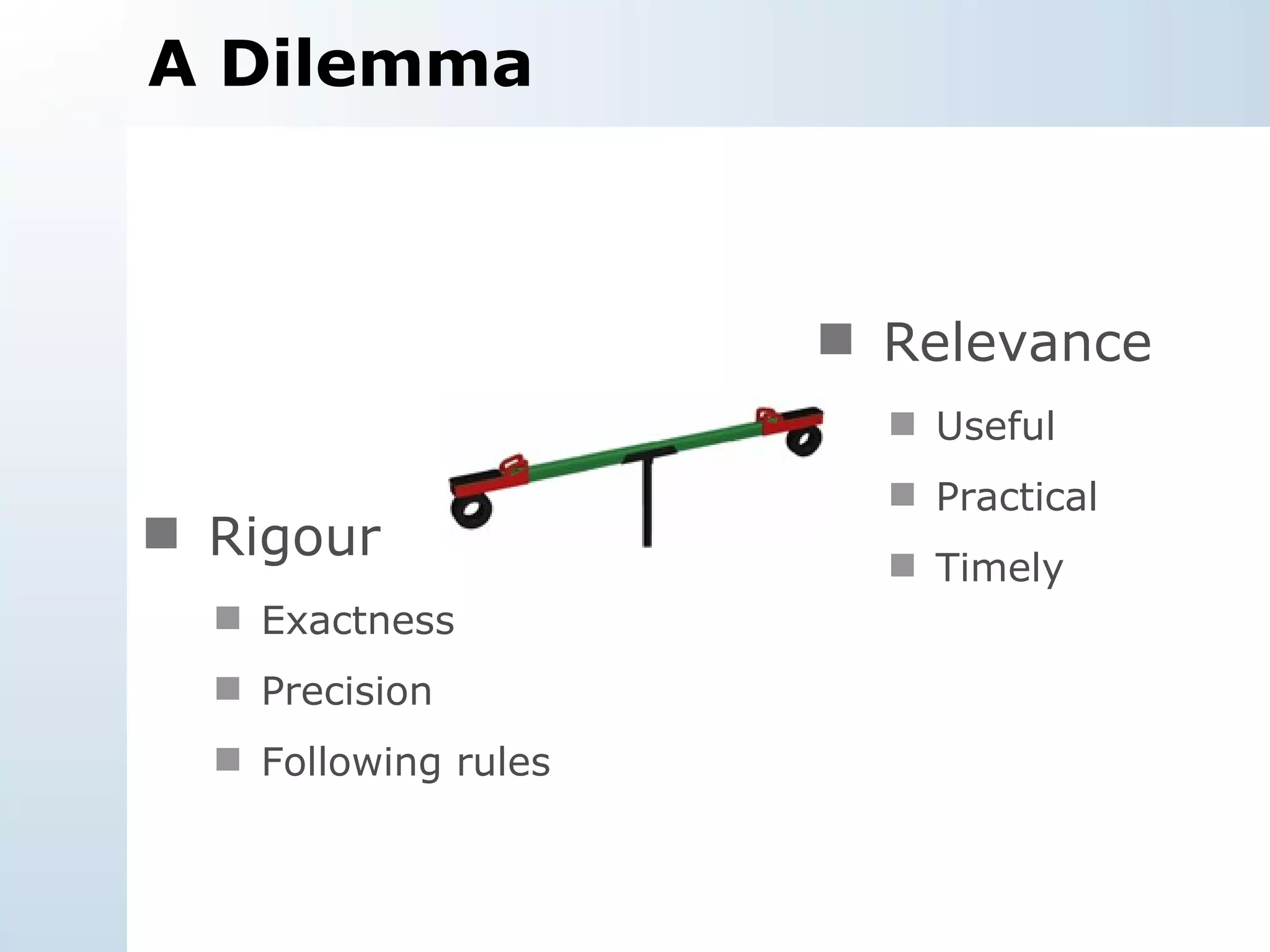
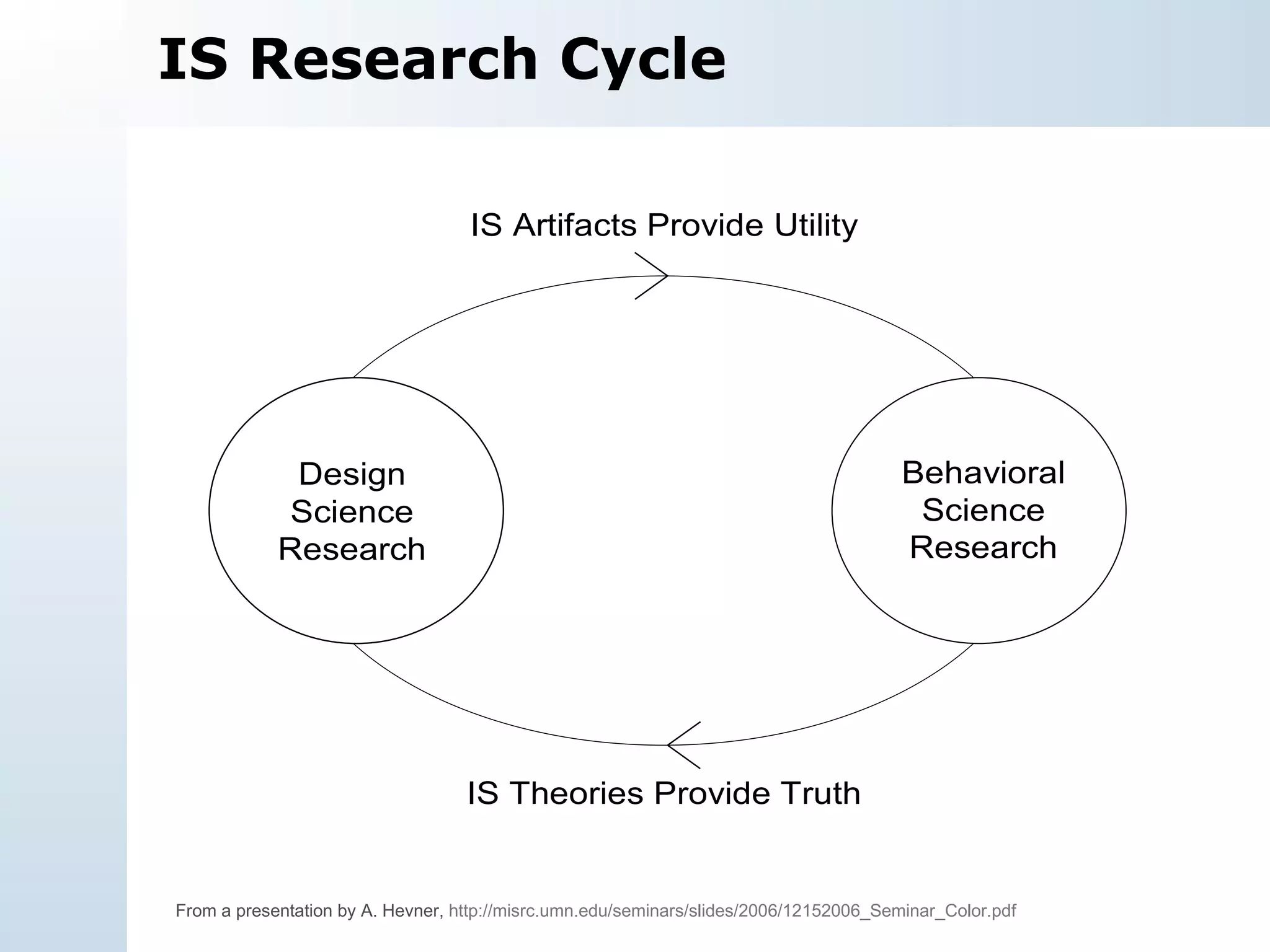
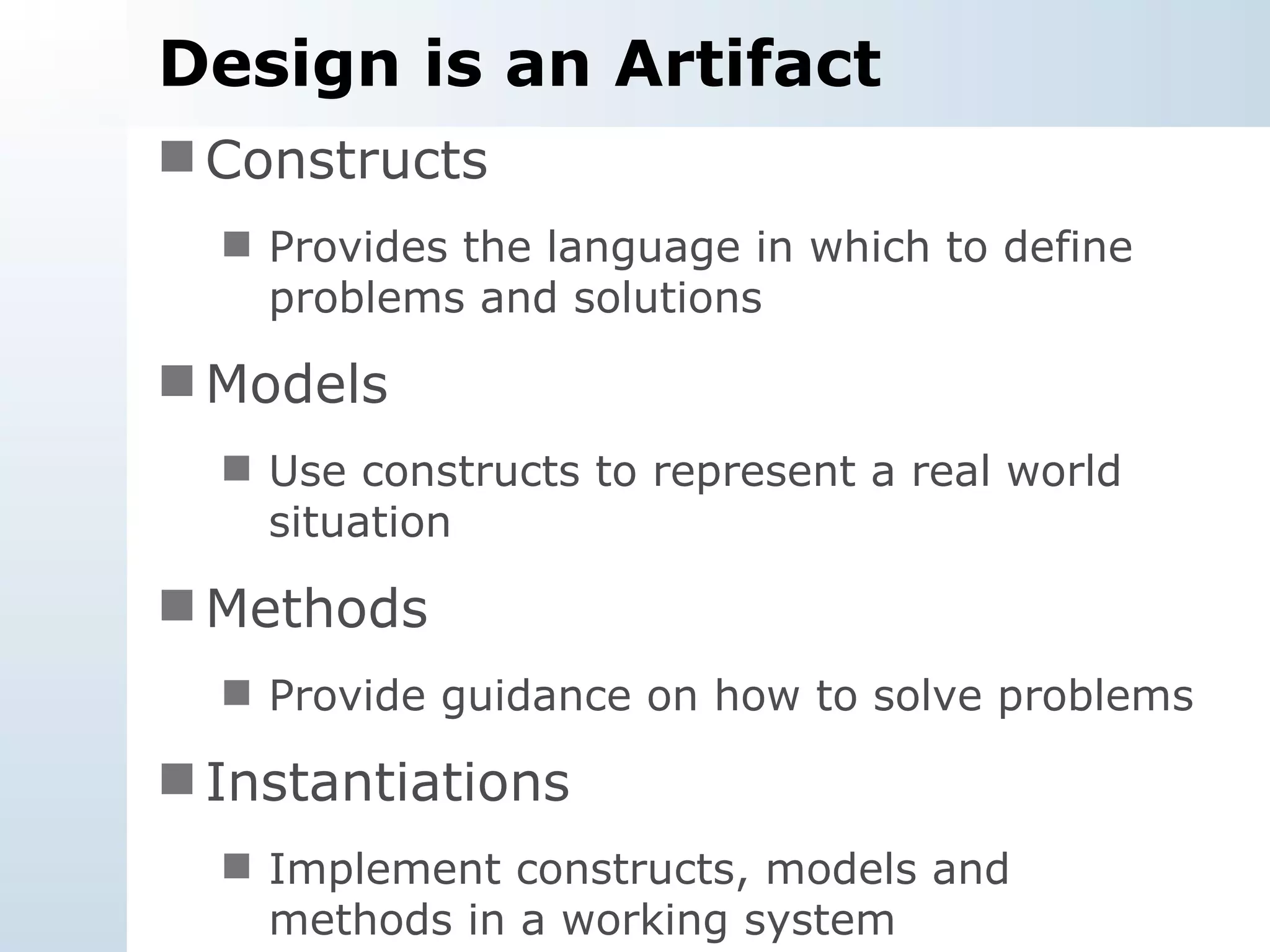
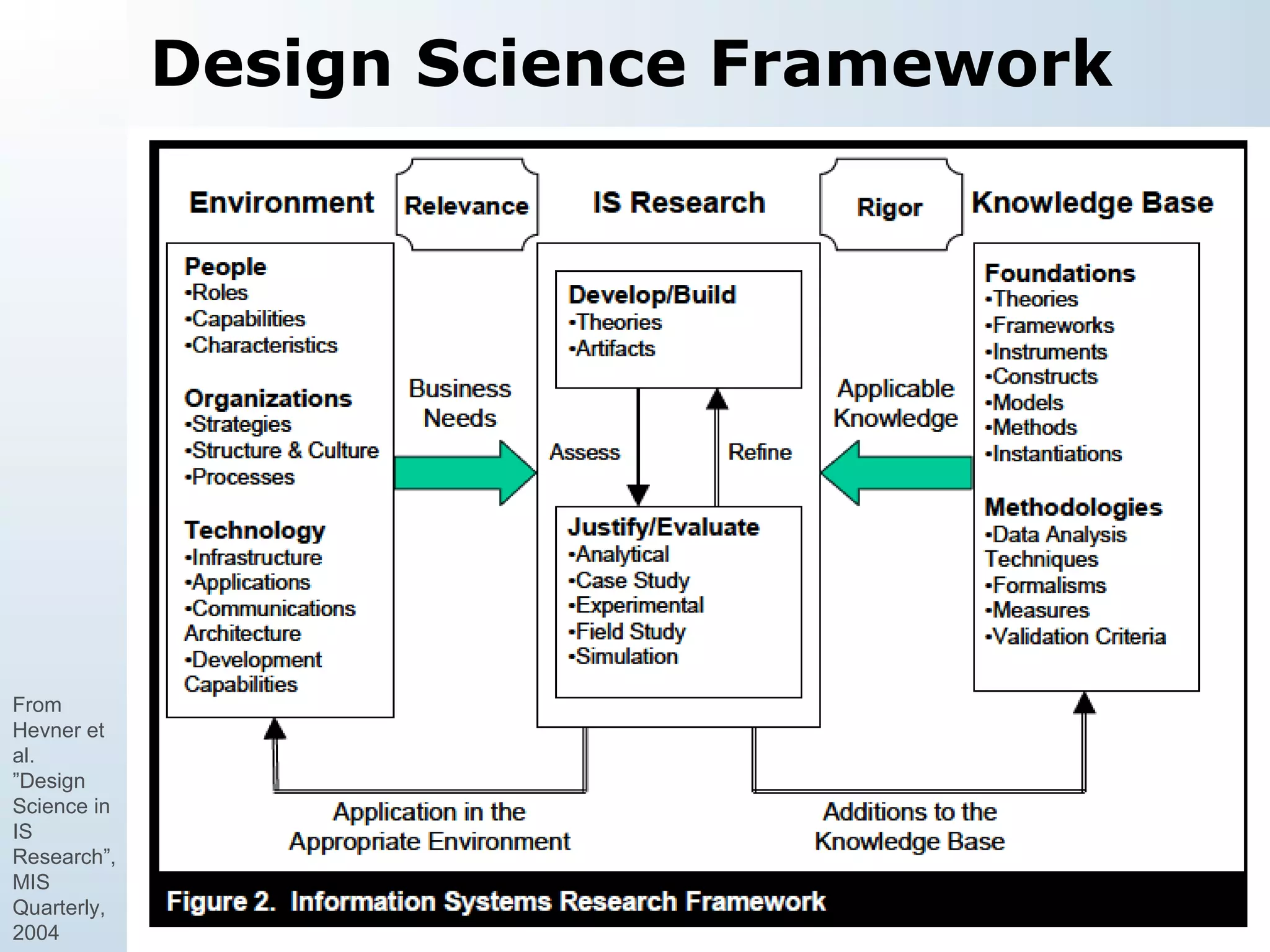
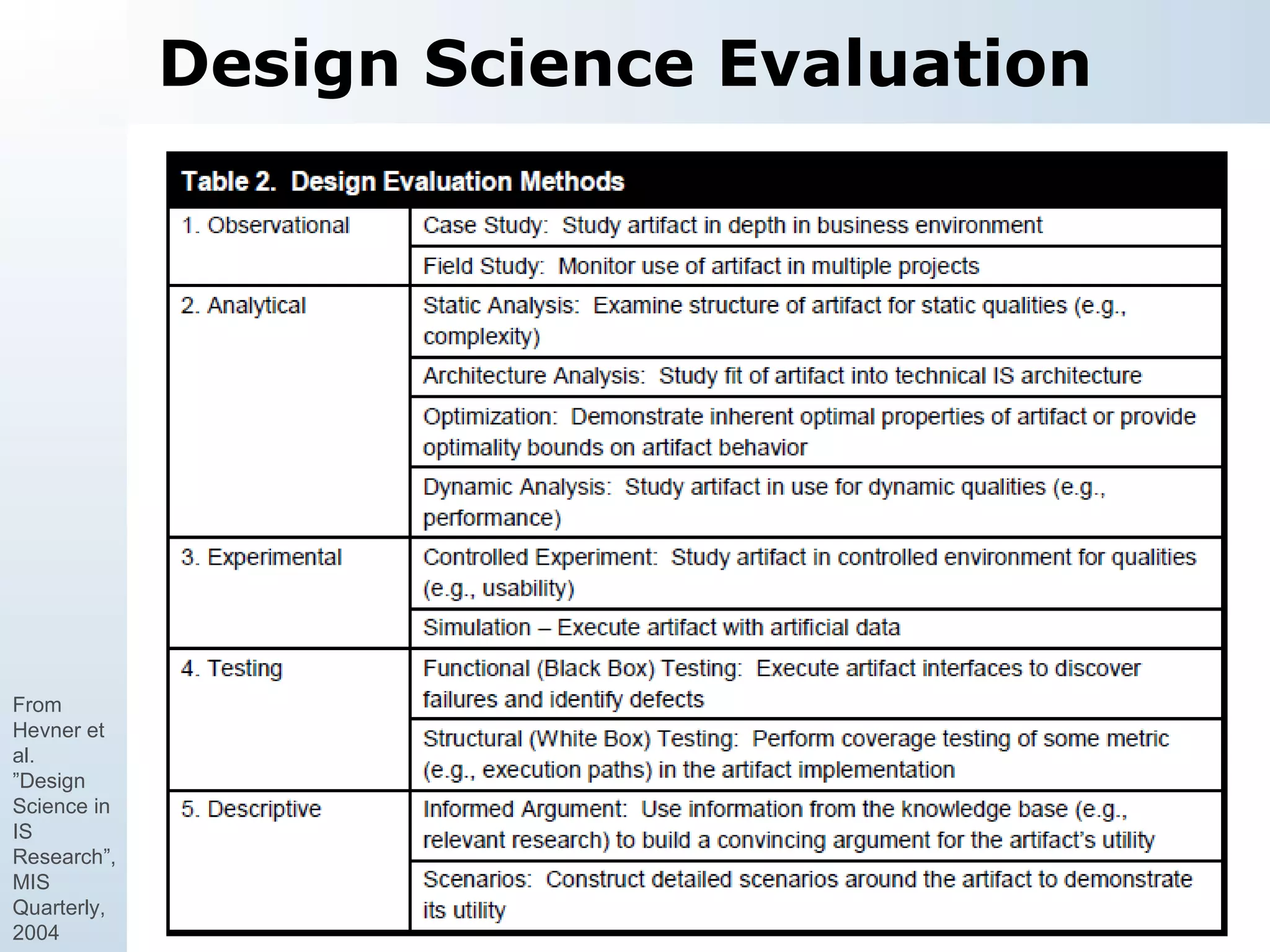
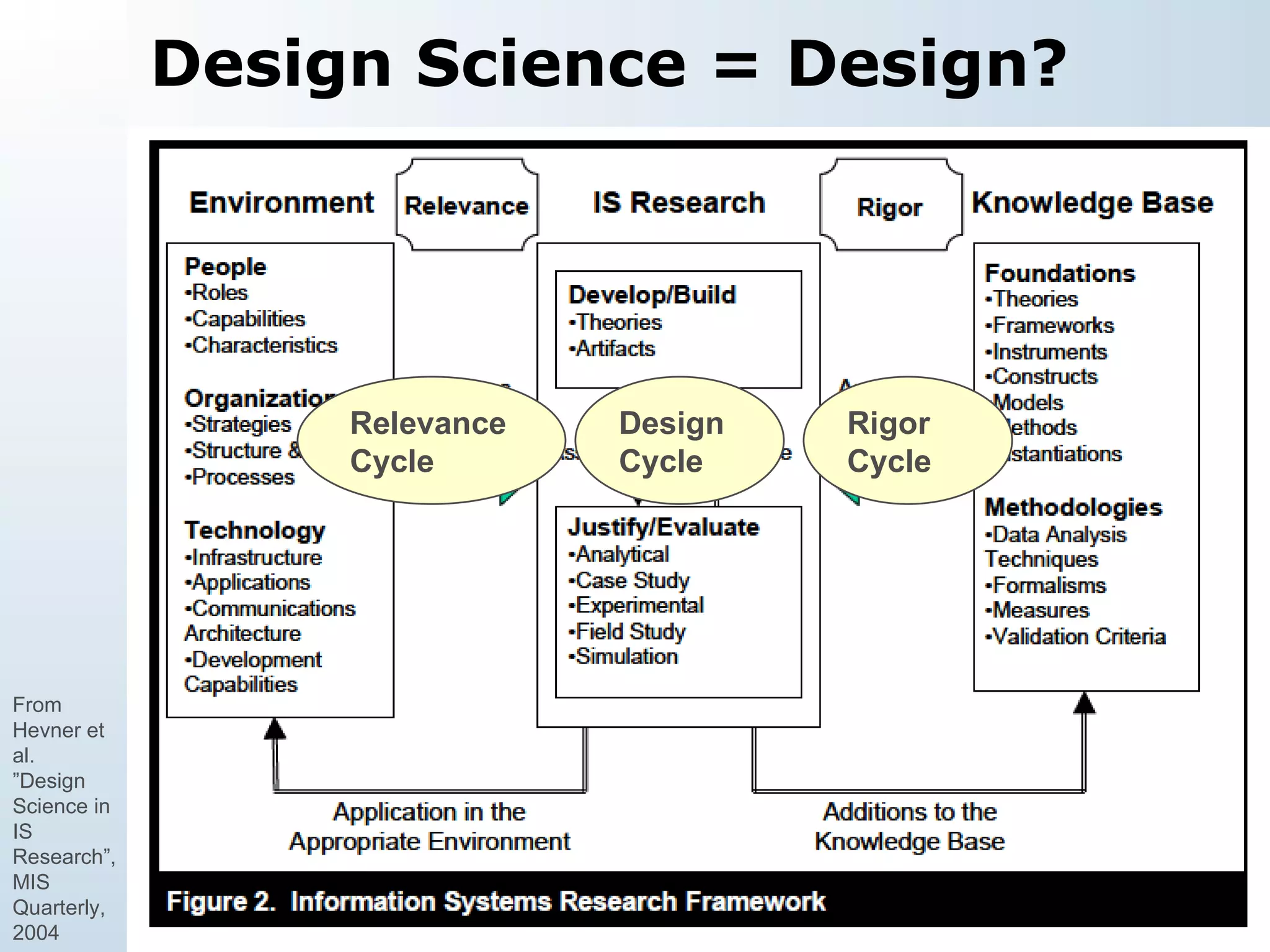
The document discusses design science as a research paradigm in information systems, contrasting it with behavioral science. It emphasizes the creation of innovative artifacts to solve relevant business problems through a structured design process while highlighting challenges such as evolving requirements and the need for effective evaluation methods. The work also stresses the importance of communication in presenting design science research to both technical and management audiences.