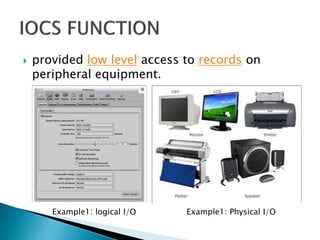
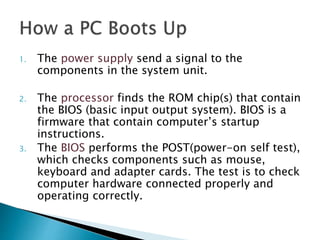
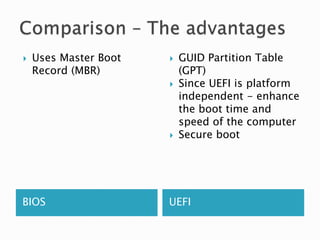
The document outlines key aspects of input/output control systems, including the differences between logical/physical I/O and directory/disk space management. It explains the boot process for computers, detailing cold and warm boots, the role of BIOS, and contrasts it with UEFI, highlighting their respective functions and advantages. Additionally, it describes how BIOS initializes components and loads the operating system, while UEFI uses a more modern approach for boot management.