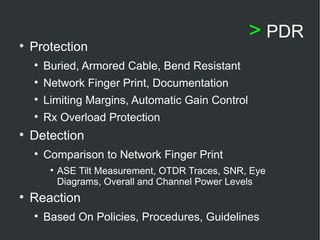
The presentation discusses Physical Layer Optical Network Security (PLONS), highlighting the need for addressing vulnerabilities in fiber networks where most traffic travels, particularly in light of recent attacks. It emphasizes the importance of awareness, research into security measures, and challenges misconceptions about network quality of service being equivalent to security. Additionally, it proposes a taxonomy for PLONS and outlines necessary protective measures against specific attacks.







![> Citations [1] Harry Dutton, Understanding Optical Communications, IBM RedBooks, SGA24-5230-00, Sep. 1998 [2] Luca Faustini and Giuseppe Martini. Bend loss in single-mode fibers. IEEE - Journal of Lightwave Technology , 15(4): 671–679, April 1997. [3] Alun J. Harris and Peter F. Castle. Bend loss measurements on high numerical aperture single-mode fibers as a function of wavelength and bend radius. IEEE - Journal of Lightwave Technology , 4(1):34–40, January 1986. [4] Muriel Medard, Douglas Marquis, Richard A. Barry, and Steven G. Finn: Security Issues in All-Optical Networks, IEEE Network Magazine 11(3), 42–8, May/June 1997. [5] Alun J. Harris, Peter F. Castle, and Paul A. Shrubshall: Wavelength Demultiplexing Using Bends in a Single- Mode Optical Fiber, IEEE - Journal of Lightwave Technology 6(1):80-86, January 1988. [6] T. H. Shake, B. Hazzard, and D. Marquis: Assessing Network Infrastucture Vulnerabilities to Physical Layer Attacks Distributed Systems Group, Advanced Networks Group, Lincoln Laboratory MIT, Sponsored By the DARPA under contract F19628-95-C-002 [7] Muriel Medard, Douglas Marquis, and Stephen R. Chinn: Attack Detection Methods for All-Optical Networks, Network and Distributed System Security Symposium , sponsored by the Internet Society Session 3(Paper 1), 1–15, 1998 [8] M.Y. Loke, and James N. McMullin: Simulation and Measurement of Radiation Loss at Multimode Fiber Macrobends, IEEE - Journal of Lightwave Technology 8(8), 1250–56, August 1990 [9] R. Morgan, J.D.C. Jones, P.G. Harper, and J.S. Barton: Observation of secondary bend loss oscillations arising from propagation of cladding modes in buffered monomode optical fibres , Optics Communications 85(1),17–20, August 1991 [10] Technical Staff of CSELT: Fiber Optic Communications Handbook , TAB Profession and Reference Books, 1990 [11] Robert S. Elliott, “Electromagnetics – History, Theory, and Applications”, IEEE Press Series on Electromagnetic Waves, IEEE Press, 1993 [12] Muriel Medard, Douglas Marquis, and Stephen R. Chinn: Attack Detection Methods for All-Optical Networks, Network and Distributed System Security Symposium, sponsored by the Internet Society Session 3(Paper 1), 1–15, 1998 [13] Cancellieri, G. single-Mode Optical Fibers, Pergamon Press, Toronto, 1991 [14] Keiser, G., Optical Fiber Communications 2 nd Edition, McGraw Hill, Inc., Toronto, 1991 [15] Walter, H., Method and Device For Extracting Signals Out of a Glass Fiber, US Patent No.: 6,265,710 B1, July 2001](https://image.slidesharecdn.com/joshuawhiteplonsissapresentation-124534258159-phpapp02/85/Physical-Layer-Optical-Network-Security-Thesis-Presentation-To-The-CNY-ISSA-Chapter-11-320.jpg)
![[16] Stoneburner, G., Goguen, A., Feringa, A., Risk Management Guide for Information Technology Systems, Special Publication 800-30 [17] Bruce Potter, Trends in wireless security – the big picture, Network Security Volume 2003, Issue 12, December 2003, Pages 4-5. [18] Opterna, State of Optical Network Security, Black Hat Federal Briefing Presentation, October 2003 [19] ISO/IEC 15408:1999(E): Information Technology – Security Techniques – Evaluation Criteria for IT Security, International Organization for Standardization, Geneva, Switzerland. [20] Schneier, Bruce. “Attack Trees.” 21-29. Dr. Dobb’s Journal of software Tools 24, 12 (December 1999): 21-29 [21] Schneier, Bruce. Secrets and Lies: Digital Security in a Networked World. New York, NY: John Wiley & Sons, 2000. > Citations](https://image.slidesharecdn.com/joshuawhiteplonsissapresentation-124534258159-phpapp02/85/Physical-Layer-Optical-Network-Security-Thesis-Presentation-To-The-CNY-ISSA-Chapter-12-320.jpg)