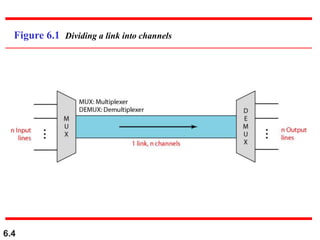
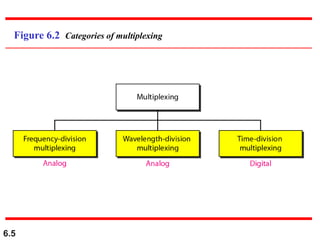
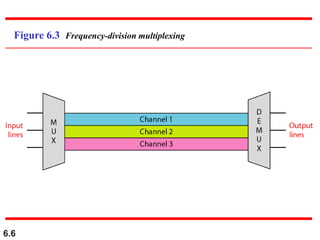
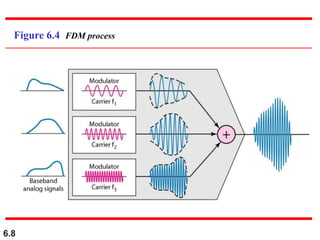
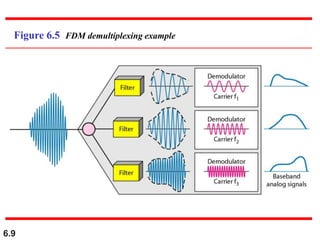
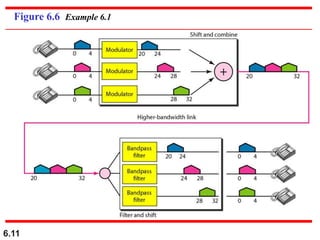
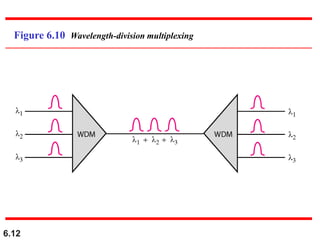
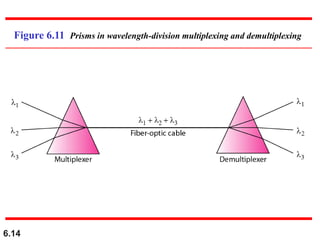
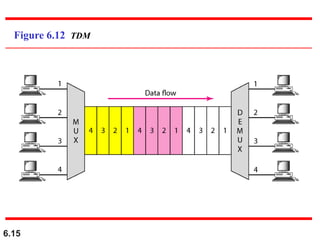
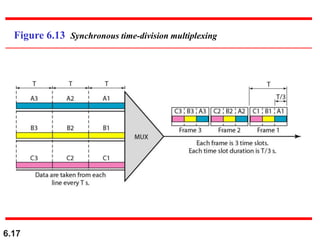
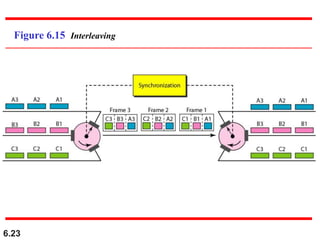
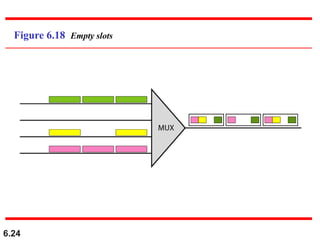
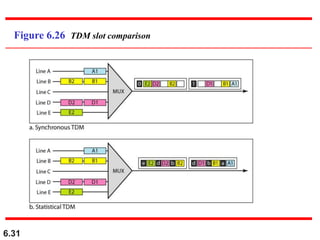
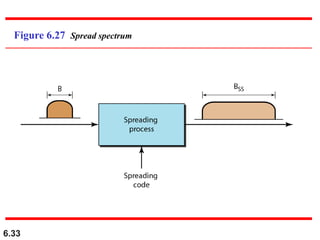
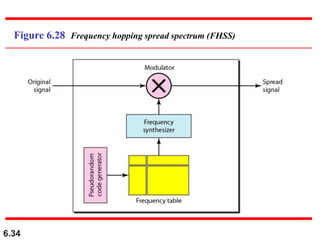
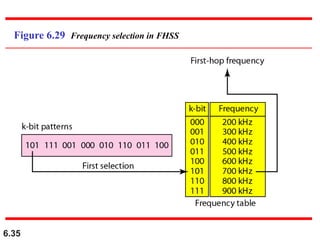
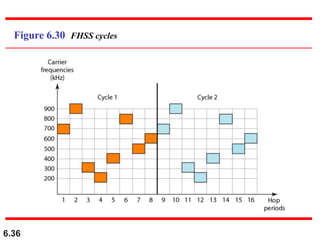
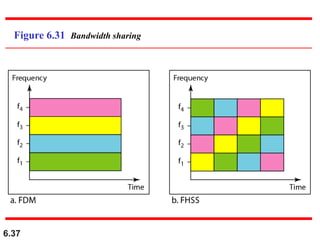
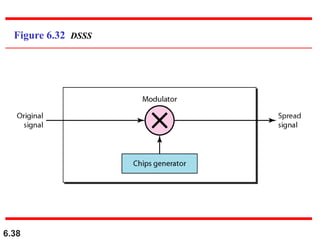
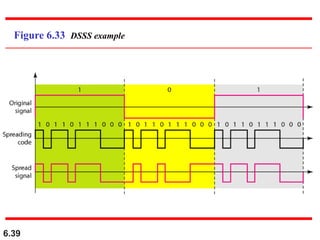
This document discusses bandwidth utilization techniques including multiplexing and spreading. It begins by defining multiplexing as techniques that allow simultaneous transmission of multiple signals across a single data link. Specific multiplexing techniques discussed include frequency-division multiplexing, wavelength-division multiplexing, synchronous time-division multiplexing, and statistical time-division multiplexing. Spread spectrum techniques like frequency hopping spread spectrum and direct sequence spread spectrum are also covered as ways to combine signals from different sources to prevent eavesdropping and jamming. Examples are provided to illustrate how these different bandwidth utilization techniques work.