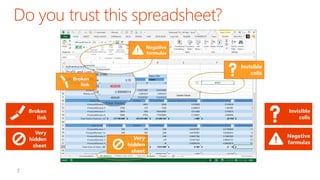
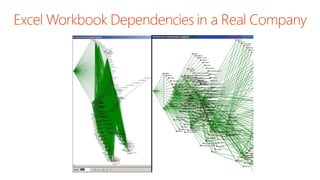
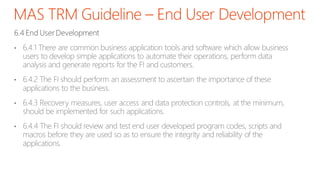
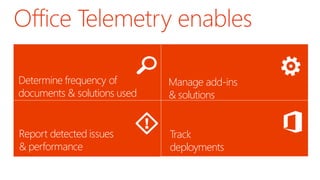
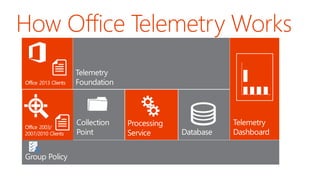
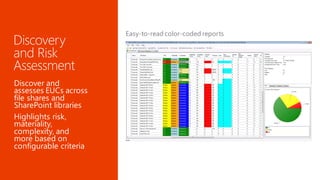
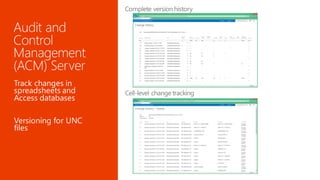
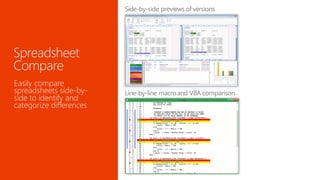
The document discusses the importance of managing end-user developed (EUD) tools and the associated risks, particularly regarding data governance and the potential for financial misstatements due to errors and fraud. It outlines Microsoft technologies as a solution for enabling EUD while minimizing risks through integrated monitoring, auditing, and security frameworks. The document also highlights best practices, tools for risk assessment, and the evolution of spreadsheet controls over the years.