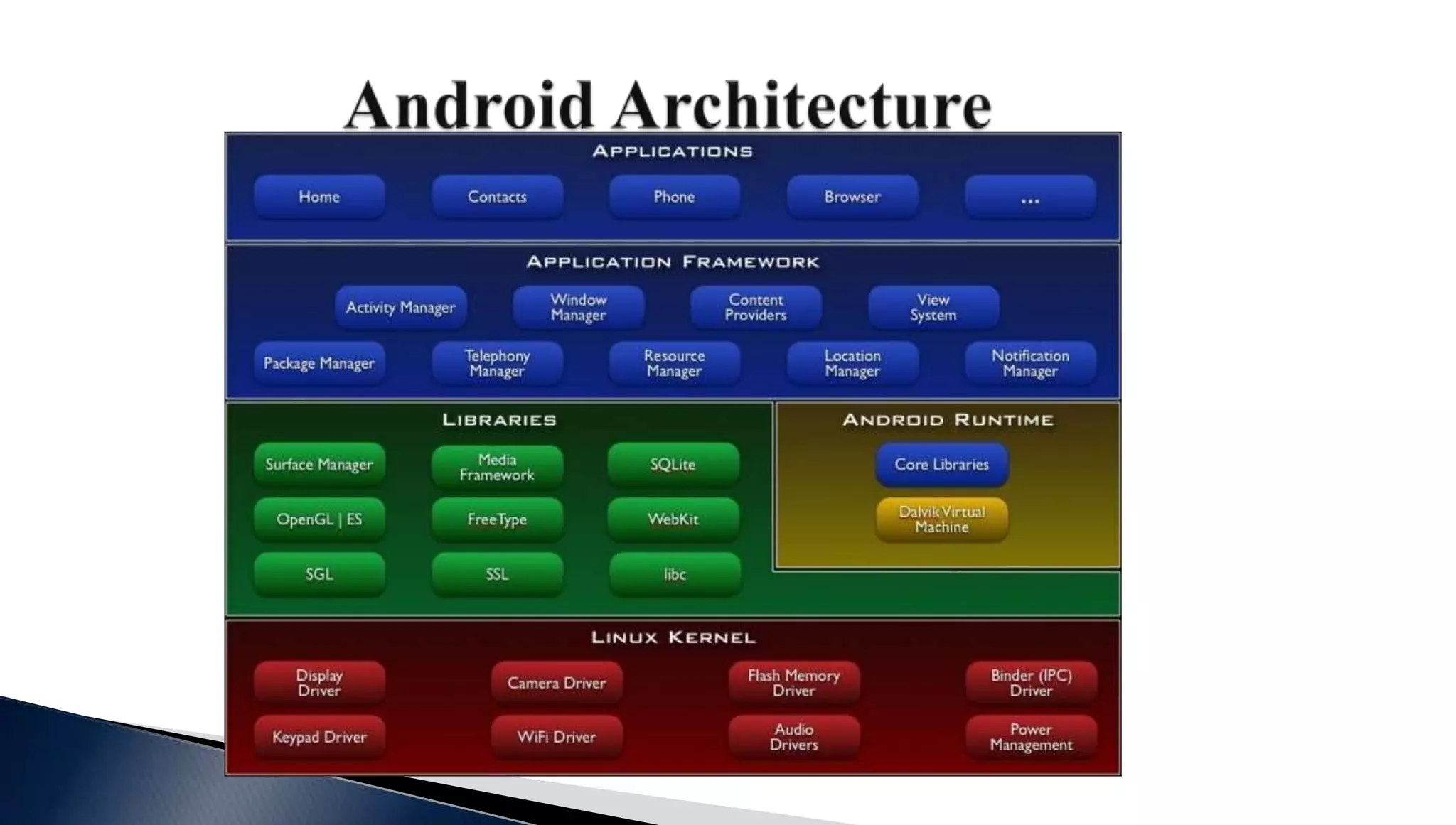
This document provides an overview of Android malware analysis training. It begins with a disclaimer and acknowledgements. It then introduces the speaker and provides a basic overview of Android architecture, security features, application format, and permissions. It discusses Dalvik bytecode and sets up an analysis lab with tools like emulators, decompilers, and reverse engineering VMs. Finally it ends with references to malware analysis projects and a tutorial on the Dalvik bytecode.
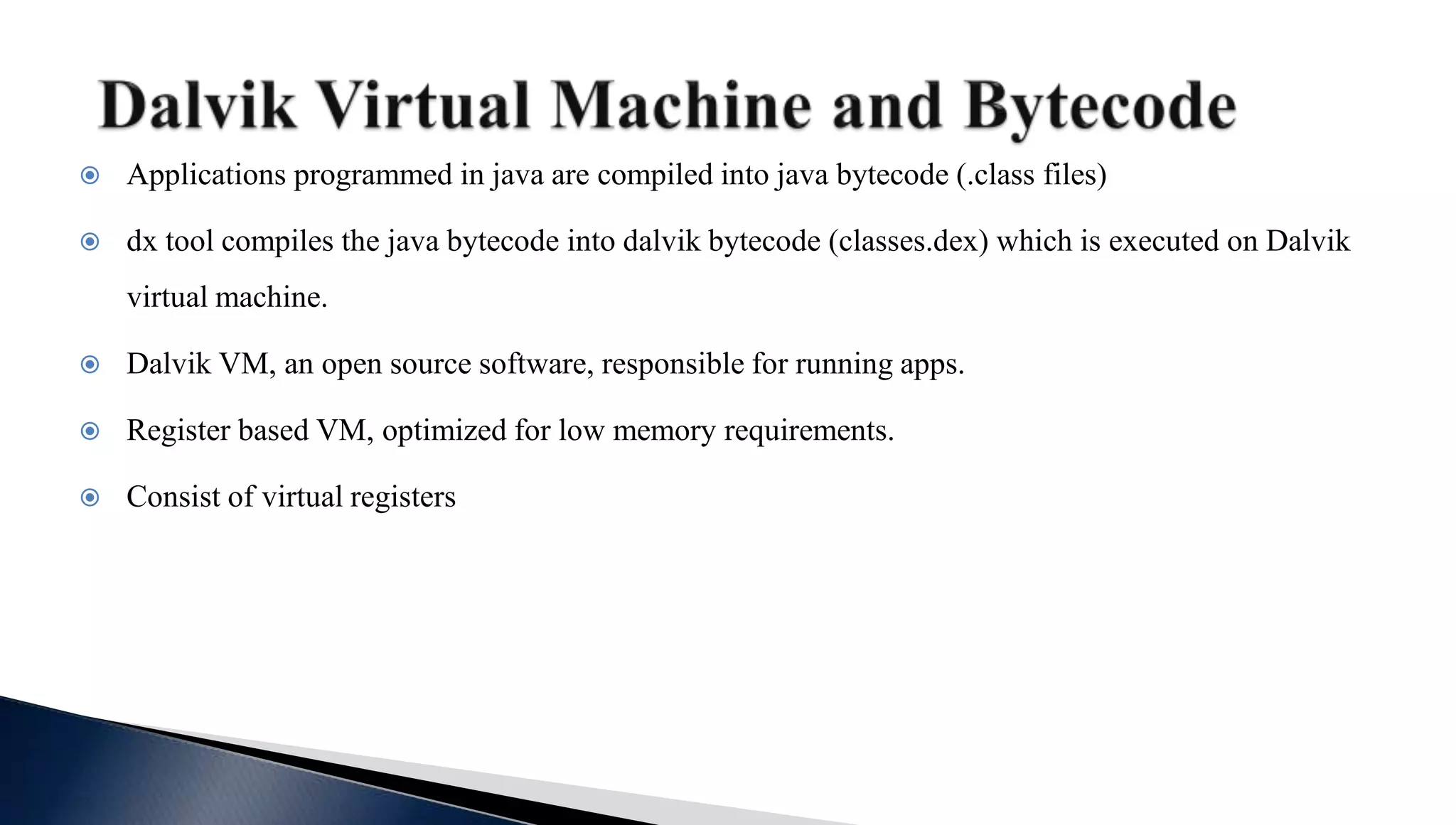
![.method public add(II)I
.limit registers 4
; this: v1 (Ltest2;)
; parameter[0] : v2 (I)
; parameter[1] : v3 (I)
add-int v0,v2,v3 ; v0=v2+v3
return v0
.end method](https://image.slidesharecdn.com/azk3camfqaoa4fkvl1el-signature-fa17ef08645a3cce9ed98bc960f7e89b419197b8ab9318d2a54057ce7f634710-poli-160709185311/75/Advanced-malware-analysis-training-session8-introduction-to-android-15-2048.jpg)