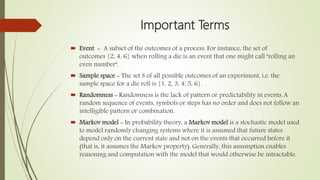
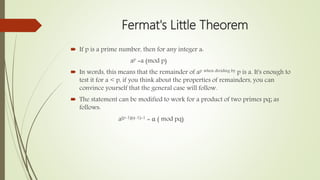
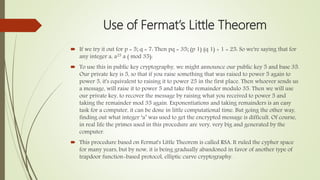
This document discusses the use of probability in cryptography. It begins with introductions to cryptography and probability. Key probability terms and concepts like events, sample spaces, and Markov models are defined. Public key cryptography using Fermat's Little Theorem is explained. Applications of probability in cryptography are explored, including checksums and the birthday problem, pseudo-random number generators, and code breaking using the Metropolis-Hastings algorithm. The document concludes that probability and cryptography are important fields that help secure communications and protect society from cyber attacks.