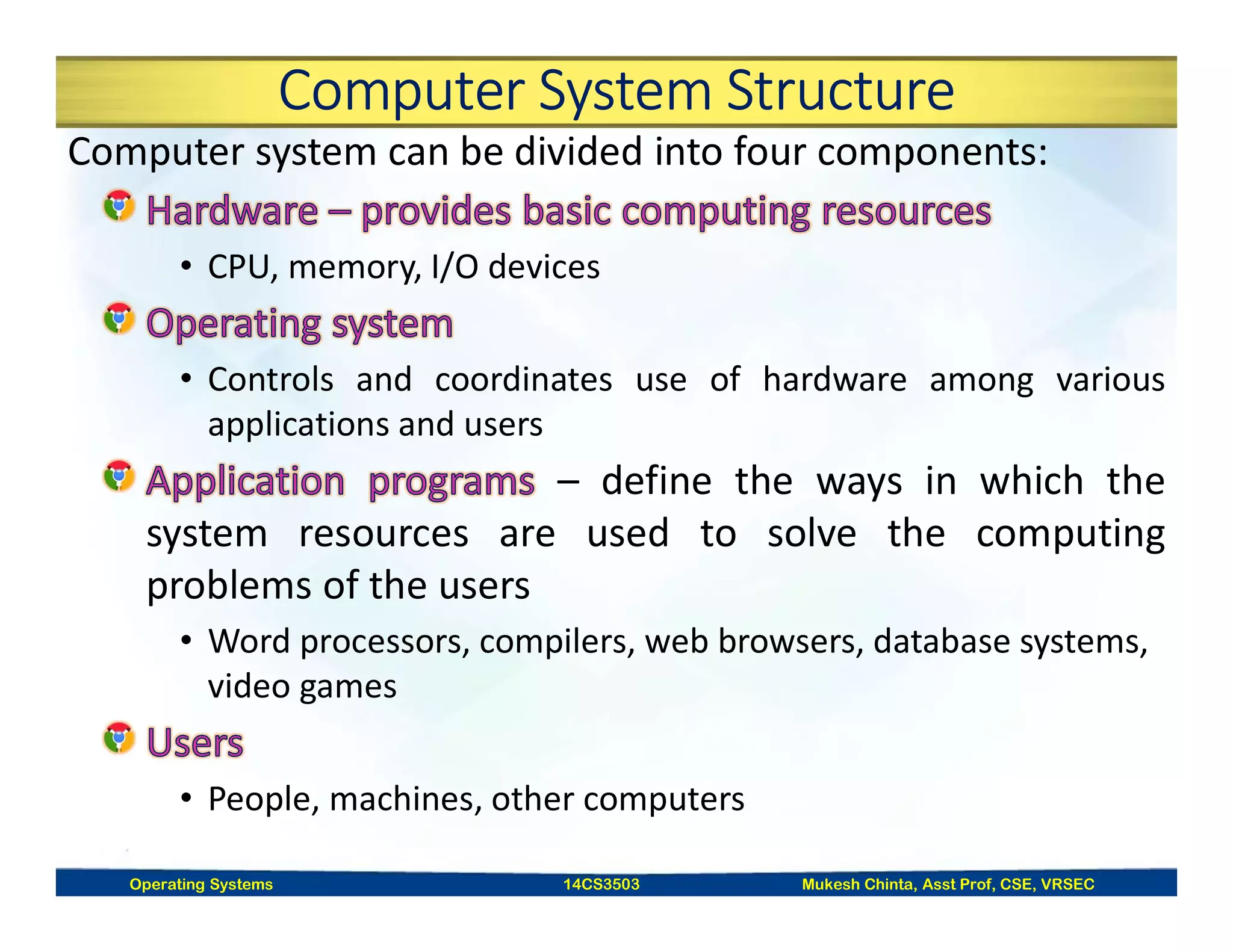
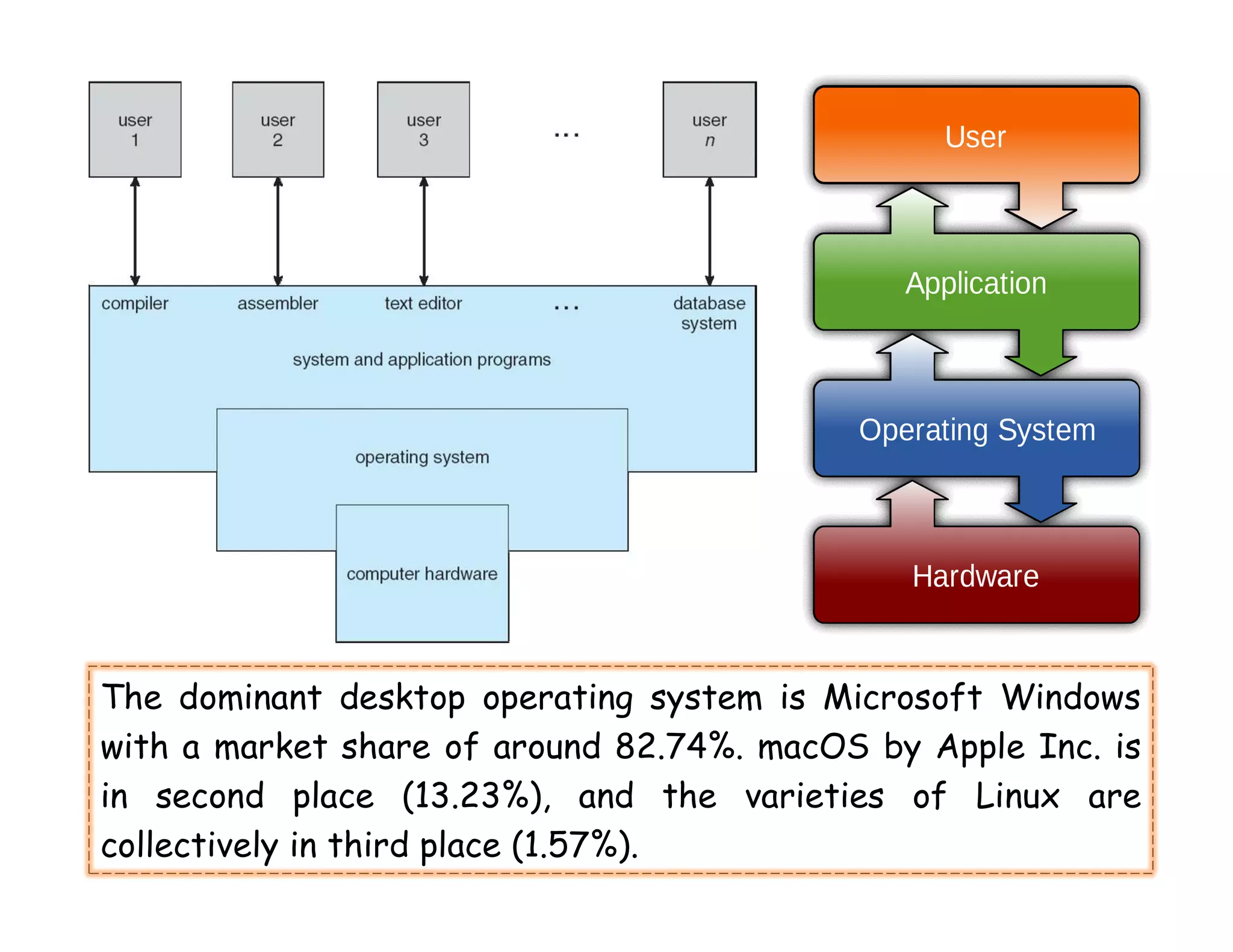
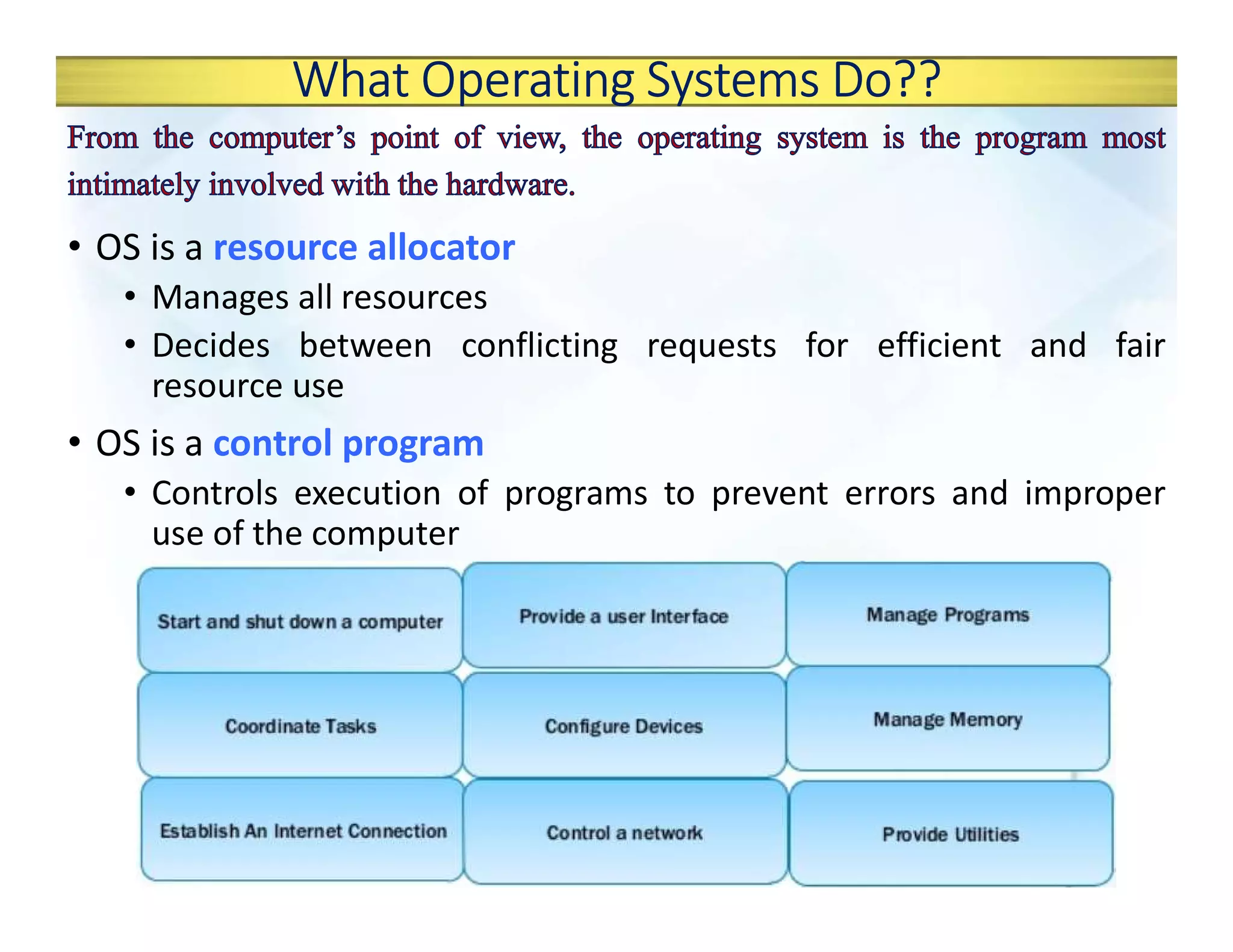
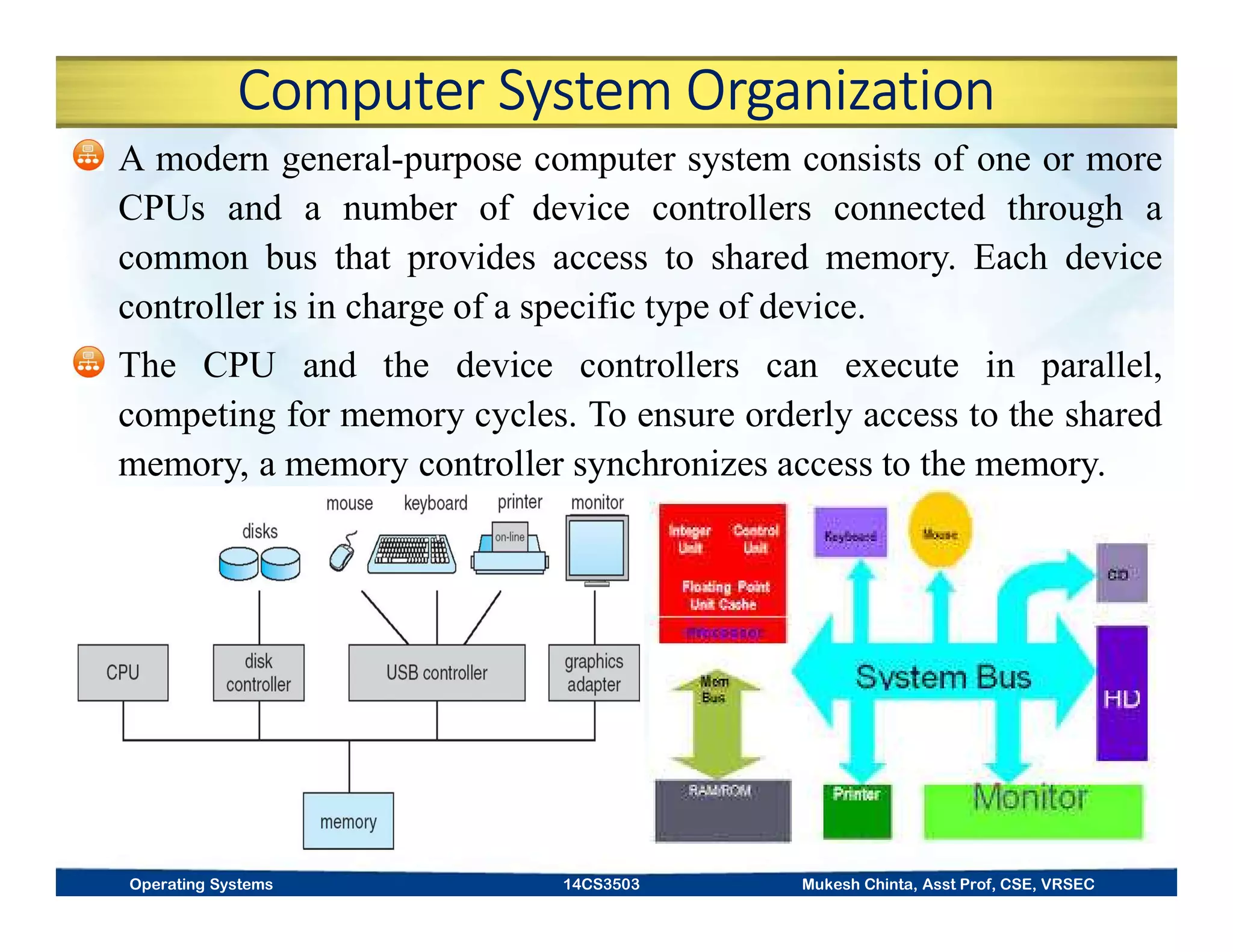
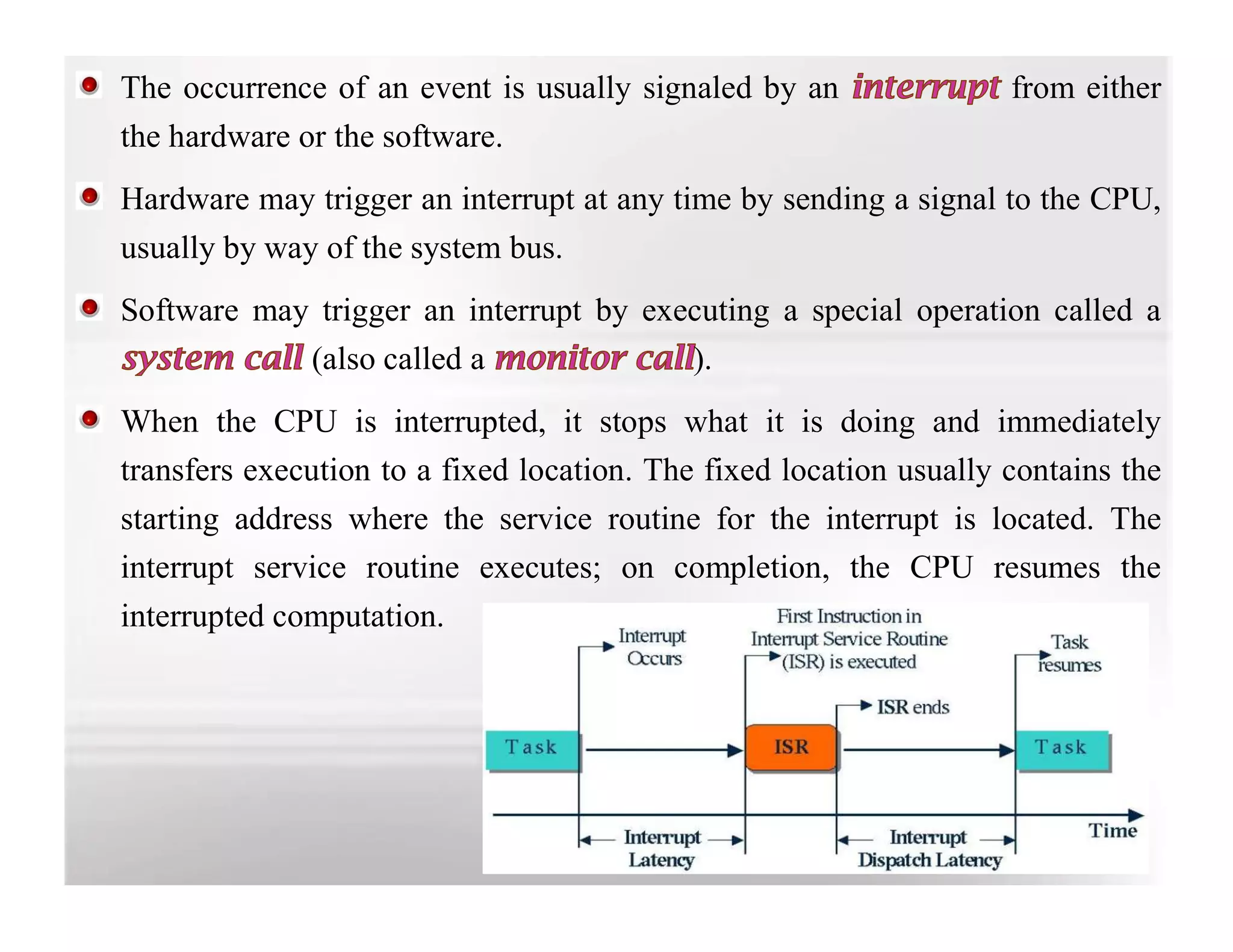
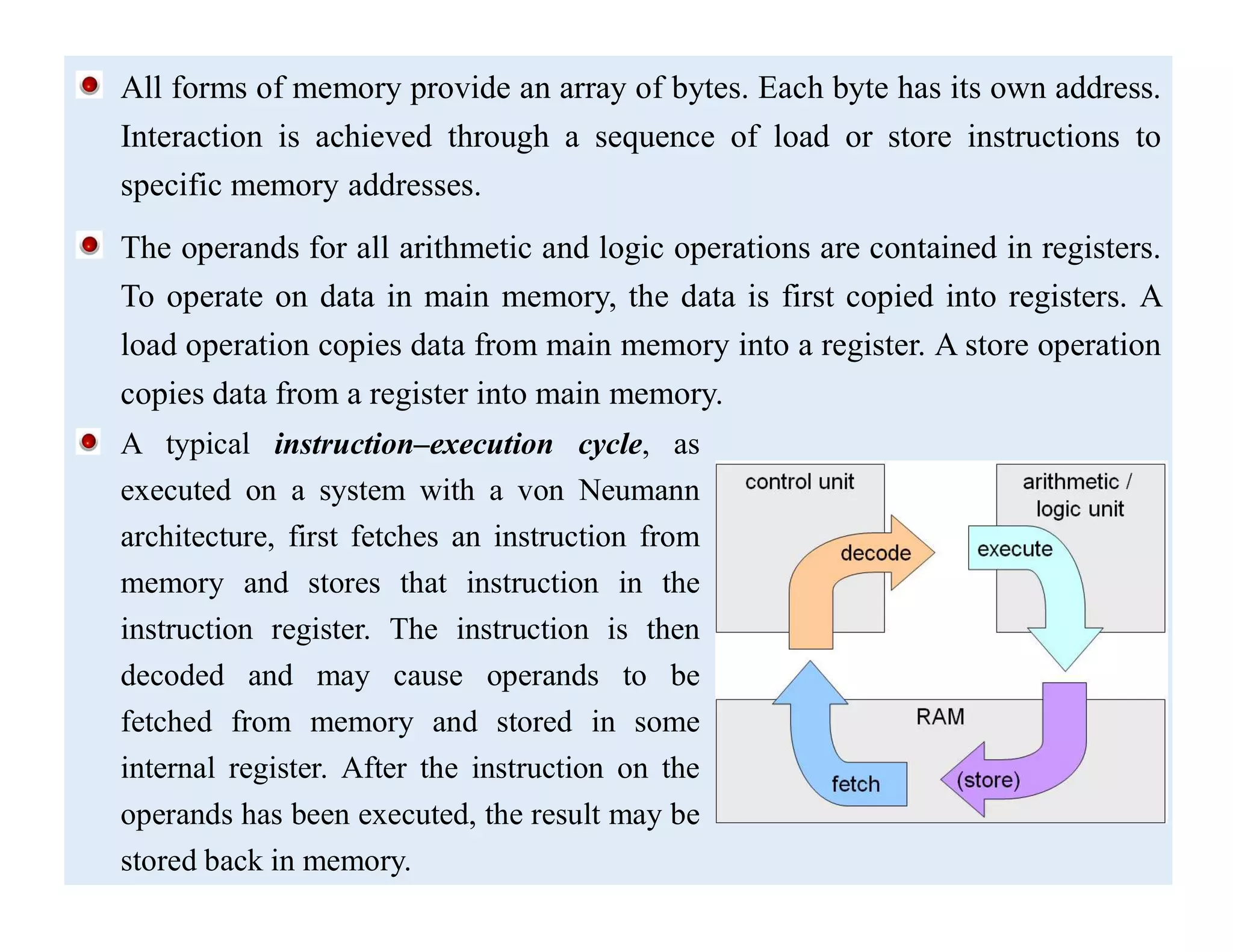
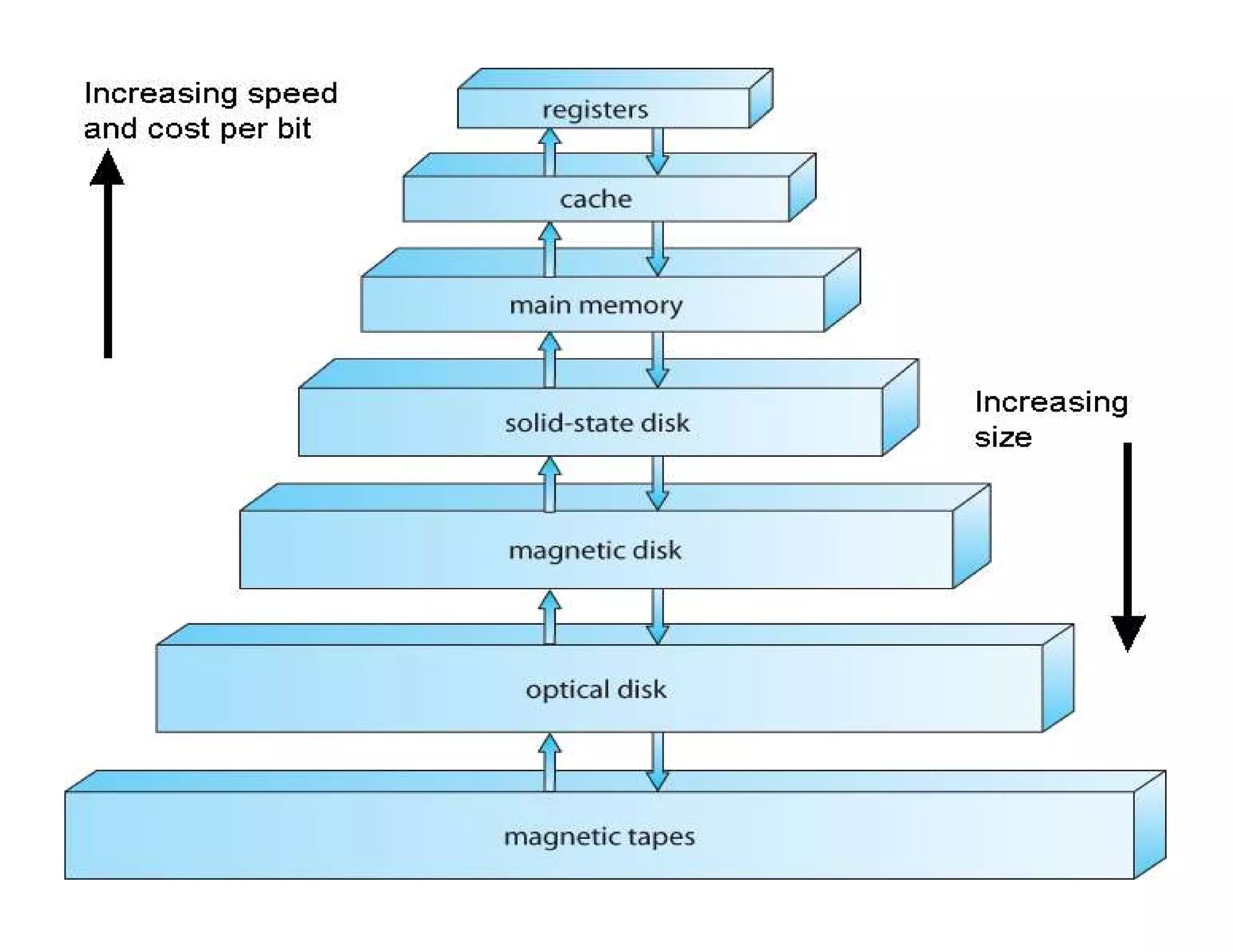
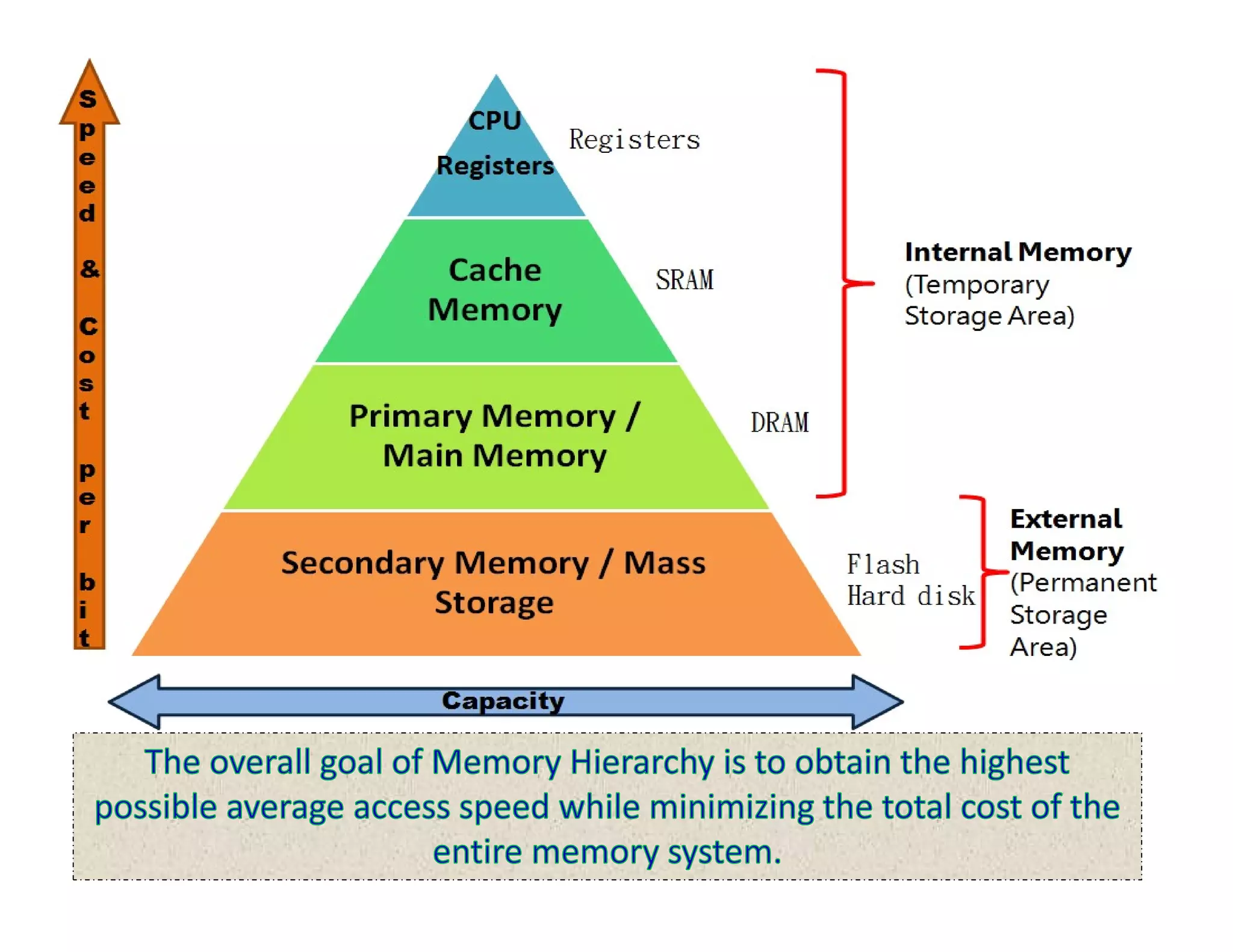
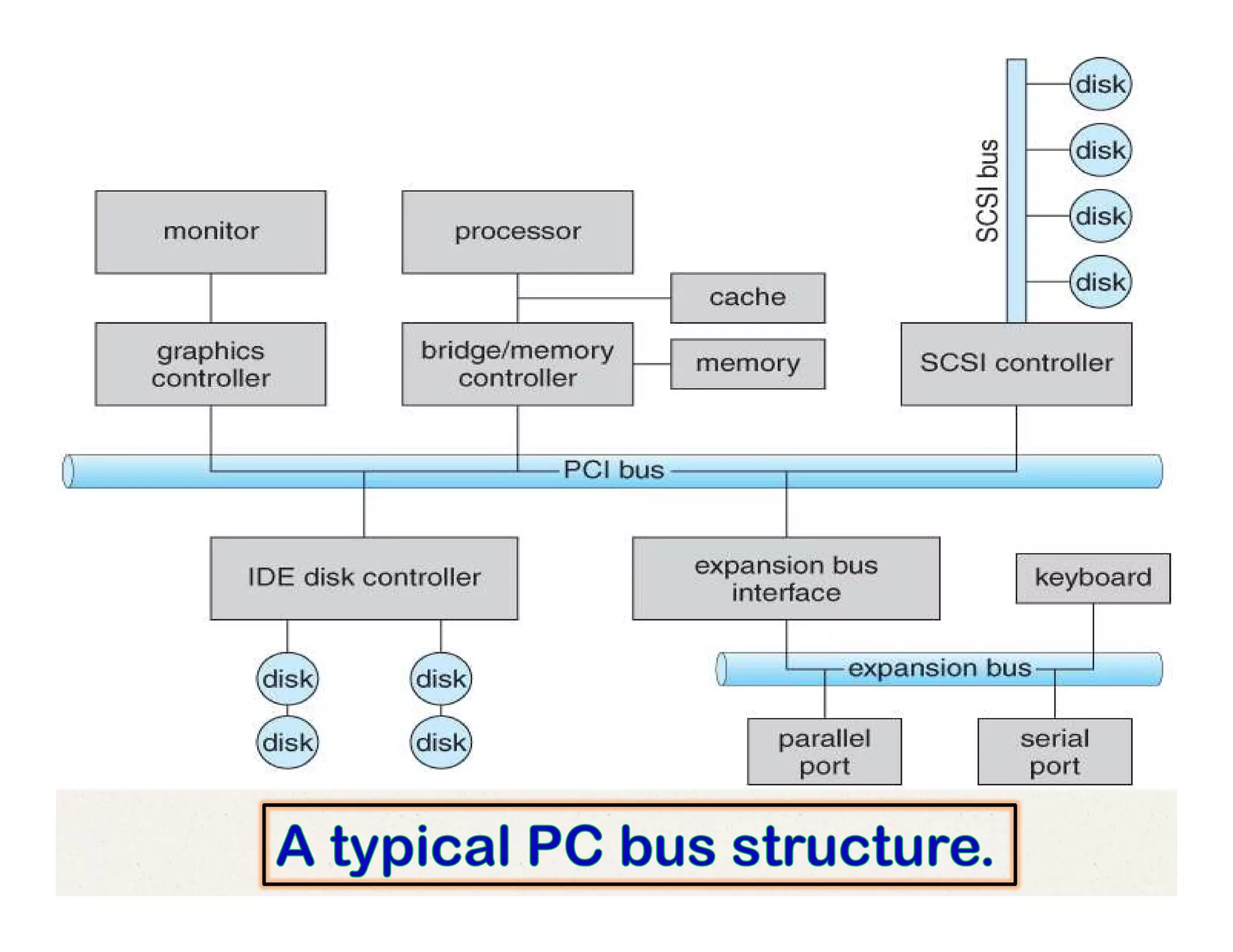
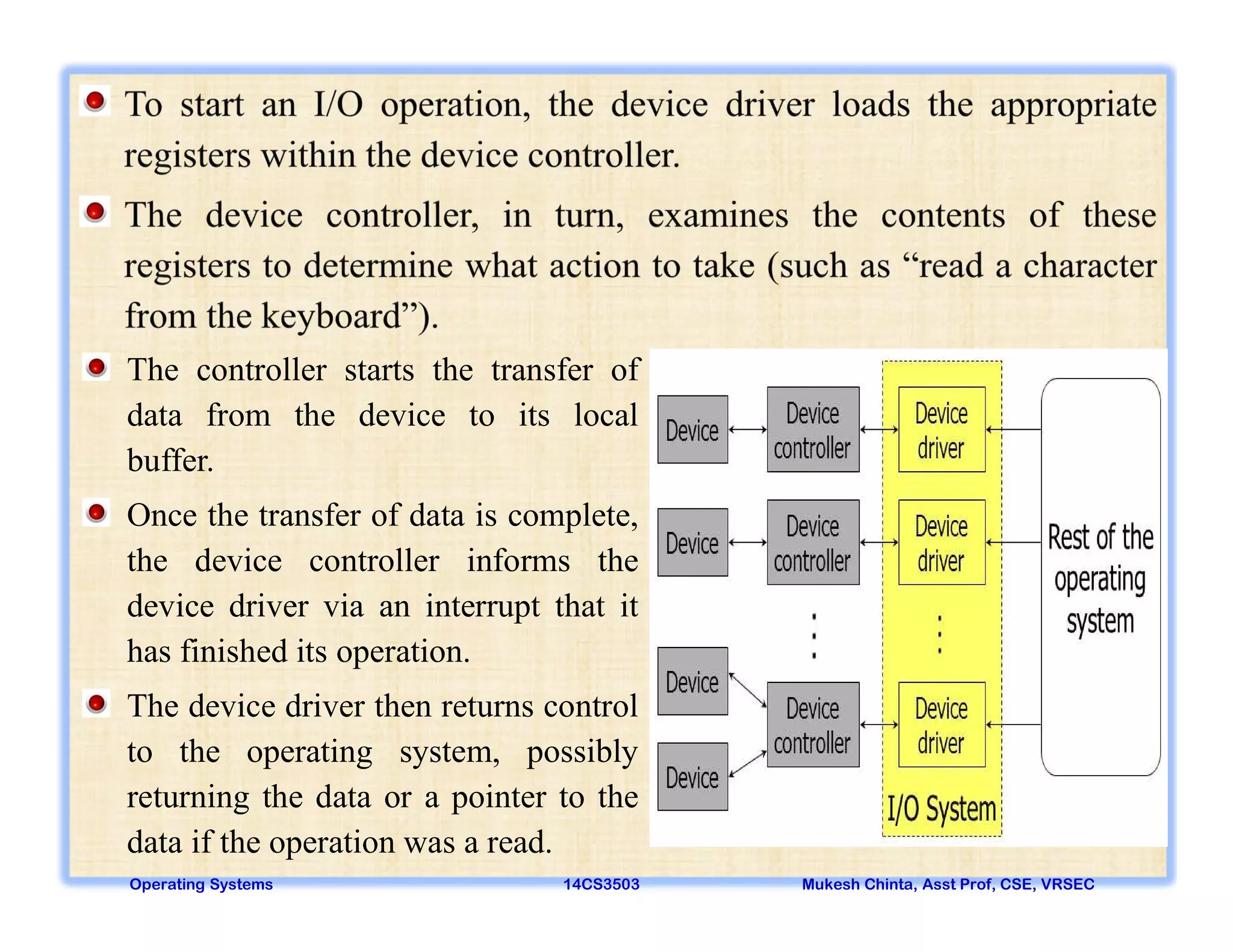
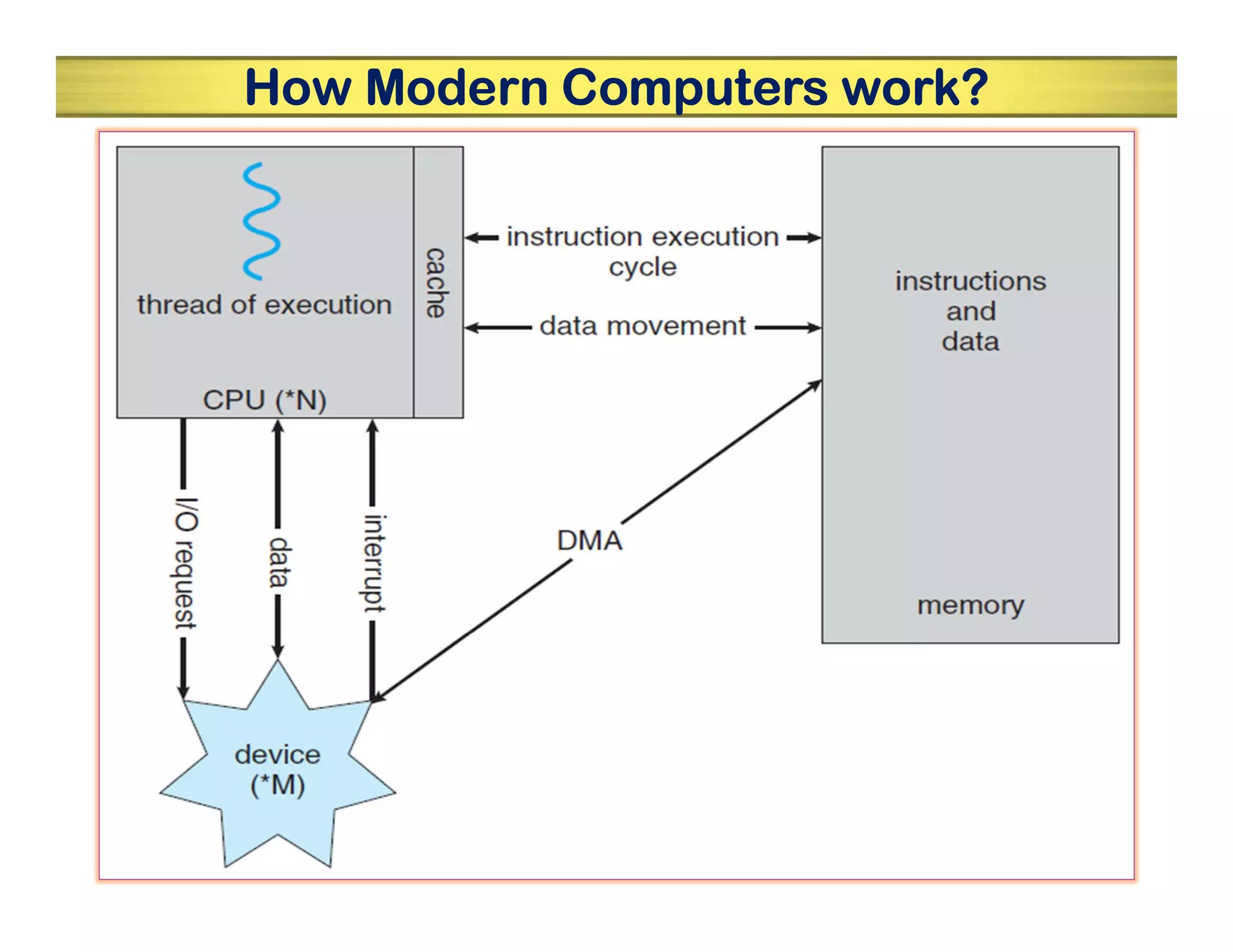
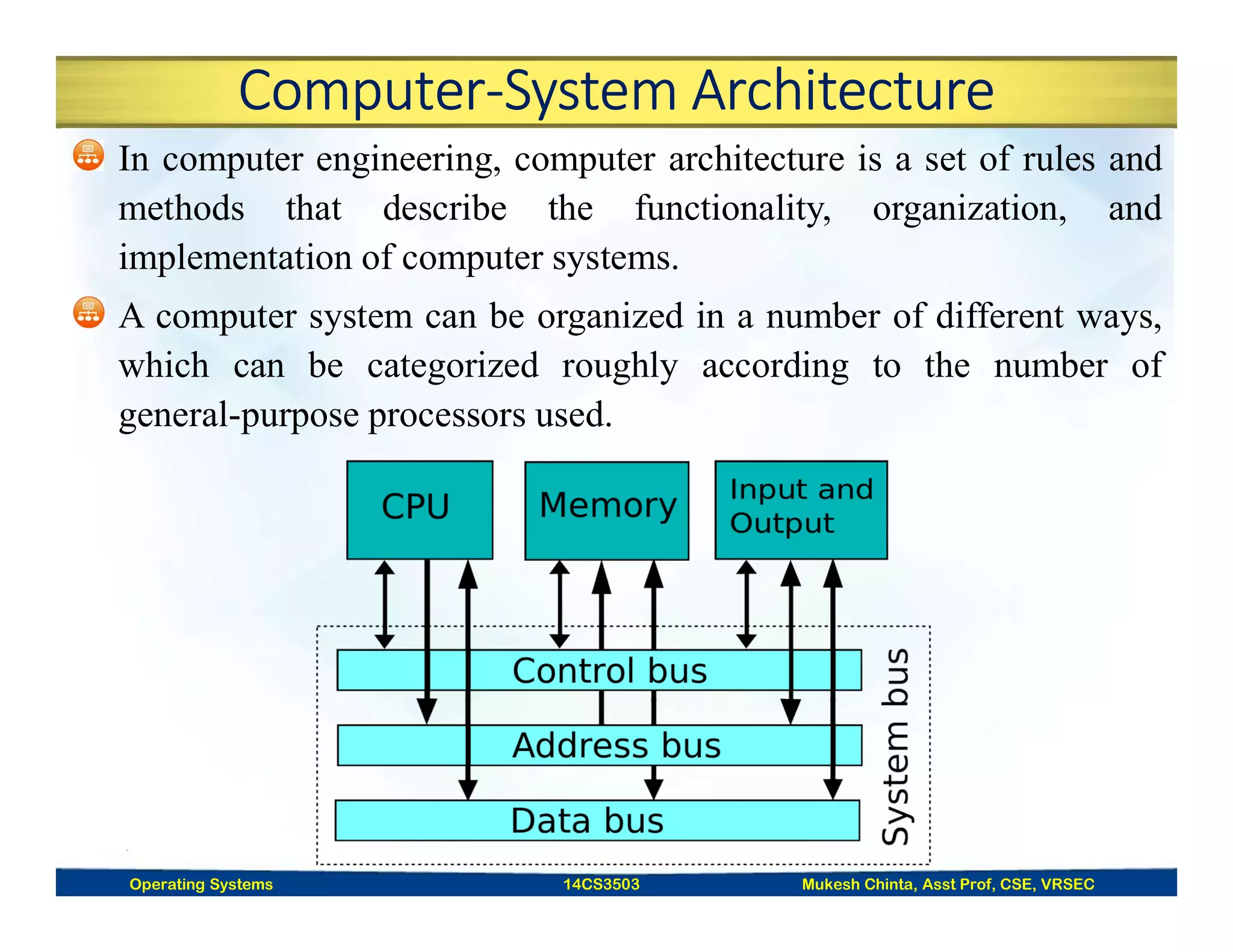
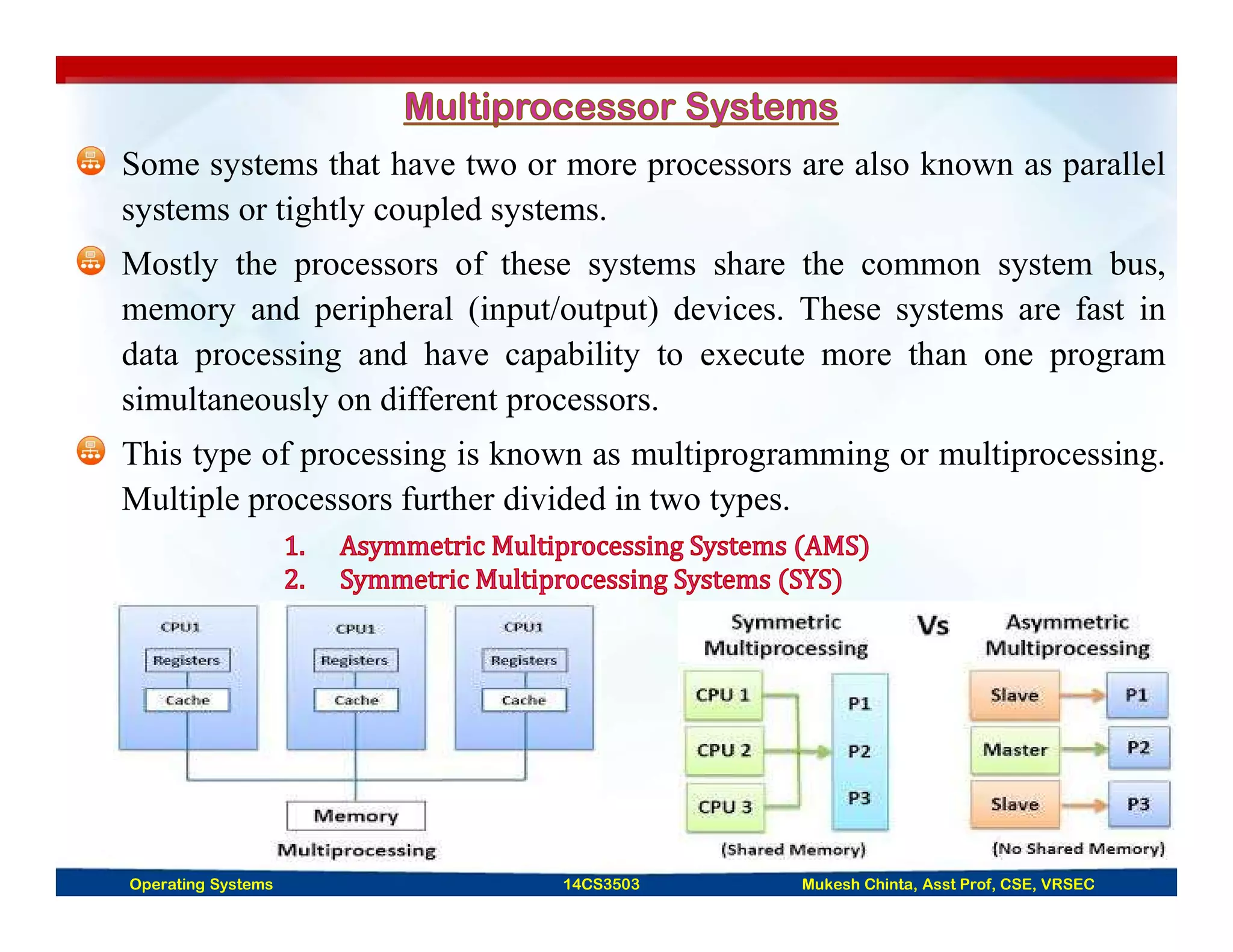
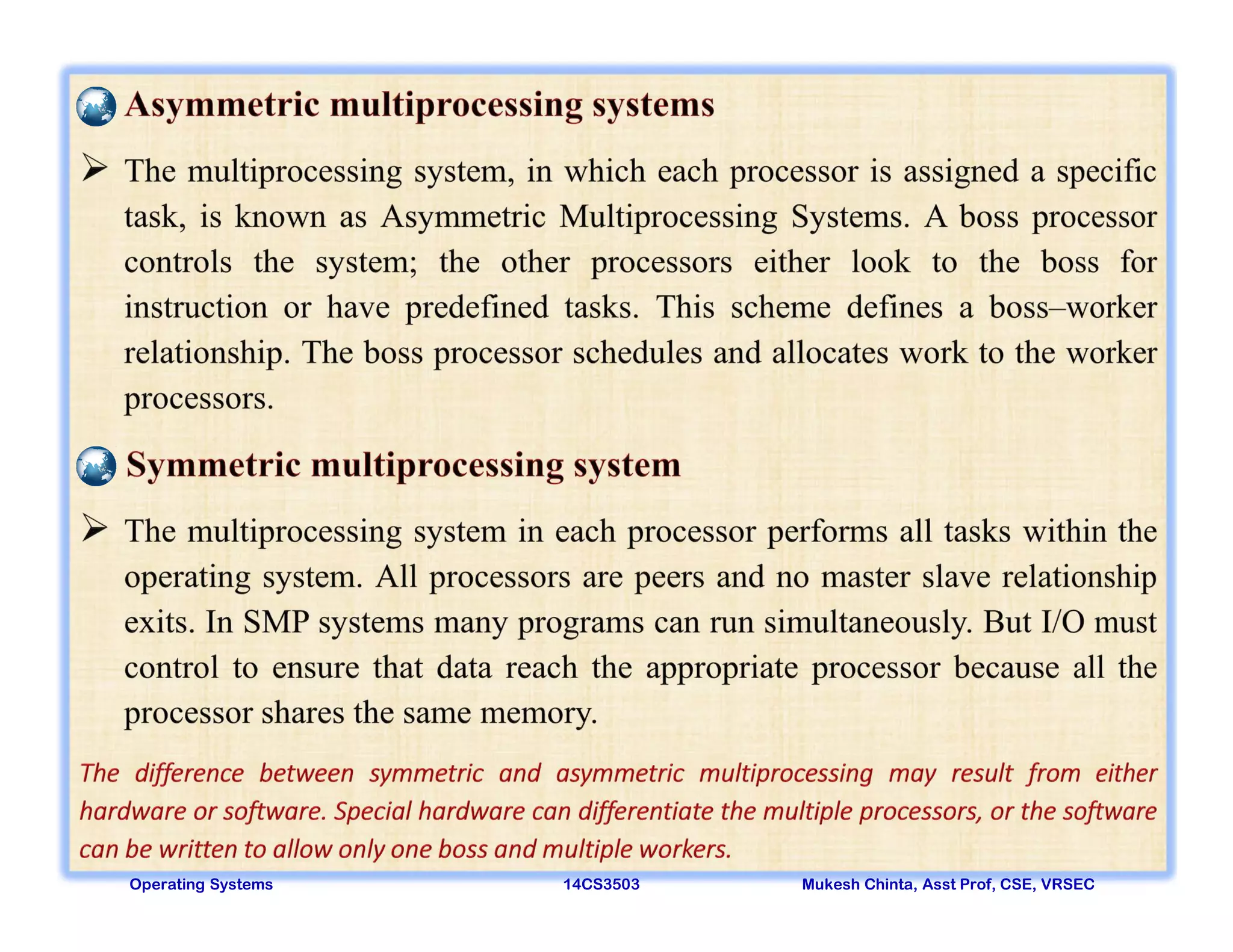
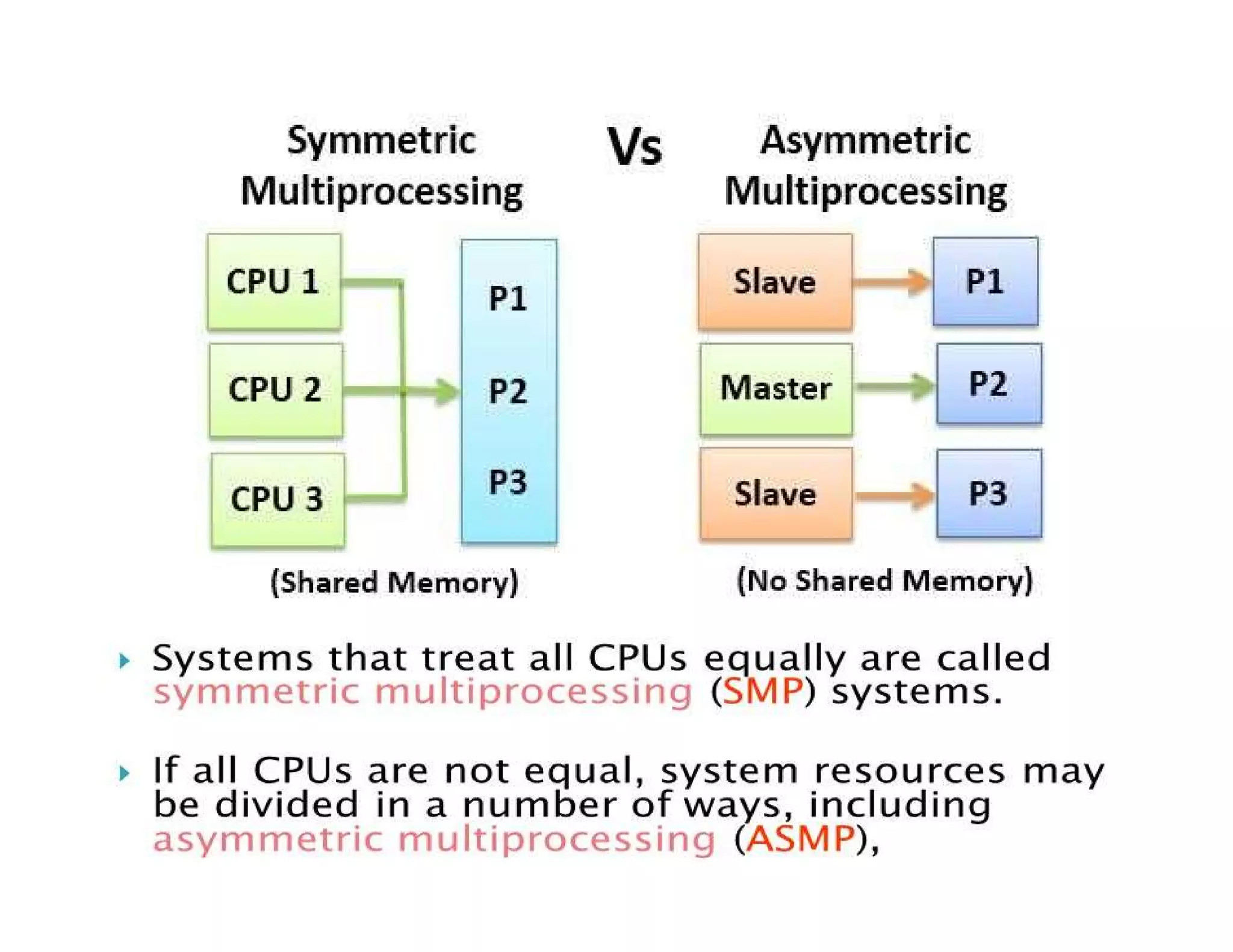
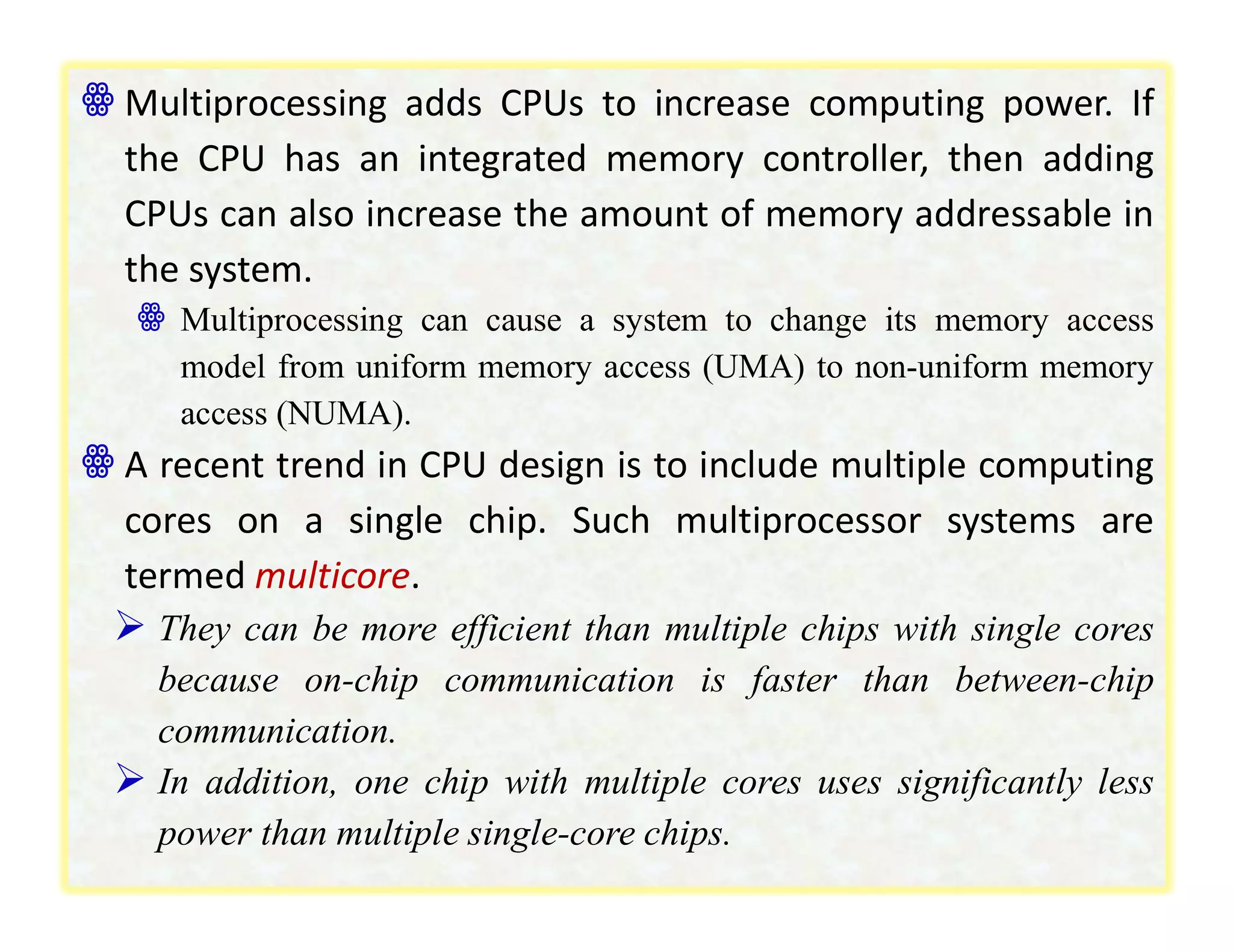
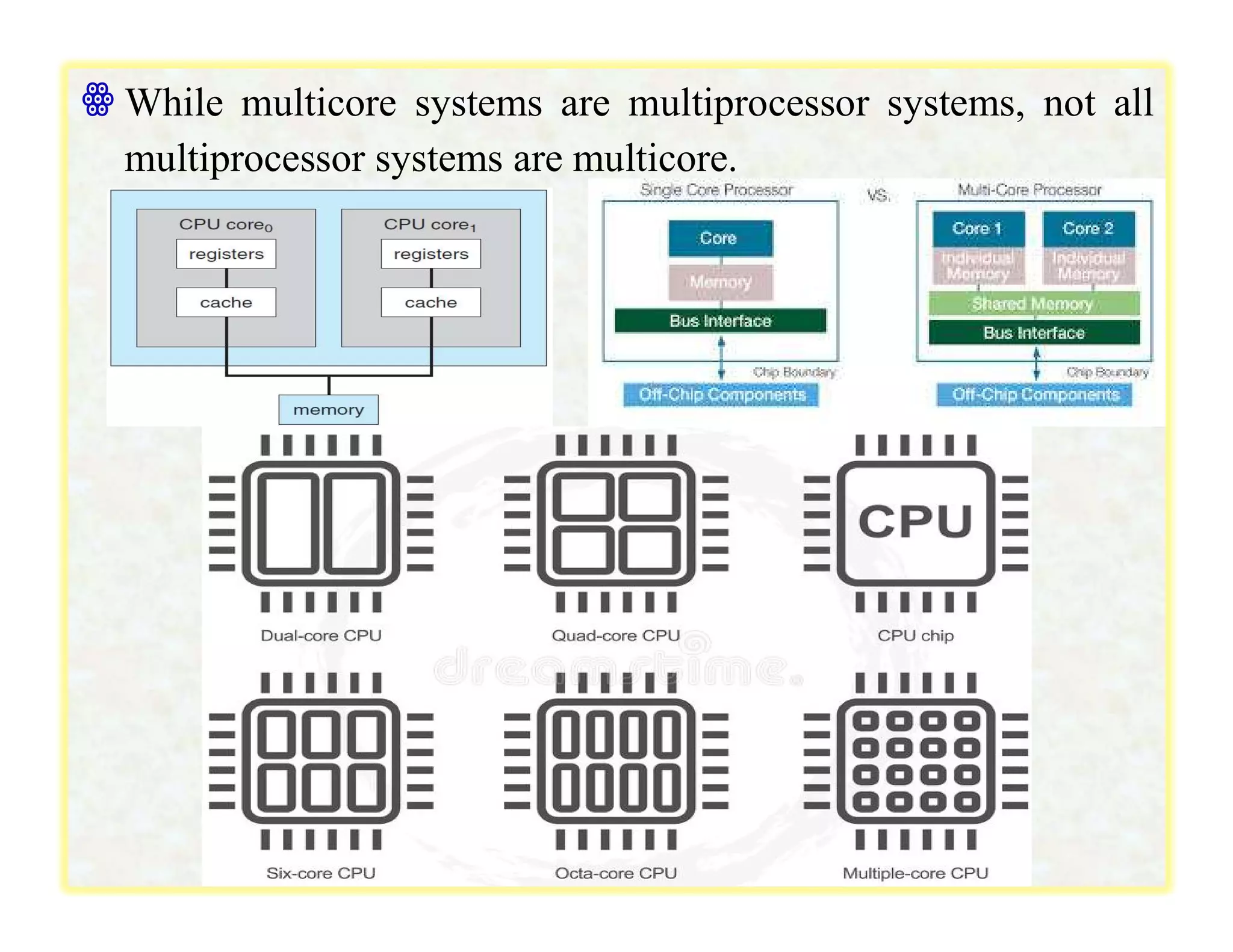
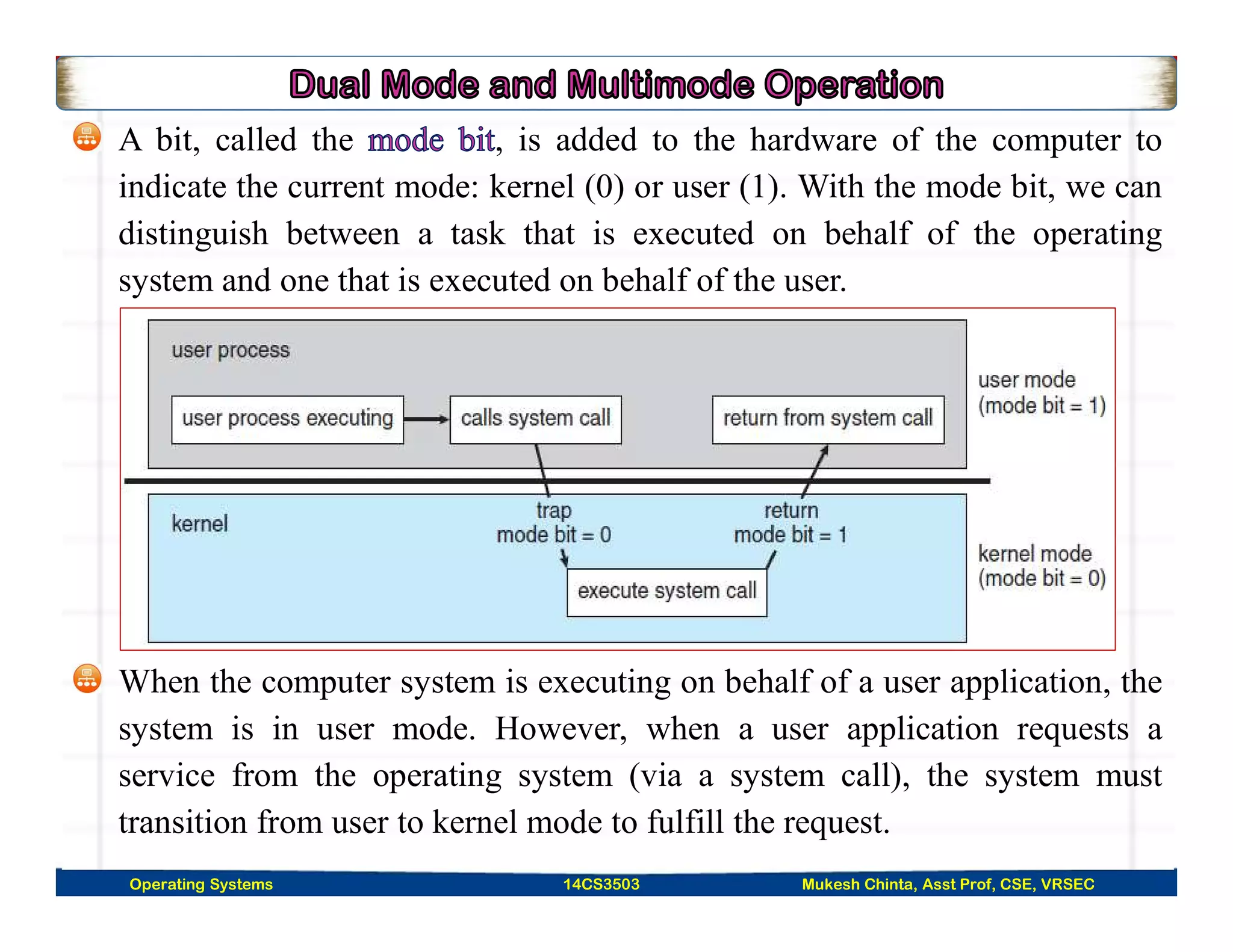
The document discusses operating systems and computer system architecture. It defines an operating system as a program that manages a computer's hardware resources and provides common services for application software. It describes the components of a computer system as the CPU, memory, I/O devices, and how the operating system controls and coordinates their use. It also discusses different types of operating systems designed for single-user systems, multi-user systems, servers, handheld devices, and embedded systems.