses technologies for improving hard disk performance and emerging technologies that could store an entire life's data on a single disk in the future.