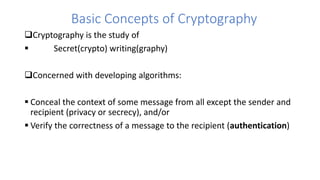
This document discusses information security, including types of attacks, security services, mechanisms, and cryptography concepts. It covers passive and active attacks such as interception and modification. Cryptography techniques include substitution and transposition ciphers using keys known only to the sender and receiver. The document also discusses cryptanalysis methods like known-plaintext analysis and man-in-the-middle attacks, as well as stream ciphers that generate a keying stream from a secret seed.