This document provides an overview of files and file handling in C programming. It discusses key concepts like defining and opening files, different modes for opening files, input/output functions like getc(), putc(), fscanf(), fprintf(), getw(), putw(), closing files, error handling, random access to files, and using command line arguments. Functions like fopen(), fclose(), feof(), ferror() are explained. Examples are given to demonstrate reading from and writing to files in text and binary formats.







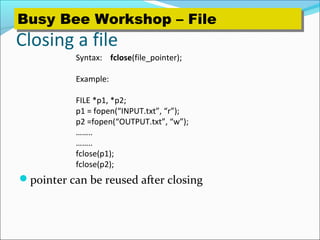








![Command line arguments
can give input to C program from command line
E.g. > prog.c 10 name1 name2
….
how to use these arguments?
main ( int argc, char *argv[] )
argc – gives a count of number of arguments (including
program name)
char *argv[] defines an array of pointers to character (or
array of strings)
argv[0] – program name
argv[1] to argv[argc -1] give the other arguments as strings
Busy Bee Workshop – FileBusy Bee Workshop – File](https://image.slidesharecdn.com/file-handling-cprogramminglanguage-151211040212/85/File-handling-c-programming-language-23-320.jpg)
![Example args.c
args.out 2 join leave 6
6
leave
join
2
args.out
#include <stdio.h>
main(int argc,char *argv[])
{
while(argc>0) /* print out all arguments in reverse order*/
{
printf("%sn",argv[argc-1]);
argc--;
}
}
Busy Bee Workshop – FileBusy Bee Workshop – File](https://image.slidesharecdn.com/file-handling-cprogramminglanguage-151211040212/85/File-handling-c-programming-language-24-320.jpg)

