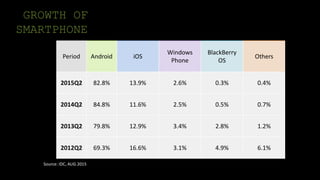
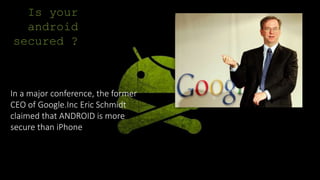
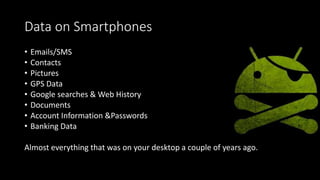
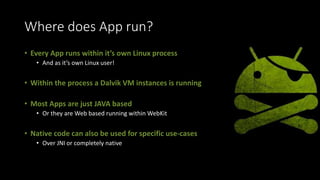
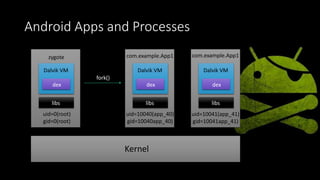
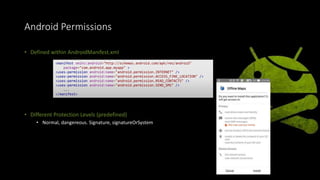
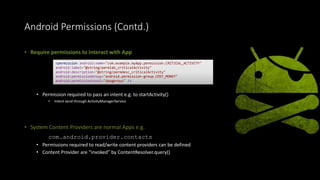
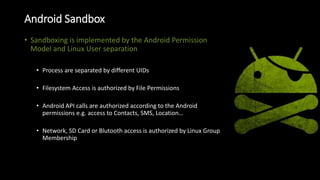
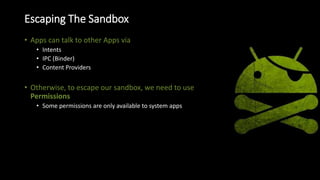
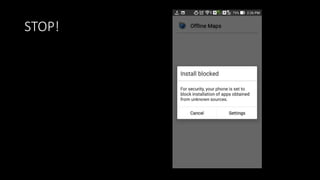
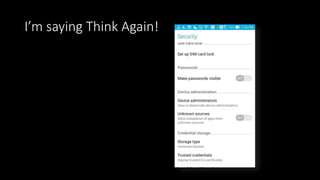
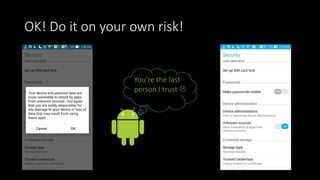
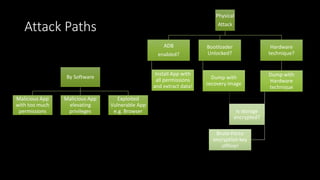
The document discusses the security vulnerabilities of the Android platform compared to other smartphone operating systems, emphasizing a growing threat from malware. It highlights the risks associated with app permissions and the importance of safeguarding personal data on mobile devices. The conclusion suggests using complex passcodes for protection, but acknowledges that physical threats and a lack of hardware support for encryption remain critical concerns.