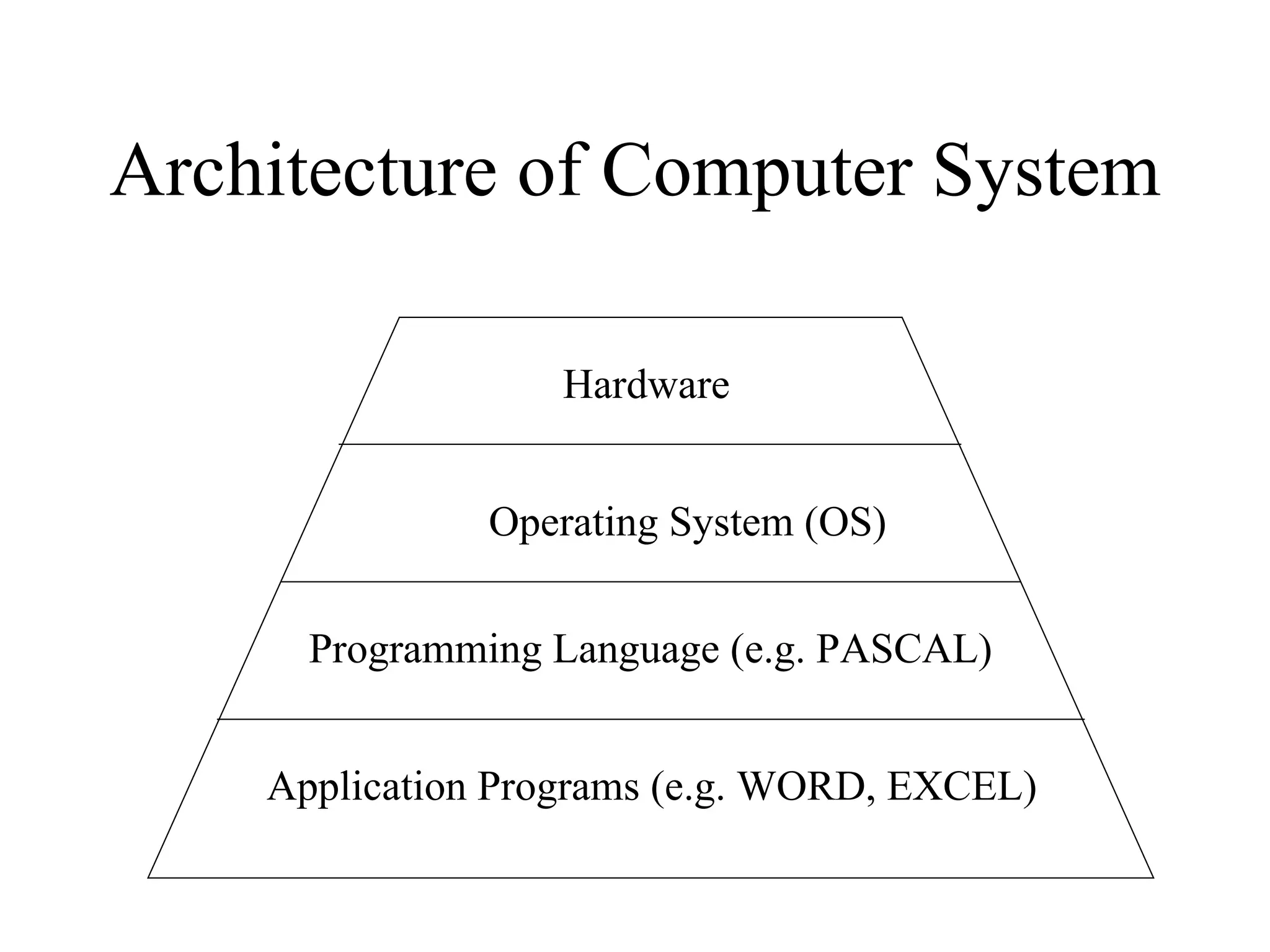
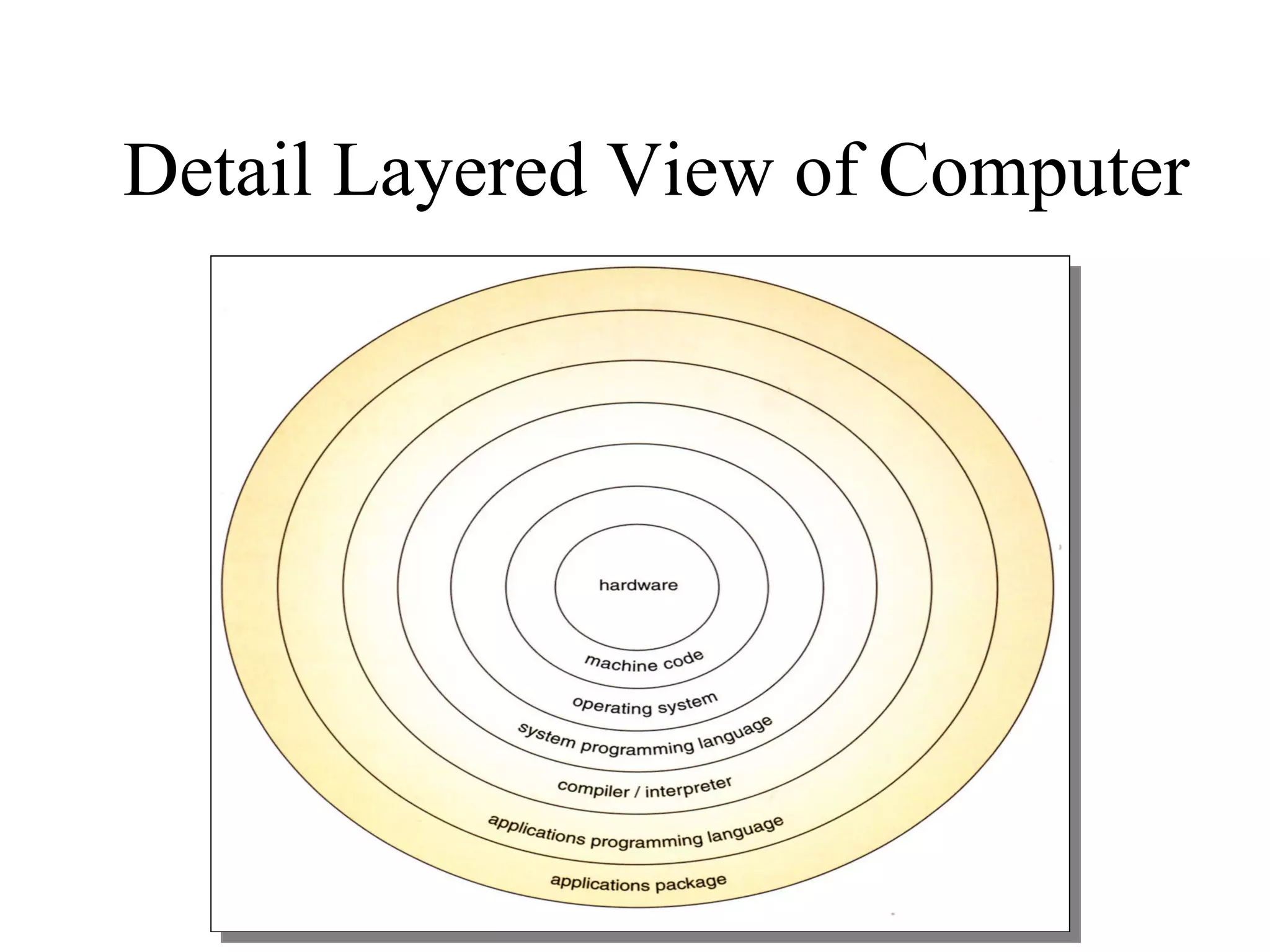
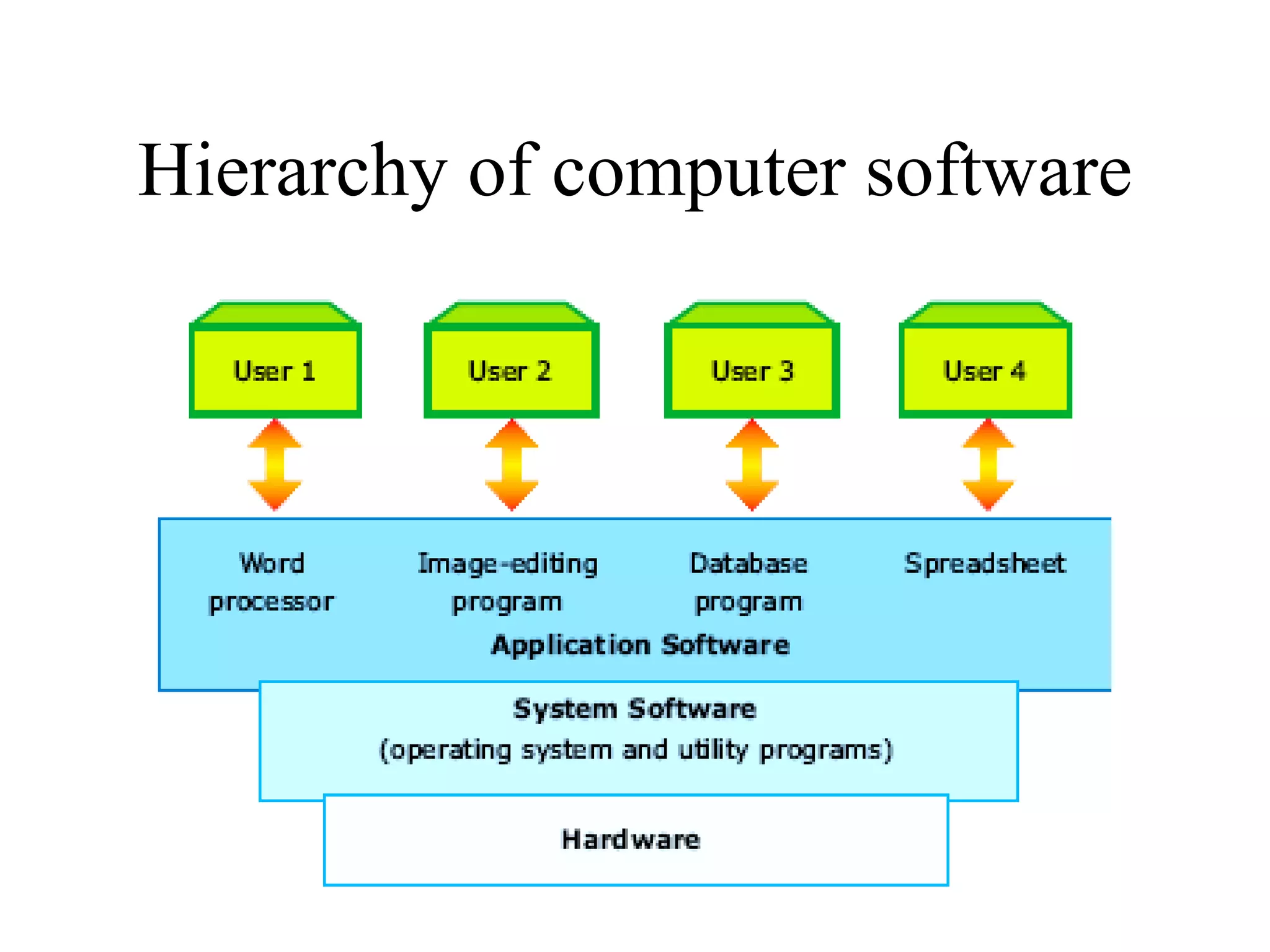
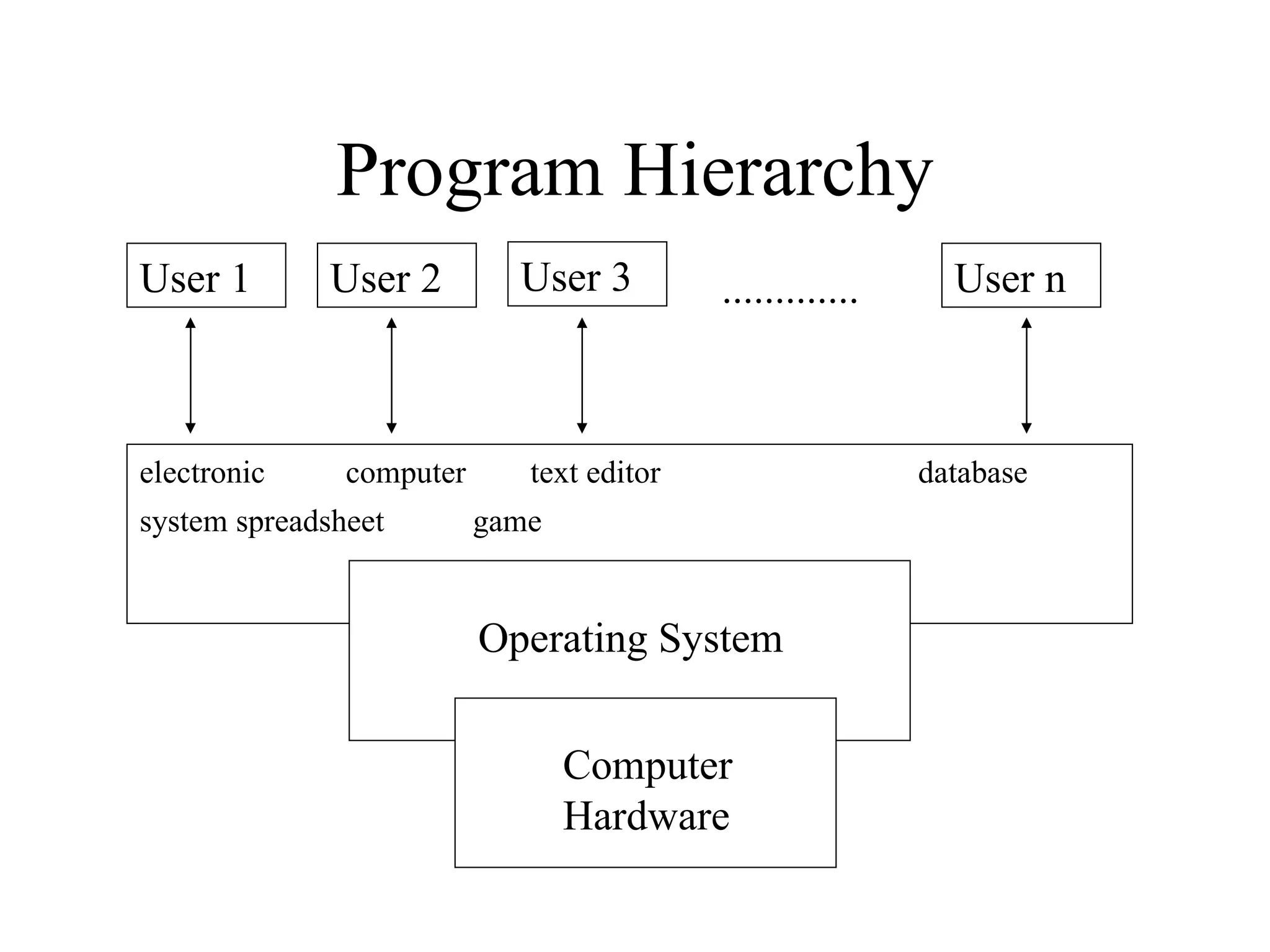
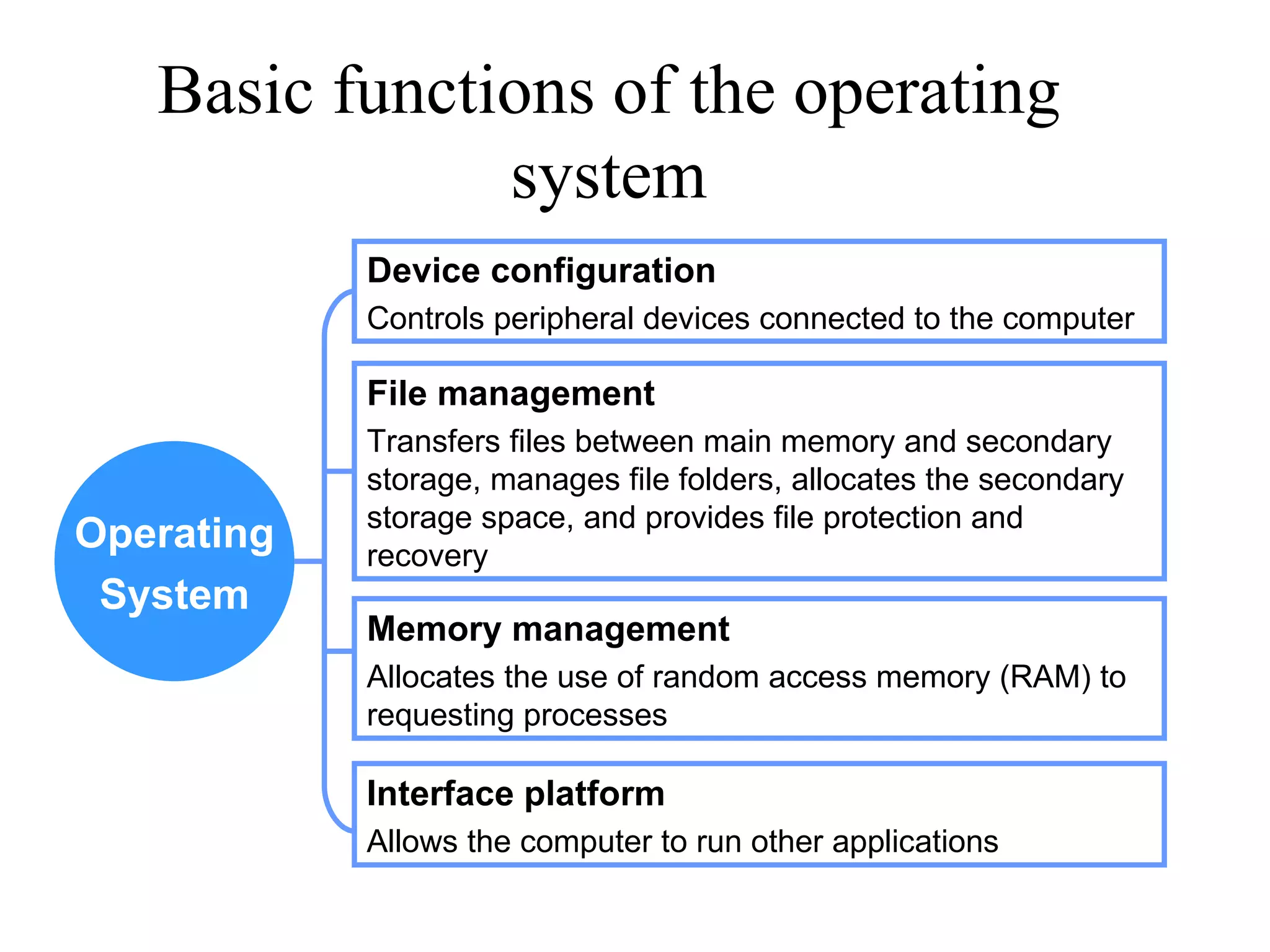
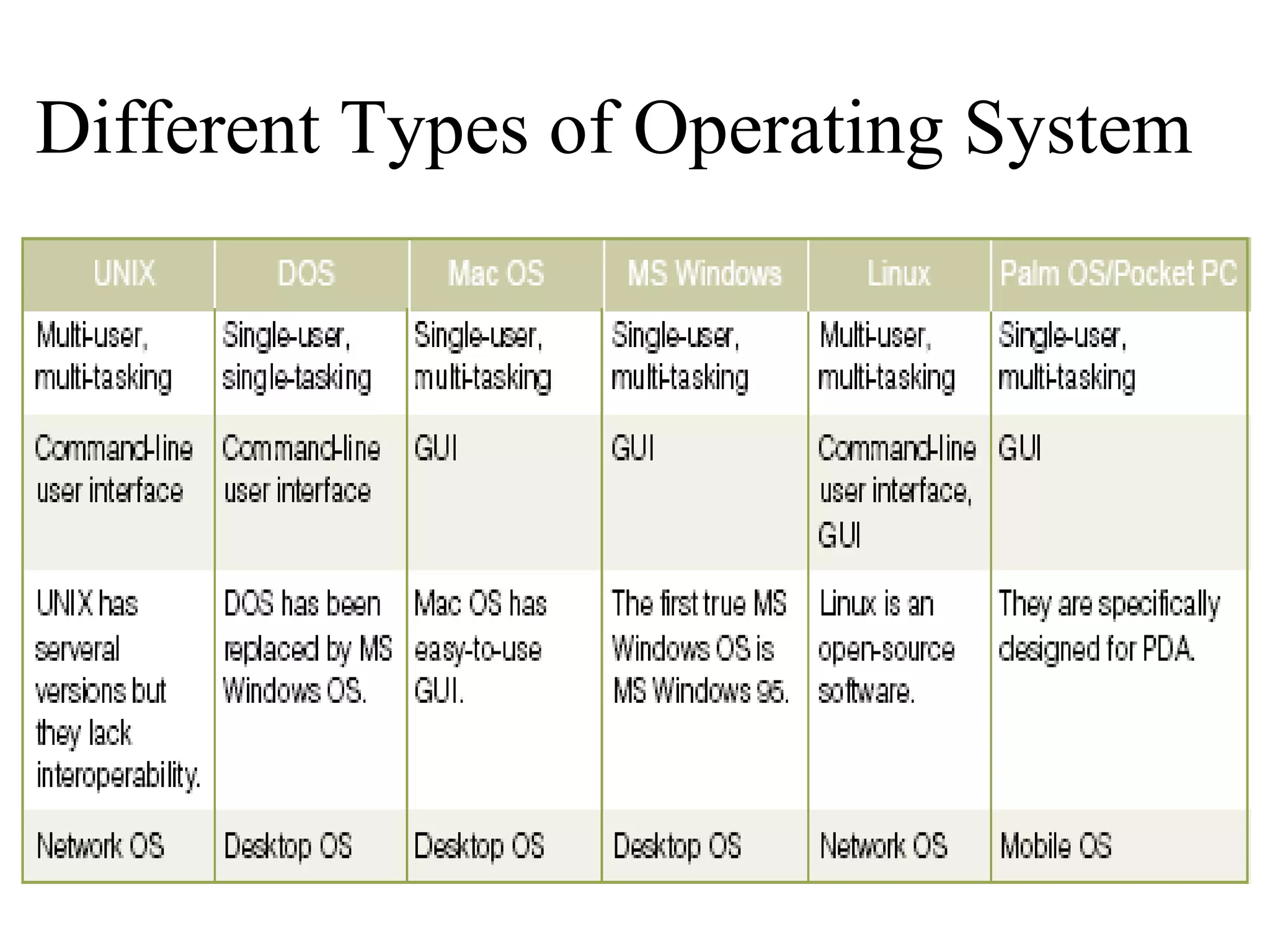
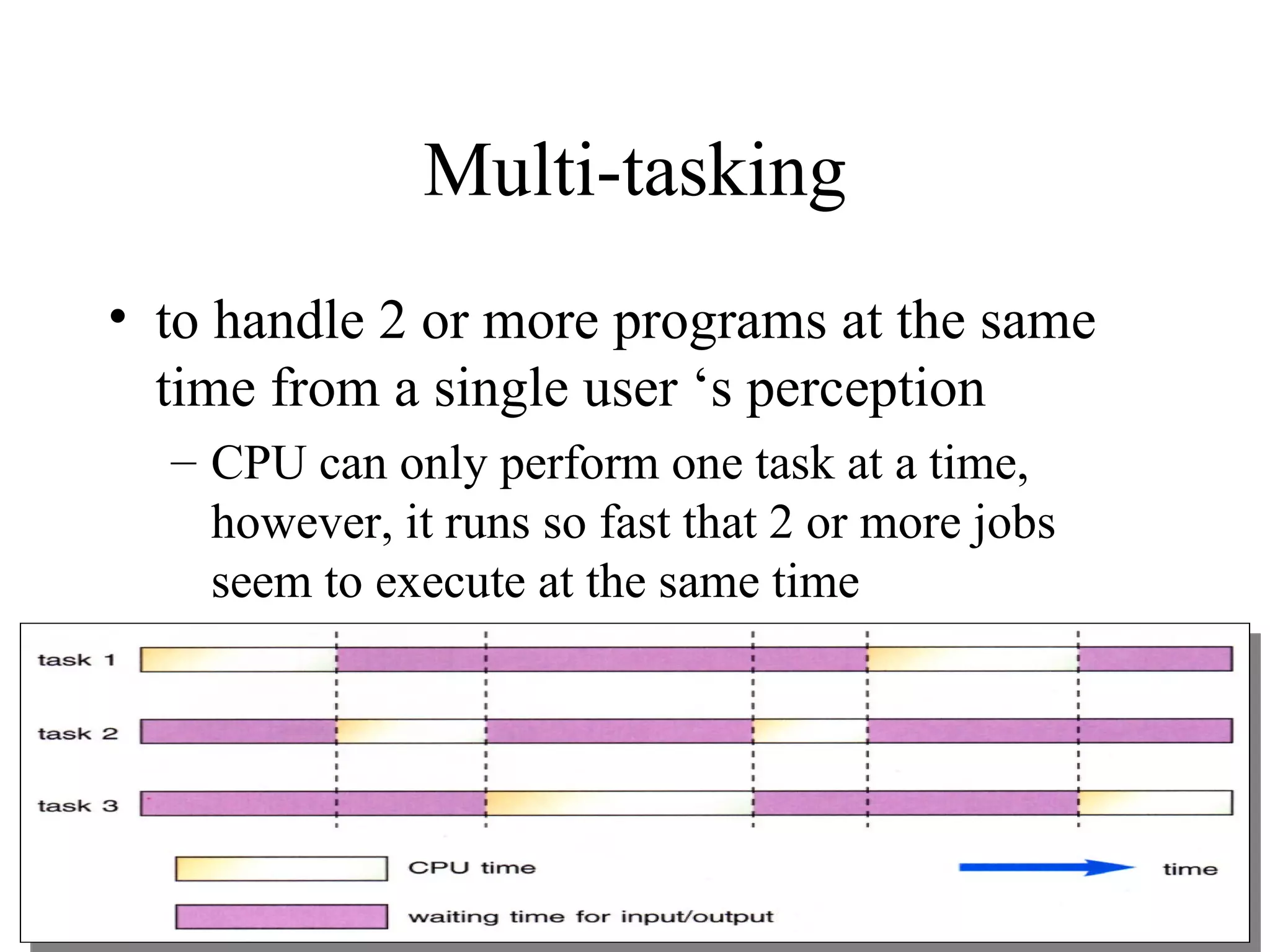
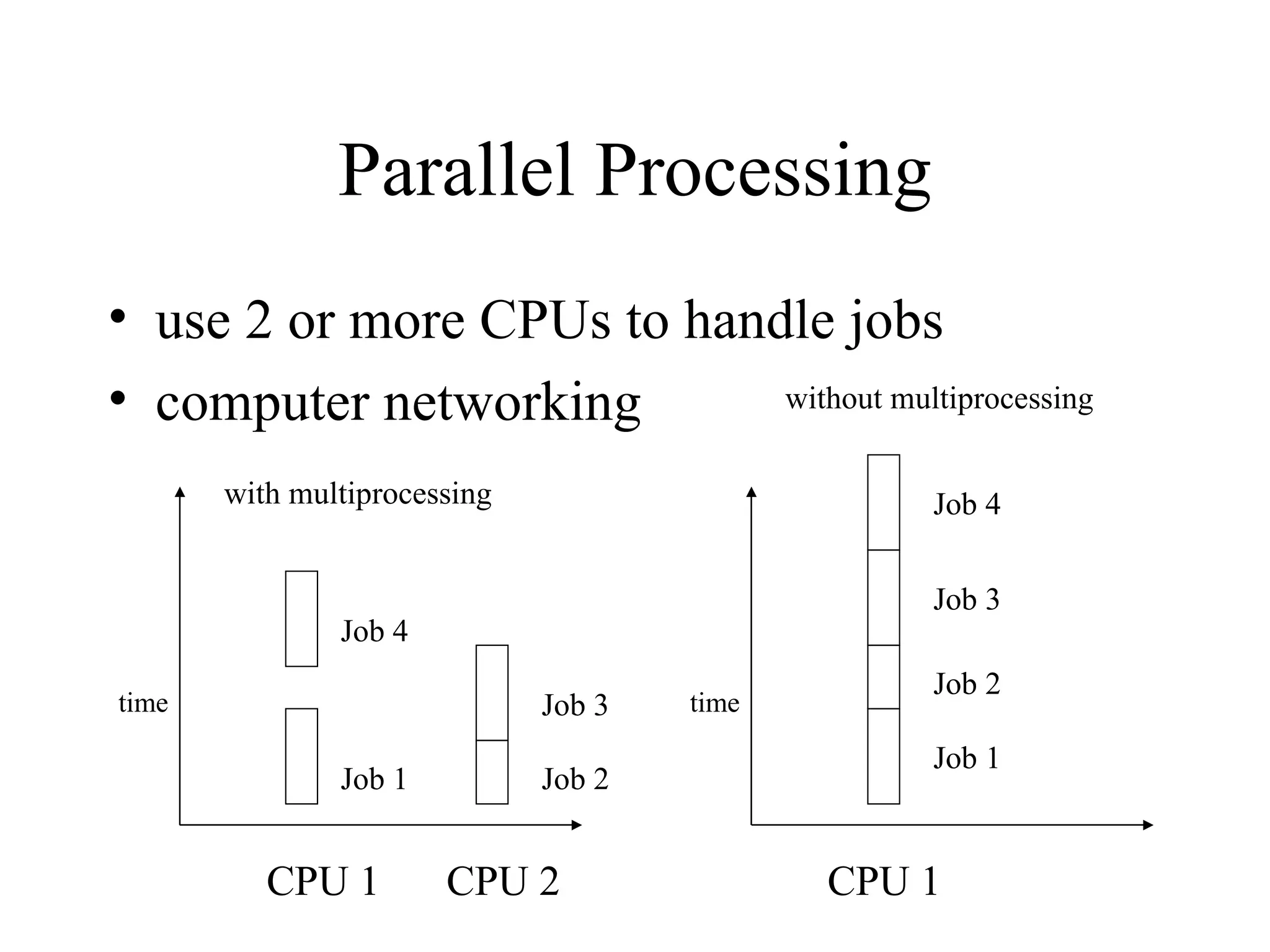
The document discusses the architecture and functions of operating systems. It describes operating systems as system software that acts as an interface between hardware and application software. The key functions of operating systems include managing memory, files, devices, and providing common services for application programs. Examples of common operating systems like Windows, UNIX, and VAX/VMS are given.