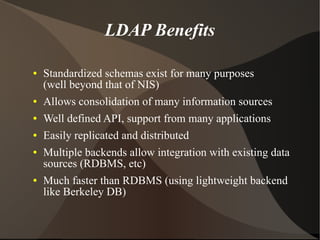
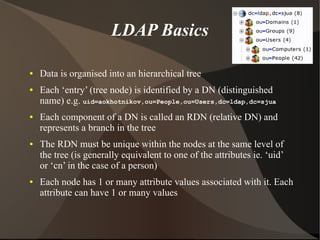
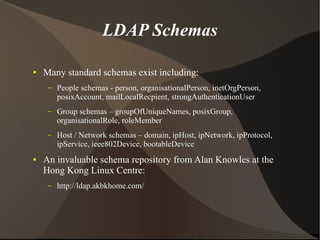
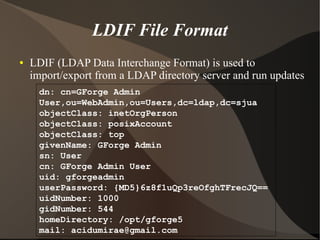
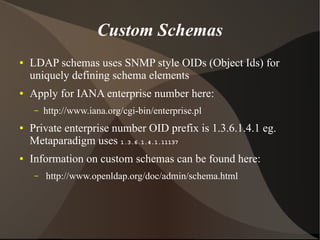
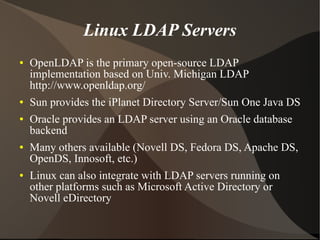
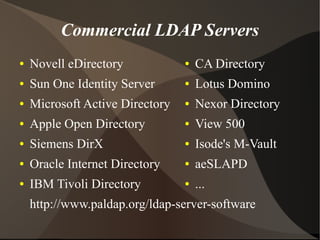
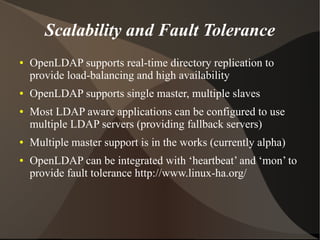
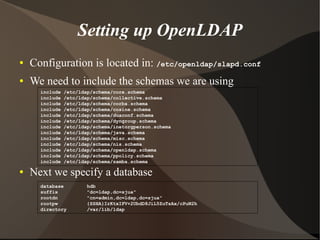
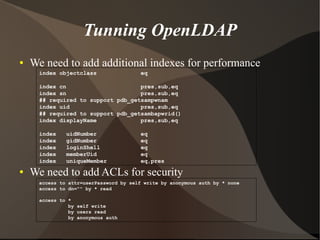
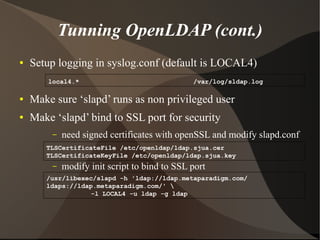
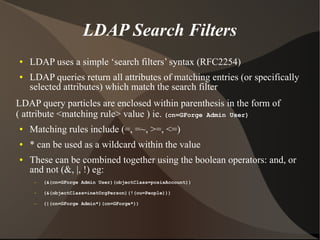
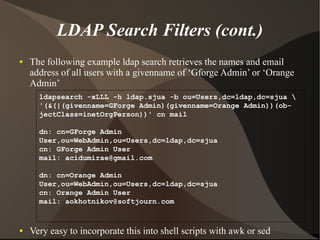
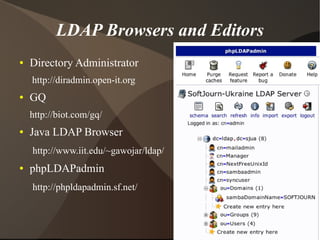
This document provides an overview of LDAP (Lightweight Directory Access Protocol). It discusses what directory services are, the need for LDAP to centralize user information, and some key LDAP concepts like its data model, schemas, and LDIF format. It also covers setting up an OpenLDAP server, including configuration, indexing, access control, and integration with other LDAP tools and applications.