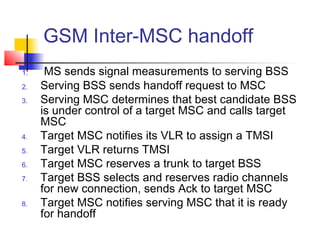
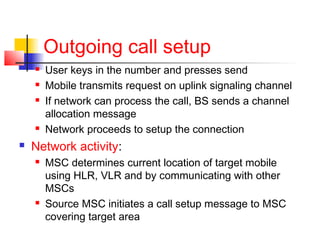
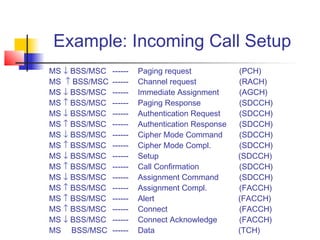
1. The target MSC sends a paging request to the target mobile station through base stations. 2. If the mobile station responds, it is authenticated and ciphering is enabled for security. 3. Radio resources are assigned and the connection is established between the mobile station and MSC to complete the call setup through the base station.