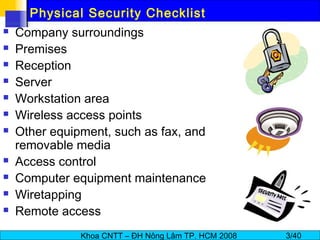
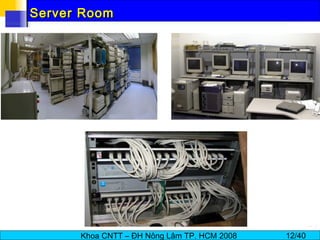
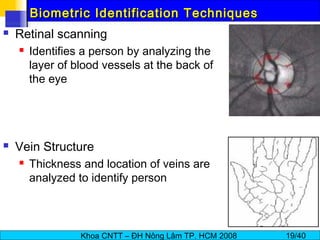
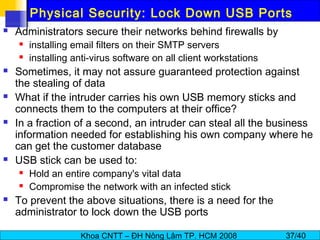
Physical security involves preventing unauthorized access to computer systems and protecting data. It includes securing the company surroundings with fences, gates, and guards. Within premises, CCTV cameras, intruder alarms, and window/door bars provide security. Servers should be locked in enclosed rooms, and workstations in open areas need locks and CCTV monitoring. Access controls like smart cards, biometrics, and entry logs restrict access to sensitive areas. Wireless networks and other equipment also require security measures like encryption and locked storage to protect physical integrity of systems and data.