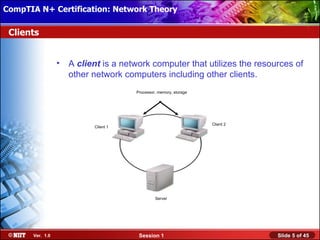
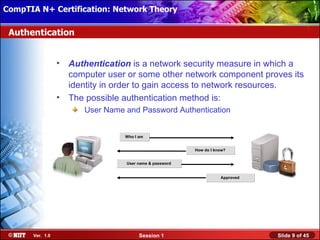
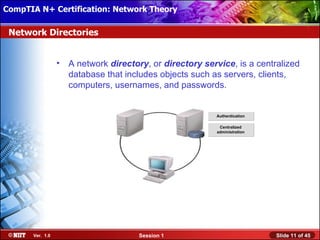
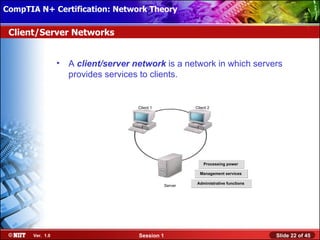
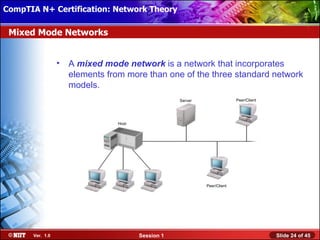
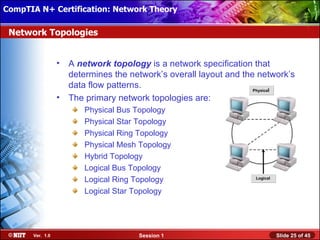
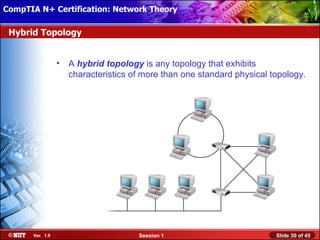
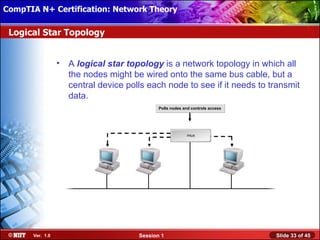
This document provides an overview of key networking concepts and terms. It defines networks, servers, clients, peers, and other common networking components. It also outlines standard networking models including centralized, client-server, and peer-to-peer networks. Additionally, it covers network topologies, categories such as LANs and WANs, and standard bodies that develop networking standards.