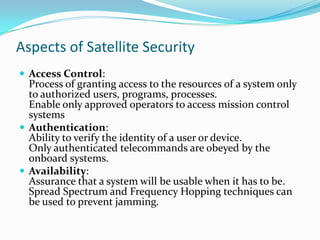
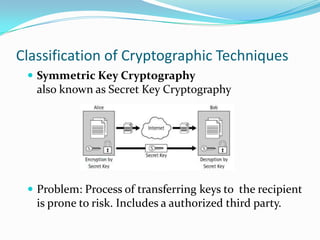
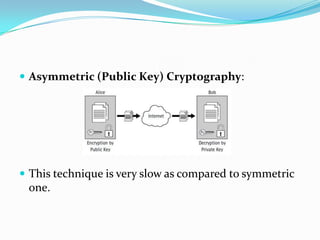
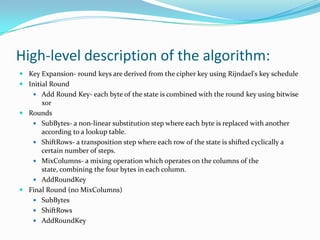
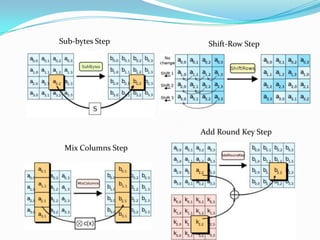
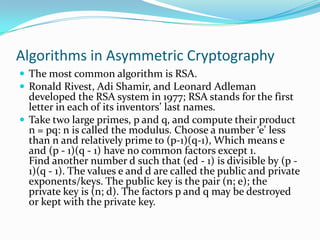
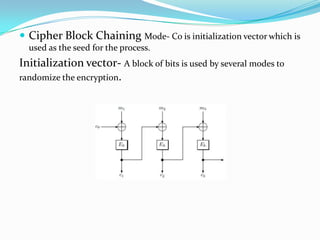
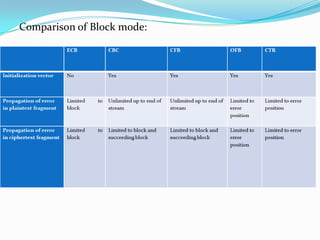
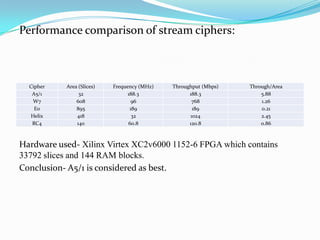
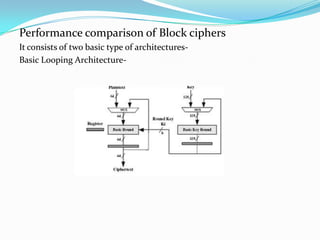
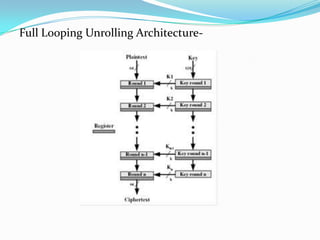
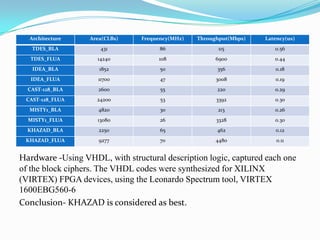
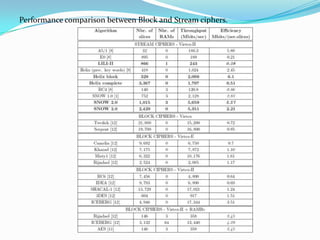
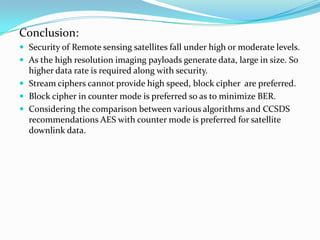
This document discusses and compares various cryptographic algorithms for use in securing satellite downlink communications. It begins with an overview of aspects of satellite security and introduces cryptography. It then covers symmetric and asymmetric cryptographic algorithms like AES, RSA and stream ciphers. It analyzes the performance of algorithms in terms of hardware usage and throughput. Block cipher modes and attacks on cryptosystems are also examined. The document concludes by recommending the KHAZAD block cipher and A5/1 stream cipher as best suited for satellite security based on a performance comparison.


![References :
[1] RSA Laboratories, RSA Laboratories’ Frequently Asked Questions About Today’s Cryptography, Version 4.1, RSA Security
Inc., 2000
[2] Encryption algorithm Trade Survey, Report Concerning Space Data System Standards, CCSDS-350.2-G-1, Green
Book, Washington D.C.: CCSDS, March 2008.
[3] Symmetric Encryption, Draft Recommendation for Space Data Practices, CCSDS 353.0-R-1, Red Book, Washington
D.C., October 2008
[4] Audia_S_Abd Al_R_Asedy, Ameer A.J Al_ Swidi, An advantages and disadvantages of Block and Stream Cipher,
<http://www.uobabylon.edu.iq/uobColeges/fileshare/articles/block.pdf>
[5]Cryptography Basics
<http://media.wiley.com/product_data/excerpt/94/07645487/0764548794.pdf>
[6] Advanced Encryption Standard, Federal Information Processing Standards Publications
197, November 26, 2001
[7] Mohammed Atiquzzaman and Md. Shohrab Hossain, Security Issues in Space Networks,
[8] The Secret Satellite, www.apscc.or.kr | APSCC Yearbook 2007
[9]Michalis Galanis, Paris Kitsos, Giorgos Kostopoulos, Nicolas Sklavos, and Costas Goutis, Comparison
of the Hardware Implementation of the Stream Ciphers, The International Arab Journal of Information
Technology, Vol. 2, No. 4, October 2005](https://image.slidesharecdn.com/astudyofcryptographyforsatelliteapplications-120430130627-phpapp02/85/A-study-of-cryptography-for-satellite-applications-50-320.jpg)