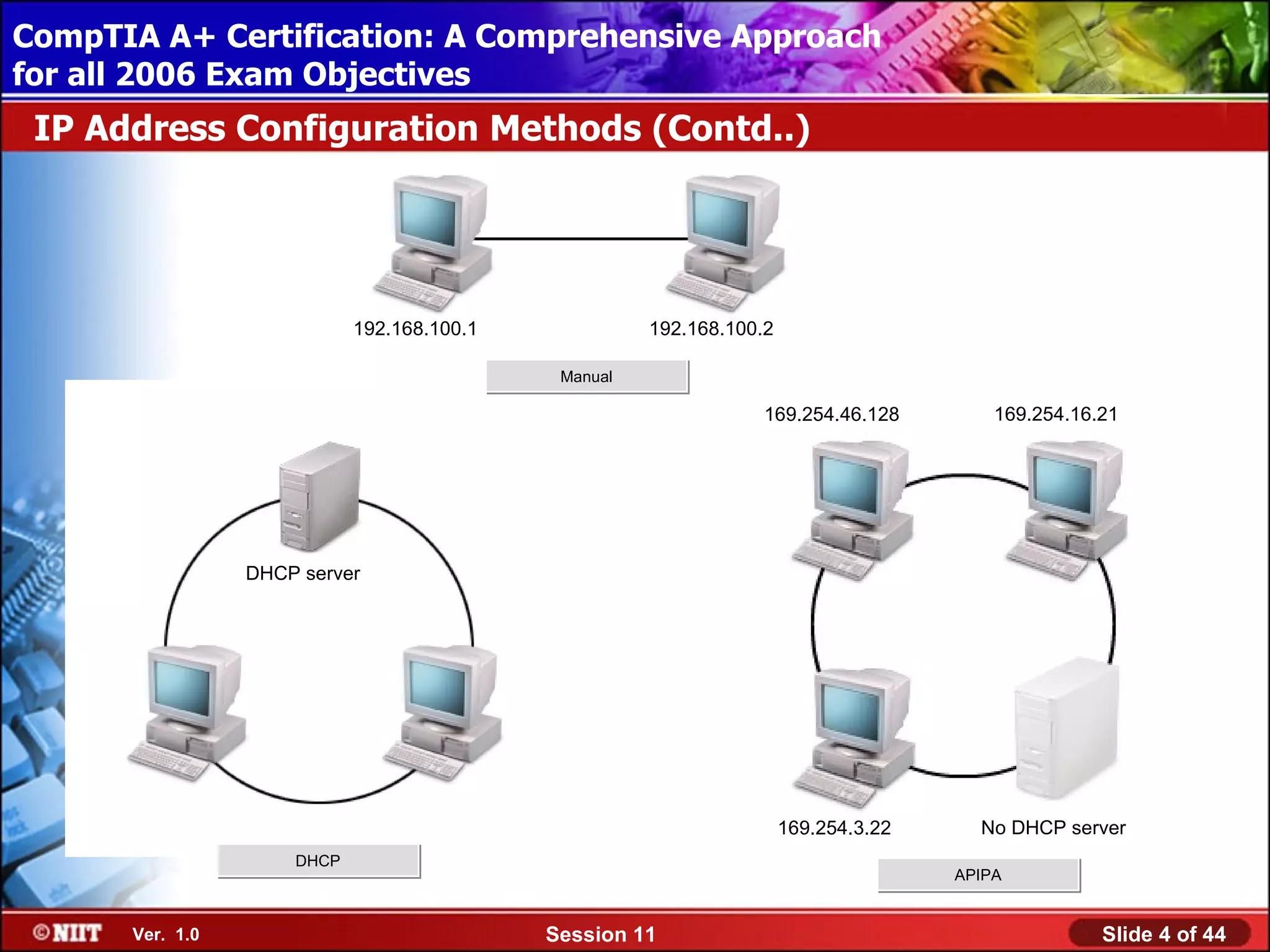
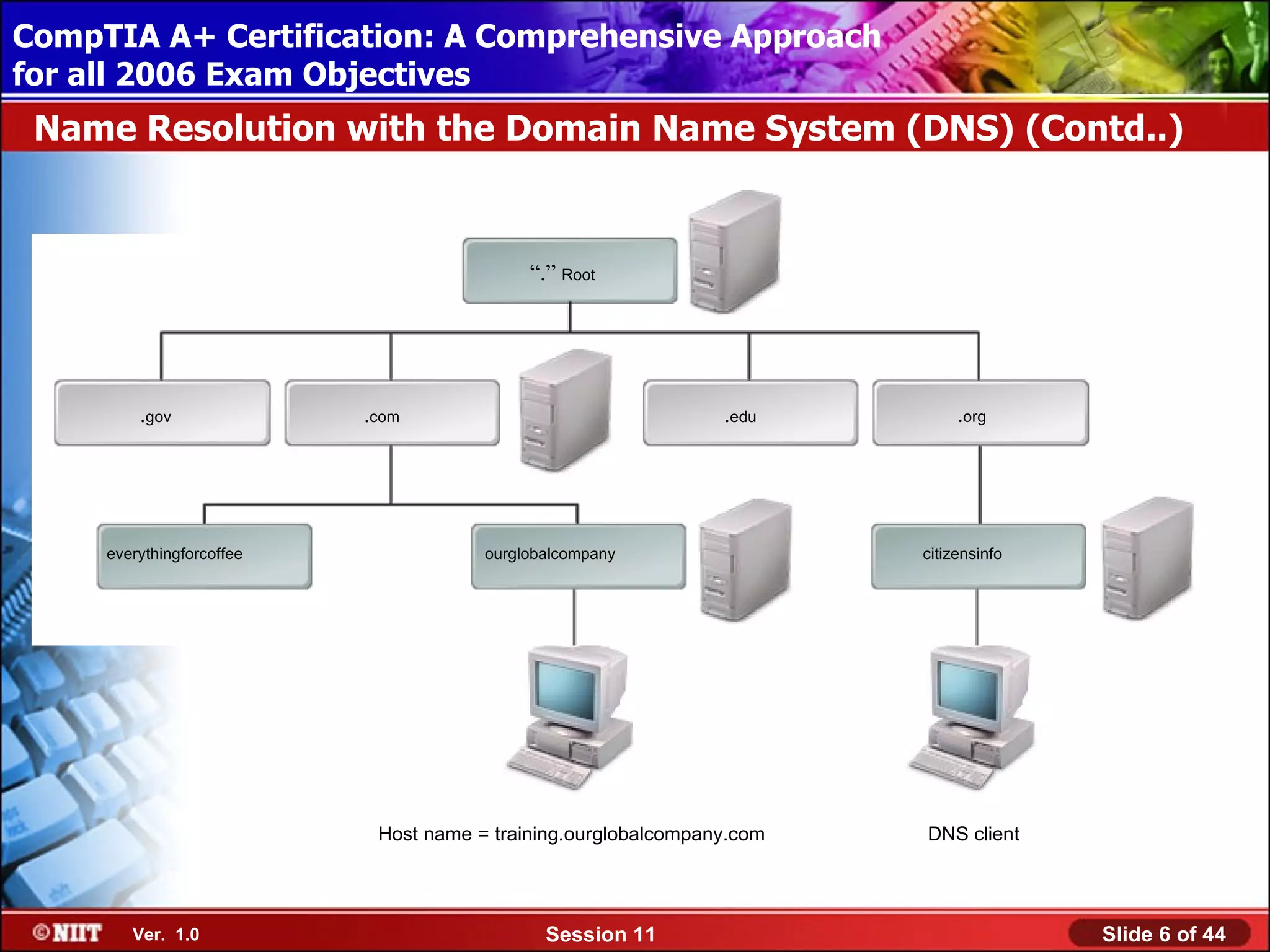
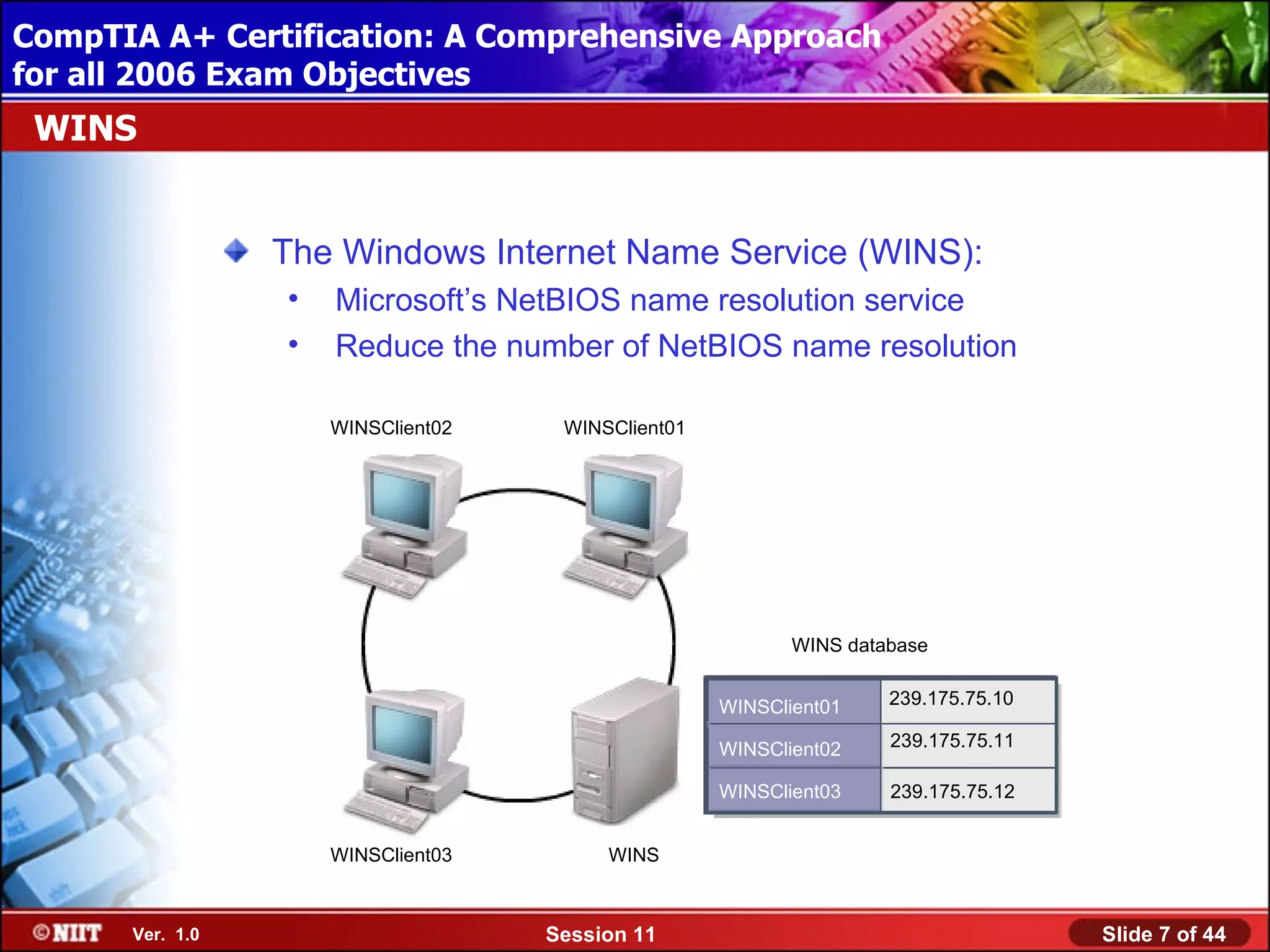
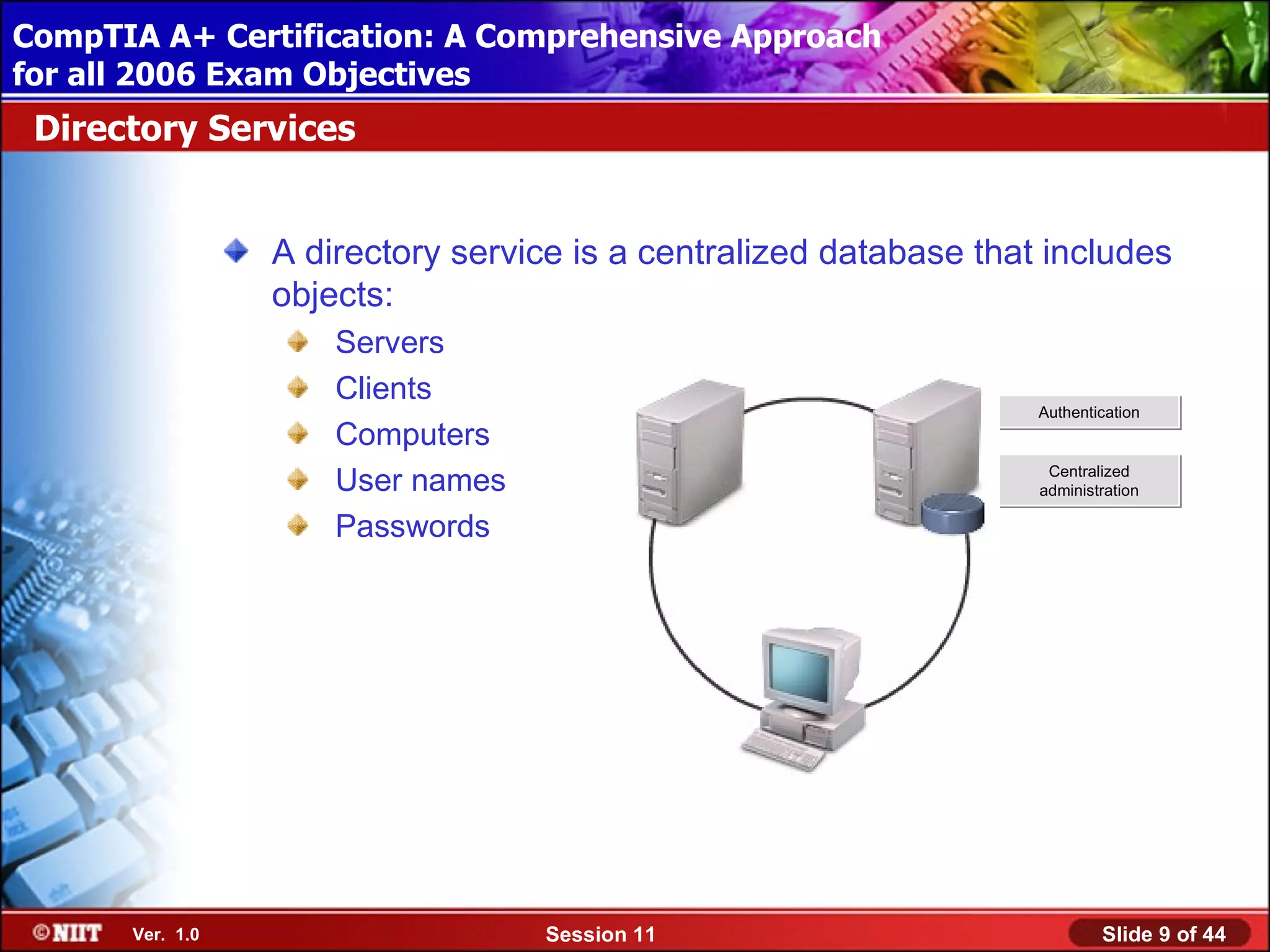
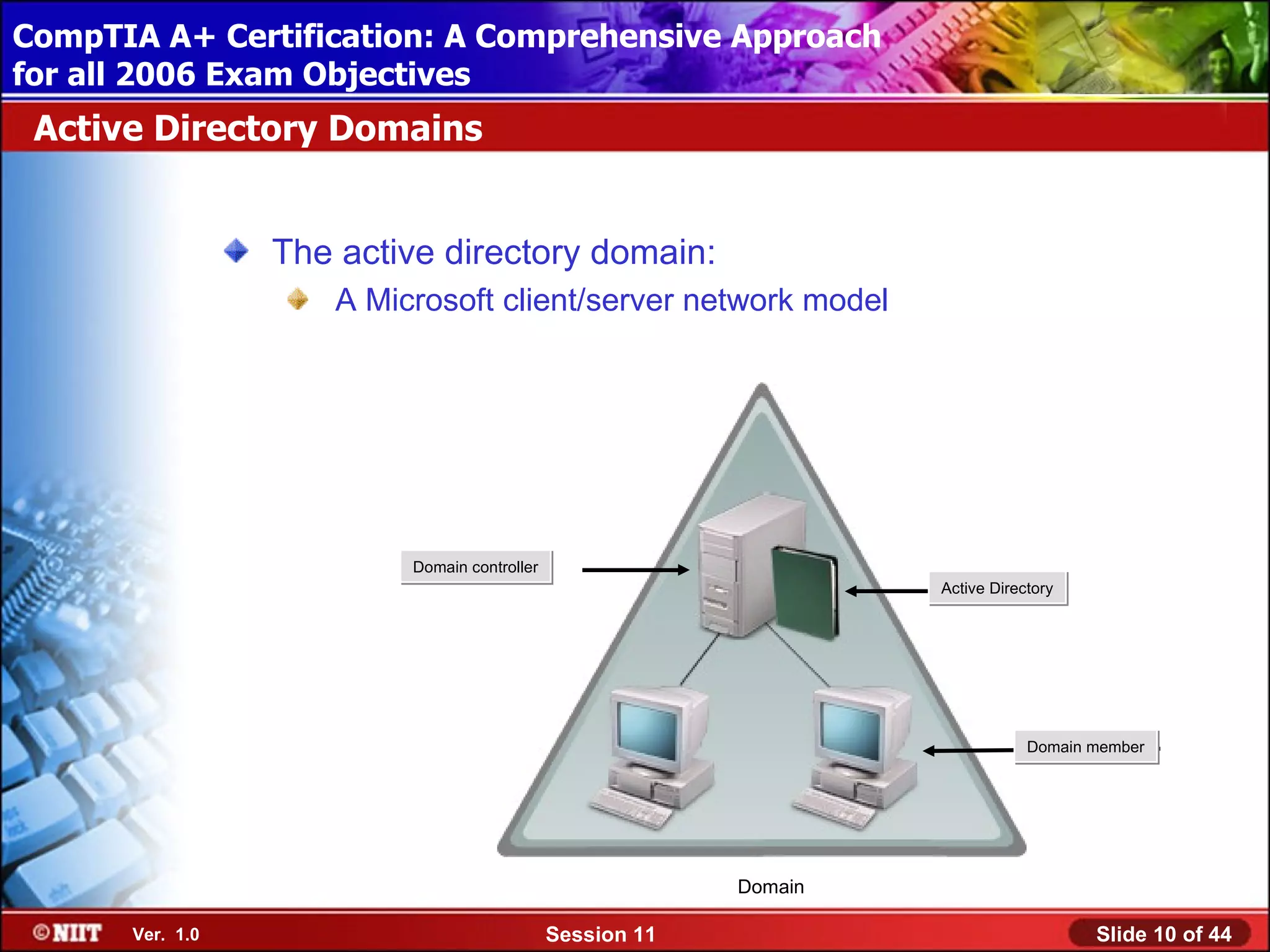
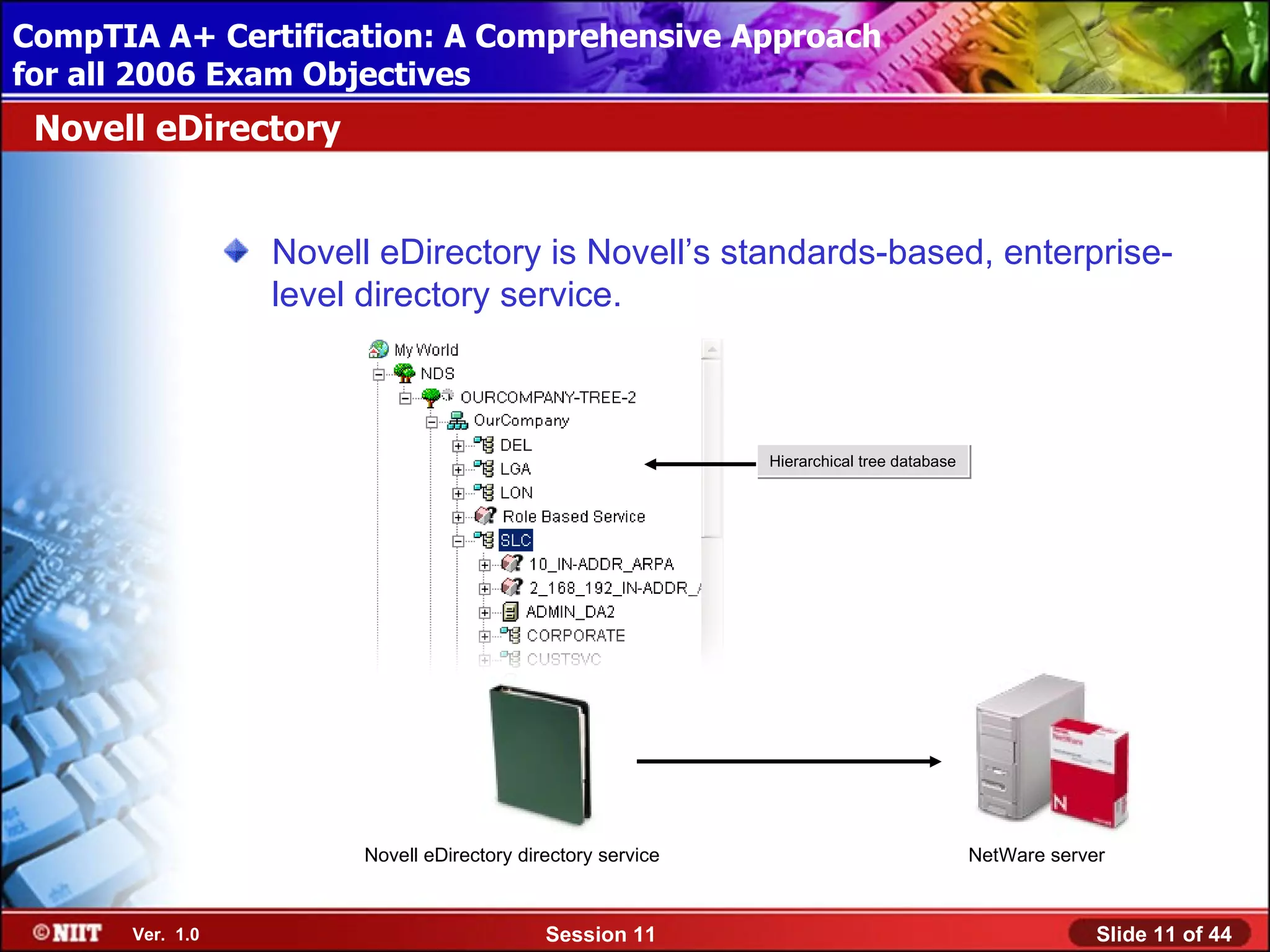
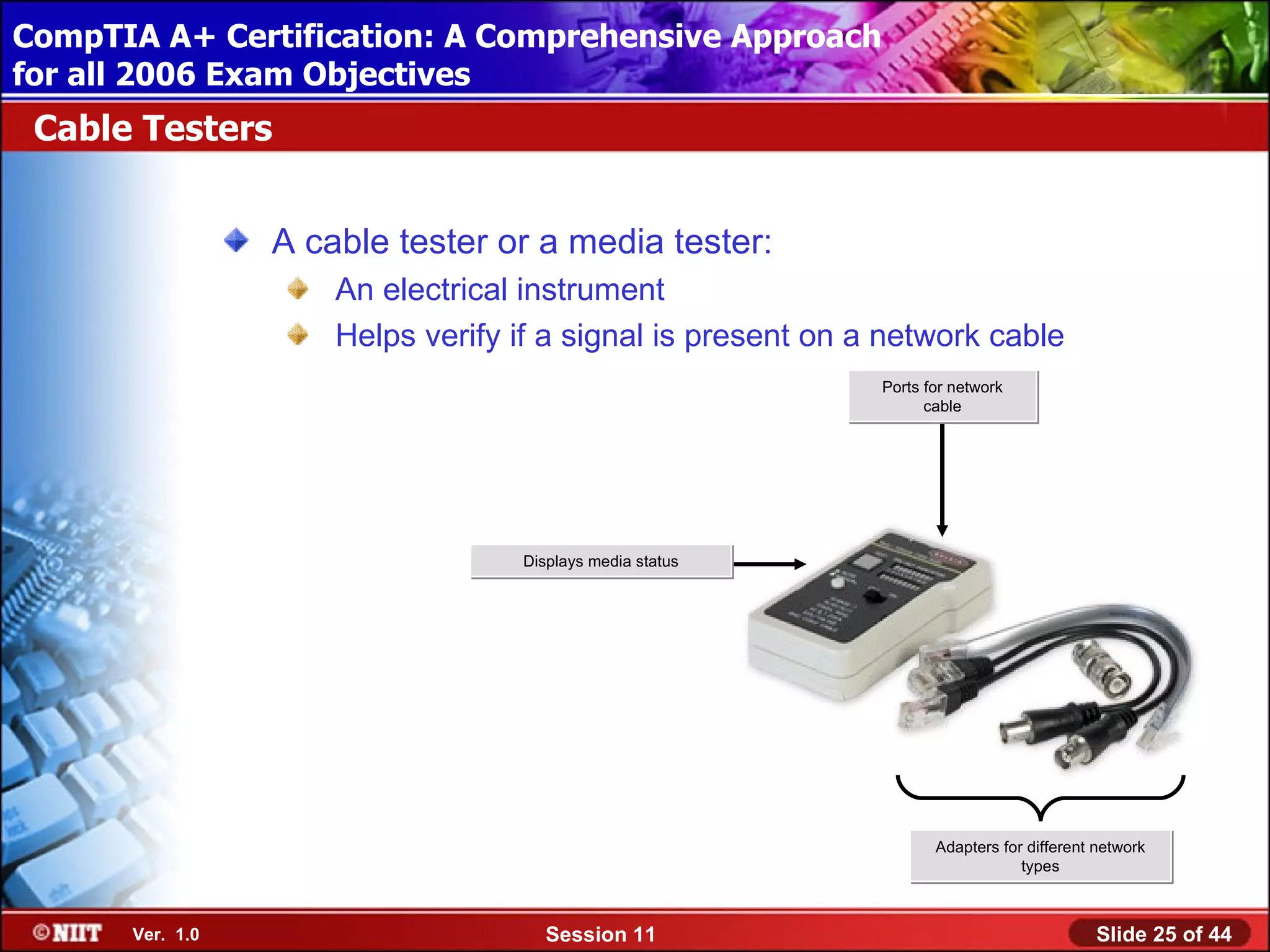
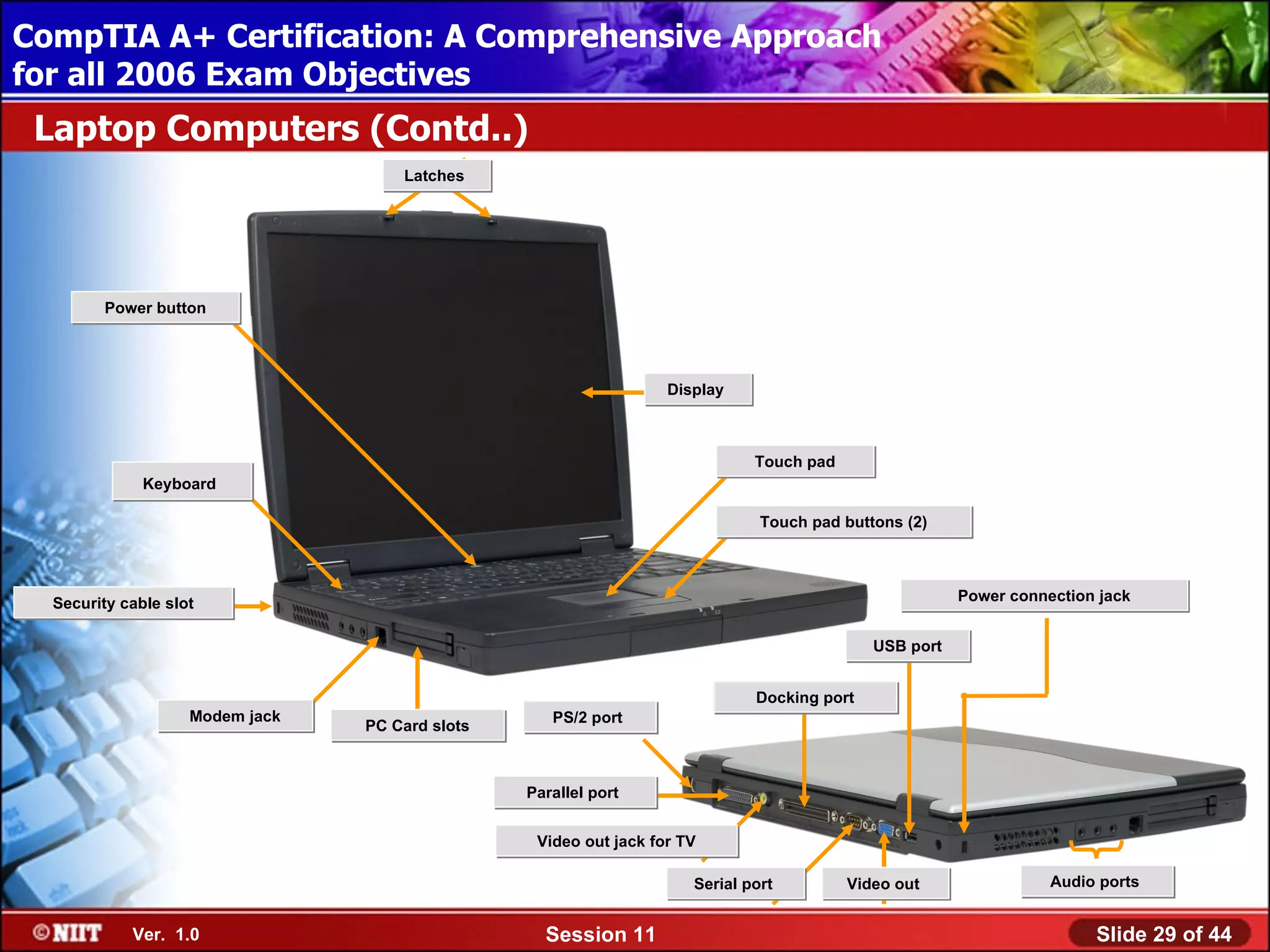
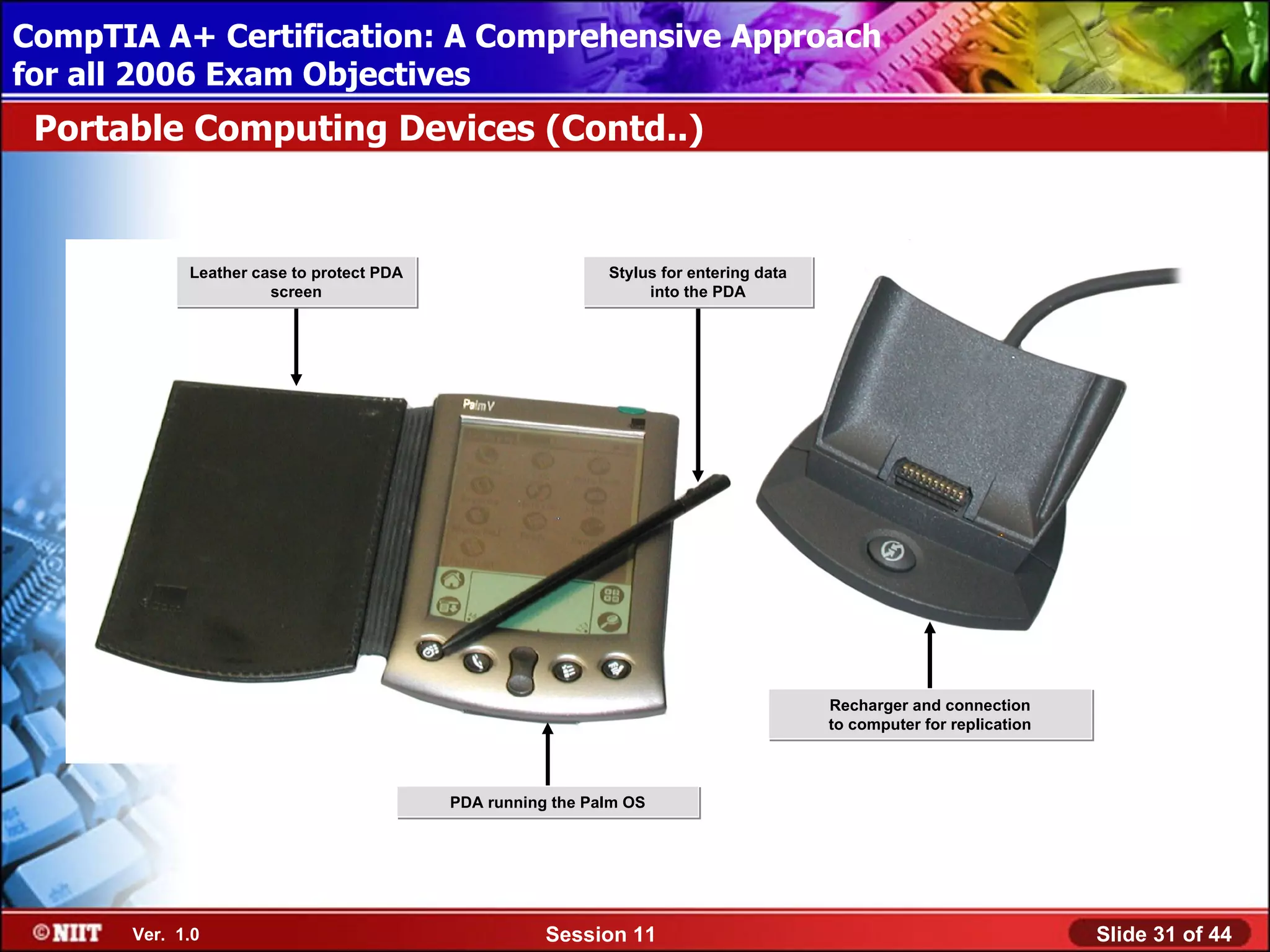
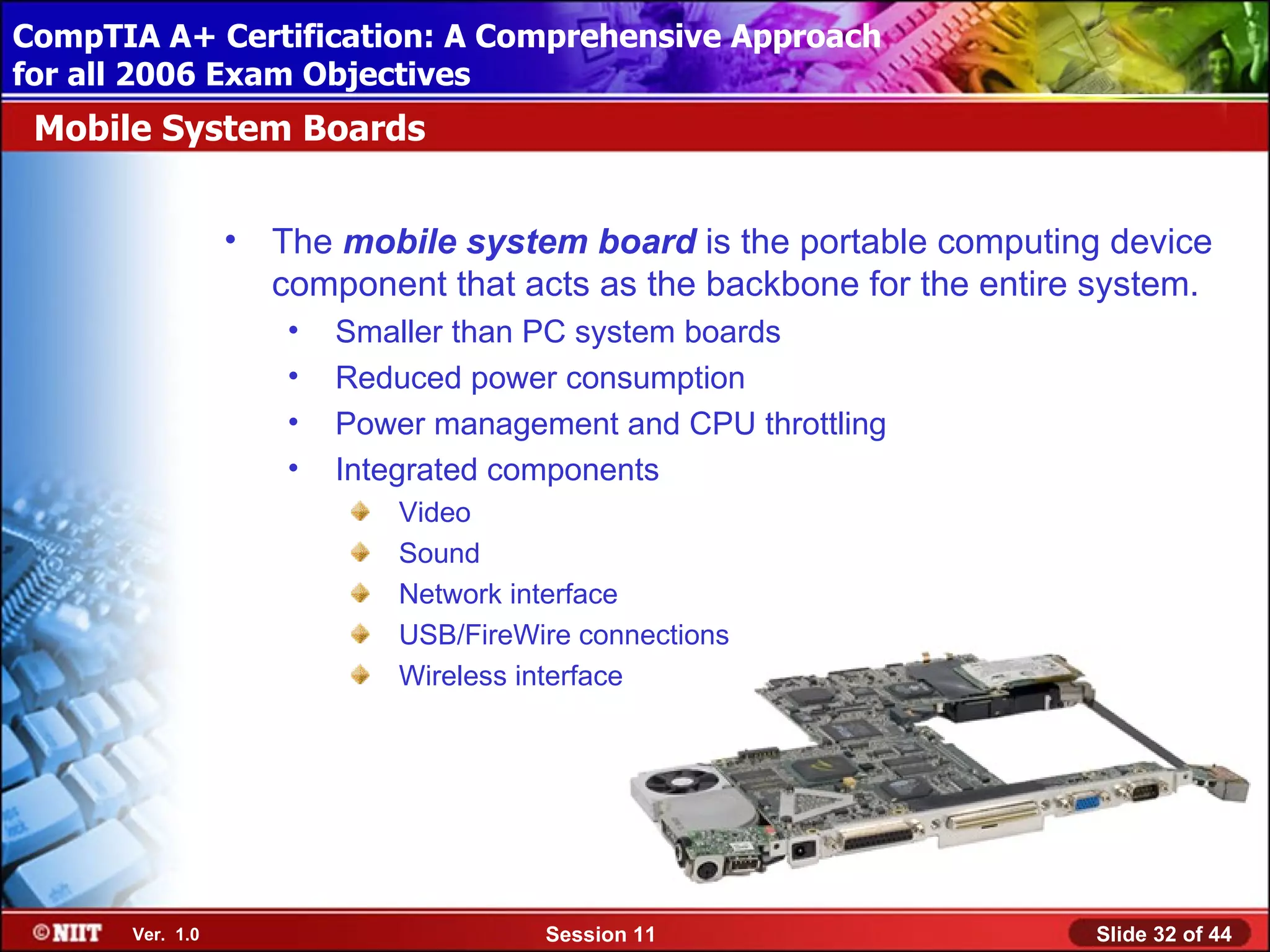
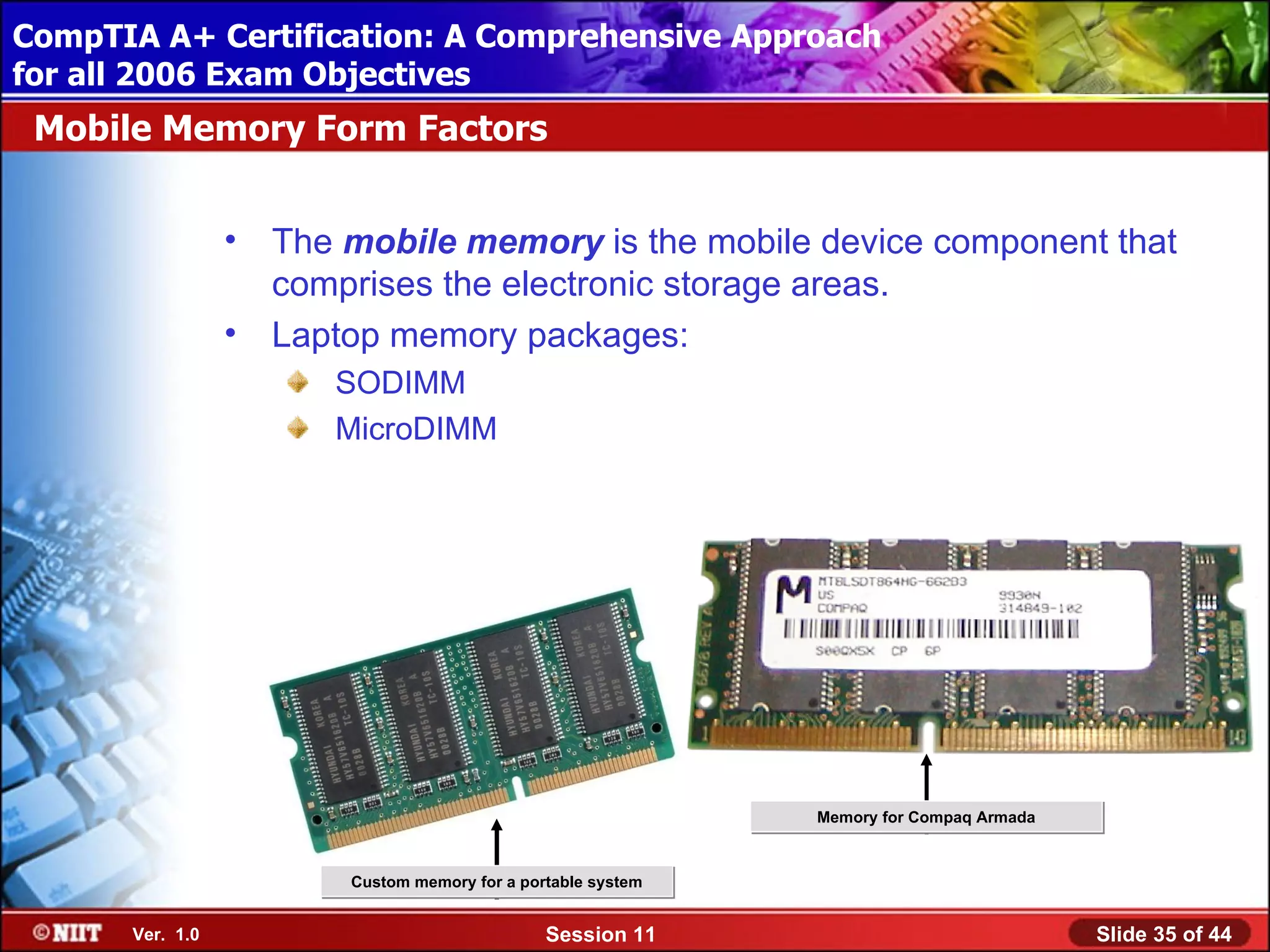
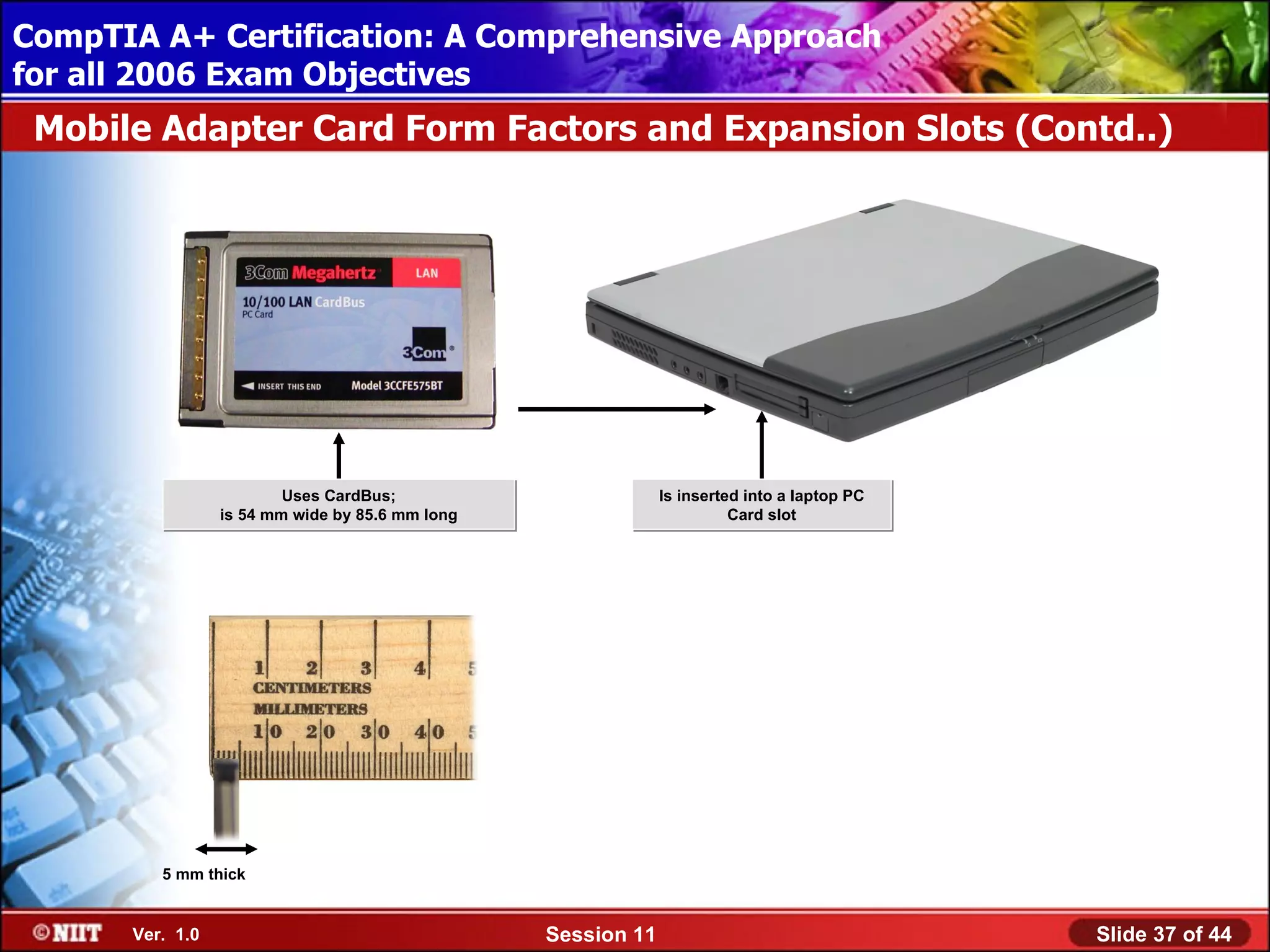
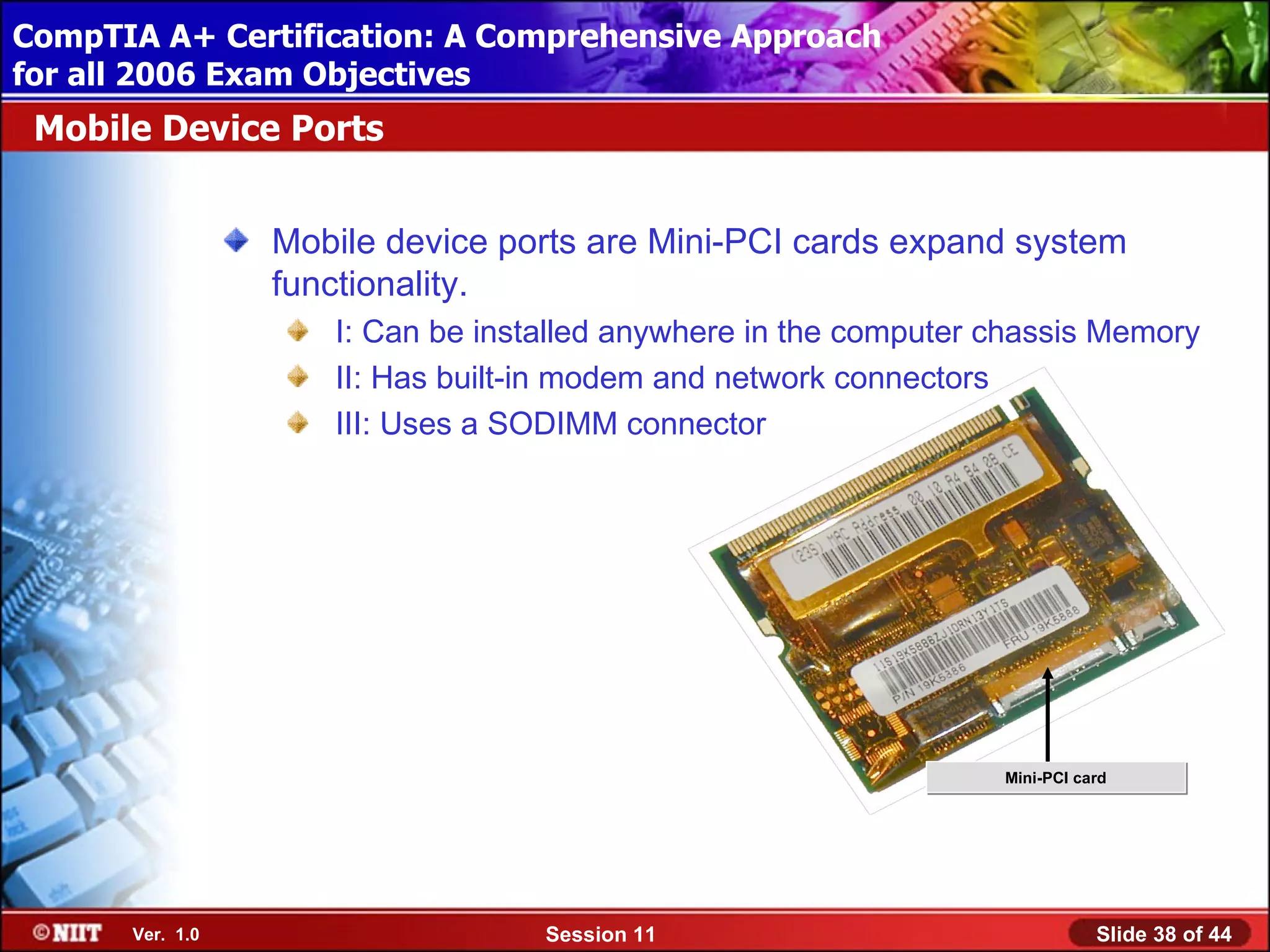
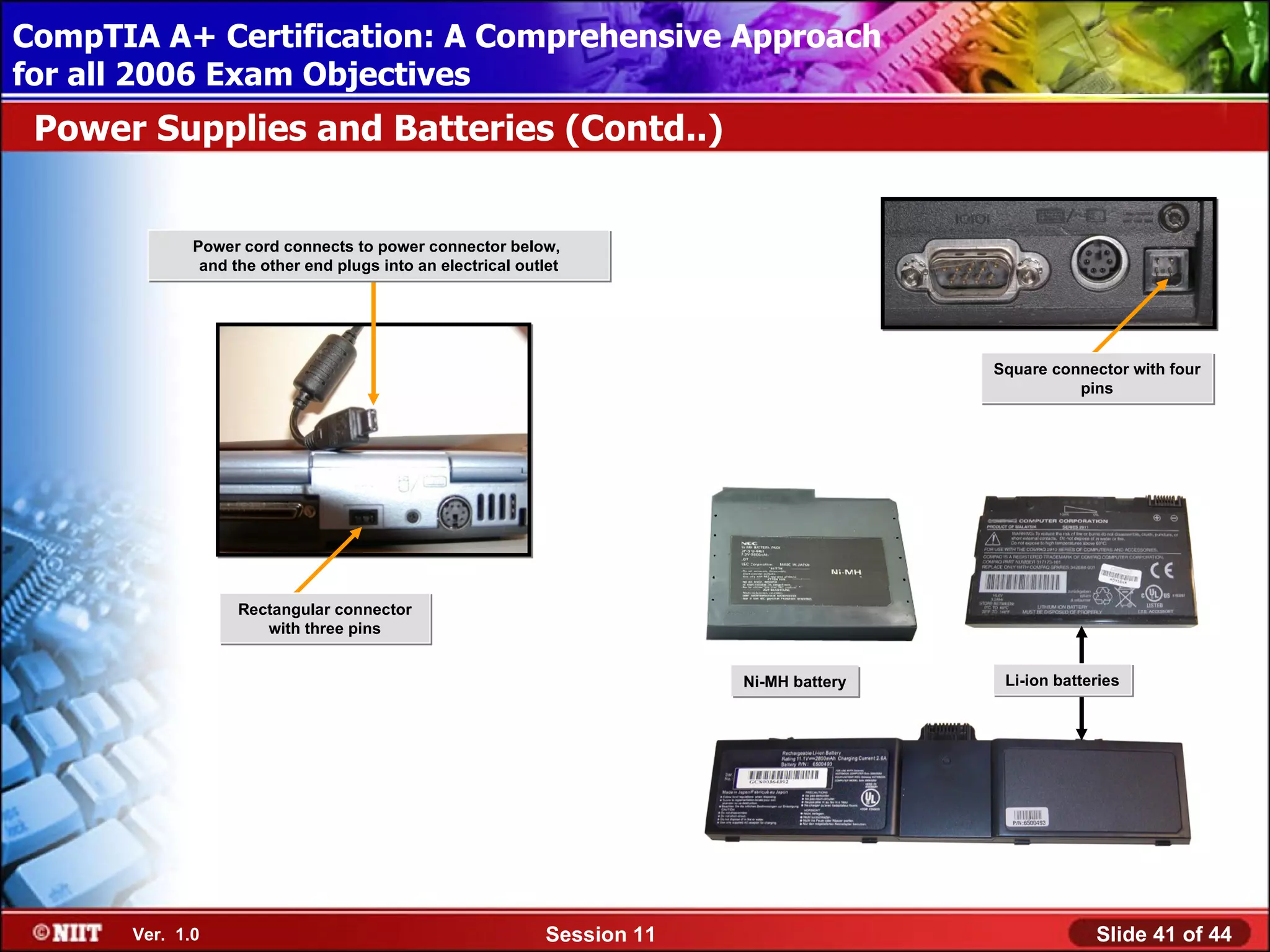
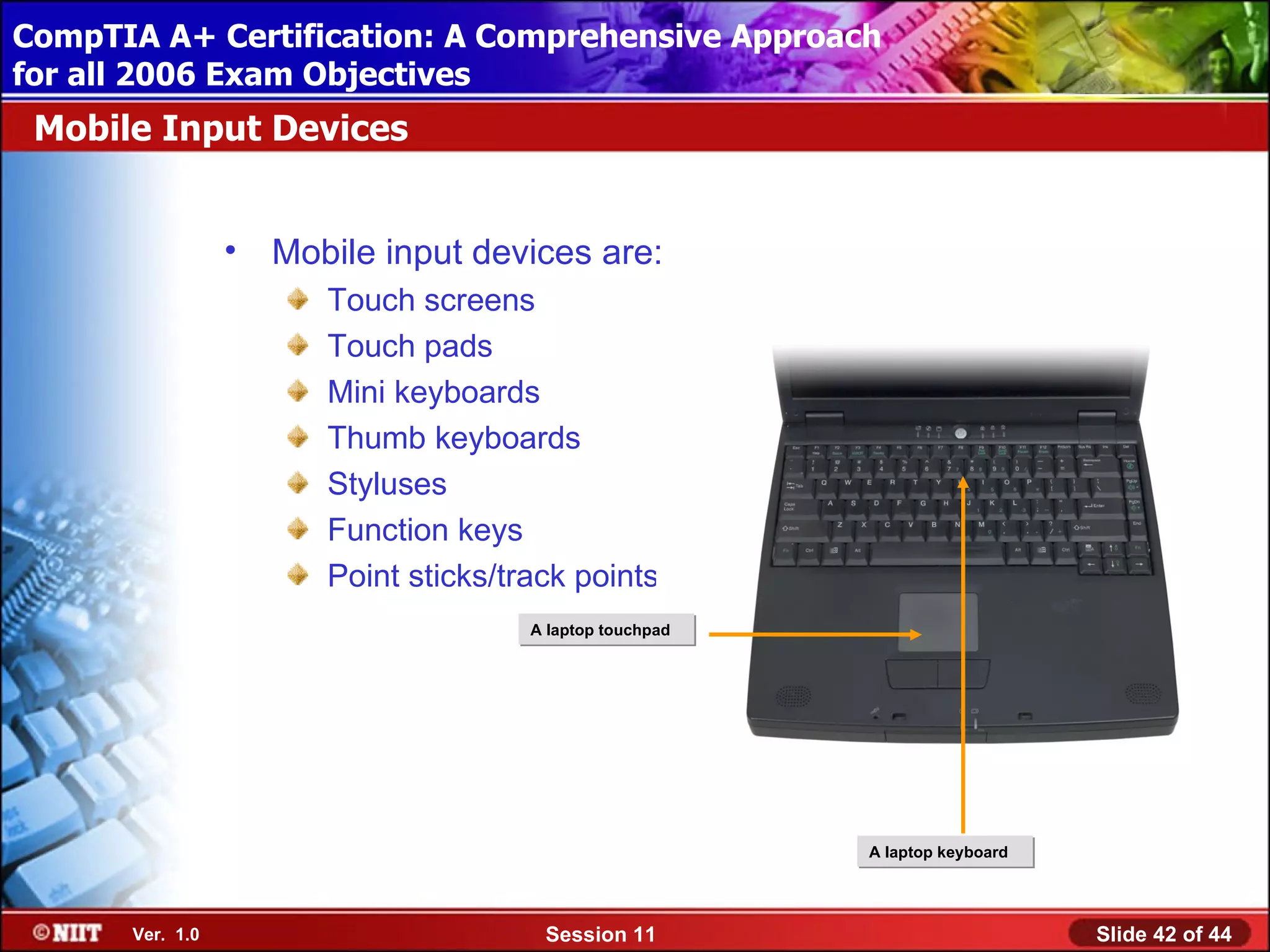
This document provides an overview of topics related to networking and laptop components for CompTIA A+ certification. It discusses network connection methods, name resolution, directory services, and troubleshooting techniques. It also covers laptop hardware such as mobile processors, memory, ports and peripherals. The goal is to teach exam objectives for installing and maintaining both networking and laptop systems.