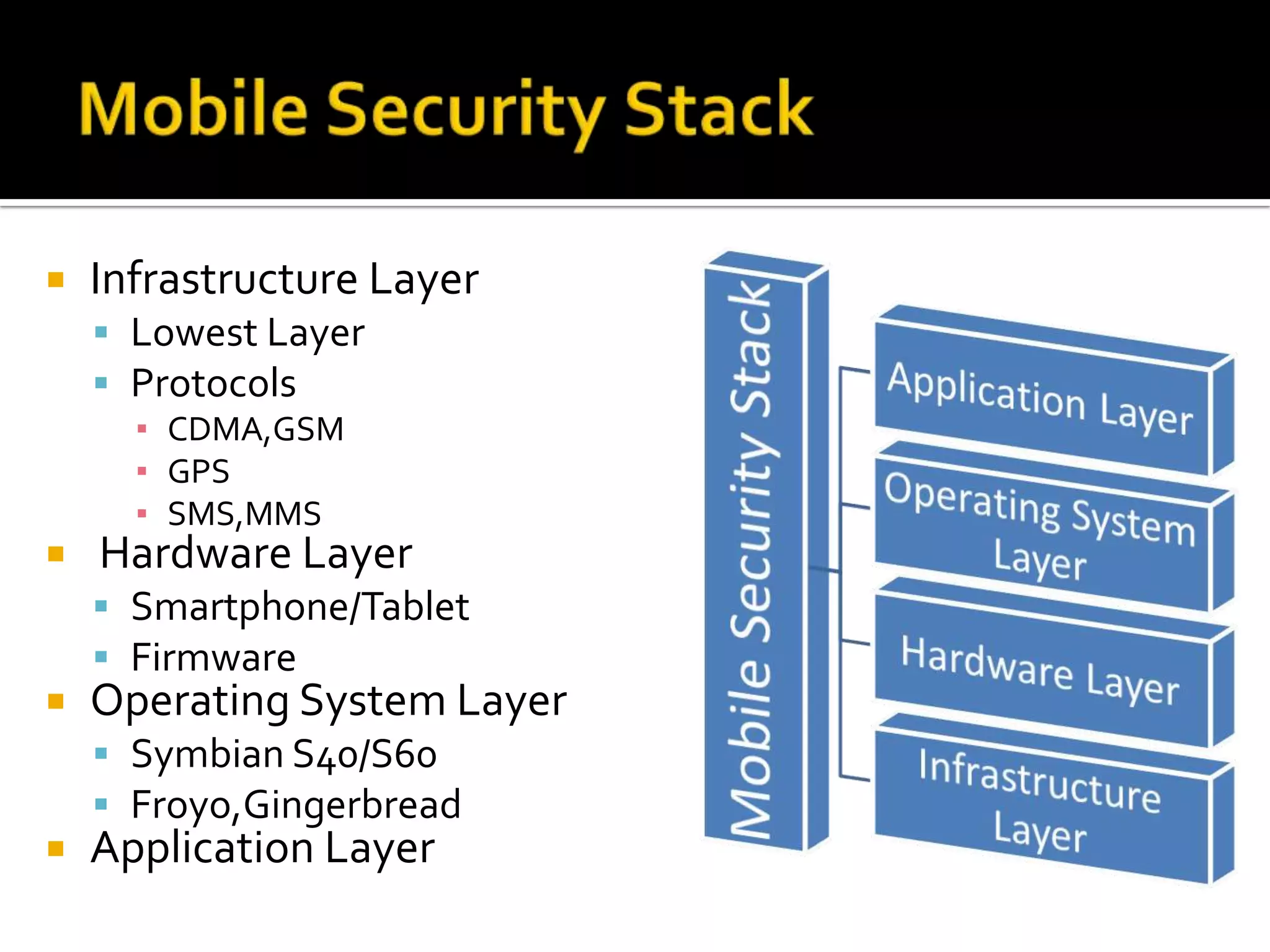
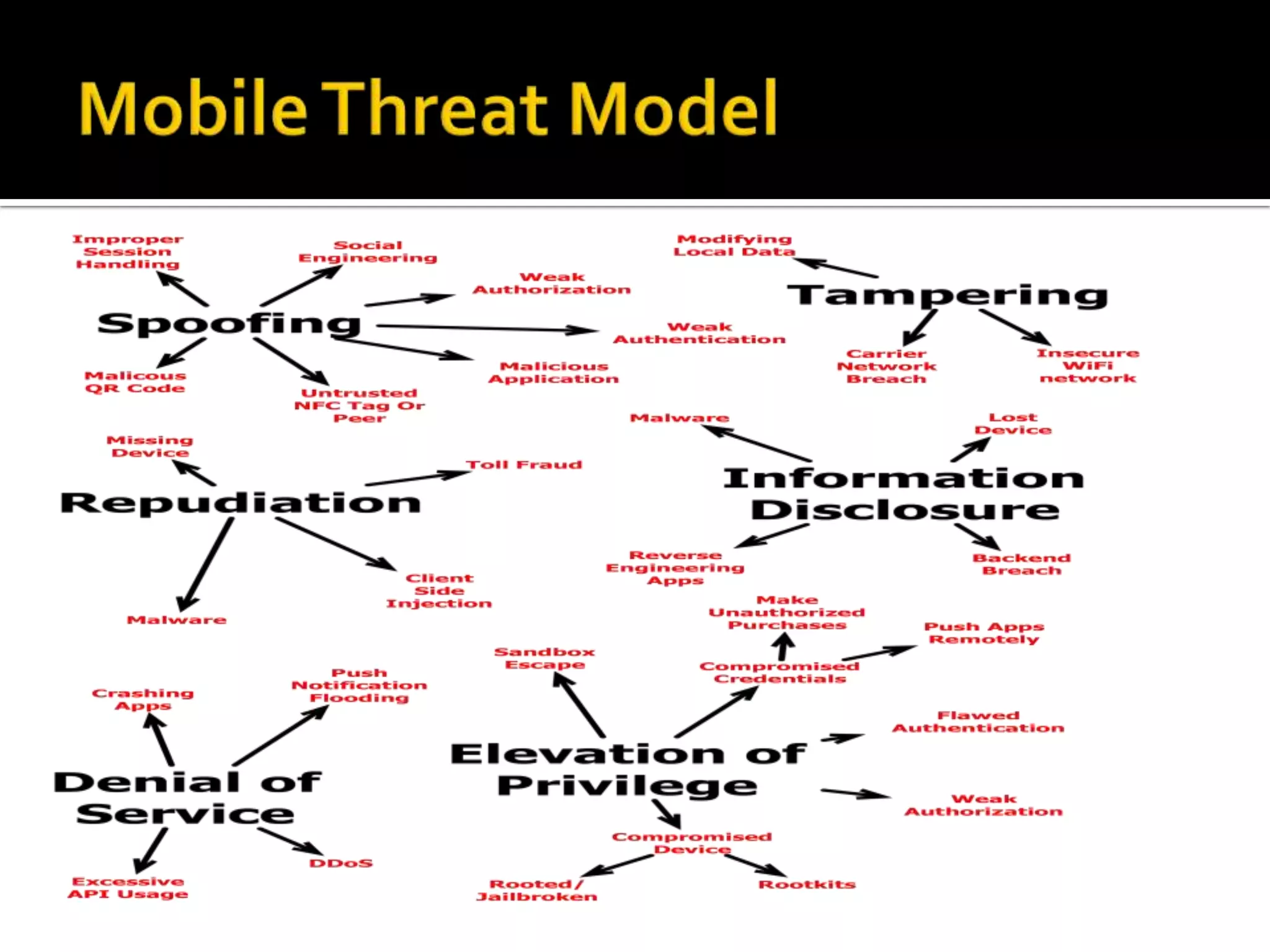
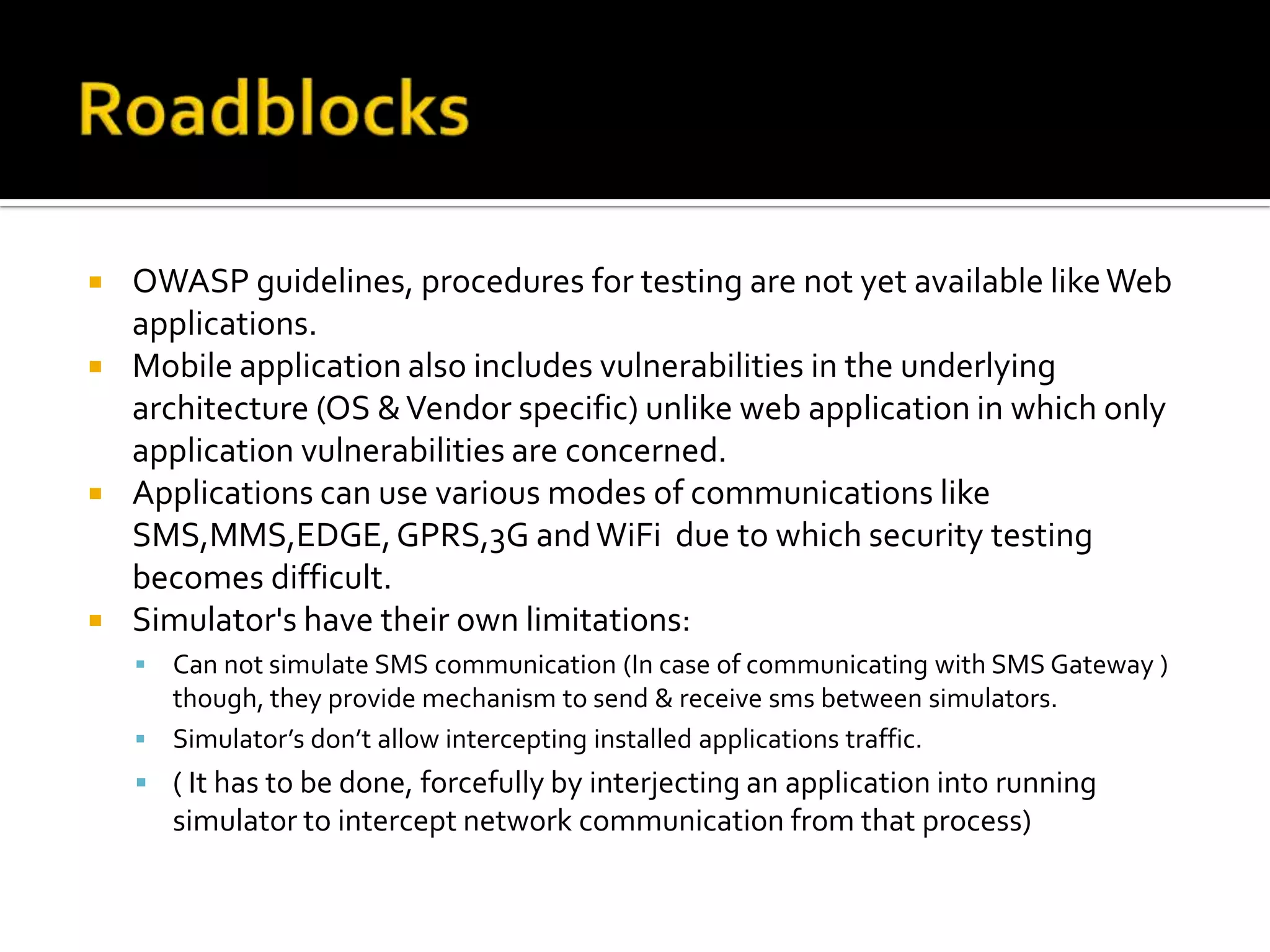
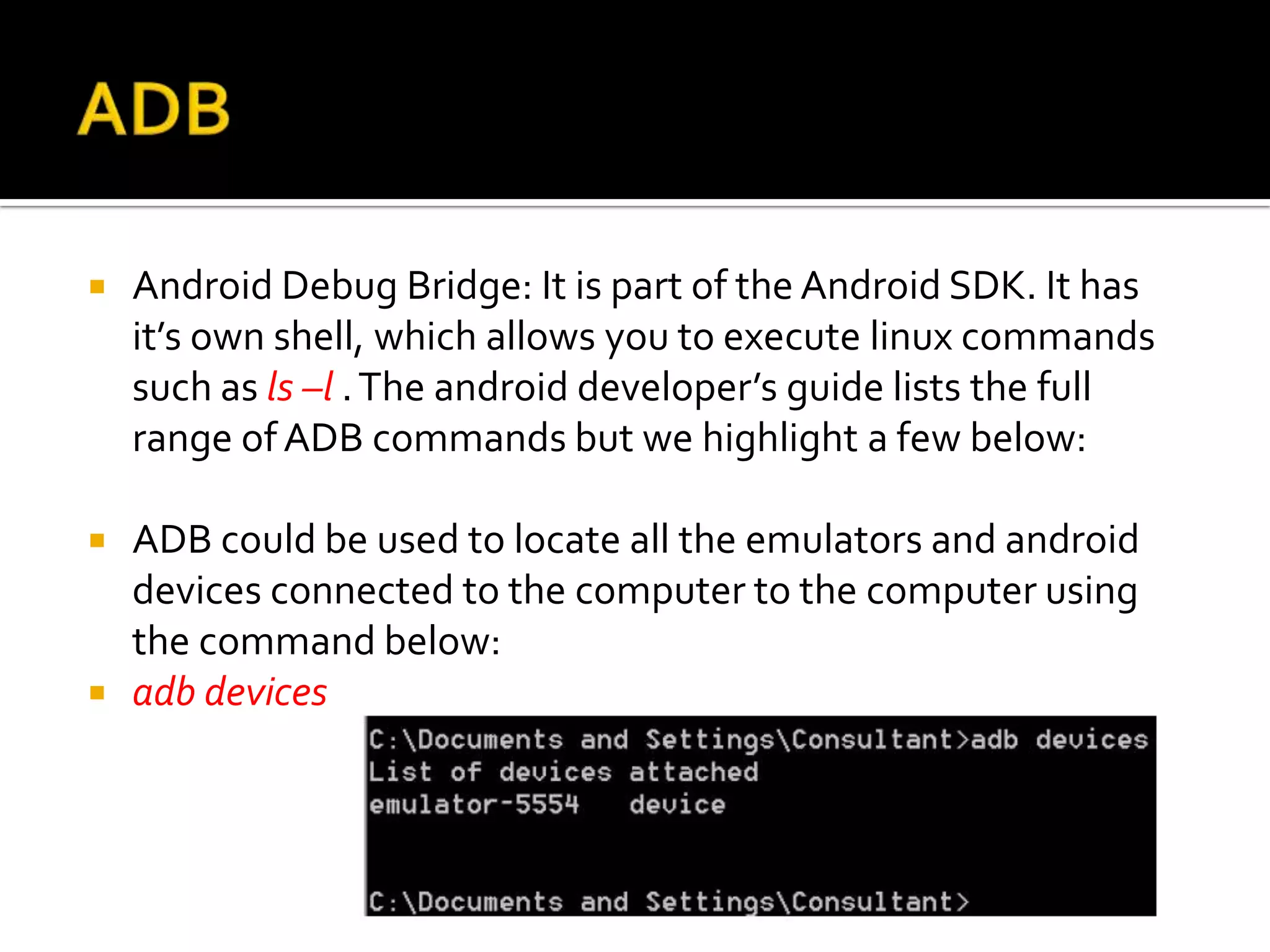
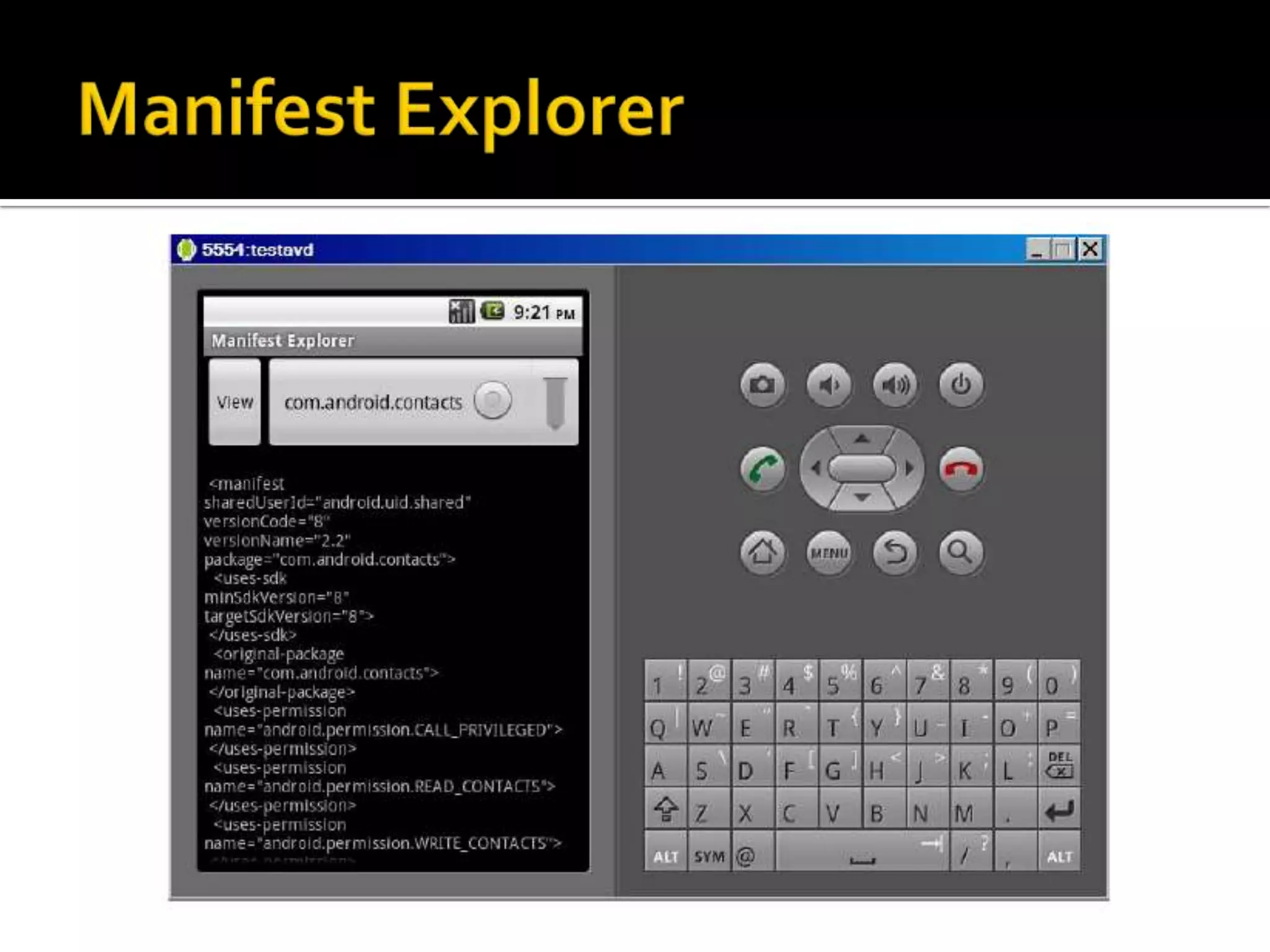
This document provides an overview of mobile application security testing. It discusses the mobile security stack including the infrastructure, hardware, operating system and application layers. It then covers topics like mobile threat modeling, mobile application auditing techniques including dynamic and static analysis. The document also discusses the OWASP top 10 mobile risks and provides case studies and demonstrations on pentesting real mobile applications and reverse engineering Android malware.