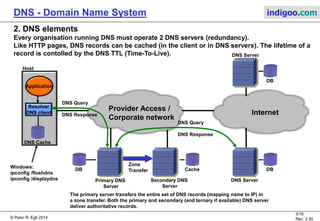
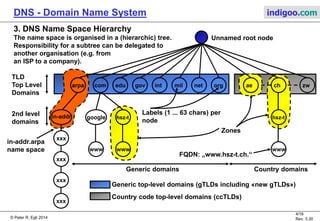
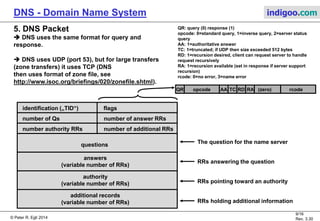
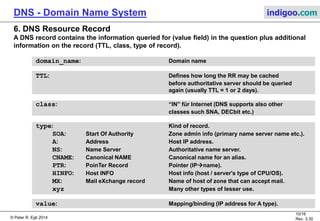
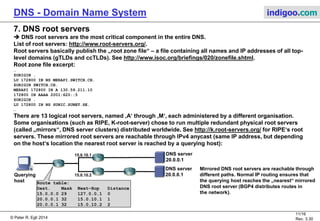
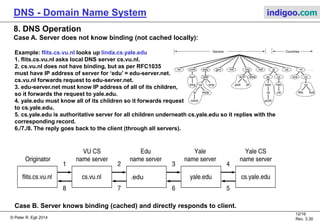
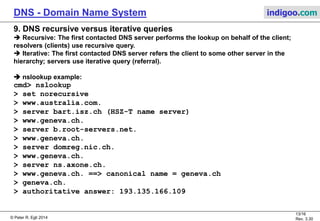
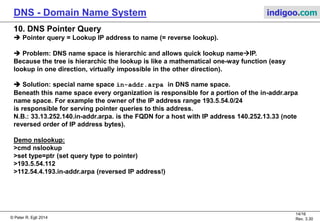
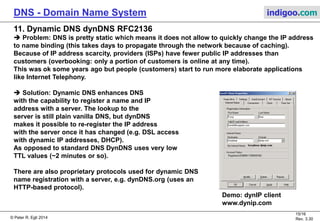
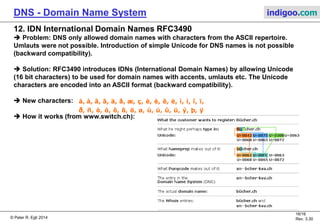
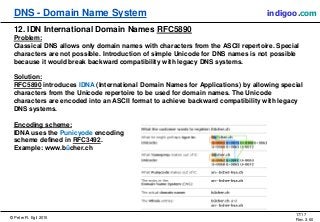
The document is an in-depth overview of the Domain Name System (DNS), detailing its purpose as a distributed system that maps symbolic names to IP addresses. It covers DNS elements, hierarchy, operational mechanisms, and various terms associated with DNS, such as authoritative records and resource records. Additionally, it addresses dynamic DNS, international domain names, and the technical specifications of DNS packets and queries.