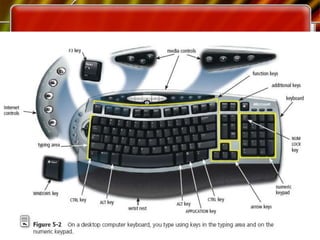
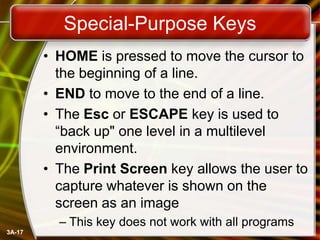
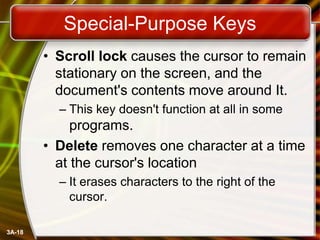
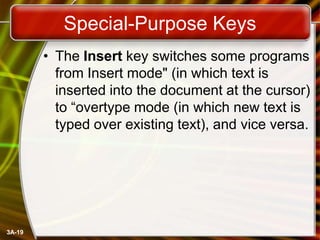
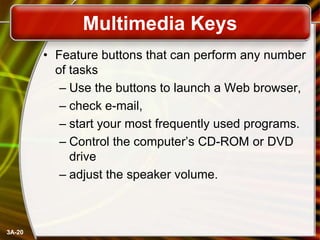
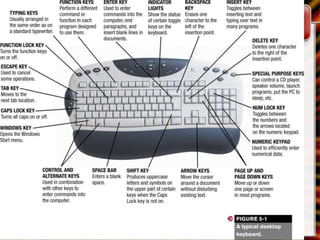
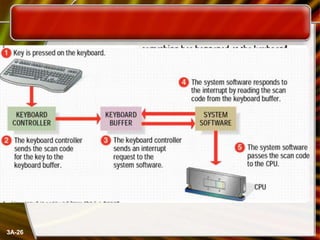
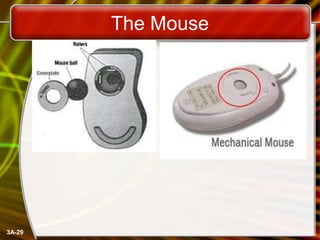
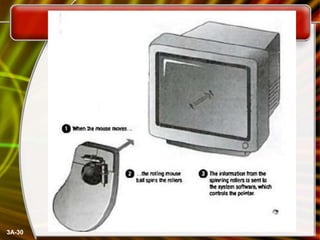
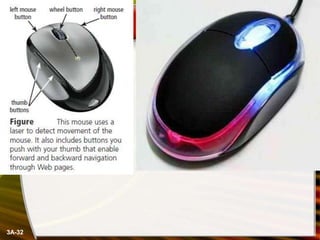
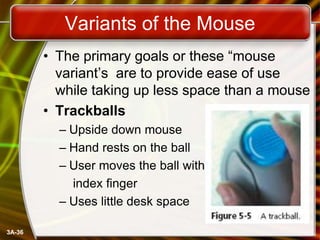
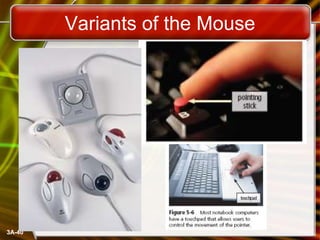
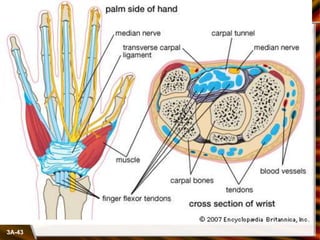
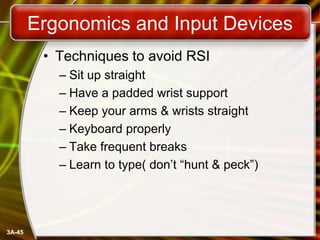
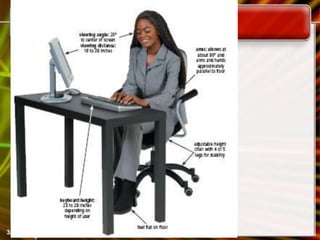
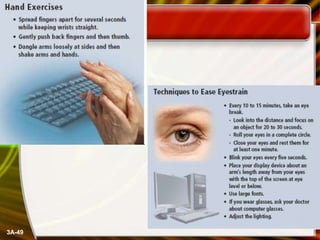
This chapter discusses common computer input devices like the keyboard and mouse. It describes the standard QWERTY keyboard layout and the purpose of different types of keys. Mice can be mechanical or optical, and variants include trackballs and touchpads. Proper ergonomics are important to prevent repetitive strain injuries when using input devices extensively. The keyboard and mouse allow users to interact with computers by entering text, numbers, commands and selecting options.