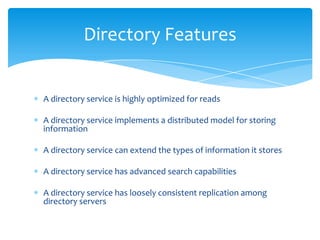
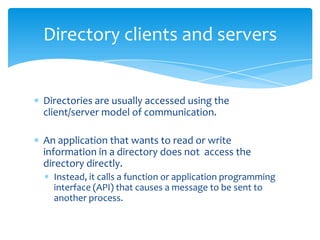
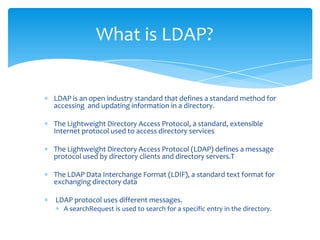
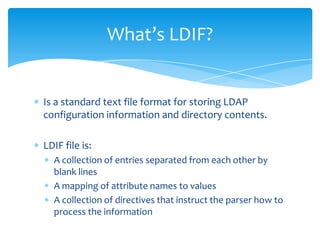
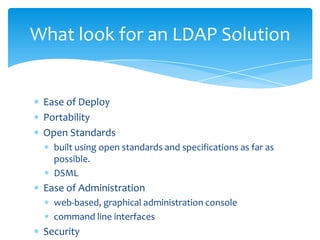
The document provides an overview of identity and access management (IAM) solutions, with a focus on directory services and the Lightweight Directory Access Protocol (LDAP). It explains the structure and features of directories, how LDAP functions for accessing and updating directory information, and highlights the importance of involving stakeholders in implementing such systems. Additionally, it offers insights into various vendors offering single sign-on solutions and emphasizes the benefits of using open standards in directory services.