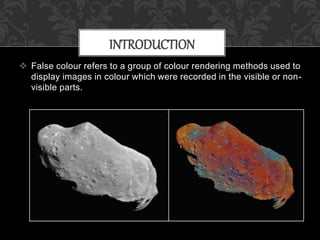
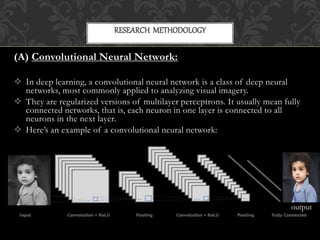
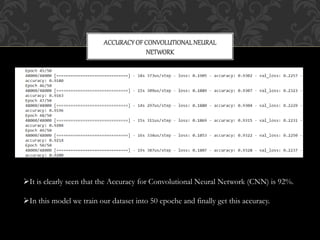
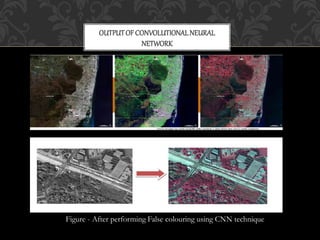
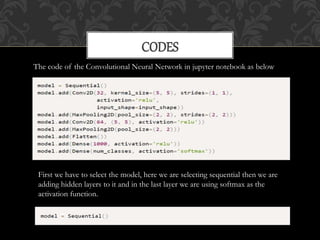
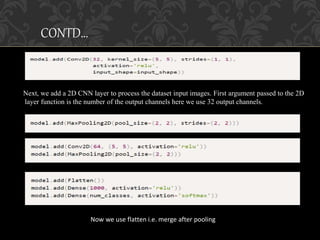
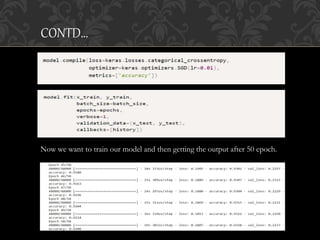
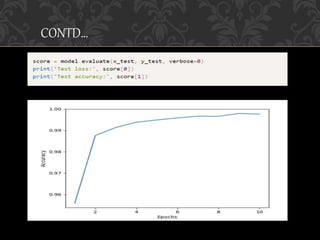
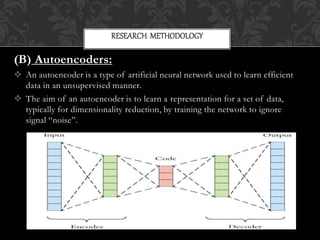
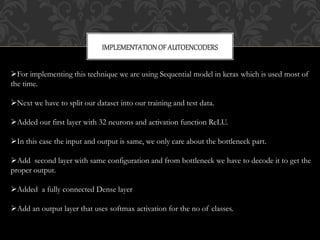
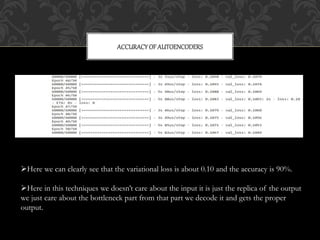
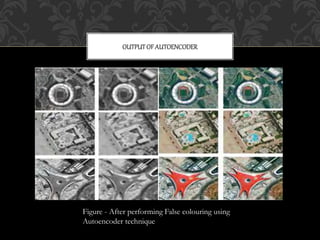
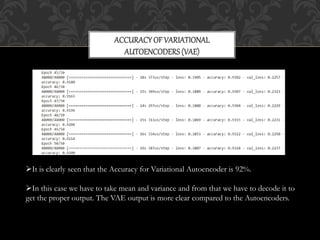
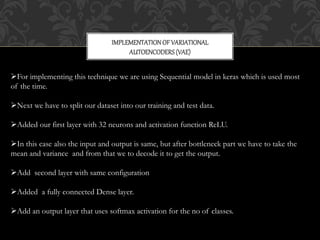
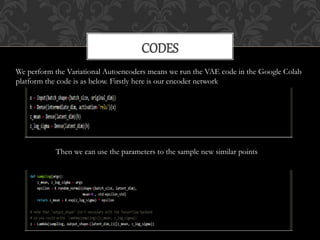
This document discusses using deep learning techniques like convolutional neural networks, autoencoders, and variational autoencoders to perform false coloring of satellite images. The techniques are implemented in Python using frameworks like Keras and TensorFlow. CNNs achieved 92% accuracy, autoencoders achieved 90% accuracy, and variational autoencoders achieved 92% accuracy in converting grayscale satellite images to color images. The codes for implementing each technique are also included.








![[1] NASA’s Earth Observatory. How to interpret a Satellite Image. K. Aardal, S. van
Hoesel, A. Koster, C. Mannino, Models and solution techniques.
[2] S. Alouf, J. Galtier, C. Touati, MFTDMA satellites, in INFOCOM 2005, 24th
Annual Joint Conference of the IEEE, in Proceedings IEEE, 2005
[3] D. Kingma, Auto-Encoding Variational Bayes of the IEEE, ICLR, 2014
[4] Xinchen Yan, Jimei Yang, Kihyuk Sohn, Honglak Lee, Attribute2Image:
Conditional Image Generation from Visual Attributes IEEE, ECCV, 2016
[5] http://earthobservatory.nasa.gov/Features/FalseColor/page6.php
[6] https://ieeexplore.ieee.org/document/861379/keywords#keywords
REFERENCES](https://image.slidesharecdn.com/falsecolouring-200701131339/85/False-colouring-32-320.jpg)
