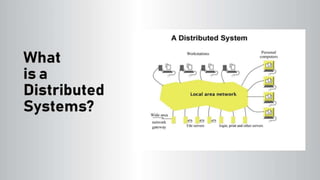
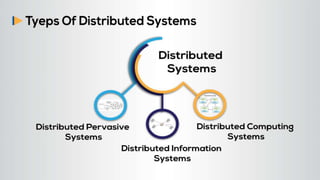
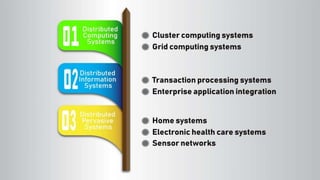
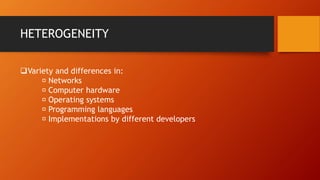
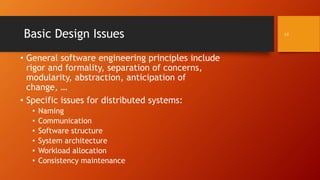
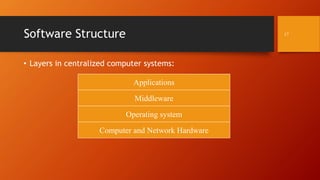
This document discusses distributed systems analysis and design. It provides an overview of common characteristics of distributed systems including heterogeneity, openness, and security. It also discusses basic design issues such as naming, communication, software structure, and system architectures. The document includes sections written by different group members on topics such as scalability, naming, communication, software structure, and the pros and cons of distributed systems.