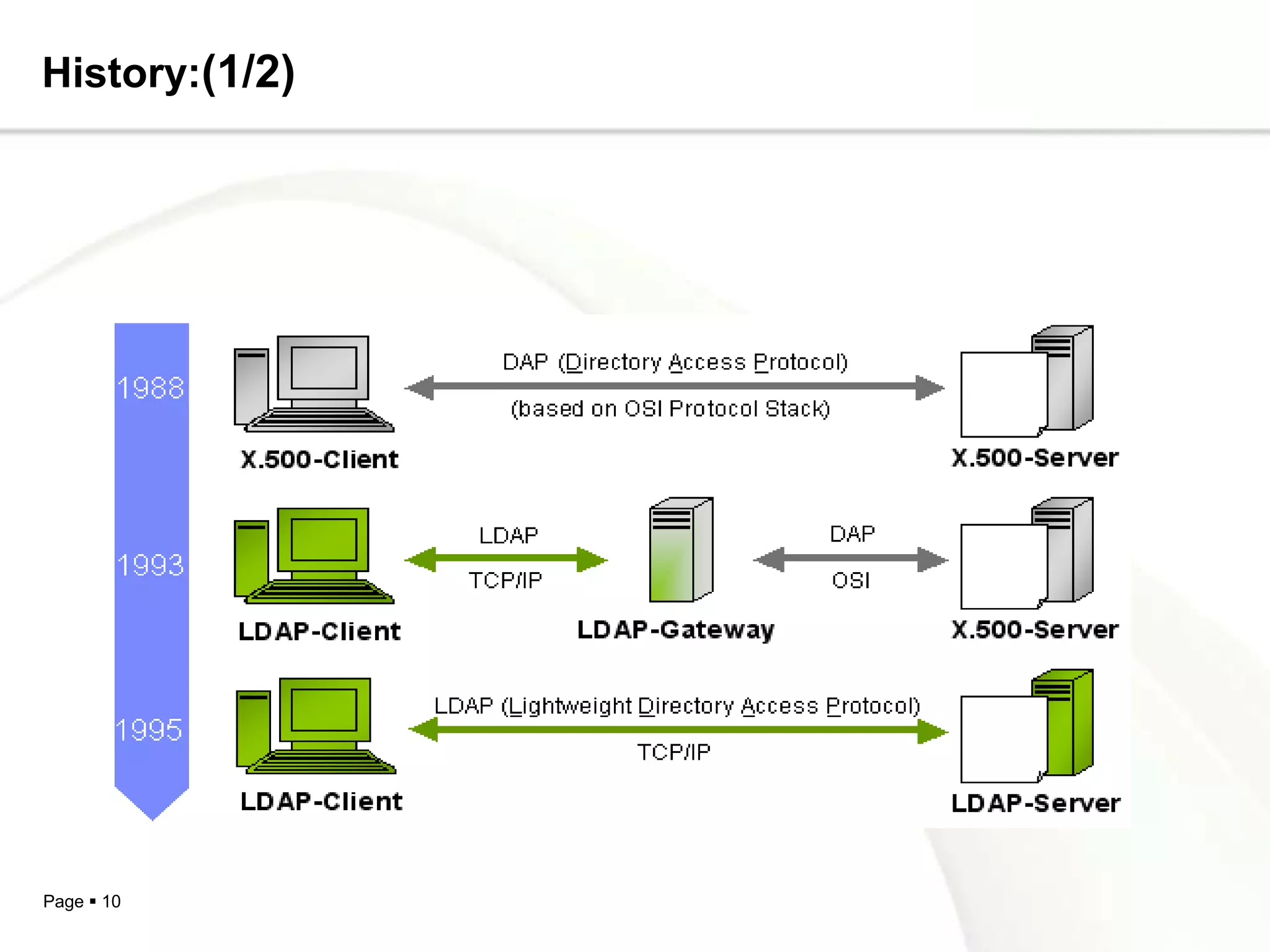
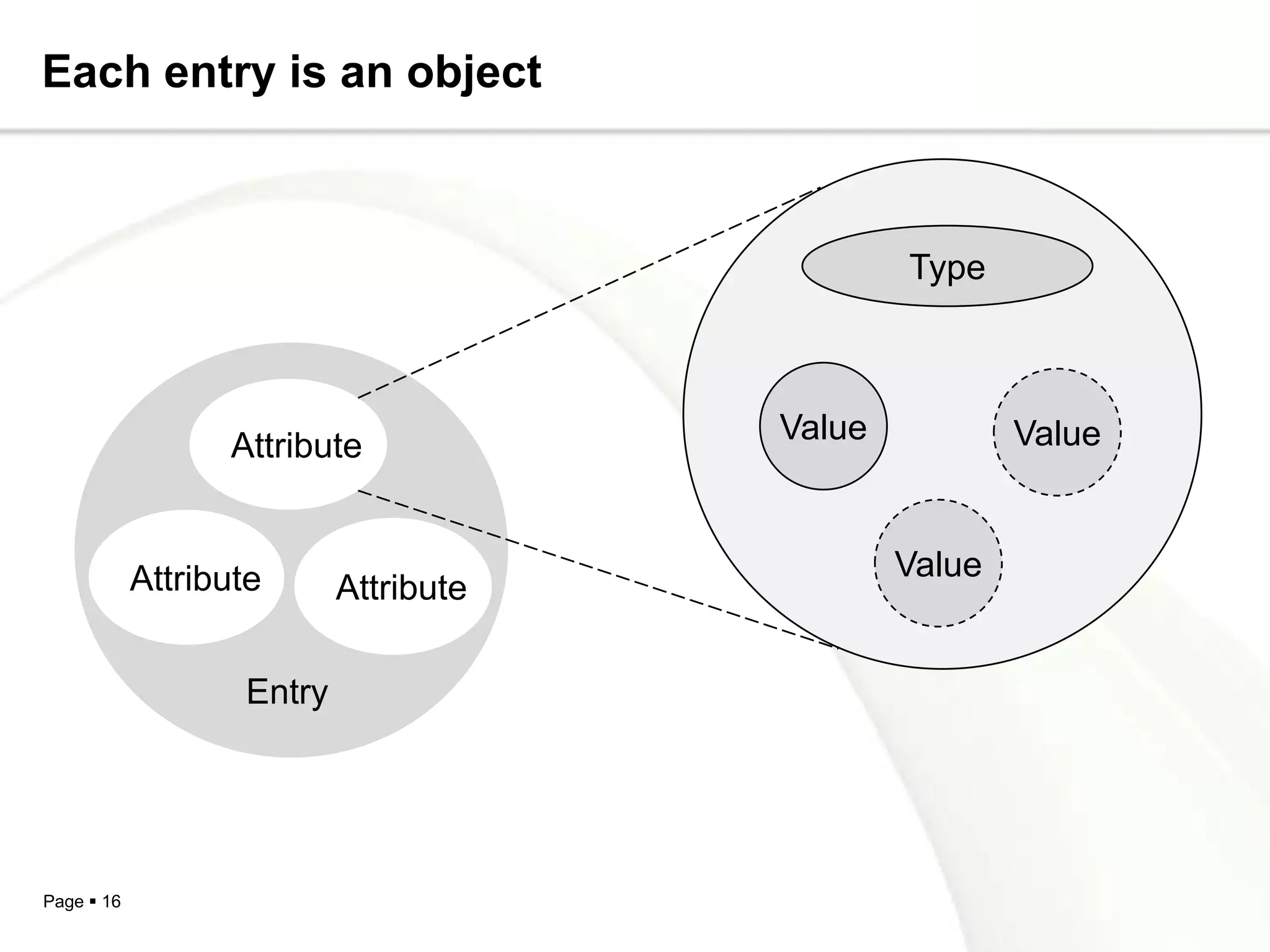
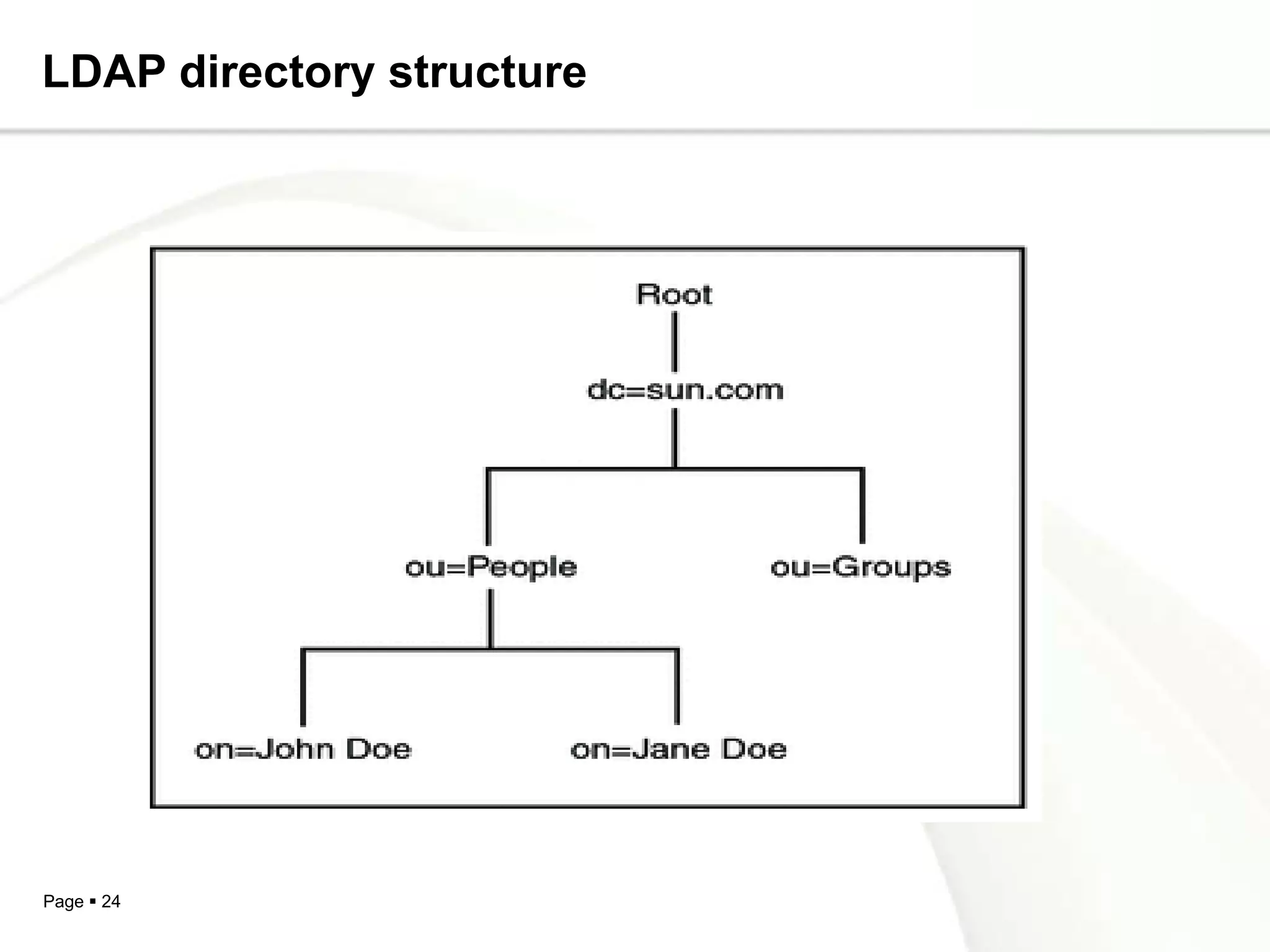
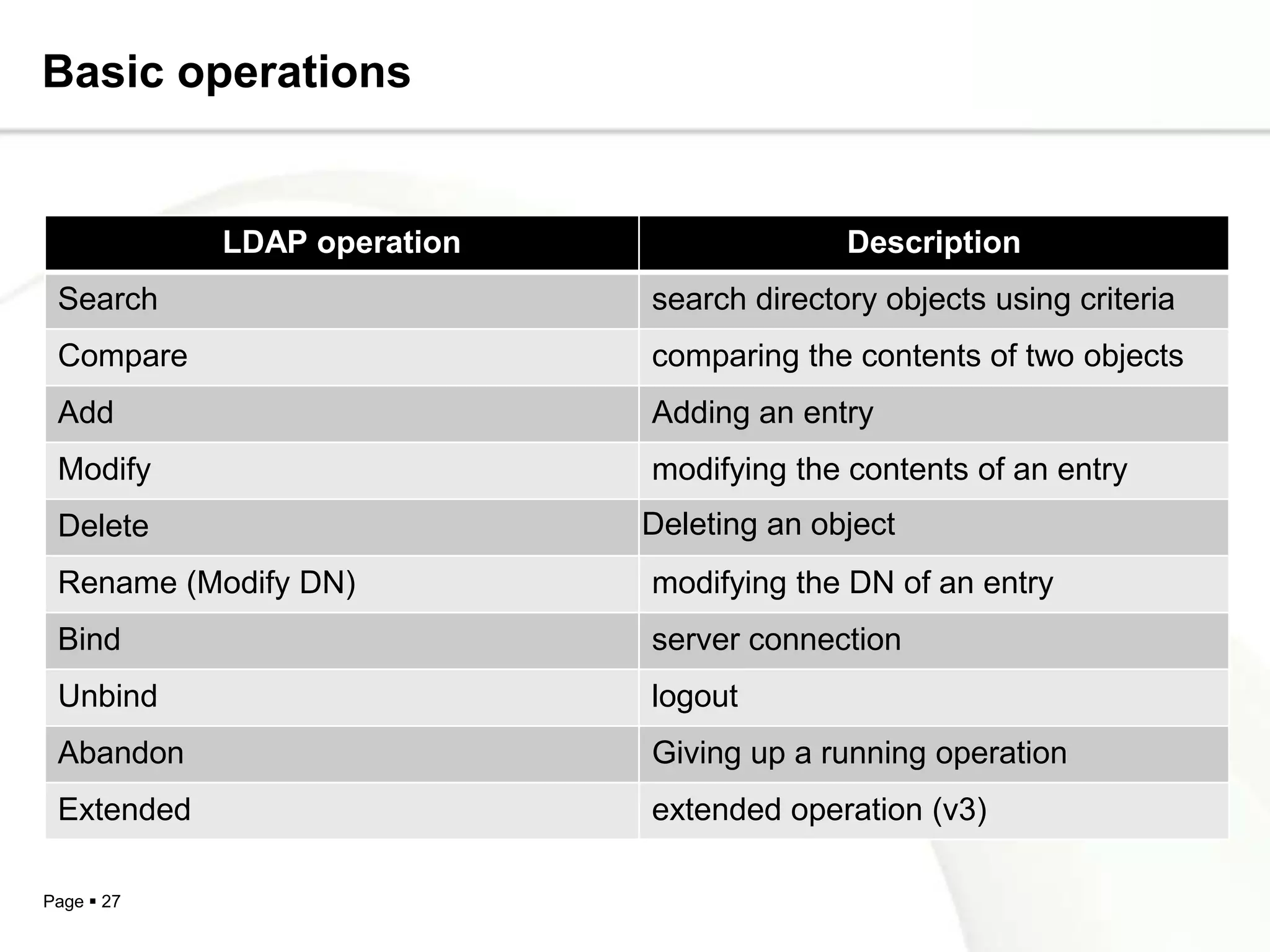
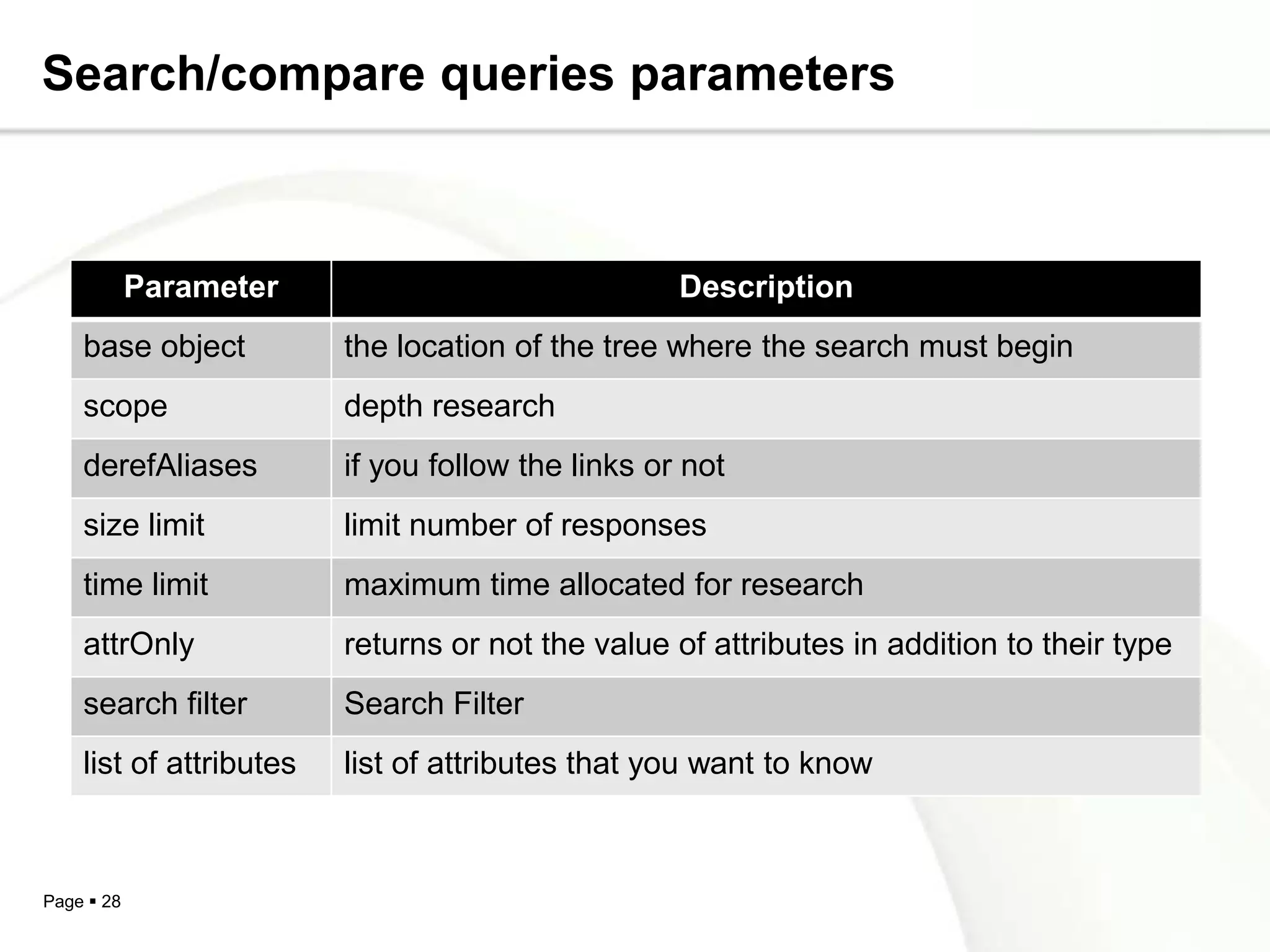
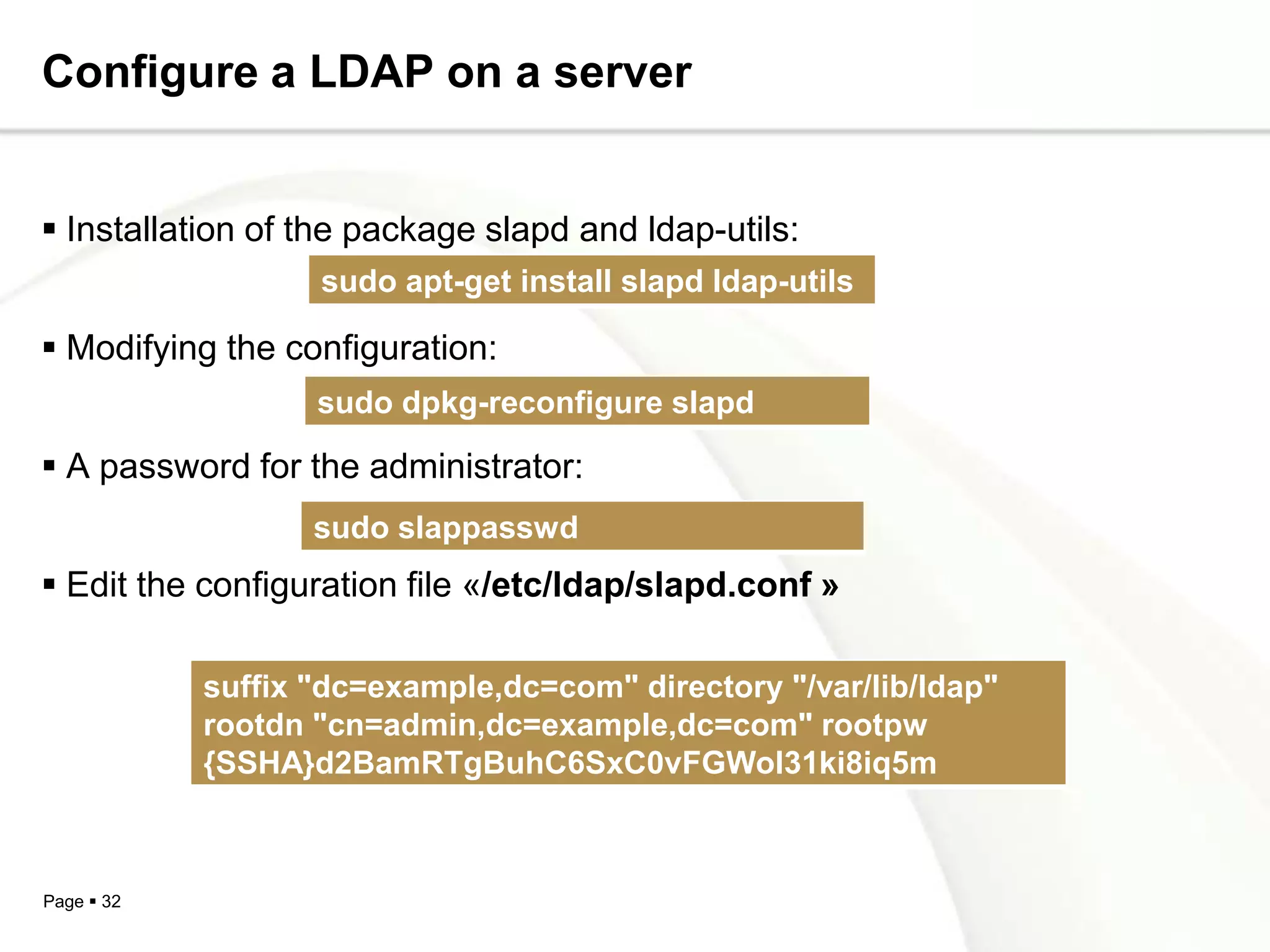
This document provides an overview of the Lightweight Directory Access Protocol (LDAP). It describes LDAP as an open standard for accessing distributed directory services that is optimized for read performance. The document outlines LDAP's information model, naming model, directory structure, supported operations, and security features. It also provides information on configuring an LDAP server and the software available to implement LDAP directories and clients.