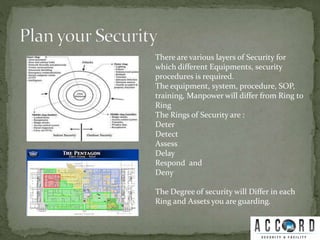
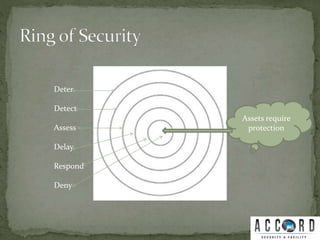
This document discusses implementing security measures in multiple layers or "rings" to protect assets. It recommends conducting a security threat assessment and identifying probable threat elements before implementing security systems. A local security expert can then guide setting up deterrents like barriers and lighting to prevent threats. Detection systems like CCTVs and intrusion detection help identify threats attempting to enter. Assessment, delay, response, and denial systems activate as threats progress further to ultimately protect the core assets. The document stresses centering all security efforts and systems around saving protected assets.

![Before Putting Your Security in place, Have Proper
Security threat Assessment.
Study and Finalize your Probable Threat
Elements[PTE].
Look for a local Security Professional / Expert to
Guide you to implement the Security Set up.](https://image.slidesharecdn.com/planyoursecurity-160206113929/85/Plan-your-security-2-320.jpg)

![Put the system like CCTV ,Proximity
system to detect the PTE determined to
enter your facility.
Use Intrusion Detection System [ IDS ]
for Detection.
Have proper system with visibility to
discourage the PTE.
Use CCTV system with Motion
Detection and tracking.](https://image.slidesharecdn.com/planyoursecurity-160206113929/85/Plan-your-security-6-320.jpg)