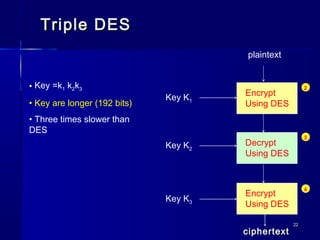
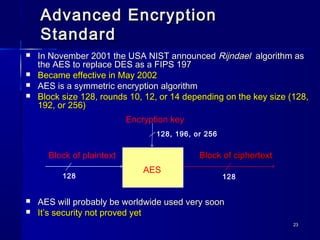
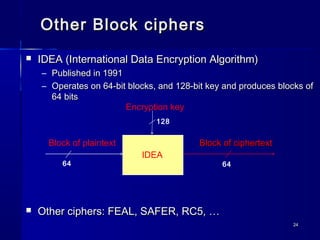
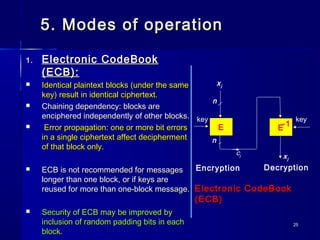
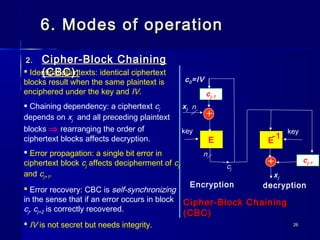
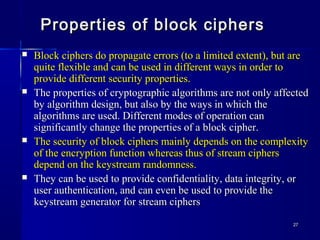
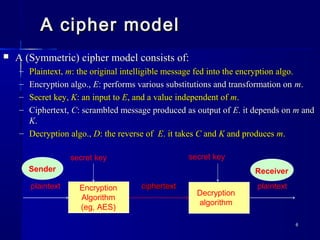
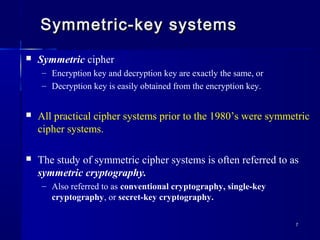
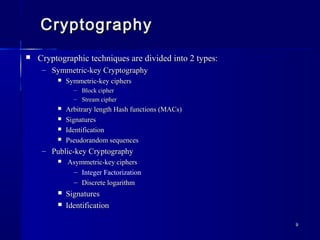
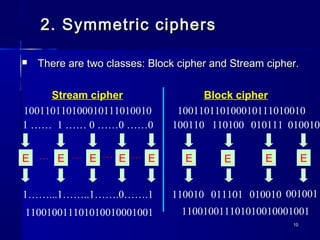
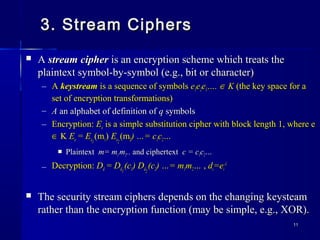
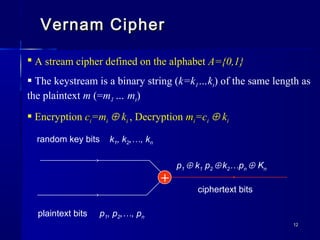
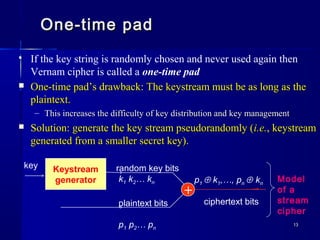
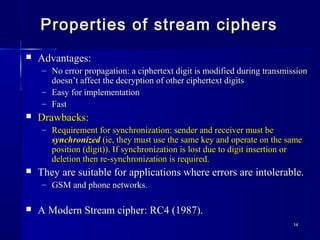
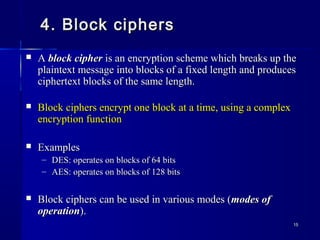
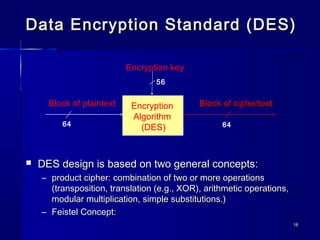
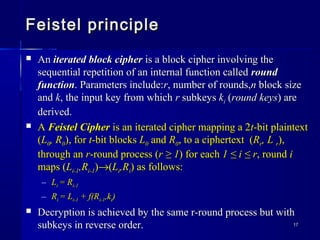
This document discusses symmetric cryptography and provides an overview of symmetric cipher systems including stream ciphers like the Vernam cipher and one-time pad, as well as block ciphers like DES, Triple DES, and AES. It describes the basic components of a symmetric cipher model and the properties and modes of operation for symmetric encryption algorithms. Key topics covered include the Feistel cipher structure used by DES, the cryptanalysis of DES leading to its replacement by AES, and the advantages and disadvantages of stream and block ciphers.
![1919
DES EncryptionDES Encryption (ch 7 ,[2])(ch 7 ,[2])
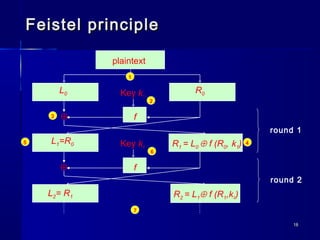
L0 R0
f
L1=R0
R1 = L0 ⊕ f (R0, k1)
Key k1
Plaintext
⊕
IP
L16 = R15
IP-1
R16 = L15 ⊕ f (R15, k16)
Ciphertext
64
3232
48
32 32
64
3232](https://image.slidesharecdn.com/isslecture2-130428071416-phpapp02/85/Iss-lecture-2-19-320.jpg)
![2121
DES propertiesDES properties
DES has 4 weak keys and six pairs of semi-weak keysDES has 4 weak keys and six pairs of semi-weak keys
– A DES weak key is a keyA DES weak key is a key kk such thatsuch that EEkk(E(Ekk(x))=x(x))=x for allfor all xx
– A pair of DES semi weak keys is a pair (A pair of DES semi weak keys is a pair (KK11,K,K22) with) with EEkk11
(E(Ekk22
(x))=x(x))=x Tables 7.5Tables 7.5
and 7.6, of weak and semi-weak keys on pp. 258 of [2].and 7.6, of weak and semi-weak keys on pp. 258 of [2].
DES TodayDES Today
– A DES key can be found by anyone determined enough.A DES key can be found by anyone determined enough.
In 1998 Electronic Frontier Foundation managed to break DES (using DESIn 1998 Electronic Frontier Foundation managed to break DES (using DES
Cracker, costing < $250,000 ) in less than 3 days.Cracker, costing < $250,000 ) in less than 3 days.
– Differential and linear cryptanalysis provide academic attacks on DES.Differential and linear cryptanalysis provide academic attacks on DES.
– However, DES is still in use in many applications.However, DES is still in use in many applications.
– Triple DES or AES are commonly recommended instead of DES.Triple DES or AES are commonly recommended instead of DES.](https://image.slidesharecdn.com/isslecture2-130428071416-phpapp02/85/Iss-lecture-2-21-320.jpg)