This document provides an overview and student guide for the "Implementing Cisco MPLS (MPLS) Version 2.2" course. It introduces basic MPLS concepts including the MPLS architecture, labels, label stacks, and applications such as MPLS VPNs and traffic engineering. It also covers frame-mode MPLS implementation on Cisco IOS platforms, including configuration, monitoring, and troubleshooting tasks. Finally, it discusses MPLS VPN technology in depth, including the MPLS VPN architecture, routing model, and packet forwarding mechanisms.
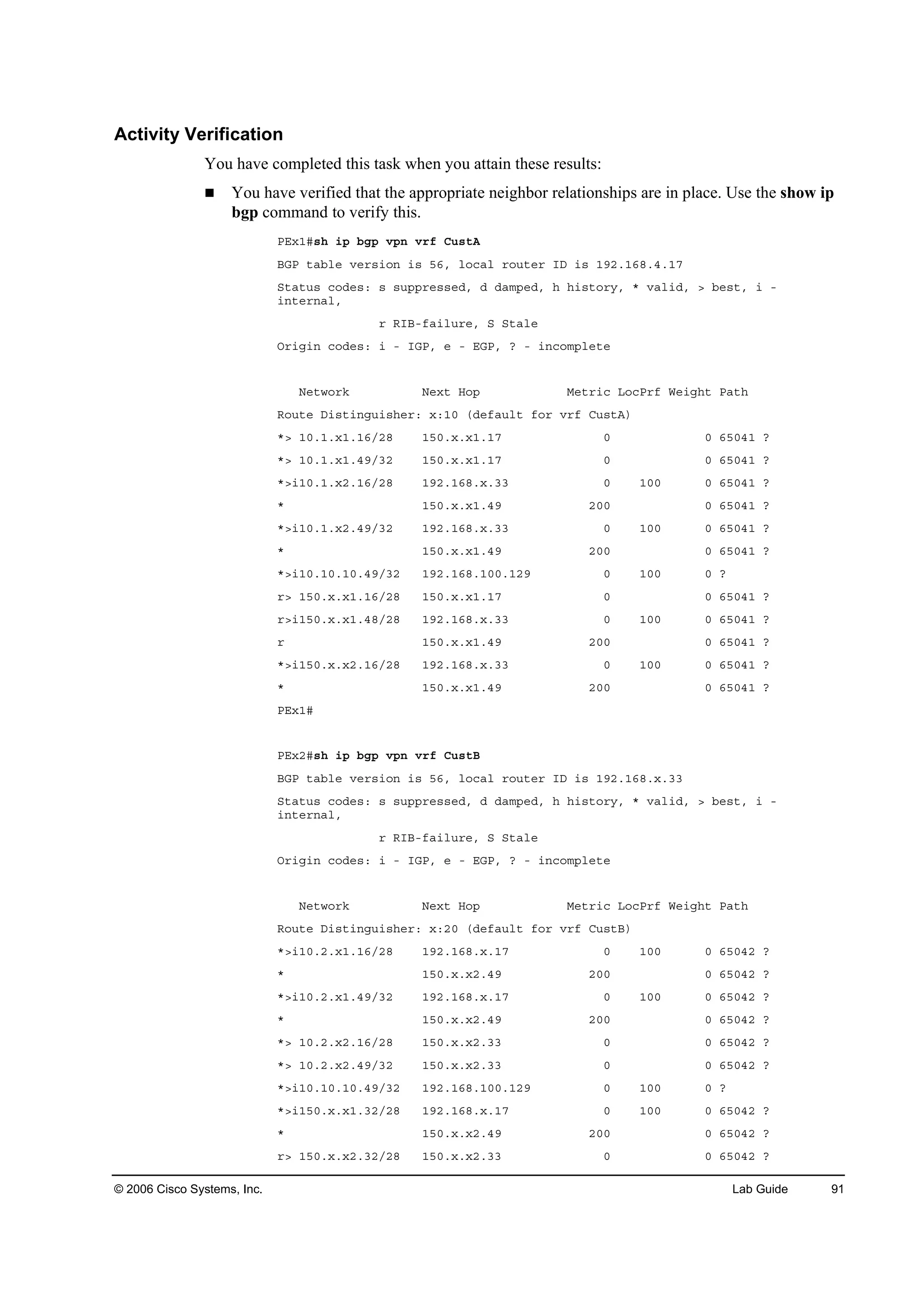
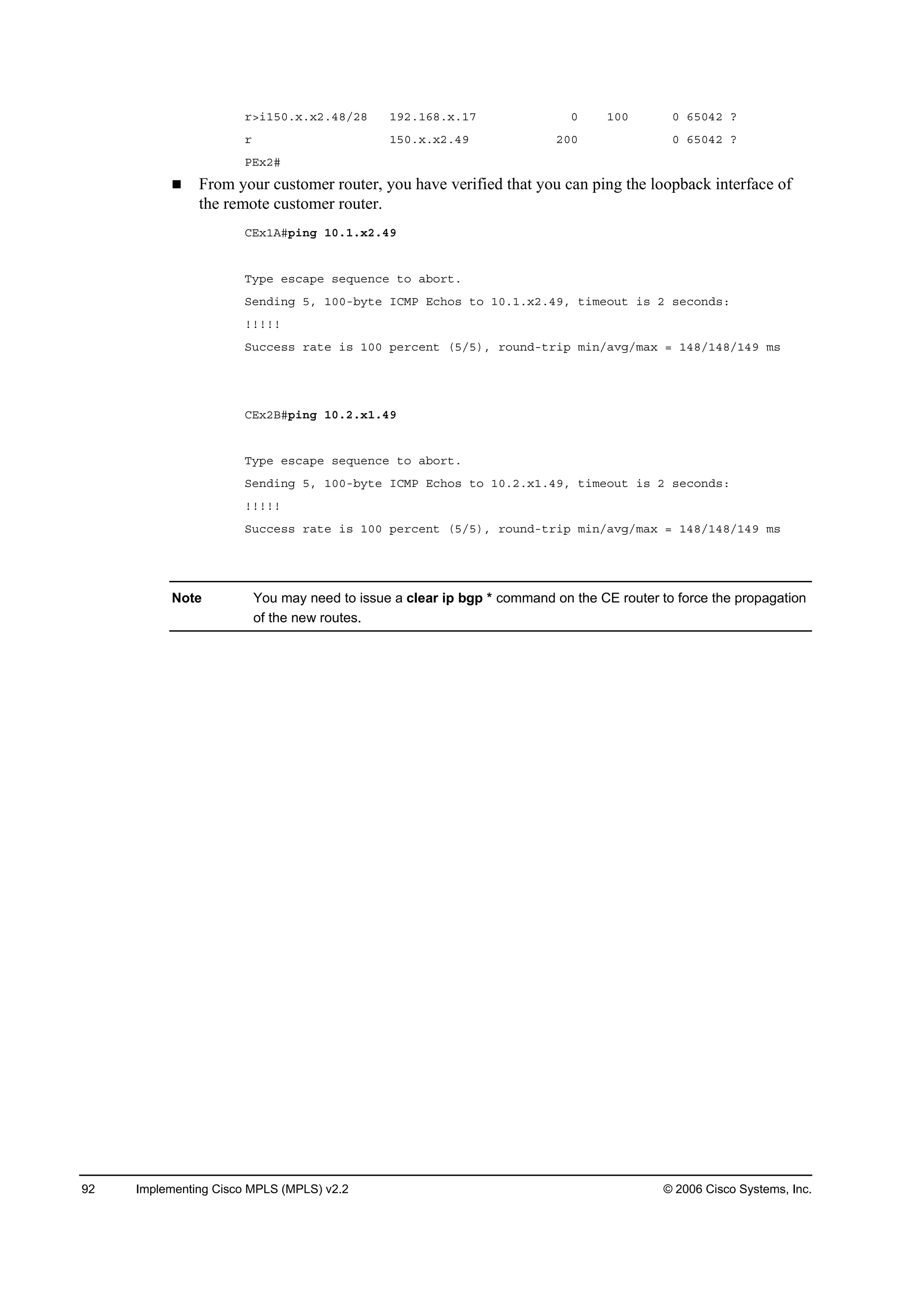
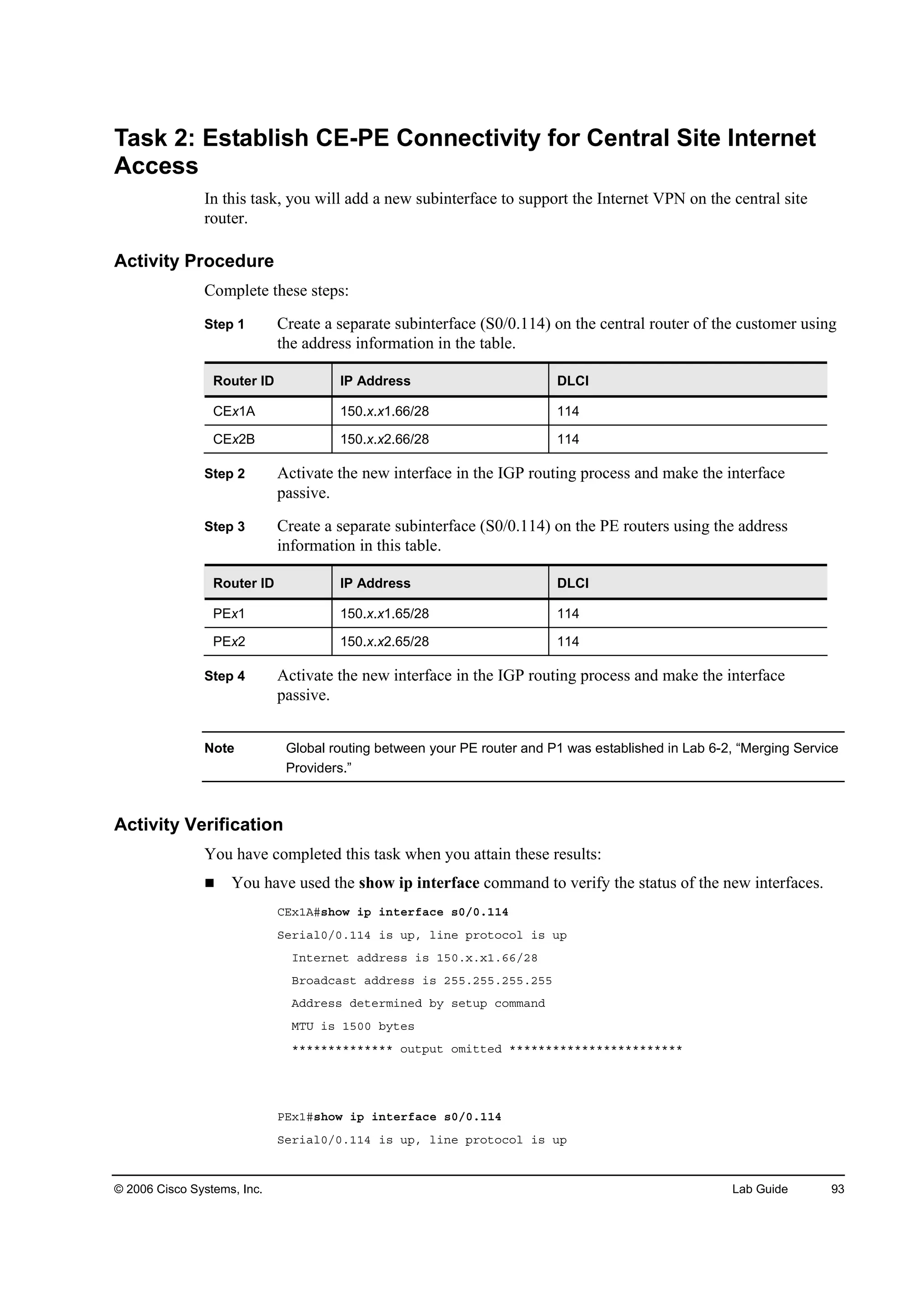
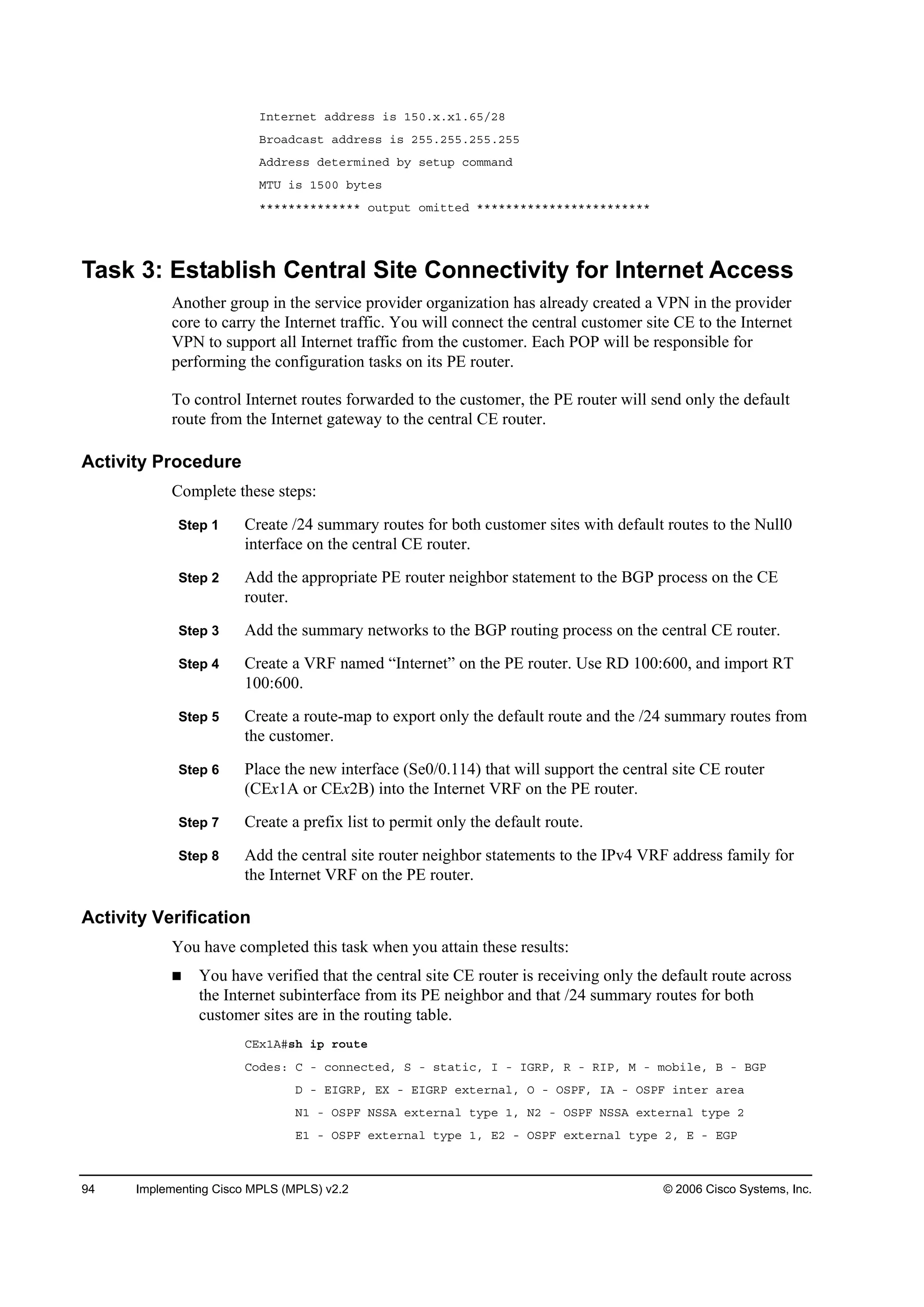
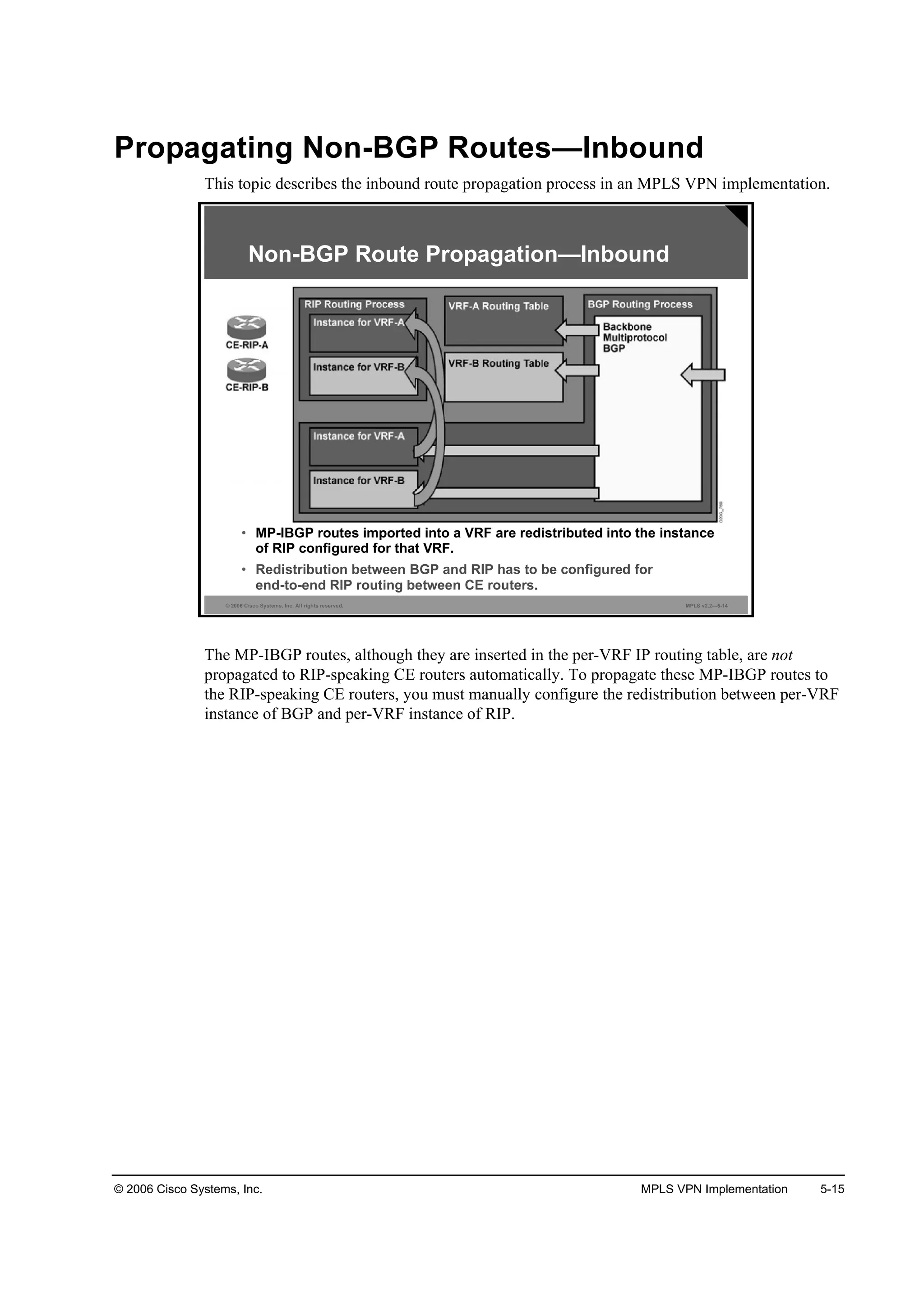
![2006 Cisco Systems, Inc. Implementing Cisco MPLS (MPLS) v2.2 iii
Introducing Convergence in Frame-Mode MPLS 2-49
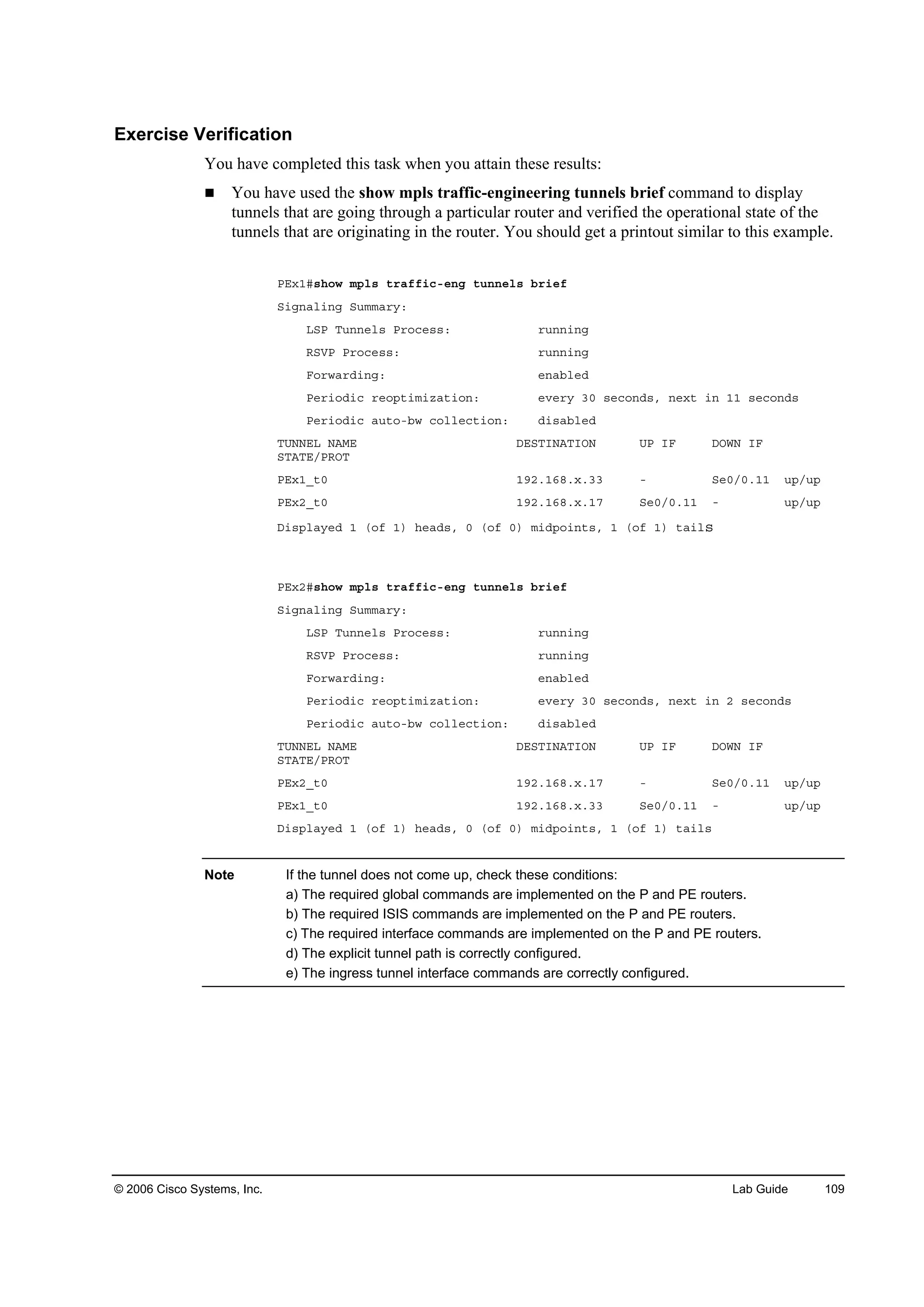
Overview 2-49
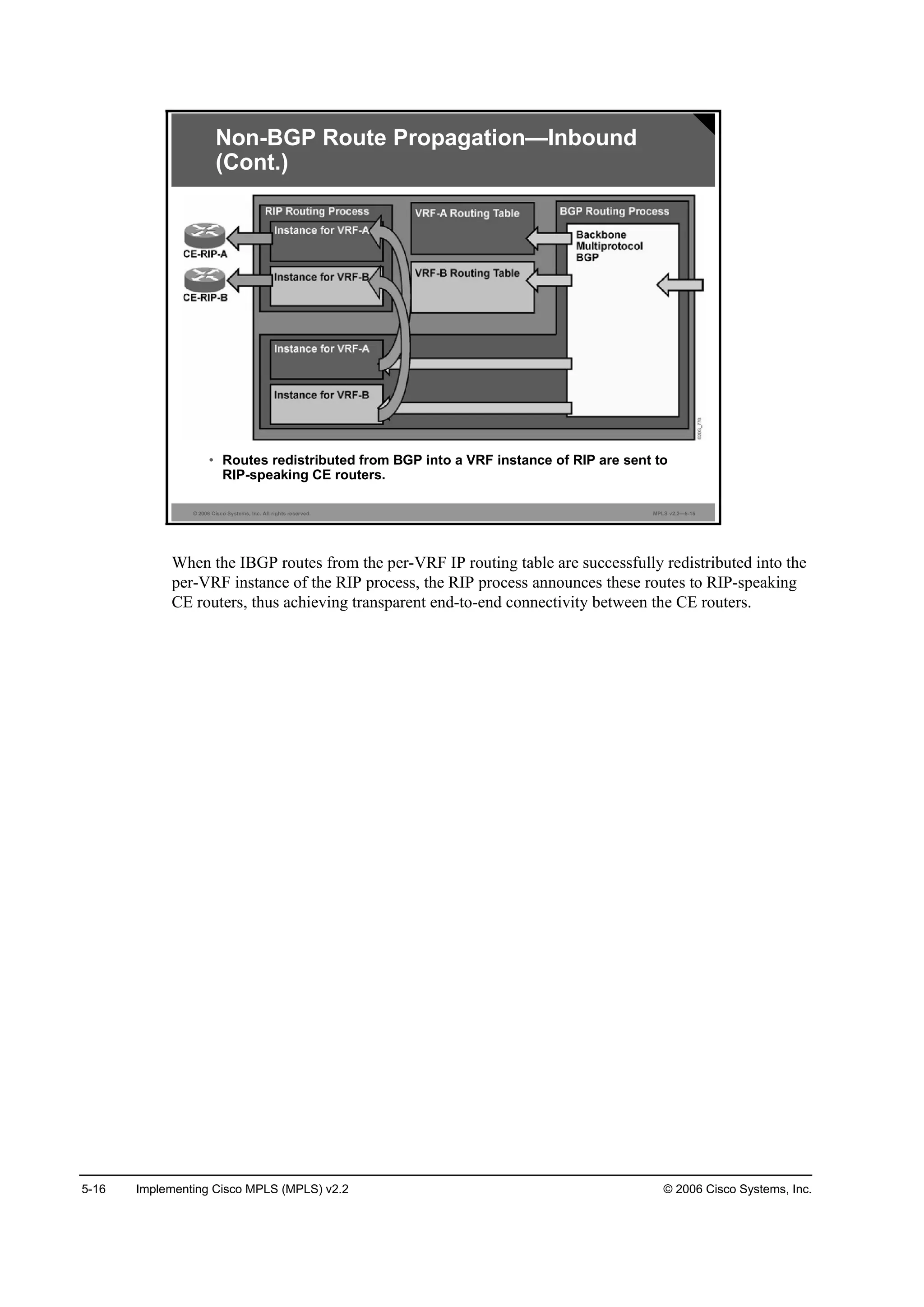
Objectives 2-49
What Is the MPLS Steady-State Operation? 2-50
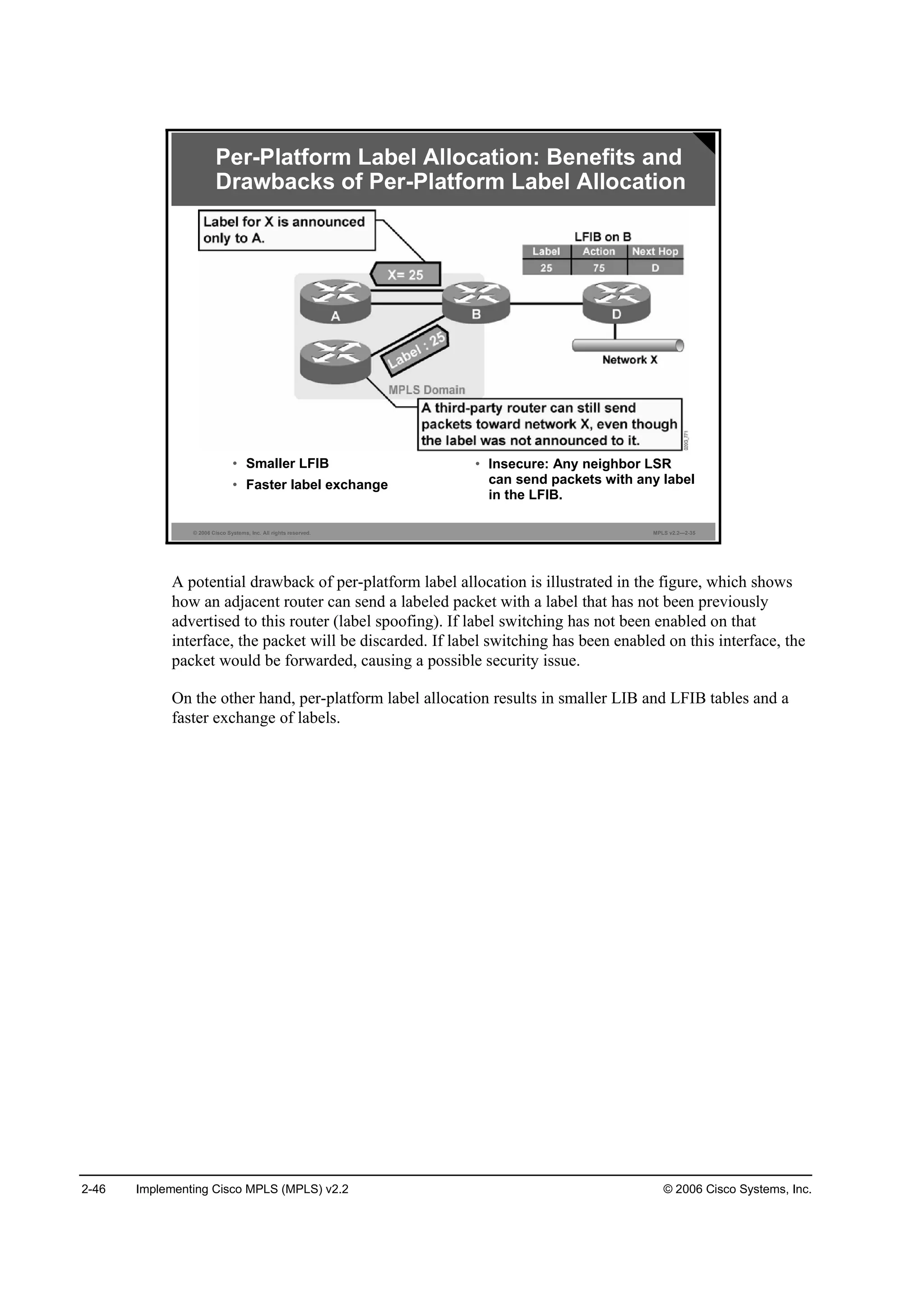
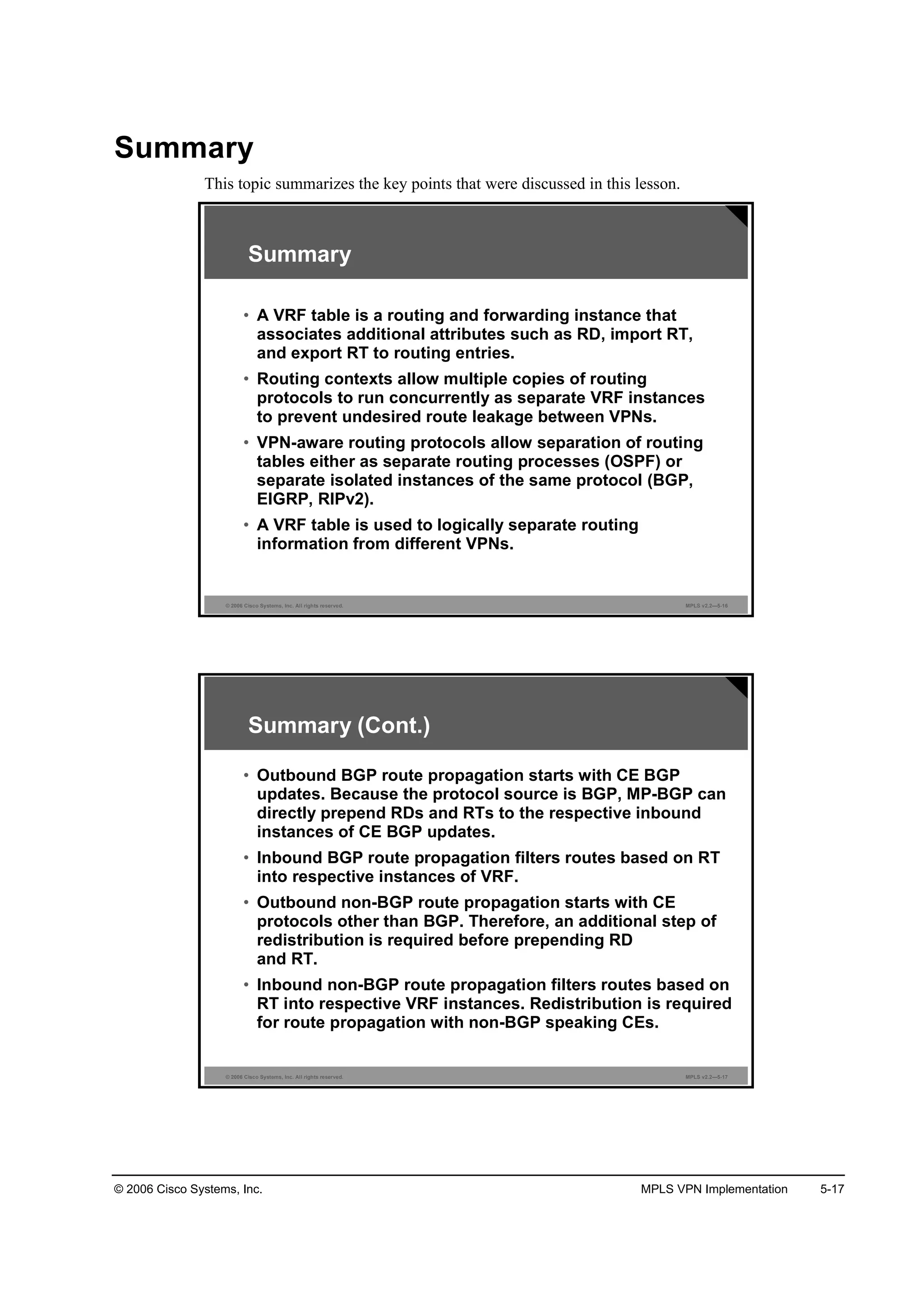
What Happens in a Link Failure? 2-51
Example: Link Failure Actions 2-51
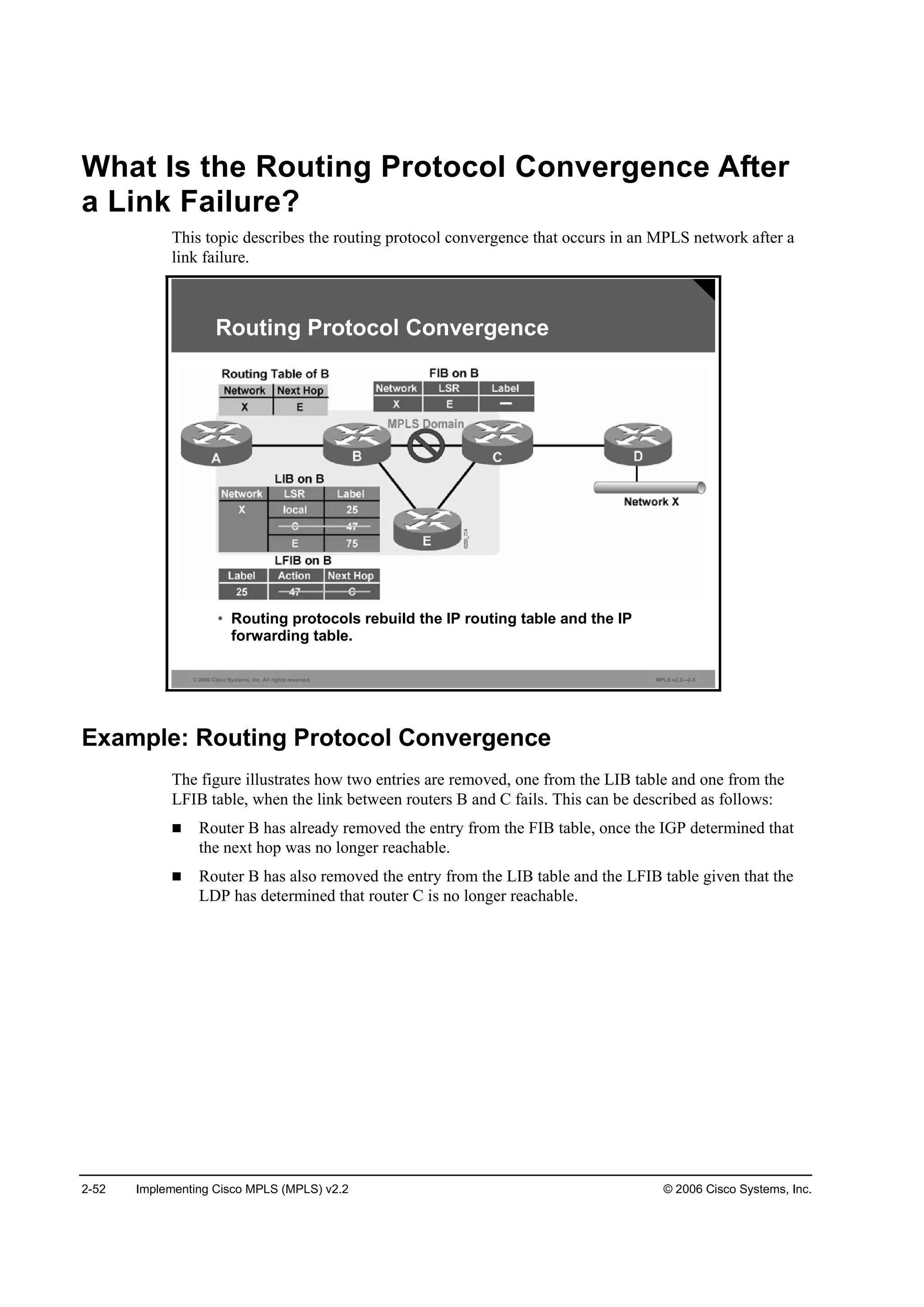
What Is the Routing Protocol Convergence After a Link Failure? 2-52
Example: Routing Protocol Convergence 2-52
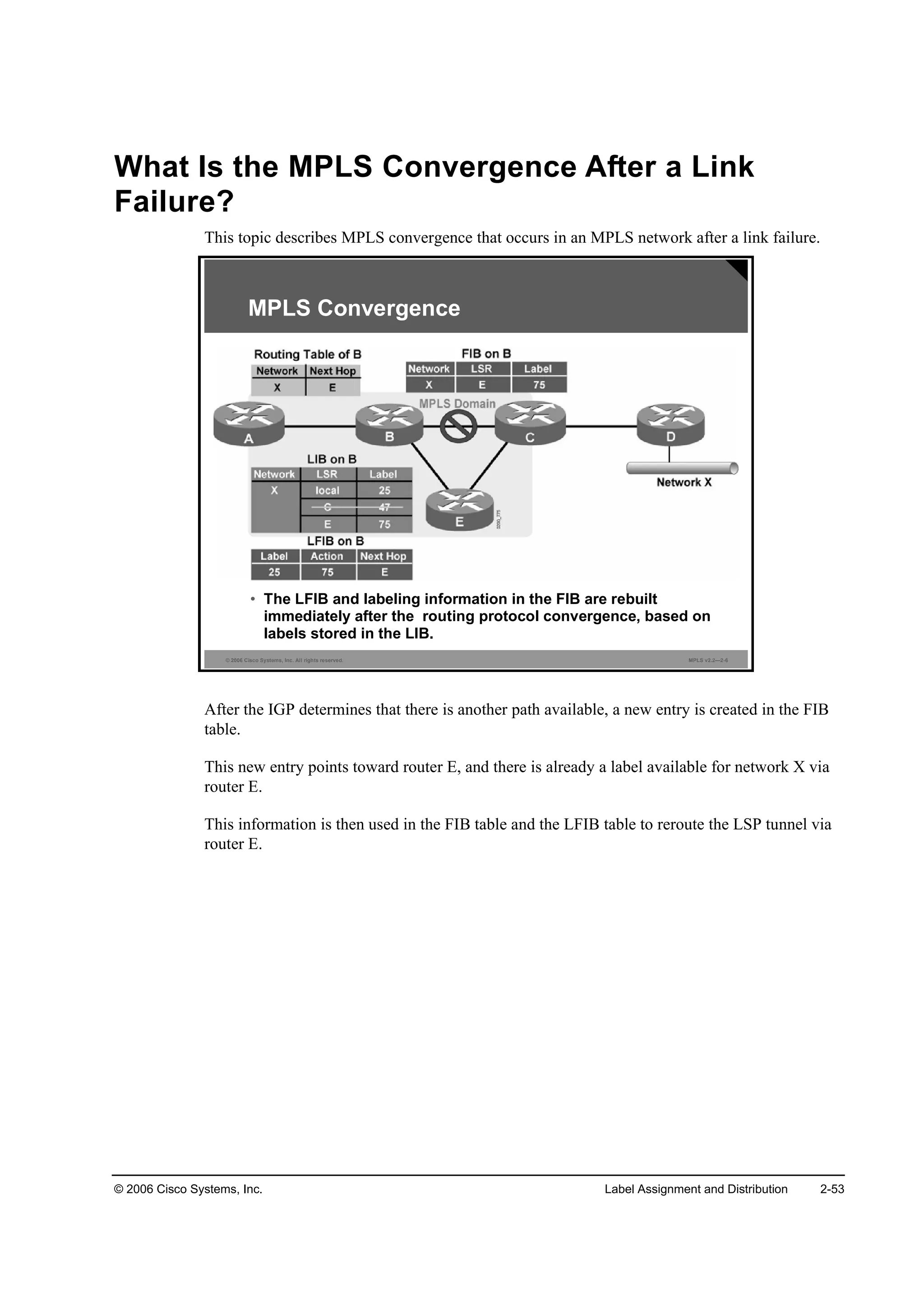
What Is the MPLS Convergence After a Link Failure? 2-53
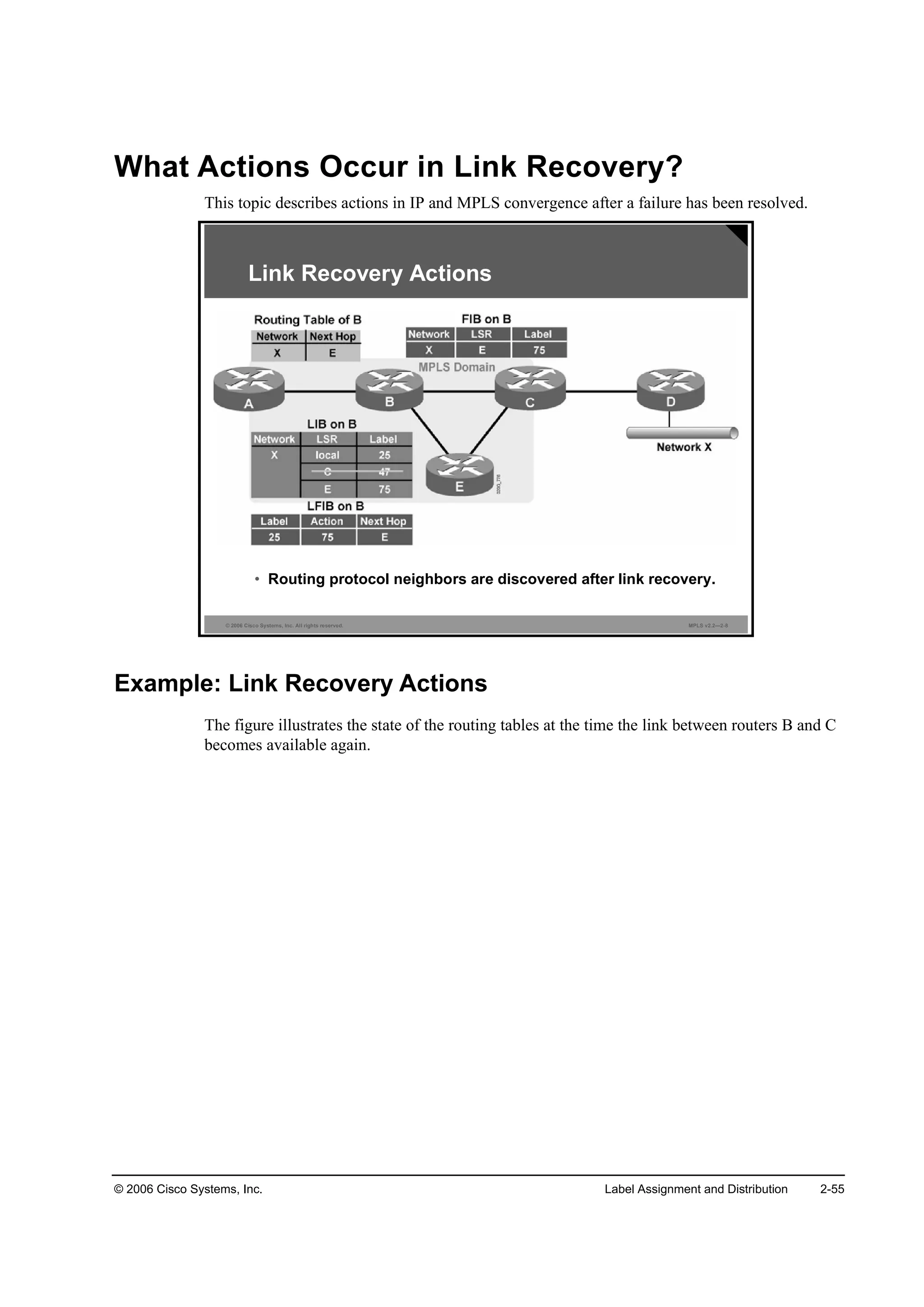
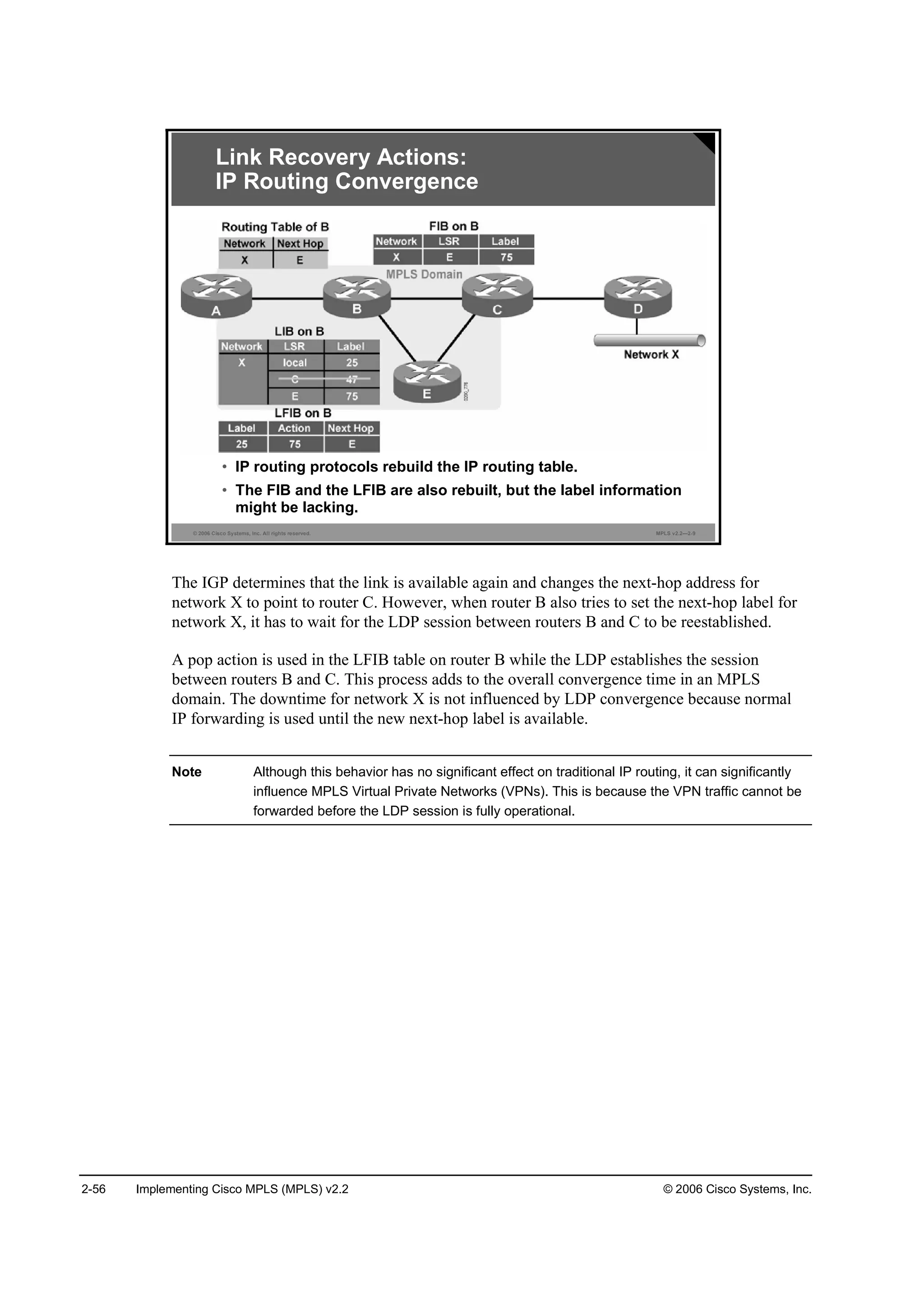
What Actions Occur in Link Recovery? 2-55
Example: Link Recovery Actions 2-55
Summary 2-58
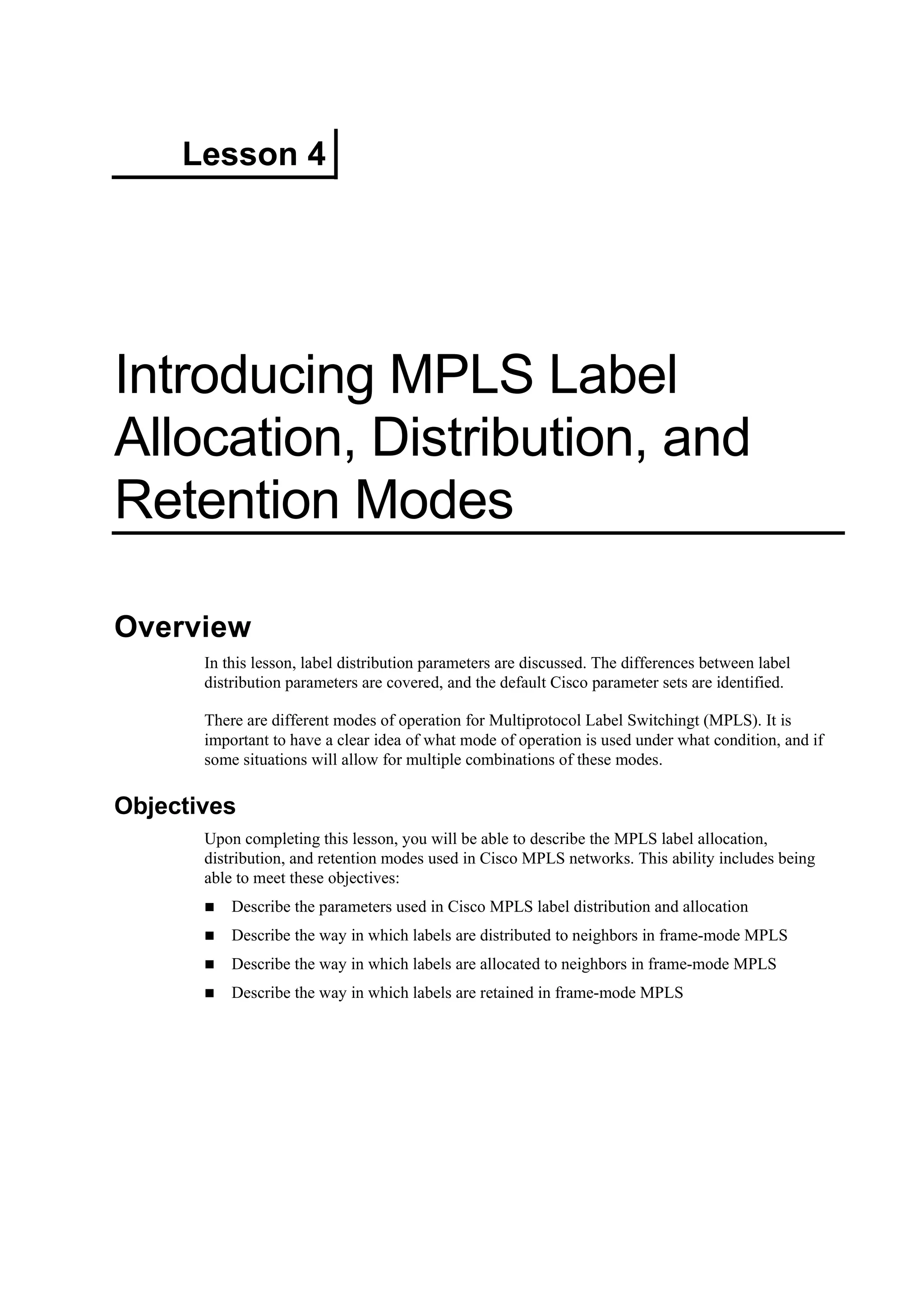
Introducing MPLS Label Allocation, Distribution, and Retention Modes 2-59
Overview 2-59
Objectives 2-59
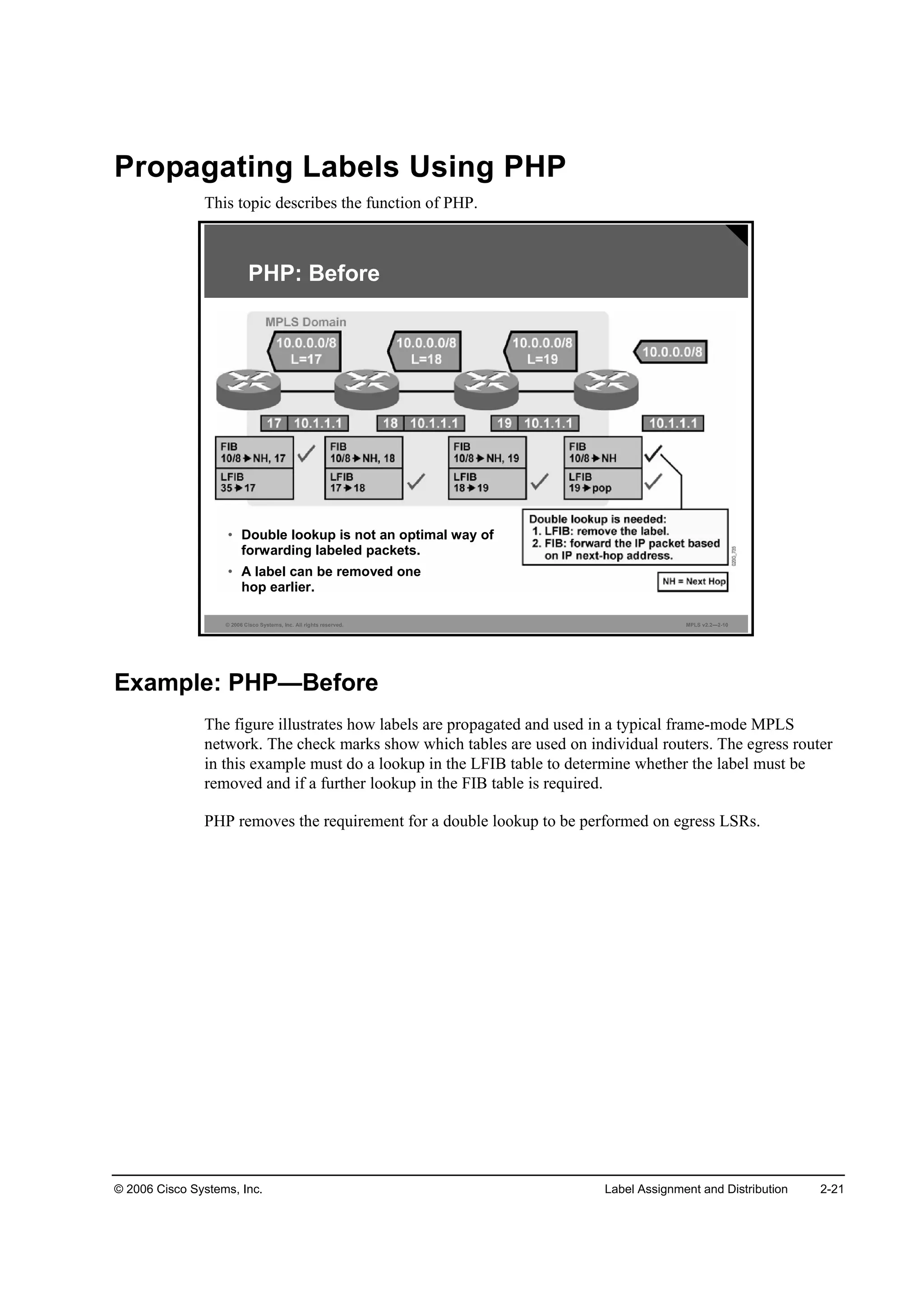
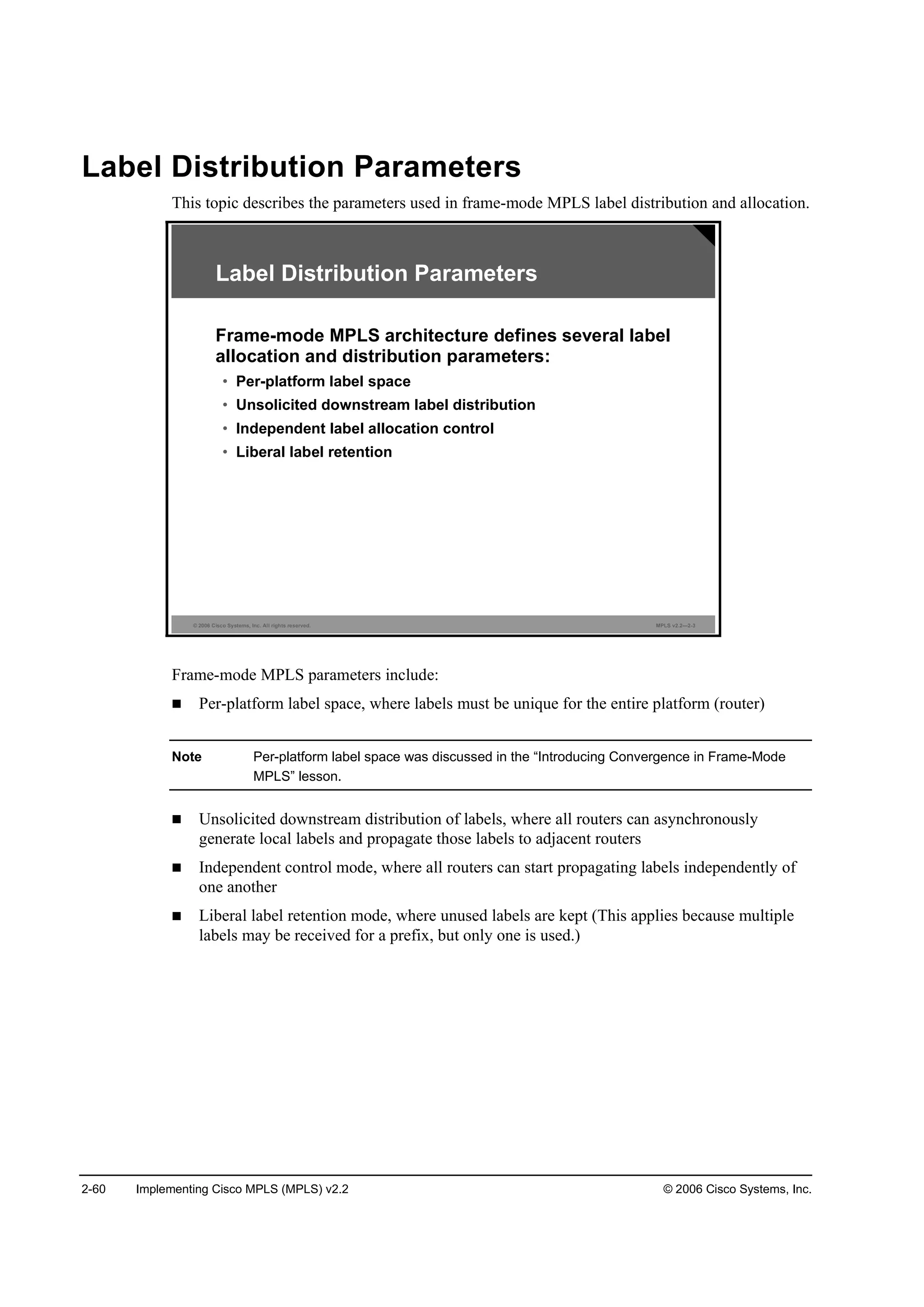
Label Distribution Parameters 2-60
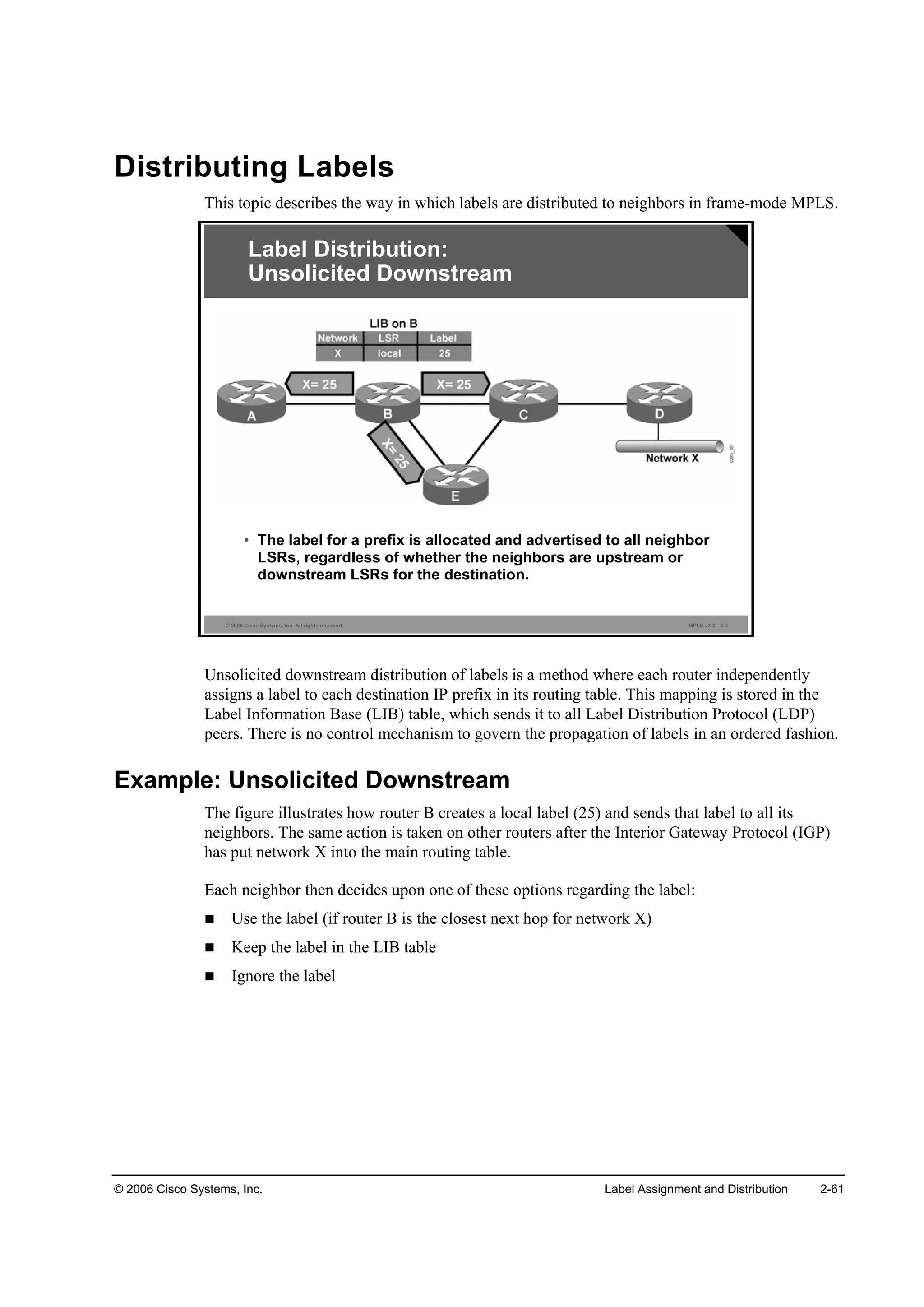
Distributing Labels 2-61
Example: Unsolicited Downstream 2-61
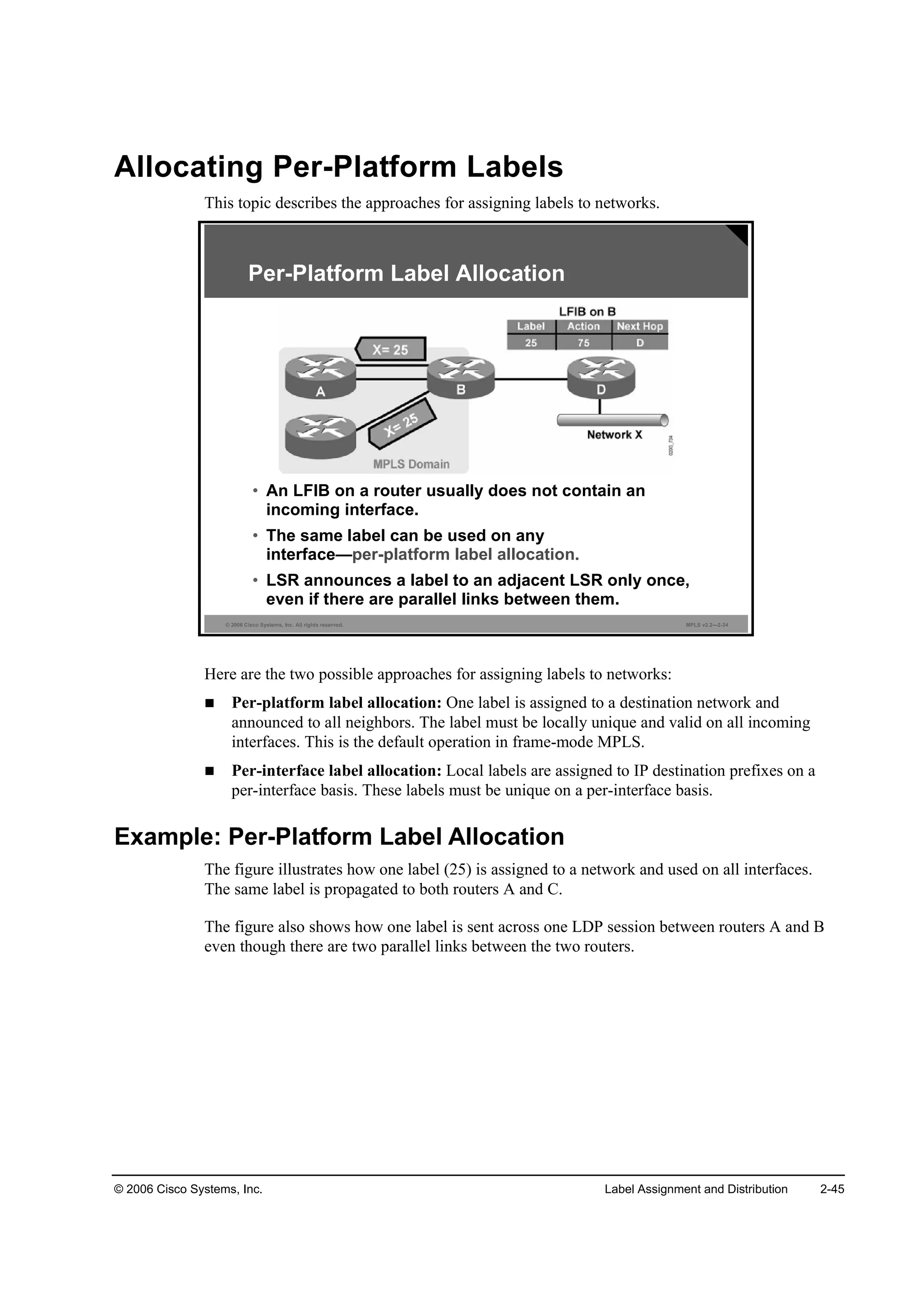
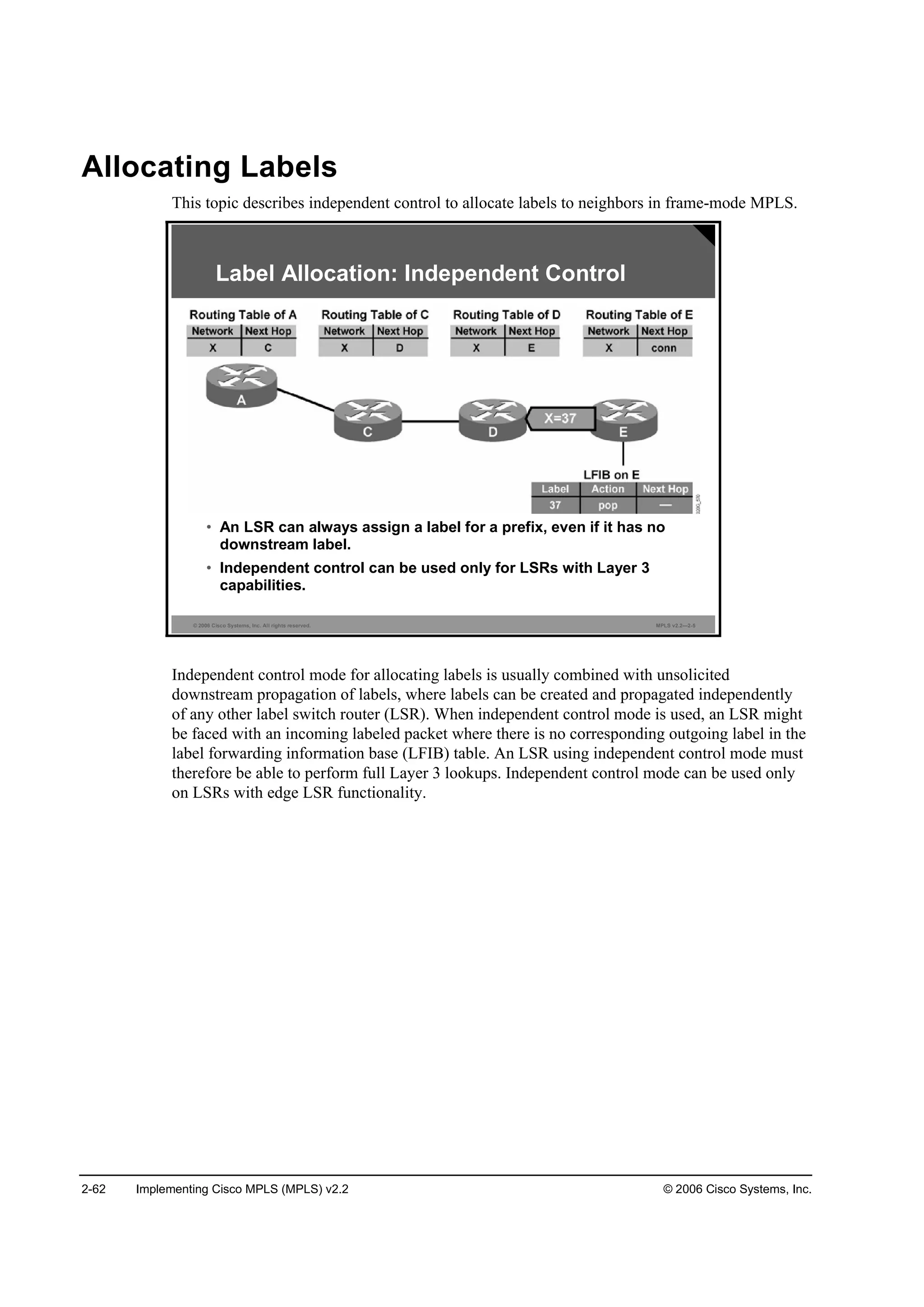
Allocating Labels 2-62
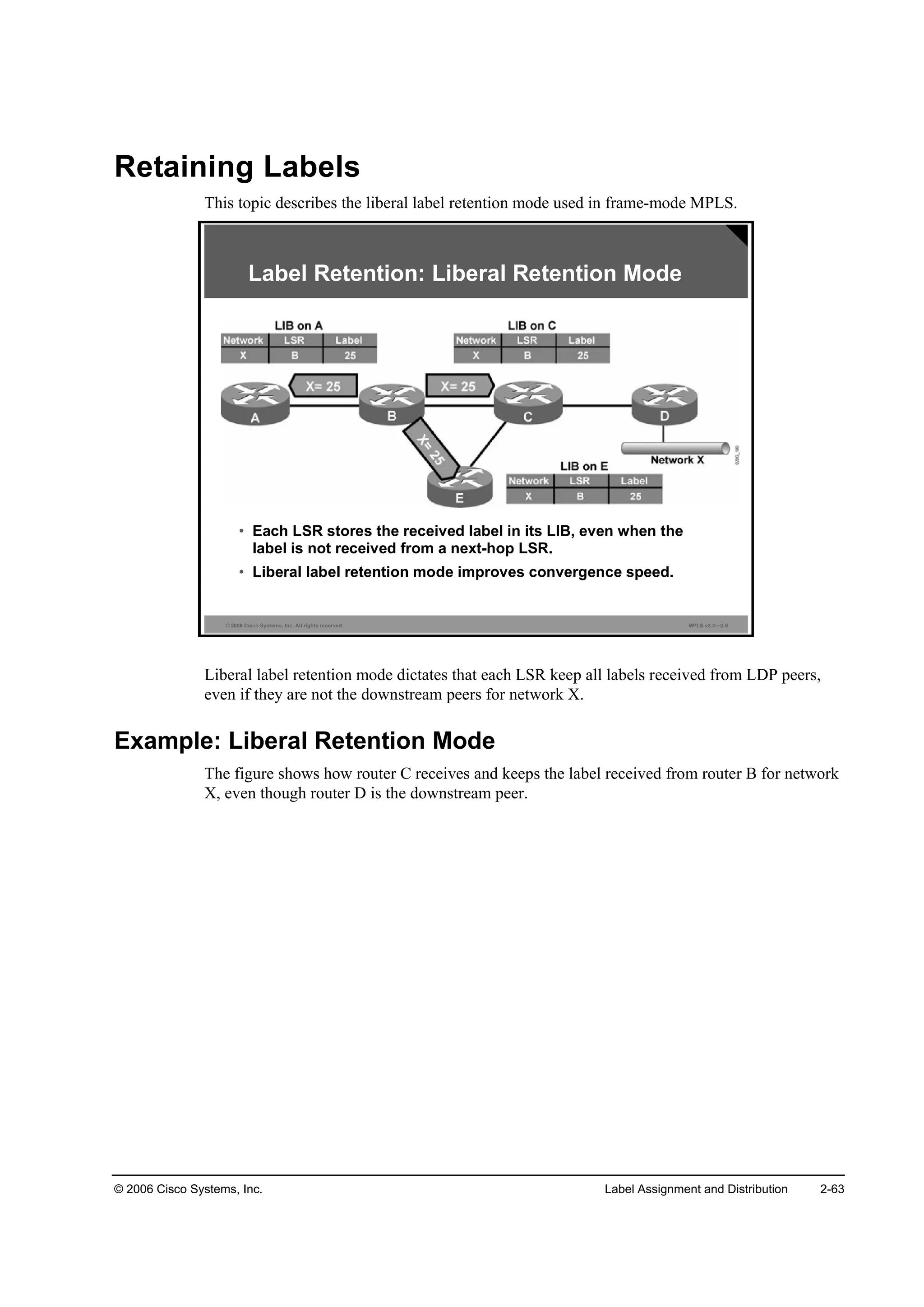
Retaining Labels 2-63
Example: Liberal Retention Mode 2-63
Summary 2-64
Module Summary 2-65
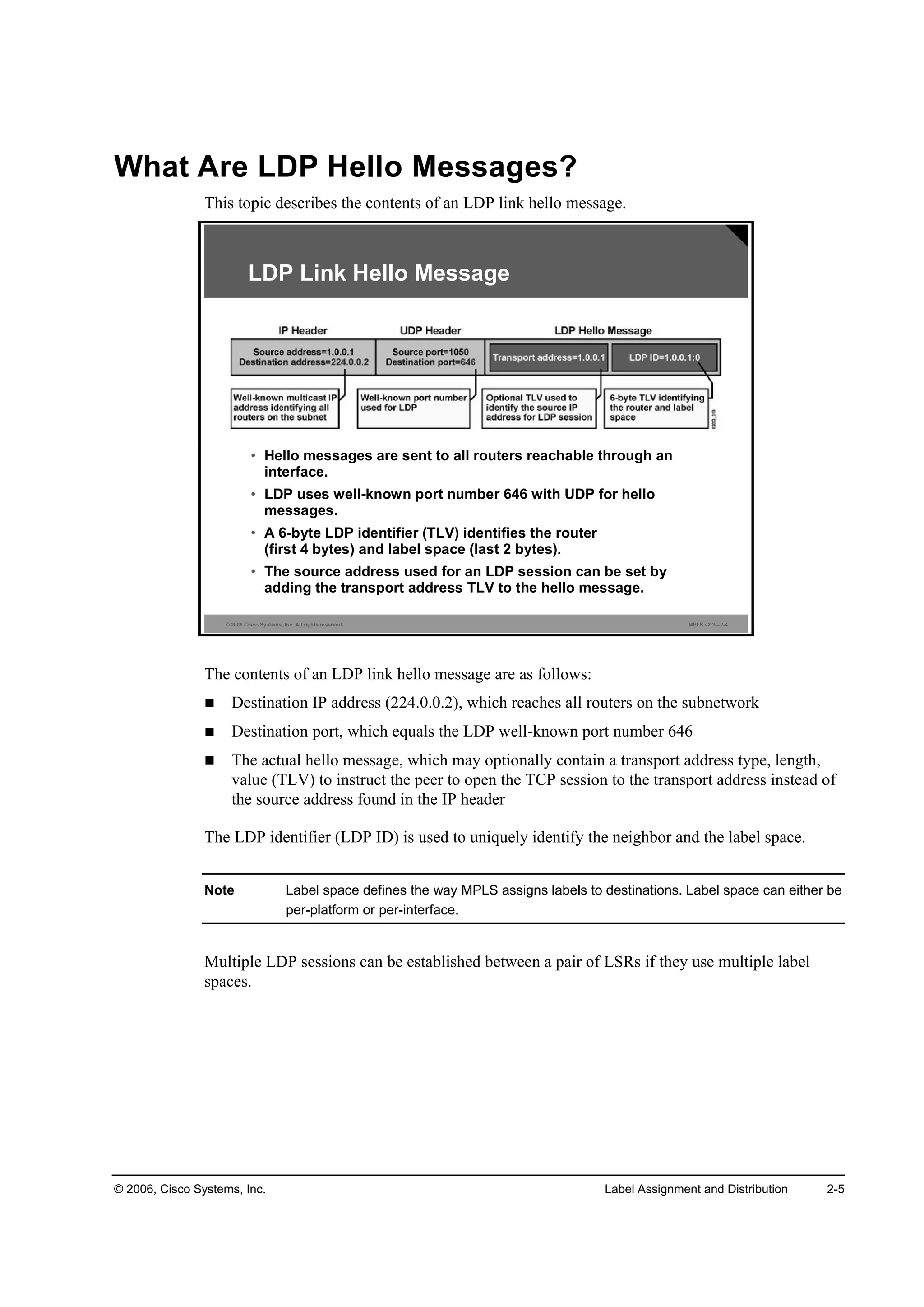
References 2-65
Module Self-Check 2-66
Module Self-Check Answer Key 2-71
Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-1
Overview 3-1
Module Objectives 3-1
Introducing CEF Switching 3-3
Overview 3-3
Objectives 3-3
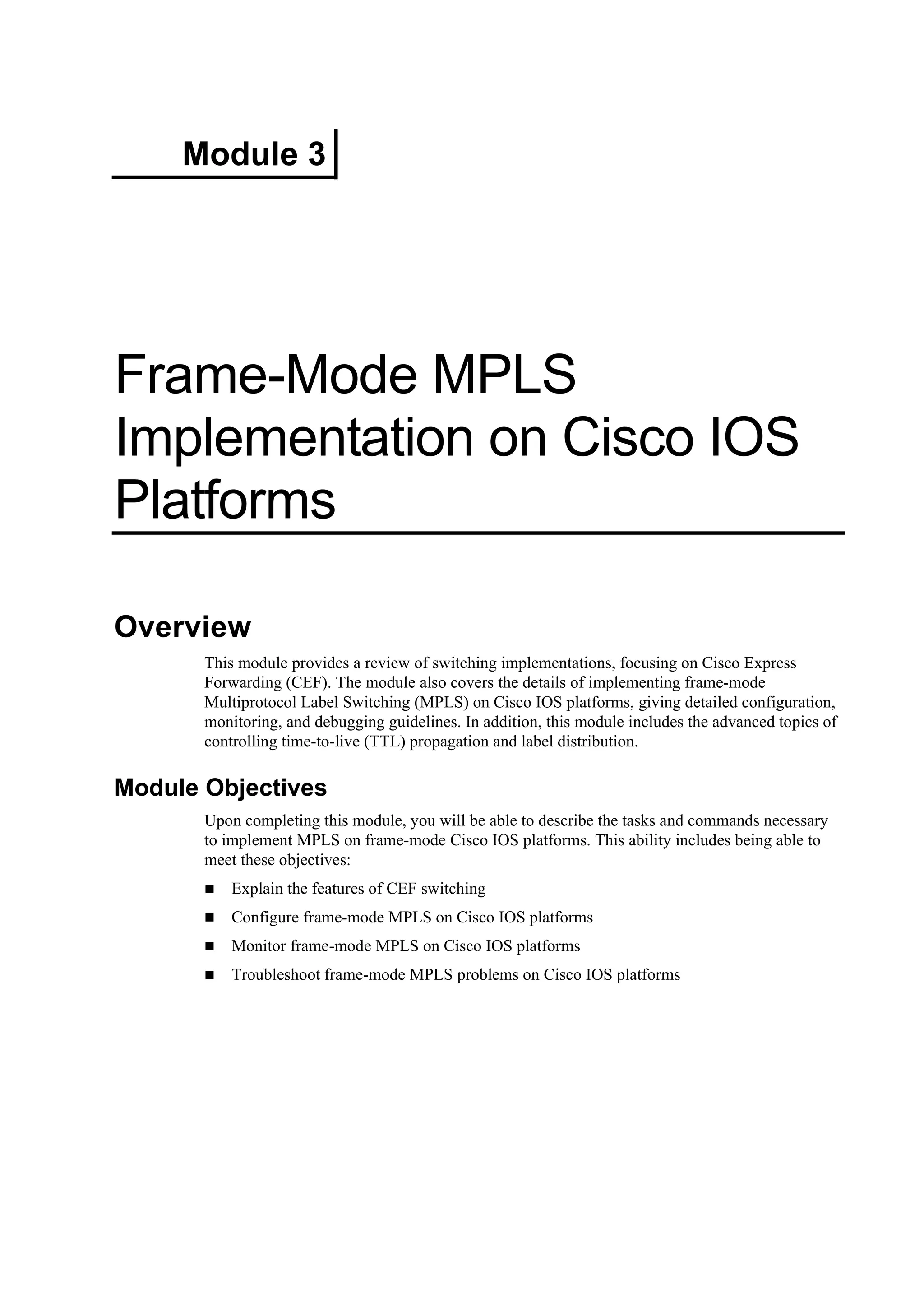
What Are Cisco IOS Platform-Switching Mechanisms? 3-4
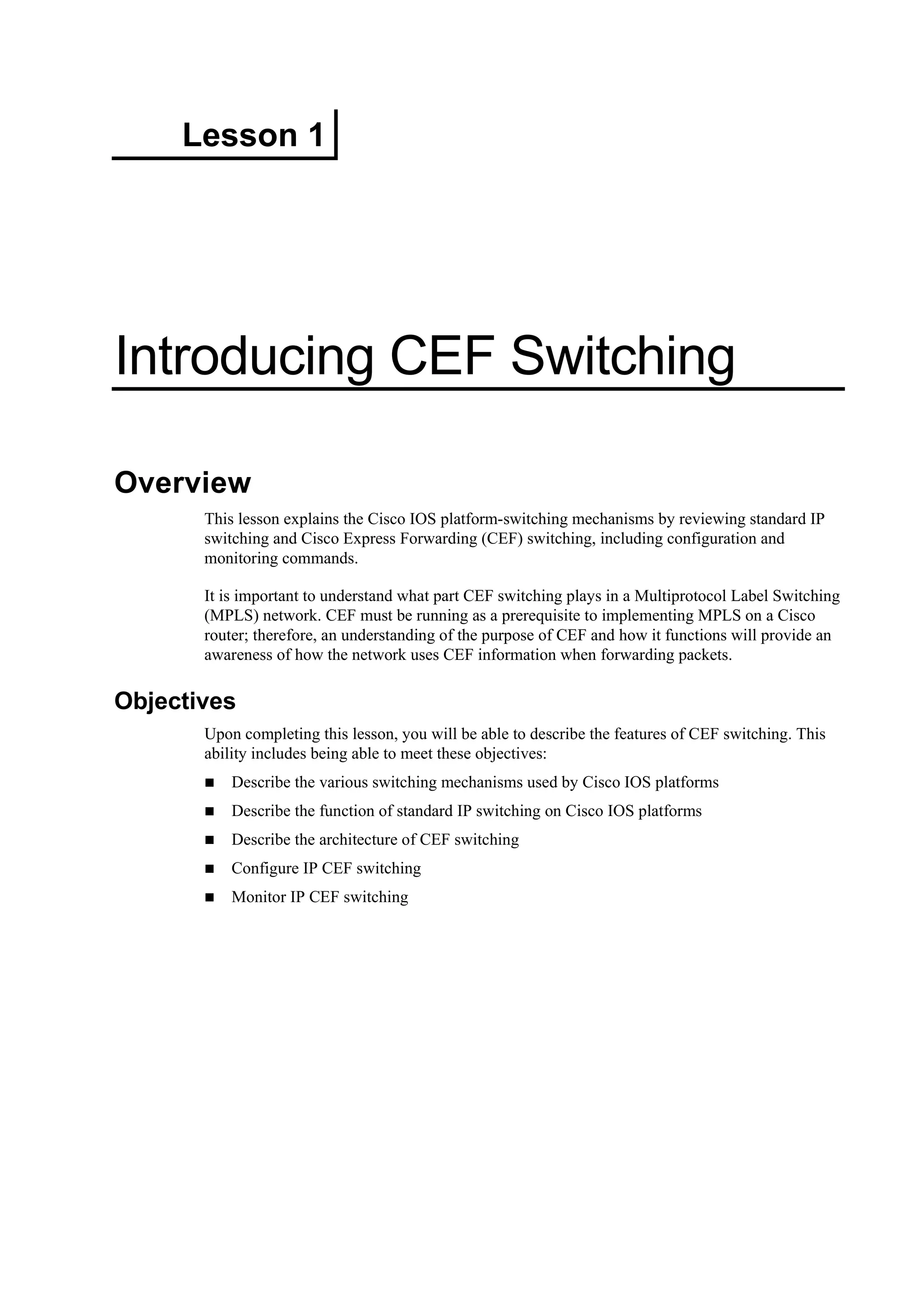
Using Standard IP Switching 3-5
Example: Standard IP Switching 3-5
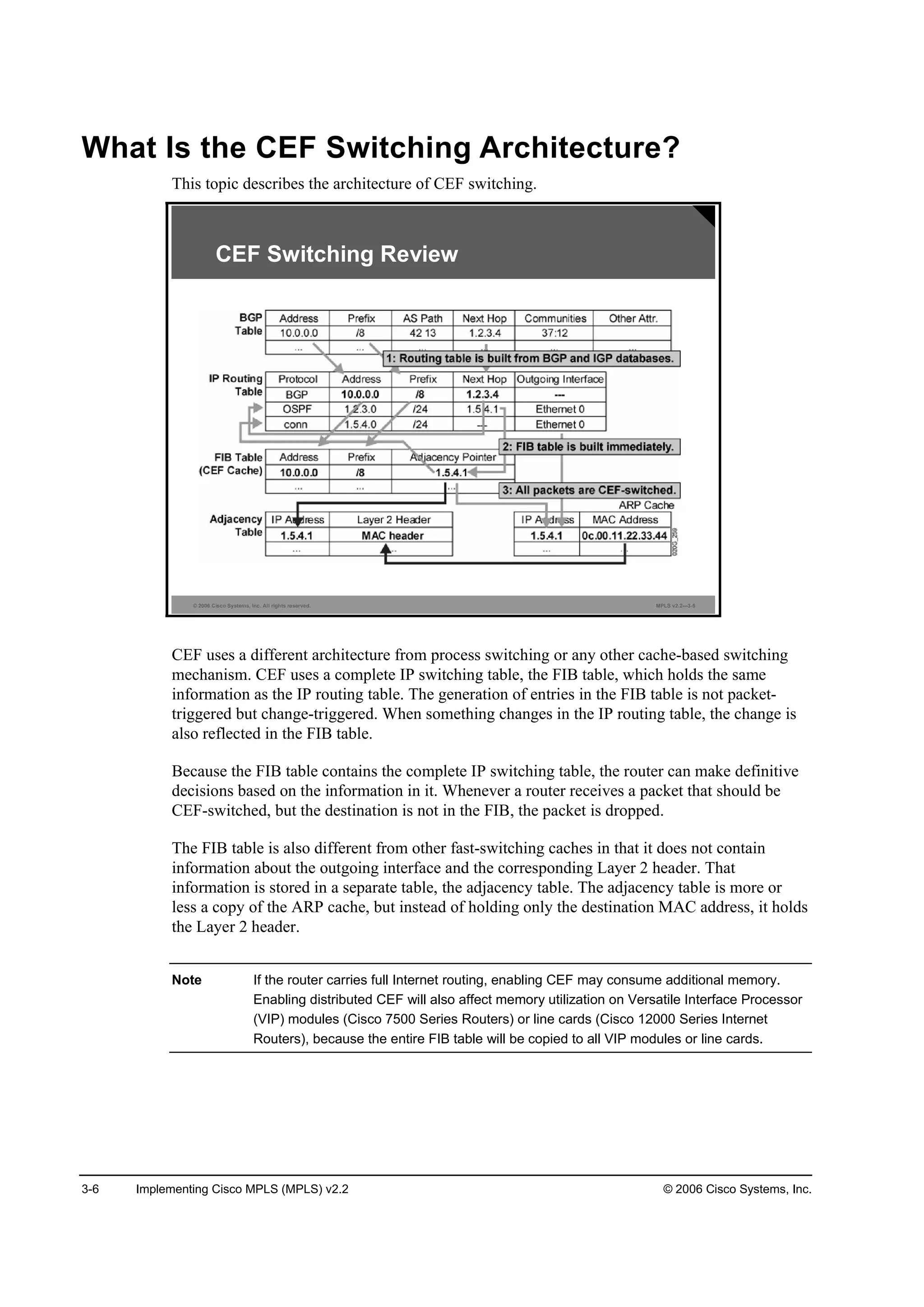
What Is the CEF Switching Architecture? 3-6
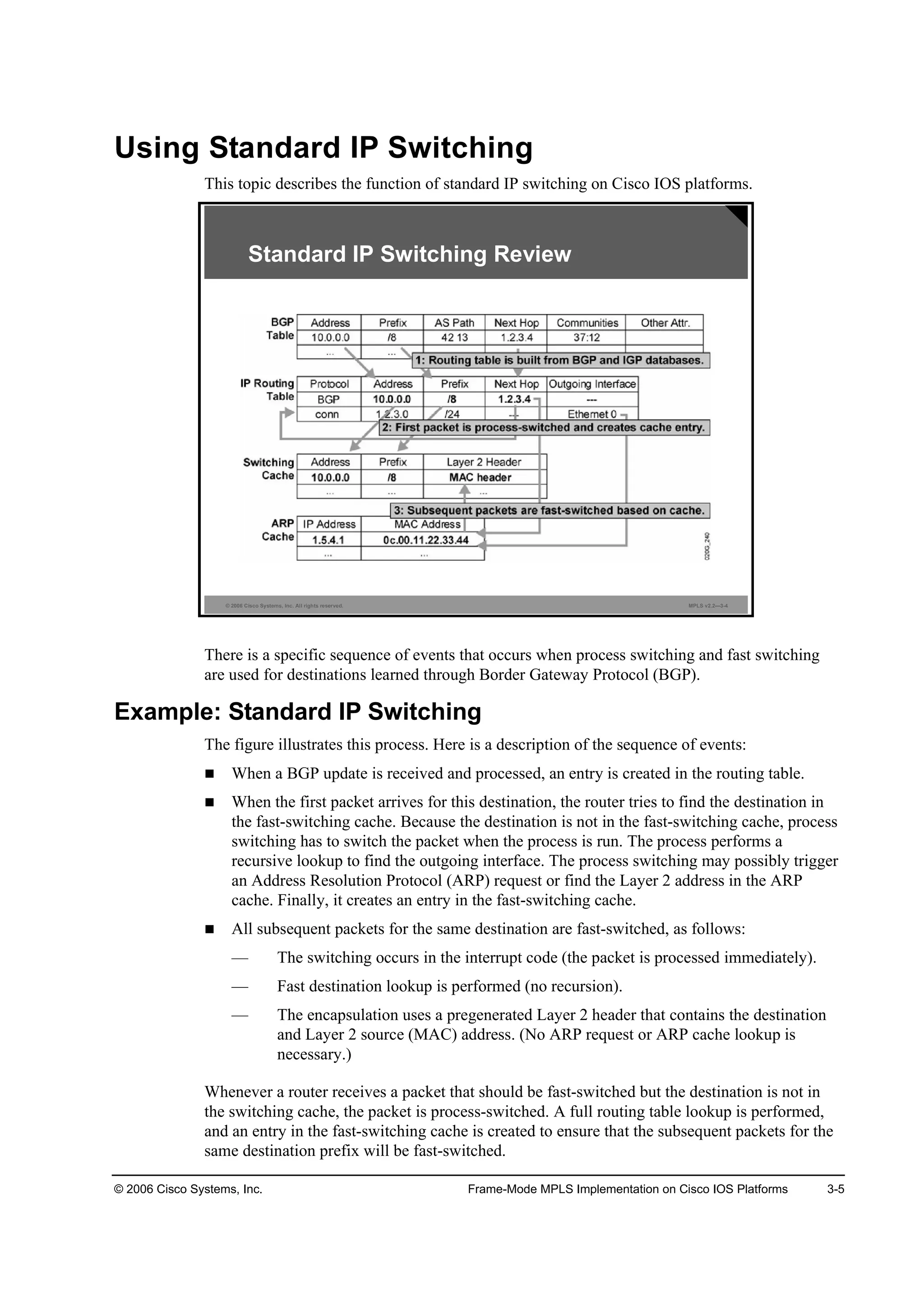
Configuring IP CEF 3-7
ip cef 3-7
Syntax Description 3-7
ip route-cache cef 3-8
Syntax Description 3-8
Defaults 3-8
Monitoring IP CEF 3-9
show ip cef 3-9
Summary 3-11
Configuring Frame-Mode MPLS on Cisco IOS Platforms 3-13
Overview 3-13
Objectives 3-13
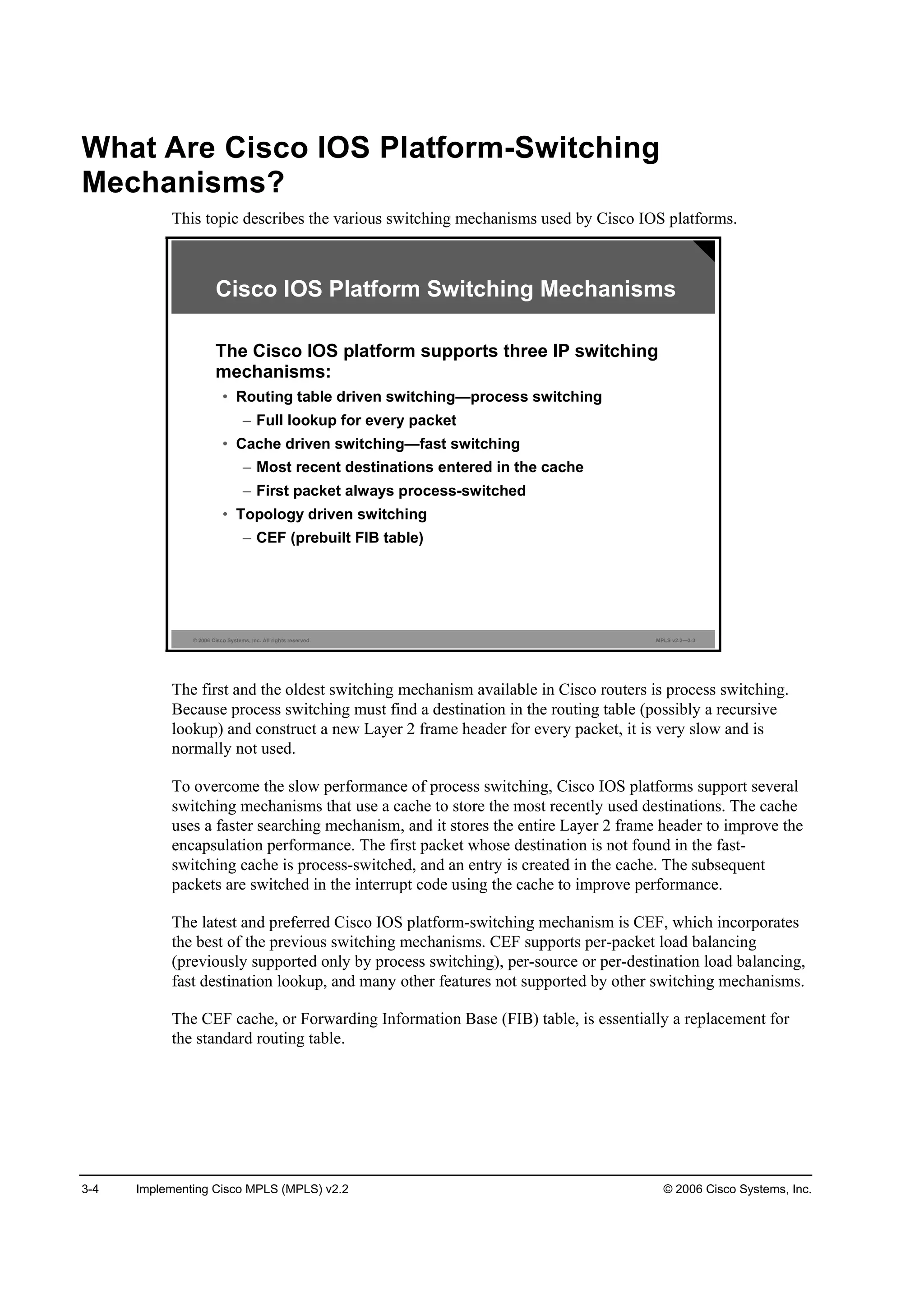
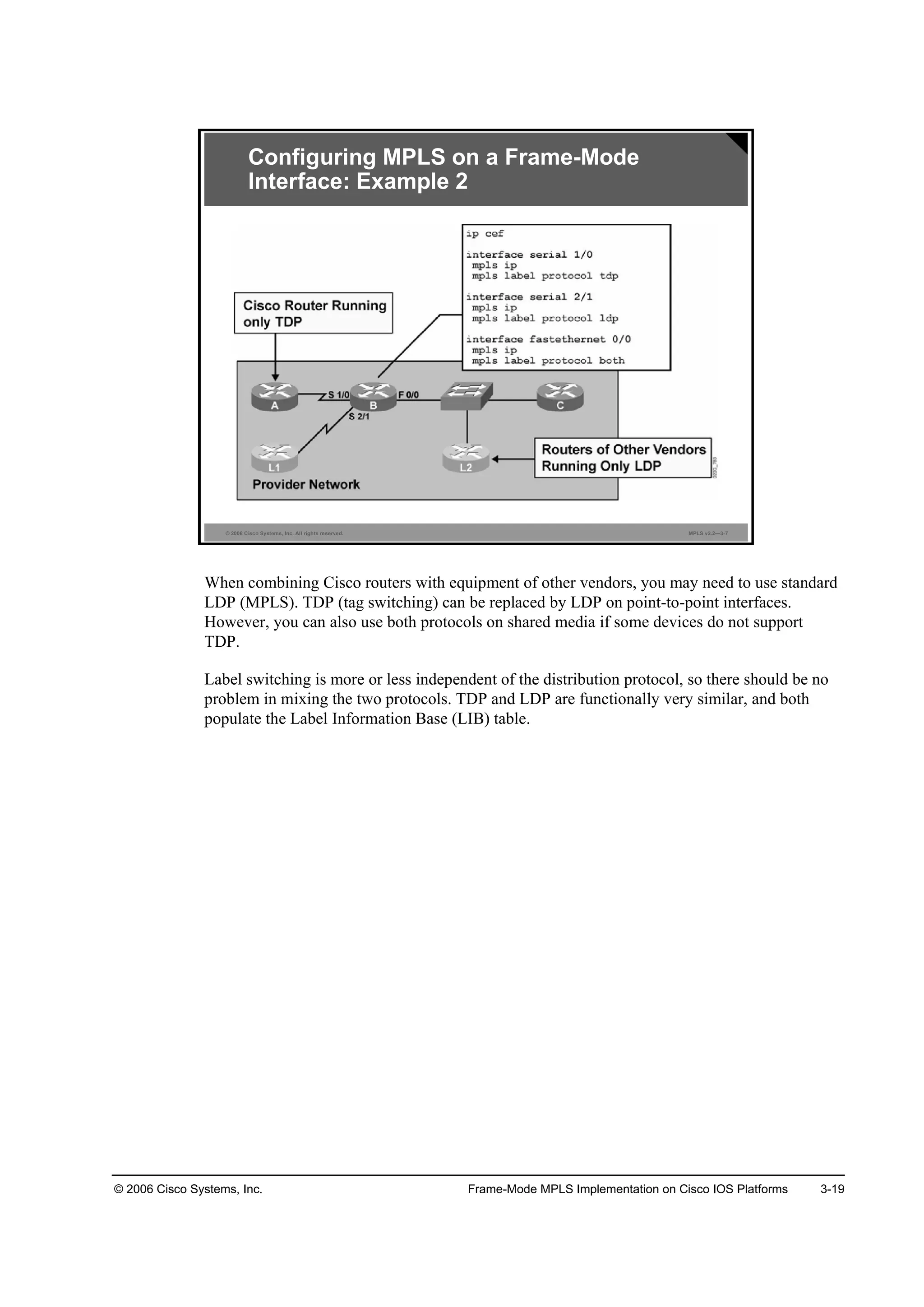
What Are MPLS Configuration Tasks? 3-14
Configuring the MPLS ID on a Router 3-15
mpls ldp router-id 3-15
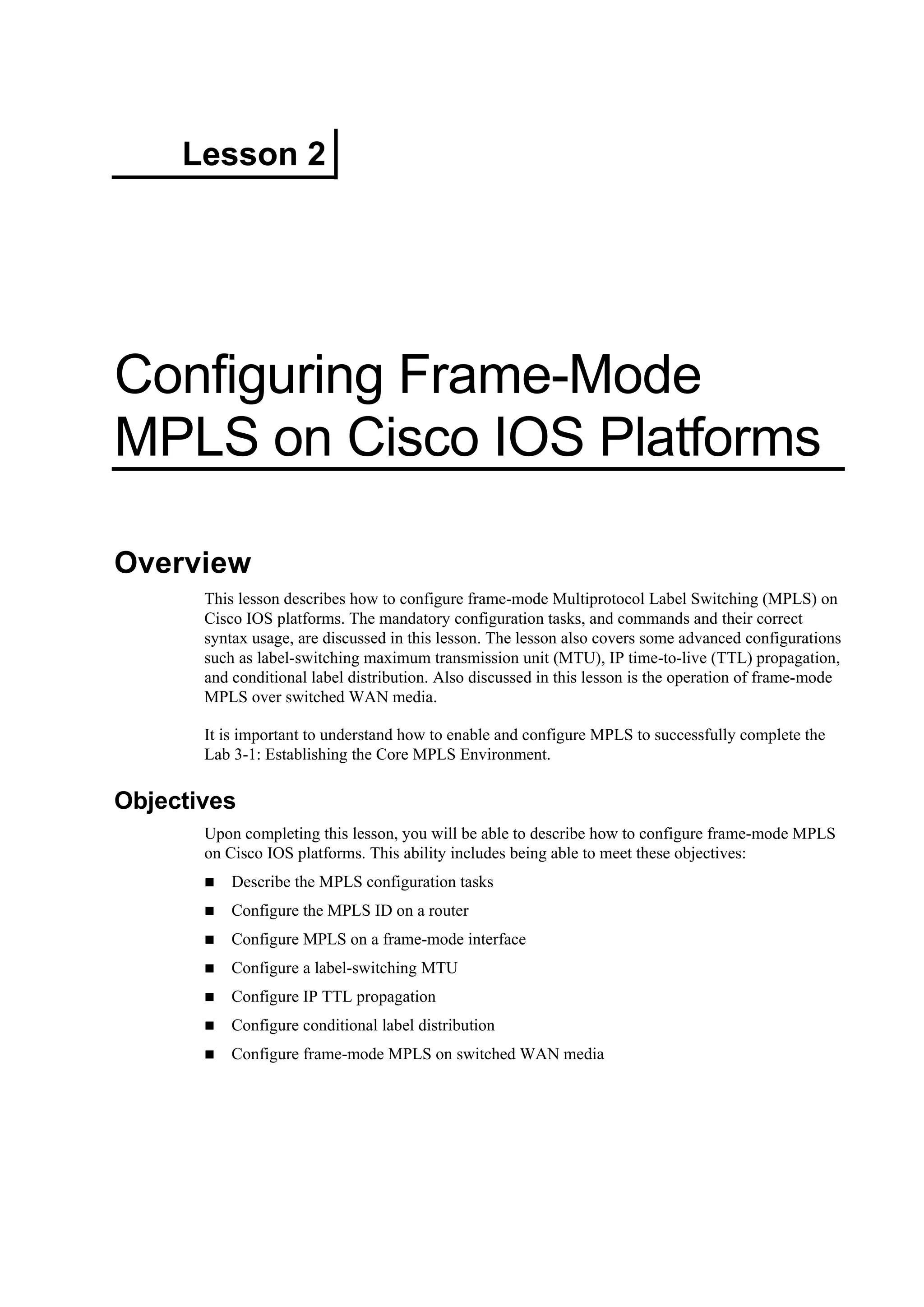
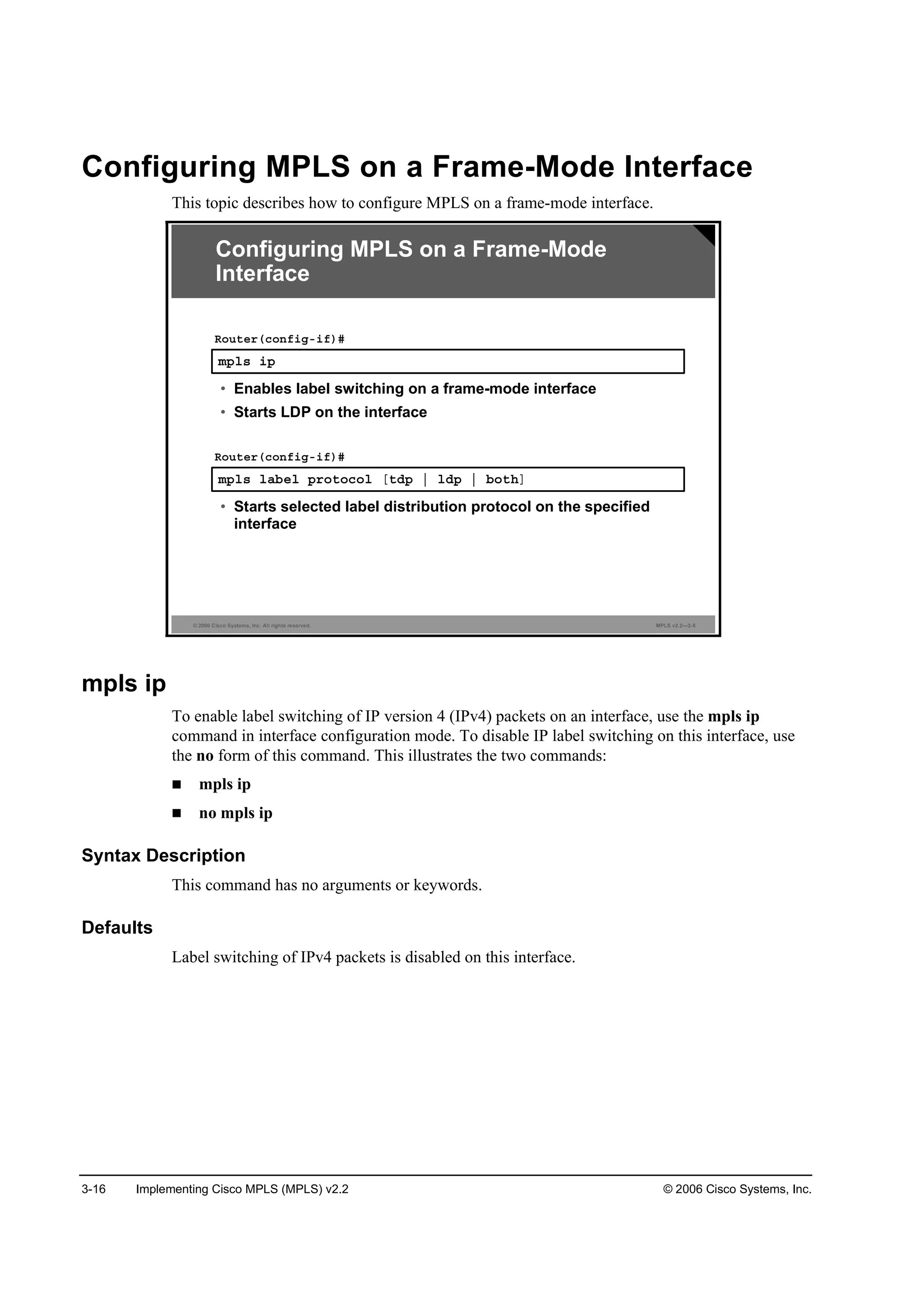
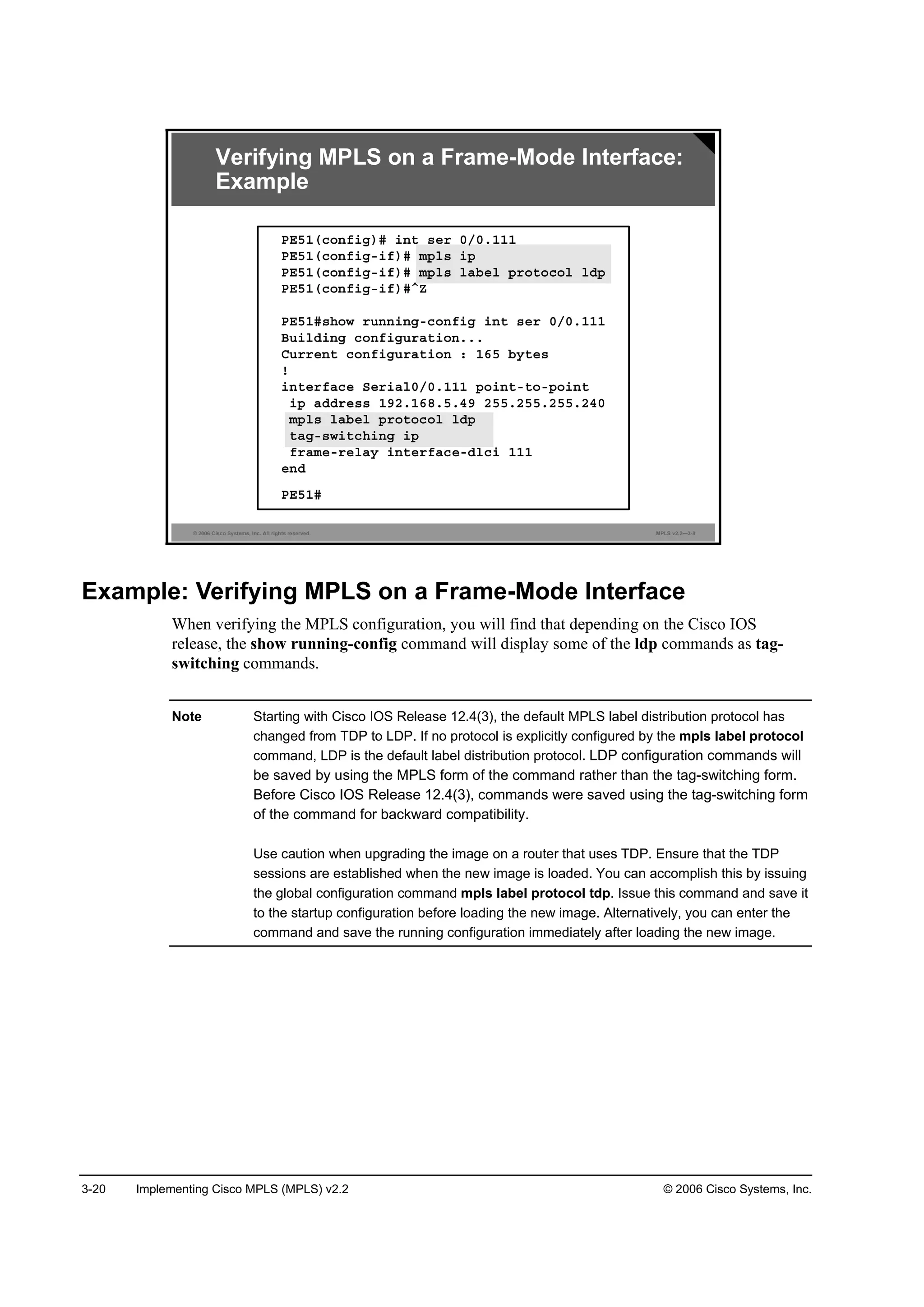
Configuring MPLS on a Frame-Mode Interface 3-16
mpls ip 3-16
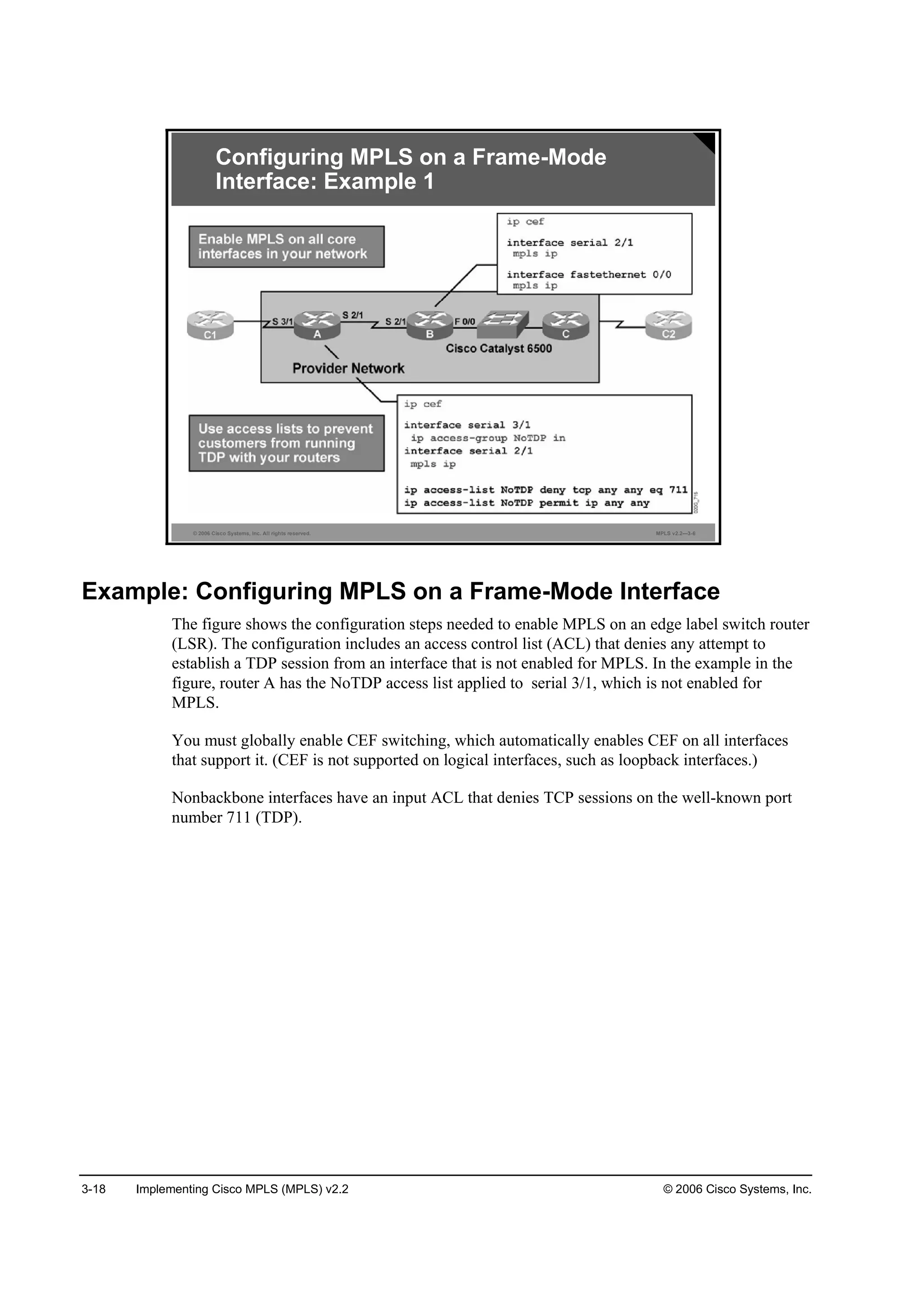
mpls label protocol [tdp | ldp | both] 3-17](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-5-2048.jpg)



![1-8 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
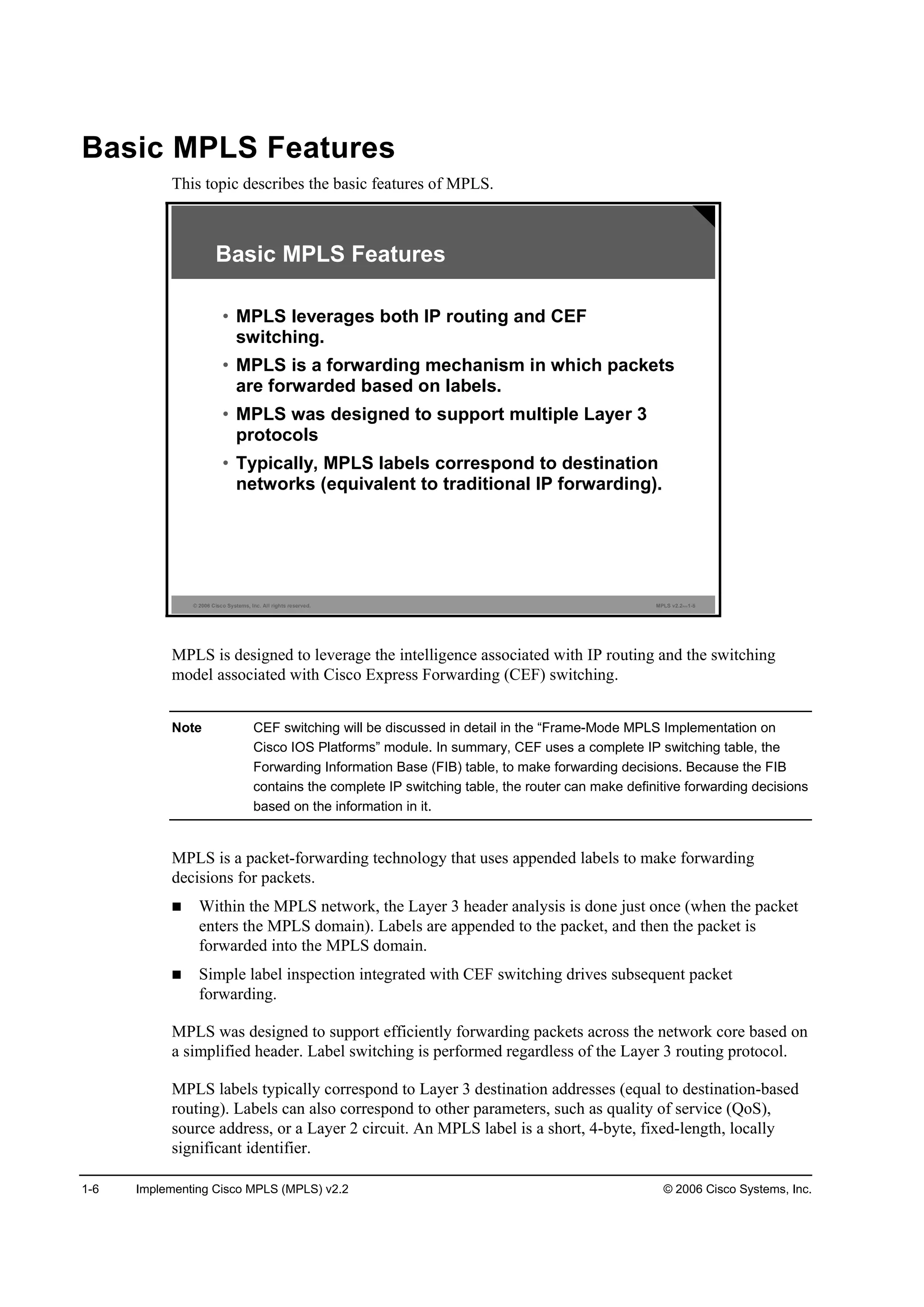
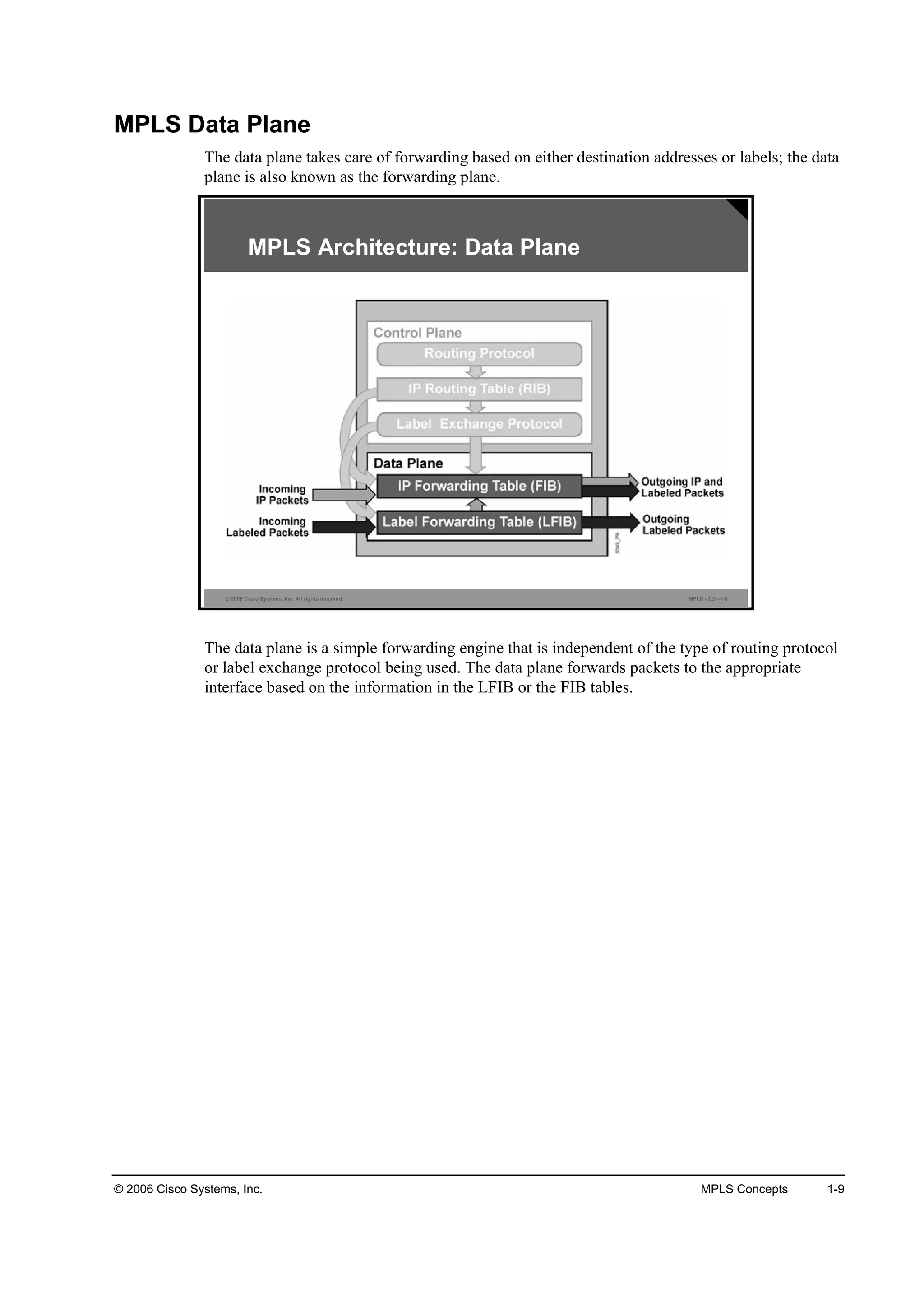
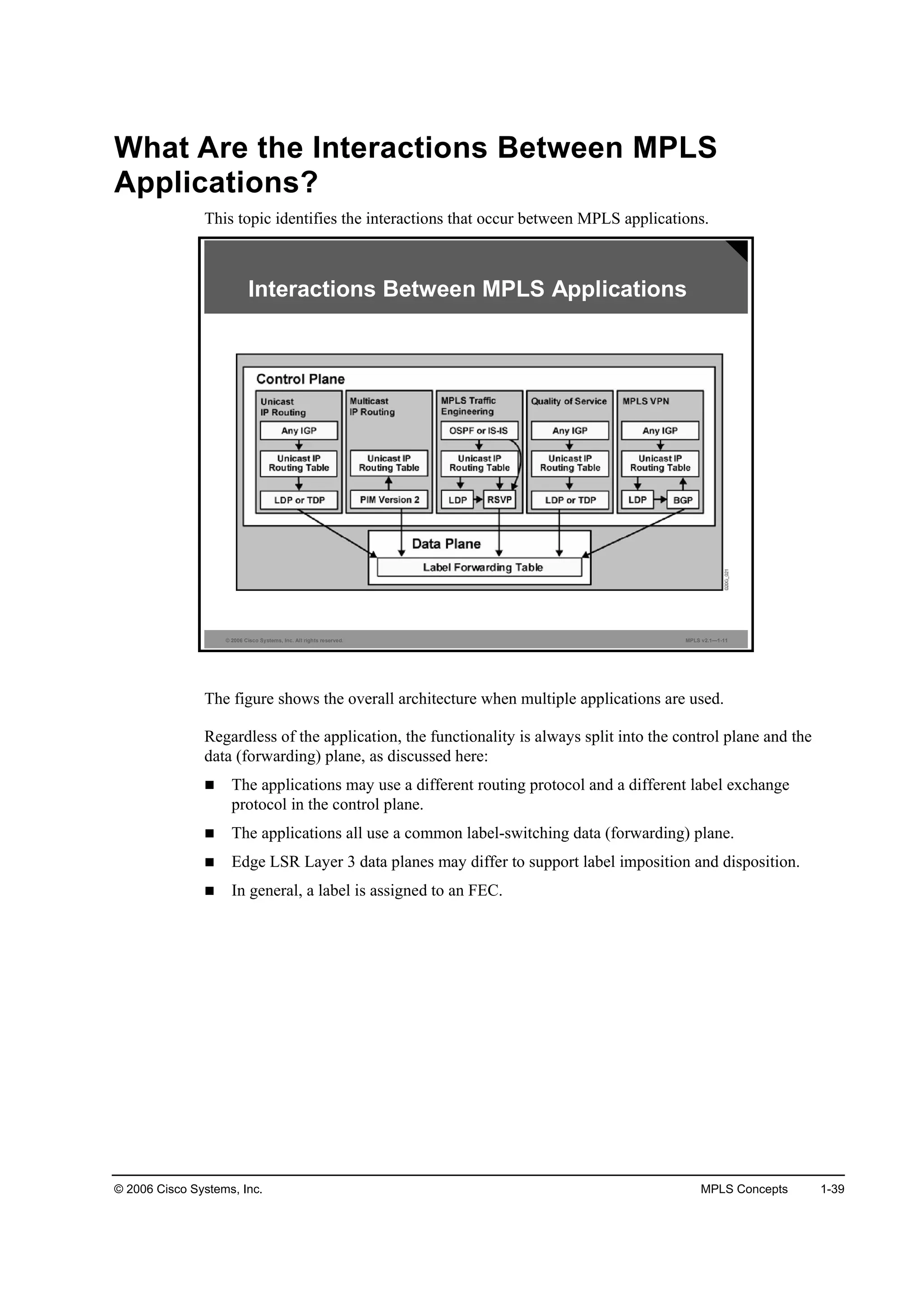
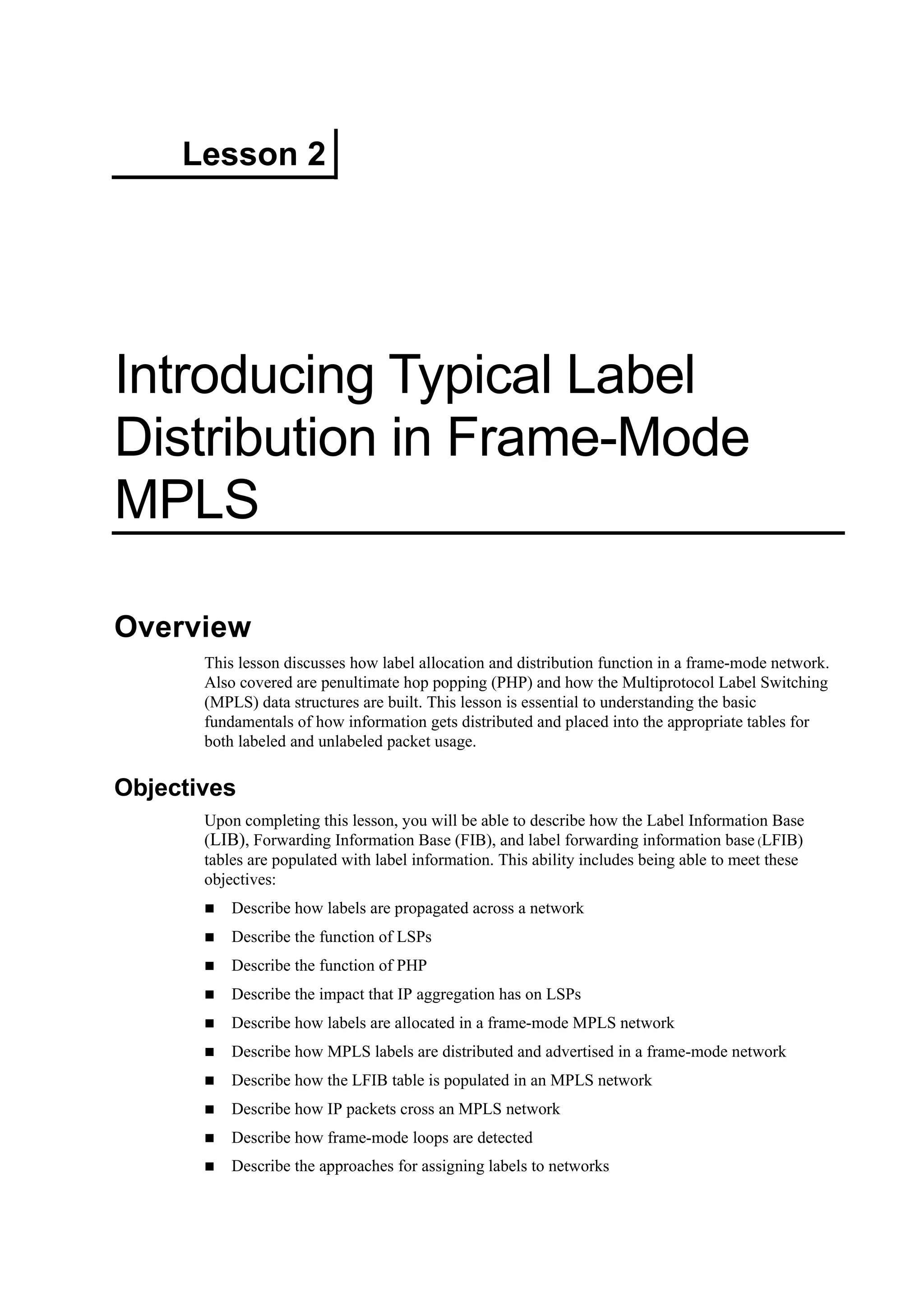
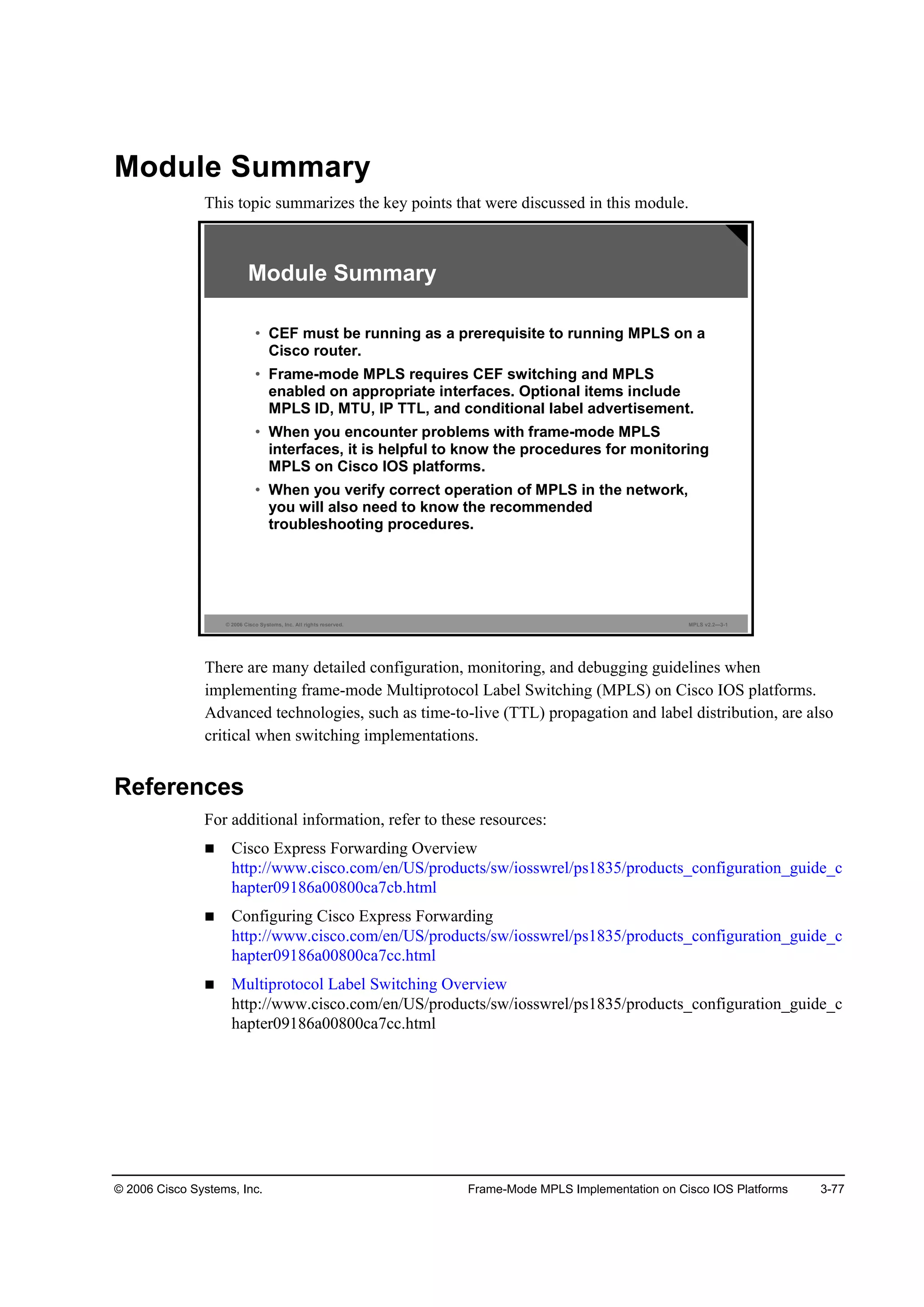
What Are the MPLS Architecture Components?
MPLS consists of these two major components:
Control plane
Data plane
MPLS Control Plane
The control plane takes care of the routing information exchange and the label exchange
between adjacent devices.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—1-7
MPLS Architecture: Control Plane
The control plane builds a routing table (Routing Information Base [RIB]) based on the routing
protocol. Various routing protocols, such as Open Shortest Path First (OSPF), Interior Gateway
Routing Protocol (IGRP), Enhanced Interior Gateway Routing Protocol (EIGRP), Intermediate
System-to-Intermediate System (IS-IS), Routing Information Protocol (RIP), and Border
Gateway Protocol (BGP), can be used in the control plane for managing Layer 3 routing.
The control plane uses a label exchange protocol to create and maintain labels internally, and to
exchange these labels with other devices. The label exchange protocol binds labels to networks
learned via a routing protocol. Label exchange protocols include MPLS Label Distribution
Protocol (LDP), the older Cisco Tag Distribution Protocol (TDP), and BGP (used by MPLS
VPN). Resource Reservation Protocol (RSVP) is used by MPLS TE to accomplish label
exchange.
The control plane also builds two forwarding tables, a FIB from the information in the RIB, and
a label forwarding information base (LFIB) table based on the label exchange protocol and the
RIB. The LFIB table includes label values and associations with the outgoing interface for
every network prefix.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-29-2048.jpg)


![© 2006 Cisco Systems, Inc. MPLS Concepts 1-33
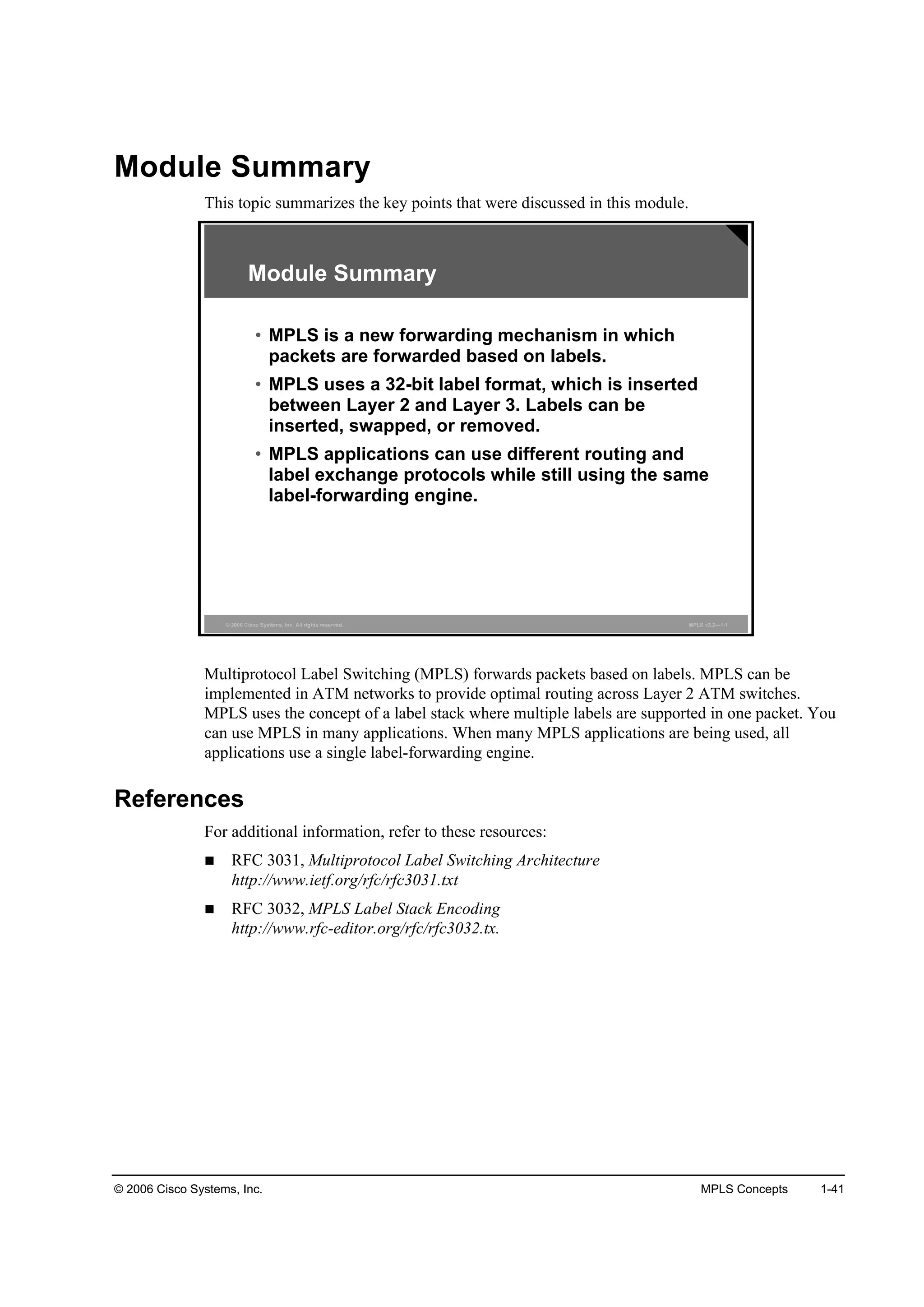
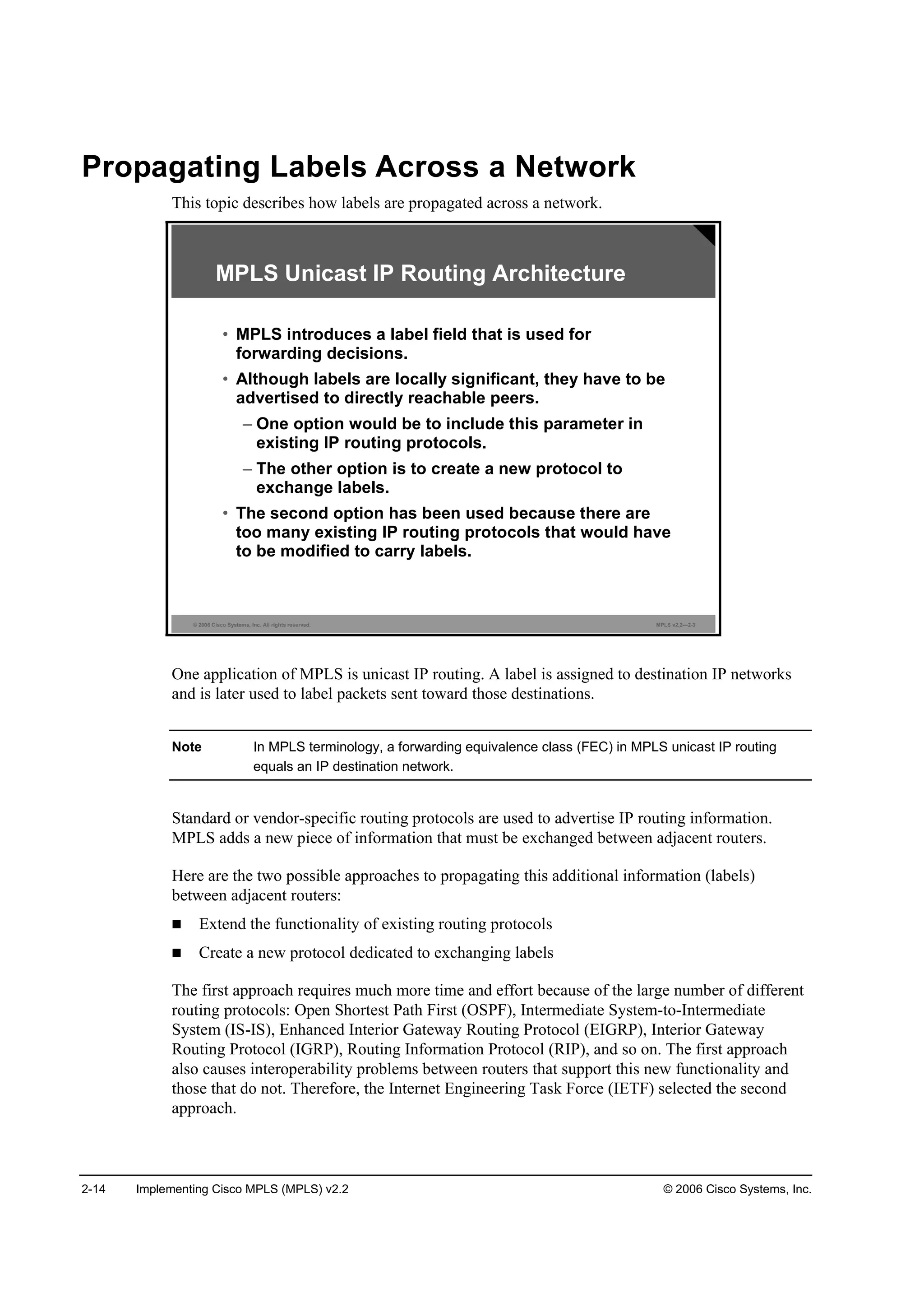
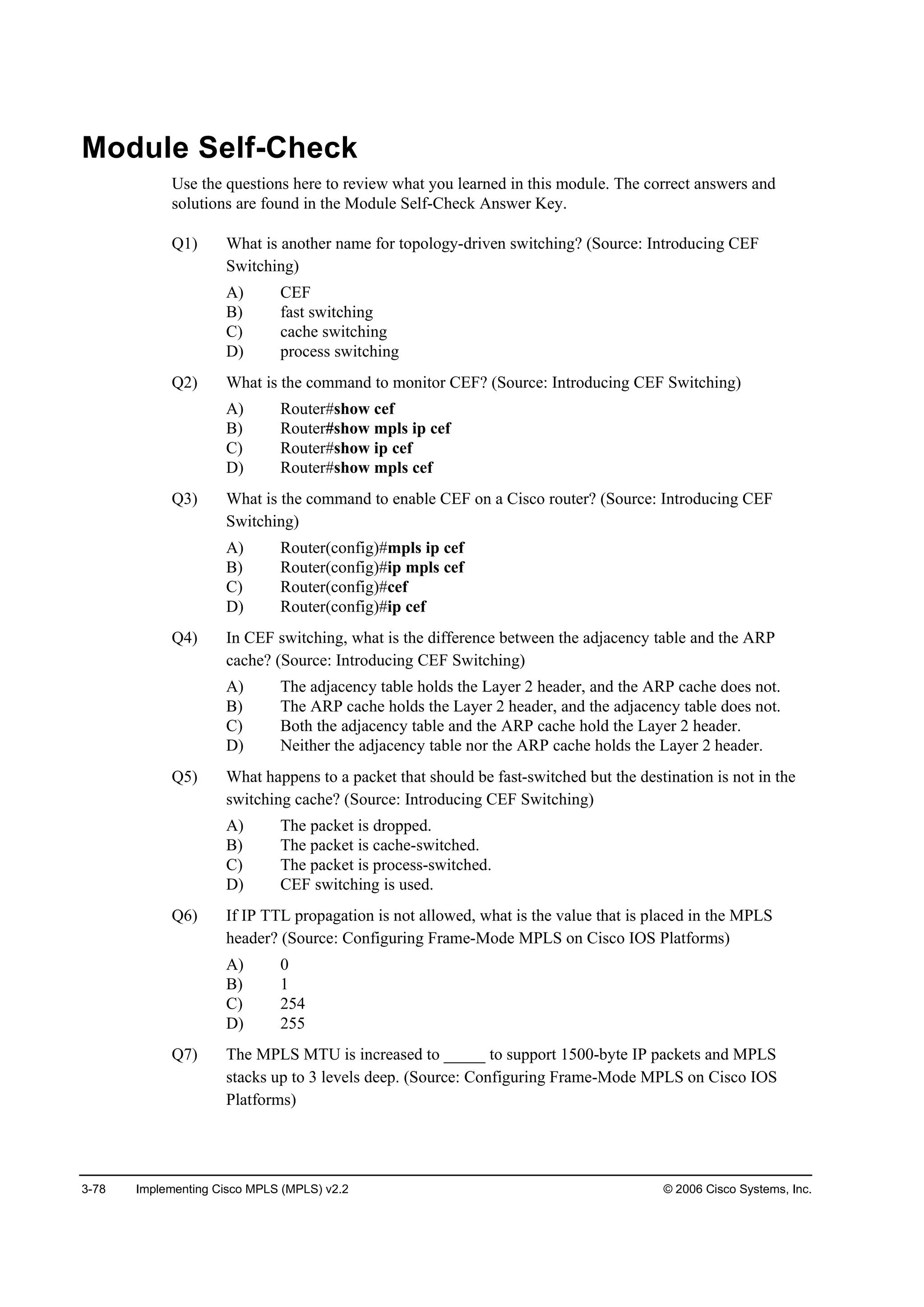
What Are MPLS VPNs?
This topic describes MPLS use in VPNs.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.1—1-6
MPLS VPNs
• MPLS VPNs are highly scaleable and support IP services
such as:
– Multicast
– Quality of QoS
– Telephony support within a VPN
– Centralized services including content and web hosting to a VPN
• Networks are learned via an IGP from a customer or via BGP
from other MPLS backbone routers.
• Labels are propagated via MP-BGP. Two labels are used:
– The top label points to the egress router.
– The second label identifies the outgoing interface on
the egress router or a routing table where a routing lookup is
performed.
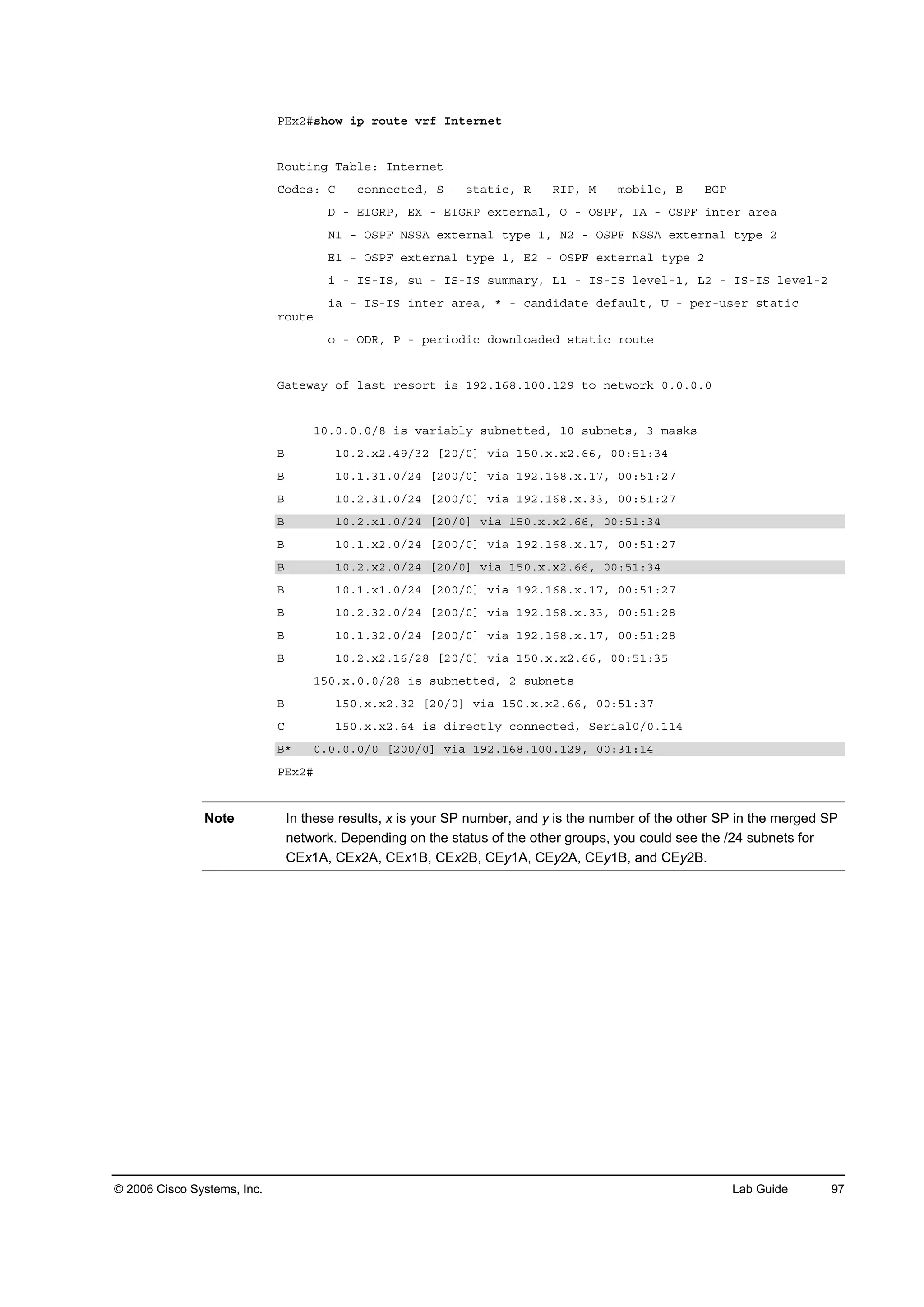
• FEC is equivalent to a VPN site descriptor or VPN routing table.
MPLS enables highly scaleable VPN services to be supported. For each MPLS VPN user, the
network appears to function as a private IP backbone over which the user can reach other sites
within the VPN organization, but not the sites of any other VPN organization. MPLS VPNs are
a common application for service providers. Building VPNs in Layer 3 allows delivery of
targeted services to a group of users represented by a VPN.
MPLS VPNs are seen as private intranets, and support IP services such as those listed here:
Multicast
QoS
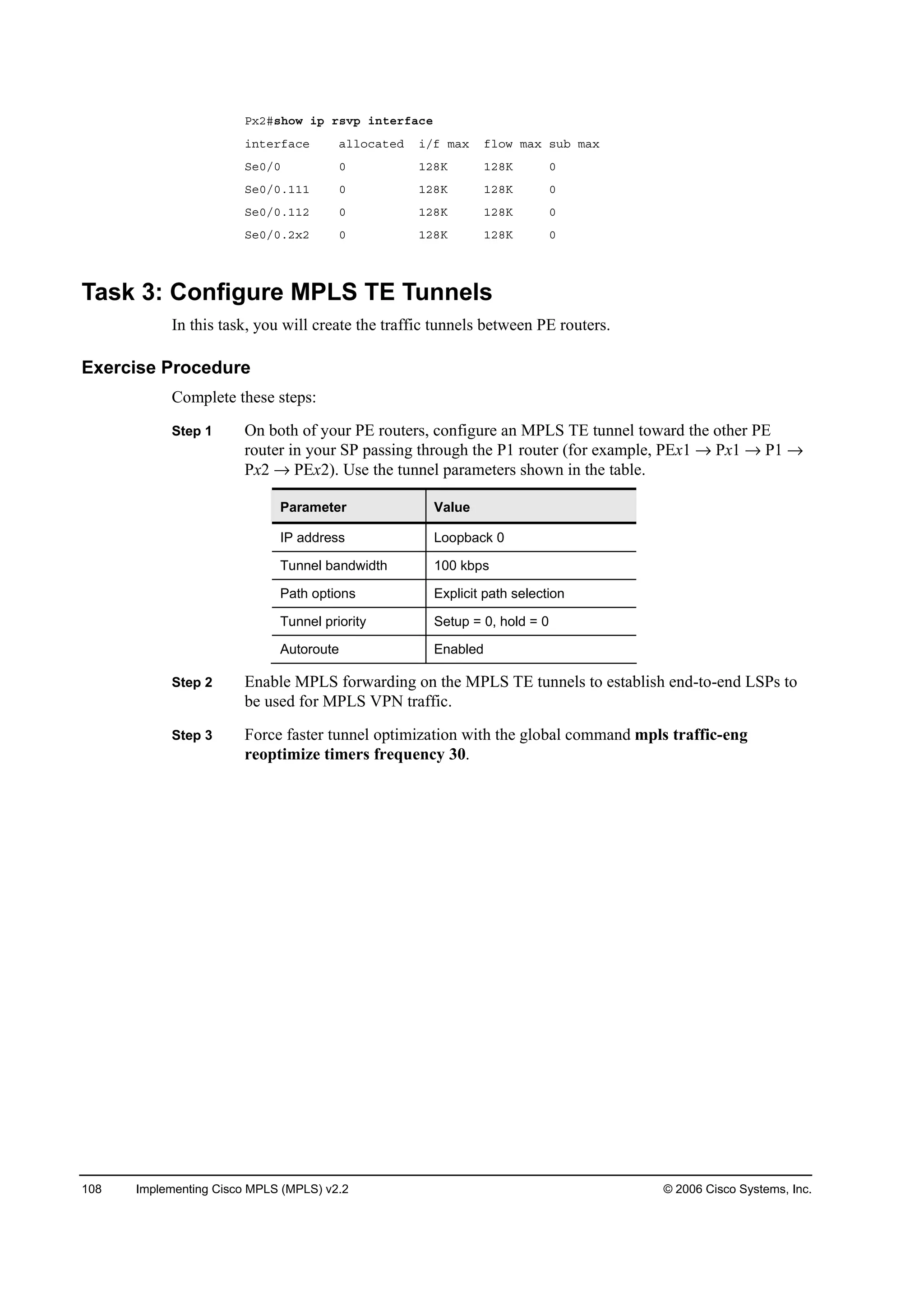
Telephony support within a VPN
Centralized services including content and web hosting to a VPN
Customer networks are learned via an Interior Gateway Protocol (IGP) (Open Shortest Path
First [OSPF], External Border Gateway Protocol [EBGP], Enhanced Interior Gateway Routing
Protocol [EIGRP], Routing Information Protocol version 2 [RIPv2], or static) from a customer,
or via Border Gateway Protocol (BGP) from other MPLS backbone routers.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-54-2048.jpg)

![© 2006 Cisco Systems, Inc. MPLS Concepts 1-35
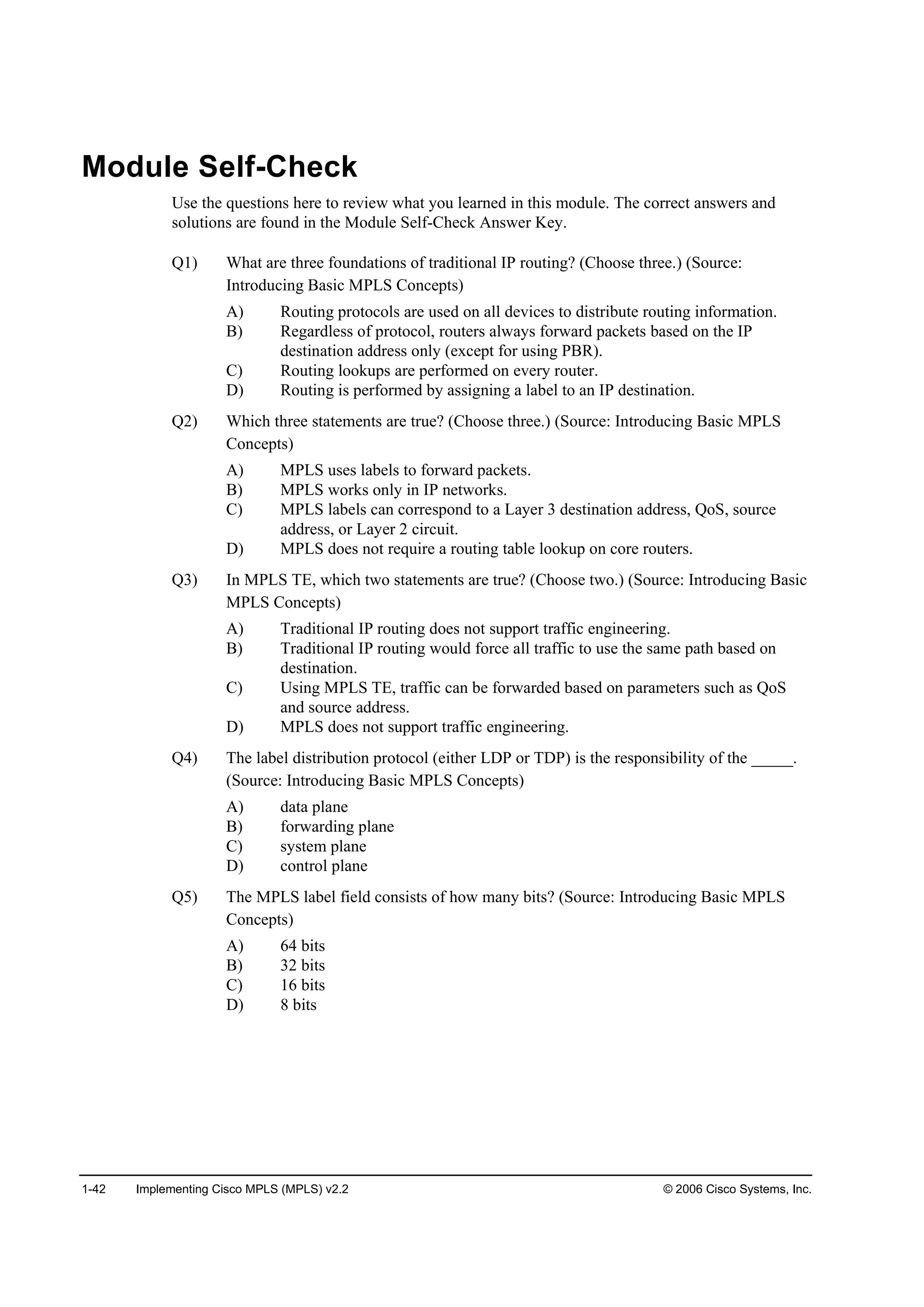
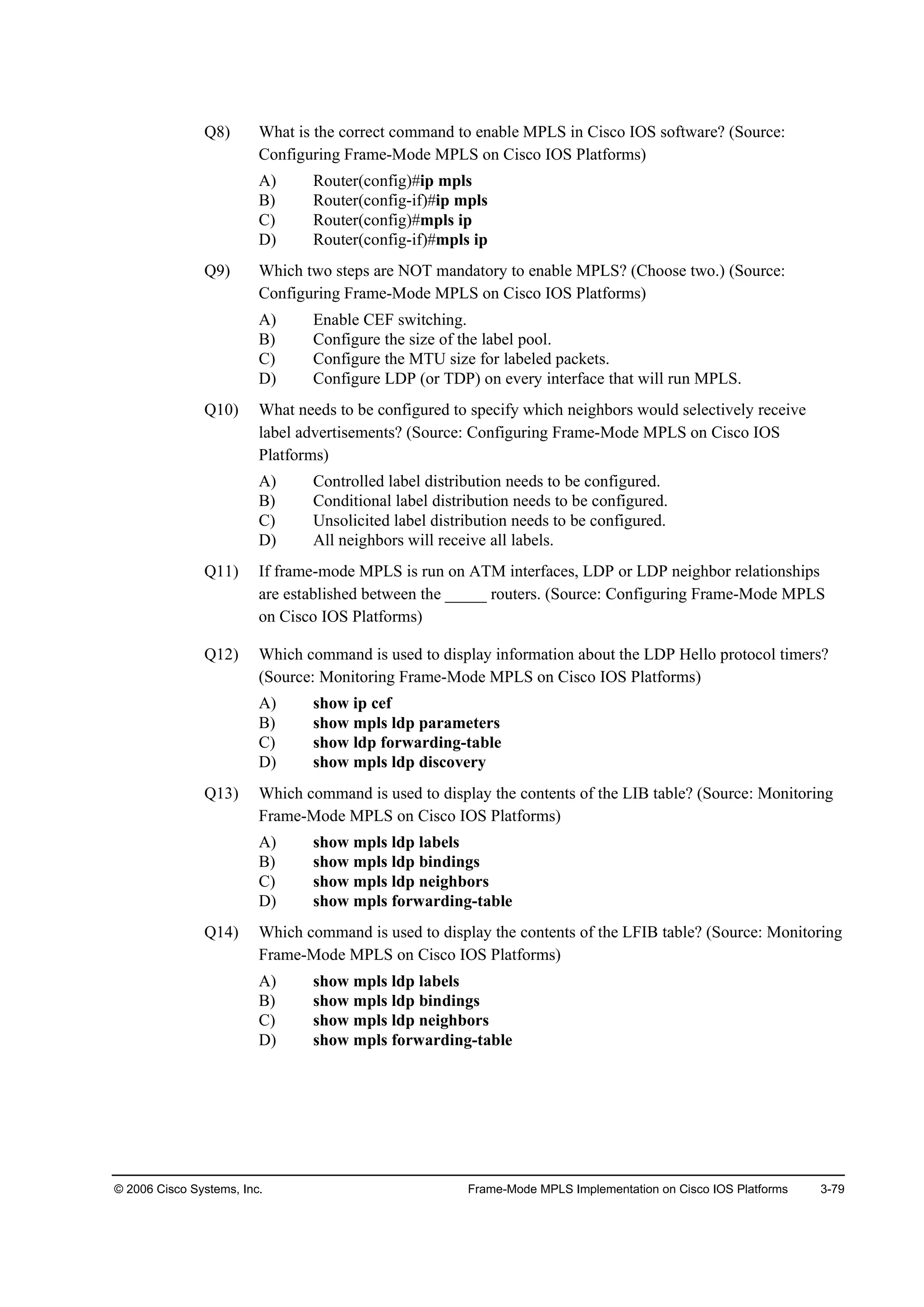
What Is MPLS TE?
This topic describes MPLS use in TE environments.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.1—1-7
MPLS TE
• MPLS TE supports constraints-based routing
• MPLS TE enables the network administrator to
– Control traffic flow in the network
– Reduce congestion in the network
– Make best use of network resources
• MPLS TE requires OSPF or IS-IS with extensions to hold the
entire network topology in their databases.
• OSPF and IS-IS should also have some additional information
about network resources and constraints.
• RSVP is used to establish TE tunnels and to propagate labels.
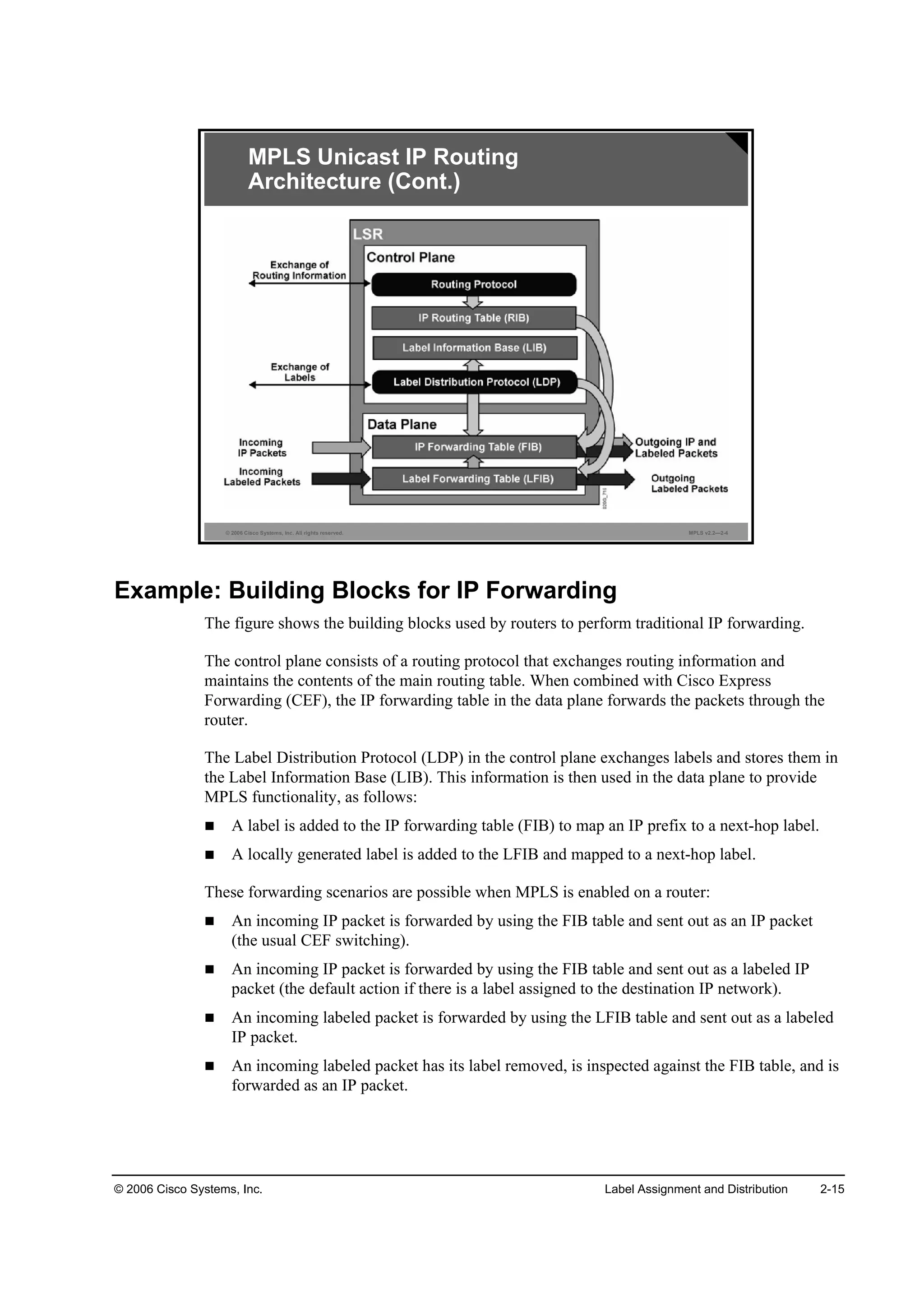
Another application of MPLS is TE. MPLS TE enables an MPLS backbone to replicate and
expand upon the TE capabilities of Layer 2 ATM and Frame Relay networks. MPLS TE
supports constraint-based routing in which the path for a traffic flow is the shortest path that
meets the resource requirements (constraints) of the traffic flow. Factors such as bandwidth
requirements, media requirements, and the priority of one traffic flow versus another can be
taken into account. TE capabilities enable the administrator of a network to accomplish these
goals:
Control traffic flow in the network
Reduce congestion in the network
Make best use of network resources
MPLS TE has these special requirements:
Every LSR must see the entire topology of the network (only OSPF and Intermediate
System-to-Intermediate System [IS-IS] hold the entire topology).
Every LSR needs additional information about links in the network. This information
includes available resources and constraints. OSPF and IS-IS have extensions to propagate
this additional information.
Resource Reservation Protocol (RSVP) is used to establish TE tunnels and to propagate the
labels.
Every edge LSR must be able to create an LSP tunnel on demand. RSVP is used to create an
LSP tunnel and to propagate labels for TE tunnels.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-56-2048.jpg)


![2-10 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
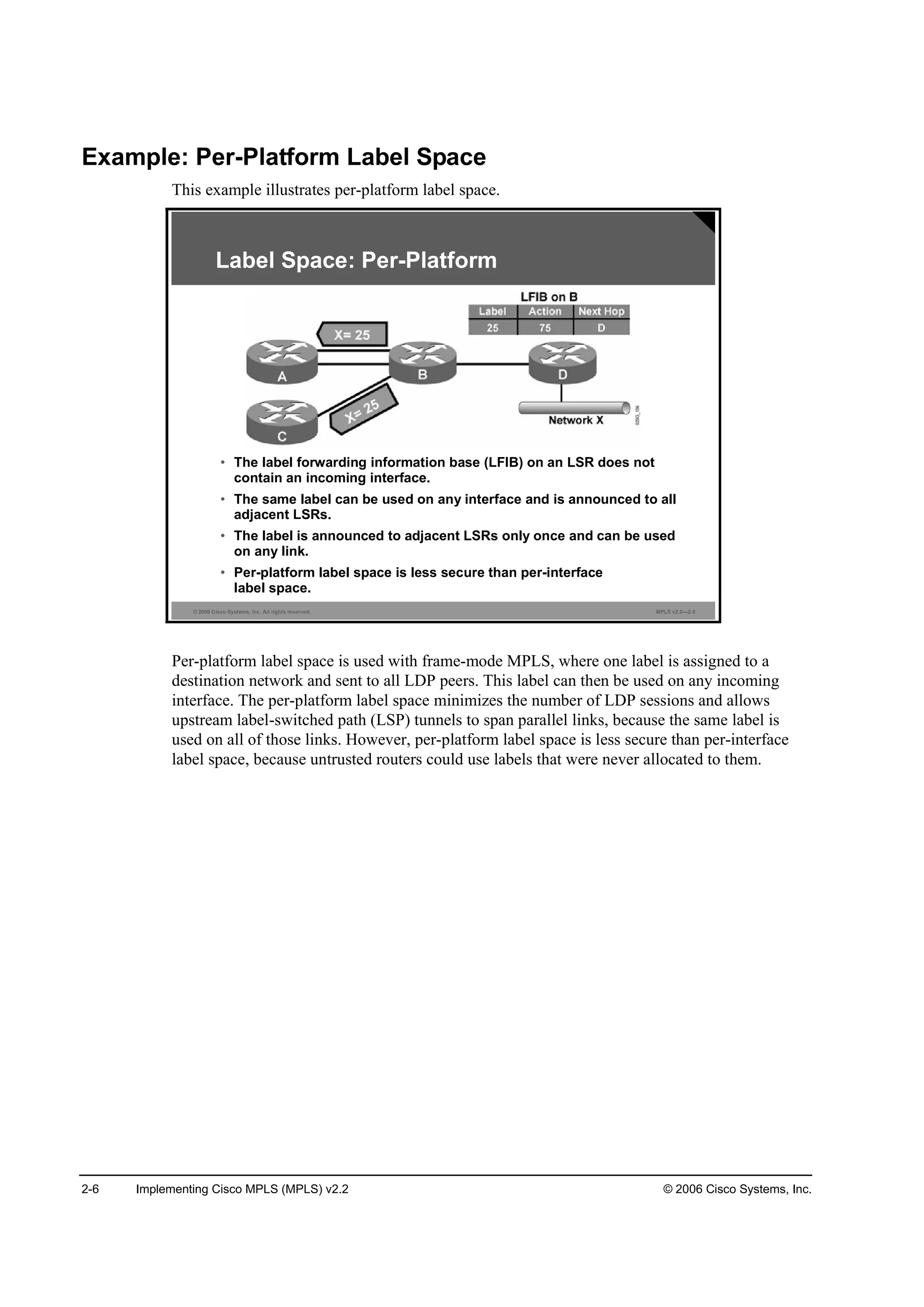
Discovering Nonadjacent Neighbors
This topic describes how LDP discovers nonadjacent neighbors.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—2-9
LDP Discovery of Nonadjacent Neighbors
• LDP neighbor discovery of nonadjacent neighbors
differs from normal discovery only in the
addressing of hello packets:
– Hello packets use unicast IP addresses instead
of multicast addresses.
• When a neighbor is discovered, the mechanism to
establish a session is the same.
If the LSR is more than one hop from its neighbor, it is not directly connected or adjacent to its
neighbor. The LSR can be configured with the mpls ldp neighbor [vrf vrf-name] ip-address
targeted command to send a directed hello message as a unicast UDP packet specifically
addressed to the nonadjacent neighbor LSR. The directed hello message is called an LDP
targeted hello.
The rest of the session negotiation is the same as for adjacent routers. The nondirectly
connected LSR will respond to the hello message by opening a unicast TCP session with the
same destination port number 646, and the two routers begin to establish an LDP session. (If
the path between two LSRs has been traffic engineered and has LDP enabled, the LDP session
between them is called a targeted session.)](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-77-2048.jpg)



![2-50 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
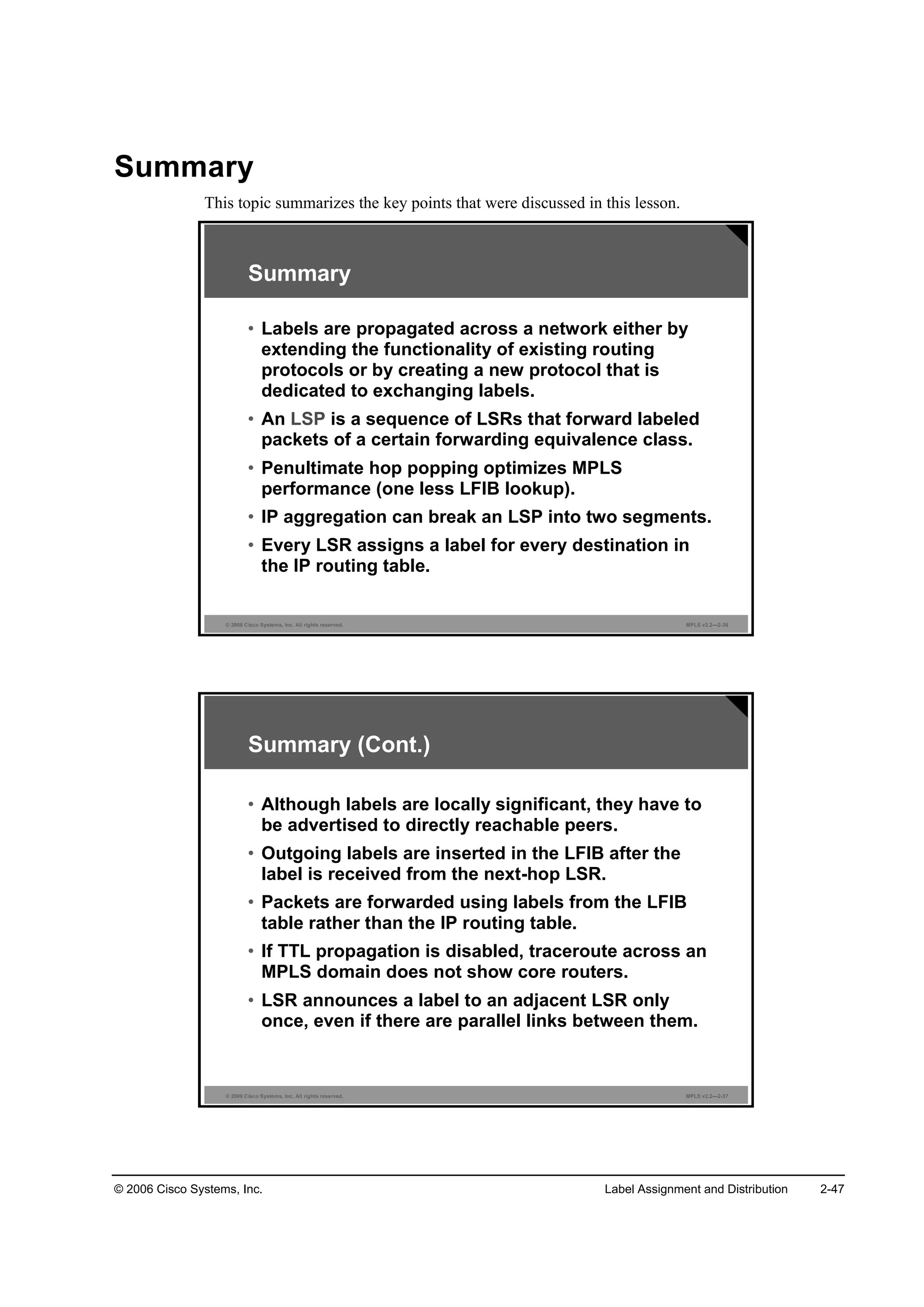
What Is the MPLS Steady-State Operation?
This topic describes an MPLS network steady-state operation.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—2-3
Steady-State Operation Description
• Occurs after the LSRs have exchanged the labels, and the LIB,
LFIB, and FIB data structures are completely populated
MPLS is fully functional when the Interior Gateway Protocol (IGP) and LDP have populated
all the tables, as listed here:
Main IP routing (routing information base [RIB]) table
Label Information Base (LIB) table
Forwarding Information Base (FIB) table
Label forwarding information base (LFIB) table
Although it takes longer for LDP to exchange labels (compared with an IGP), a network can
use the FIB table in the meantime; therefore, there is no routing downtime while LDP
exchanges labels between adjacent LSRs.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-117-2048.jpg)


![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-7
Configuring IP CEF
This topic describes how to configure CEF on Cisco IOS platforms.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-6
·° ˝»ş ĹĽ·¬®·ľ«¬»ĽĂ
᫬»®ř˝±˛ş·ą÷ý
Configuring IP CEF
˛± ·° ®±«¬»ó˝ż˝¸» ˝»ş
᫬»®ř˝±˛ş·ąó·ş÷ý
• Disables CEF switching on an interface
• Usually not needed
• This command starts CEF switching and creates the FIB
table.
• The distributed keyword configures distributed CEF
(running on VIP or line cards).
• All CEF-capable interfaces run CEF switching.
ip cef
To enable CEF on the route processor card, use the ip cef global command in global
configuration mode. To disable CEF, use the no form of this command. Use the appropriate
form of the command:
ip cef [distributed]
no ip cef [distributed]
Syntax Description
distributed (optional): Enables the distributed CEF operation. This option distributes the CEF
information to the line cards. The line cards perform express forwarding.
CEF is disabled by default, excluding these platforms:
CEF is enabled on Cisco 7100 Series Routers.
CEF is enabled on Cisco 7200 Series Routers.
CEF is enabled on Cisco 7500 Series Routers.
CEF is enabled on Cisco 7600 Series Routers, and distributed CEF is enabled on some
Cisco 7600 Series Line Cards.
Distributed CEF is enabled on Cisco 12000 Series Internet Routers.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-146-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-9
Monitoring IP CEF
This topic describes how to monitor CEF on Cisco IOS platforms.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-7
Monitoring IP CEF
᫬»®ý¸±© ·° ˝»ş Ľ»¬ż·´
×Đ ÝŰÚ ©·¬¸ ©·¬˝¸·˛ą řĚżľ´» Ę»®·±˛ ę÷ô ş´żąăđ¨đ
ę ®±«¬»ô đ ®»®»±´Ş»ô 𠫲®»±´Ş»Ľ řđ ±´Ľô 𠲻©÷
ç ´»żŞ»ô ďď ˛±Ľ»ô ďîëëę ľ§¬»ô ç ·˛»®¬ô đ ·˛Şż´·Ľż¬·±˛
đ ´±żĽ ¸ż®·˛ą »´»ł»˛¬ô 𠾧¬»ô đ ®»ş»®»˛˝»
î ÝŰÚ ®»»¬ô đ ®»Ş··±˛ ±ş »¨·¬·˛ą ´»żŞ»
®»ş˝±«˛¬ć ëěí ´»żşô ëěě ˛±Ľ»
߼¶ż˝»˛˝§ Ěżľ´» ¸ż ě żĽ¶ż˝»˛˝·»
đňđňđňđńíîô Ş»®·±˛ đô ®»˝»·Ş»
ďçîňďęčňíňďńíîô Ş»®·±˛ íô ˝ż˝¸»Ľ żĽ¶ż˝»˛˝§ ¬± Í»®·ż´đńđňďđ
đ °ż˝µ»¬ô 𠾧¬»
¬żą ·˛ş±®łż¬·±˛ »¬
´±˝ż´ ¬żąć îč
şż¬ ¬żą ®»©®·¬» ©·¬¸ Í»đńđňďđô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄîčŁ
Ş·ż ďçîňďęčňíňďđô Í»®·ż´đńđňďđô đ Ľ»°»˛Ľ»˛˝·»
˛»¨¬ ¸±° ďçîňďęčňíňďđô Í»®·ż´đńđňďđ
Şż´·Ľ ˝ż˝¸»Ľ żĽ¶ż˝»˛˝§
¬żą ®»©®·¬» ©·¬¸ Í»đńđňďđô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄîčŁ
᫬»®ý¸±© ·° ˝»ş Ľ»¬ż·´
show ip cef
To display unresolved entries in the FIB table or to display a summary of the FIB, use this form
of the show ip cef EXEC command: show ip cef [unresolved | summary].
To display specific entries in the FIB table based on IP address information, use this form of
the show ip cef command in EXEC mode: show ip cef [network [mask [longer-prefix]]]
[detail].
To display specific entries in the FIB table based on interface information, use this form of the
show ip cef command in EXEC mode: show ip cef [type number] [detail].](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-148-2048.jpg)

![3-14 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
What Are MPLS Configuration Tasks?
This topic describes the MPLS configuration tasks.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-3
MPLS Configuration Tasks
Mandatory:
• Enable CEF switching
• Configure LDP on every label-enabled interface
Optional:
• Configure the MPLS ID
• Configure MTU size for labeled packets
• Configure IP TTL propagation
• Configure conditional label advertising
To enable MPLS, you must first enable Cisco Express Forwarding (CEF) switching. Depending
on the Cisco IOS software release, you may need to establish the range for the label pool.
You must enable Label Distribution Protocol (LDP) on the interface by using label switching.
Optionally, the maximum size of labeled packets may be changed.
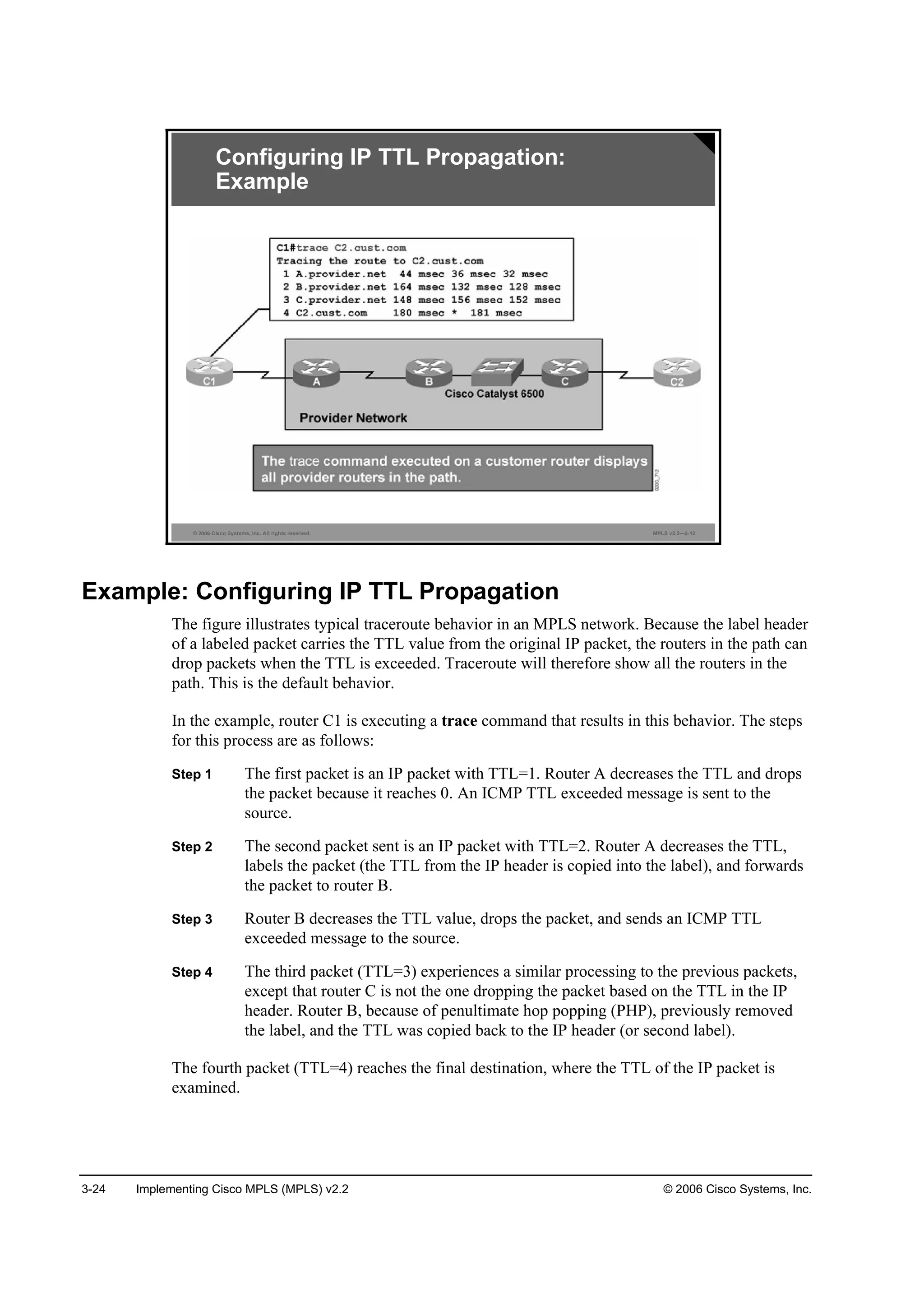
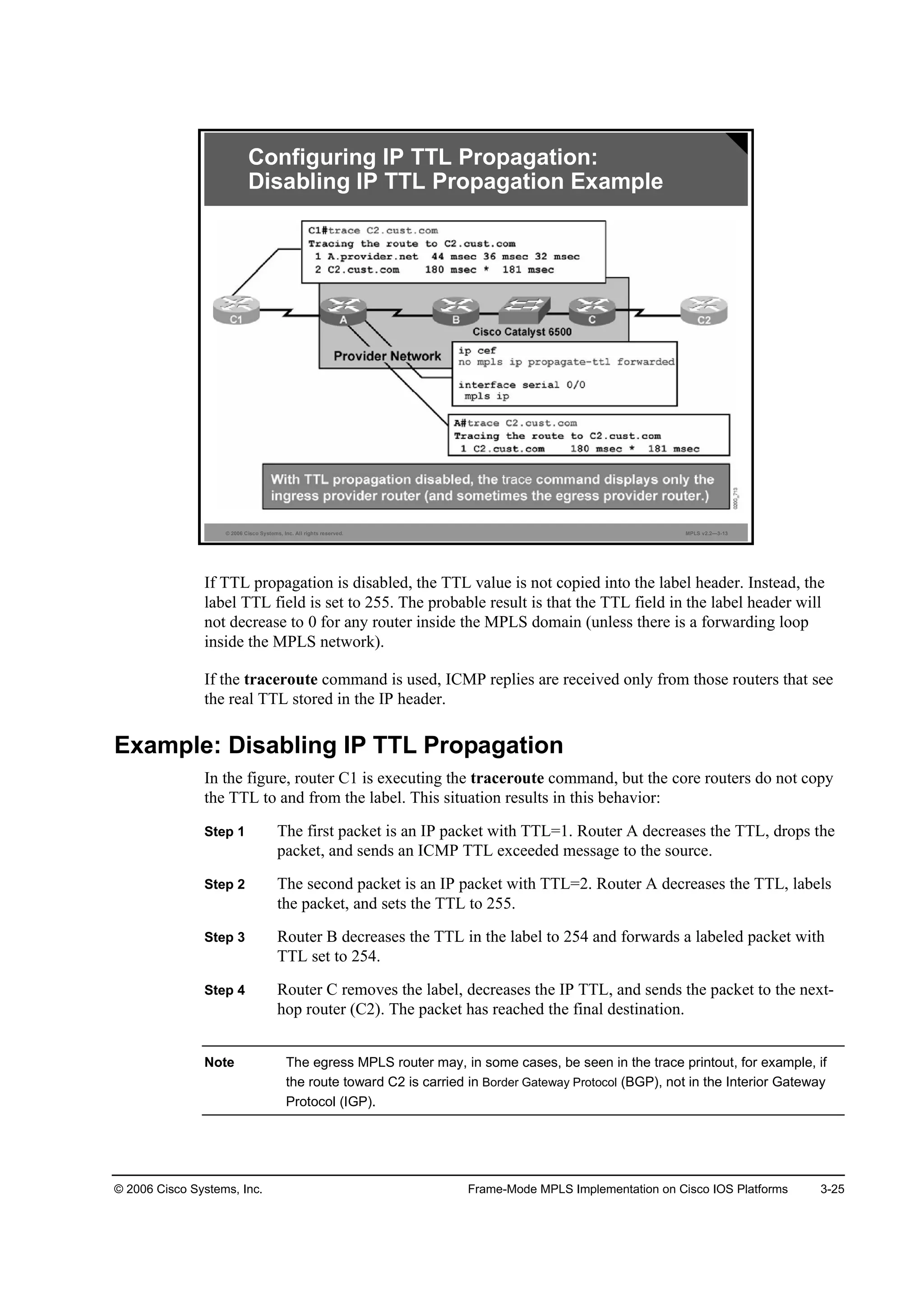
By default, the TTL field is copied from the IP header and placed in the MPLS label when a
packet enters an MPLS network. To prevent core routers from responding with (Internet
Control Message Protocol [ICMP]) TTL exceeded messages, disable TTL propagation. If TTL
propagation is disabled, the value in the TTL field of the label is 255.
Note Ensure that all routers have TTL propagation either enabled or disabled. If TTL is enabled in
some routers and disabled in others, the result may be that a packet leaving the MPLS
domain will have a larger TTL value than when it entered.
By default, a router will generate and propagate labels for all networks that it has in the routing
table. If label switching is required for only a limited number of networks (for example, only
for router loopback addresses), configure conditional label advertising.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-153-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-15
Configuring the MPLS ID on a Router
This topic describes how to configure the MPLS identifier (MPLS ID) on a router.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-4
ł°´ ´Ľ° ®±«¬»®ó·Ľ ·˛¬»®şż˝» Ĺş±®˝»Ă
᫬»®ř˝±˛ş·ą÷ý
Specifies a preferred interface for determining the
LDP router ID:
• Parameters
– interface: Causes the IP address of the specified interface
to be used as the LDP router ID, provided that the interface
is operational
– force: Alters the behavior of the
command to force the use of the named interface as the
LDP router ID
Configuring the MPLS ID on a Router
mpls ldp router-id
To specify a preferred interface for determining the LDP router ID, use the mpls ldp router-id
command in global configuration mode. To remove the preferred interface for determining the
LDP router ID, use the no form of this command. This illustrates the two commands:
mpls ldp router-id interface [force]
no mpls ldp router-id
This table describes the parameters for the mpls idp router-id command.
mpls idp router-id Syntax Description
Parameter Description
·˛¬»®şż˝» Causes the IP address of the specified interface to be used as
the LDP router ID, provided that the interface is operational
ş±®˝» (Optional) Alters the behavior of the mpls ldp router-id
command to force the use of the named interface as the LDP
router ID
Defaults
The mpls ldp router-id command is disabled.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-154-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-17
mpls label protocol [tdp | ldp | both]
To select the label distribution protocol to be used on an interface, use the mpls label protocol
command in interface configuration mode. To revert to the default label distribution protocol,
use the no form of this command. This illustrates the two commands:
mpls label protocol protocol
no mpls label protocol protocol
This table describes the parameters for the mpls label protocol [tdp | ldp | both] command.
mpls label protocol [tdp | ldp | both] Syntax Description
Parameter Description
¬Ľ° Enables Tag Distribution Protocol (TDP) on an interface
´Ľ° Enables LDP on an interface
ľ±¬¸ Enables TDP and LDP on an interface
Defaults
TDP has been the default label distribution protocol. Starting in Cisco IOS Release 12.4(3), the
default MPLS label distribution protocol is LDP.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-156-2048.jpg)
![3-26 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-14
˛± ł°´ ·° °®±°żąż¬»ó¬¬´ Ĺş±®©ż®Ľ»Ľ ¤ ´±˝ż´Ă
᫬»®ř˝±˛ş·ą)#
Selectively disables IP TTL propagation for:
• Forwarded traffic (Traceroute does not work for
transit traffic labeled by this router.)
• Local traffic (Traceroute does not work from the
router but works for transit traffic labeled by this
router.)
Configuring IP TTL Propagation:
Extended Options
mpls ip propagate-ttl
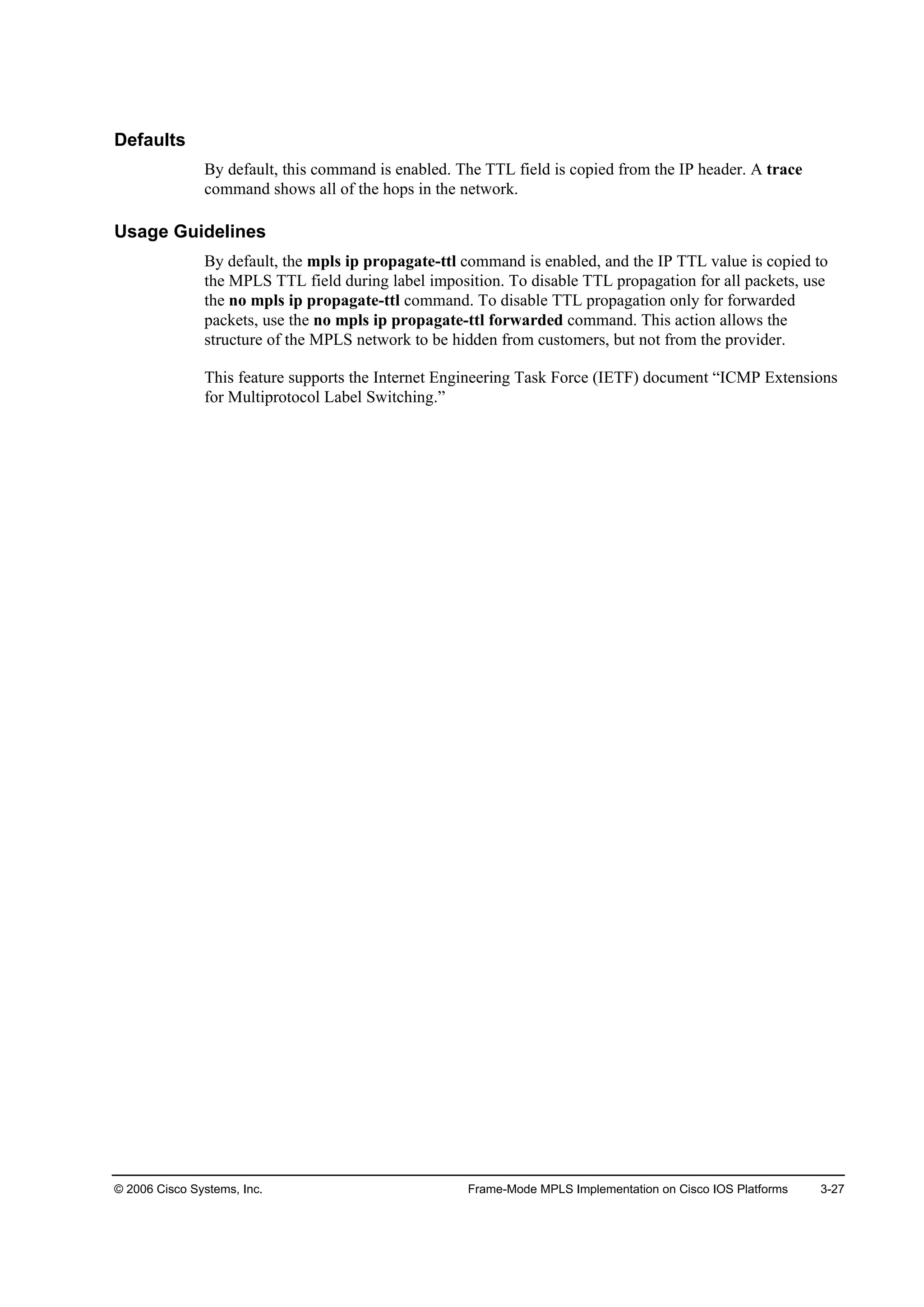
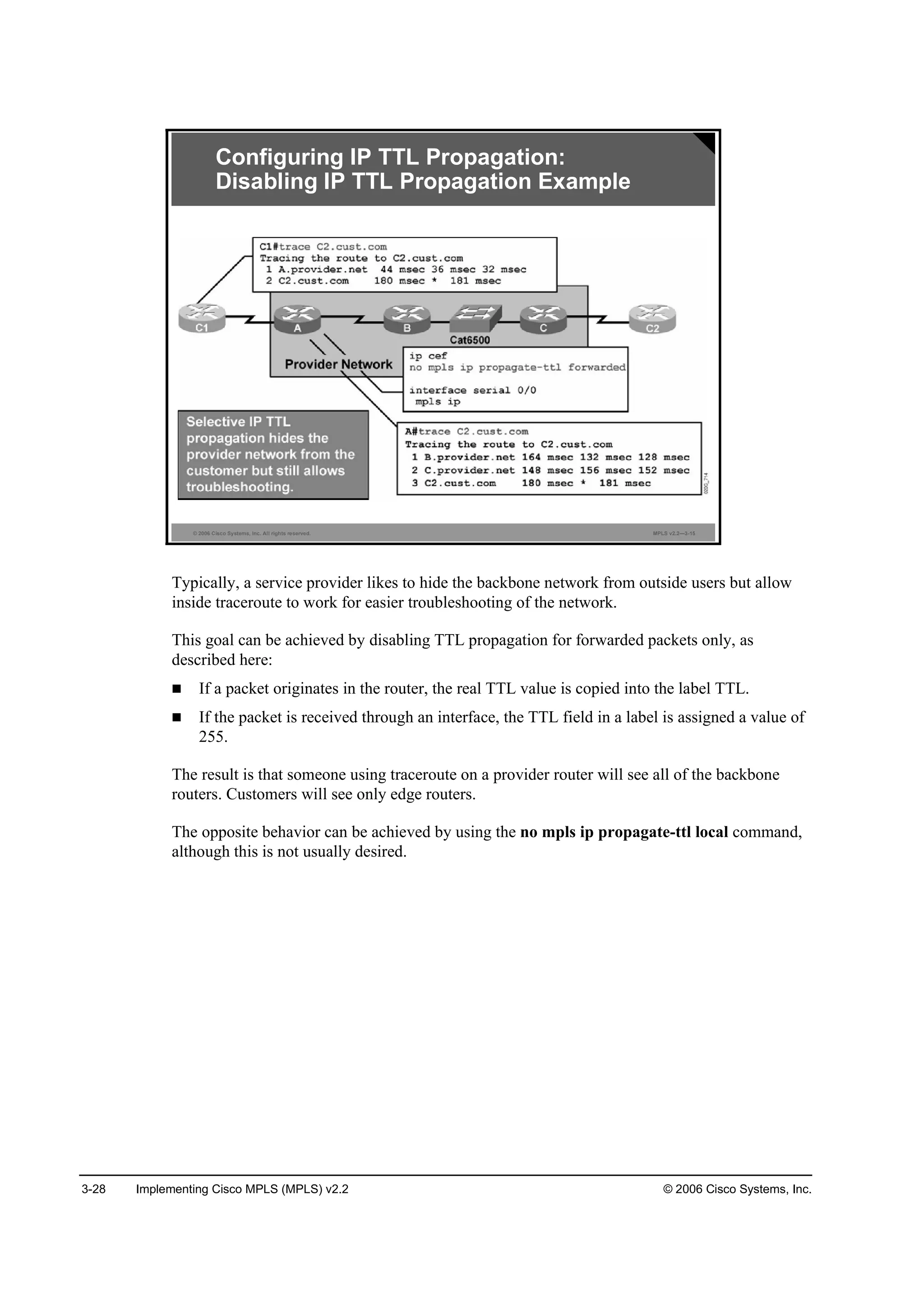
Use the mpls ip propagate-ttl global configuration command to control generation of the TTL
field in the label when the label is first added to the IP packet. By default, this command is
enabled, which means that the TTL field is copied from the IP header and inserted into the
MPLS label. This aspect allows a trace command to show all of the hops in the network.
To use a fixed TTL value (255) for the first label of the IP packet, use the no form of the mpls
ip propagate-ttl command. This action hides the structure of the MPLS network from a trace
command. Specify the types of packets to be hidden by using the forwarded and local
arguments. Specifying no mpls ip propagate-ttl forwarded allows the structure of the MPLS
network to be hidden from customers but not from the provider. Here are the most common
applications of this command:
mpls ip propagate-ttl [forwarded | local]
no mpls ip propagate-ttl [forwarded | local]
This table describes the parameters for the mpls ip propagate-ttl command.
mpls ip propagate-ttl Syntax Description
Parameter Description
ş±®©ż®Ľ»Ľ (Optional) Hides the structure of the MPLS network from a trace
command only for forwarded packets; prevents the trace
command from showing the hops for forwarded packets
´±˝ż´ (Optional) Hides the structure of the MPLS network from a trace
command only for local packets; prevents the trace command
from showing the hops only for local packets](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-165-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-29
Configuring Conditional Label Distribution
This topic describes how to configure conditional label distribution.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-16
ł°´ ´Ľ° żĽŞ»®¬·»ó´żľ»´ Ĺş±® °®»ş·¨óż˝˝»ó´·¬ Ŭ± °»»®ó
ż˝˝»ó´·¬ĂĂ
᫬»®ř˝±˛ş·ą÷ý
• By default, labels for all destinations are announced to all LDP or
TDP neighbors.
• This command enables you to selectively advertise some labels
to some LDP or TDP neighbors.
• Conditional label advertisement works only over frame-mode
interfaces.
• Parameters:
– for —The IP access list that selects the
destinations for which the labels will be generated
– to —The IP access list that selects the MPLS
neighbors that will receive the labels
Conditional Label Distribution
Configuration
mpls ldp advertise-labels
To control the distribution of locally assigned (incoming) labels by means of LDP, use the
mpls ldp advertise-labels command in global configuration mode. This command is used to
control which labels are advertised to which LDP neighbors. To prevent the distribution of
locally assigned labels, use the no form of this command, as shown here:
mpls ldp advertise-labels [for prefix-access-list [to peer-access-list]]
no mpls ldp advertise-labels [for prefix-access-list [to peer-access-list]]
This table describes the parameters for the mpls idp advertise-labels command.
mpls idp advertise-labels Syntax Description
Parameter Description
ş±® °®»ş·¨óż˝˝»ó´·¬ (Optional) This parameter specifies which destinations should
have their labels advertised.
¬± °»»®óż˝˝»ó´·¬ (Optional) This parameter specifies which LSR neighbors should
receive label advertisements. An LSR is identified by its router ID,
which consists of the first 4 bytes of its 6-byte LDP identifier.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-168-2048.jpg)


![3-40 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Monitoring MPLS
This topic describes how to monitor MPLS.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-3
¸±© ł°´ ´Ľ° °ż®żł»¬»®
᫬»®ý
• Displays LDP parameters on the local router
MPLS Monitoring Commands
¸±© ł°´ ·˛¬»®şż˝»
᫬»®ý
• Displays MPLS status on individual interfaces
¸±© ł°´ ´Ľ° Ľ·˝±Ş»®§
᫬»®ý
• Displays all discovered LDP neighbors
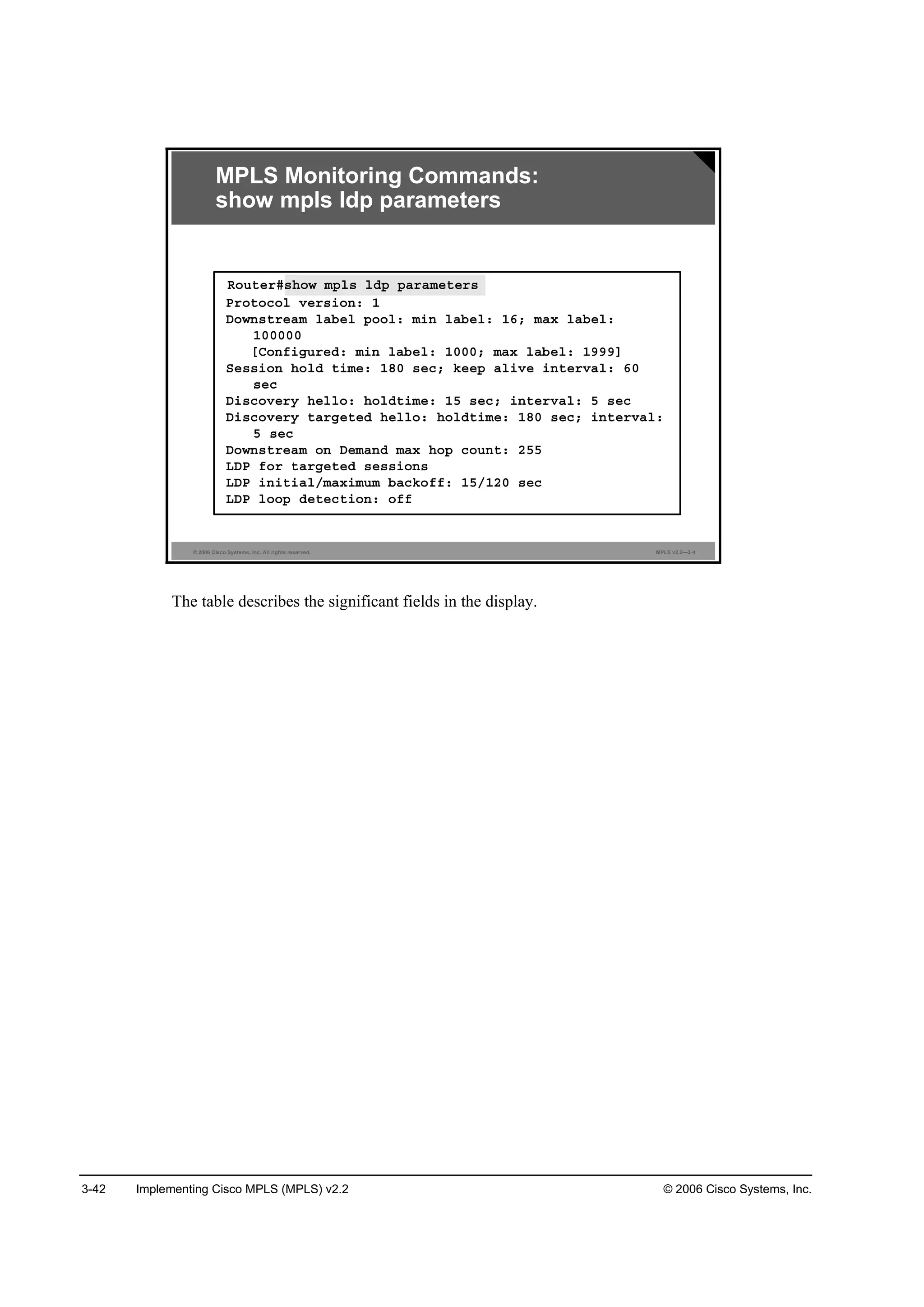
show mpls ldp parameters
To display available Label Distribution Protocol (LDP) parameters, use the show mpls ldp
parameters command in privileged EXEC mode.
Syntax Description
This command has no arguments or keywords.
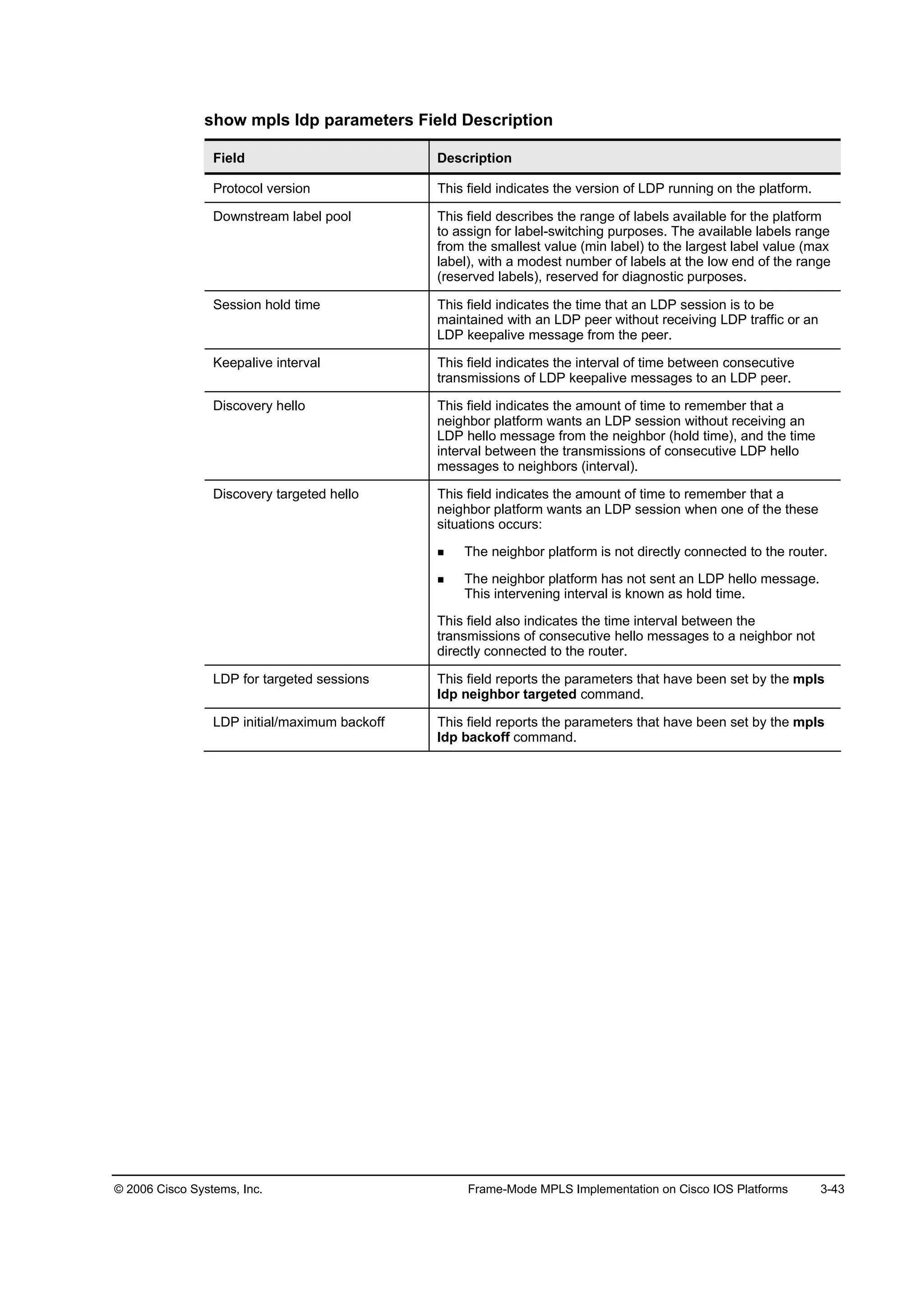
show mpls interfaces
To display information about one or more interfaces that have the MPLS feature enabled, use
the show mpls interfaces [interface] [detail] command in EXEC mode.
The table describes the parameters for the show mpls interfaces command.
show mpls interfaces Syntax Description
Parameter Description
·˛¬»®şż˝» (Optional) Defines the interface about which to display label-
switching information
Ľ»¬ż·´ (Optional) Displays detailed label-switching information for the
specified interface](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-179-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-41
show mpls ldp discovery
To display the status of the LDP discovery process (Hello protocol), use these commands in
privileged EXEC mode:
show mpls ldp discovery [vrf vpn-name]
show mpls ldp discovery [all]
The show mpls ldp discovery command displays all MPLS-enabled interfaces and the
neighbors that are present on the interfaces.
show mpls ldp discovery Syntax Description
Parameter Description
Ş®ş Ş°˛ó˛żł» (Optional) Displays the neighbor discovery information for the
specified Virtual Private Network (VPN) routing or forwarding
instance (vpn-name)
ż´´ (Optional) Displays LDP discovery information for all VPNs when
the all keyword is specified alone in this command, including
those in the default routing domain](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-180-2048.jpg)
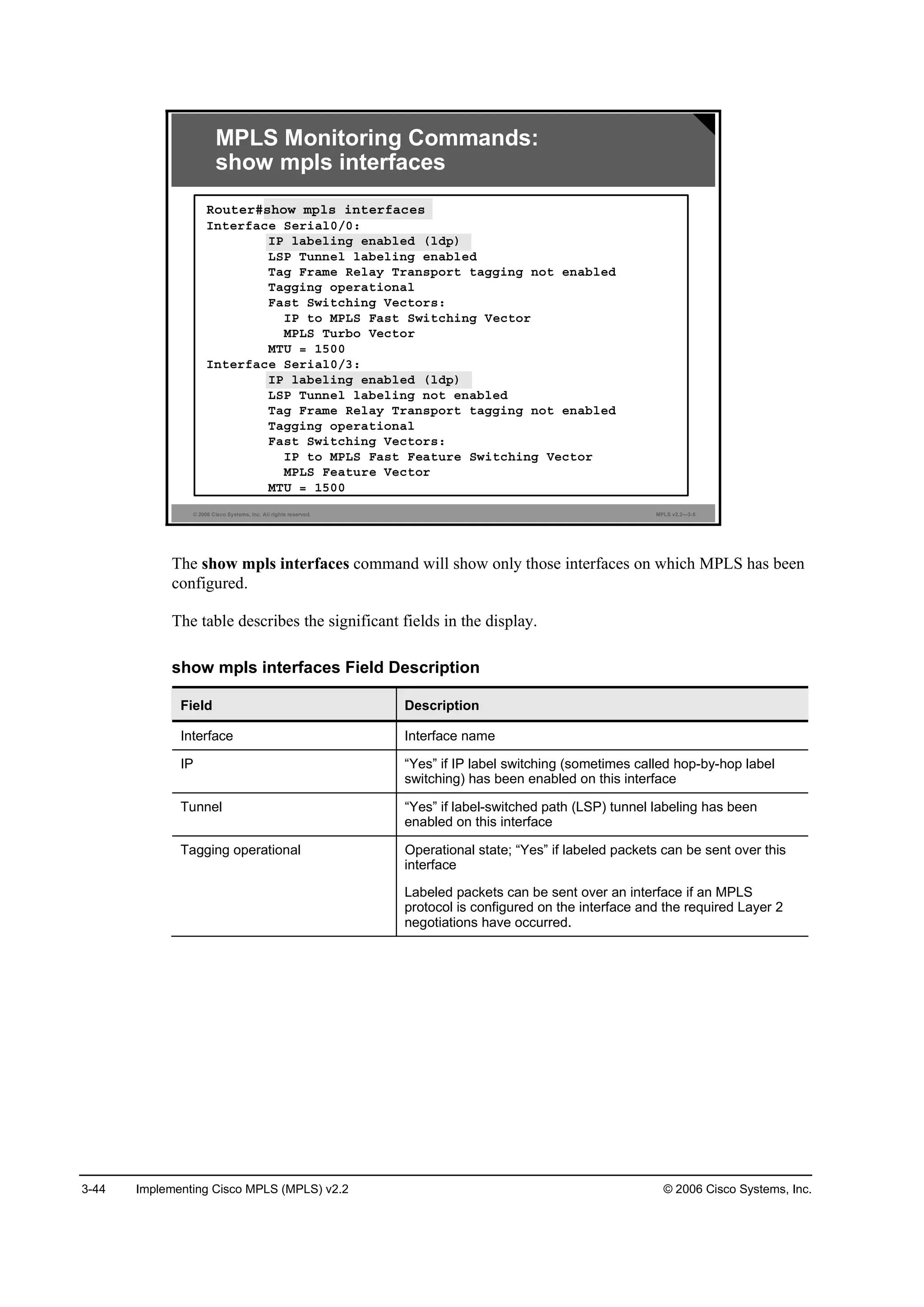
![3-46 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
show mpls ldp discovery Field Description
Field Description
Local LDP Identifier This field indicates the LDP identifier (LDP ID) for the local router.
An LDP ID is a 6-byte construct displayed in the form “IP
address:number”.
By convention, the first 4 bytes of the LDP ID constitute the router
ID; integers, starting with 0, constitute the final 2 bytes of the IP
address:number construct.
Interfaces This field lists the interfaces that are engaging in LDP discovery
activity, as described here:
The xmit field indicates that the interface is transmitting LDP
discovery hello packets.
The recv field indicates that the interface is receiving LDP
discovery hello packets.
The (ldp) or (tdp) field indicates the label distribution protocol
configured for the interface.
The LDP (or Tag Distribution Protocol [TDP]) identifiers indicate
LDP (or TDP) neighbors discovered on the interface.
Targeted Hellos This field lists the platforms to which targeted hello messages are
being sent, as described here:
The xmit, recv, and (ldp) or (tdp) fields are as described for
the Interfaces field.
The active field indicates that this label switch router (LSR)
has initiated targeted hello messages.
The passive field indicates that the neighbor LSR has
initiated targeted hello messages and that this LSR is
configured to respond to the targeted hello messages from
the neighbor.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-185-2048.jpg)
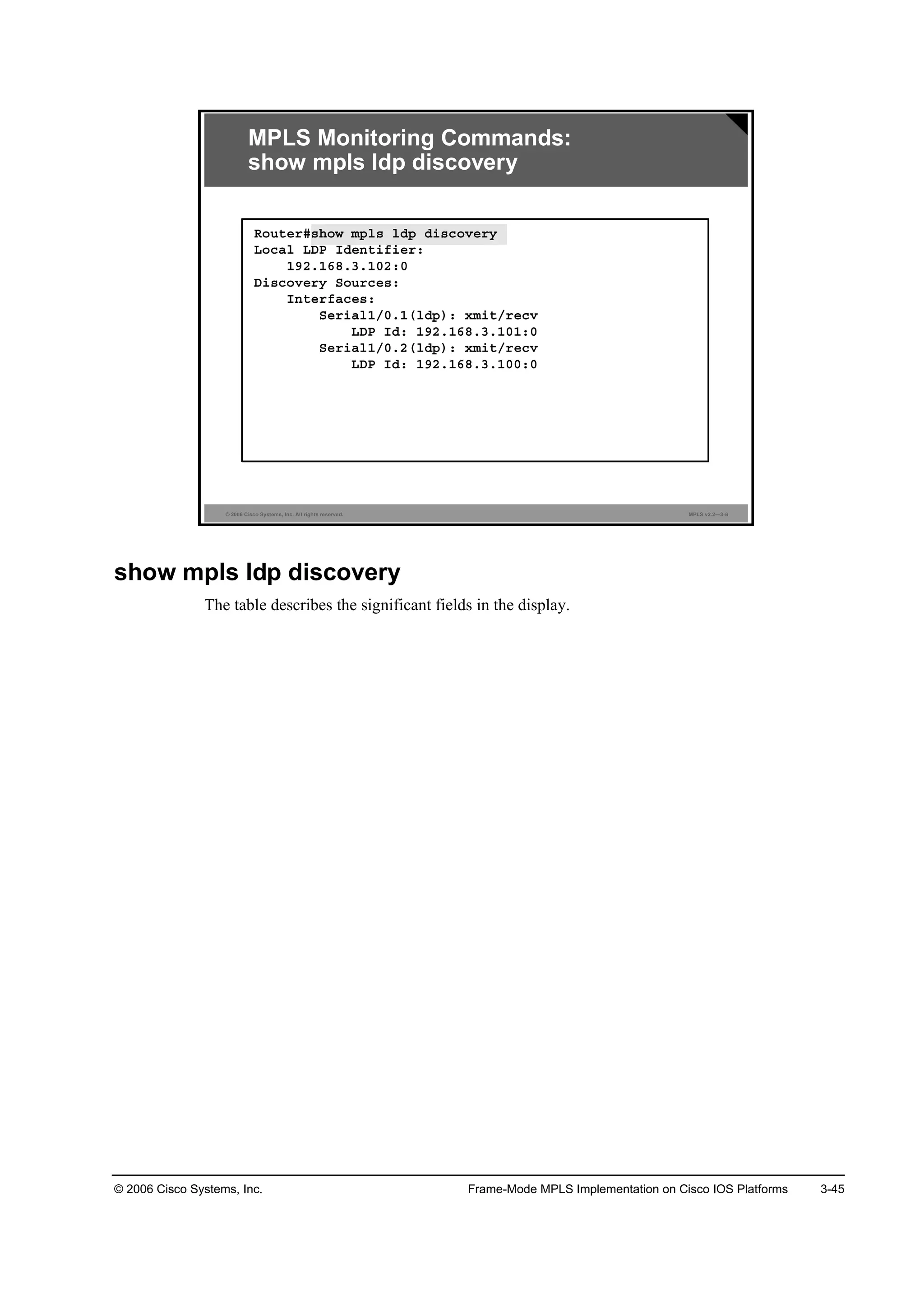
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-47
Monitoring LDP
This topic describes how to monitor LDP.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-7
¸±© ł°´ ´Ľ° ˛»·ą¸ľ±®
᫬»®ý
• Displays individual LDP neighbors
LDP Monitoring Commands
¸±© ł°´ ´Ľ° ˛»·ą¸ľ±® Ľ»¬ż·´
᫬»®ý
• Displays more details about LDP neighbors
¸±© ł°´ ´Ľ° ľ·˛Ľ·˛ą
᫬»®ý
• Displays LIB
• show mpls ldp bindings [network {mask | length} [longer-prefixes]]
[local-label label [- label]} [remote-label label [- label] [neighbor address]
[local]
show mpls ldp neighbor
To display the status of LDP sessions, use these show mpls ldp neighbor commands in
privileged EXEC mode:
show mpls ldp neighbor [vrf vpn-name] [address] [interface] [detail]
show mpls ldp neighbor [all]
show mpls ldp neighbor Syntax Description
Parameter Description
vrf vpn-name (Optional) Displays the LDP neighbors for the specified VPN
routing or forwarding instance (vpn-name)
address (Optional) Identifies the neighbor with this IP address
interface (Optional) Defines the LDP neighbors accessible over this
interface
detail (Optional) Displays information in long form
all (Optional) Displays LDP neighbor information for all VPNs when
the all keyword is specified alone in this command, including
those in the default routing domain](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-186-2048.jpg)
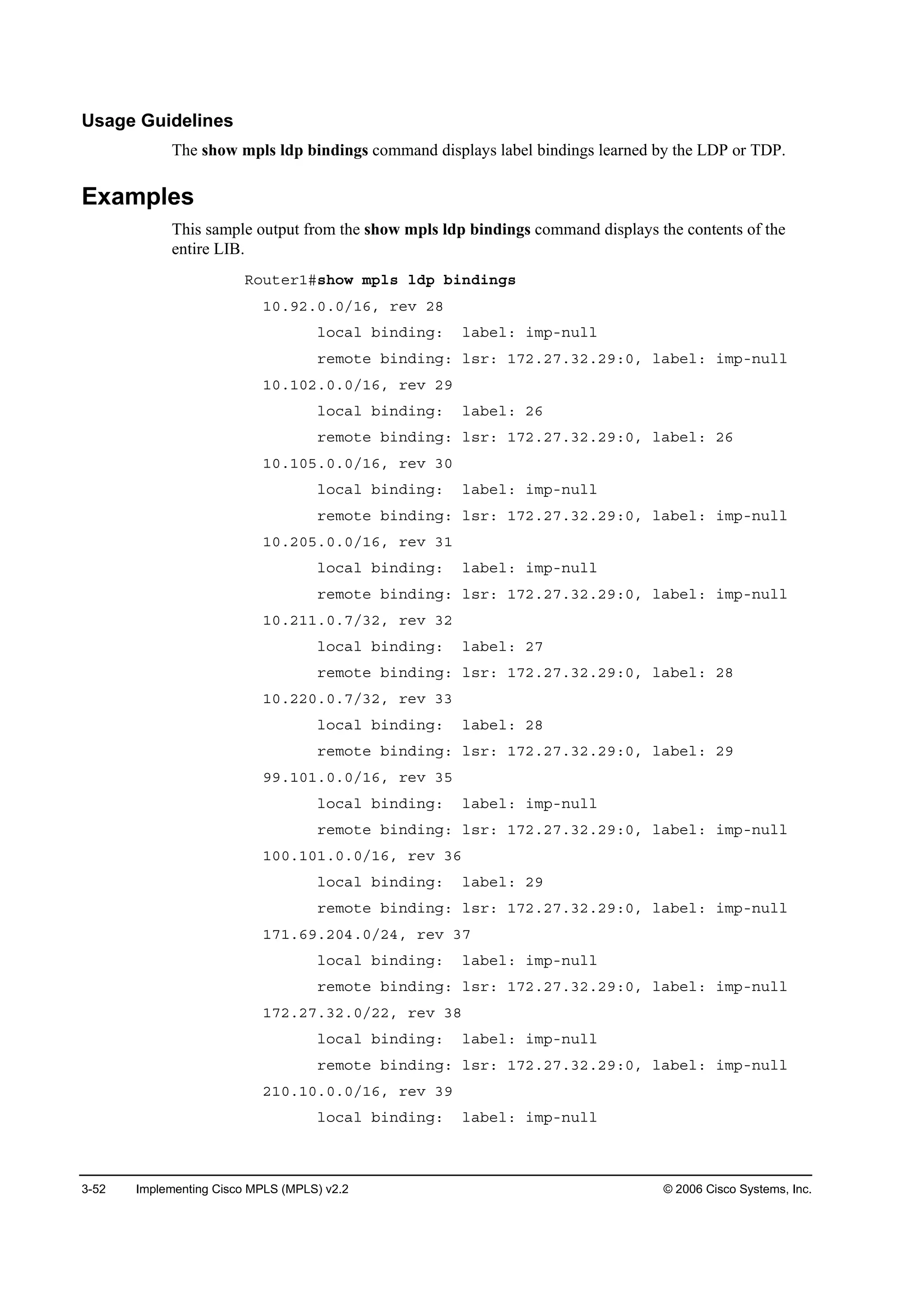
![3-48 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
show mpls ldp bindings
To display the contents of the LIB, use this show mpls ldp bindings command in privileged
EXEC mode: show mpls ldp bindings [network {mask | length} [longer-prefixes]]
[local-label label [-label]] [remote-label label [-label]] [neighbor address] [local].
show mpls ldp bindings Syntax Description
Parameter Description
vrf vpn-name (Optional) This parameter displays the label bindings for the specified
VPN routing or forwarding instance (vpn-name).
network (Optional) This parameter defines the destination network number.
mask (Optional) This parameter specifies the network mask, written as
A.B.C.D.
length (Optional) This parameter specifies the mask length (1 to 32
characters).
longer-prefixes (Optional) This parameter selects any prefix that matches mask with a
length from 1 to 32 characters.
local-label label-label (Optional) This parameter displays entries matching local label values.
Use the label-label argument to indicate the label range.
remote-label label-label (Optional) This parameter displays entries matching the label values
assigned by a neighbor router. Use the label-label argument to
indicate the label range.
neighbor address (Optional) This parameter displays the label bindings assigned by the
selected neighbor.
local (Optional) This parameter displays the local label bindings.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-187-2048.jpg)
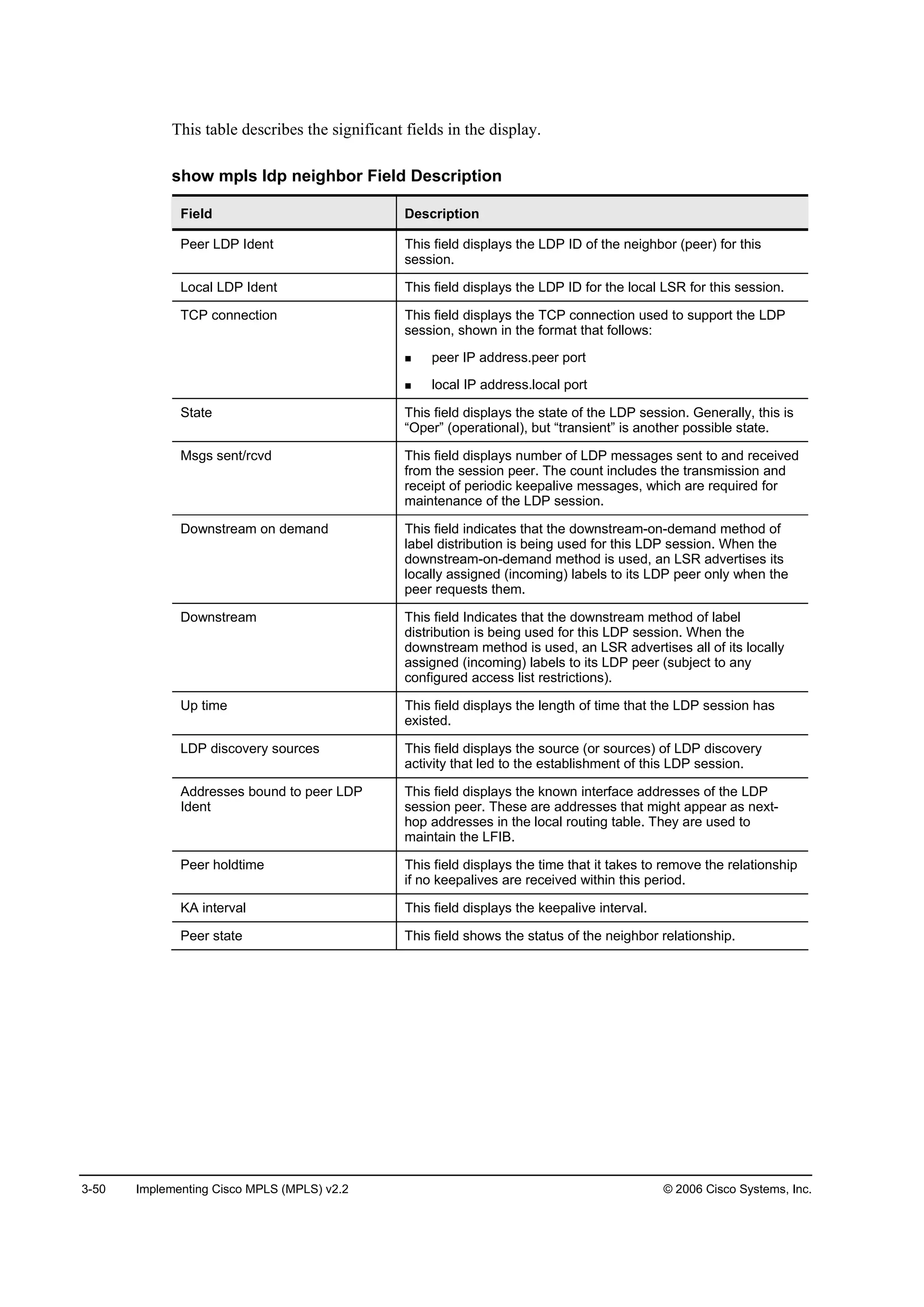
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-49
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-8
LDP Monitoring Commands:
show mpls ldp neighbor detail
᫬»®ý¸±© ł°´ ´Ľ° ˛»·ą¸ľ±® Ľ»¬ż·´
Đ»»® ÔÜР׼»˛¬ć ďçîňďęčňíňďđđćđĺ Ô±˝ż´ ÔÜР׼»˛¬ ďçîňďęčňíňďđîćđ
ĚÝĐ ˝±˛˛»˝¬·±˛ć ďçîňďęčňíňďđđňęěę Š ďçîňďęčňíňďđîňďďđđđ
ͬż¬»ć Ń°»®ĺ Óą »˛¬ń®˝ŞĽć íďďéńíďďîĺ ܱ©˛¬®»żłĺ
Ôż¬ Ě×Ţ ®»Ş »˛¬î
Ë° ¬·ł»ć î©ěĽĺ Ë×Üć ěĺ Đ»»® ׼ đĺ
ÔÜĐ Ľ·˝±Ş»®§ ±«®˝»ć
Í»®·ż´đńđĺ Í®˝ ×Đ żĽĽ®ć ďíđňđňđňî
¸±´Ľ¬·ł»ć ďëđđđ łô ¸»´´± ·˛¬»®Şż´ć ëđđđ ł
߼Ľ®»» ľ±«˛Ľ ¬± °»»® ÔÜР׼»˛¬ć
ďçîňďęčňíňďđ ďçîňďęčňíňďě ďçîňďęčňíňďđđ
Đ»»® ¸±´Ľ¬·ł»ć ďčđđđđ łĺ Őß ·˛¬»®Şż´ć ęđđđđ łĺ Đ»»®
¬ż¬»ć »¬żľ
The status of the LDP session is indicated by “State: Oper” (operational).
show mpls ldp neighbor
To display the status of LDP sessions, issue these show mpls ldp neighbor commands in
privileged EXEC mode:
show mpls ldp neighbor [vrf vpn-name] [address] [interface] [detail]
show mpls ldp neighbor [all]
Usage Guidelines
The show mpls ldp neighbor command can provide information about all LDP neighbors, or
the information can be limited to the following:
Neighbor with specific IP address
LDP neighbors known to be accessible over a specific interface](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-188-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-51
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-9
LDP Monitoring Commands:
show mpls ldp bindings
᫬»®ý¸±© ł°´ ´Ľ° ľ·˛Ľ·˛ą
¬·ľ »˛¬®§ć ďđňďđîňđňđńďęô ®»Ş îç
´±˝ż´ ľ·˛Ľ·˛ąć ´żľ»´ć îę
®»ł±¬» ľ·˛Ľ·˛ąć ´®ć ďéîňîéňíîňîçćđô ´żľ»´ć îę
¬·ľ »˛¬®§ć ďđňîďďňđňéńíîô ®»Ş íî
´±˝ż´ ľ·˛Ľ·˛ąć ´żľ»´ć îé
®»ł±¬» ľ·˛Ľ·˛ąć ´®ć ďéîňîéňíîňîçćđô ´żľ»´ć îč
¬·ľ »˛¬®§ć ďđňîîđňđňéńíîô ®»Ş íí
´±˝ż´ ľ·˛Ľ·˛ąć ´żľ»´ć îč
®»ł±¬» ľ·˛Ľ·˛ąć ´®ć ďéîňîéňíîňîçćđô ´żľ»´ć îç
show mpls ldp bindings
To display the contents of the LIB, use this show mpls ldp bindings command in privileged
EXEC mode: show mpls ldp bindings [vrf vpn-name] [network {mask | length} [longer-
prefixes]] [local-label label [-label]] [remote-label label [-label]] [neighbor address] [local].
show mpls ldp bindings Syntax Description
Parameter Description
vrf vpn-name (Optional) This parameter displays the label bindings for the
specified VPN routing or forwarding instance (vpn-name).
network (Optional) This parameter defines the destination network
number.
mask (Optional) This parameter specifies the network mask, written as
A.B.C.D.
length (Optional) This parameter specifies the mask length (1 to 32
characters).
longer-prefixes (Optional) This parameter selects any prefix that matches mask
with a length from 1 to 32 characters.
local-label label-label (Optional) This parameter displays entries matching local label
values. Use the label-label argument to indicate the label range.
remote-label label-label (Optional) This parameter displays entries matching the label
values assigned by a neighbor router. Use the label-label
argument to indicate the label range.
neighbor address (Optional) This parameter displays the label bindings assigned by
the selected neighbor.
local (Optional) This parameter displays the local label bindings.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-190-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-53
Monitoring Label Switching
This topic describes how to monitor label switching.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-10
¸±© ł°´ ş±®©ż®Ľ·˛ąó¬żľ´»
᫬»®ý
• Displays contents of LFIB
Monitoring Label Switching
¸±© ·° ˝»ş Ľ»¬ż·´
᫬»®ý
• Displays label or labels attached to a packet during label
imposition on edge LSR
show mpls forwarding-table
To display the contents of the MPLS LFIB, use this show mpls forwarding-table command in
privileged EXEC mode: show mpls forwarding-table [{network {mask | length} | labels label
[-label]| interface interface | next-hop address | lsp-tunnel [tunnel-id]}] [detail].
show ip cef
To display entries in the FIB that are unresolved or to display a summary of the FIB, use the
this form of the show ip cef command in privileged EXEC mode: show ip cef [unresolved |
summary].
To display specific entries in the FIB based on IP address information, use this form of the
show ip cef command in privileged EXEC mode: show ip cef [network [mask [longer-
prefix]]] [detail].
To display specific entries in the FIB based on interface information, use this form of the show
ip cef command in privileged EXEC mode: show ip cef [type number] [detail].](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-192-2048.jpg)
![3-54 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-11
Monitoring Label Switching:
show mpls forwarding-table
᫬»®ý¸±© ł°´ ş±®©ż®Ľ·˛ąó¬żľ´» á
ßňŢňÝňÜ Ü»¬·˛ż¬·±˛ °®»ş·¨
Ľ»¬ż·´ Ü»¬ż·´»Ľ ·˛ş±®łż¬·±˛
·˛¬»®şż˝» Óż¬˝¸ ±«¬ą±·˛ą ·˛¬»®şż˝»
´żľ»´ Óż¬˝¸ ´żľ»´ Şż´«»
´°ó¬«˛˛»´ ÔÍĐ Ě«˛˛»´ ·Ľ
˛»¨¬ó¸±° Óż¬˝¸ ˛»¨¬ ¸±° ˛»·ą¸ľ±®
Ş®ş ͸±© »˛¬®·» ş±® ż ĘĐŇ
᫬·˛ąńÚ±®©ż®Ľ·˛ą ·˛¬ż˛˝»
¤ Ń«¬°«¬ ł±Ľ·ş·»®
ä˝®â
show mpls forwarding-table
To display the contents of the MPLS LFIB, use this show mpls forwarding-table command in
privileged EXEC mode: show mpls forwarding-table [{network {mask | length} | labels label
[-label]| interface interface | next-hop address | lsp-tunnel [tunnel-id]}] [detail].
show mpls forwarding-table Syntax Description
Parameter Description
network (Optional) Displays destination network number
mask Displays IP address of destination mask whose entry is to be
shown
length Displays number of bits in mask of destination
labels label-label (Optional) Shows only entries with specified local labels
interface interface (Optional) Shows only entries with specified outgoing interface
next-hop address (Optional) Shows only entries with specified neighbor as next hop
lsp-tunnel tunnel-id (Optional) Shows only entries with specified LSP tunnel, or all
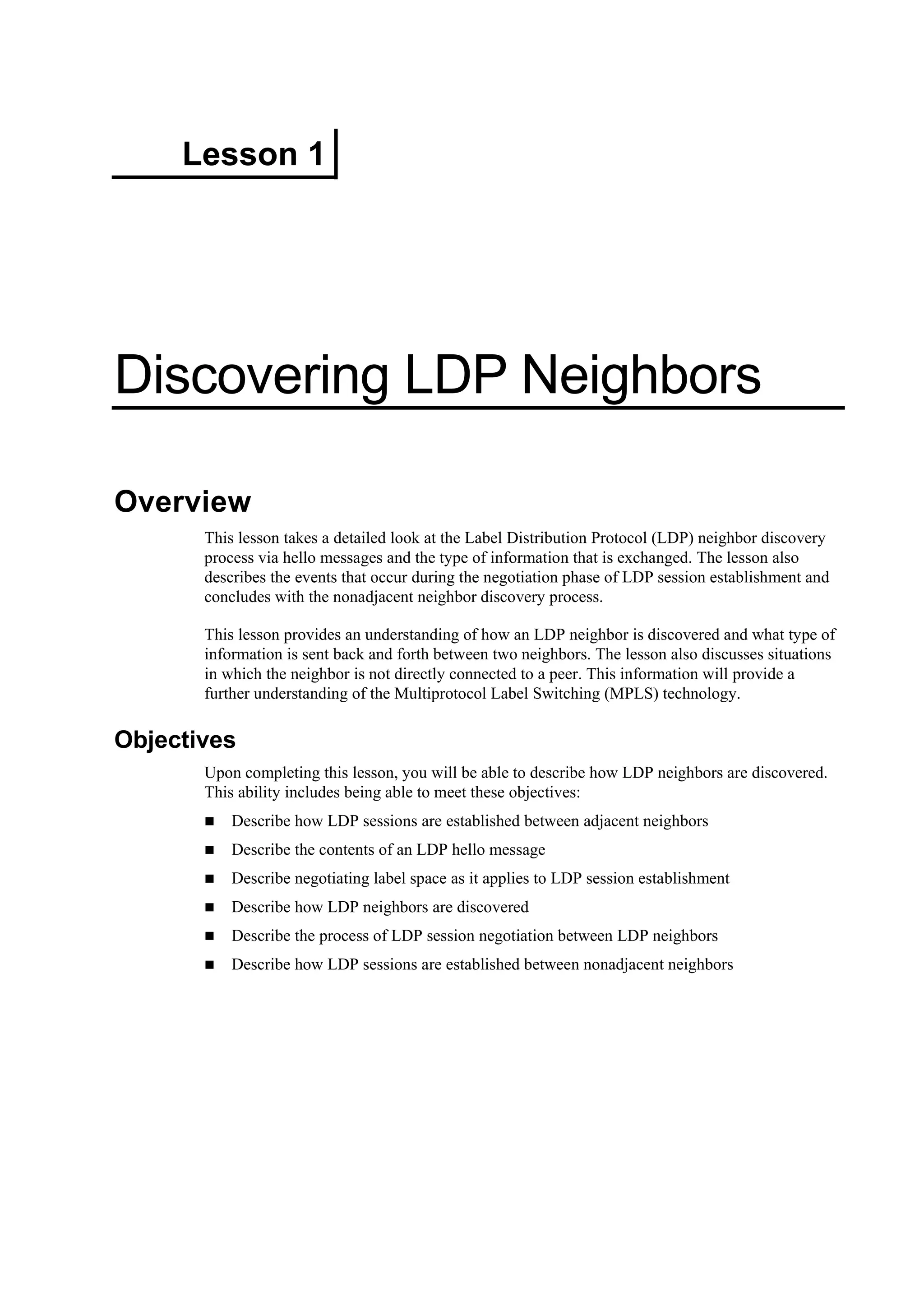
LSP tunnel entries
detail (Optional) Displays information in long form (includes length of
encapsulation, length of MAC string, maximum transmission unit
(MTU), and all labels)](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-193-2048.jpg)
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-55
Examples: show mpls forwarding table Command Output
This is a sample output from the show mpls forwarding table command.
᫬»®ý¸±© ł°´ ş±®©ż®Ľ·˛ąó¬żľ´»
Ô±˝ż´ Ń«¬ą±·˛ą Đ®»ş·¨ ާ¬» ¬żą Ń«¬ą±·˛ą Ň»¨¬ ر°
¬żą ¬żą ±® ĘÝ ±® Ě«˛˛»´ ׼ ©·¬˝¸»Ľ ·˛¬»®şż˝»
îę ˲¬żąą»Ľ ďđňîëíňđňđńďę đ ۬ěńđńđ ďéîňîéňîíîňę
îč ďńíí ďđňďëňđňđńďę đ ßĚđńđňď °±·˛¬î°±·˛¬
îç б° ¬żą ďđňçďňđňđńďę đ Řëńđ °±·˛¬î°±·˛¬
ďńíę ďđňçďňđňđńďę đ ßĚđńđňď °±·˛¬î°±·˛¬
íđ íî ďđňîëđňđňçéńíî đ ۬ěńđńî ďđňçîňđňé
íî ďđňîëđňđňçéńíî đ Řëńđ °±·˛¬î°±·˛¬
íě îę ďđňééňđňđńîě đ ۬ěńđńî °±·˛¬î°±·˛¬
îę ďđňééňđňđńîě đ Řëńđ °±·˛¬î°±·˛¬
íë ˲¬żąą»ĽĹĚĂ ďđňďđđňďđđňďđďńíî đ Ě«ď °±·˛¬î°±·˛¬
íę б° ¬żą ďęčňďňđňđńďę đ Řëńđ °±·˛¬î°±·˛¬
ďńíé ďęčňďňđňđńďę đ ßĚđńđňď °±·˛¬î°±·˛¬
[T] = Forwarding through an LSP tunnel.
Note View additional tagging information with the detail option.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-194-2048.jpg)
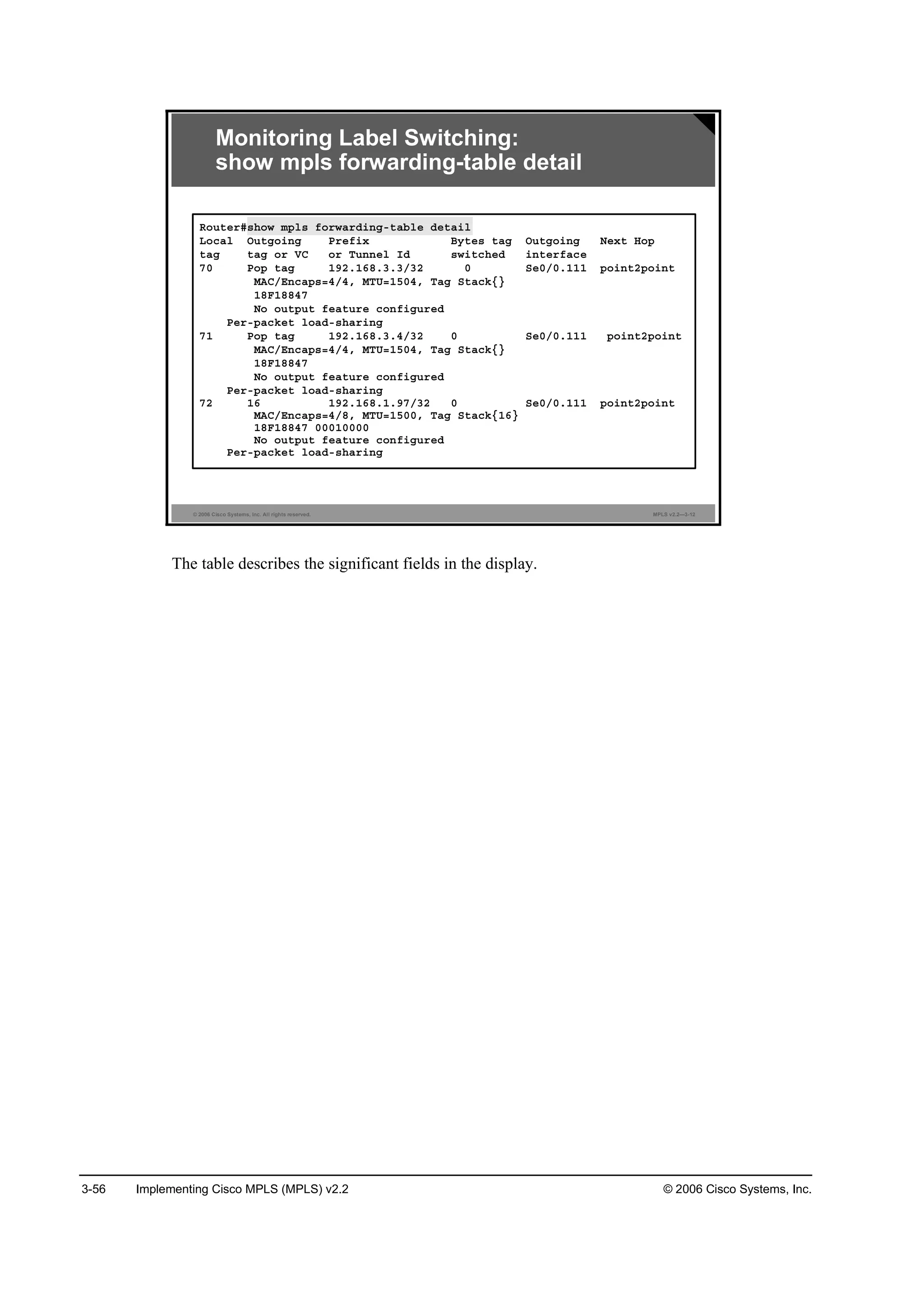
![© 2006 Cisco Systems, Inc. Frame-Mode MPLS Implementation on Cisco IOS Platforms 3-57
show mpls forwarding table Field Description
Field Description
Local tag This field displays the label assigned by this router.
Outgoing tag or VC This field displays the label assigned by the next hop or virtual
path identifier/virtual channel identifier (VPI/VCI) used to get to
next hop. Some of the entries that you can specify in this column
are as follows:
[T]: Forwarding is through an LSP tunnel.
untagged: There is no label for the destination from the next hop,
or label switching is not enabled on the outgoing interface.
Pop tag: The next hop advertised an implicit null label for the
destination, and this router popped the top label.
Prefix or Tunnel ID This field displays the address or tunnel to which packets with
this label are going.
Bytes tag switched This field displays the number of bytes switched with this
incoming label.
Outgoing interface This field displays the interface through which packets with this
label are sent.
Next Hop This field displays the IP address of the neighbor that assigned
the outgoing label.
MAC/Encaps This field displays the length in bytes of Layer 2 header, and
length in bytes of packet encapsulation, including Layer 2 header
and label header.
MTU This field displays the MTU of the labeled packet.
Tag Stack This field displays all the outgoing labels. If the outgoing interface
is transmission convergence-ATM (TC-ATM), the virtual circuit
descriptor (VCD) is also shown.
18F18847 00010000 This field displays the actual encapsulation in hexadecimal form.
There is a space shown between Layer 2 and the label header.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-196-2048.jpg)
![3-58 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-13
Monitoring Label Switching:
show ip cef detail
᫬»®ý¸±© ·° ˝»ş ďçîňďęčňîđňđ Ľ»¬ż·´
ďçîňďęčňîđňđńîěô Ş»®·±˛ îíô ˝ż˝¸»Ľ żĽ¶ż˝»˛˝§ ¬± Í»®·ż´ďńđňî
đ °ż˝µ»¬ô 𠾧¬»
¬żą ·˛ş±®łż¬·±˛ »¬
´±˝ż´ ¬żąć íí
¬żą ®»©®·¬» ©·¬¸ Í»ďńđňîô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄíîŁ
Ş·ż ďçîňďęčňíňďđô Í»®·ż´ďńđňîô đ Ľ»°»˛Ľ»˛˝·»
˛»¨¬ ¸±° ďçîňďęčňíňďđô Í»®·ż´ďńđňî
Şż´·Ľ żĽ¶ż˝»˛˝§
¬żą ®»©®·¬» ©·¬¸ Í»ďńđňîô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄíîŁ
show ip cef detail
To display detailed FIB entry information for all FIB entries, use this show ip cef detail
command in privileged EXEC mode: show ip cef [type number] [detail].
show ip cef detail Syntax Description
Parameter Description
unresolved (Optional) Displays unresolved FIB entries
summary (Optional) Displays a summary of the FIB
network (Optional) Displays the FIB entry for the specified destination
network
mask (Optional) Displays the FIB entry for the specified destination
network and mask
longer-prefix (Optional) Displays FIB entries for all more specific destinations
detail (Optional) Displays detailed FIB entry information
type number (Optional) Displays interface type and number for which to
display FIB entries
Usage Guidelines
The show ip cef command without any keywords or arguments shows a brief display of all FIB
entries.
The show ip cef detail command shows detailed FIB entry information for all FIB entries.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-197-2048.jpg)
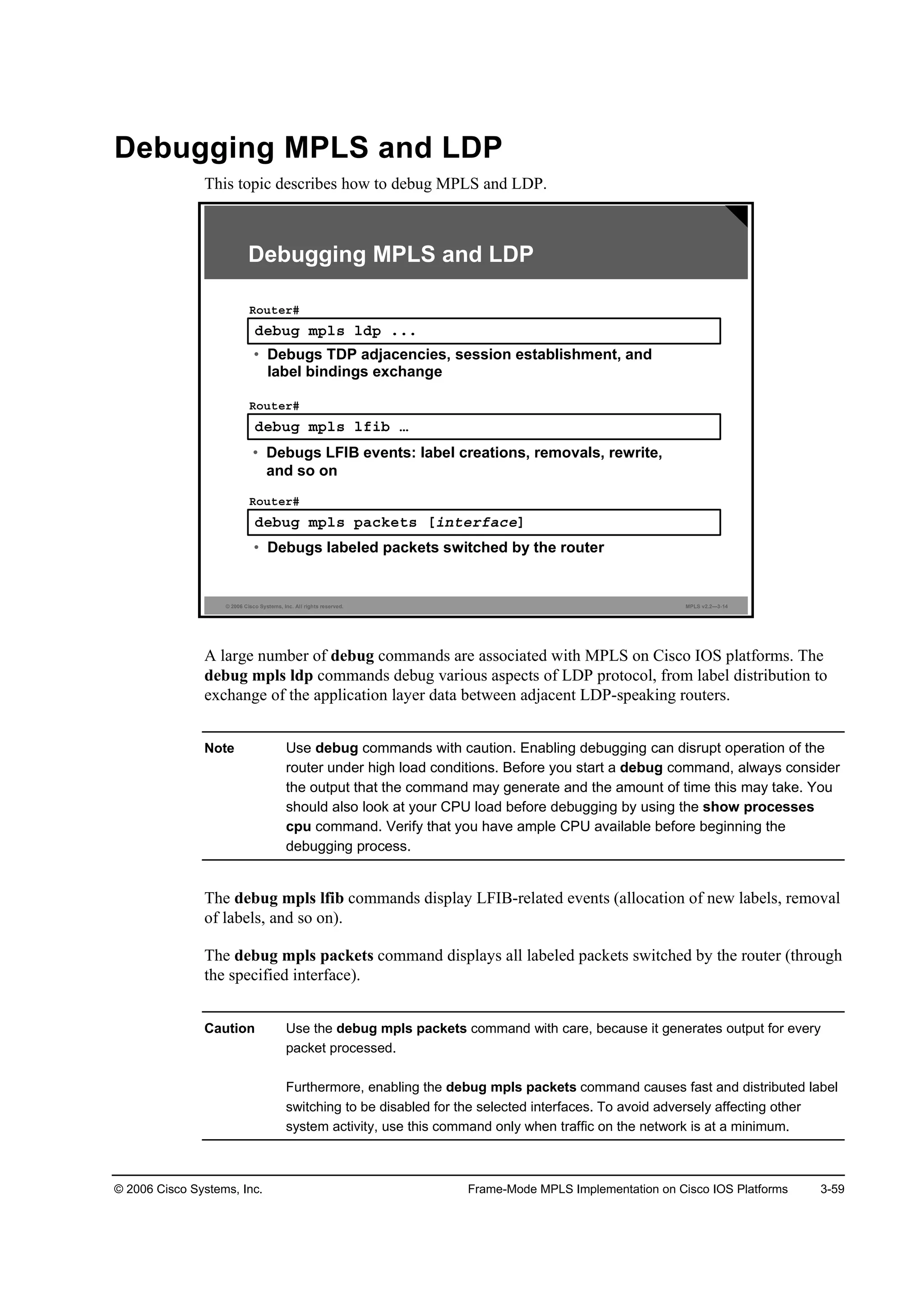
![3-60 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
debug mpls packets
To display labeled packets switched by the host router, use the debug mpls packets command
in privileged EXEC mode. To disable debugging output, use the no form of this command.
This illustrates these two commands:
debug mpls packets [interface]
no debug mpls packets [interface]
debug mpls packets Syntax Description
Field Description
Hs0/0 Displays the identifier for the interface on which the packet was
received or transmitted
Recvd Displays the packet received
Xmit Displays the packet transmitted
CoS Displays the class of service (CoS) field from the packet label
header
TTL Displays the time-to-live (TTL) field from the packet label header
(no tag) Displays the last label popped off the packet and transmitted
unlabeled
Tag(s) Displays a list of labels on the packet, ordered from the top of the
stack to the bottom](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-199-2048.jpg)


![3-72 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—3-11
Packet Labeling Issues: show cef interface
᫬»®ý¸±© ˝»ş ·˛¬»®şż˝»
Í»®·ż´ďńđňď · «° ř·şÁ˛«łľ»® ďë÷
ײ¬»®˛»¬ żĽĽ®» · ďçîňďęčňíňëńíđ
×ÝÓĐ ®»Ľ·®»˝¬ ż®» ż´©ż§ »˛¬
Đ»® °ż˝µ»¬ ´±żĽľż´ż˛˝·˛ą · Ľ·żľ´»Ľ
×Đ «˛·˝ż¬ ÎĐÚ ˝¸»˝µ · Ľ·żľ´»Ľ
ײľ±«˛Ľ ż˝˝» ´·¬ · ˛±¬ »¬
Ń«¬ľ±«˛Ľ ż˝˝» ´·¬ · ˛±¬ »¬
×Đ °±´·˝§ ®±«¬·˛ą · Ľ·żľ´»Ľ
ײ¬»®şż˝» · łż®µ»Ľ ż °±·˛¬ ¬± °±·˛¬ ·˛¬»®şż˝»
Řż®Ľ©ż®» ·Ľľ · Í»®·ż´ďńđ
Úż¬ ©·¬˝¸·˛ą ¬§°» ëô ·˛¬»®şż˝» ¬§°» ęě
×Đ ÝŰÚ ©·¬˝¸·˛ą »˛żľ´»Ľ
×Đ ÝŰÚ ĘĐŇ Úż¬ ©·¬˝¸·˛ą ¬«®ľ± Ş»˝¬±®
ײ°«¬ şż¬ ş´żą đ¨ďđđđô Ń«¬°«¬ şż¬ ş´żą đ¨đ
·ş·˛Ľ»¨ íří÷
Í´±¬ ď Í´±¬ «˛·¬ đ ĘÝ óď
Ě®ż˛ł·¬ ´·ł·¬ ż˝˝«ł«´ż¬±® đ¨đ řđ¨đ÷
×Đ ÓĚË ďëđđ
᫬»®ý¸±© ˝»ş ·˛¬»®şż˝»
×Đ ÝŰÚ ©·¬˝¸·˛ą »˛żľ´»Ľ
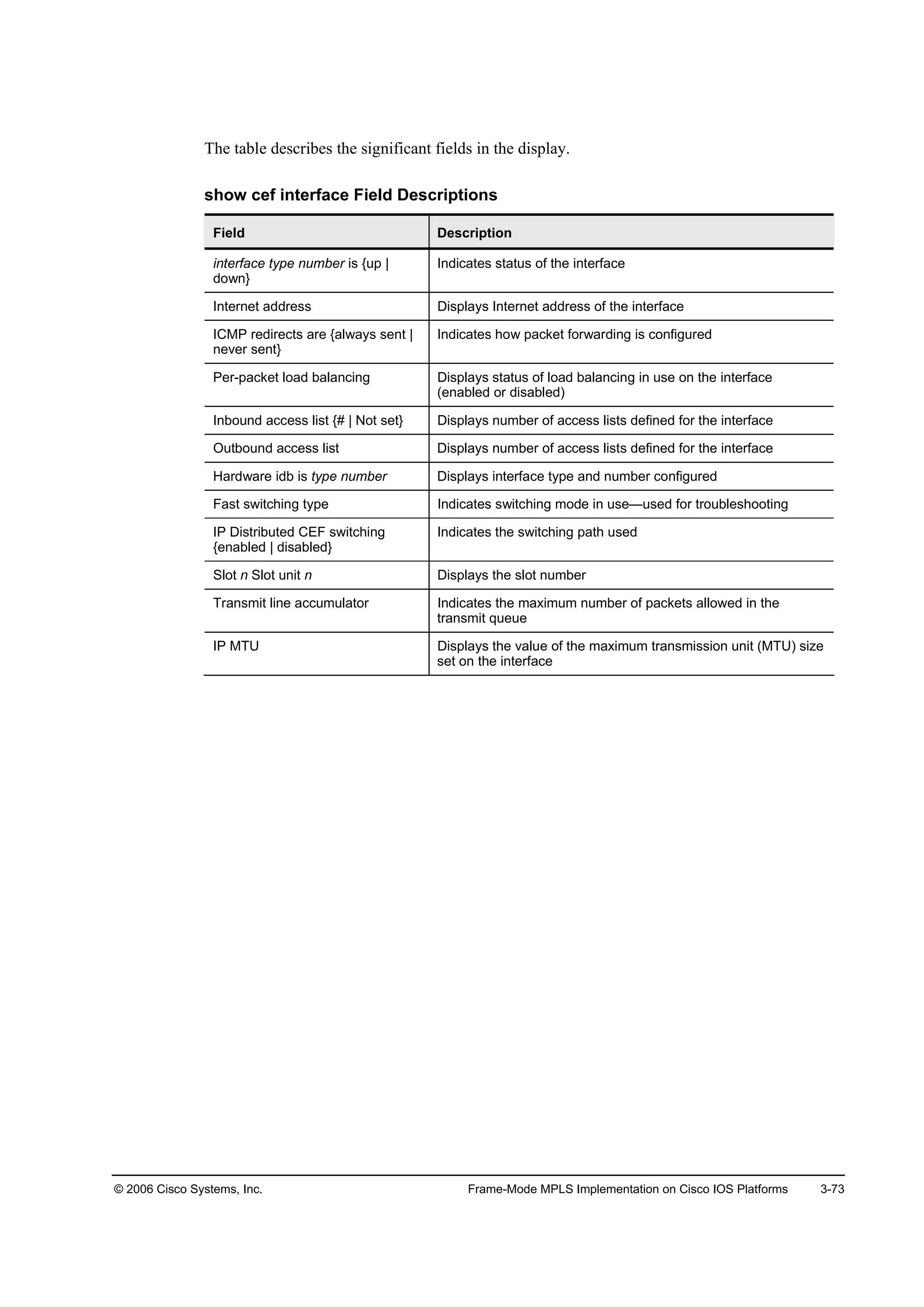
show cef interface
The show cef interface command is used in privileged EXEC mode to display CEF interface
information.
The table describes the parameters for the show cef interface type number [detail] command.
show cef interface Syntax Descriptions
Parameter Description
type number Displays interface number and the number about which to display
CEF-related information
detail (Optional) Displays detailed CEF information for the specified
interface port number
Usage Guidelines
The show cef interface command is available on routers that have route processor (RP) cards
and line cards.
You can use this command to show the CEF state on an individual interface.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-211-2048.jpg)


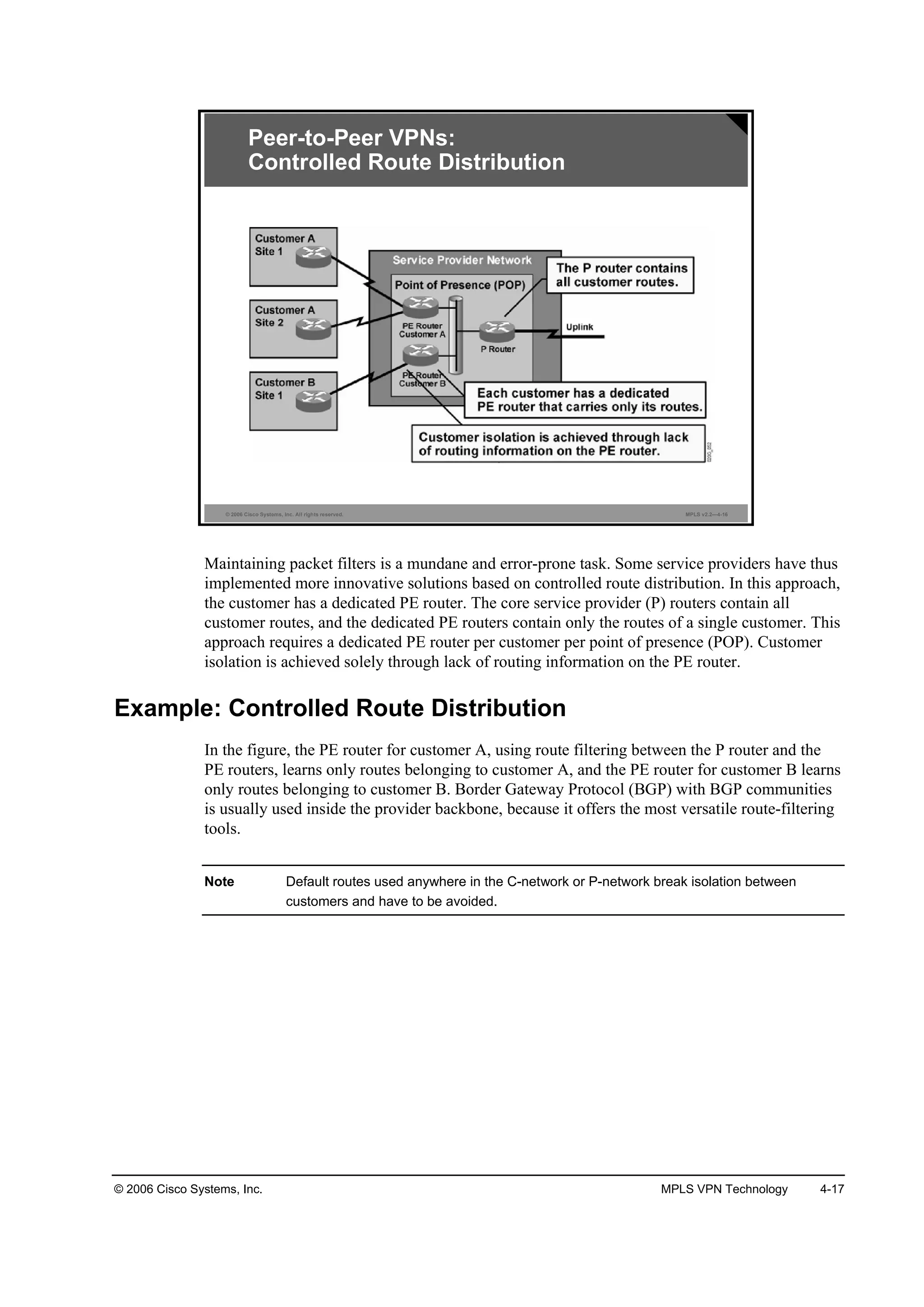
![4-14 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—4-13
Overlay VPNs:
Layer 3 Routing
• The service provider infrastructure appears as point-to-point
links to customer routes.
• Routing protocols run directly between customer routers.
• The service provider does not see customer routes and is
responsible only for providing point-to-point transport of
customer data.
From the Layer 3 perspective, the P-network is invisible to the customer routers, which are
linked with emulated point-to-point links. The routing protocol runs directly between customer
routers that establish routing adjacencies and exchange routing information.
The service provider is not aware of customer routing and has no information about customer
routes. The responsibility of the service provider is purely the point-to-point data transport
between customer sites.
The overlay VPN model has a number of drawbacks, most significantly the need for customers
to establish point-to-point links or virtual circuits between sites. The formula to calculate how
many point-to-point links or virtual circuits are needed in the worst case is ([n][n-1])/2, where n
is the number of sites to be connected. For example, if you need to have full mesh connectivity
between four sites, you will need a total of six point-to-point links or virtual circuits: (4 * (4-1))
/ 2. This leads to scalability issues.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-235-2048.jpg)

![4-34 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—4-5
MPLS VPN Architecture:
Terminology
Note:
• PE Router = Edge LSR
• P Router = LSR
MPLS VPN terminology divides the overall network into a customer-controlled part (the C-
network) and a provider-controlled part (the provider network [P-network]). Contiguous
portions of the C-network are called sites and are linked with the P-network via customer edge
(CE) routers. The CE routers are connected to the PE routers, which serve as the edge devices
of the P-network. The core devices in the P-network, the provider routers (P routers), provide
transit transport across the provider backbone and do not carry customer routes.
Note In an MPLS VPN implementation, the P router is the LSR.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-255-2048.jpg)



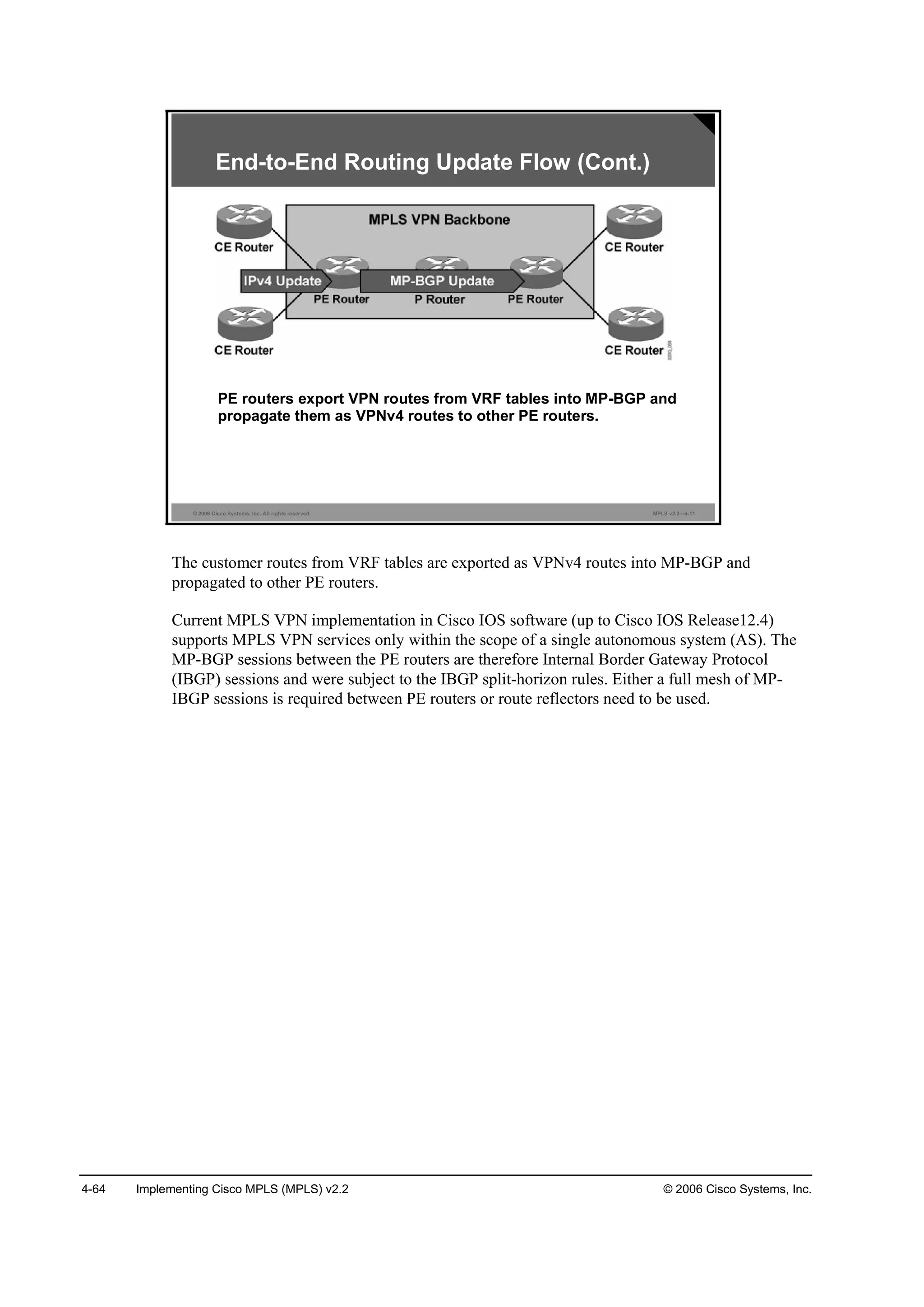
![© 2006 Cisco Systems, Inc. MPLS VPN Technology 4-65
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—4-12
End-to-End Routing Update Flow:
MP-BGP Update
An MP-BGP update contains these elements:
• VPNv4 address
• Extended communities
(route targets, optionally SOO)
• Label used for VPN packet forwarding
• Any other BGP attribute (for example, AS path, local
preference, MED, standard community)
An MP-BGP update exchange between PE routers contains these elements:
VPNv4 address
Extended BGP communities (route targets [RTs] are required; Site of Origin [SOO] is
optional)
Label used for VPN packet forwarding
Note The “Forwarding MPLS VPN Packets” lesson explains how this label is used in the MPLS
label stack.
Mandatory BGP attributes (for example, AS path)
Optionally, the MP-BGP update can contain any other BGP attribute; for example, local
preference, multi-exit discriminator (MED), or standard BGP community.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-286-2048.jpg)
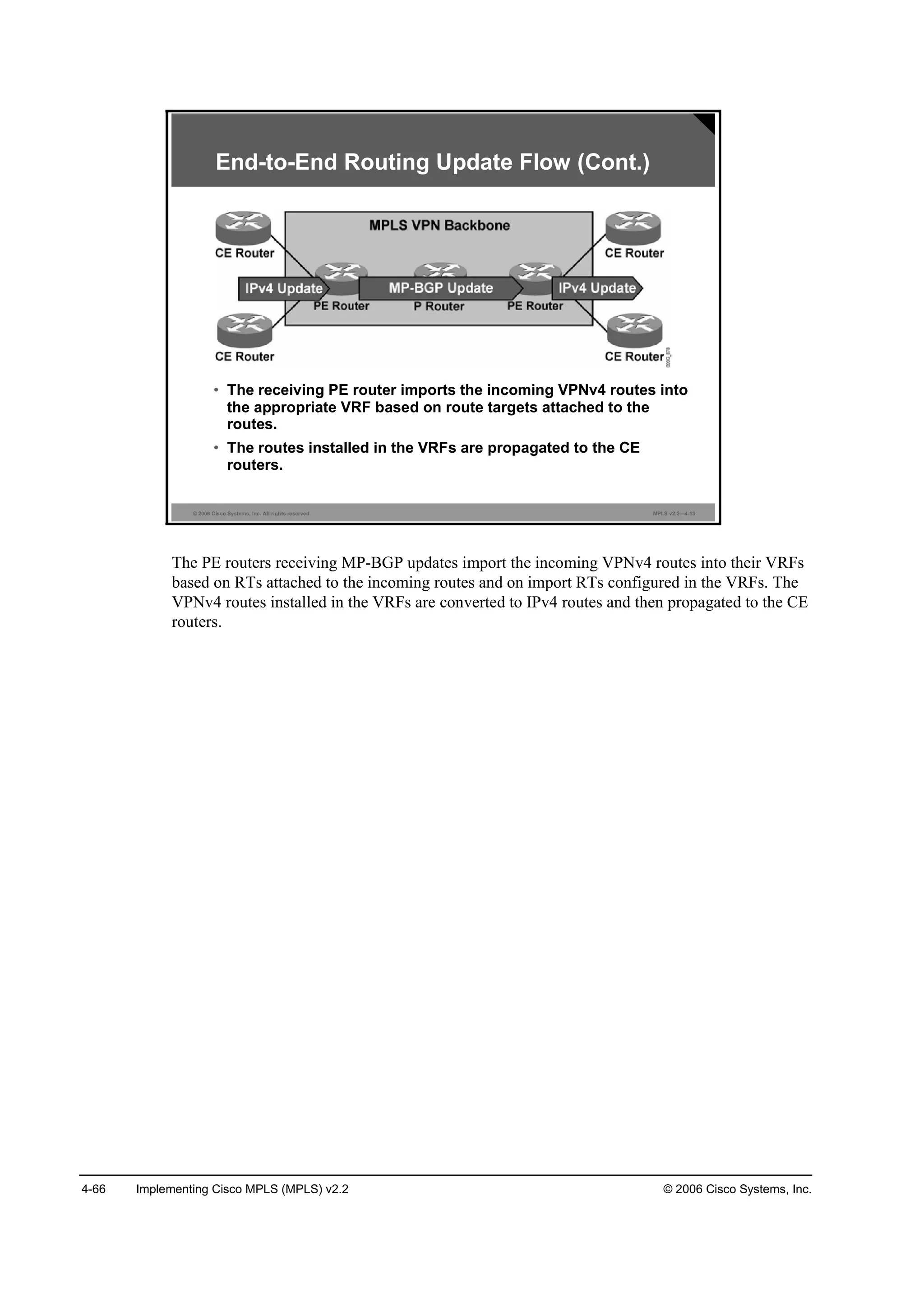


![4-78 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
What Are the Effects of MPLS VPNs on Label
Propagation?
This topic describes the effects of MPLS VPNs on label propagation.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—4-8
MPLS VPNs and Label Propagation
• The VPN label must be assigned by the BGP next hop.
• The BGP next hop should not be changed in the
MP-IBGP update propagation.
– Do not use the command on confederation
boundaries.
• The PE router must be the BGP next hop.
– Use the command on the PE router.
• The label must be reoriginated if the next hop is changed.
– A new label is assigned every time that the MP-BGP
update crosses the AS boundary where the next hop is
changed.
MPLS VPN packet forwarding works correctly only if the router specified as the BGP next hop
in the incoming BGP update is the same router as the one that assigned the second label in the
label stack. Here are three scenarios that can cause the BGP next hop to be different from the IP
address of the PE router assigning the VPN label:
If the customer route is received from the CE router via an External Border Gateway
Protocol (EBGP) session, the next hop of the VPNv4 route is still the IP address of the CE
router (the BGP next hop of an outgoing Internal Border Gateway Protocol [IBGP] update
is always identical to the BGP next hop of the incoming EBGP update). You have to
configure the next-hop-self command on the MP-BGP sessions between PE routers to
make sure that the BGP next hop of the VPNv4 route is always the IP address of the PE
router, regardless of the routing protocol used between the PE router and the CE router.
The BGP next hop should not change inside an autonomous system (AS). It can change,
however, if you use the next-hop-self command on an inter-AS boundary inside a BGP
confederation or if you use inbound the route-map command on a PE route to change the
next hop (a strongly discouraged practice). To prevent this situation, never change the BGP
next hop with the route-map or next-hop-self commands inside an AS.
The BGP next hop is always changed on an EBGP session. If the MPLS VPN network
spans multiple public autonomous systems (not just autonomous systems within a BGP
confederation), special provisions must be made in the AS boundary routers to reoriginate
the VPN label at the same time that the BGP next hop is changed. This functionality is
supported by Cisco IOS Releases 12.1(4)T, 12.2, and later.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-299-2048.jpg)


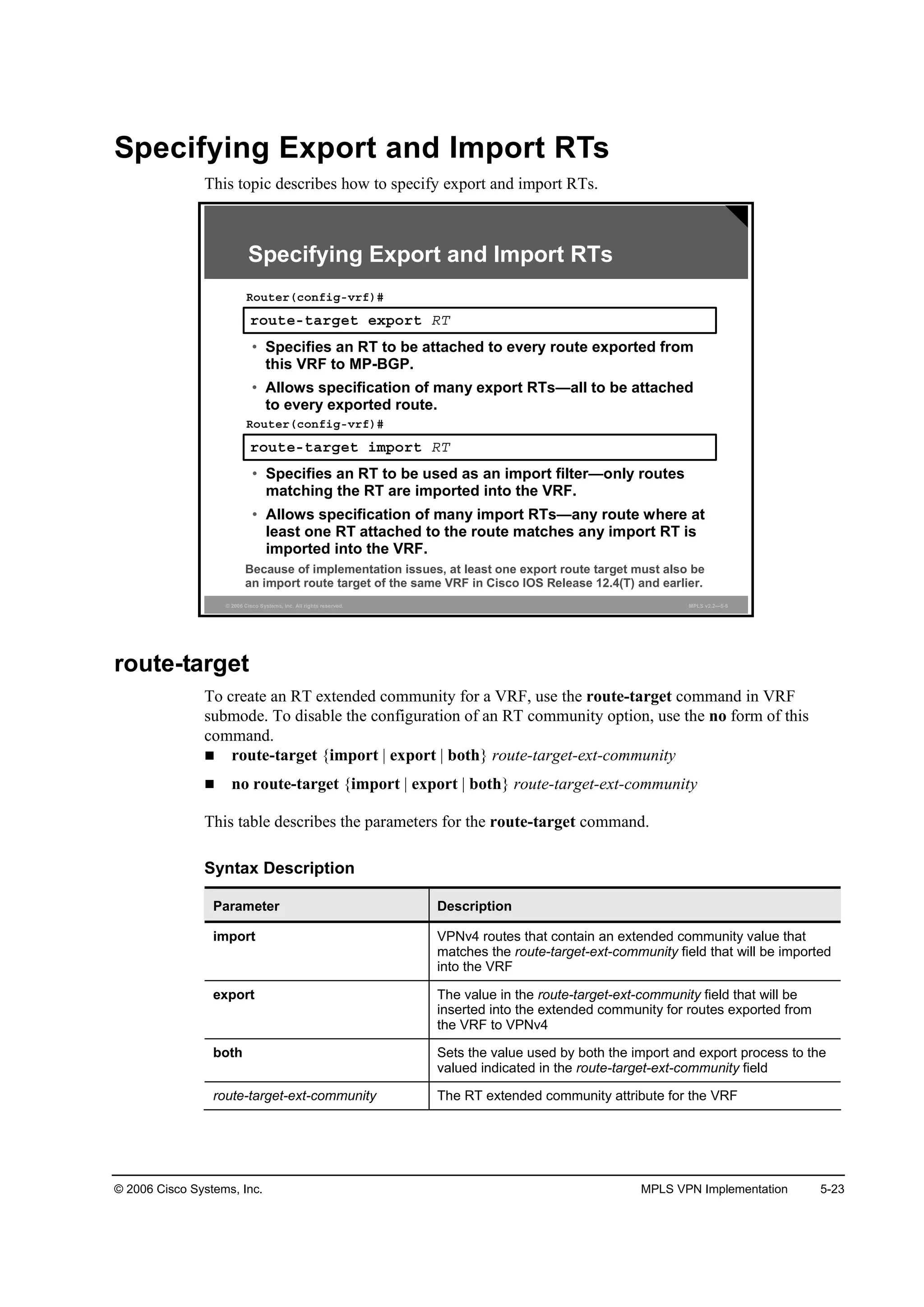
![5-4 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
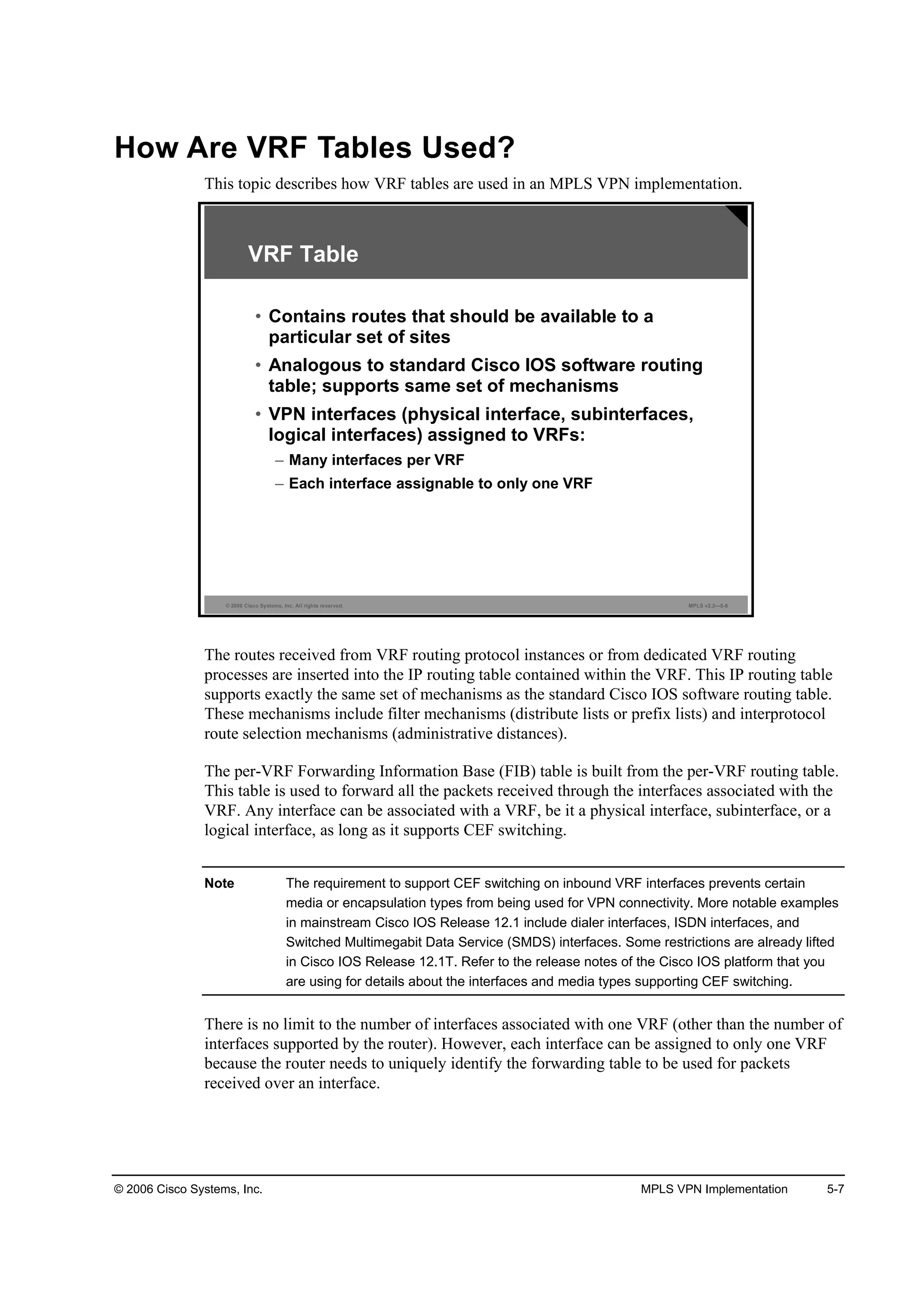
What Is a VRF Table?
This topic describes the characteristics of a VRF table.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-3
VRF Table
• A VRF is the routing and forwarding instance for a set
of sites with identical connectivity requirements.
• Data structures associated with a VRF are as follows:
– IP routing table
– CEF table
– Set of rules and routing protocol parameters
(routing protocol contexts)
– List of interfaces that use the VRF
• Other information associated with a VRF is as follows:
– Route distinguisher
– Set of import and export route targets
The major data structure associated with MPLS VPN implementation on Cisco IOS platforms
is the VRF table. This data structure encompasses an IP routing table identical in function to the
following:
The global IP routing table in Cisco IOS software
A Cisco Express Forwarding (CEF) table identical in function to the global CEF
forwarding table (Forwarding Information Base [FIB])
Specifications for routing protocols running inside the VRF instance
A VRF is a routing and forwarding instance that you can use for a single VPN site or for many
sites connected to the same provider edge (PE) router if and only if these sites share exactly the
same connectivity requirements.
Other MPLS VPN attributes associated with a VRF table are as follows:
The route distinguisher (RD), which is prepended (for example, RD + IP address) to all
routes exported from the VRF into the global VPN version 4 (VPNv4)—also called VPN
IP version 4 (IPv4) Border Gateway Protocol (BGP) table
A set of export route targets (RTs), which are attached to any route exported from the VRF
A set of import RTs, which are used to select VPNv4 routes that are to be imported into the
VRF](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-319-2048.jpg)

![5-34 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
address-family
To enter the address family submode for configuring routing protocols, such as BGP, Routing
Information Protocol (RIP), and static routing, use the address-family command in global
configuration mode. To disable the address family submode for configuring routing protocols,
use the no form of this command.
VPNv4 unicast:
— address-family vpnv4 [unicast]
— no address-family vpnv4 [unicast]
IPv4 unicast:
— address-family ipv4 [unicast]
— no address-family ipv4 [unicast]
IPv4 unicast with CE router:
— address-family ipv4 [unicast] vrf vrf-name
— no address-family ipv4 [unicast] vrf vrf-name
This table describes the address-family command.
Syntax Description
Parameter Description
·°Şě Configures sessions that carry standard IPv4 address prefixes
Ş°˛Şě Configures sessions that carry customer VPNv4 prefixes, each of
which has been made globally unique by adding an 8-byte route
distinguisher (RD)
«˛·˝ż¬ (Optional) Specifies unicast prefixes
Ş®ş Ş®şó˛żł» Specifies the name of a VPN VRF to associate with submode
commands](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-349-2048.jpg)

![5-42 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
neighbor send-community
To specify that BGP community attributes that are attached to a BGP route should be sent to a
BGP neighbor, use the neighbor send-community command in router configuration mode. To
remove the entry, use the no form of this command.
neighbor {ip-address | peer-group-name} send-community [extended | both]
no neighbor {ip-address | peer-group-name} send-community
This table describes the neighbor send-community command.
Syntax Description
Parameter Description
·°óżĽĽ®» Neighbor IP address
°»»®óą®±«°ó˛żł» Name of BGP peer group
Defaults
BGP communities are not propagated to any neighbor.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-357-2048.jpg)
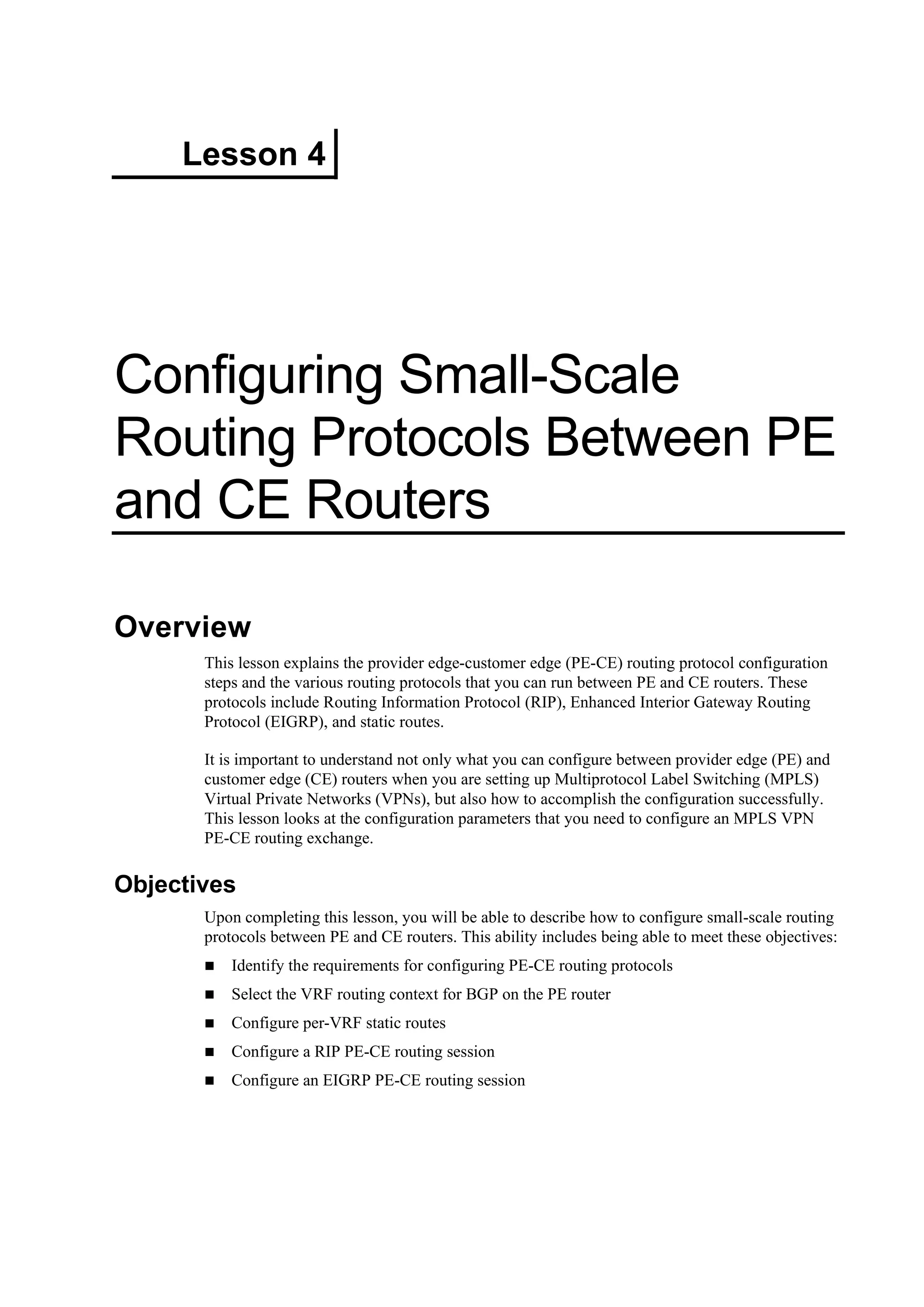
![5-48 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Configuring PE-CE Routing Protocols
This topic identifies the requirements for configuring PE-CE routing protocols.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-3
PE-CE Routing Protocols
• PE-CE routing protocols are configured for
individual VRFs.
• Per-VRF routing protocols can be configured in
two ways:
– Per-VRF parameters are specified in routing contexts,
which are selected with the address-family command.
– A separate OSPF process has to be started for each VRF.
• Prior to Cisco IOS Release 12.3(4)T, the overall
number of routing processes per router was
limited to 32, of which only 28 were available for
VRF assignment.
After you configure virtual routing and forwarding instances (VRFs) and establish
Multiprotocol Internal Border Gateway Protocol (MP-IBGP) connectivity between PE routers,
you have to configure routing protocols between the PE router and the attached CE routers. The
PE-CE routing protocols need to be configured for individual VRFs. Sites in the same VPN but
in different VRFs cannot share the same PE-CE routing protocol.
Note The per-VRF configuration of the PEvirtual-CE routing protocols is another good reason for
grouping as many sites into a VRF as possible.
The per-VRF routing protocols can be configured in these two ways:
Per-VRF routing protocols can be configured as individual address families belonging to
the same routing process (similar to what you have already seen for Border Gateway
Protocol [BGP]).
Per-VRF routing protocols can be configured as separate routing processes. This option is
used for more complex routing protocols that need to maintain a separate topology database
for each VRF (for example, Open Shortest Path First [OSPF]).
Note Prior to Cisco IOS Release 12.3(4)T, Cisco IOS software implementation limits the overall
number of routing protocols in a router to 32. Two routing methods are predefined (static
and connected), and two routing protocols are needed for proper MPLS VPN backbone
operation—BGP and backbone Interior Gateway Protocol (IGP). The number of PE-CE
routing processes was therefore limited to 28.
This restriction was removed for MPLS in Cisco IOS Release 12.3(4)T.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-363-2048.jpg)
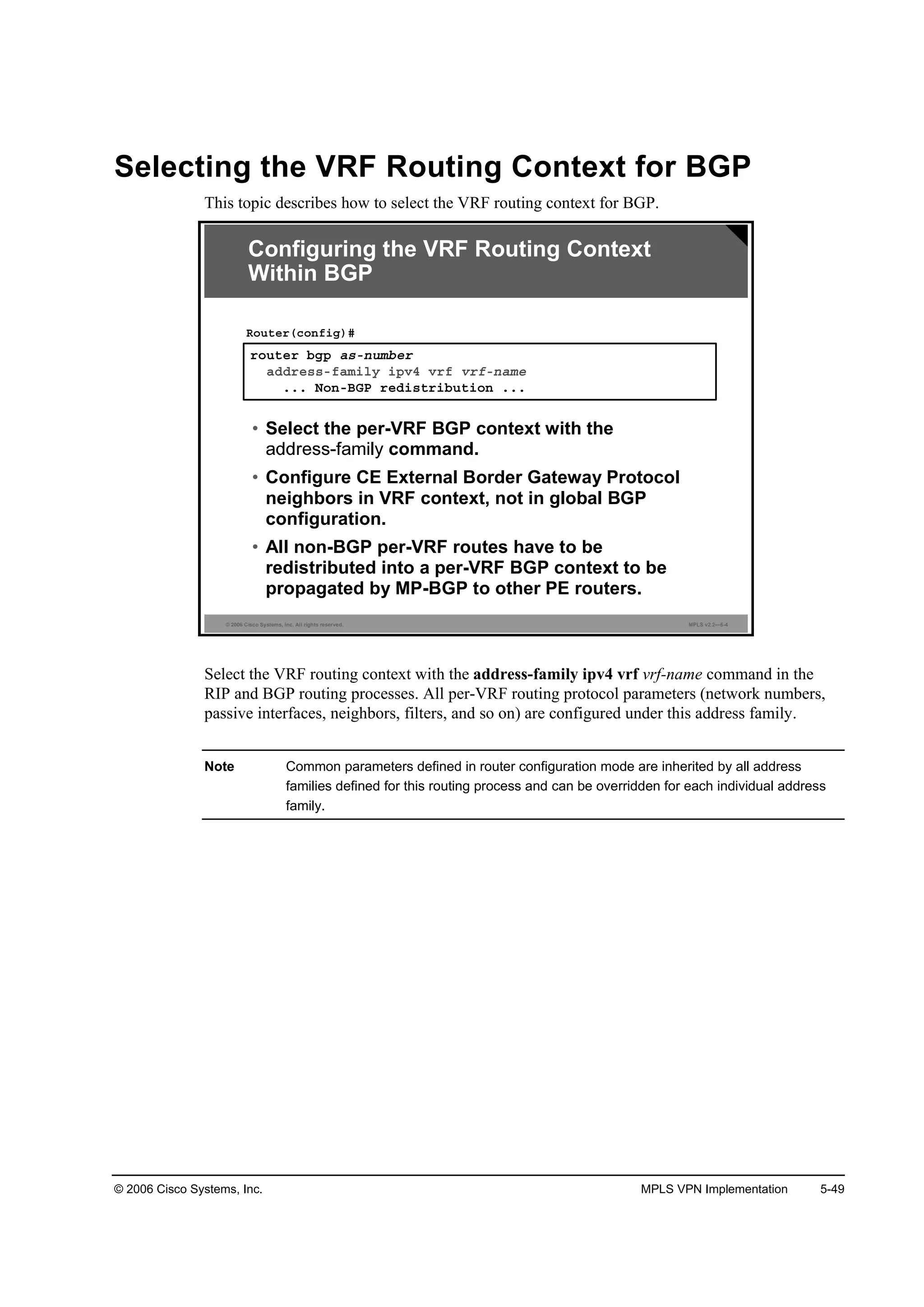
![5-50 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
address-family ipv4
To enter address family configuration mode for configuring routing sessions, such as BGP, that
use standard IP version 4 (IPv4) address prefixes, use the address-family ipv4 command in
router configuration mode. To disable address family configuration mode, use the no form of
this command.
address-family ipv4 [multicast | unicast | vrf vrf-name]
no address-family ipv4 [multicast | unicast | vrf vrf-name]
This table describes the address-family ipv4 command.
Syntax Description
Parameter Description
ł«´¬·˝ż¬ (Optional) Specifies IPv4 multicast address prefixes
«˛·˝ż¬ (Optional) Specifies IPv4 unicast address prefixes
Ş®ş Ş®şó˛żł» (Optional) Specifies the name of the VRF instance to associate
with subsequent IPv4 address family configuration mode
commands
Defaults
IPv4 address prefixes are not enabled. Unicast address prefixes are the default when IPv4
address prefixes are configured.
Command Modes
This command is used in router configuration mode.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-365-2048.jpg)
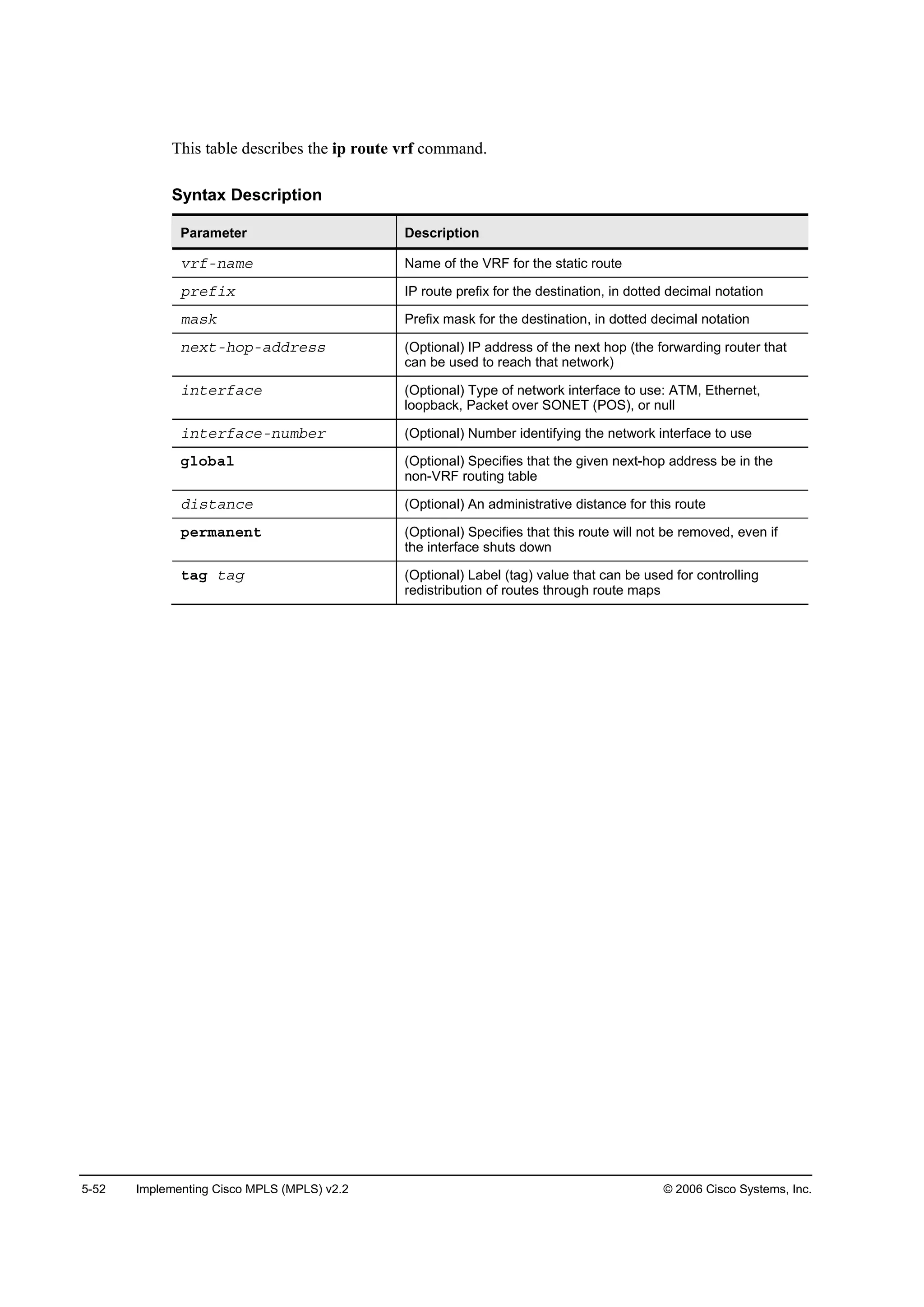
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-51
Configuring Per-VRF Static Routes
This topic describes how to configure per-VRF static routes.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-5
·° ®±«¬» Ş®ş Ý«¬±ł»®ÁßŢÝ ďđňđňđňđ îëëňđňđňđ »®·ż´đńđ ďđňîëđňđňî
˙
®±«¬»® ľą° ęëďéí
żĽĽ®»óşżł·´§ ·°Şě Ş®ş Ý«¬±ł»®ÁßŢÝ
®»Ľ·¬®·ľ«¬» ¬ż¬·˝
Configuring Per-VRF Static Routes
·° ®±«¬» Ş®ş Ş®şó˛żł» °®»ş·¨ łżµ Ĺ·˛¬»®şż˝» ·˛¬»®şż˝»ó
˛«łľ»®Ă Ų»¨¬ó¸±°óżĽĽ®»Ă
᫬»®ř˝±˛ş·ą÷ý
• This command configures per-VRF static routes.
• The route is entered in the VRF table.
• You must specify a next-hop IP address if you are
not using a point-to-point interface.
Sample router configuration:
ip route vrf
To establish static routes for a VRF, use the ip route vrf command in global configuration
mode. To disable static routes, use the no form of this command.
ip route vrf vrf-name prefix mask [interface {interface-number}] [next-hop-address]
[global] [distance] [permanent] [tag tag]
no ip route vrf vrf-name prefix mask [interface {interface-number}] [next-hop-address]
[global] [distance] [permanent] [tag tag]
Note You must specify a next-hop IP address if you are not using a point-to-point interface.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-366-2048.jpg)
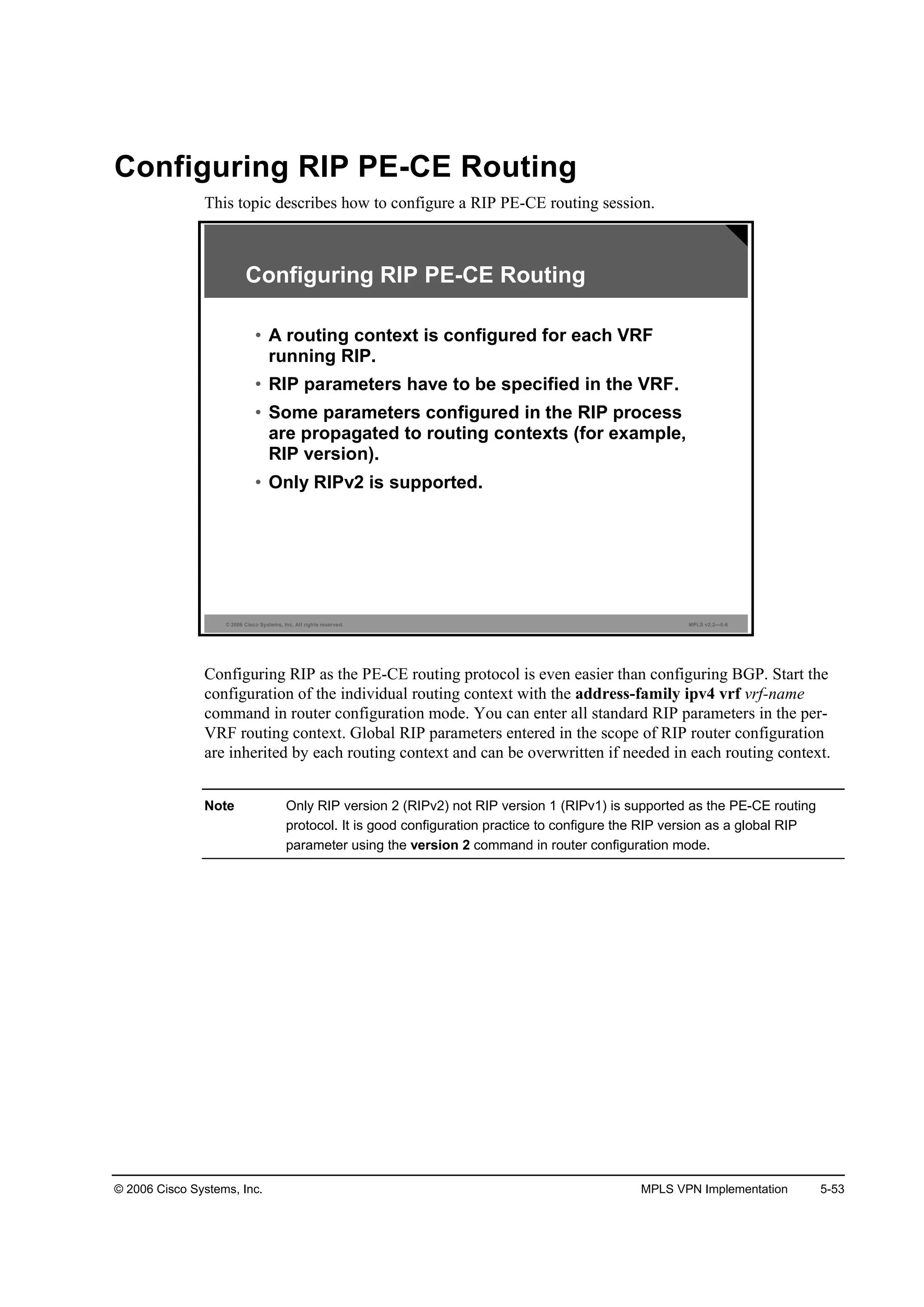
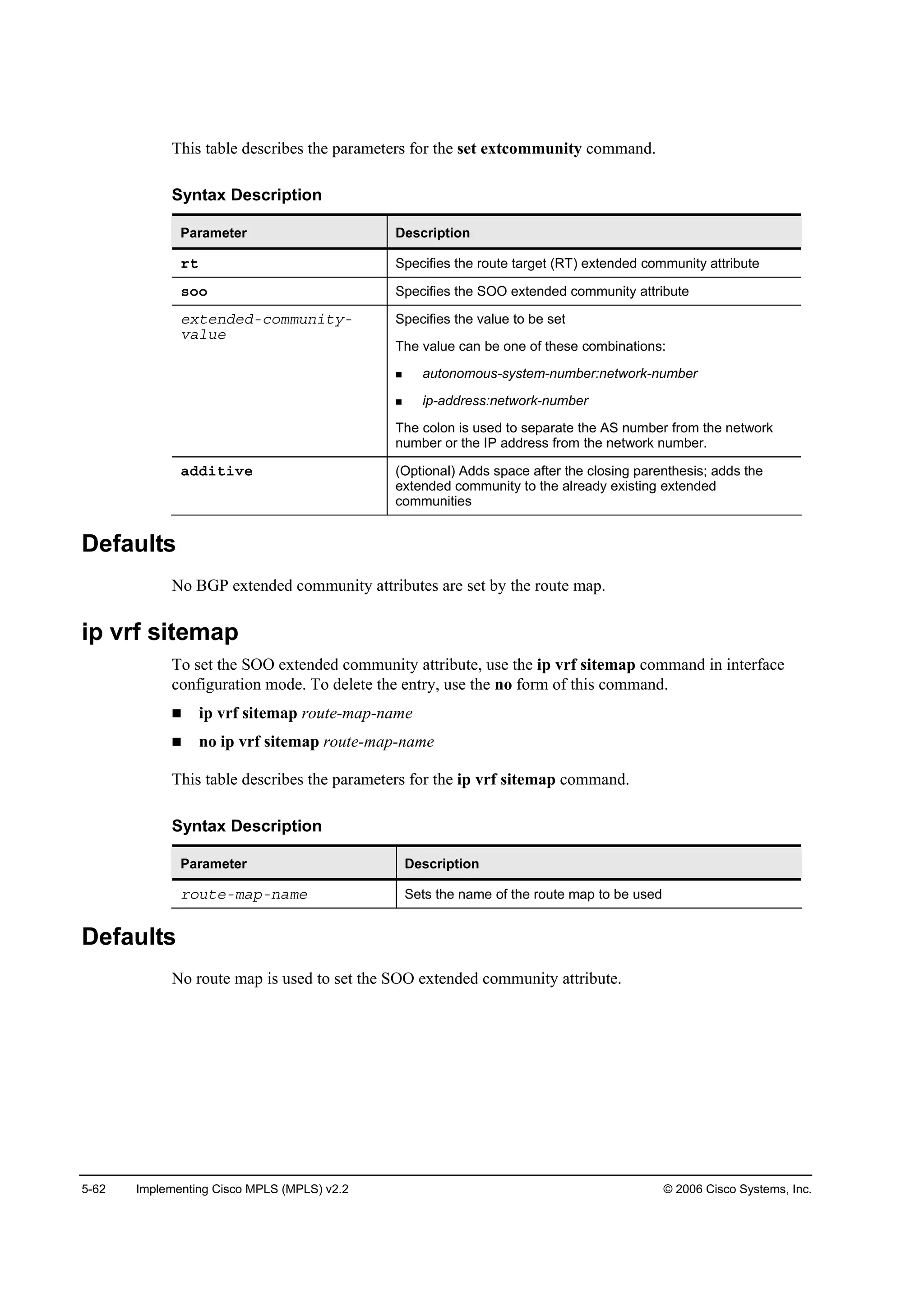
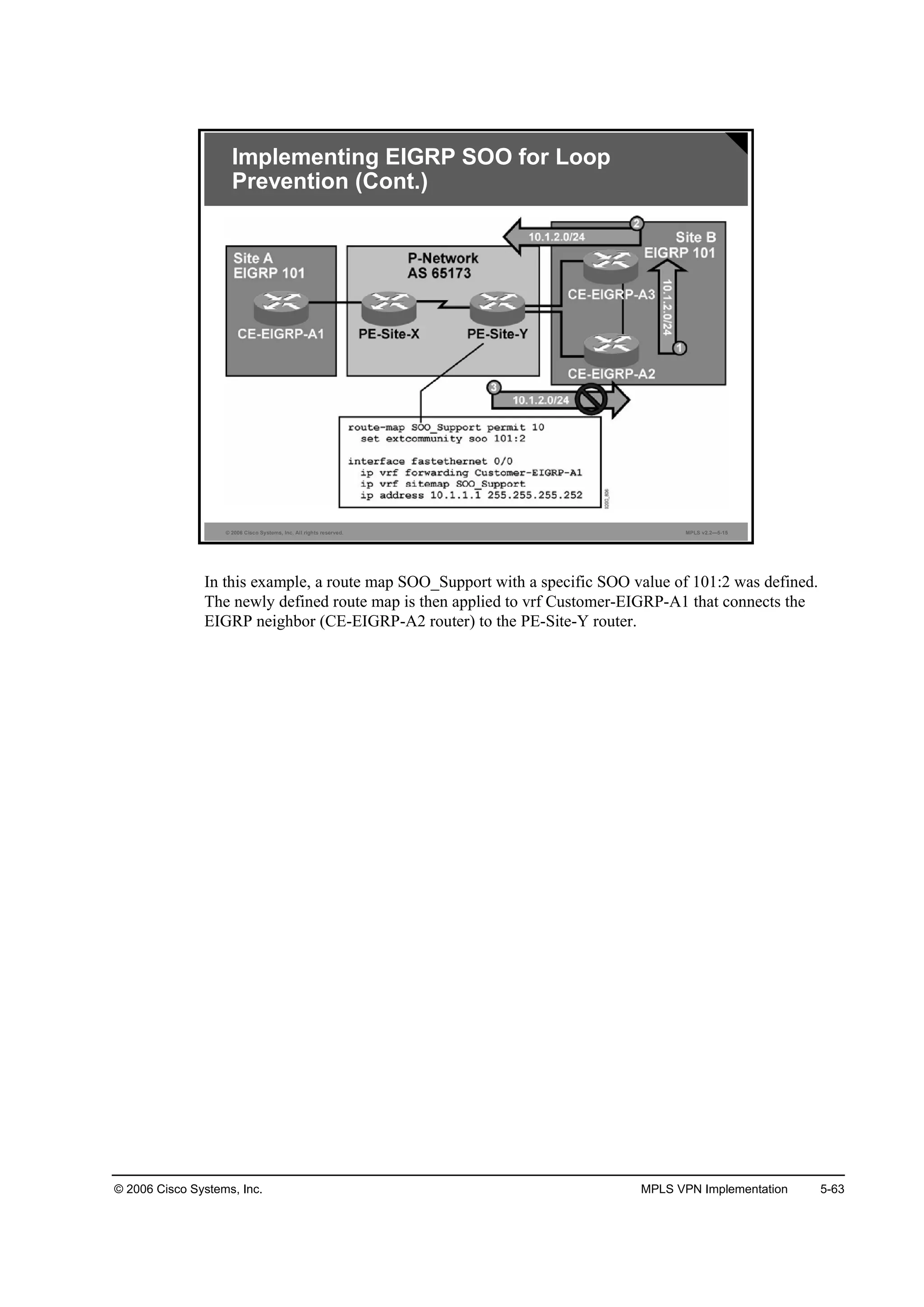
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-61
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-14
®±«¬»ółż° ˛żł» °»®ł·¬ »Ż
»¬ »¨¬˝±łł«˛·¬§ ±± »¨¬»˛Ľ»Ľó˝±łł«˛·¬§óŞż´«»
᫬»®ř˝±˛ş·ą÷ý
• Creates a route map that sets the SOO attribute
·° Ş®ş ş±®©ż®Ľ·˛ą Ş®şó˛żł»
·° Ş®ş ·¬»łż° ®±«¬»ółż°ó˛żł»
·° żĽĽ®» ·°óżĽĽ®» «ľ˛»¬ółżµ
᫬»®ř˝±˛ş·ąó·ş÷ý
• Applies a route map that sets SOO extended
community attribute to inbound routing updates
received from this interface
Implementing EIGRP SOO for Loop
Prevention (Cont.)
set extcommunity
To set the extended communities attribute, use the set extcommunity command in route map
configuration mode. To delete the entry, use the no form of this command.
set extcommunity {rt extended-community-value [additive] | soo extended-community-
value}
no set extcommunity
set extcommunity extcommunity-type community-number [additive]
no set extcommunity extcommunity-type community-number [additive]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-376-2048.jpg)
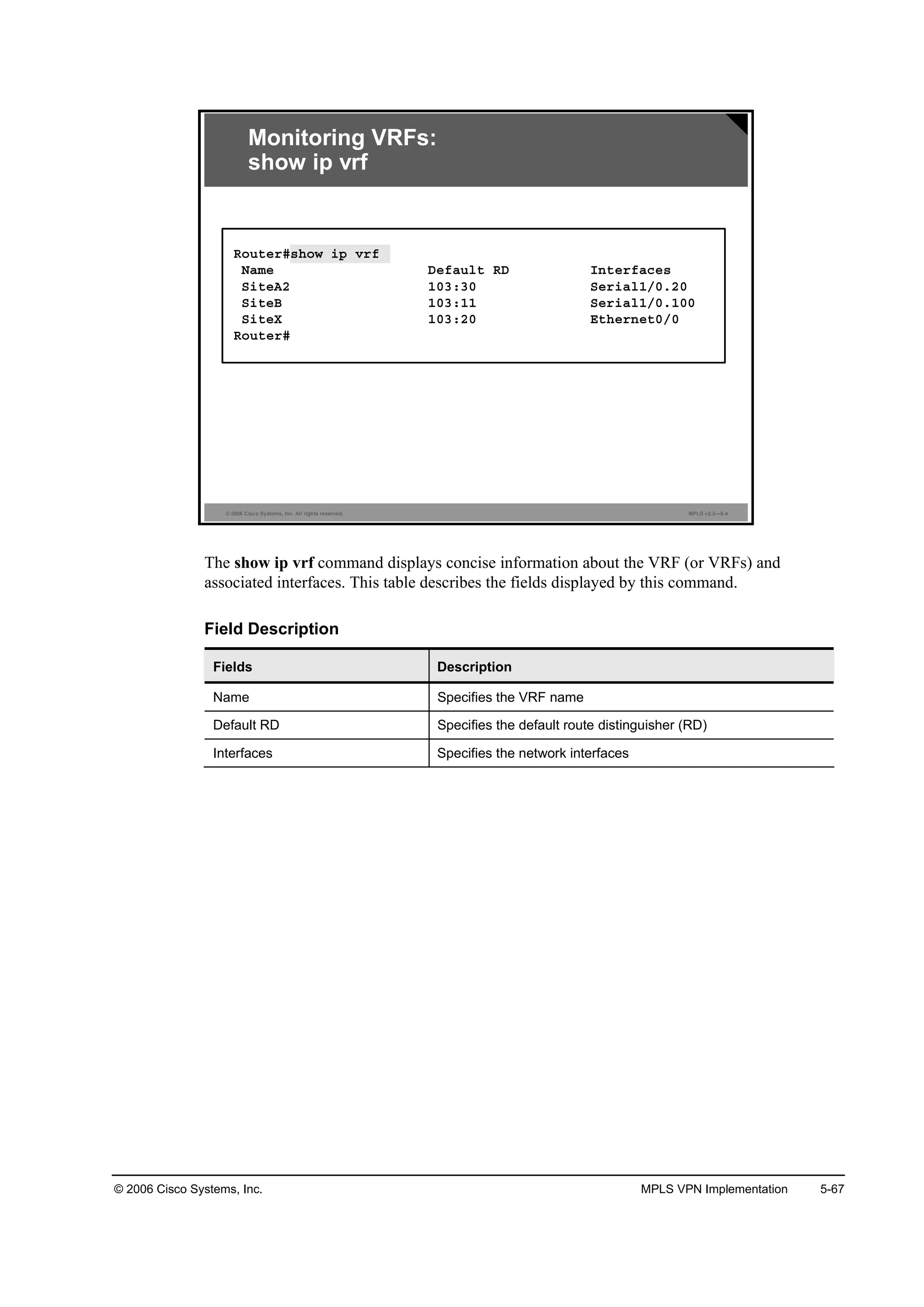
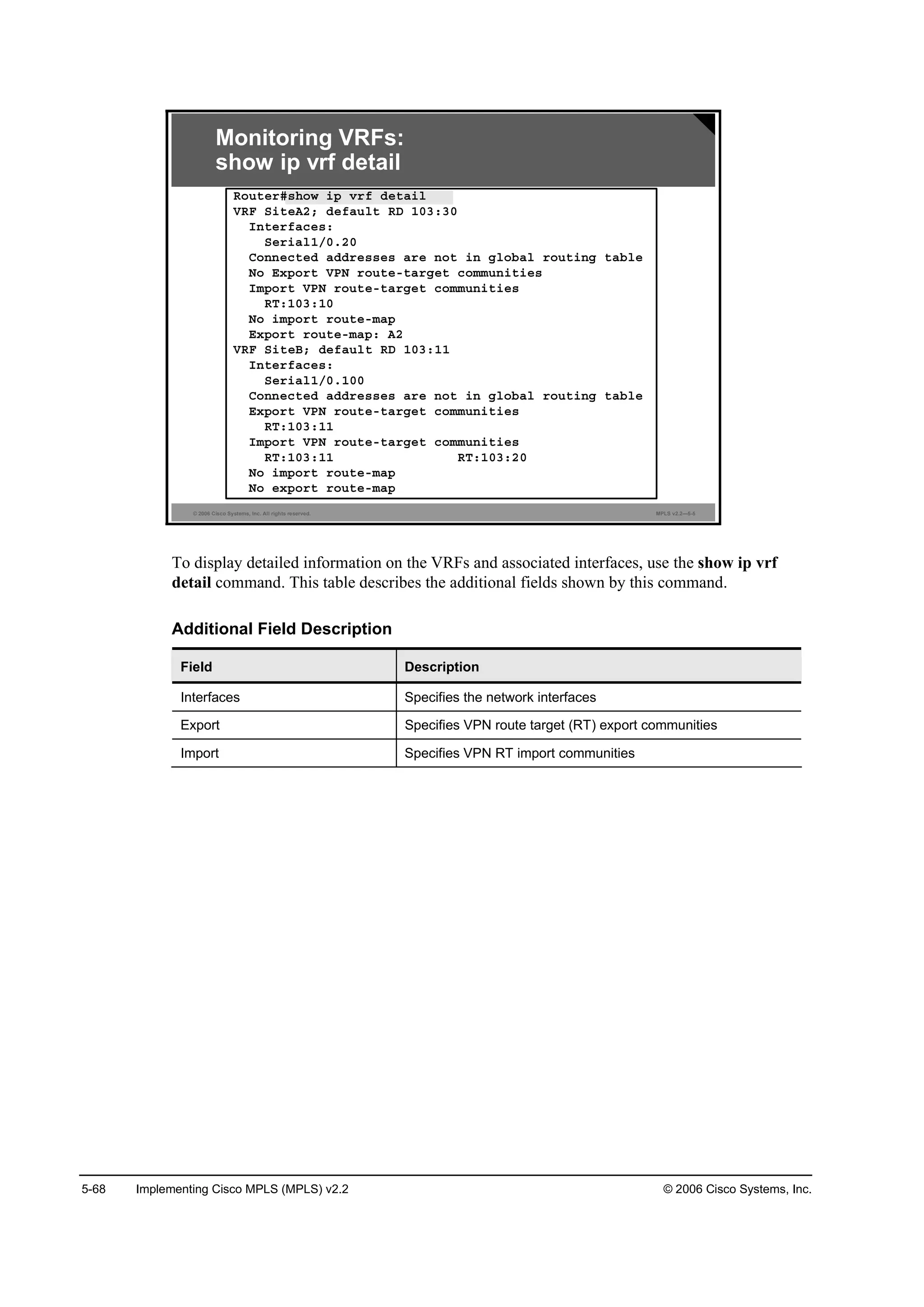
![5-66 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Monitoring VRFs
This topic describes how to monitor VRF information.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-3
¸±© ·° Ş®ş
᫬»®ý
• Displays the list of all VRFs configured in the router
¸±© ·° Ş®ş Ľ»¬ż·´
᫬»®ý
• Displays detailed VRF configuration
¸±© ·° Ş®ş ·˛¬»®şż˝»
᫬»®ý
• Displays interfaces associated with VRFs
Monitoring VRFs
show ip vrf
To display the set of defined VRFs and associated interfaces, use the show ip vrf command in
EXEC mode: show ip vrf [{brief | detail | interfaces}] [vrf-name] [output-modifiers].
This table describes the parameters for the show ip vrf command.
Syntax Description
Parameter Description
ľ®·»ş (Optional) Displays concise information on the VRF (or VRFs)
and associated interfaces
Ľ»¬ż·´ (Optional) Displays detailed information on the VRF (or VRFs)
and associated interfaces
·˛¬»®şż˝» (Optional) Displays detailed information about all interfaces
bound to a particular VRF or to any VRF
Ş®şó˛żł» (Optional) Displays the name assigned to a VRF
±«¬°«¬ół±Ľ·ş·»® (Optional) For a list of associated keywords and arguments, use
context-sensitive help
Defaults
When no optional parameters are specified, the command shows concise information about all
configured VRFs.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-381-2048.jpg)
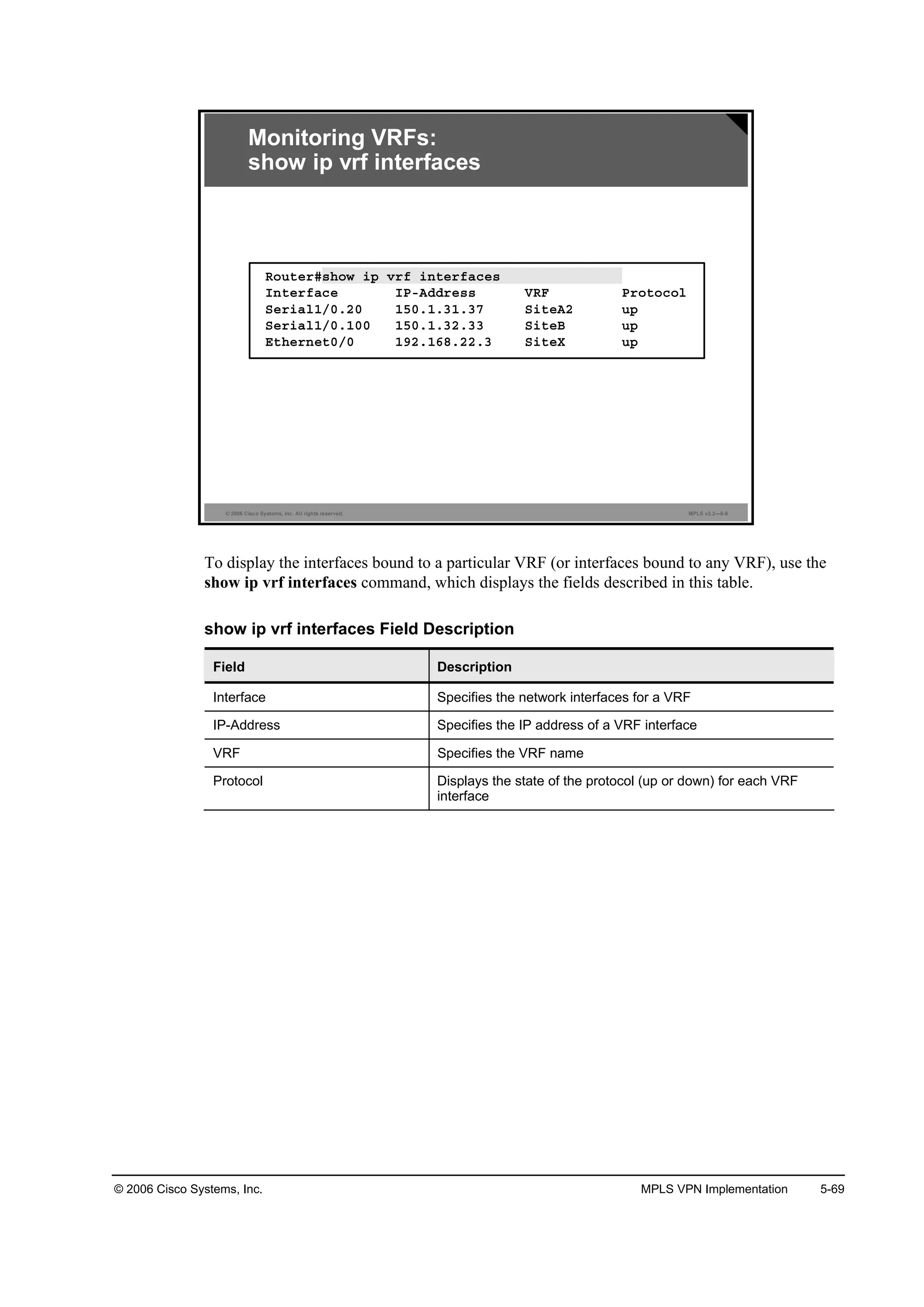
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-71
show ip route vrf
To display the IP routing table associated with a VRF, use the show ip route vrf command in
EXEC mode: show ip route vrf vrf-name [connected] [protocol [as-number] [tag] [output-
modifiers]] [list number [output-modifiers]] [profile] [static [output-modifiers]] [summary
[output-modifiers]] [supernets-only [output-modifiers]] [traffic-engineering [output-
modifiers]].
This table describes the parameters for the show ip route vrf command.
Syntax Description
Parameter Description
Ş®şó˛żł» Specifies the name assigned to the VRF
˝±˛˛»˝¬»Ľ (Optional) Displays all connected routes in a VRF
°®±¬±˝±´ (Optional) To specify a routing protocol, use one of these
keywords: bgp, egp, eigrp, hello, igrp, isis, ospf, or rip
żó˛«łľ»® (Optional) Specifies the autonomous system (AS) number
¬żą (Optional) Specifies Cisco IOS software routing area label
±«¬°«¬ół±Ľ·ş·»® (Optional) For a list of associated keywords and arguments, use
context-sensitive help
´·¬ ˛«łľ»® (Optional) Specifies the IP access list to display
°®±ş·´» (Optional) Displays the IP routing table profile
¬ż¬·˝ (Optional) Displays static routes
«łłż®§ (Optional) Displays a summary of routes
«°»®˛»¬ó±˛´§ (Optional) Displays supernet entries only
¬®żşş·˝ó»˛ą·˛»»®·˛ą (Optional) Displays only traffic-engineered routes](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-386-2048.jpg)
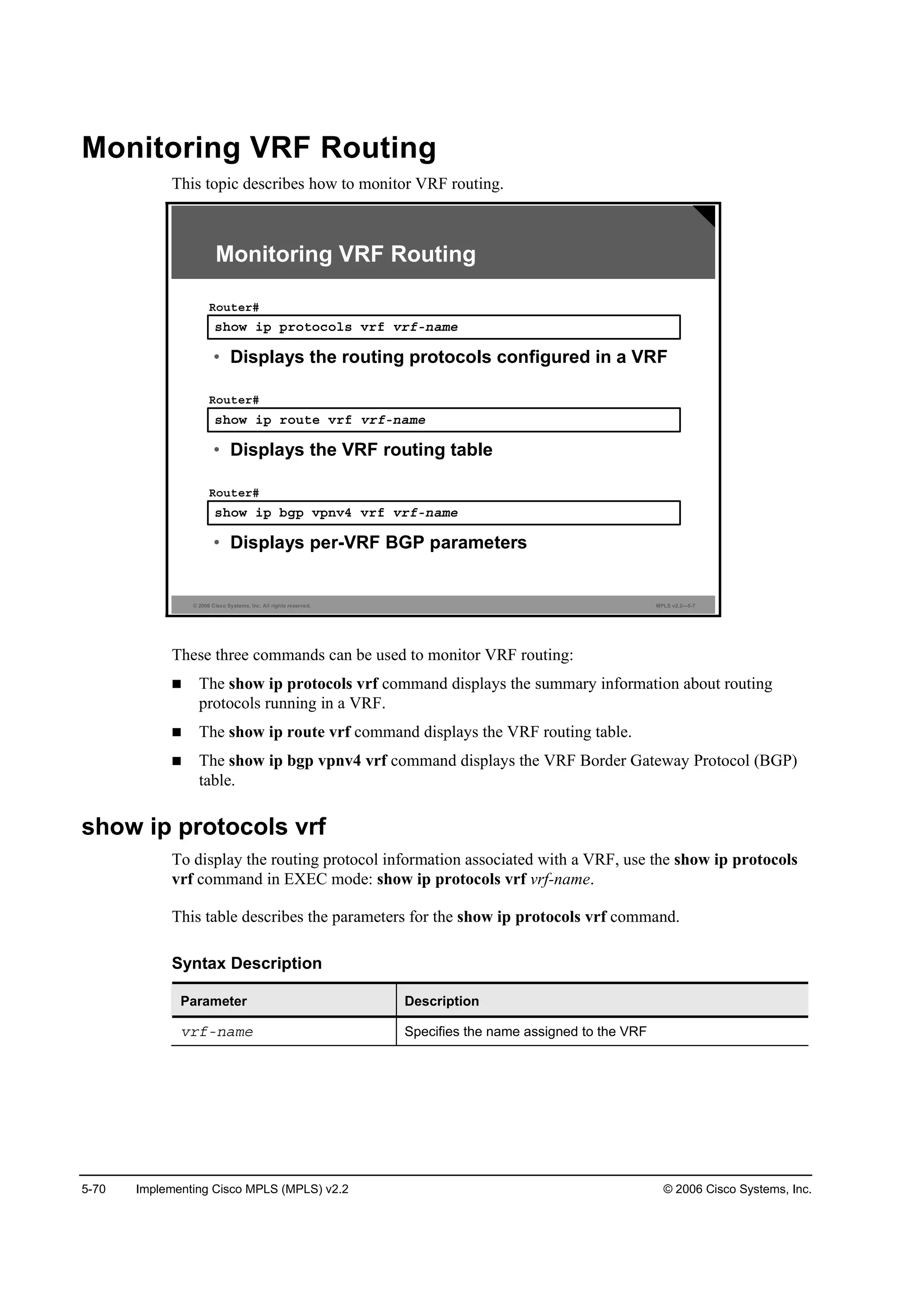
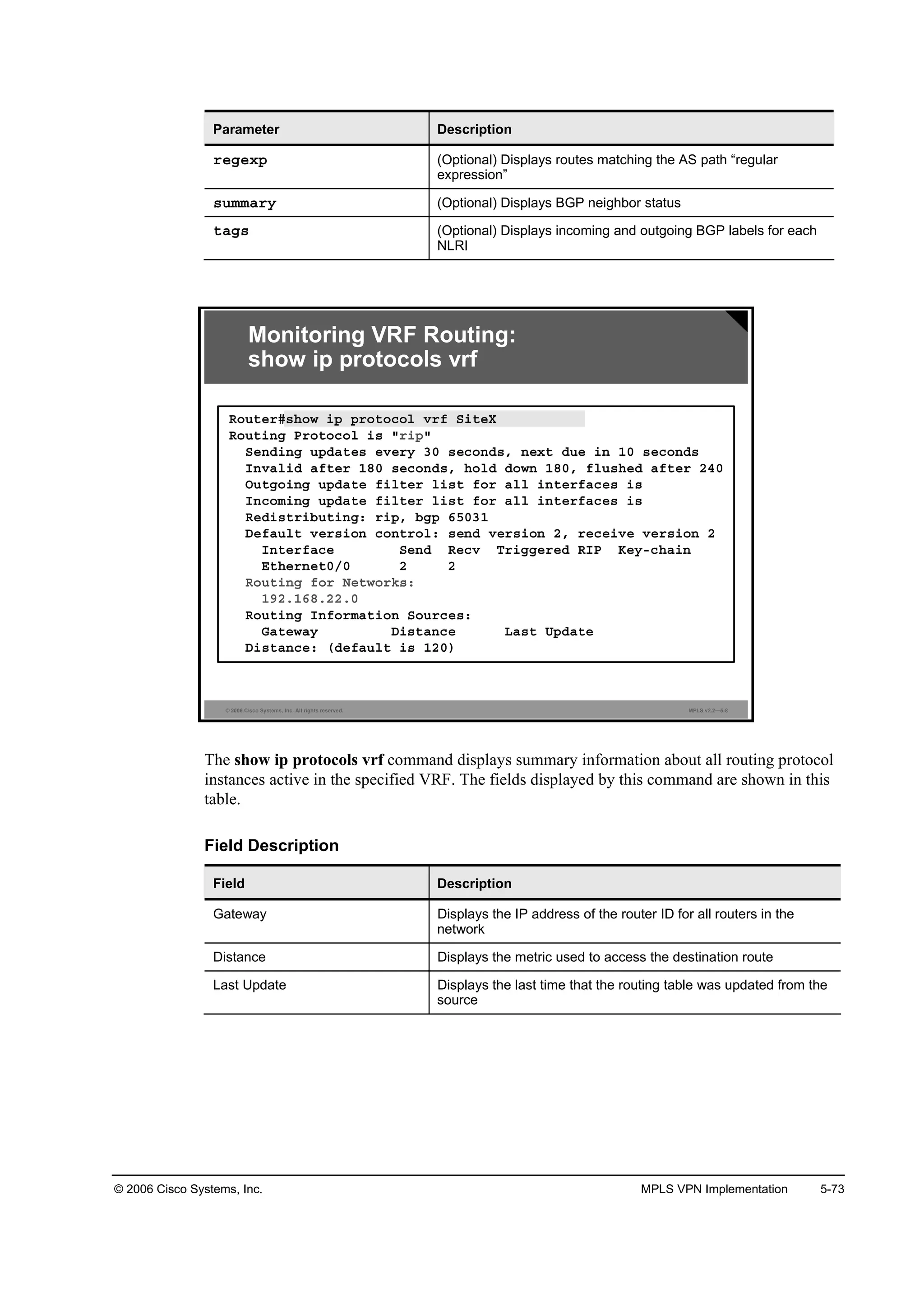
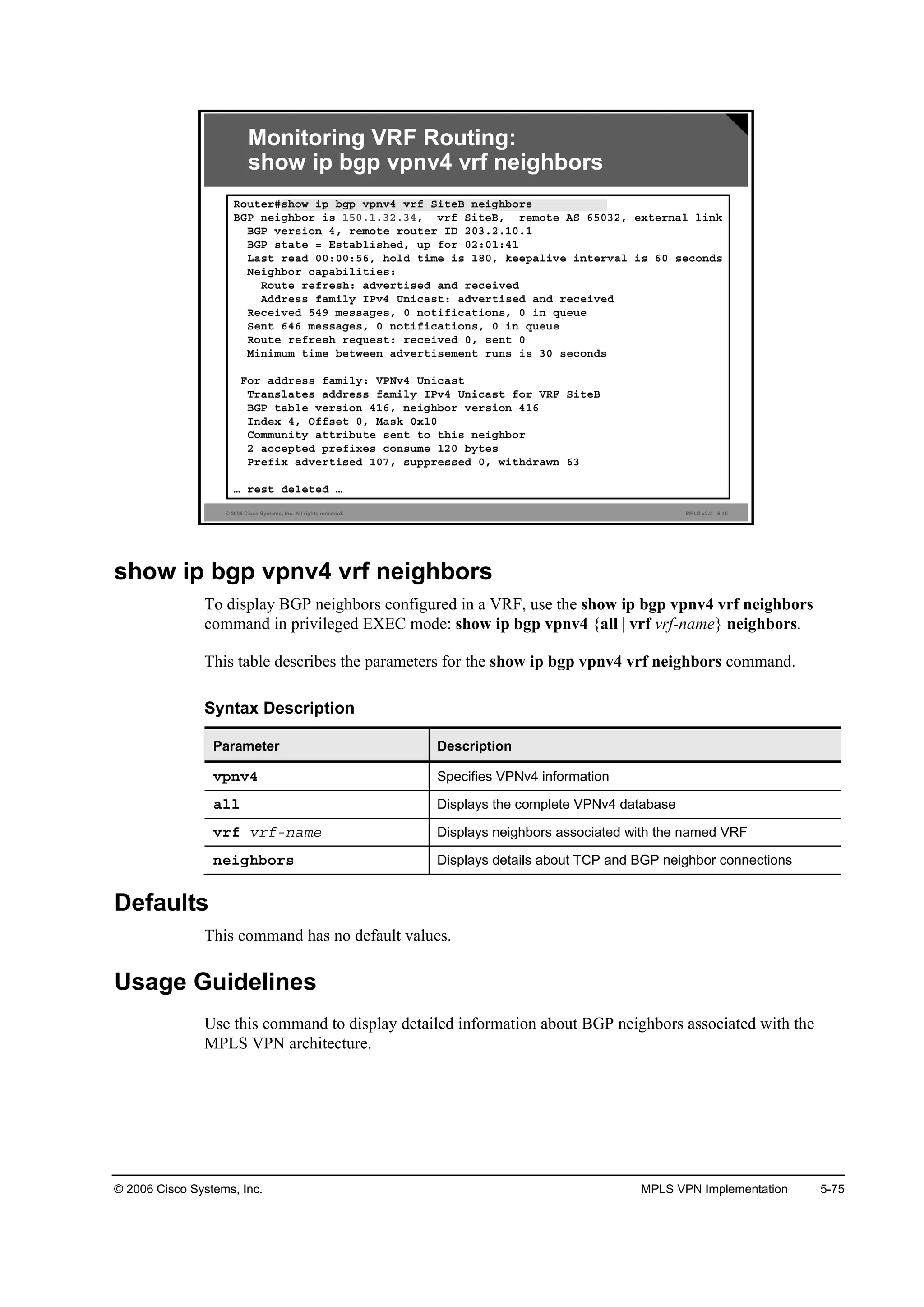
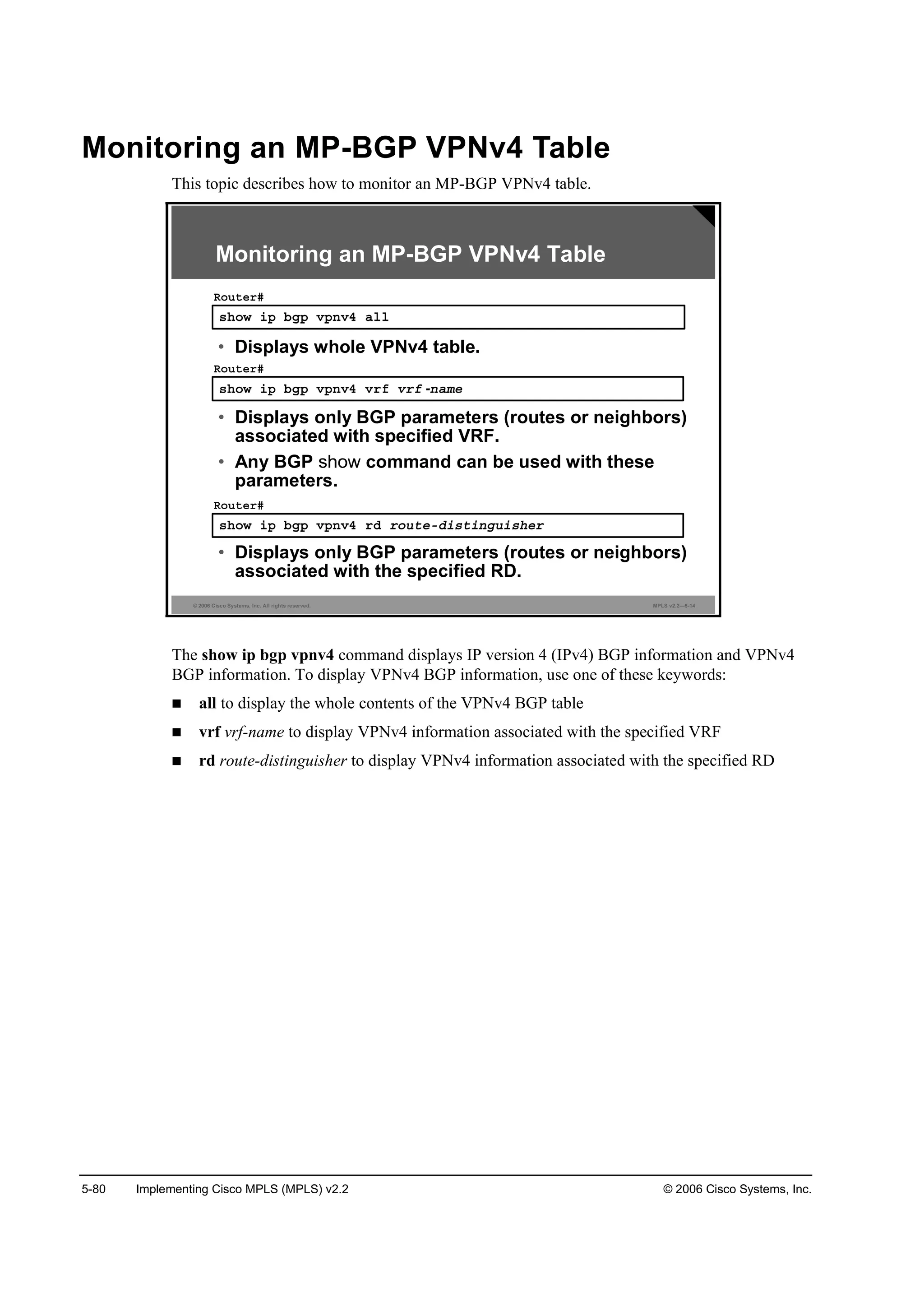
![5-72 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
show ip bgp vpnv4
To display VPN address information from the BGP table, use the show ip bgp vpnv4
command in EXEC mode: show ip bgp vpnv4 {all | rd route-distinguisher | vrf vrf-name} [ip-
prefix/length [longer-prefixes] [output-modifiers]] [network-address [mask] [longer-prefixes]
[output-modifiers]] [cidr-only] [community] [community-list] [dampened-paths] [filter-list]
[flap-statistics] [inconsistent-as] [neighbors] [paths [line]] [peer-group] [quote-regexp]
[regexp] [summary] [labels].
This table describes the parameters for the show ip bgp vpnv4 command.
Syntax Description
Parameter Description
ż´´ Displays the complete VPN version 4 (VPNv4) database
®Ľ ®±«¬»óĽ·¬·˛ą«·¸»® Displays Network Layer Reachability Information (NLRI) prefixes
that have a matching RD
Ş®ş Ş®şó˛żł» Displays NLRI prefixes associated with the named VRF
·°ó°®»ş·¨ń´»˛ą¬¸ (Optional) Displays the IP prefix address (in dotted decimal
notation) and length of mask (0 to 32)
´±˛ą»®ó°®»ş·¨» (Optional) Displays the entry, if any, that exactly matches the
specified prefix parameter, and all entries that match the prefix
in a “longest-match” sense—that is, prefixes for which the
specified prefix is an initial substring
±«¬°«¬ół±Ľ·ş·»® (Optional) For a list of associated keywords and arguments, use
context-sensitive help
˛»¬©±®µóżĽĽ®» (Optional) Displays the IP address of a network in the BGP
routing table
łżµ (Optional) Displays the mask of the network address, in dotted
decimal notation
˝·Ľ®ó±˛´§ (Optional) Displays only routes that have non-natural net masks
˝±łł«˛·¬§ (Optional) Displays routes matching this community
˝±łł«˛·¬§ó´·¬ (Optional) Displays routes matching this community list
Ľżł°»˛»Ľó°ż¬¸ (Optional) Displays paths suppressed on account of dampening
(BGP route from peer is up and down)
ş·´¬»®ó´·¬ (Optional) Displays routes conforming to the filter list
ş´ż°ó¬ż¬·¬·˝ (Optional) Displays flap statistics of routes
·˛˝±˛·¬»˛¬óż (Optional) Displays only routes that have inconsistent
autonomous systems of origin
˛»·ą¸ľ±® (Optional) Displays details about TCP and BGP neighbor
connections
°ż¬¸ (Optional) Displays path information
´·˛» (Optional) Displays a regular expression to match the BGP AS
paths
°»»®óą®±«° (Optional) Displays information about peer groups
Ż«±¬»ó®»ą»¨° (Optional) Displays routes matching the AS path “regular
expression”](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-387-2048.jpg)

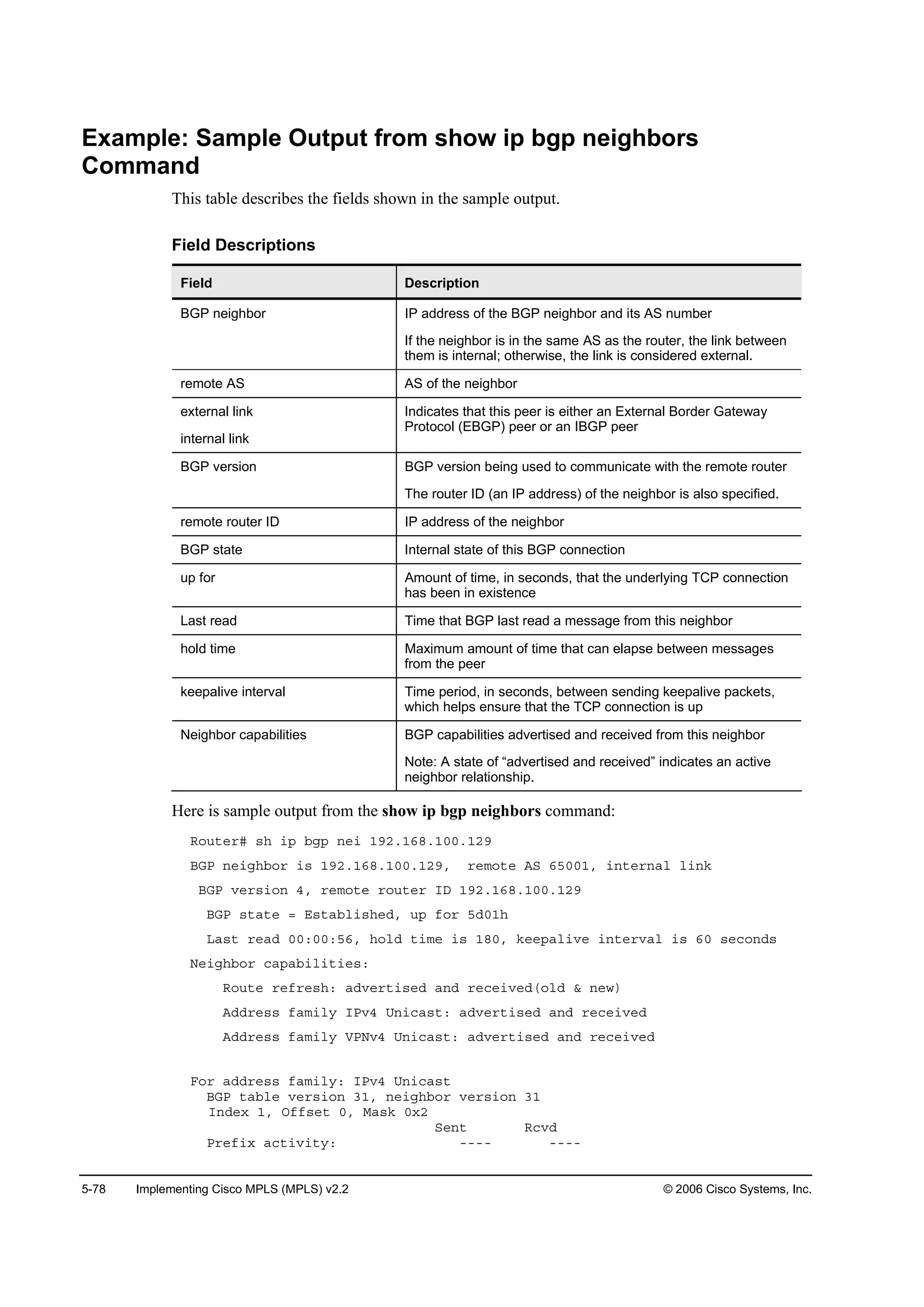
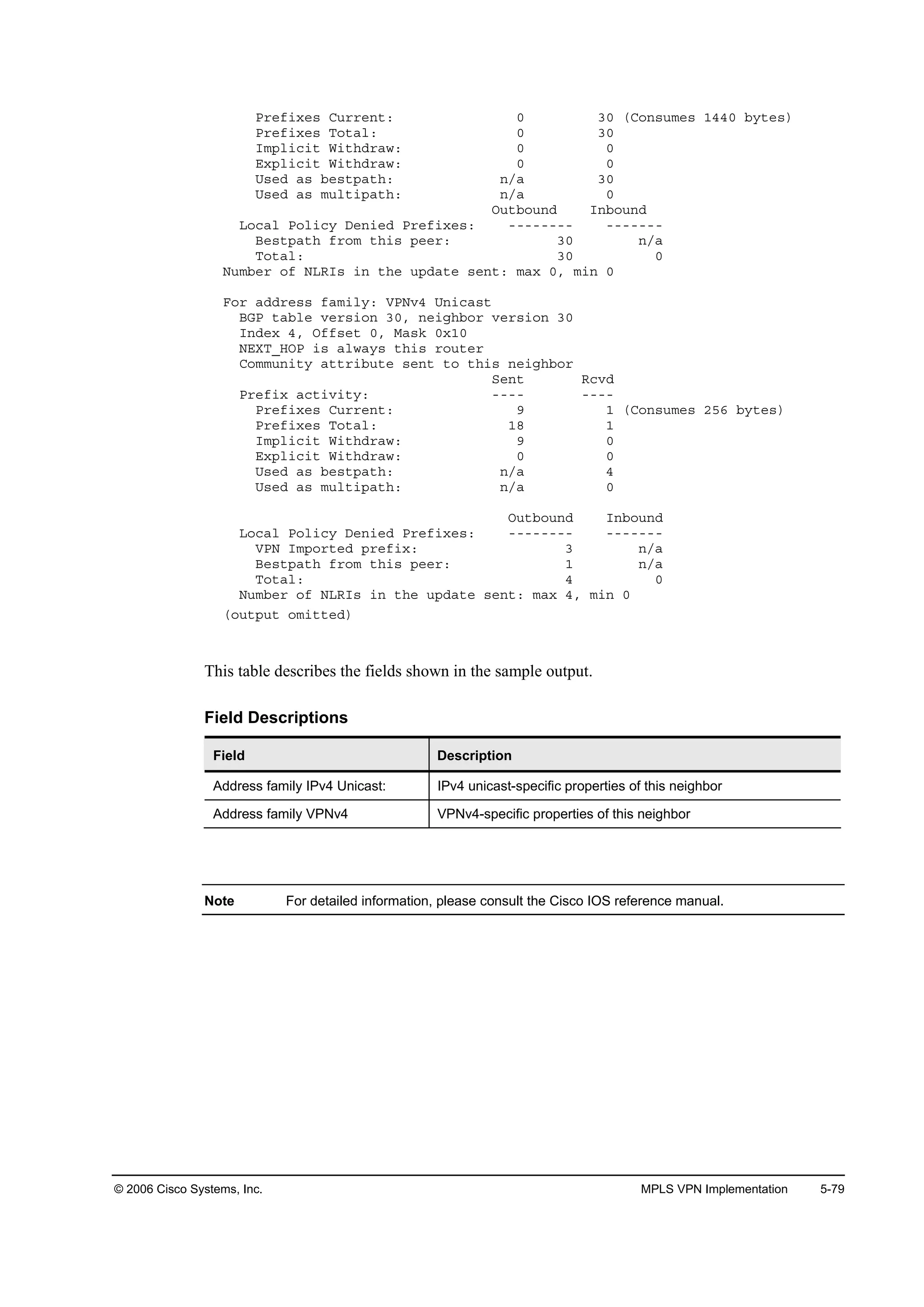
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-77
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-13
Monitoring MP-BGP Sessions:
show ip bgp neighbors (Cont.)
᫬»®ý¸±© ·° ľą° ˛»·ą¸ľ±® ďçîňďęčňíňďđď
ňňň ݱ˛¬·˛«»Ľ
Ú±® żĽĽ®» şżł·´§ć ĘĐŇŞě ˲·˝ż¬
ŢŮĐ ¬żľ´» Ş»®·±˛ ěďęô ˛»·ą¸ľ±® Ş»®·±˛ ěďę
ײĽ»¨ îô Ńşş»¬ đô Óżµ đ¨ě
ŇŰČĚÁŘŃĐ · ż´©ż§ ¬¸· ®±«¬»®
ݱłł«˛·¬§ ż¬¬®·ľ«¬» »˛¬ ¬± ¬¸· ˛»·ą¸ľ±®
ę ż˝˝»°¬»Ľ °®»ş·¨» ˝±˛«ł» íę𠾧¬»
Đ®»ş·¨ żĽŞ»®¬·»Ľ ěíďô «°°®»»Ľ đô ©·¬¸Ľ®ż©˛ ďďí
ݱ˛˛»˝¬·±˛ »¬żľ´·¸»Ľ éĺ Ľ®±°°»Ľ ę
Ôż¬ ®»»¬ đîćďčćííô Ľ«» ¬± Đ»»® ˝´±»Ľ ¬¸» »·±˛
ňňň λ¬ Ľ»´»¬»Ľ
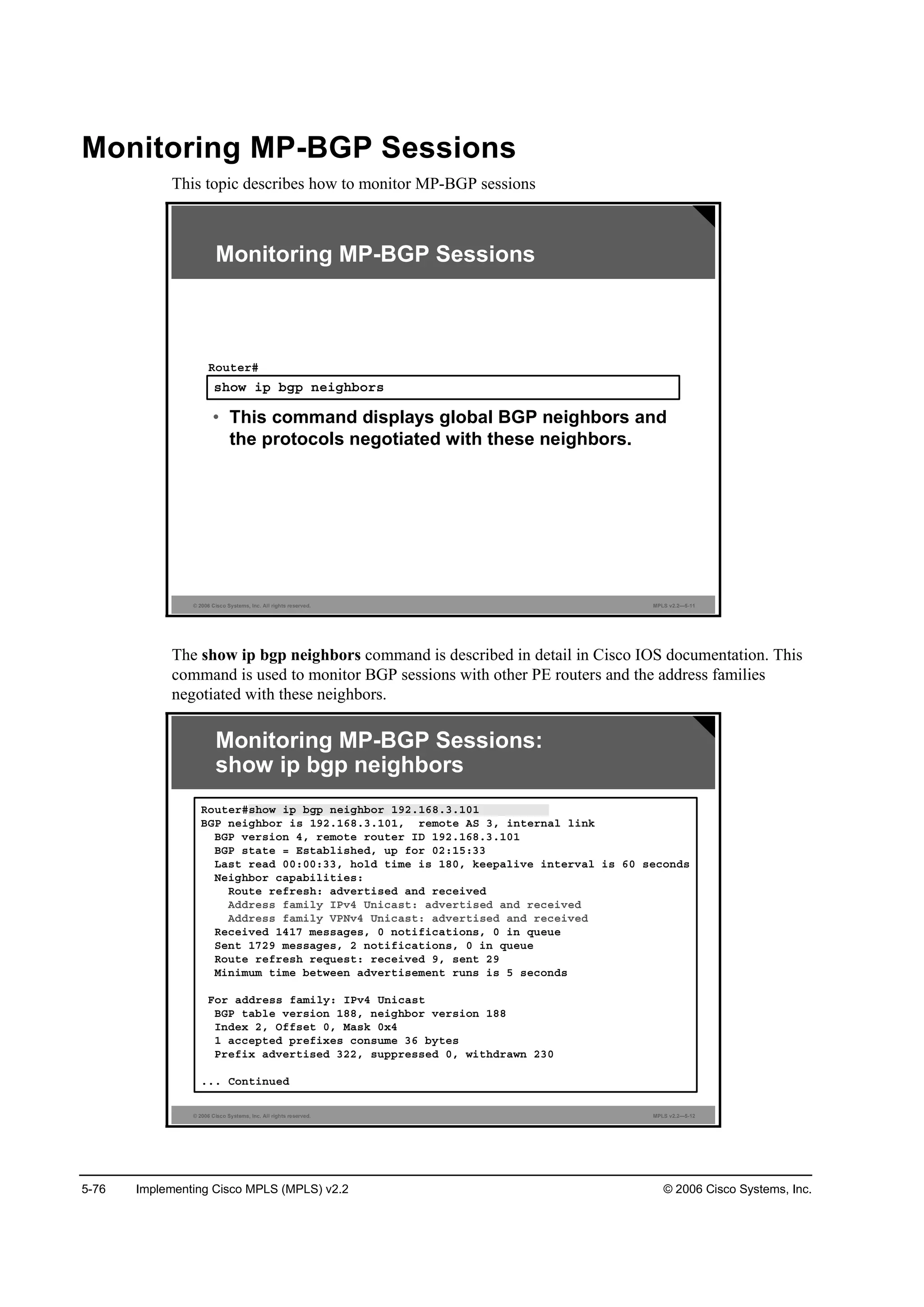
show ip bgp neighbors
To display information about the TCP and BGP connections to neighbors, use the show ip bgp
neighbors command in EXEC mode: show ip bgp neighbors [neighbor-address] [received-
routes | routes | advertised-routes | {paths regexp} | dampened-routes].
This table describes the parameters for the show ip bgp neighbors command.
Syntax Description
Parameter Description
˛»·ą¸ľ±®óżĽĽ®» (Optional) Displays the address of the neighbor whose routes you
have learned from
If you omit this argument, all neighbors will be displayed.
®»˝»·Ş»Ľó®±«¬» (Optional) Displays all received routes (both accepted and
rejected) from the specified neighbor
®±«¬» (Optional) Displays all routes that are received and accepted
This parameter is a subset of the output from the received-
routes keyword.
żĽŞ»®¬·»Ľó®±«¬» (Optional) Displays all the routes that the router has advertised to
the neighbor
°ż¬¸ ®»ą»¨° (Optional) Matches the paths received
Ľżł°»˛»Ľó®±«¬» (Optional) Displays the dampened routes to the neighbor at the
IP address specified](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-392-2048.jpg)
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-81
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-15
Monitoring an MP-BGP VPNv4 Table:
show ip bgp vpnv4 vrf-name
᫬»®ý¸±© ·° ľą° Ş°˛Şě Ş®ş Í·¬»ßî
ŢŮĐ ¬żľ´» Ş»®·±˛ · ěďęô ´±˝ż´ ®±«¬»® ×Ü · ďçîňďęčňíňďđî
ͬż¬« ˝±Ľ»ć «°°®»»Ľô Ľ Ľżł°»Ľô ¸ ¸·¬±®§ô ö Şż´·Ľô â ľ»¬ô ·
ó ·˛¬»®˛ż´
Ń®·ą·˛ ˝±Ľ»ć · ó ×ŮĐô » ó ŰŮĐô á ó ·˛˝±ł°´»¬»
Ň»¬©±®µ Ň»¨¬ ر° Ó»¬®·˝ Ô±˝Đ®ş É»·ą¸¬ Đż¬¸
᫬» Ü·¬·˛ą«·¸»®ć ďđíćíđ řĽ»şż«´¬ ş±® Ş®ş Í·¬»ßî÷
öâ ďëđňďňíďňíęńíđ đňđňđňđ đ íîéęč á
öâ·ďëđňďňíďňďîčńíđ ďçîňďęčňíňďđď đ ďđđ đ á
öâ·ďëđňďňíďňďíîńíđ ďçîňďęčňíňďđď đ ďđđ đ á
öâ·îđíňďňďňďńíî ďçîňďęčňíňďđí ď ďđđ đ ęëđíď
·
öâ îđíňďňîňďńíî ďëđňďňíďňíč éčî íîéęč á
öâ·îđíňďňďđňđ ďçîňďęčňíňďđí ď ďđđ đ ęëđíď
·
öâ îđíňďňîđňđ ďëđňďňíďňíč éčî íîéęč á
öâ·îđíňďňďîéňíńíî ďçîňďęčňíňďđď ď ďđđ đ á
öâ·îđíňďňďîéňěńíî ďçîňďęčňíňďđď éčî ďđđ đ á
öâ·îđíňďňďíěňđ ďçîňďęčňíňďđď ď ďđđ đ á
öâ·îđíňďňďíëňđ ďçîňďęčňíňďđď éčî ďđđ đ á
show ip bgp vpnv4 vrf
To display VPNv4 information from the BGP database associated with a VRF, use the show ip
bgp vpnv4 vrf command in privileged EXEC mode: show ip bgp vpnv4 vrf vrf-name [ip-
prefix/length [longer-prefixes] [output-modifiers]] [network-address [mask] [longer-prefixes]
[output-modifiers]] [cidr-only] [community][community-list] [dampened-paths] [filter-list]
[flap-statistics] [inconsistent-as] [neighbors] [paths [line]] [peer-group] [quote-regexp]
[regexp] [summary] [tags].
This table describes the syntax for the show ip bgp vpnv4 vrf command.
Syntax Description
Parameter Description
Ş®ş Ş®şó˛żł» Displays NLRI prefixes associated with the named VRF
Defaults
This command has no default values.
Usage Guidelines
Use this command to display VPNv4 information that is associated with a VRF from the BGP
database. A similar command—show ip bgp vpnv4 all—displays all available VPNv4
information. The show ip bgp vpnv4 summary command displays BGP neighbor status.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-396-2048.jpg)
![5-82 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-16
Monitoring an MP-BGP VPNv4 Table:
show ip bgp vpnv4 rd route-distinguisher
᫬»®ý¸±© ·° ľą° Ş°˛Şě ®Ľ ďđíćíđ îđíňďňďîéňí
ŢŮĐ ®±«¬·˛ą ¬żľ´» »˛¬®§ ş±® ďđíćíđćîđíňďňďîéňíńíîô Ş»®·±˛
ďęě
Đż¬¸ć řď żŞż·´żľ´»ô ľ»¬ ýďô ¬żľ´» Í·¬»ßî÷
ұ¬ żĽŞ»®¬·»Ľ ¬± ż˛§ °»»®
Ô±˝ż´ô ·ł°±®¬»Ľ °ż¬¸ ş®±ł ďđíćďđćîđíňďňďîéňíńíî
ďçîňďęčňíňďđď řł»¬®·˝ ďđ÷ ş®±ł ďçîňďęčňíňďđď
řďçîňďęčňíňďđď÷
Ń®·ą·˛ ·˛˝±ł°´»¬»ô ł»¬®·˝ ďô ´±˝ż´°®»ş ďđđô Şż´·Ľô
·˛¬»®˛ż´ô ľ»¬
ۨ¬»˛Ľ»Ľ ݱłł«˛·¬§ć ÎĚćďđíćďđ
show ip bgp vpnv4 rd route-distinguisher
To display all VPNv4 routes that contain a specified RD, use the show ip bgp vpnv4 rd
command in privileged EXEC mode: show ip bgp vpnv4 rd route-distinguisher [ip-
prefix/length [longer-prefixes] [output-modifiers]] [network-address [mask] [longer-prefixes]
[output-modifiers]] [cidr-only] [community][community-list] [dampened-paths] [filter-list]
[flap-statistics] [inconsistent-as] [paths [line]] [quote-regexp] [regexp] [summary] [tags].
This table describes the syntax for the show ip bgp vpnv4 rd route-distinguisher command.
Syntax Description
Parameter Description
®Ľ ®±«¬»óĽ·¬·˛ą«·¸»® Displays NLRI prefixes that have a matching RD
Defaults
There is no default. An RD must be configured for a VRF to be functional.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-397-2048.jpg)
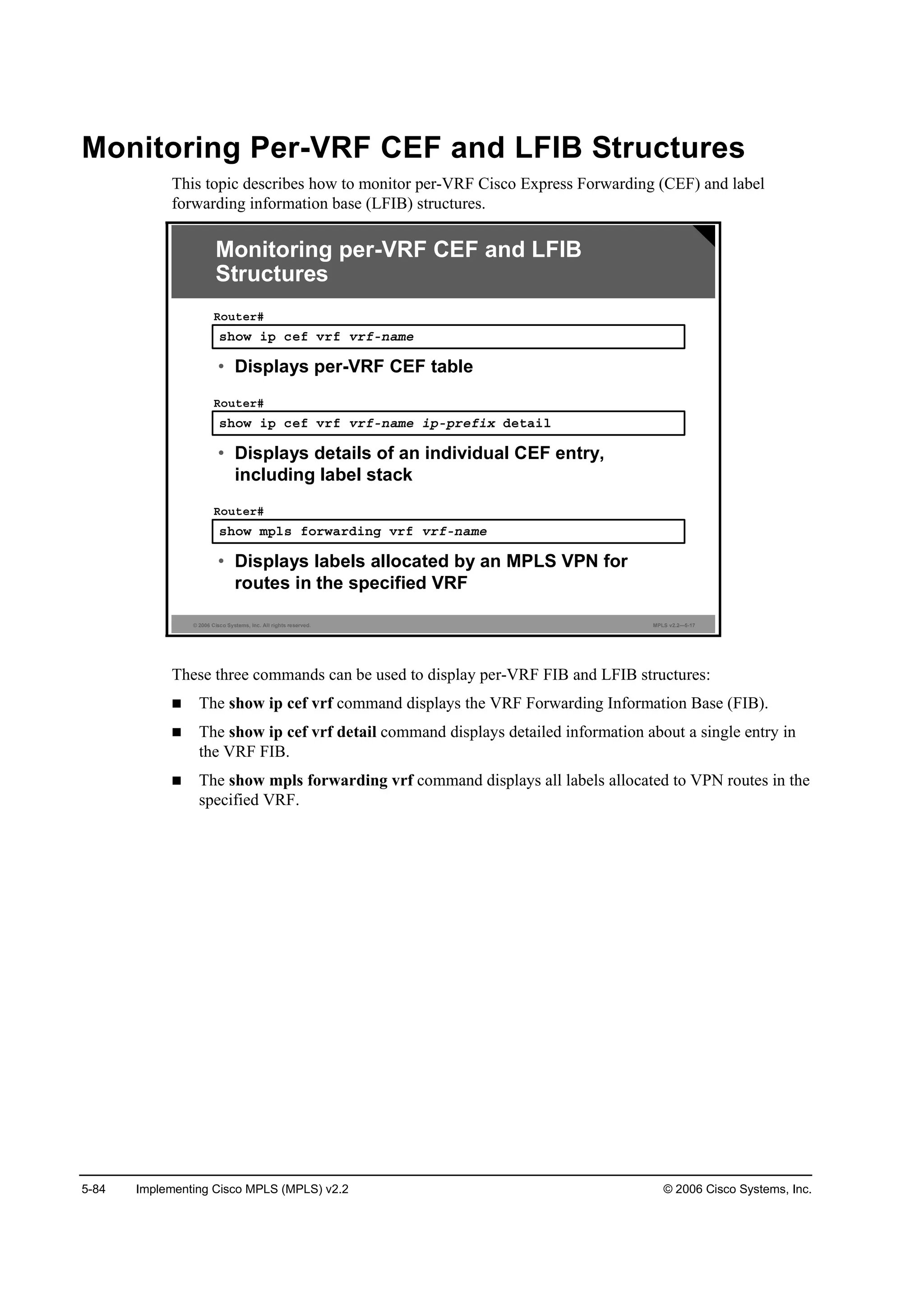
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-85
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-18
The show ip cef command can also display the label stack associated
with the MP-IBGP route.
Monitoring per-VRF CEF and LFIB
Structures (Cont.)
᫬»®ý¸±© ·° ˝»ş Ş®ş Í·¬»ßî îđíňďňďňď îëëňîëëňîëëňîëë Ľ»¬ż·´
îđíňďňďňďńíîô Ş»®·±˛ ëéô ˝ż˝¸»Ľ żĽ¶ż˝»˛˝§ ¬± Í»®·ż´ďńđňî
đ °ż˝µ»¬ô 𠾧¬»
¬żą ·˛ş±®łż¬·±˛ »¬
´±˝ż´ ¬żąć ĘĐŇ󮱫¬»ó¸»żĽ
şż¬ ¬żą ®»©®·¬» ©·¬¸ Í»ďńđňîô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć Ąîę íçŁ
Ş·ż ďçîňďęčňíňďđíô đ Ľ»°»˛Ľ»˛˝·»ô ®»˝«®·Ş»
˛»¨¬ ¸±° ďçîňďęčňíňďđô Í»®·ż´ďńđňî Ş·ż ďçîňďęčňíňďđíńíî
Şż´·Ľ ˝ż˝¸»Ľ żĽ¶ż˝»˛˝§
¬żą ®»©®·¬» ©·¬¸ Í»ďńđňîô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć Ąîę íçŁ
show ip cef vrf
To display the CEF forwarding table associated with a VRF, use the show ip cef vrf command
in privileged EXEC mode: show ip cef vrf vrf-name [ip-prefix [mask [longer-prefixes]]
[detail] [output-modifiers]] [interface interface-number] [adjacency [interface interface-
number] [detail] [discard] [drop] [glean] [null] [punt] [output-modifiers]] [detail [output-
modifiers]] [non-recursive [detail] [output-modifiers]] [summary [output-modifiers]] [traffic
[prefix-length] [output-modifiers]] [unresolved [detail] [output-modifiers]].
The label stack in the VRF table can be inspected using the show ip cef vrf vrf-name detail
command. The tags imposed values in the output displays the MPLS label stack. The first label
in the MPLS label stack is the Label Distribution Protocol (LDP) label forwarded toward the
egress provider edge (PE) router, and the second label is the VPN label advertised by the egress
PE router.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-400-2048.jpg)
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-87
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-19
Monitoring per-VRF CEF and LFIB
Structures (Cont.)
᫬»®ý¸±© ł°´ ş±®©ż®Ľ·˛ą Ş®ş Í·¬»ßî
Ô±˝ż´ Ń«¬ą±·˛ą Đ®»ş·¨ ާ¬» ¬żą Ń«¬ą±·˛ą Ň»¨¬ ر°
¬żą ¬żą ±® ĘÝ ±® Ě«˛˛»´ ׼ ©·¬˝¸»Ľ ·˛¬»®şż˝»
îę ßąą®»ąż¬» ďëđňďňíďňíęńíđĹĘĂ đ
íé ˲¬żąą»Ľ îđíňďňîňďńíîĹĘĂ đ Í»ďńđňîđ
°±·˛¬î°±·˛¬
íč ˲¬żąą»Ľ îđíňďňîđňđńîěĹĘĂ đ Í»ďńđňîđ
°±·˛¬î°±·˛¬
᫬»®ý¸±© ł°´ ş±®©ż®Ľ·˛ą Ş®ş Í·¬»ßî ¬żą íé Ľ»¬ż·´
Ô±˝ż´ Ń«¬ą±·˛ą Đ®»ş·¨ ާ¬» ¬żą Ń«¬ą±·˛ą Ň»¨¬ ر°
¬żą ¬żą ±® ĘÝ ±® Ě«˛˛»´ ׼ ©·¬˝¸»Ľ ·˛¬»®şż˝»
íé ˲¬żąą»Ľ îđíňďňîňďńíîĹĘĂ đ Í»ďńđňîđ
°±·˛¬î°±·˛¬
ÓßÝń۲˝ż°ăđńđô ÓĚËăďëđěô Ěżą ͬż˝µĄŁ
ĘĐŇ ®±«¬»ć Í·¬»ßî
Đ»®ó°ż˝µ»¬ ´±żĽó¸ż®·˛ą
show mpls forwarding vrf
To display label-forwarding information for advertised VRF routes, use the show mpls
forwarding vrf command in EXEC mode.
show mpls forwarding vrf vrf-name [ip-prefix/length [mask]] [detail] [output-modifiers]
This table describes the parameters for the show mpls forwarding vrf command.
Syntax Description
Parameter Description
Ş®şó˛żł» Displays NLRI prefixes associated with the named VRF
·°ó°®»ş·¨ń´»˛ą¬¸ (Optional) Displays IP prefix address (in dotted decimal notation)
and length of mask (0 to 32)
łżµ (Optional) Displays destination network mask in dotted decimal
notation
Ľ»¬ż·´ (Optional) Displays detailed information on the VRF routes
±«¬°«¬ół±Ľ·ş·»® (Optional) For a list of associated keywords and arguments, use
context-sensitive help
Defaults
This command has no default behavior or values.
Usage Guidelines
Use this command to display label-forwarding entries associated with a particular VRF or IP
prefix.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-402-2048.jpg)
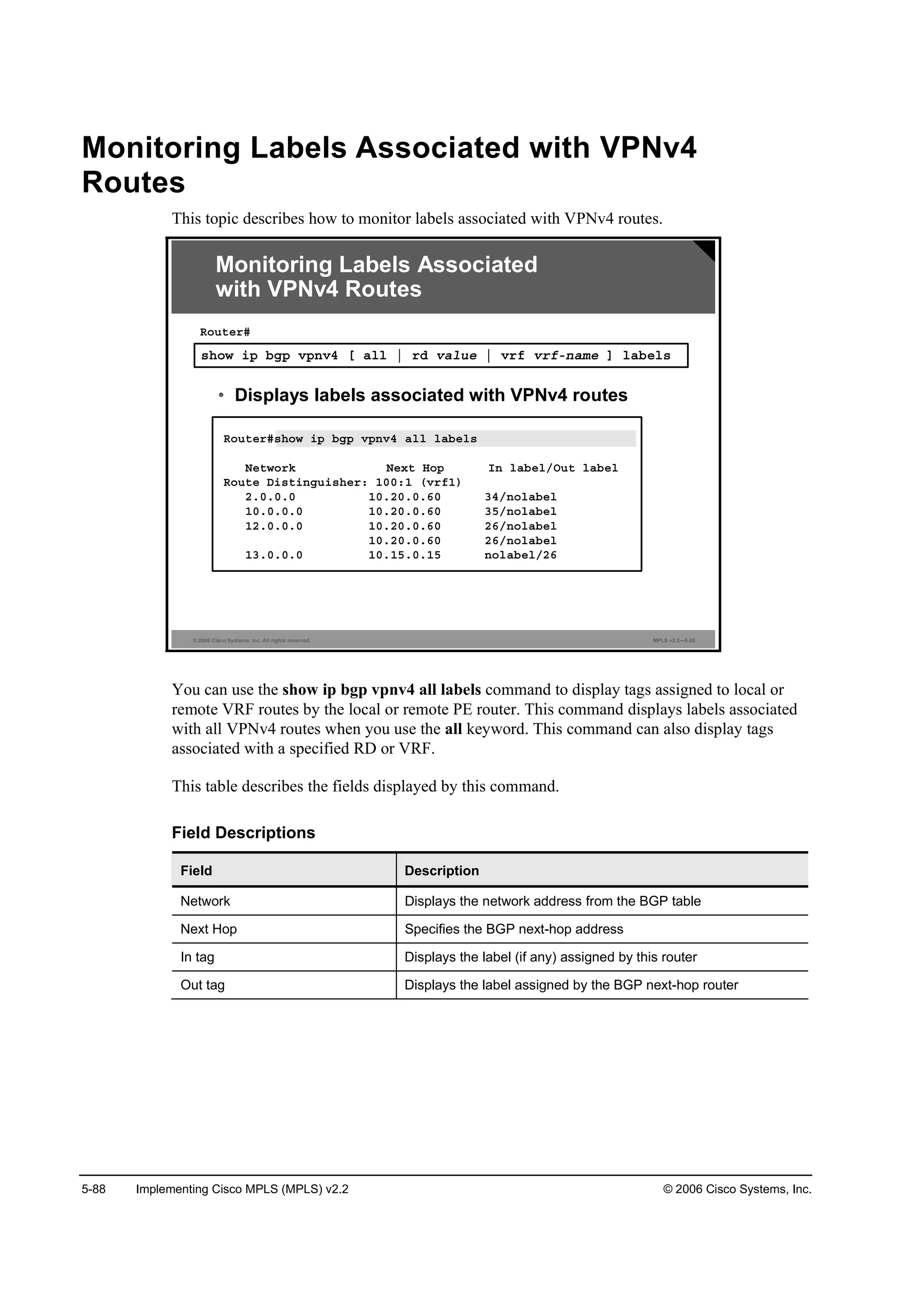
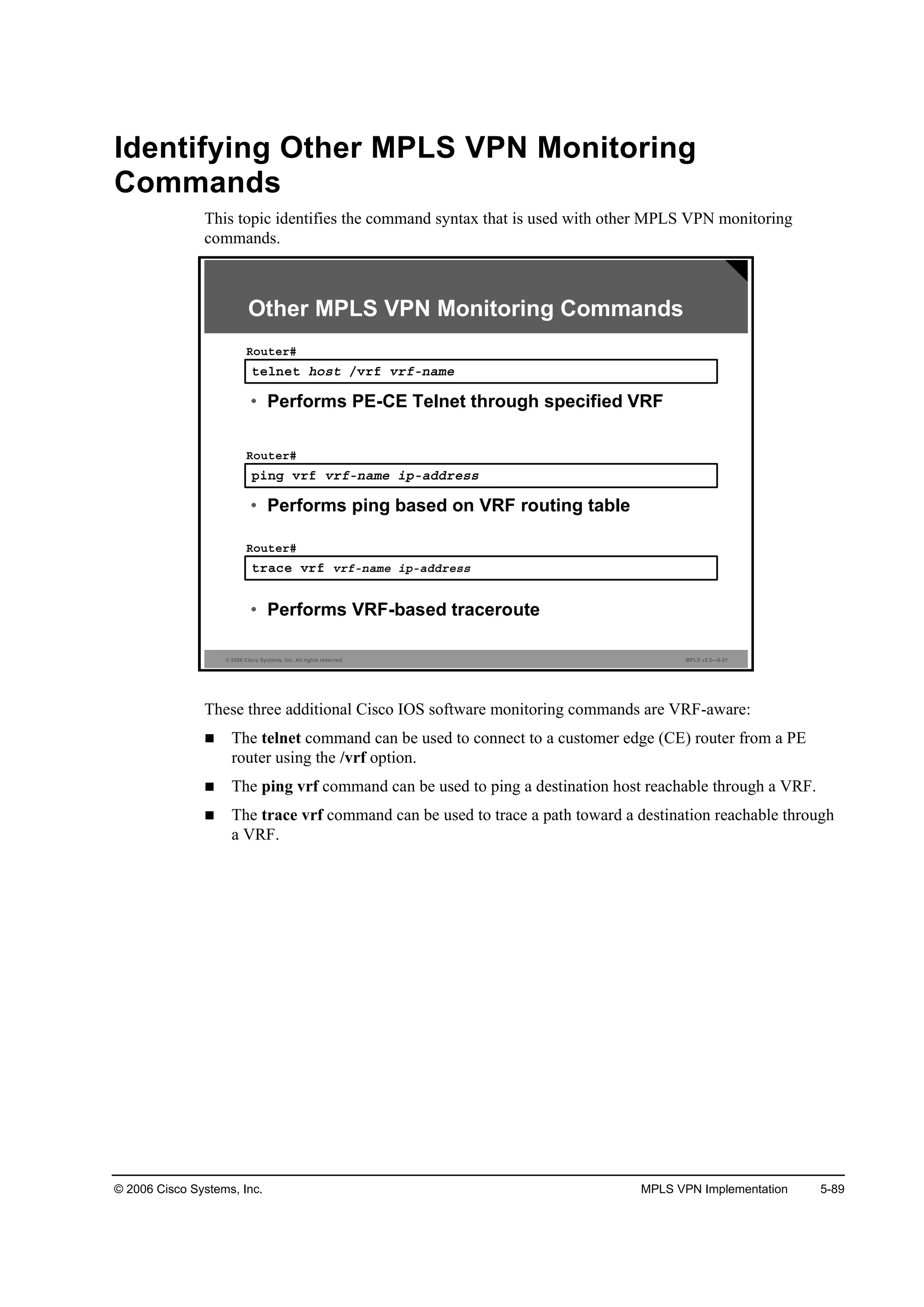
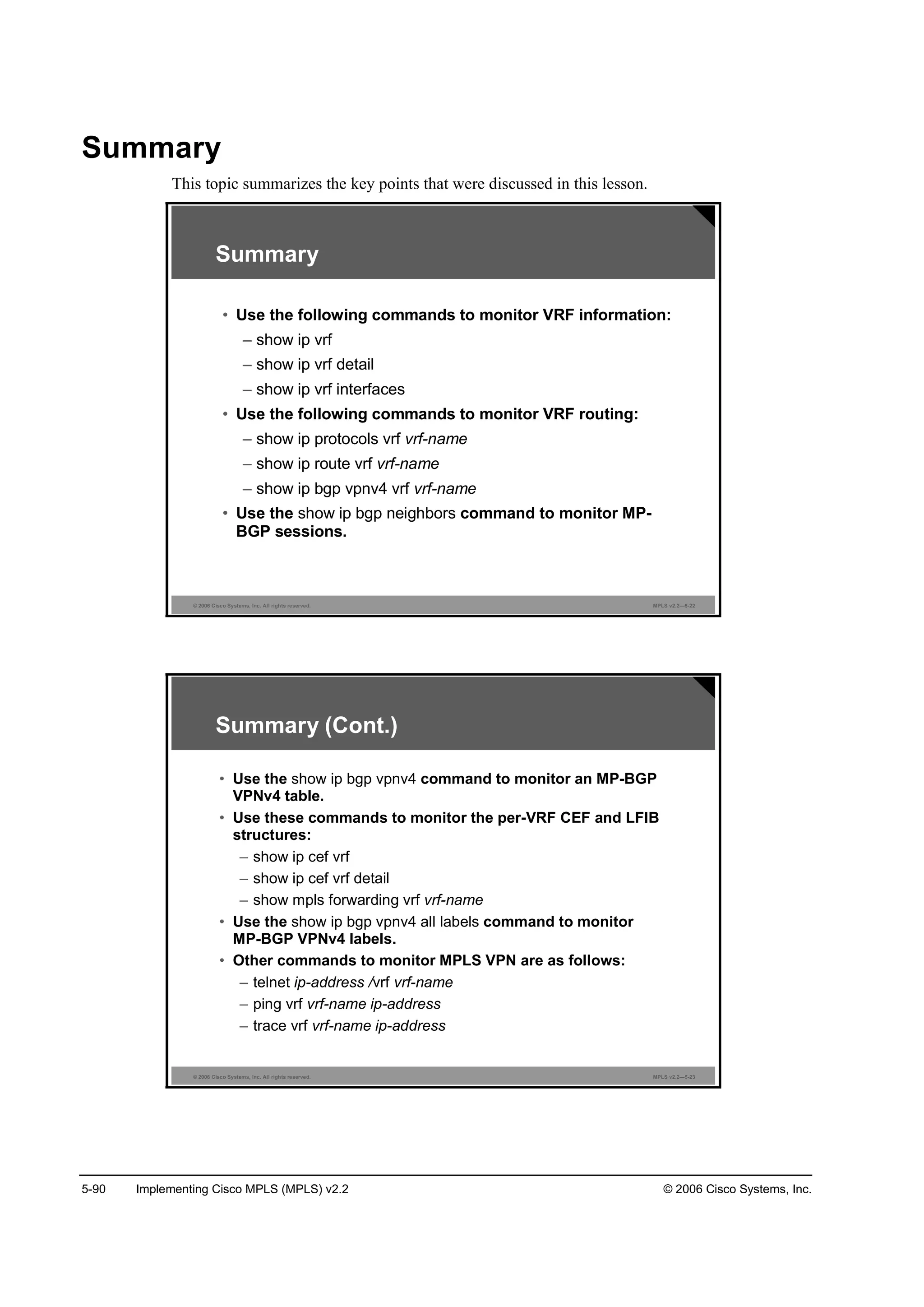
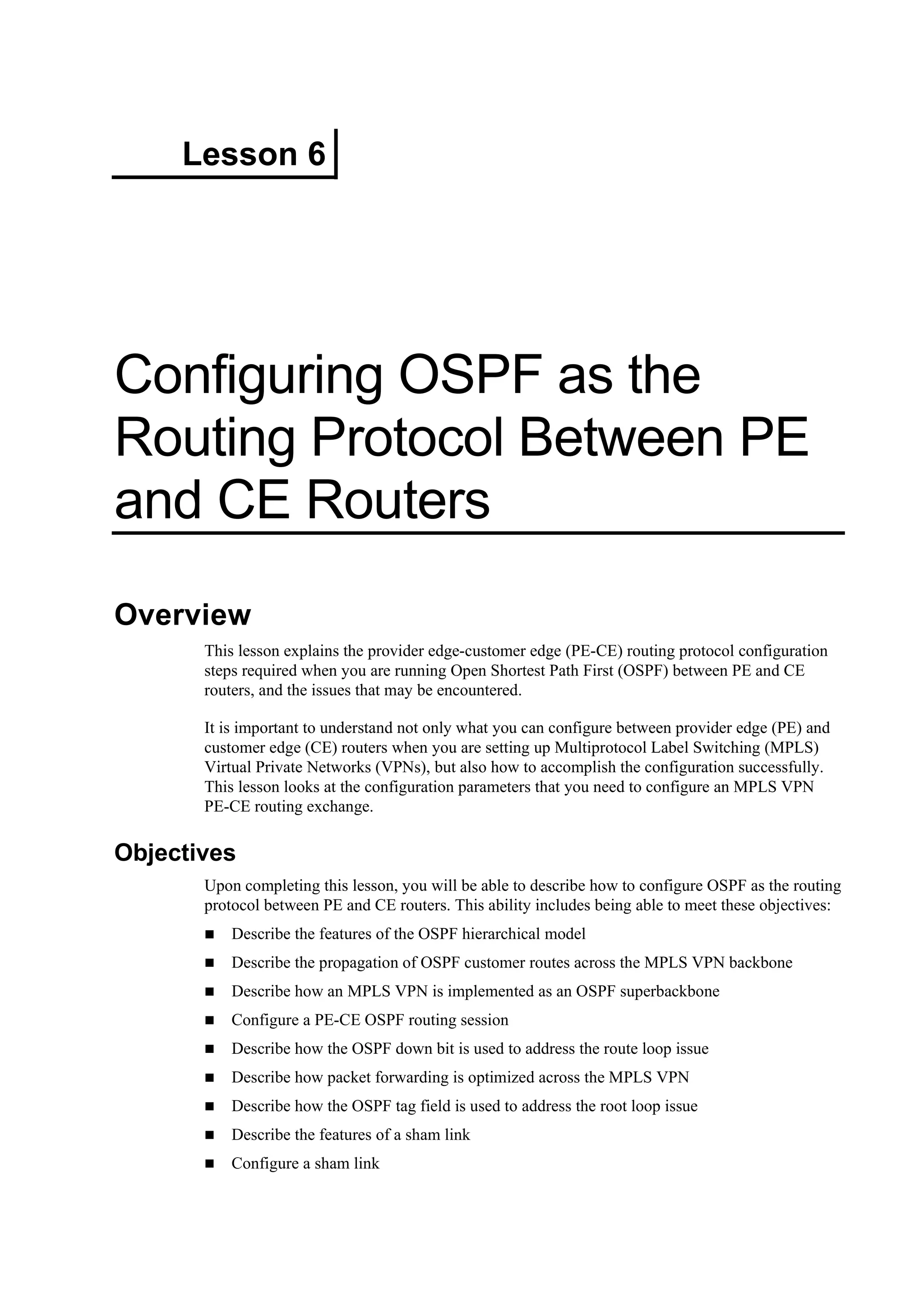
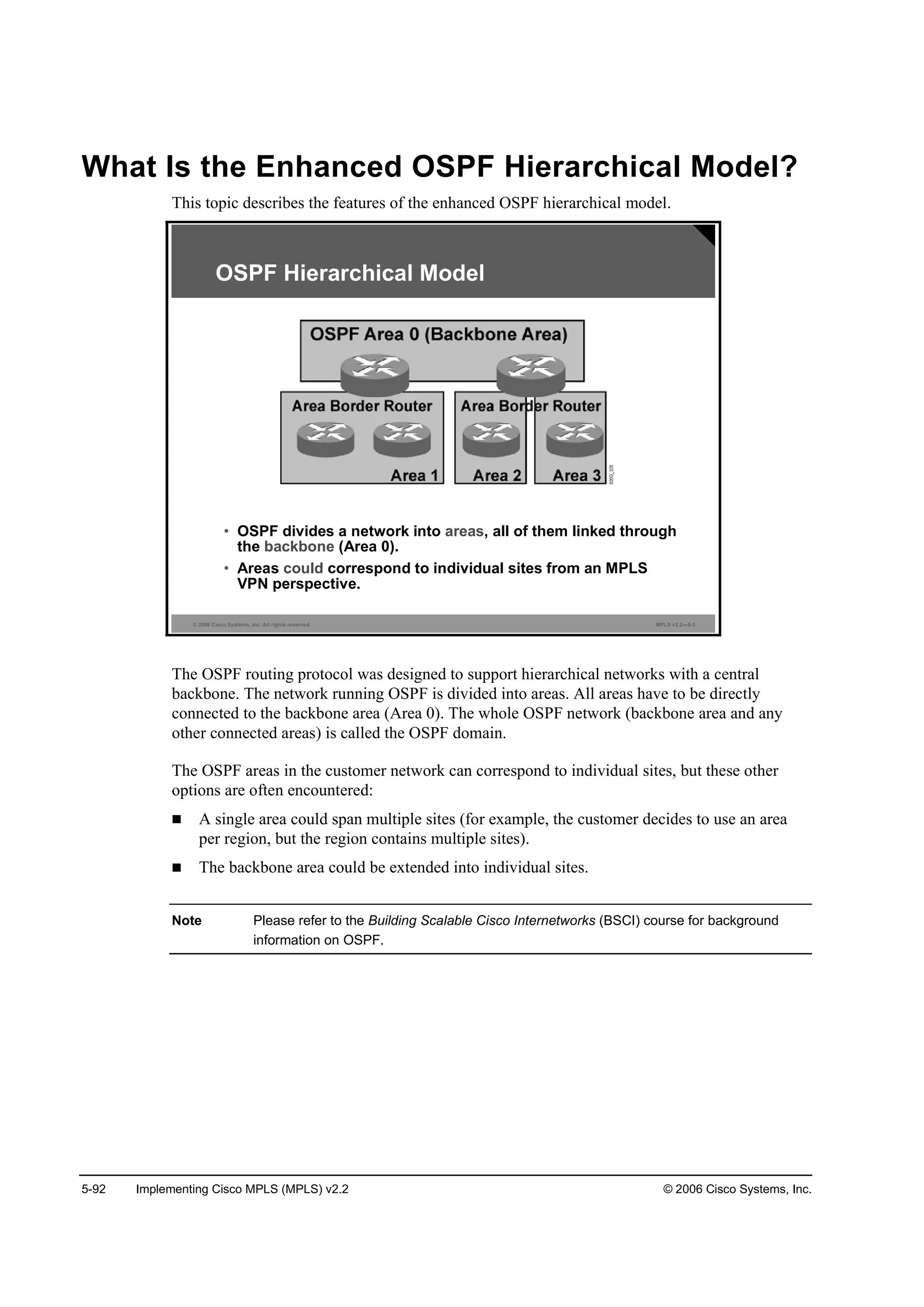
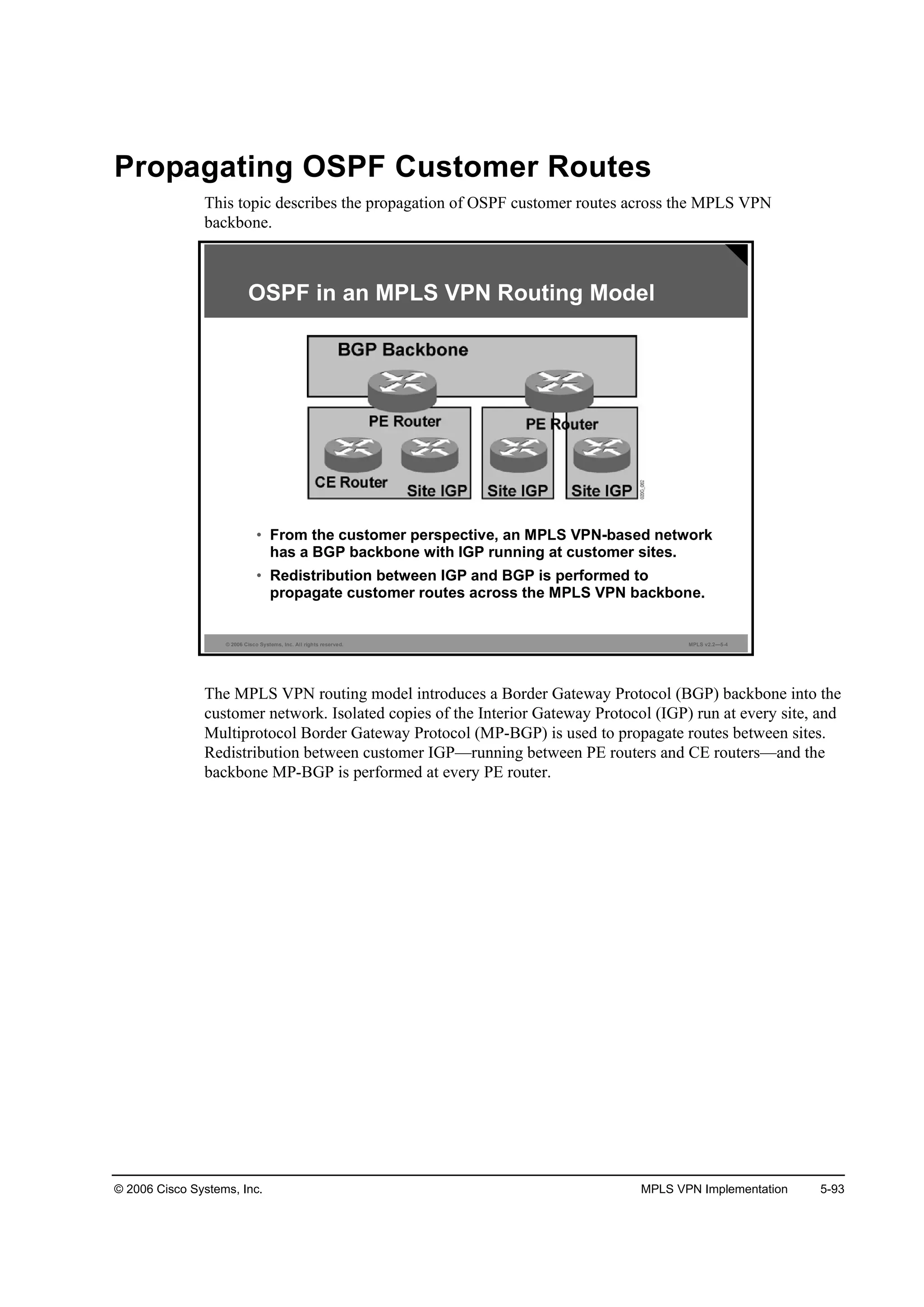
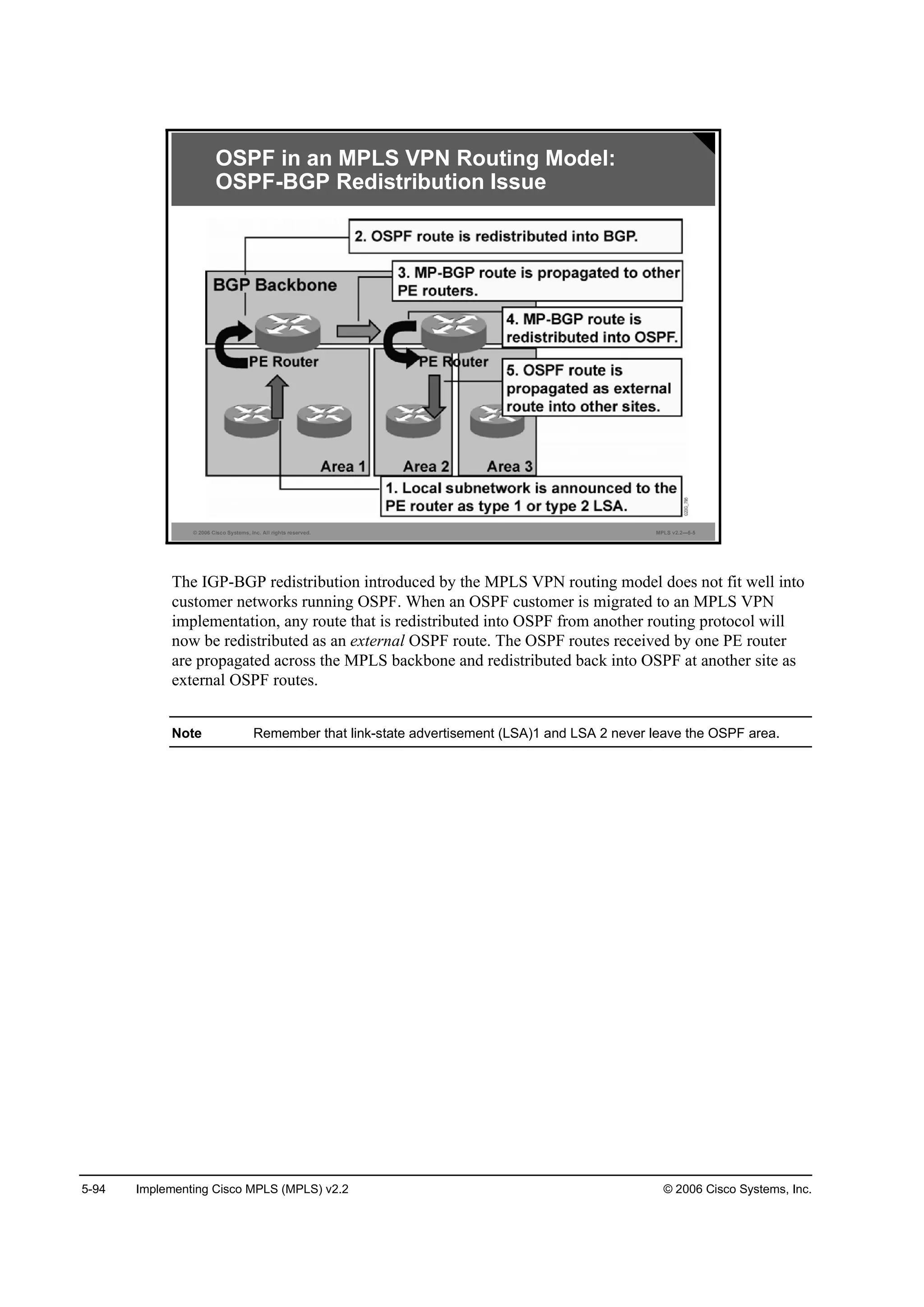
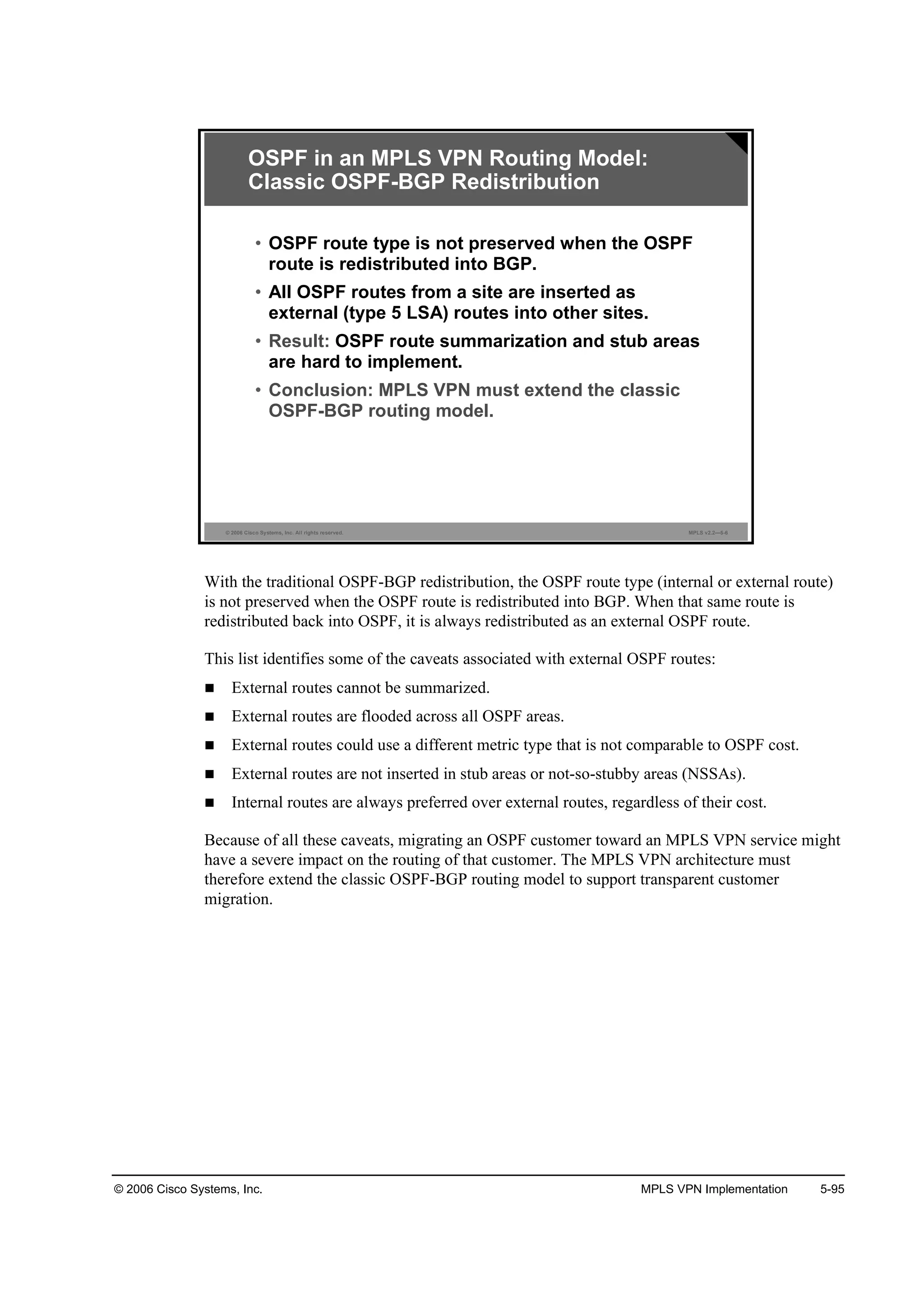
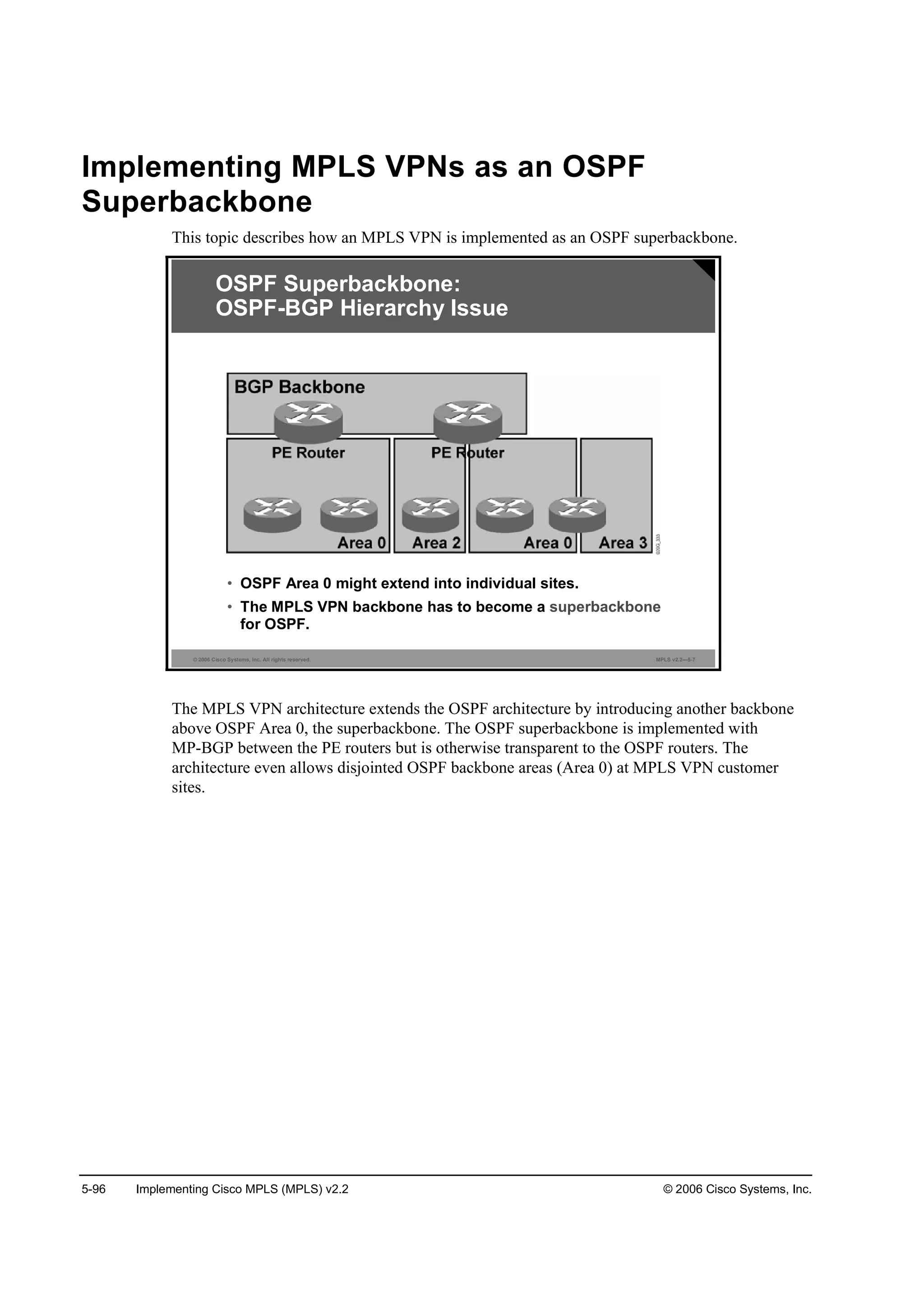
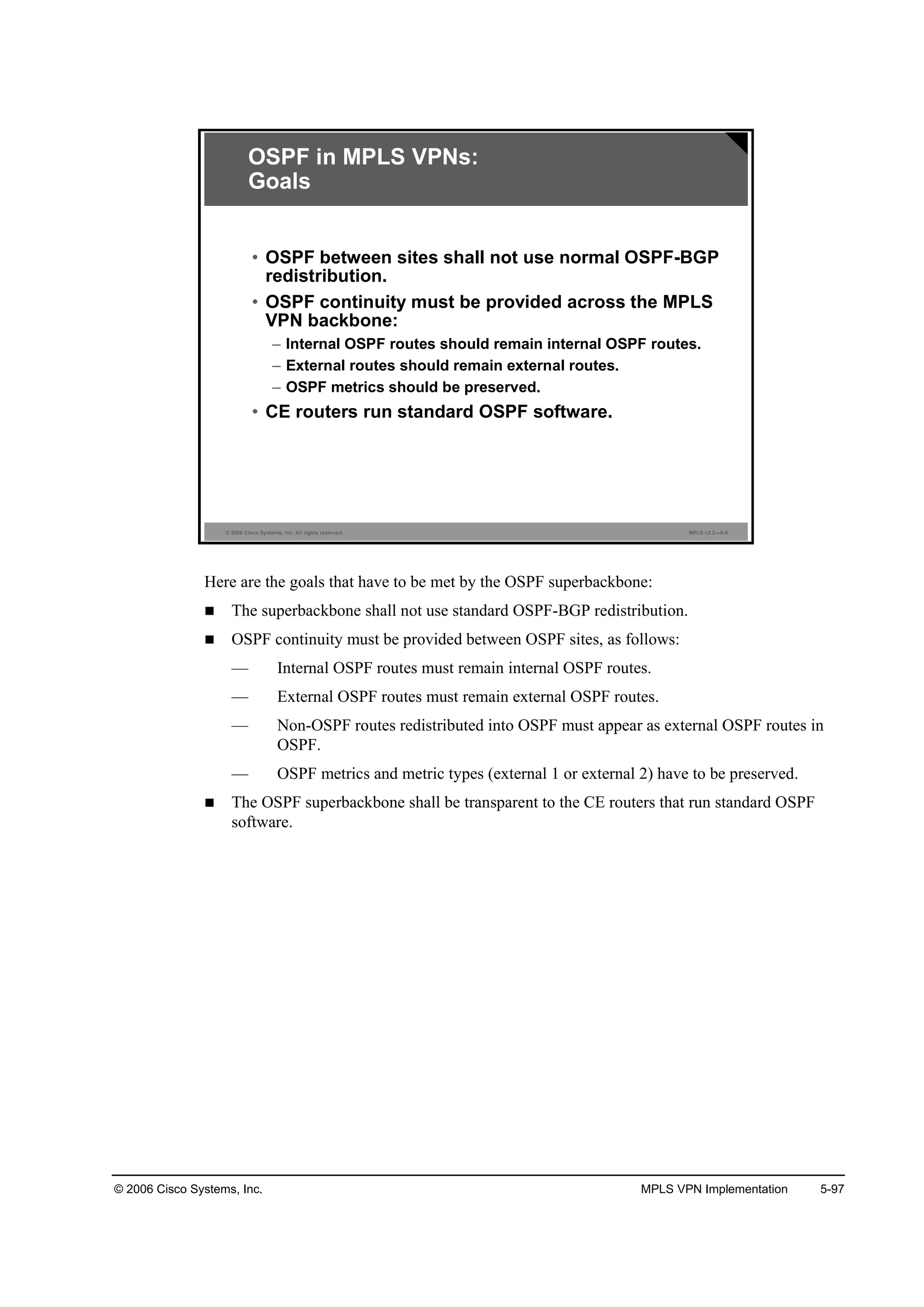
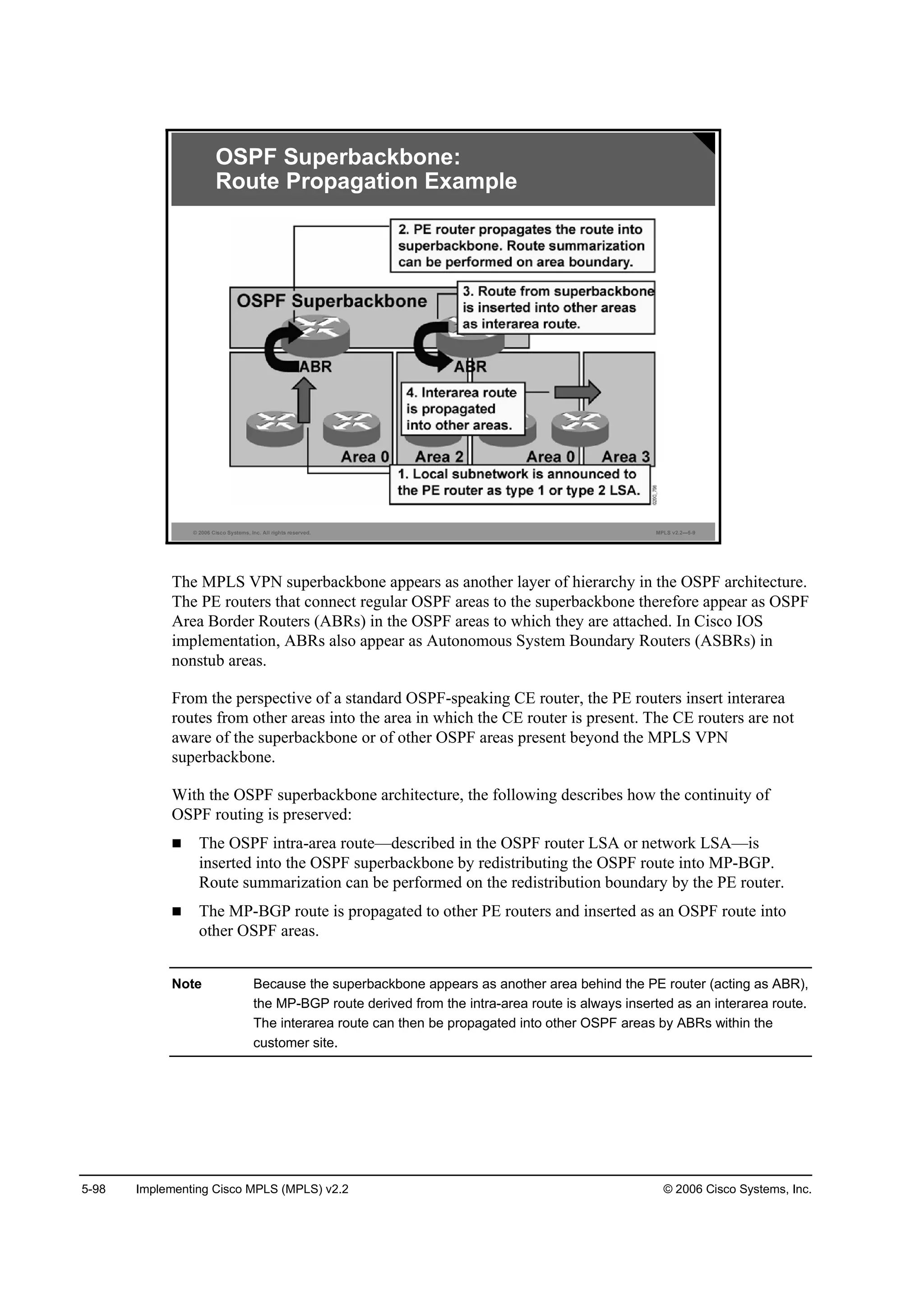
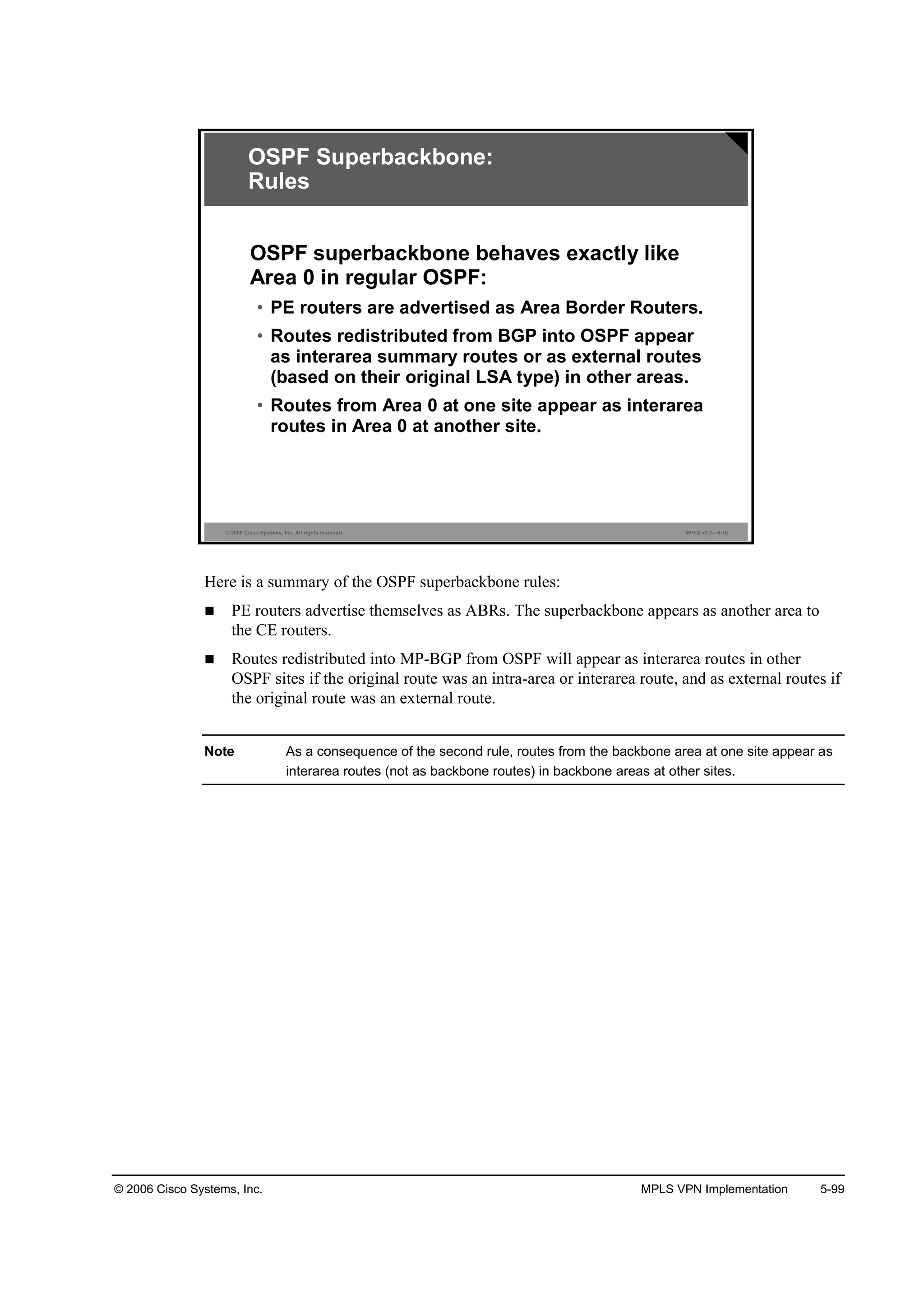
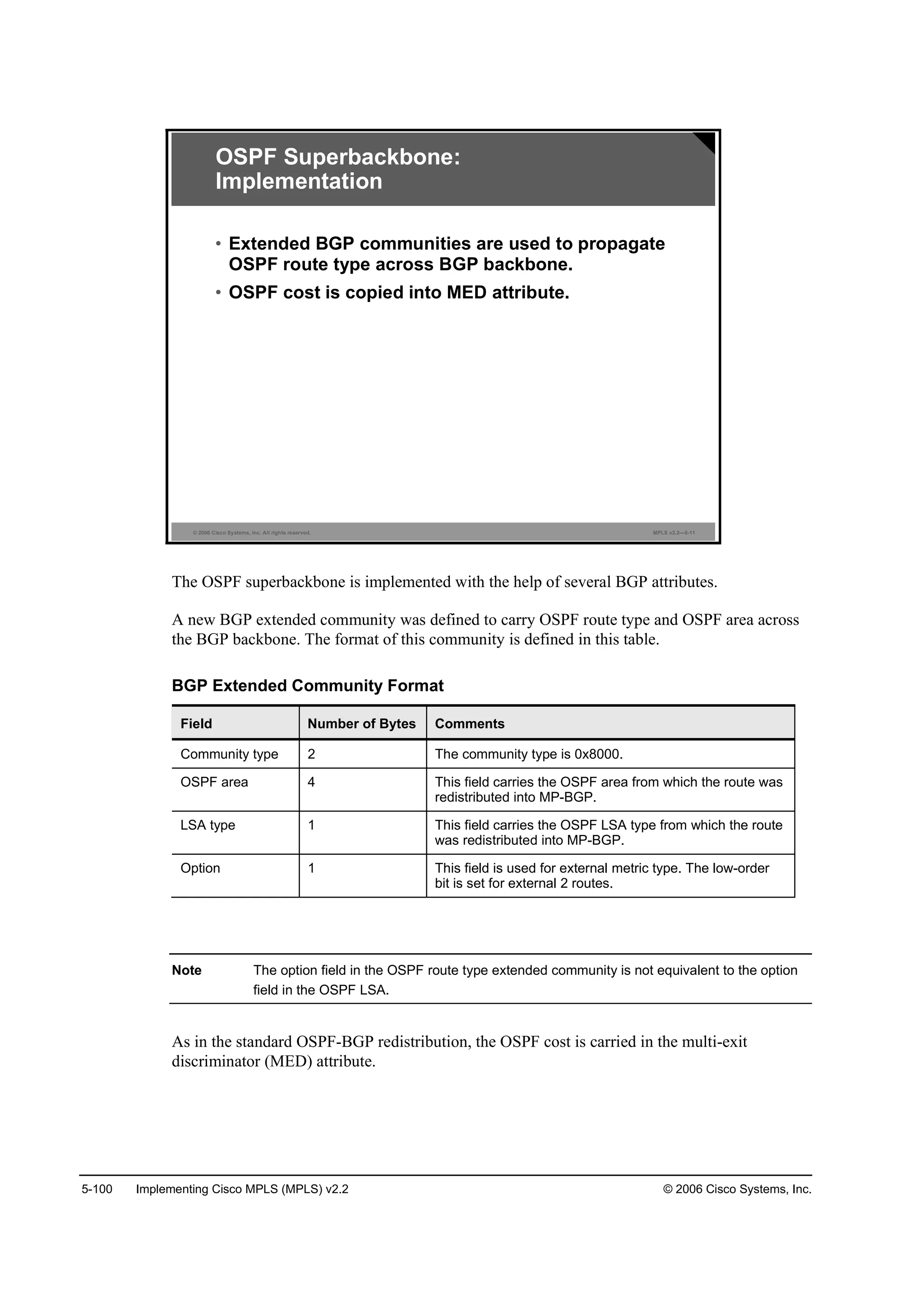
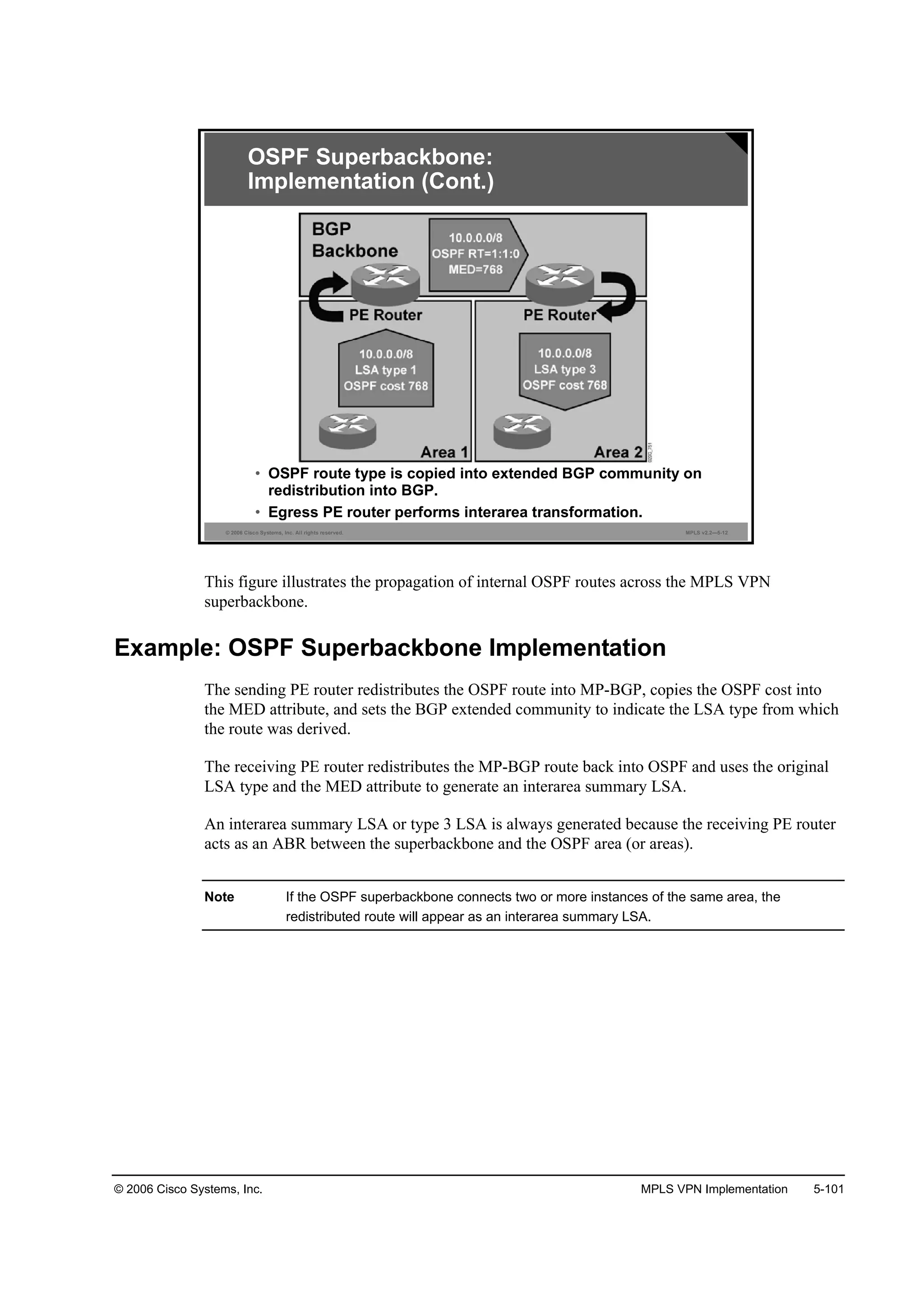
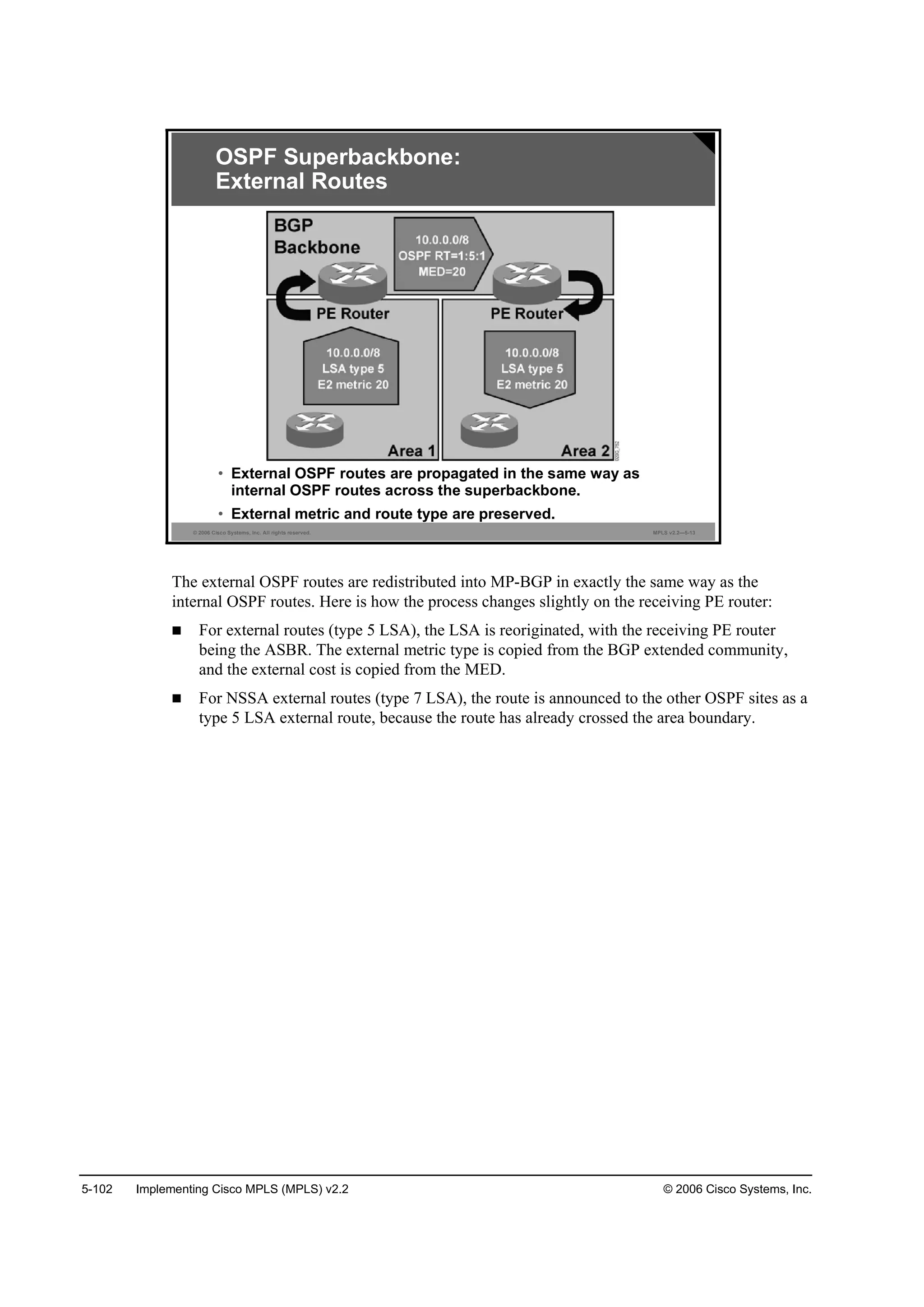
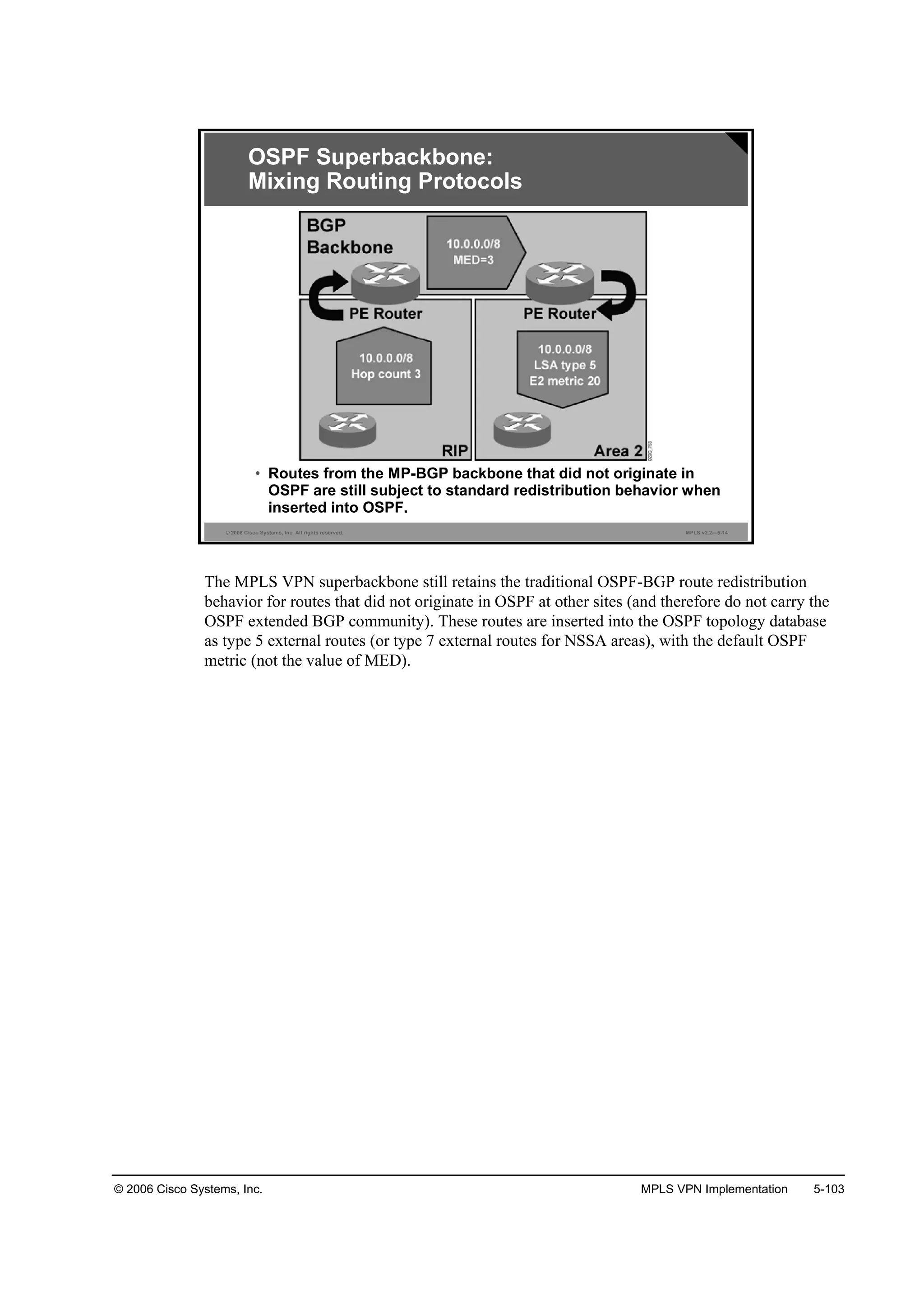
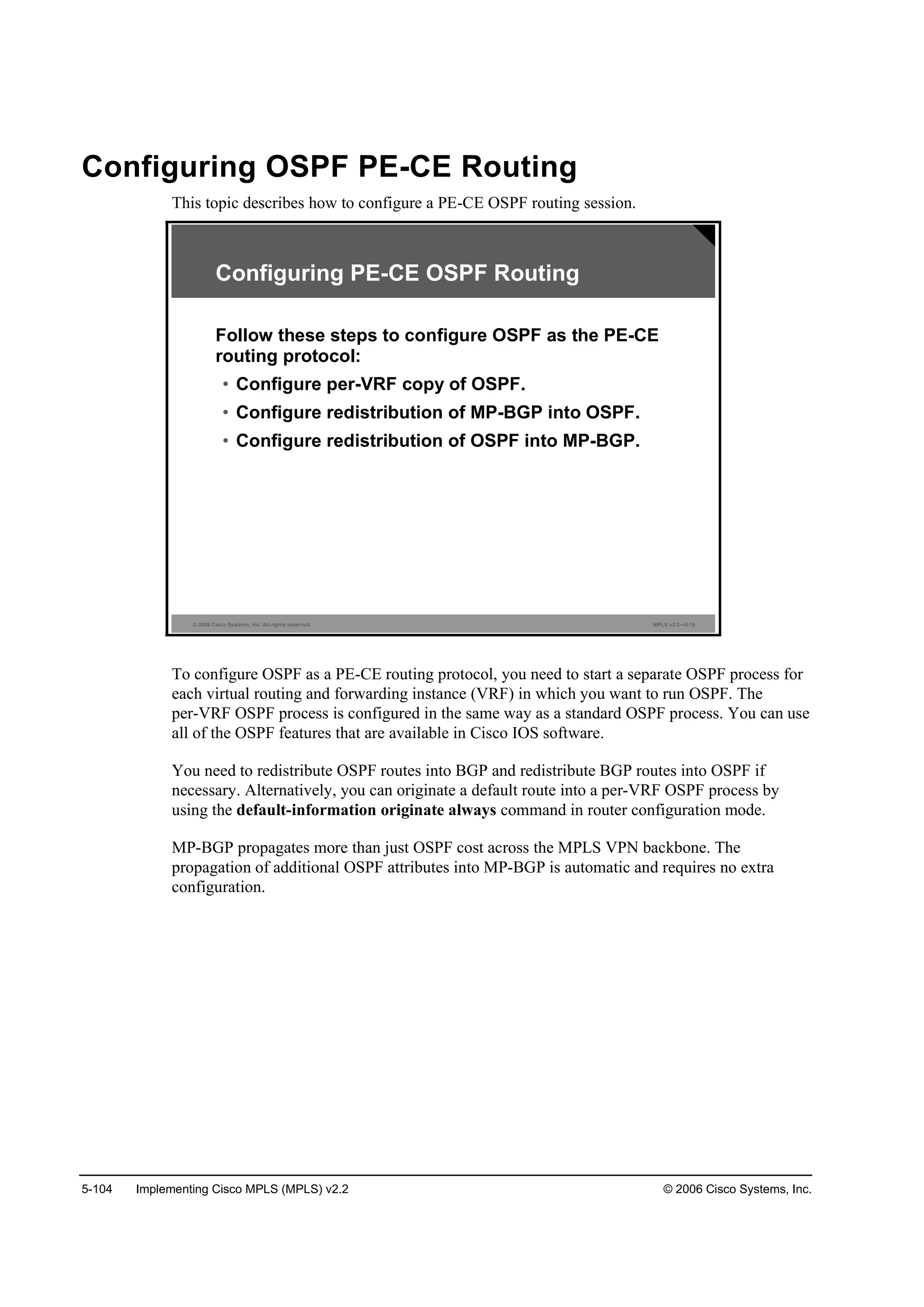
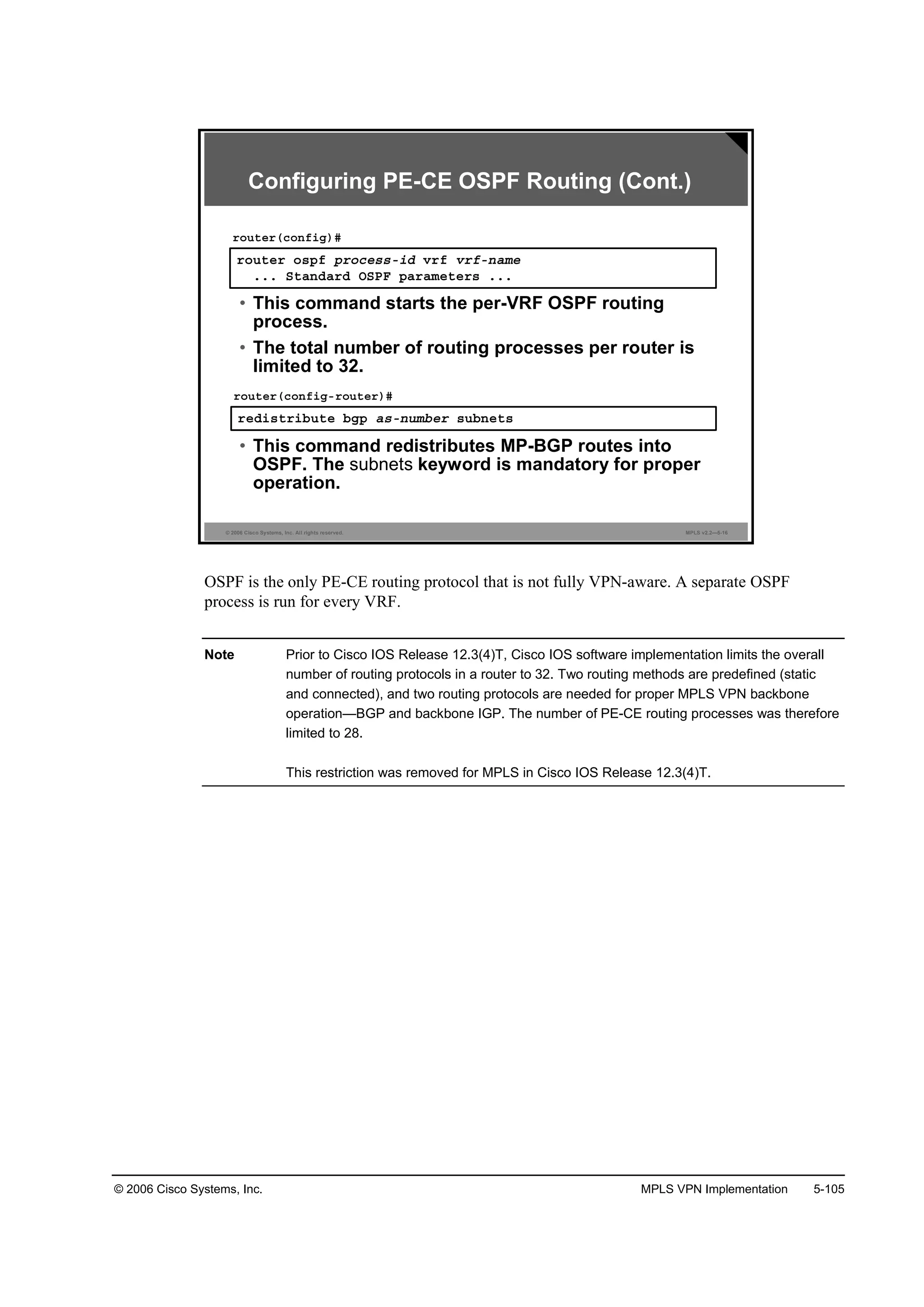

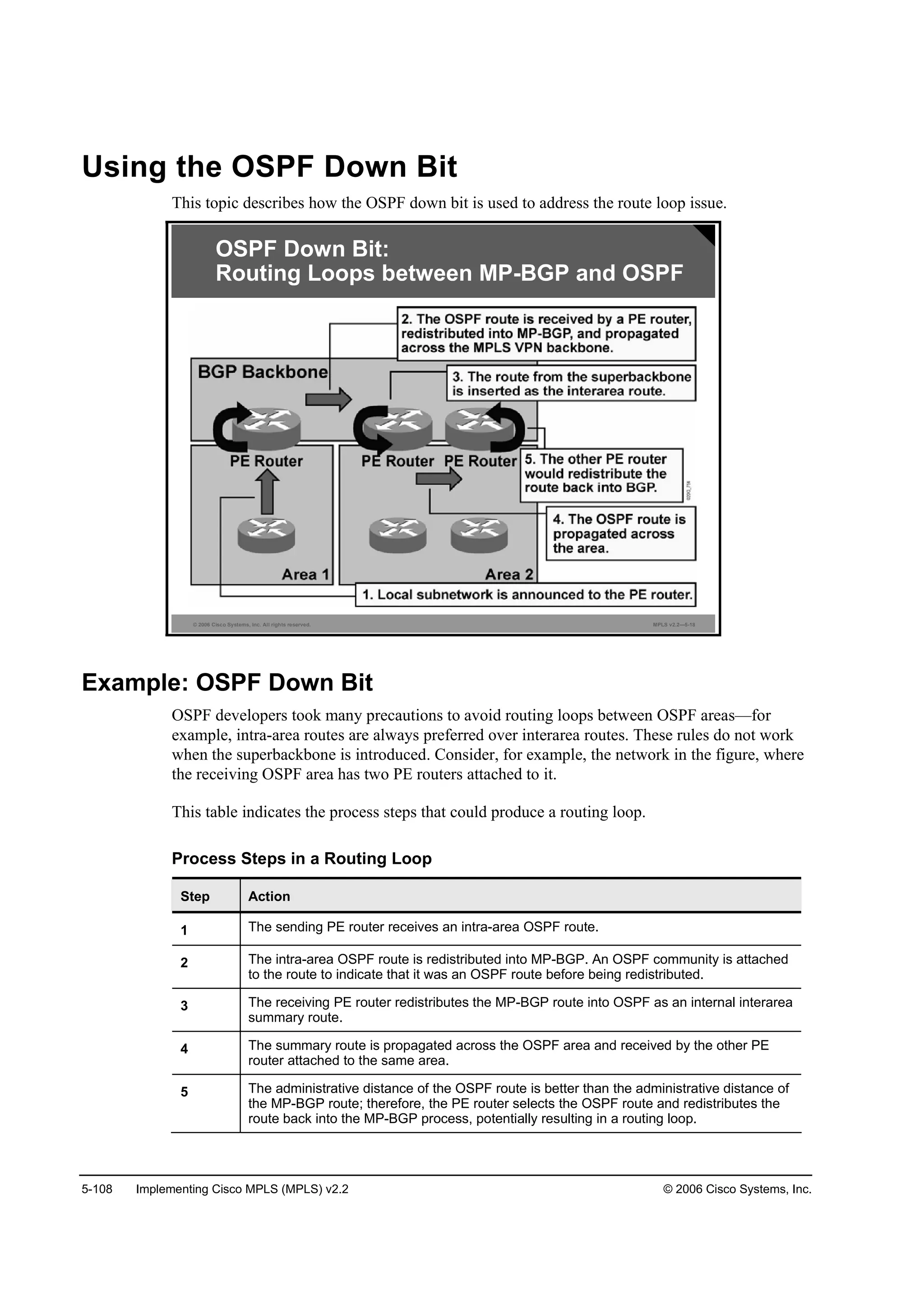
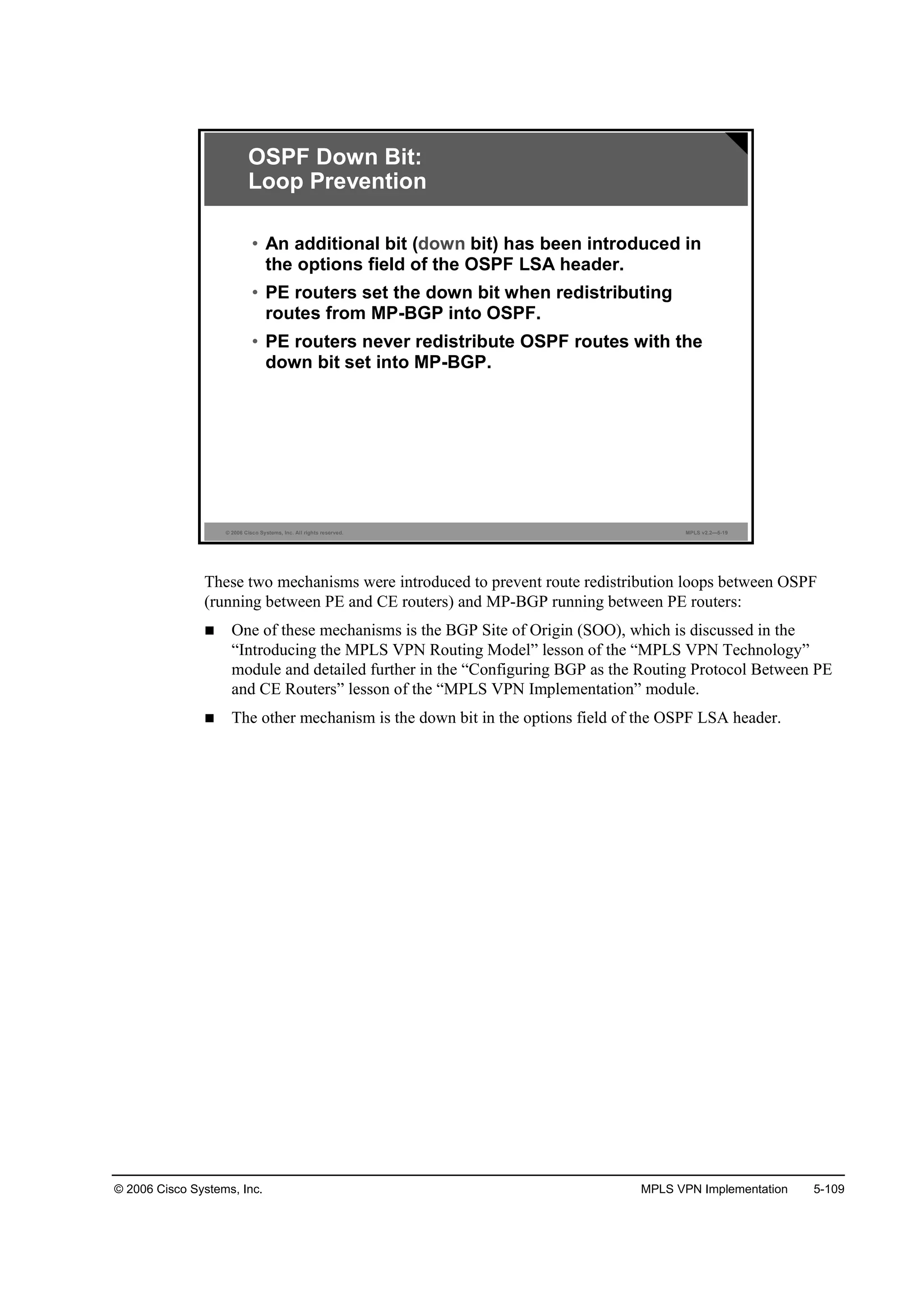
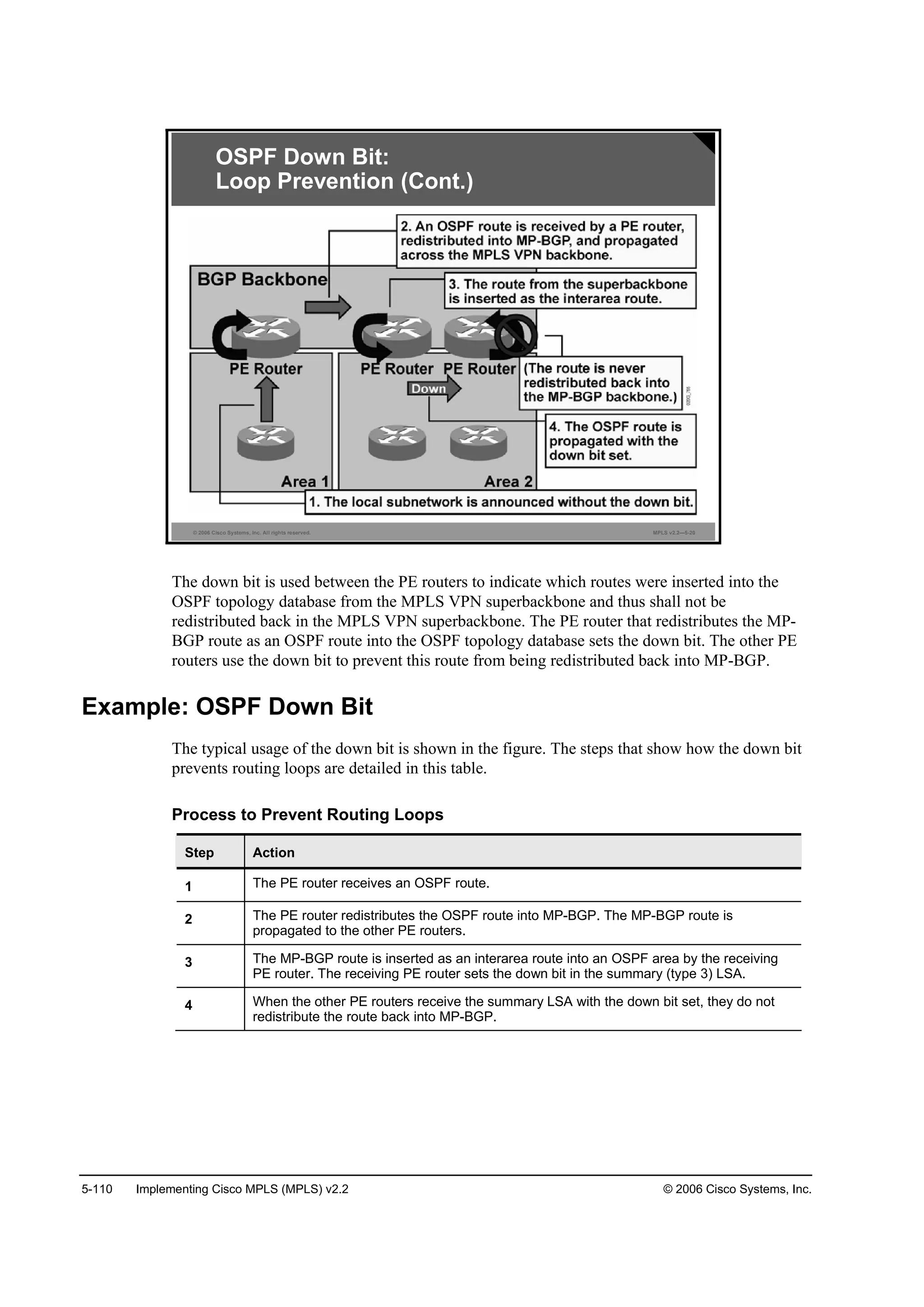
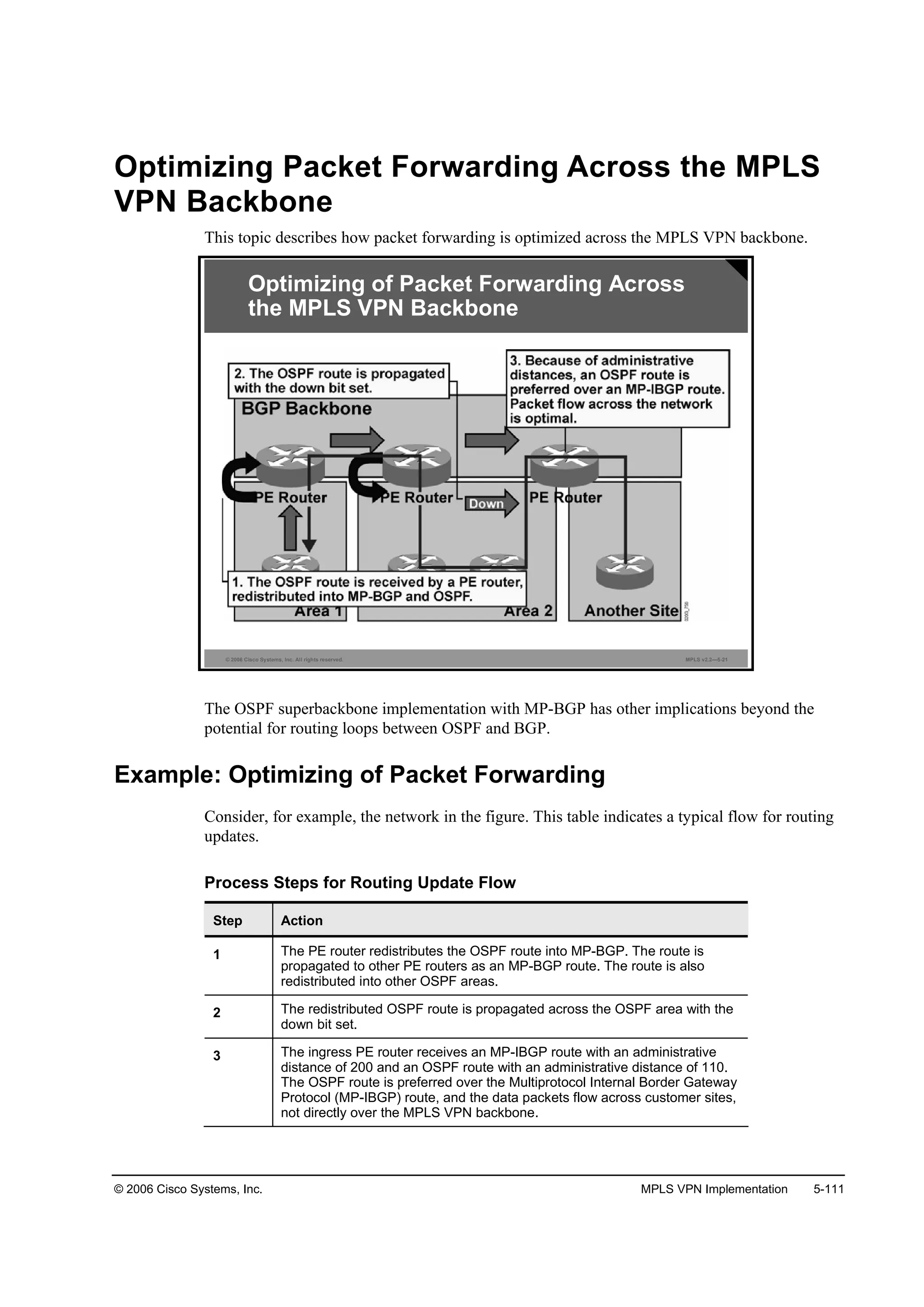
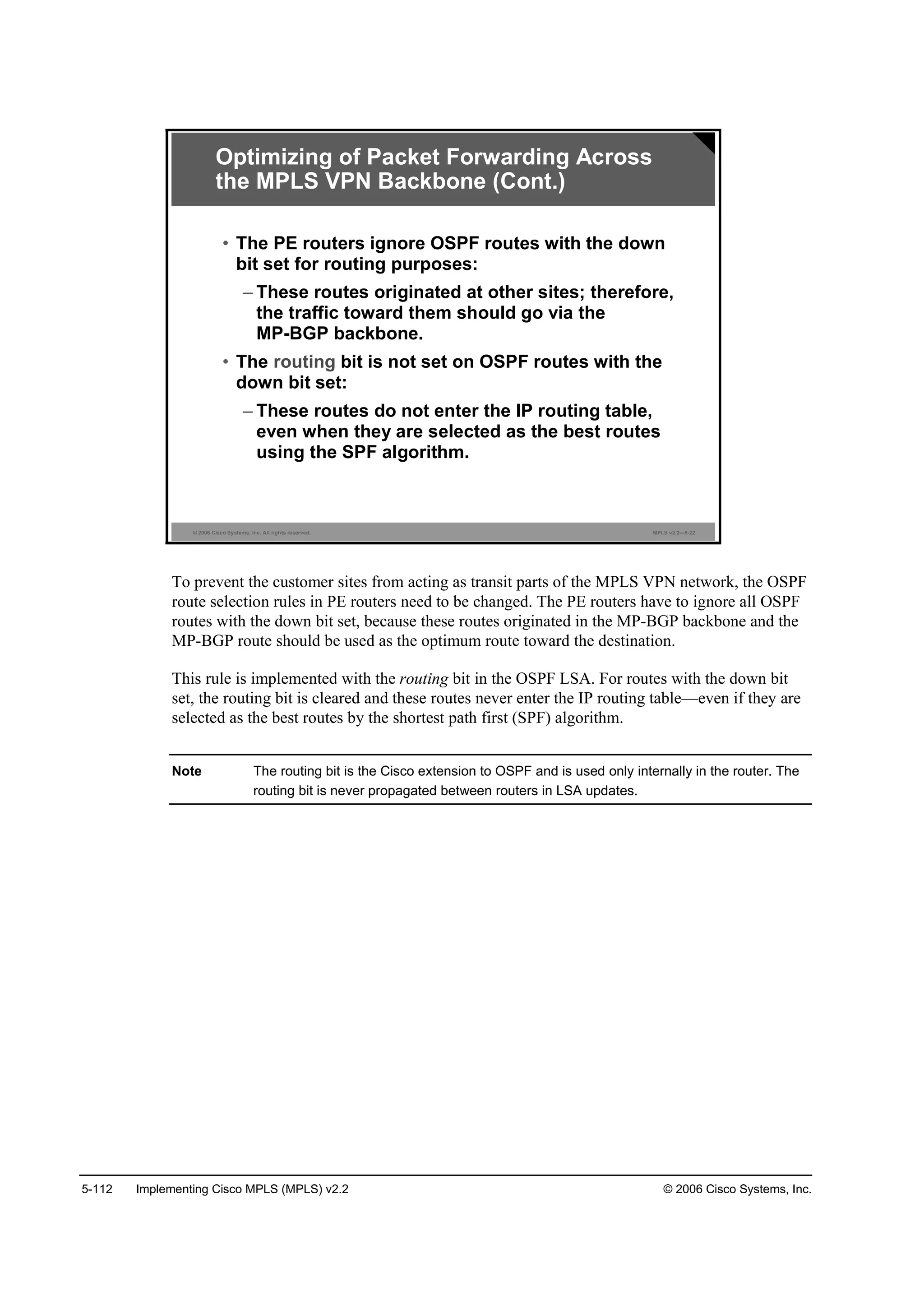
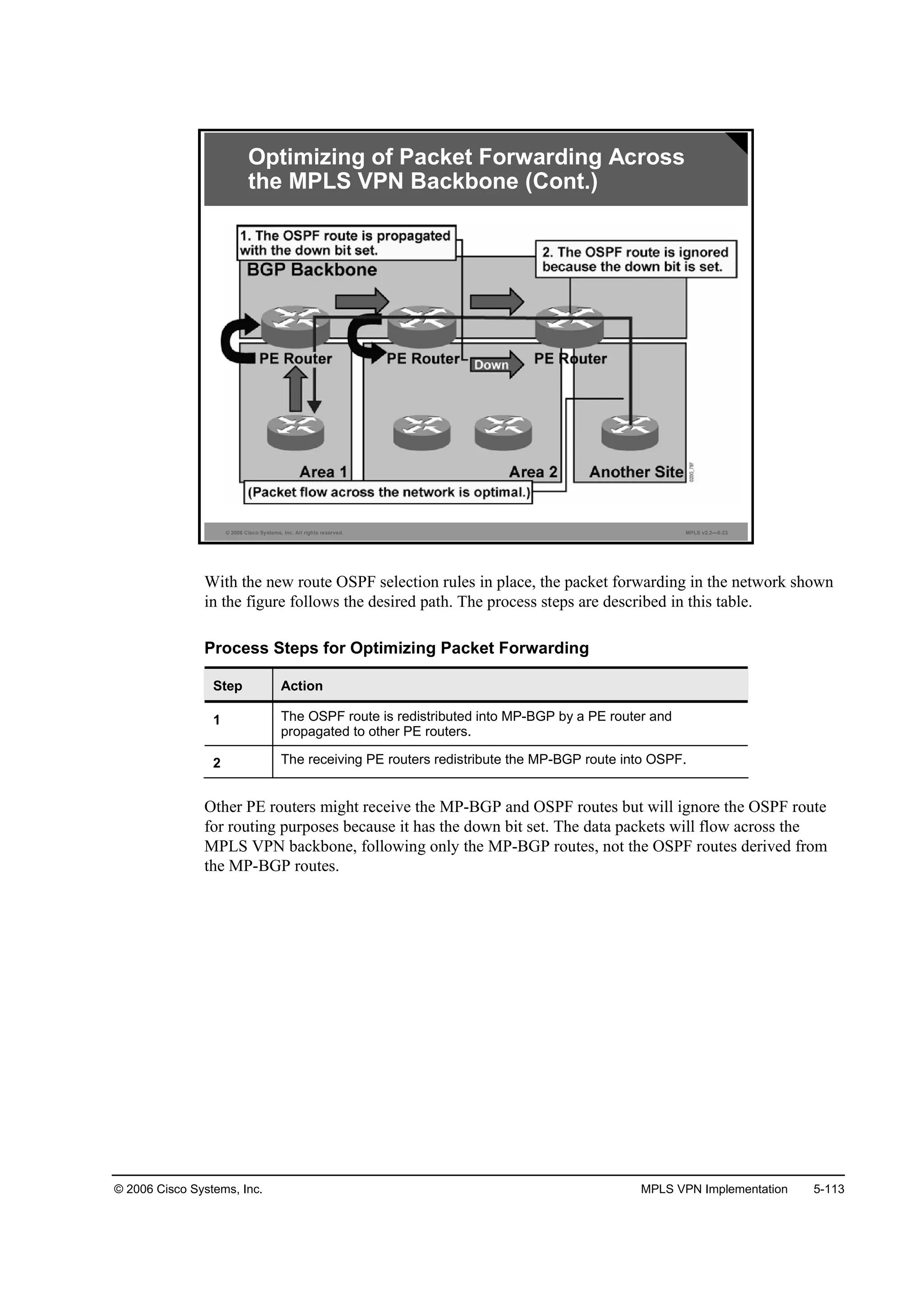
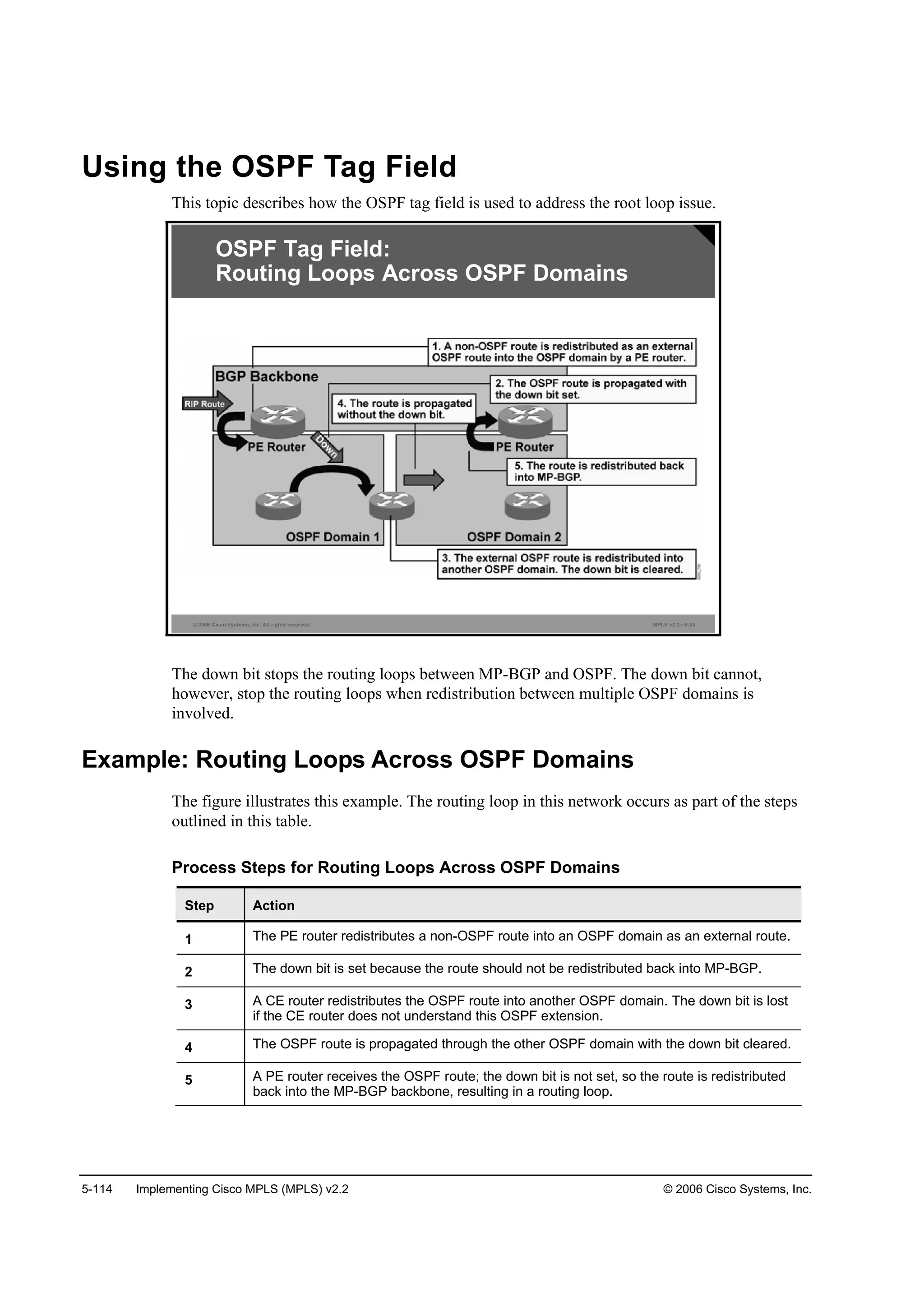
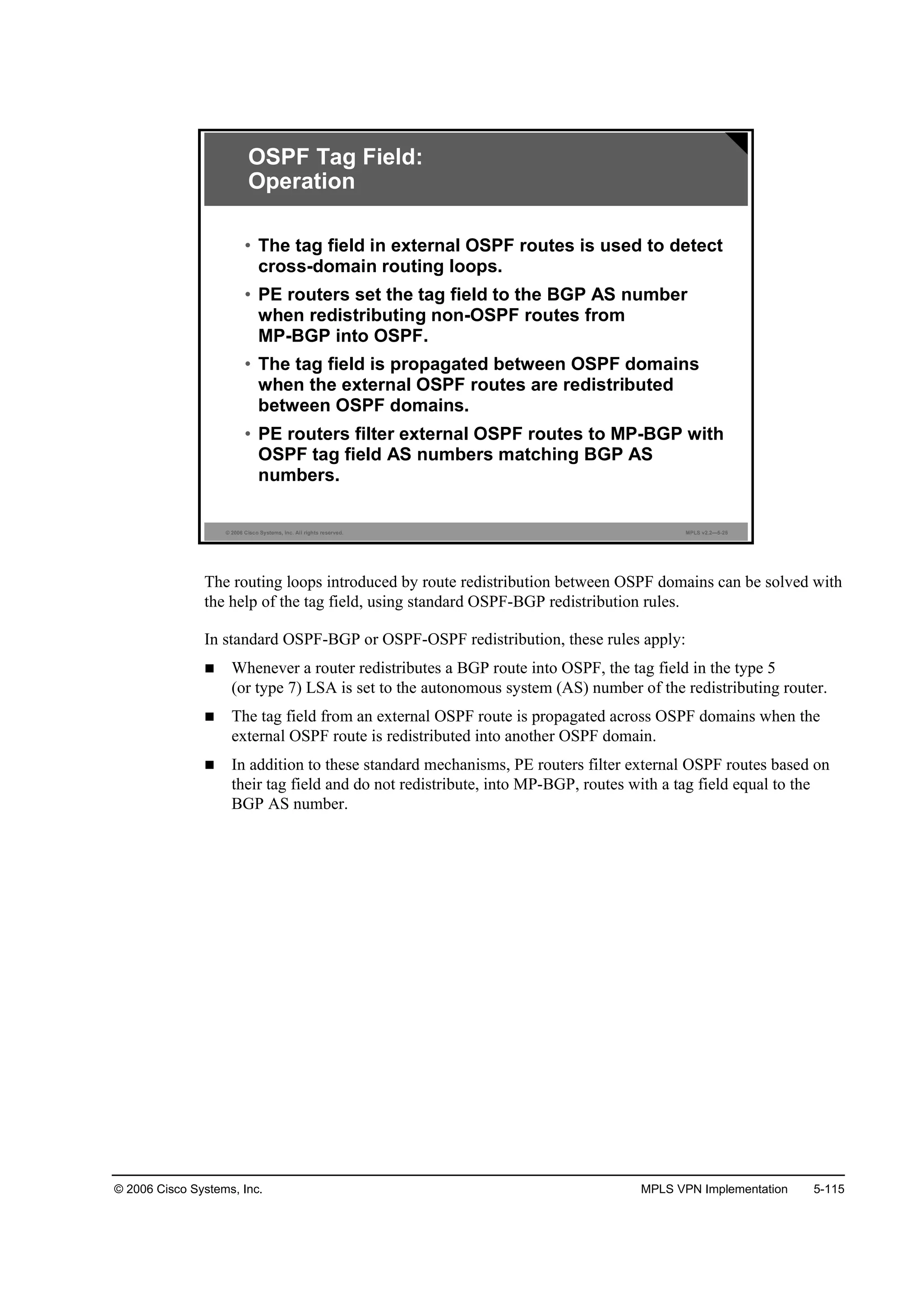
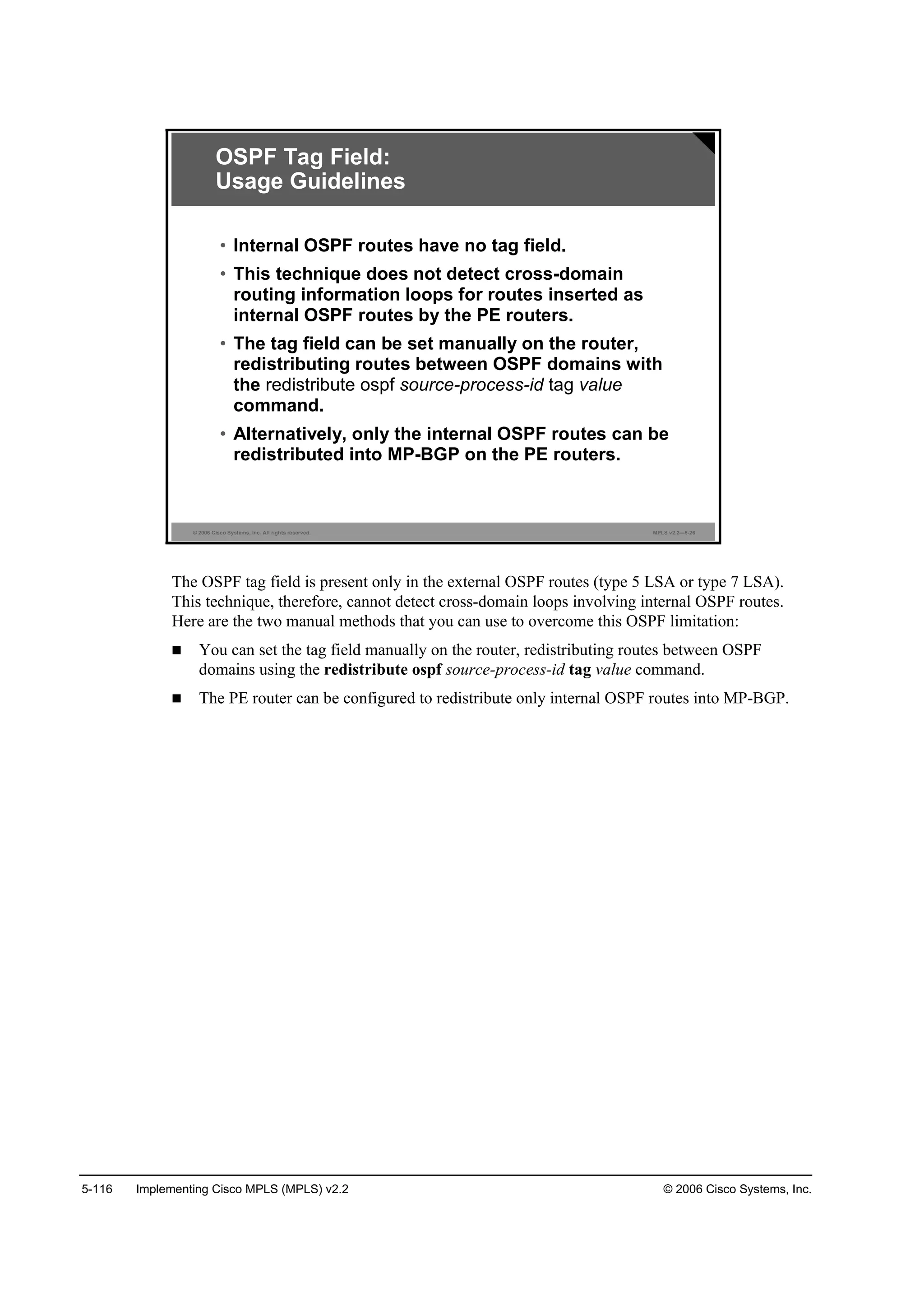
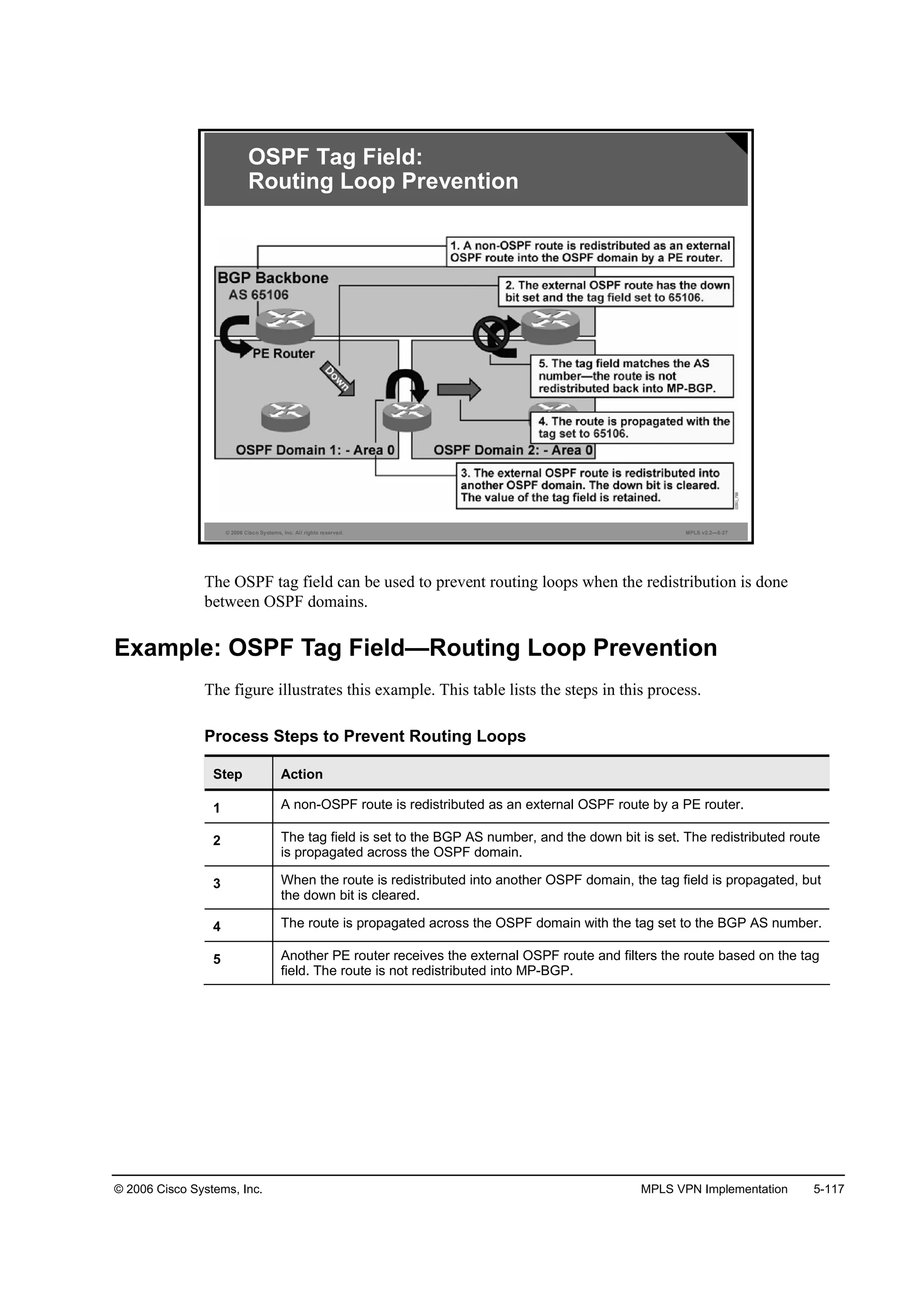
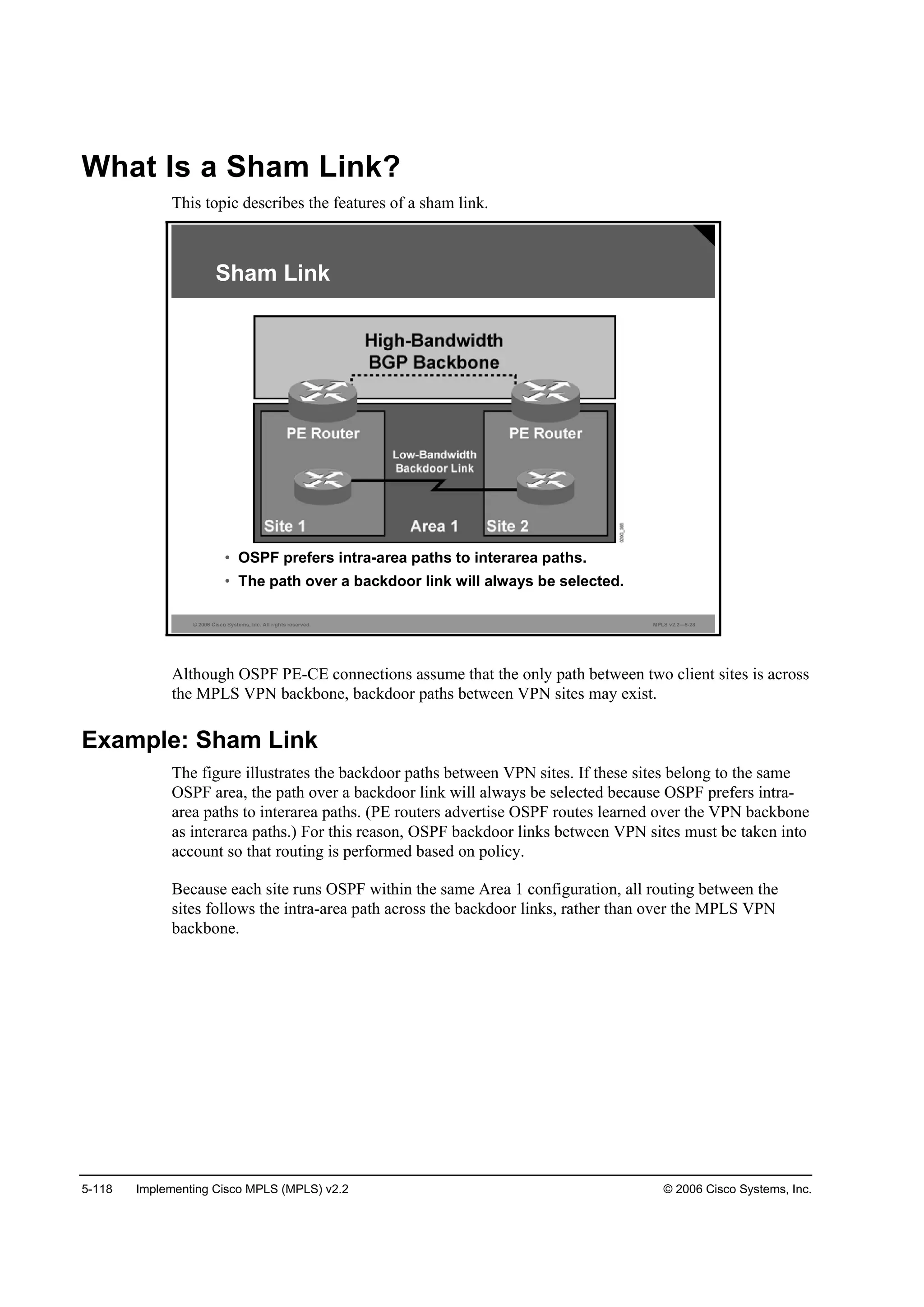
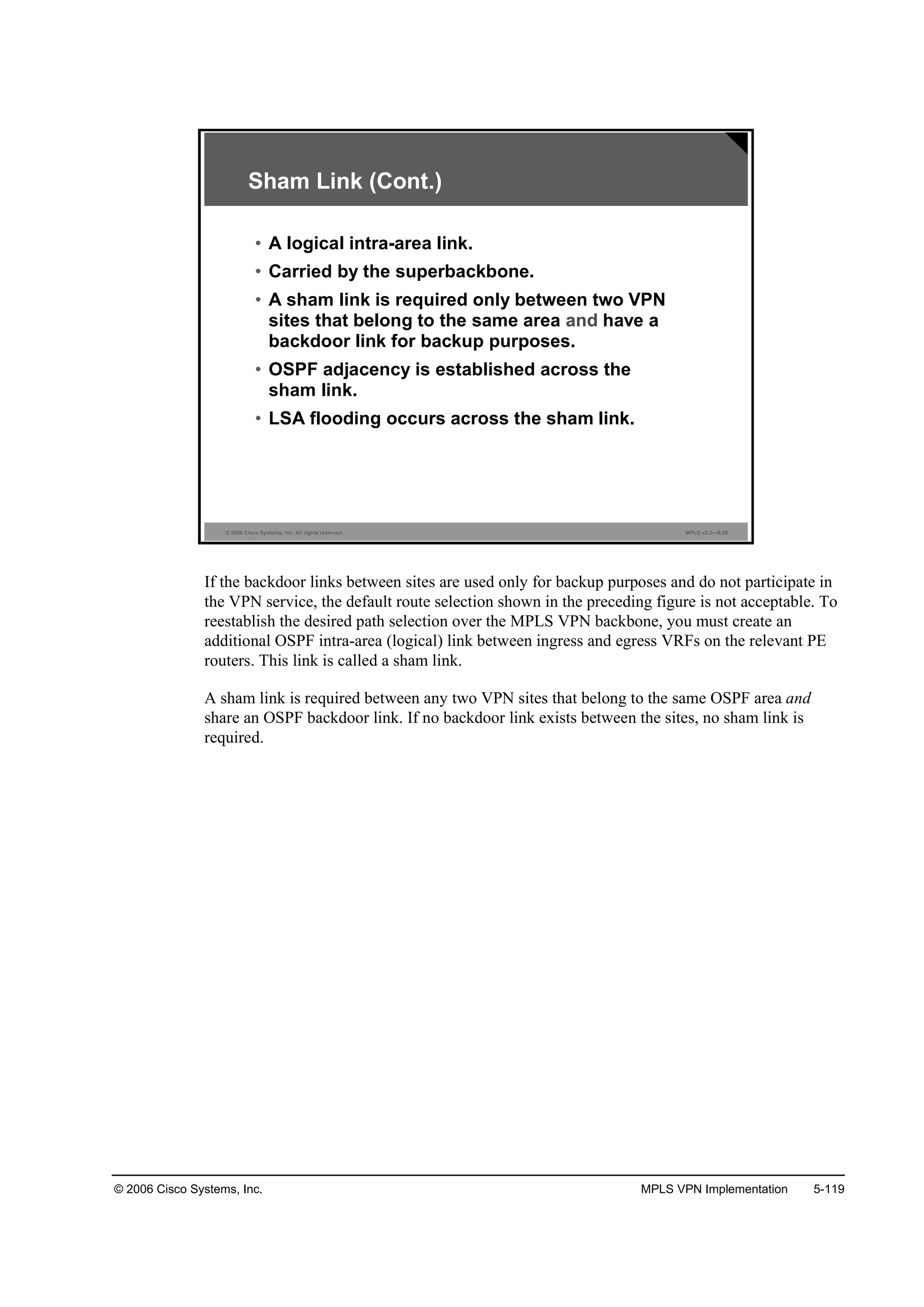
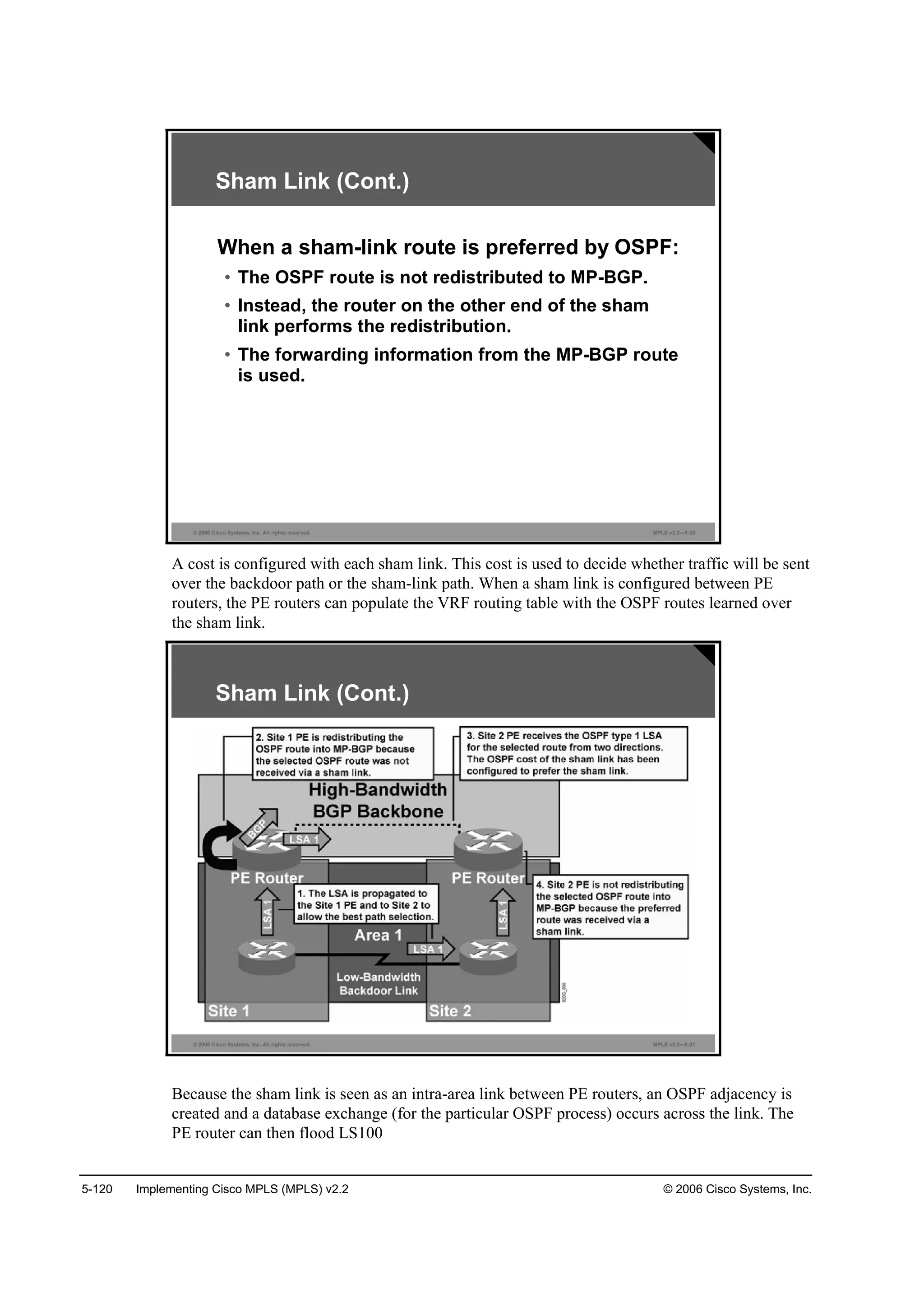
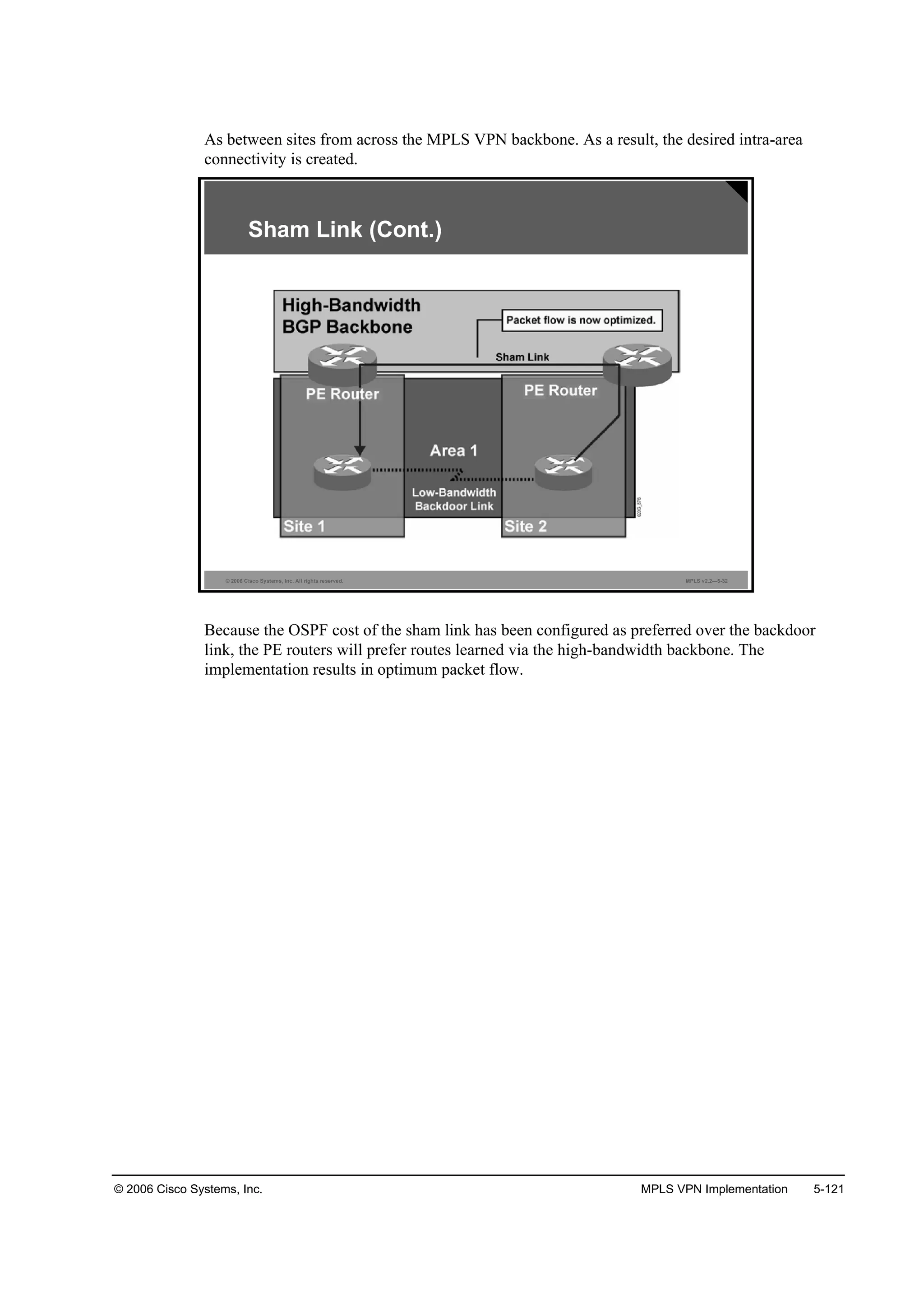
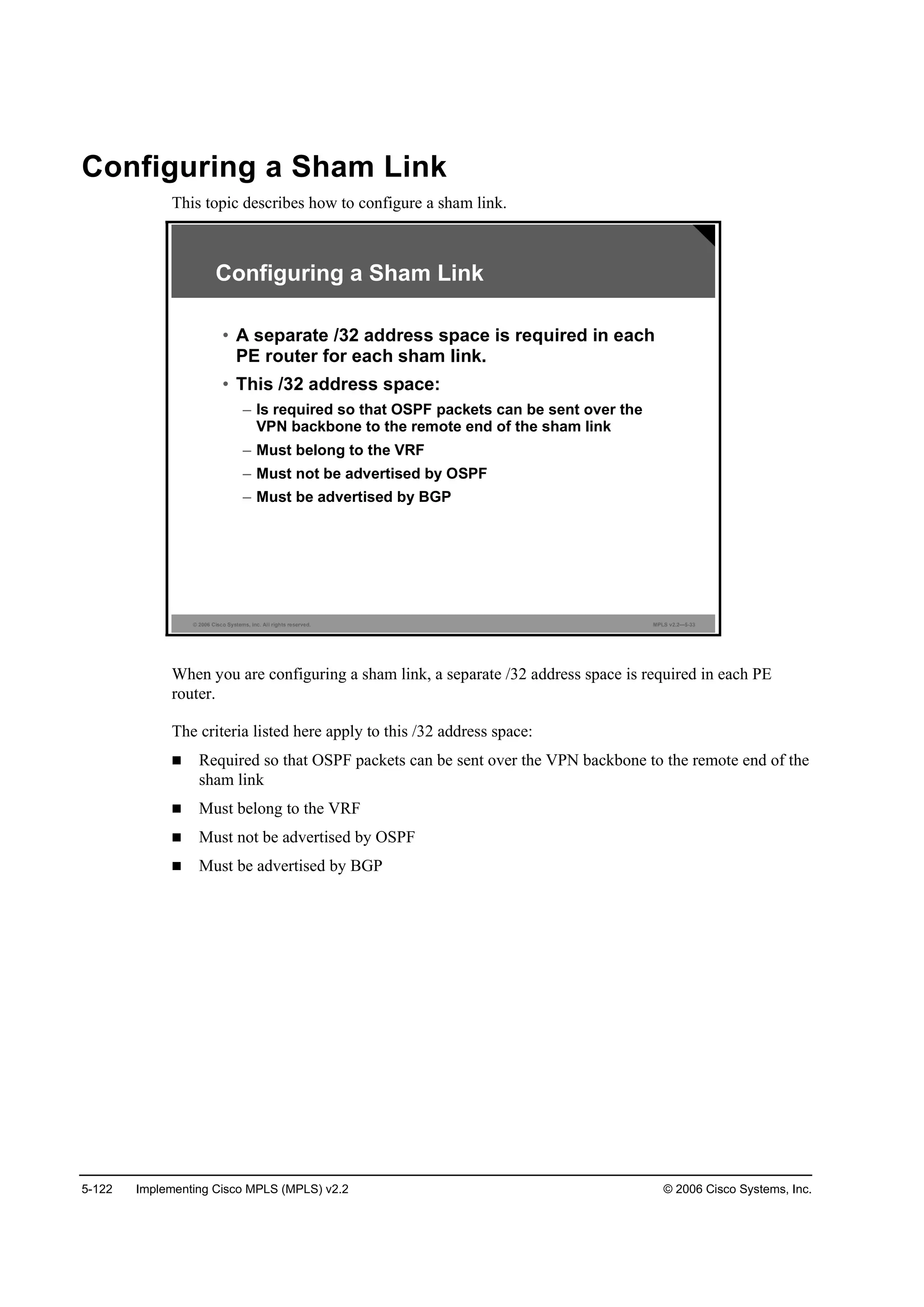
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-123
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-34
ż®»ż ż®»żó·Ľ ¸żłó´·˛µ ±«®˝»óżĽĽ®» Ľ»¬·˛ż¬·±˛óżĽĽ®» ˝±¬ ˛«łľ»®
®±«¬»®ř˝±˛ş·ąó®±«¬»®÷ý
• This command was introduced in Cisco IOS
Release 12.2(8)T.
• The sham link belongs to the specified area.
• Sham-link packets sent across the MPLS VPN
backbone will have the specified source and
destination addresses.
• When the SPF algorithm is executed, the sham link
will have the specified cost.
Configuring a Sham Link (Cont.)
To configure a sham-link interface on a PE router in an MPLS VPN backbone, use the area
sham-link cost command in global configuration mode. To remove the sham link, use the no
form of this command.
area area-id sham-link source-address destination-address cost number
no area area-id sham-link source-address destination-address cost number
This table describes the parameters for the area sham-link cost command.
Syntax Description
Parameter Description
ż®»żó·Ľ ID number of the OSPF area assigned to the sham link; valid
values: numeric value or valid IP address
There is no default.
±«®˝»óżĽĽ®» IP address of the source PE router in the format: ip-address
[mask]
Ľ»¬·˛ż¬·±˛óżĽĽ®» IP address of the destination PE router in the format: ip-address
[mask]
˛«łľ»® OSPF cost to send IP packets over the sham-link interface
Valid values are from 1 to 65535.
Defaults
There is no default behavior or values.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-438-2048.jpg)
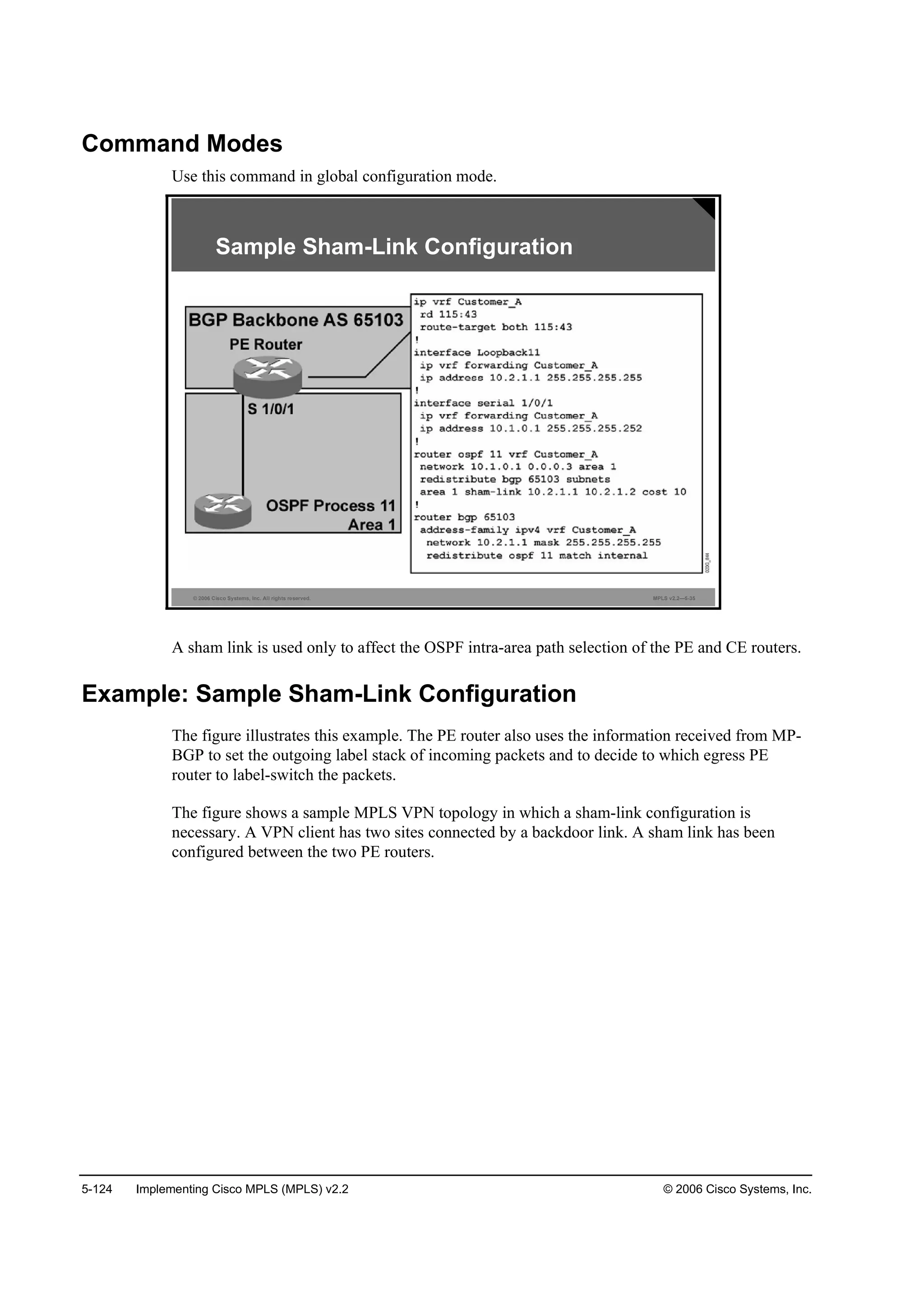
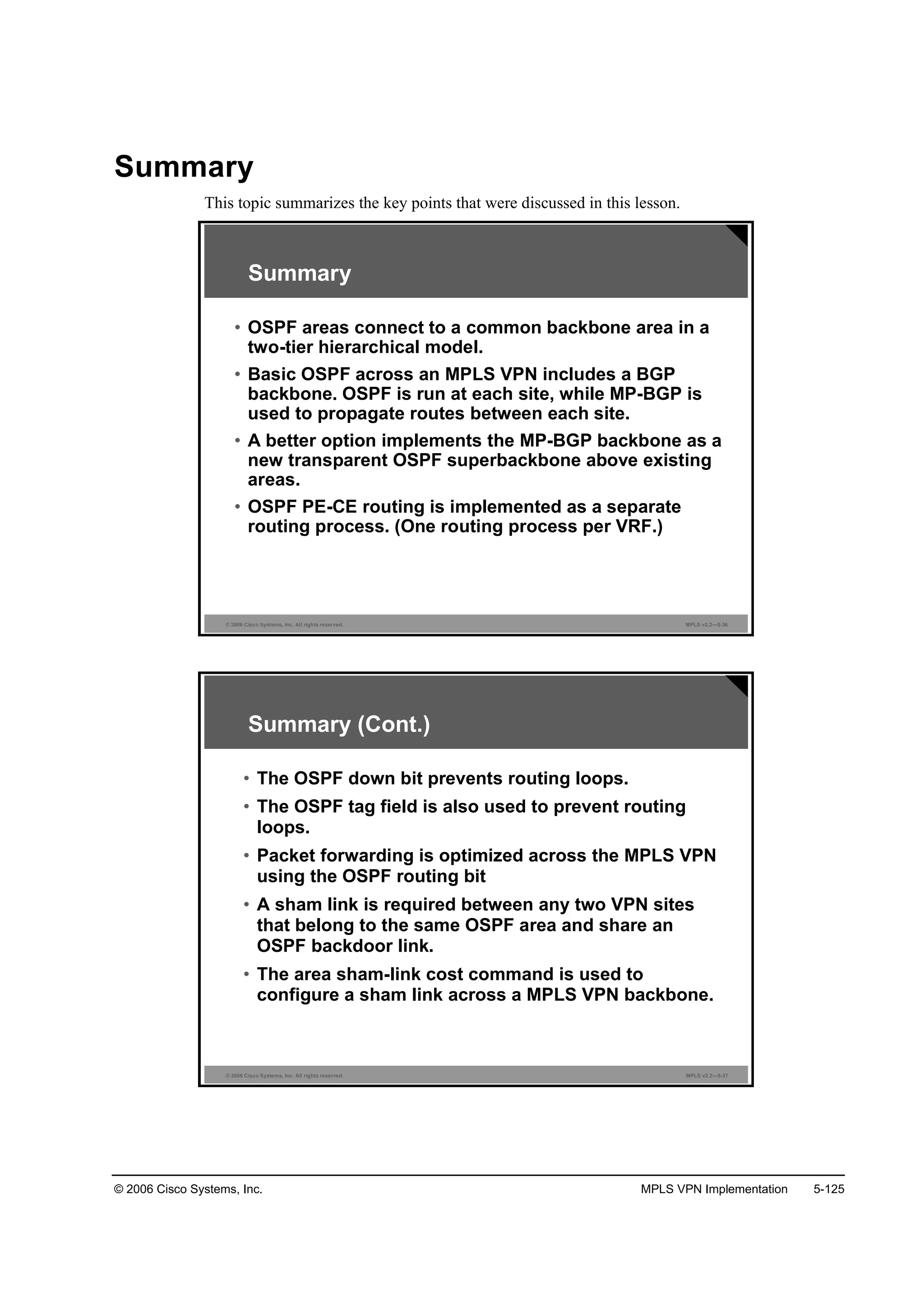

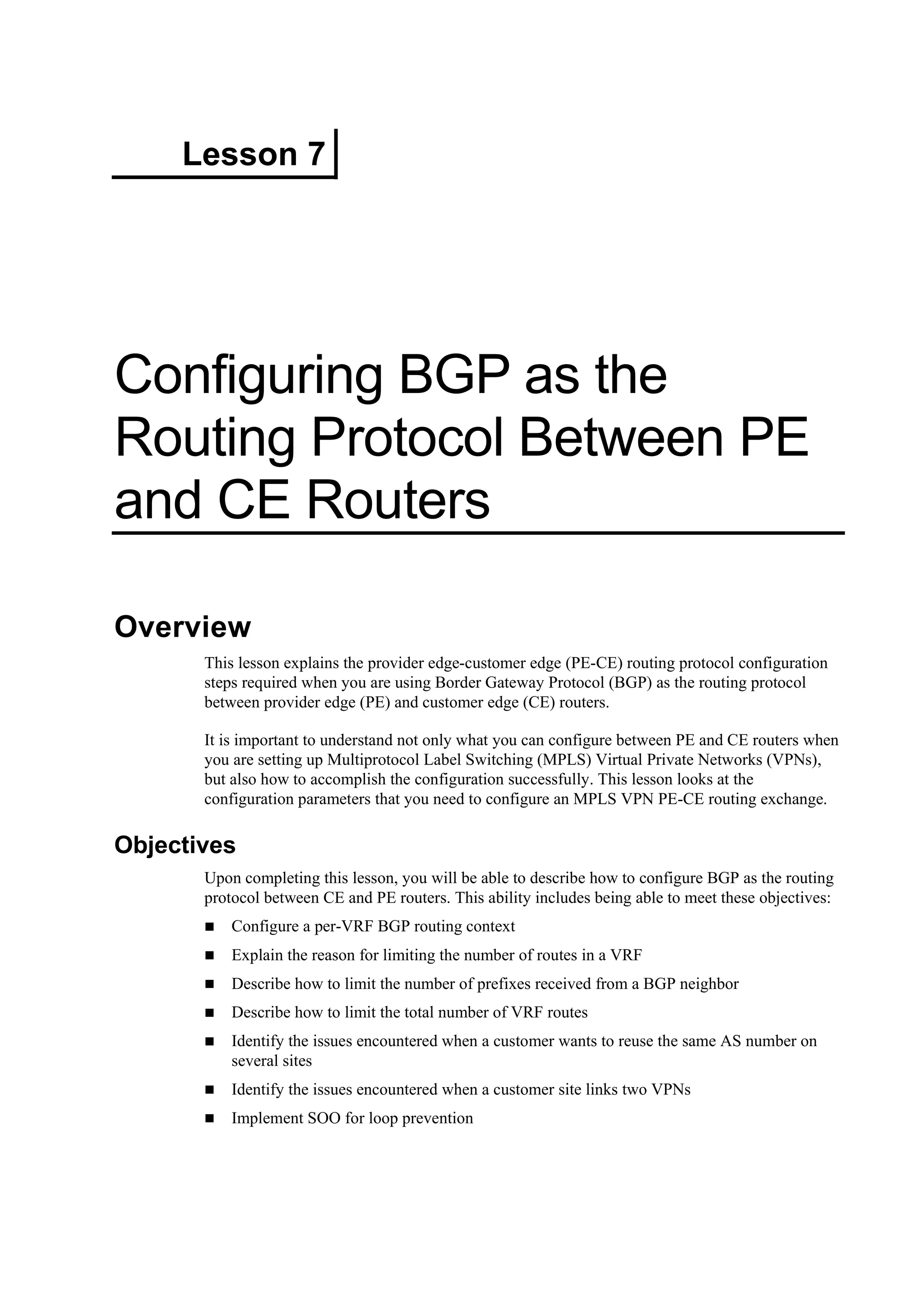
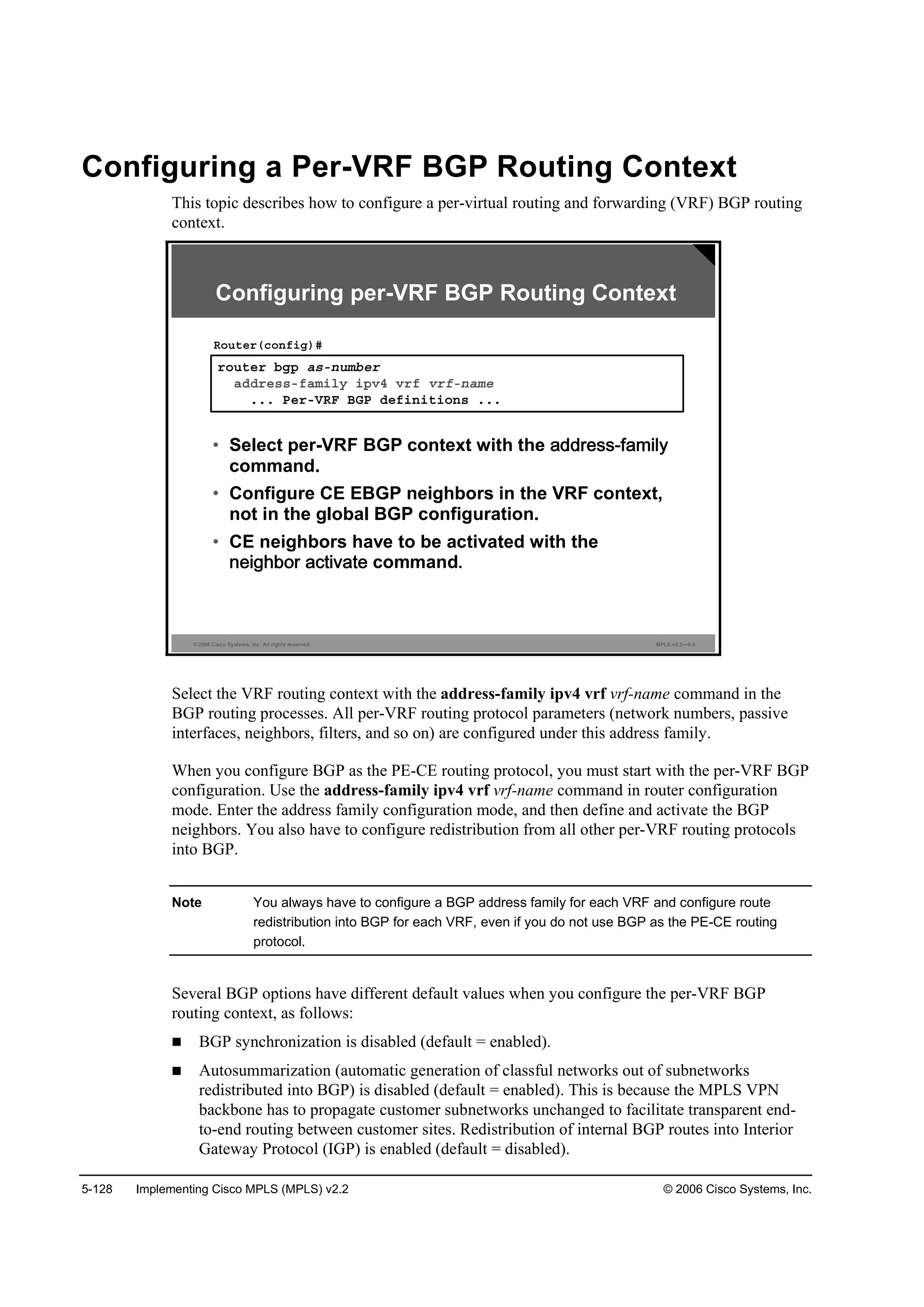
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-129
Note The common parameters defined in router configuration mode are inherited by all address
families defined for this routing process and can be overridden for each individual address
family.
address-family ipv4
To enter address family configuration mode for configuring routing sessions (such as BGP) that
use standard IP version 4 (IPv4) address prefixes, use the address-family ipv4 command in
router configuration mode. To disable address family configuration mode, use the no form of
this command.
address-family ipv4 [multicast | unicast | vrf vrf-name]
no address-family ipv4 [multicast | unicast | vrf vrf-name]
This table describes the parameters for the address-family ipv4 command.
Syntax Description
Parameter Description
ł«´¬·˝ż¬ (Optional) Specifies IPv4 multicast address prefixes
«˛·˝ż¬ (Optional) Specifies IPv4 unicast address prefixes
Ş®ş Ş®şó˛żł» (Optional) Specifies the name of the VRF instance to associate
with subsequent IPv4 address family configuration mode
commands
Defaults
IPv4 address prefixes are not enabled. Unicast address prefixes are the default when IPv4
address prefixes are configured.
Command Modes
Use this command in router configuration mode.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-444-2048.jpg)
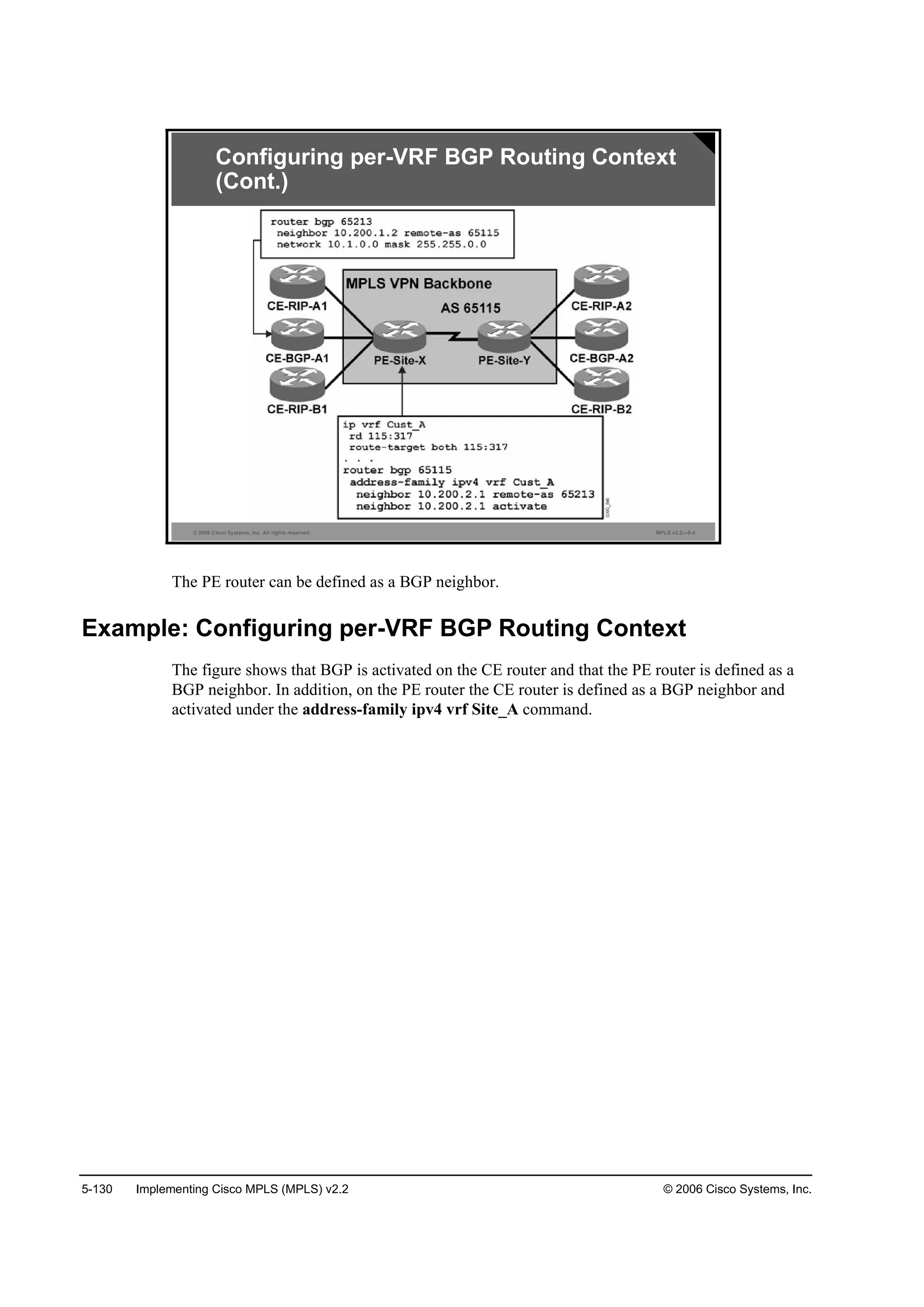
![5-132 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Limiting the Number of Prefixes Received from a
BGP Neighbor
This topic describes how to limit the number of prefixes received from a BGP neighbor.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-6
˛»·ą¸ľ±® ·°óżĽĽ®» łż¨·ł«łó°®»ş·¨ łż¨·ł«ł Ŭ¸®»¸±´ĽĂ
Ĺ©ż®˛·˛ąó±˛´§Ă
᫬»®ř˝±˛ş·ąó®±«¬»®óżş÷ý
• Controls how many prefixes can be received from a
neighbor
• Optional threshold parameter specifies the
percentage where a warning message is logged
(default is 75 percent)
• Optional warning-only keyword specifies the
action on exceeding the maximum number
(default is to drop peering)
Limiting the Number of Prefixes Received
from a BGP Neighbor
neighbor maximum-prefix
To control how many prefixes can be received from a neighbor, use the neighbor maximum-
prefix command in router configuration mode. To disable this function, use the no form of this
command.
neighbor {ip-address | peer-group-name} maximum-prefix maximum [threshold]
[warning-only]
no neighbor {ip-address | peer-group-name} maximum-prefix maximum [threshold]
[warning-only]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-447-2048.jpg)
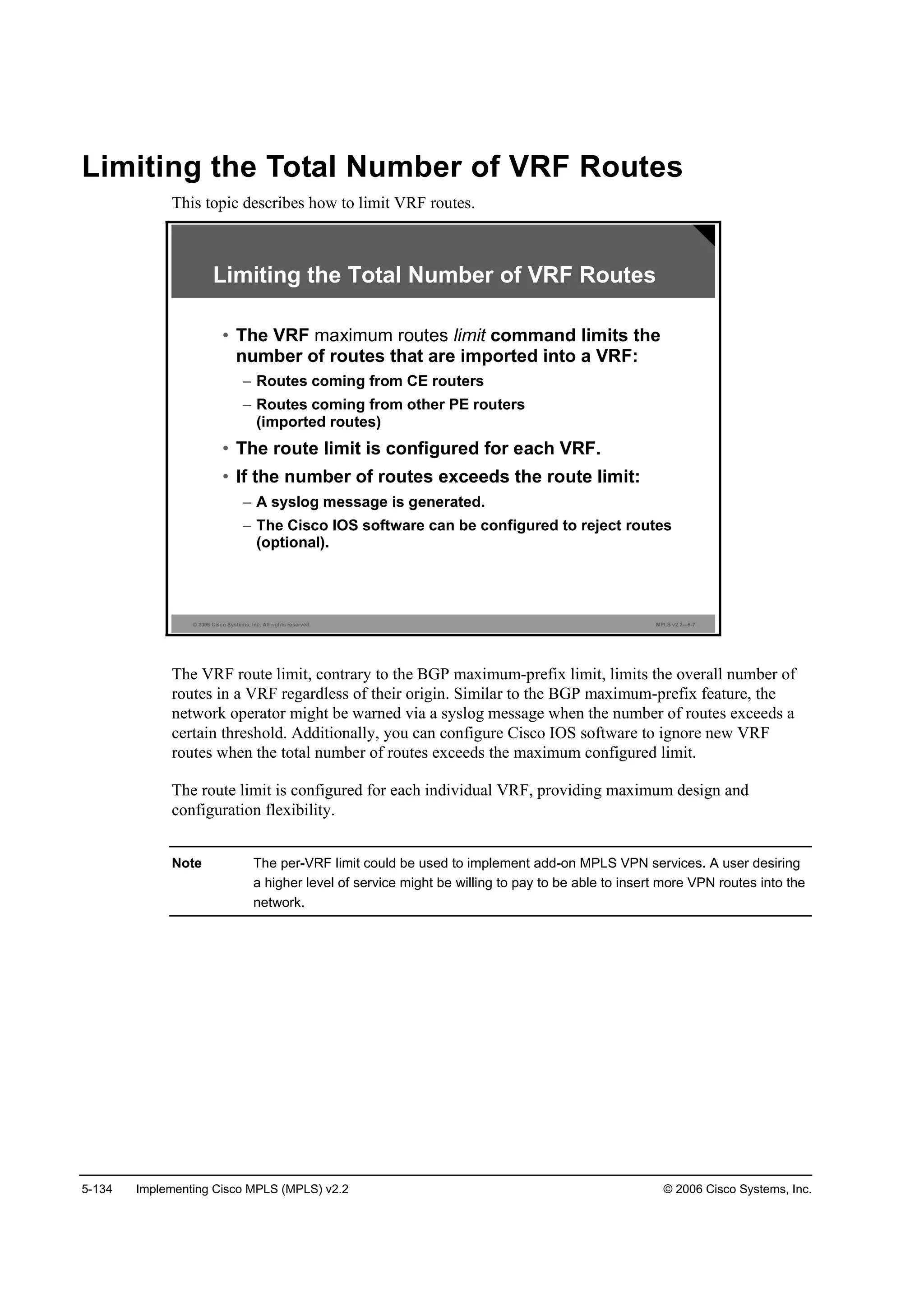
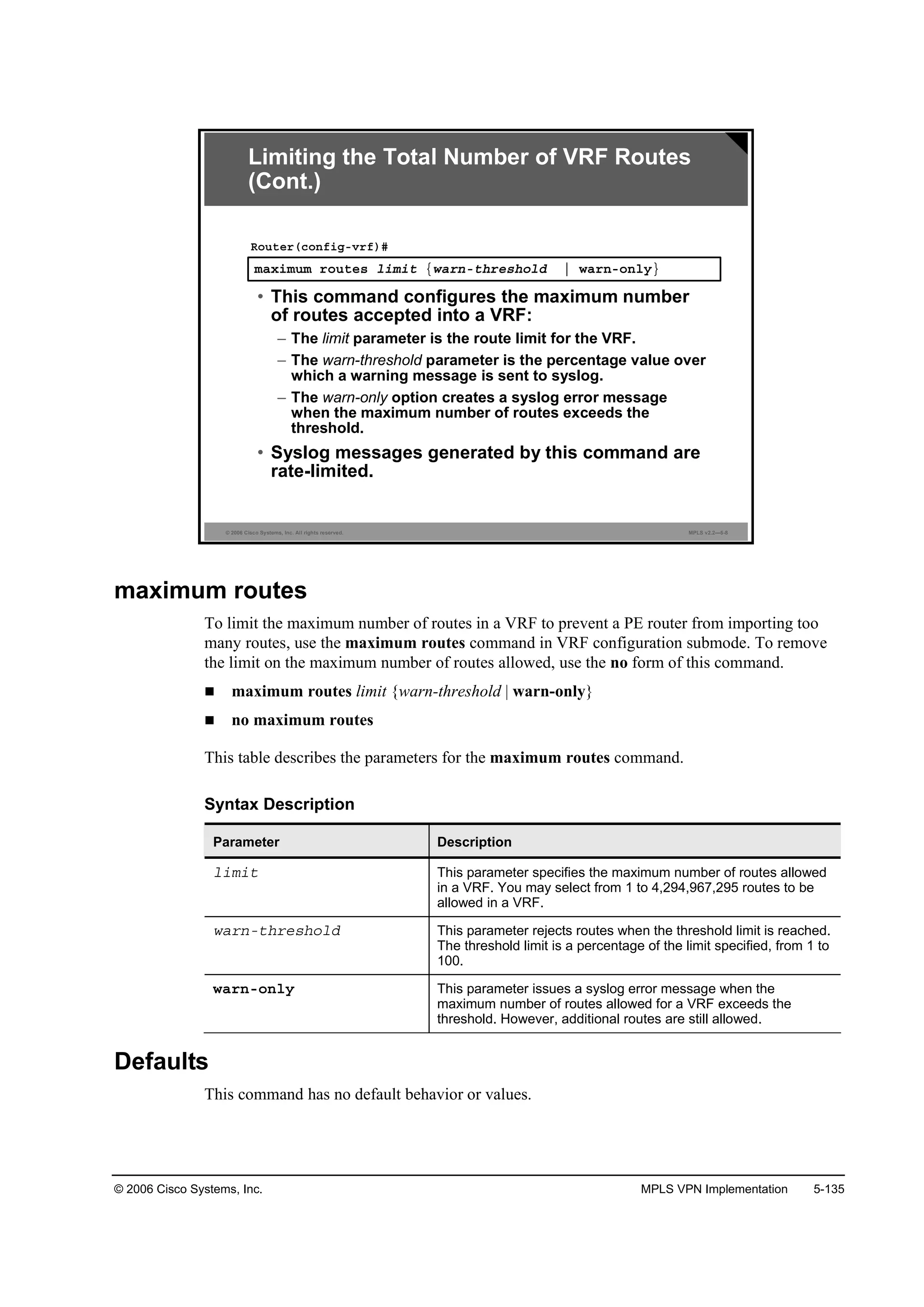
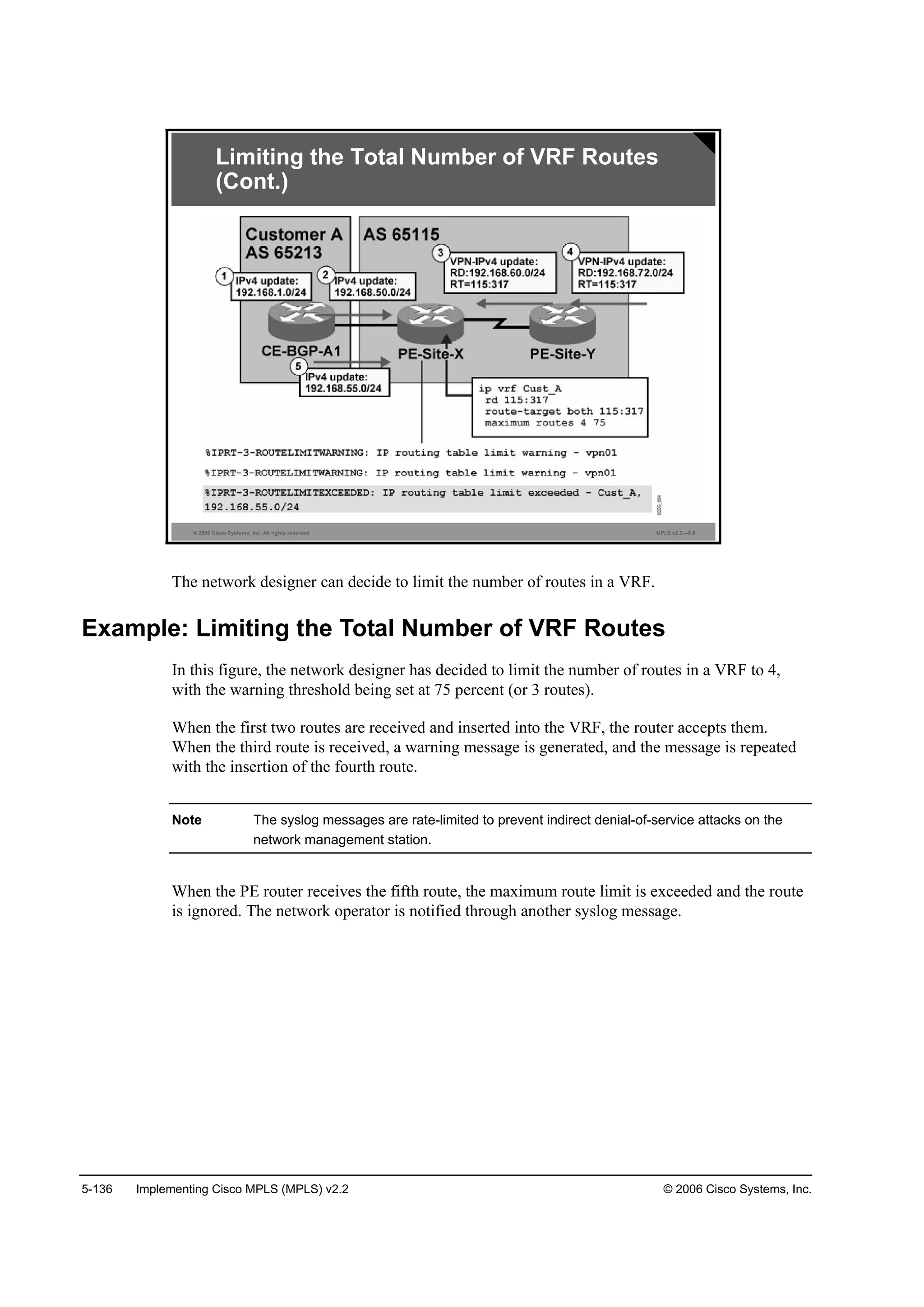
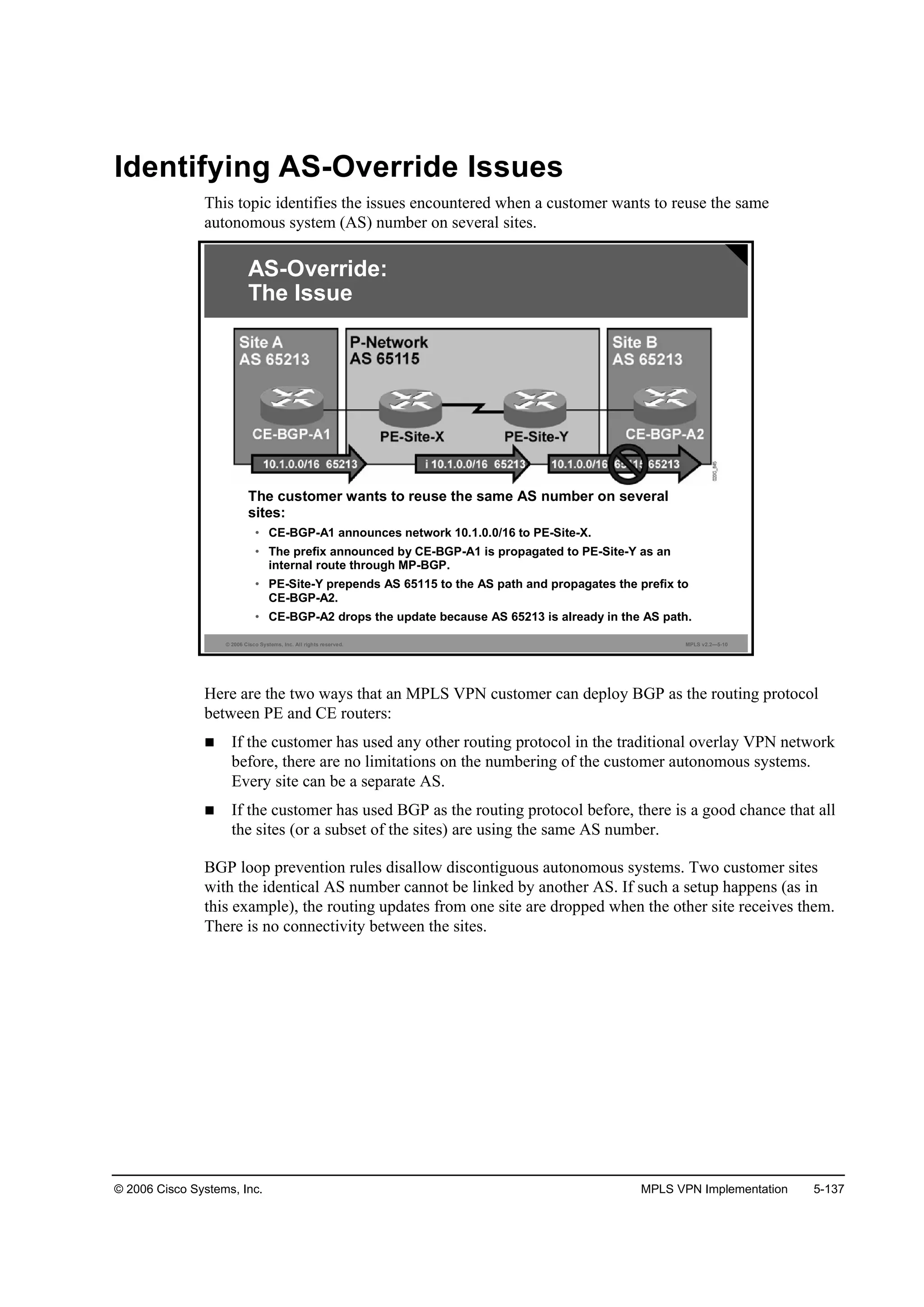
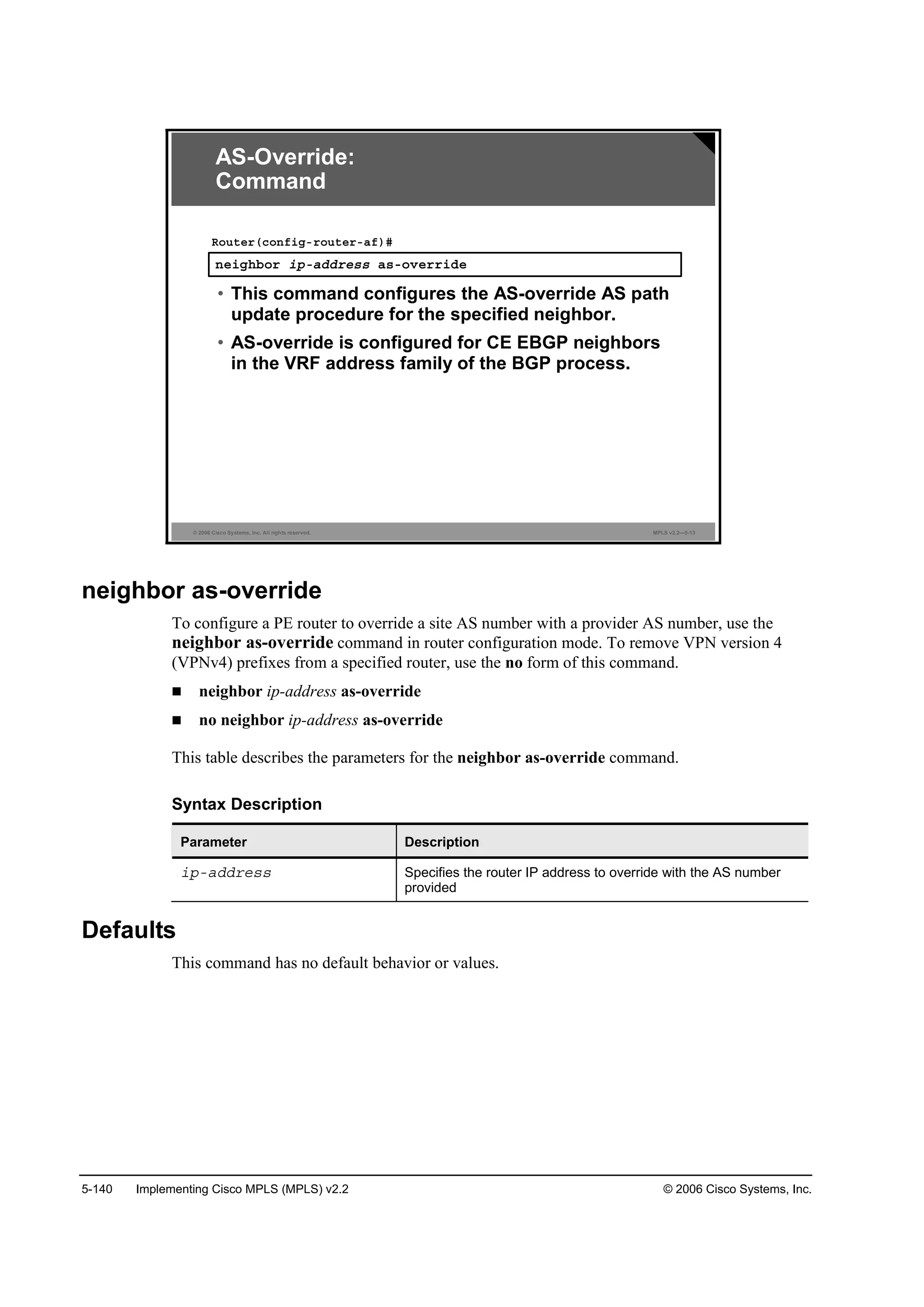
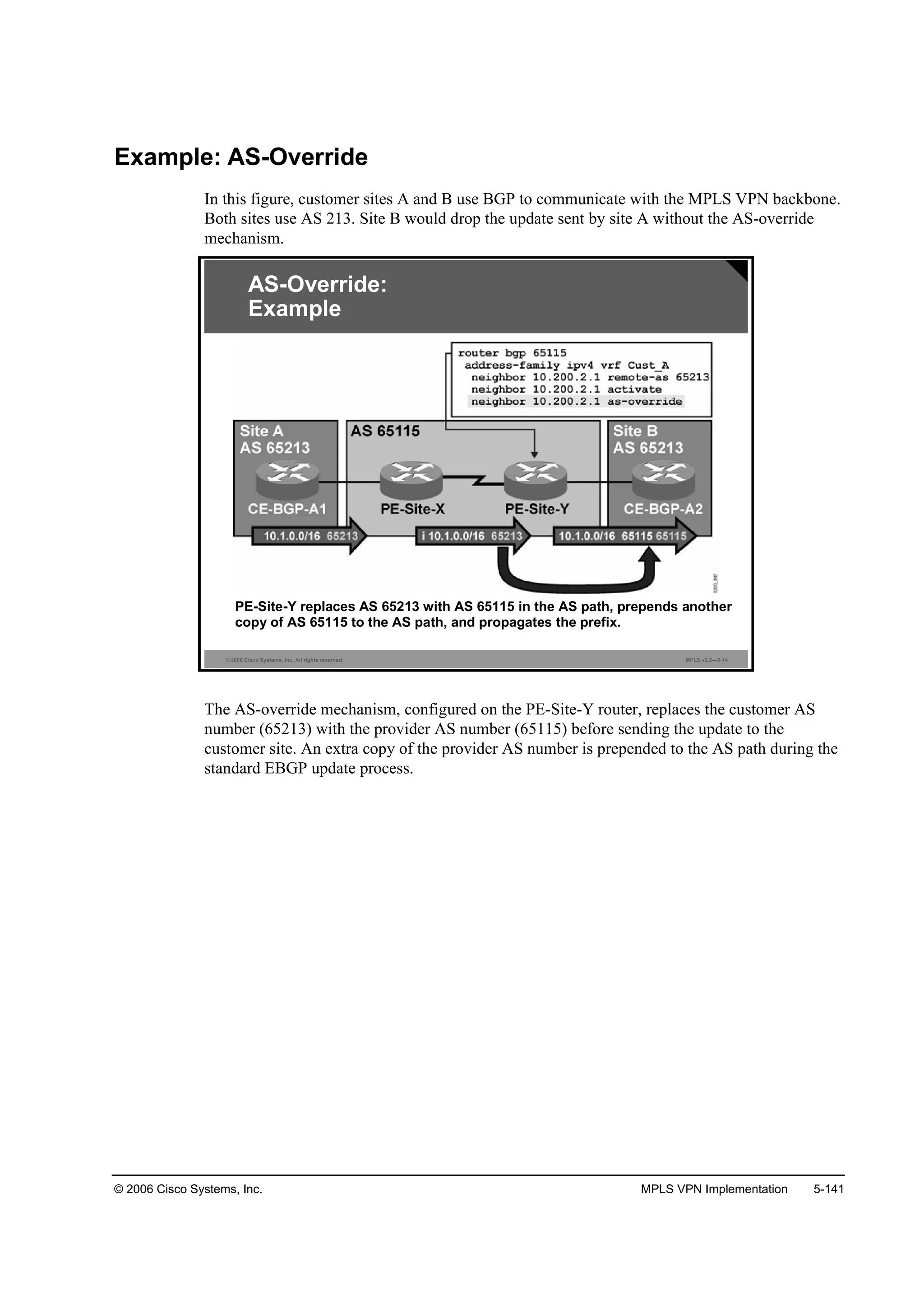
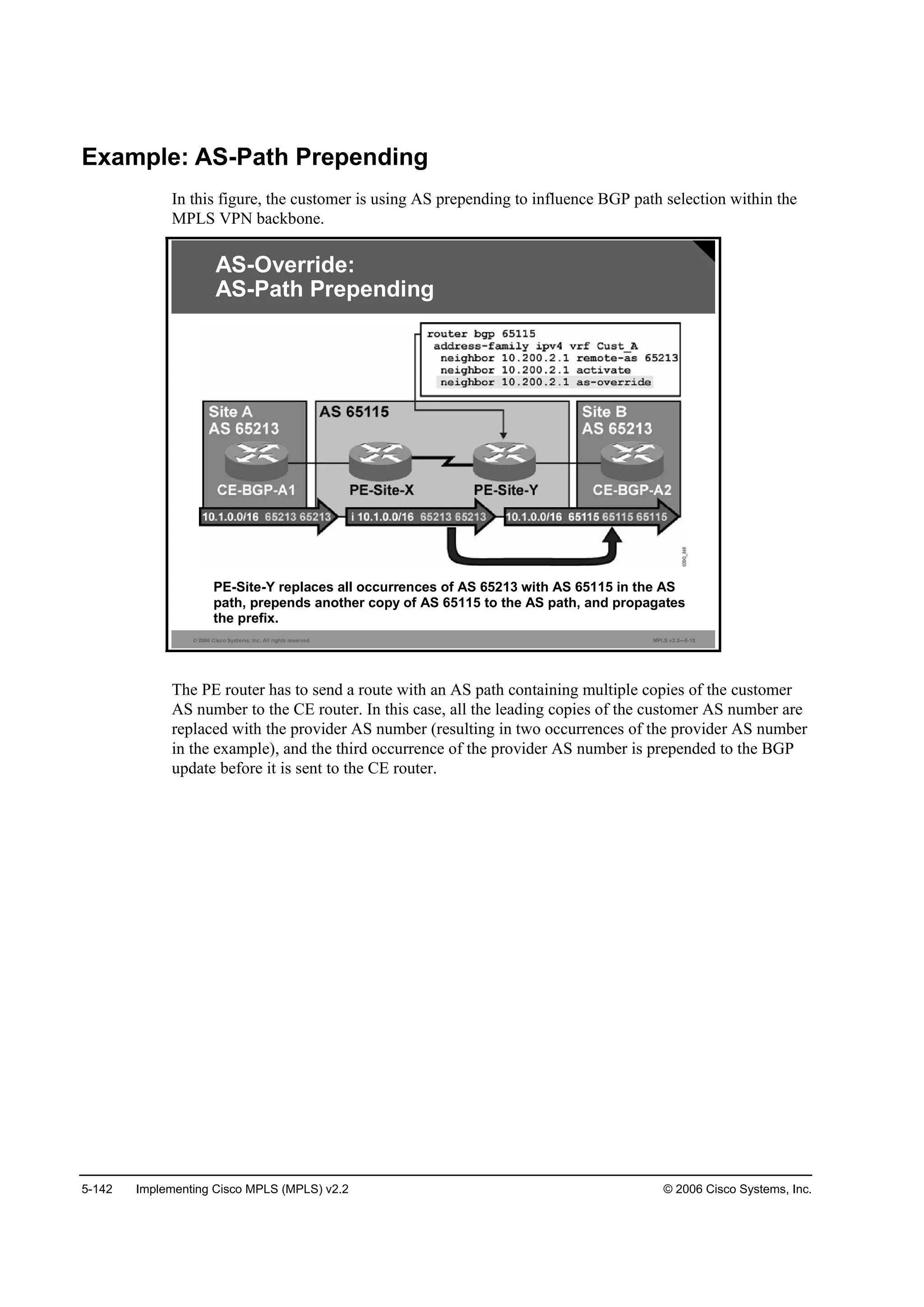
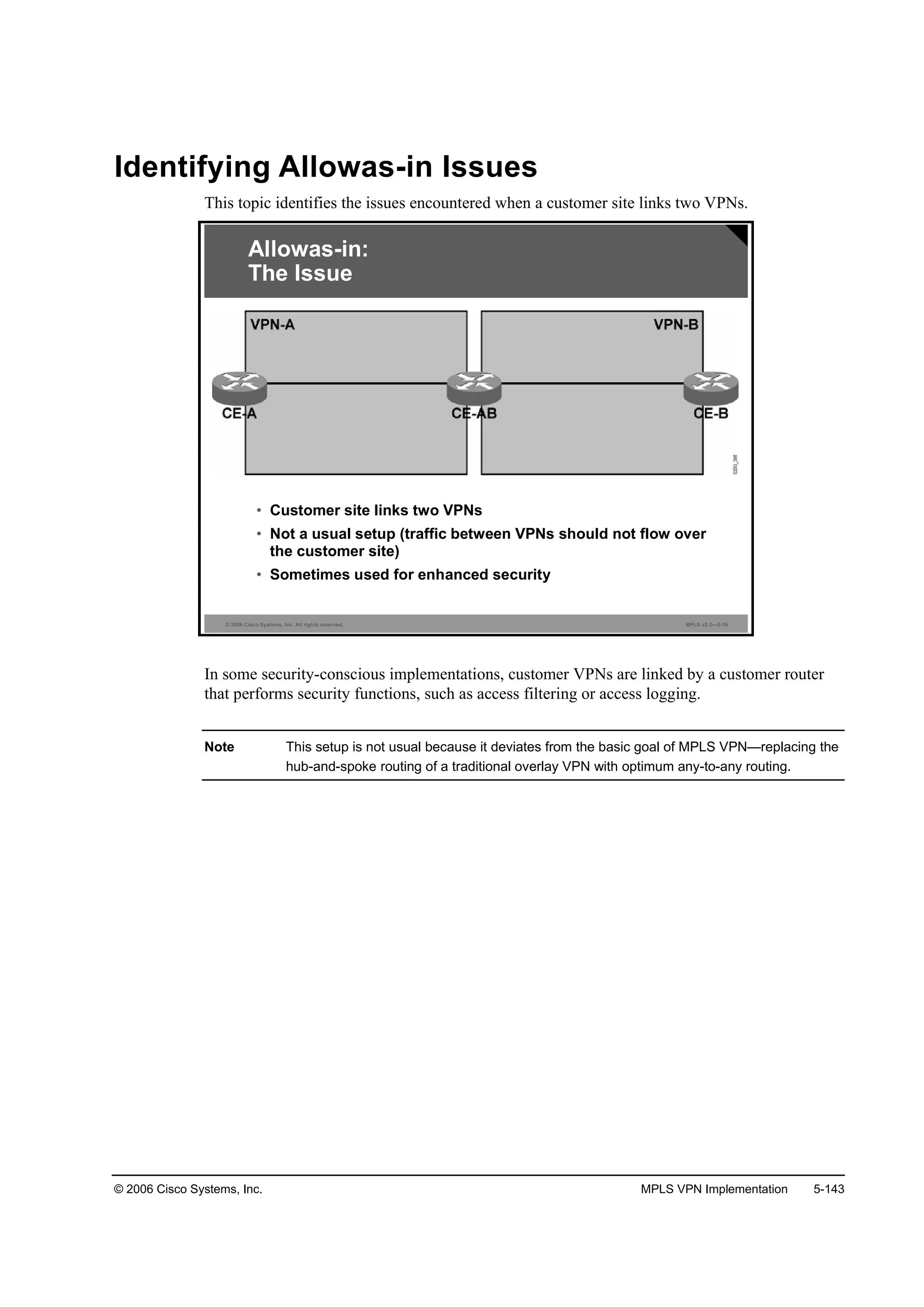
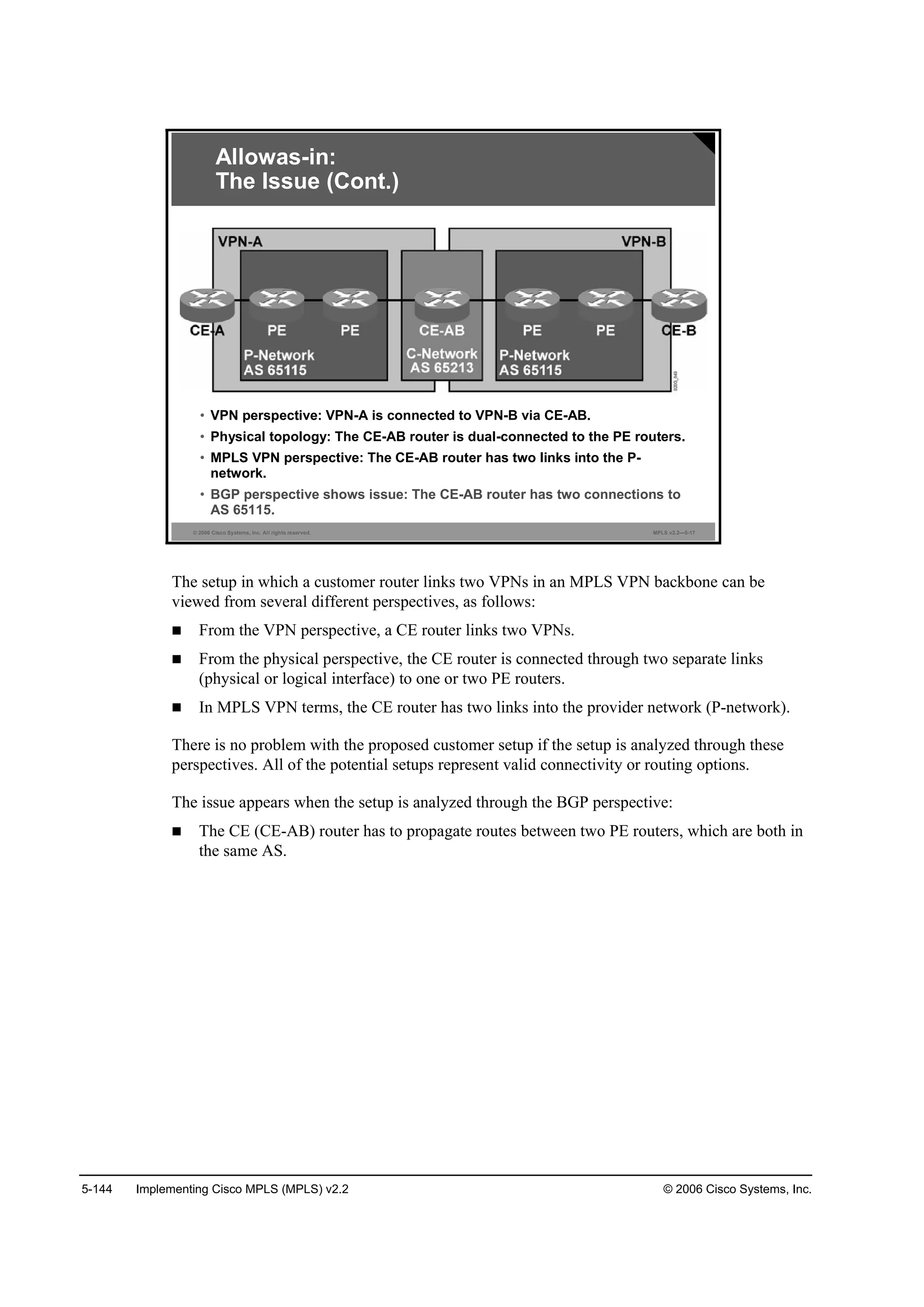
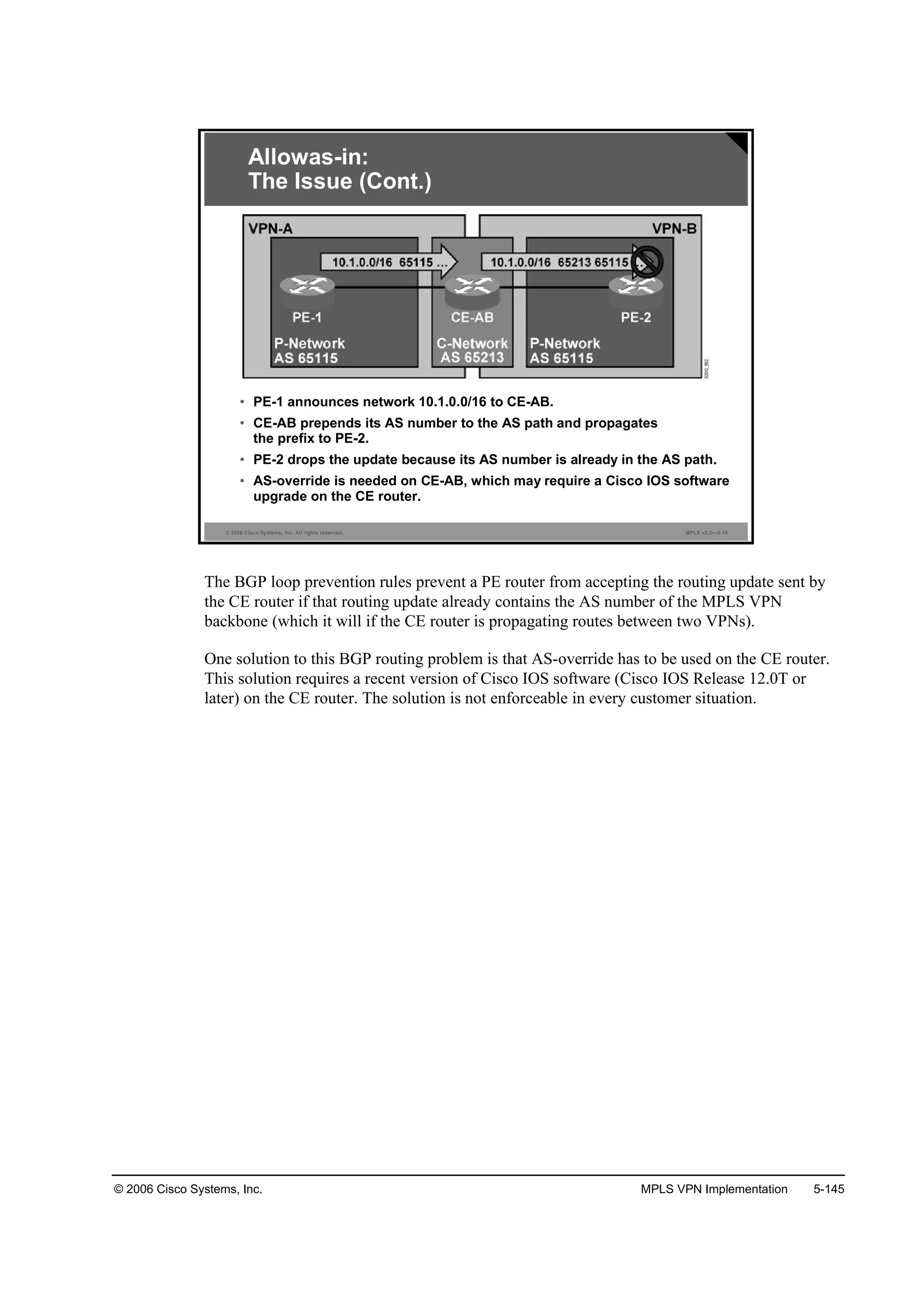
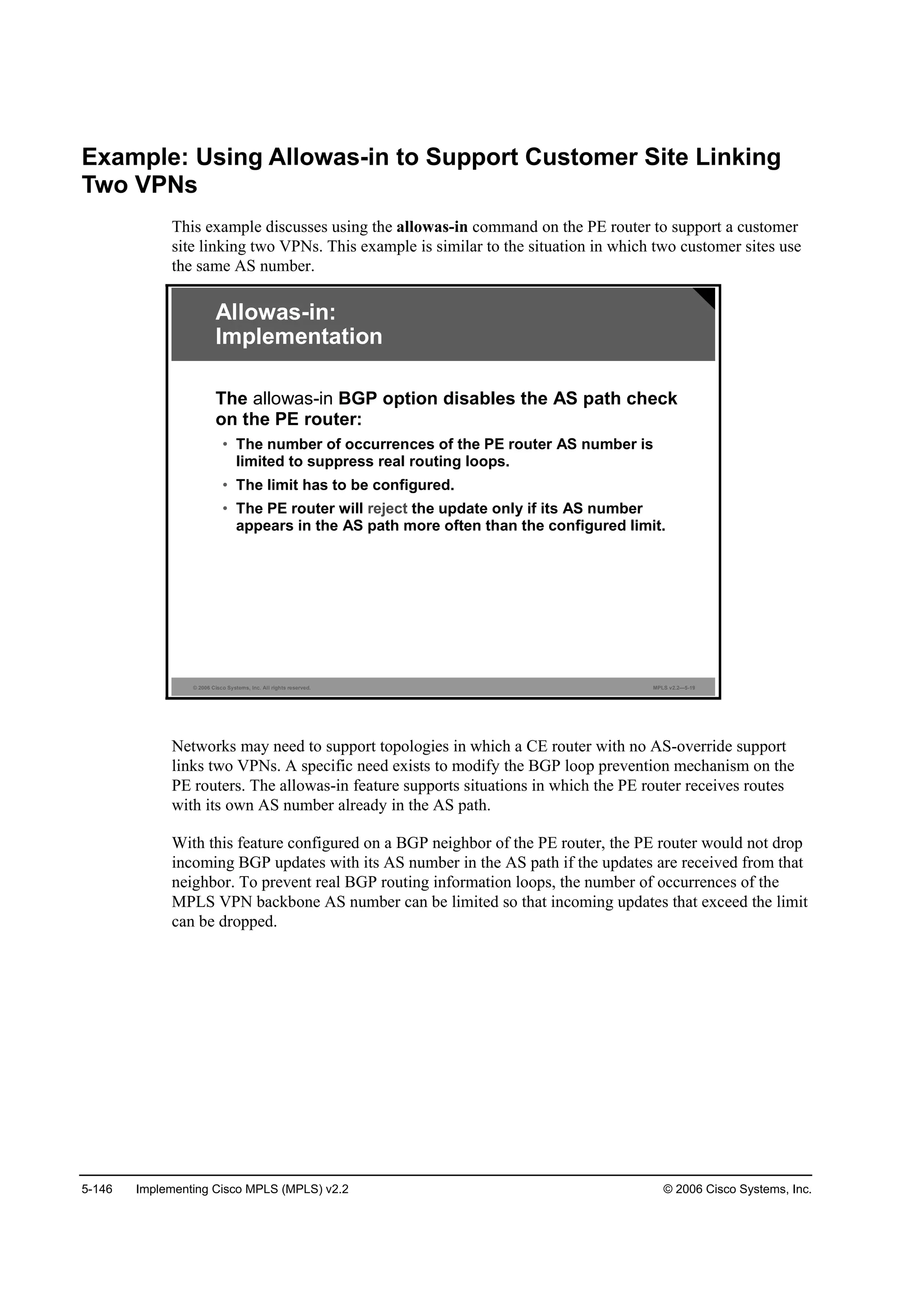
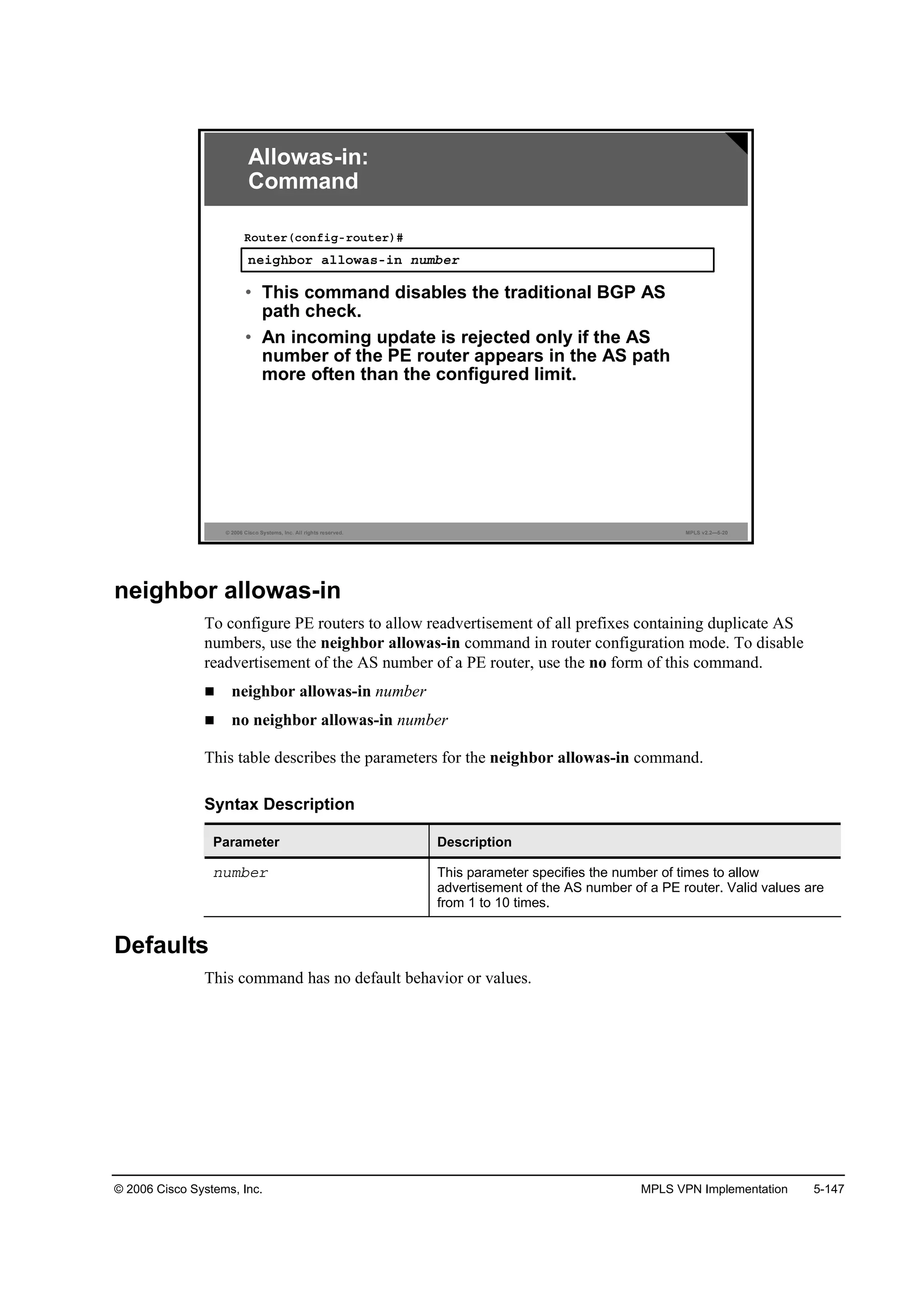
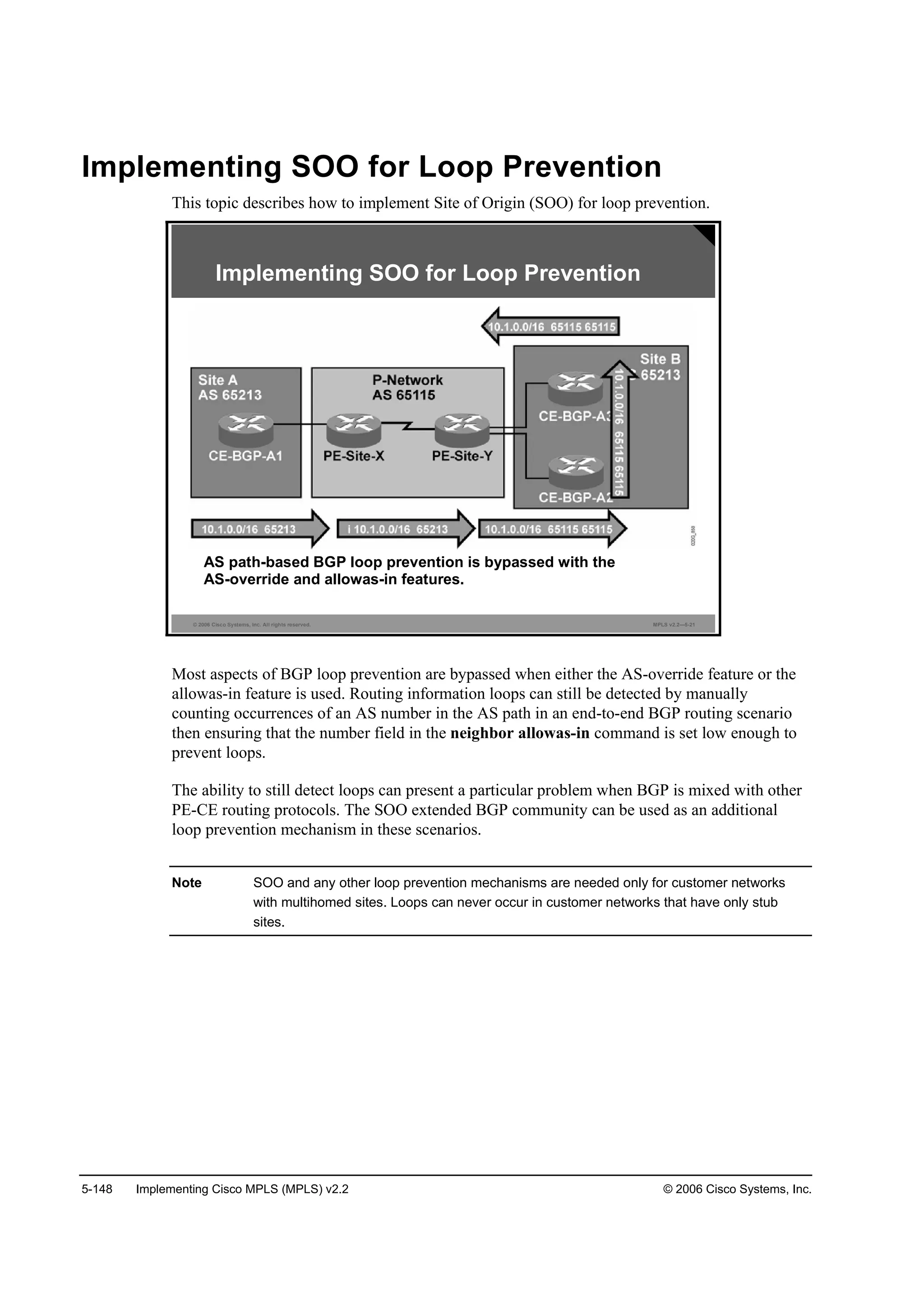
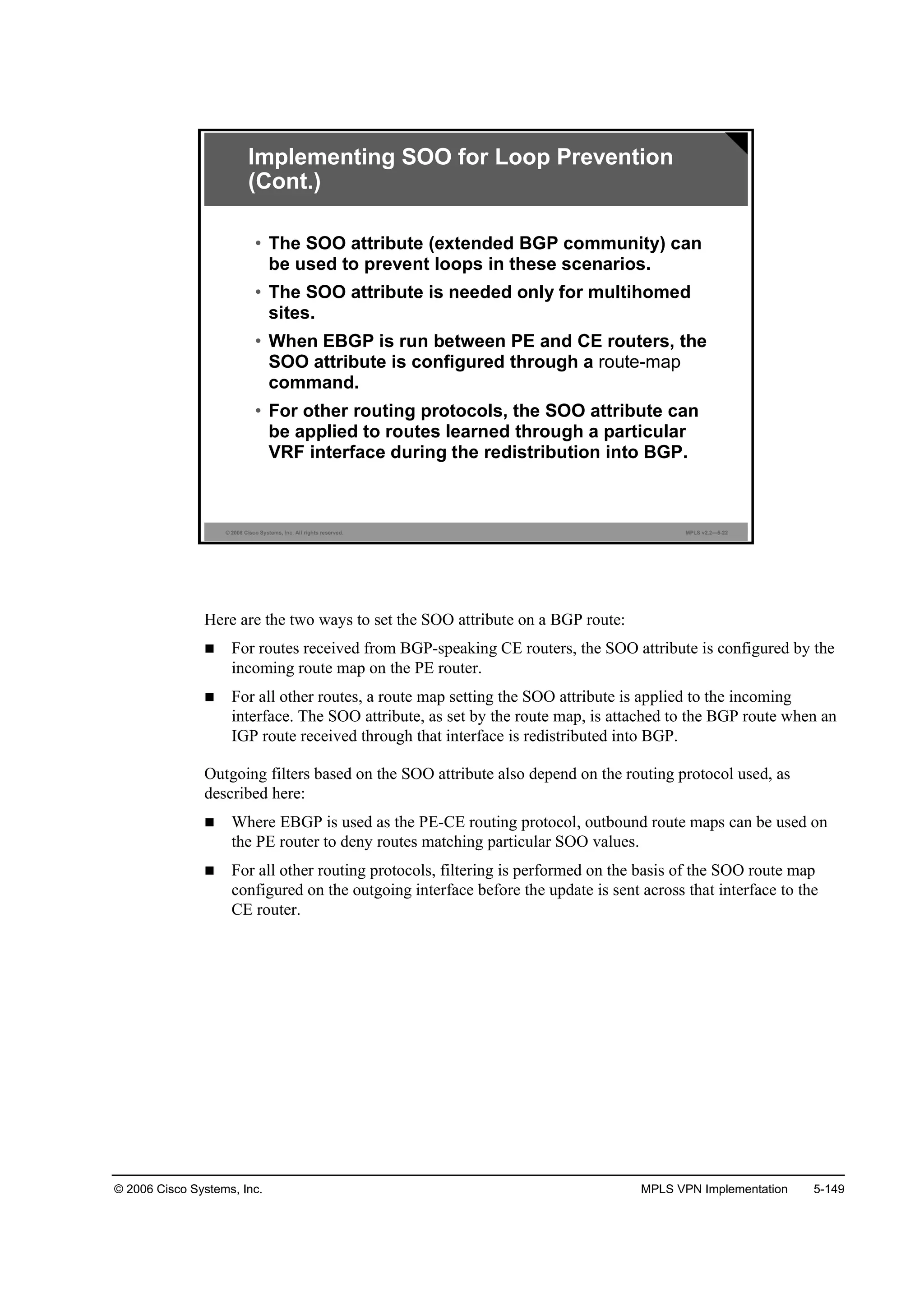
![5-150 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-23
®±«¬»ółż° ˛żł» °»®ł·¬ »Ż
łż¬˝¸ ˝±˛Ľ·¬·±˛
»¬ »¨¬˝±łł«˛·¬§ ±± »¨¬»˛Ľ»Ľó˝±łł«˛·¬§óŞż´«»
᫬»®ř˝±˛ş·ą÷ý
• Creates a route map that sets the SOO attribute
˛»·ą¸ľ±® ·°óżĽĽ®» ®±«¬»ółż° ˛żł» ·˛
᫬»®ř˝±˛ş·ąó®±«¬»®óżş÷ý
• Applies an inbound route map to the CE EBGP
neighbor
Inbound EBGP Update
Implementing SOO for Loop Prevention
(Cont.)
set extcommunity
To set the extended communities attribute, use the set extcommunity command in route map
configuration mode. To delete the entry, use the no form of this command.
set extcommunity {rt extended-community-value [additive] | soo extended-community-
value}
no set extcommunity
set extcommunity extcommunity-type community-number [additive]
no set extcommunity extcommunity-type community-number [additive]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-465-2048.jpg)
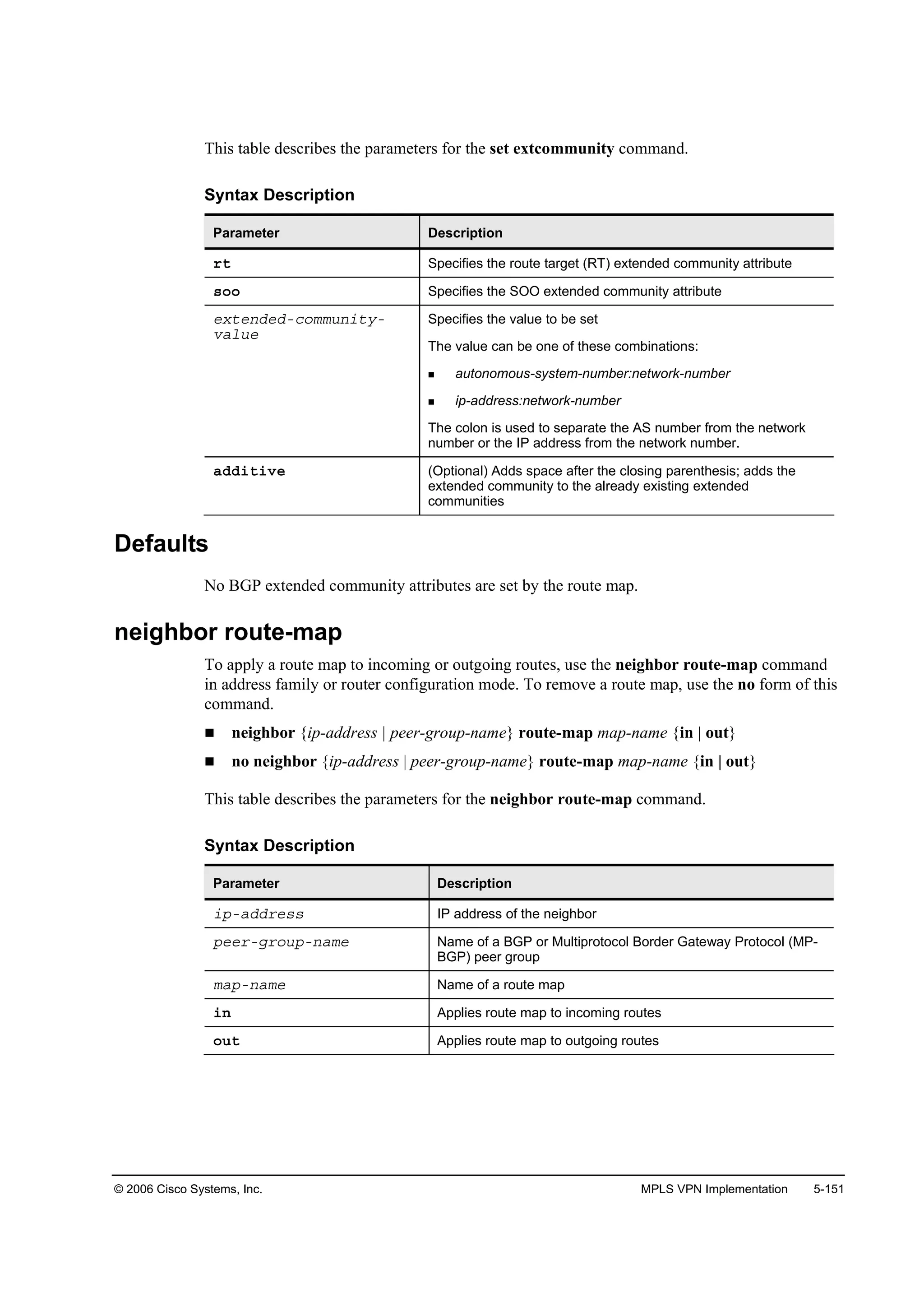
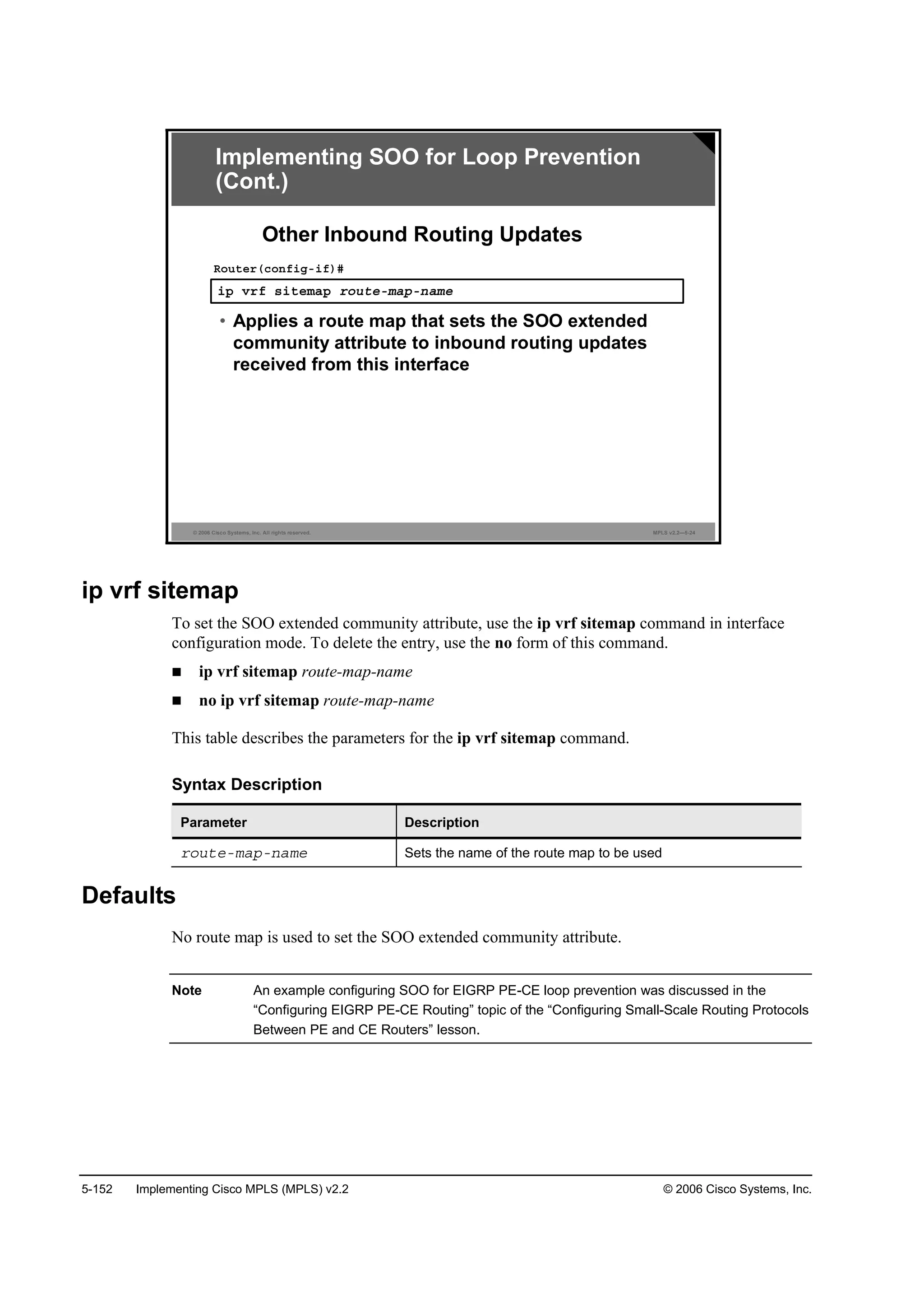
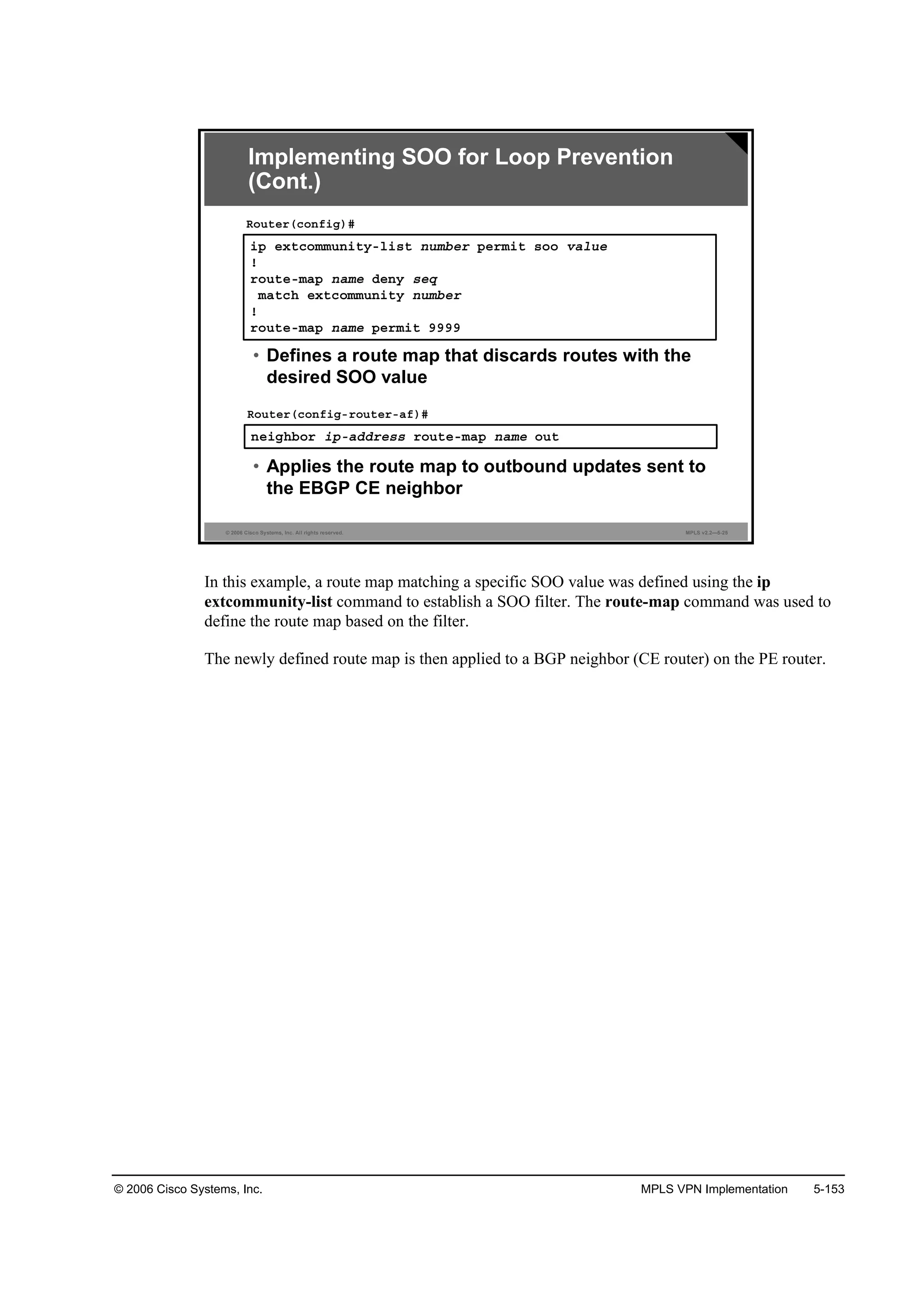
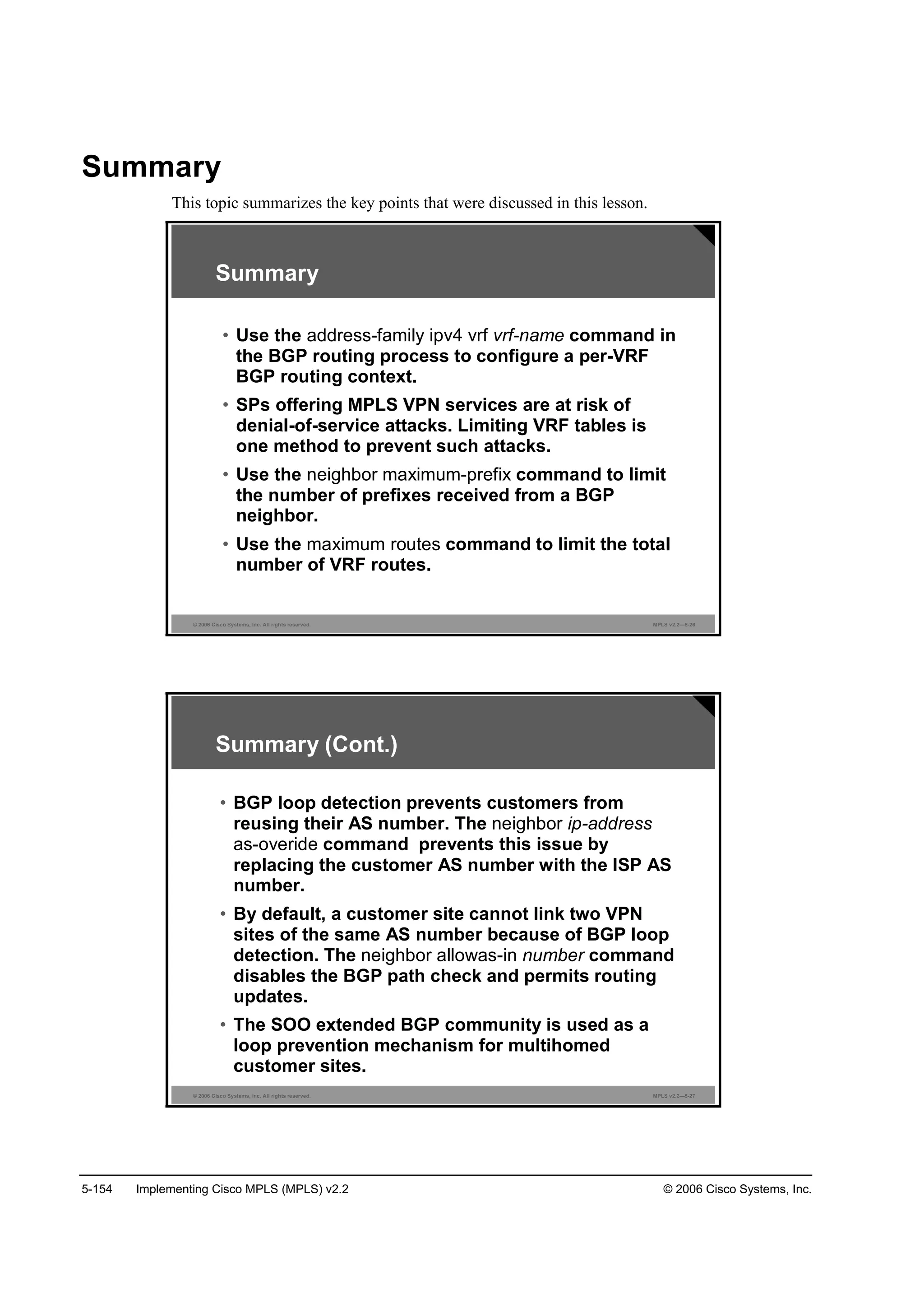
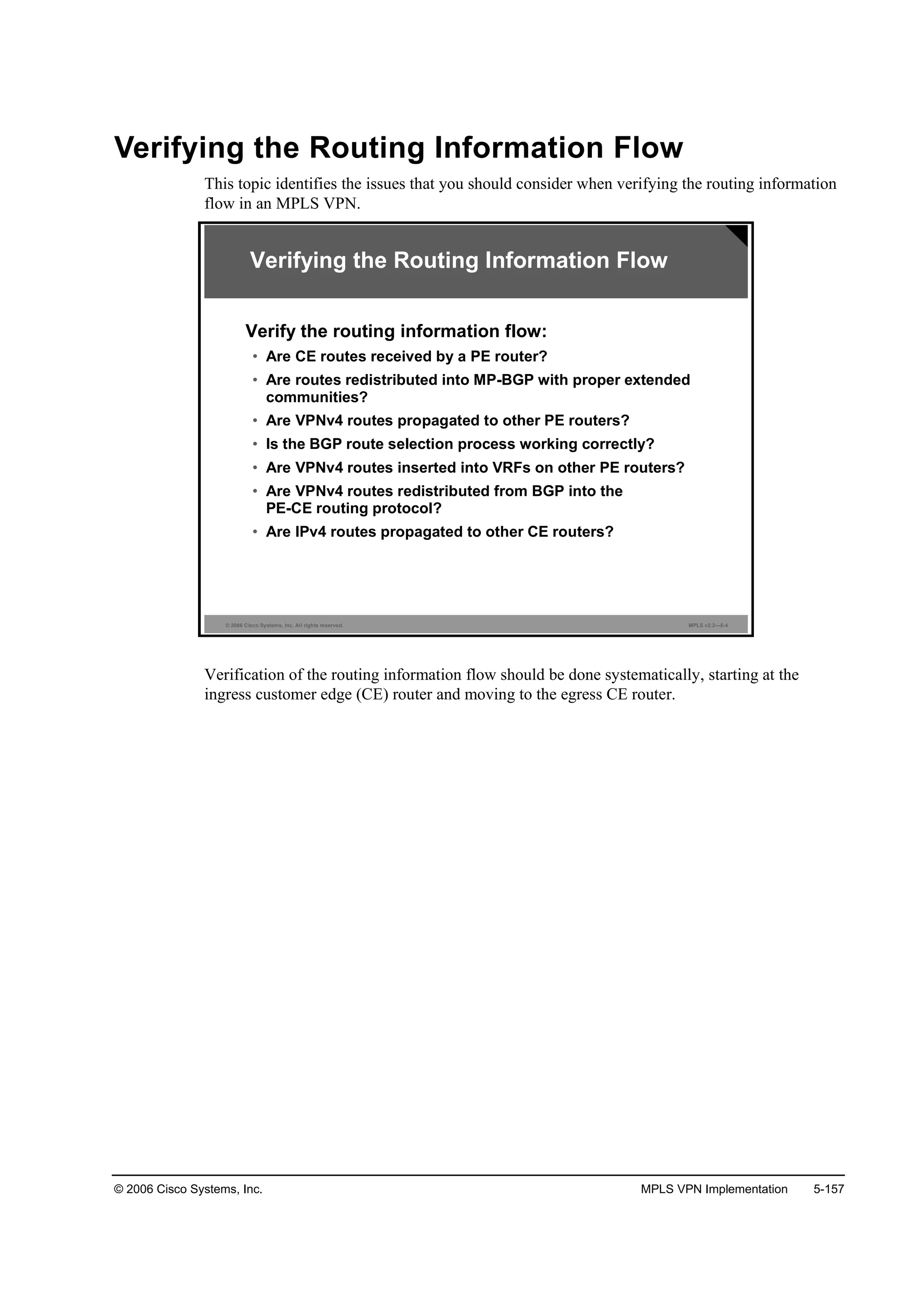
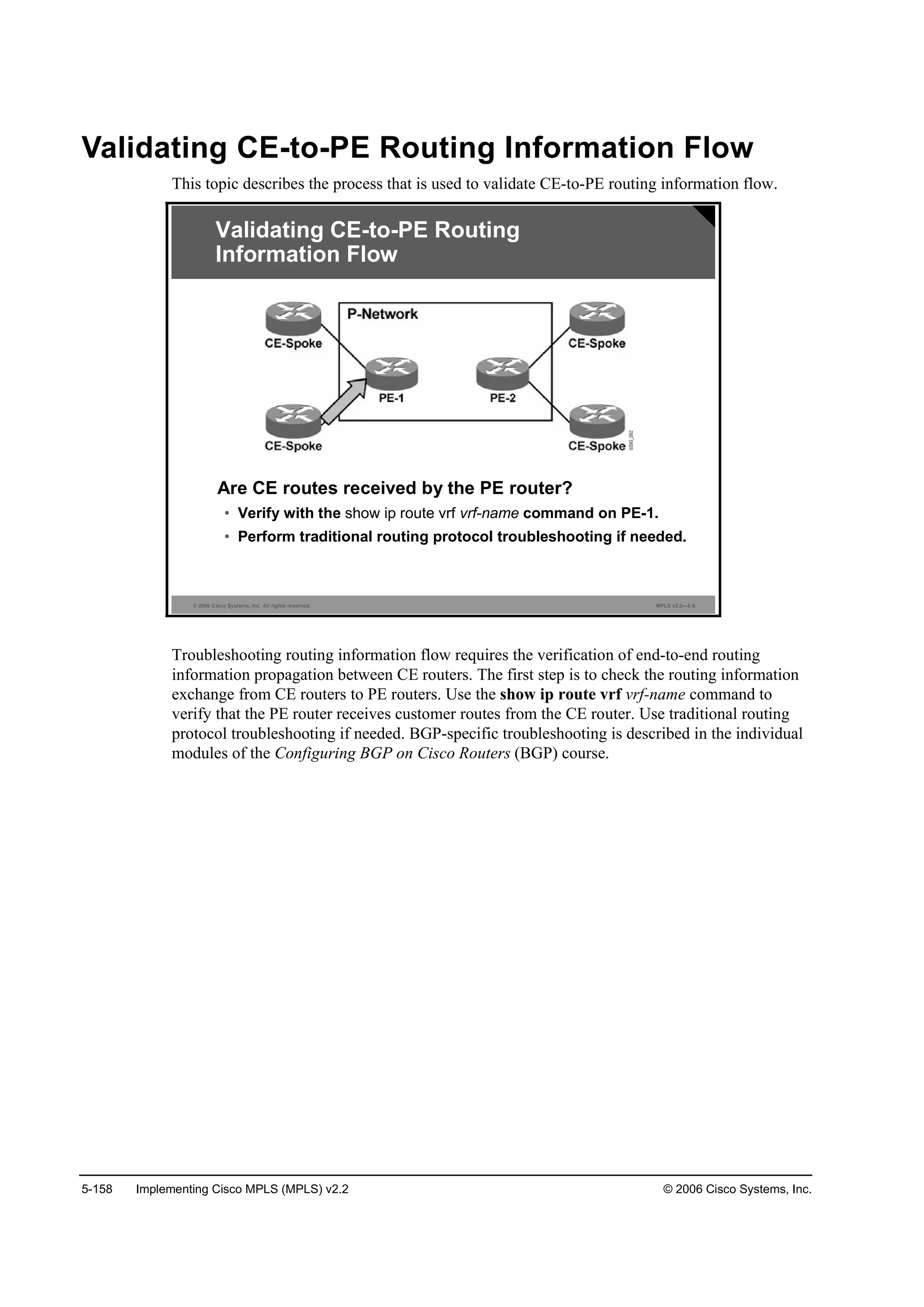
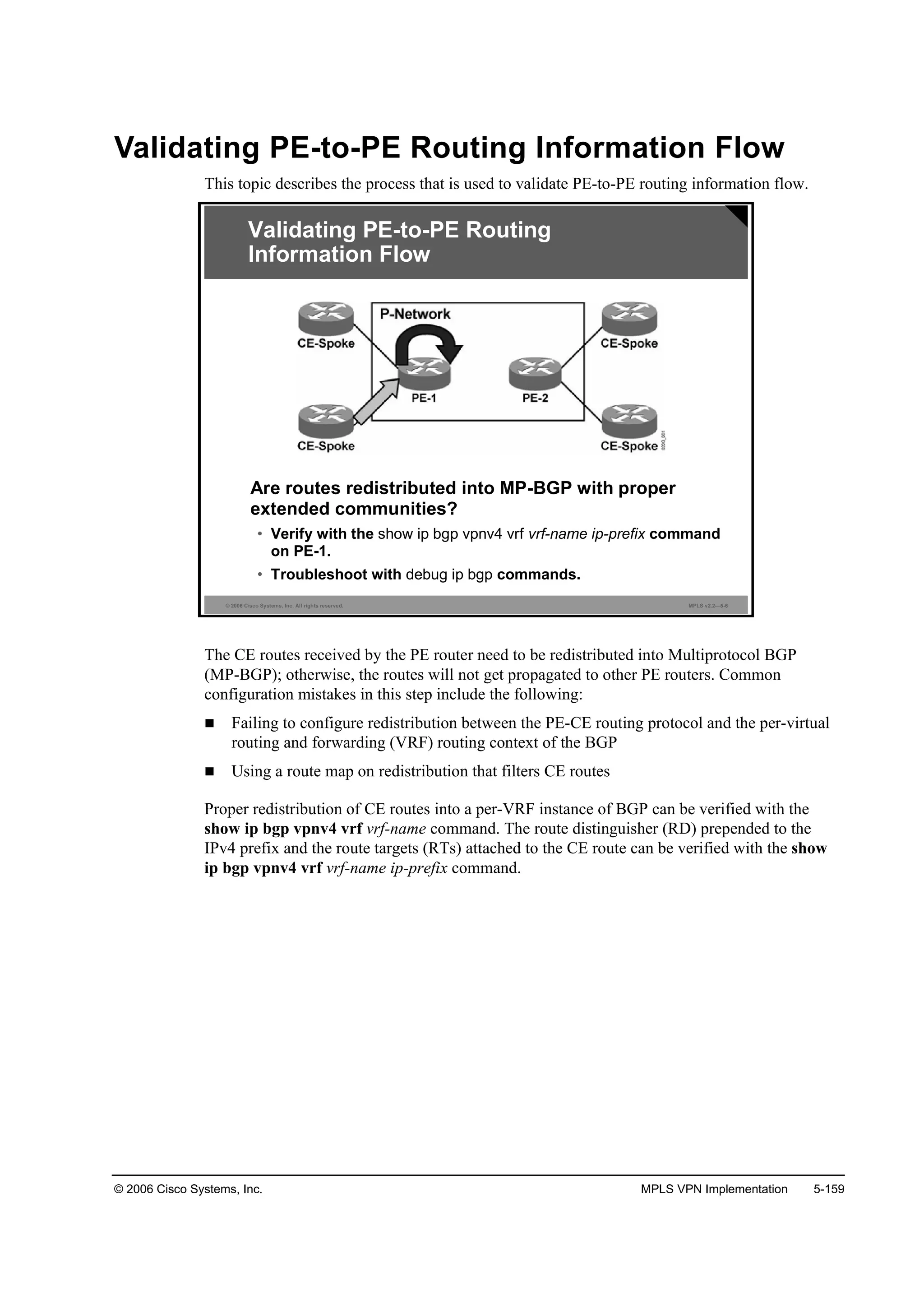
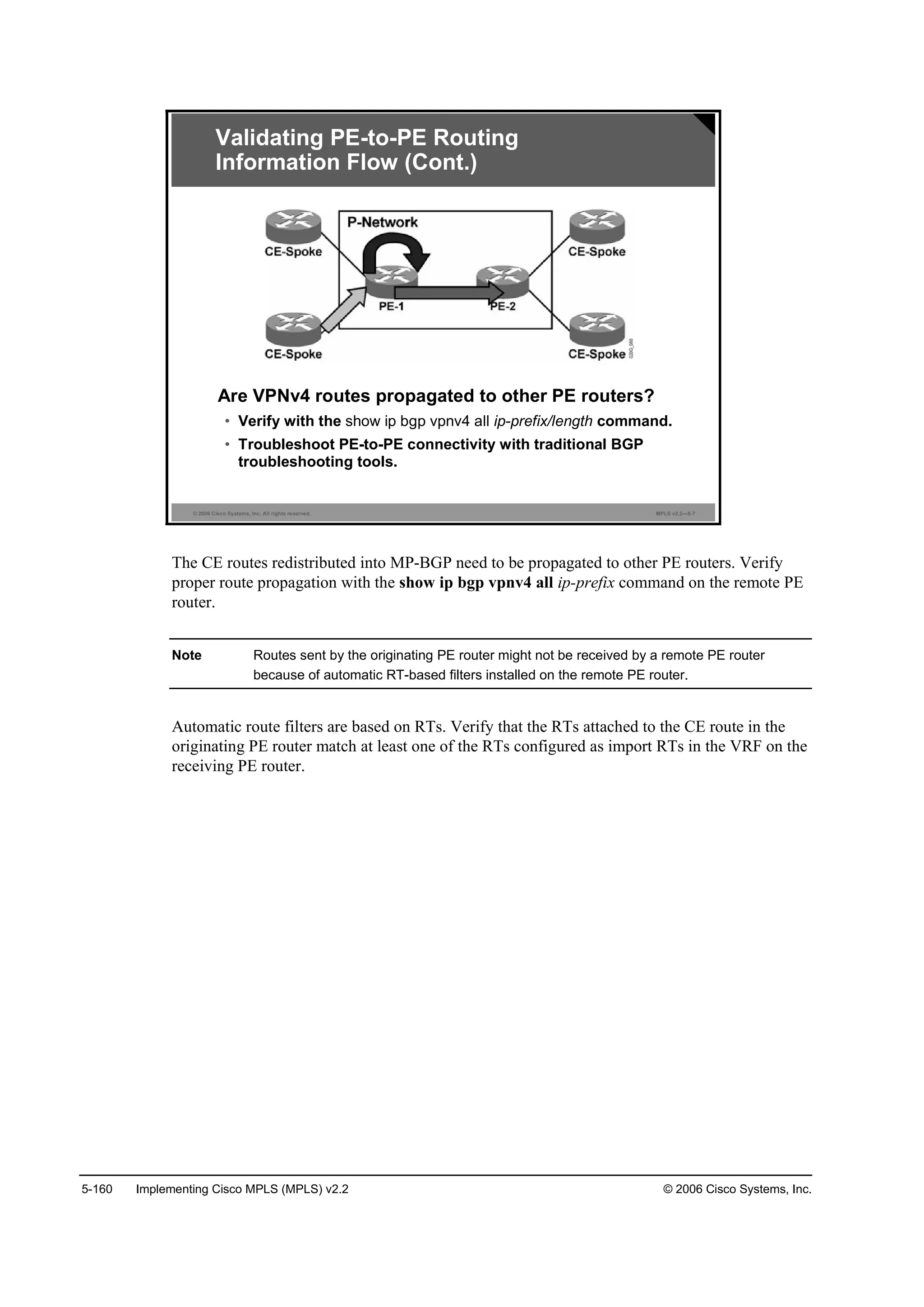
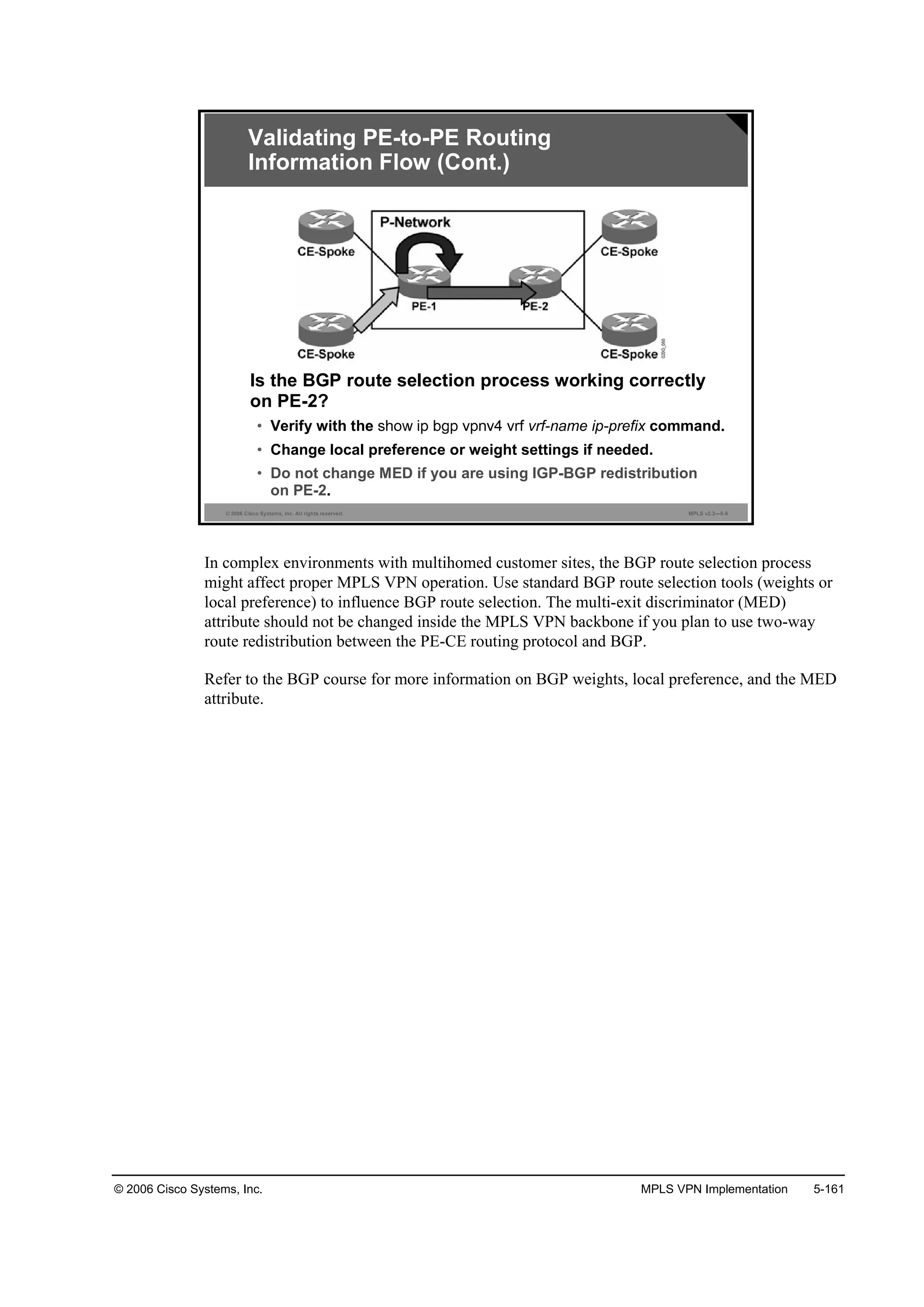
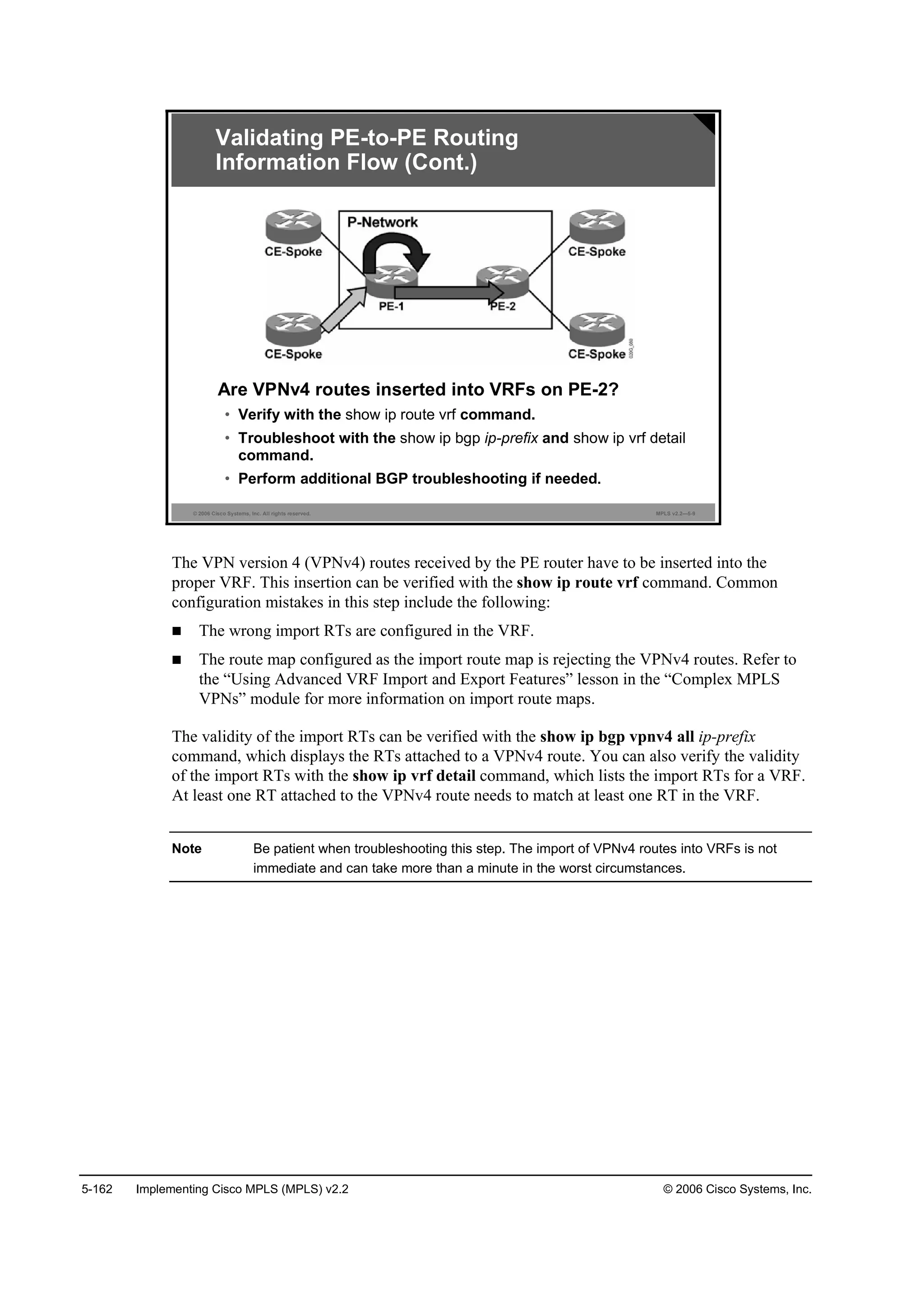

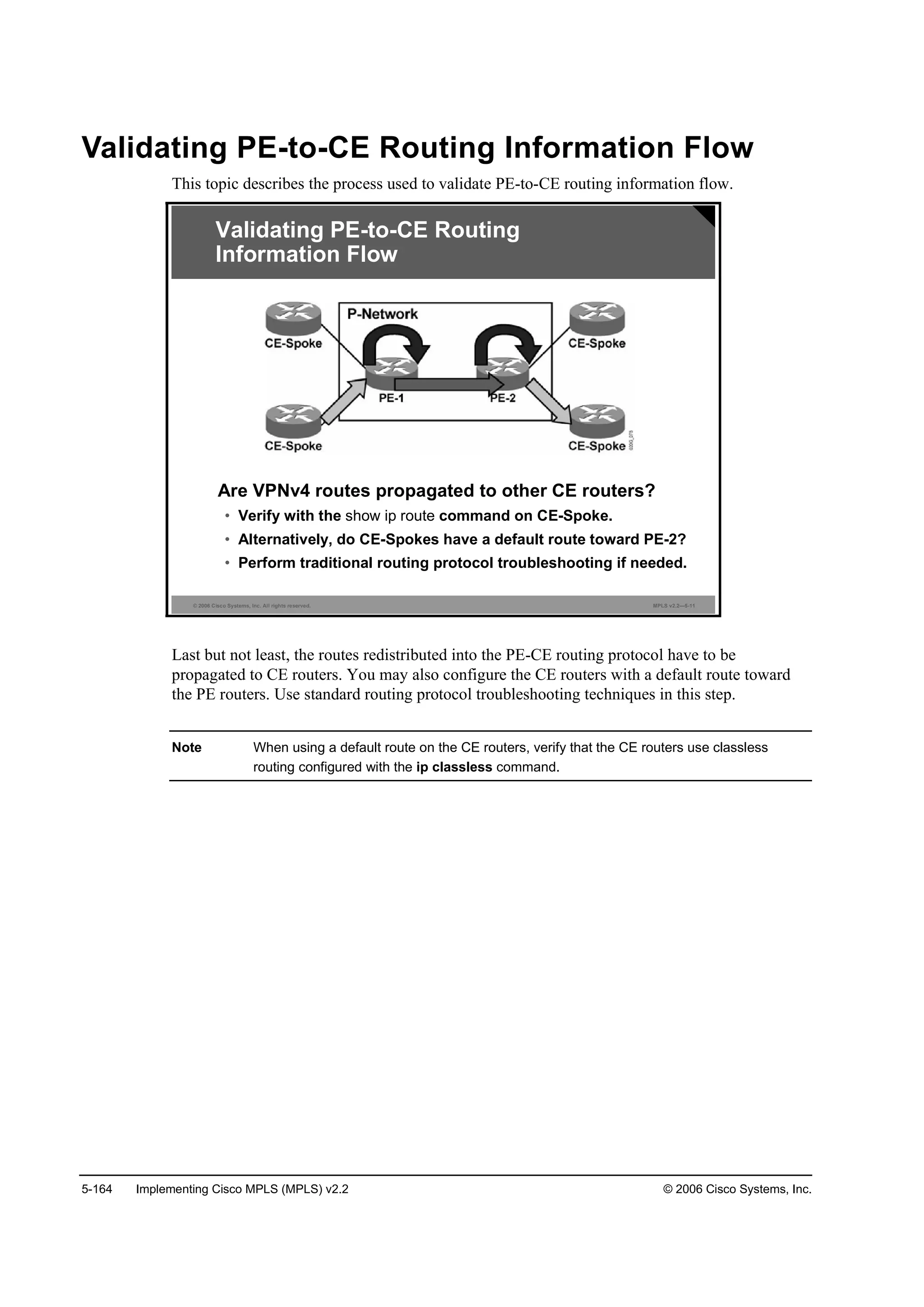
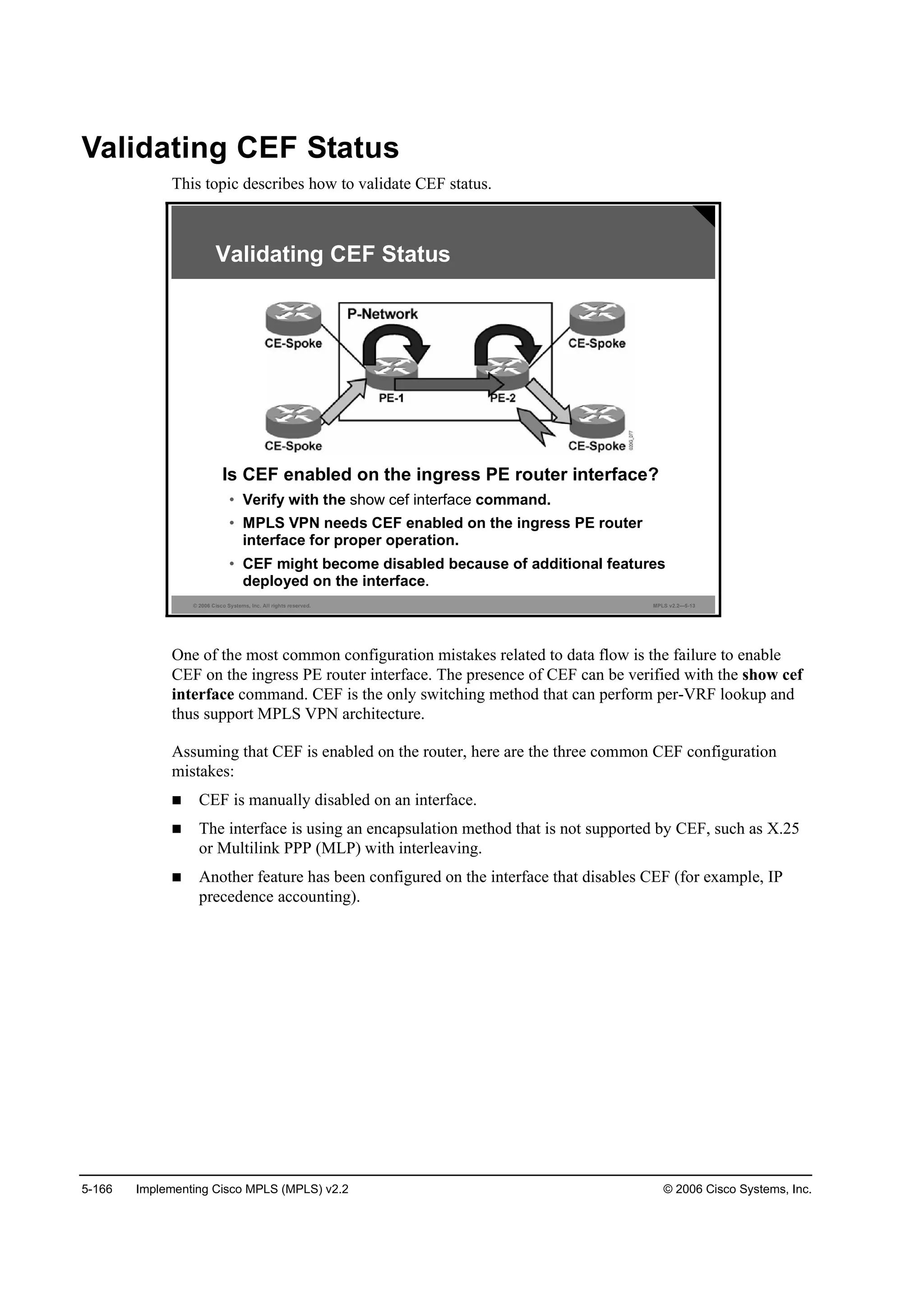
![© 2006 Cisco Systems, Inc. MPLS VPN Implementation 5-167
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—5-14
᫬»®ý¸±© ˝»ş ·˛¬»®şż˝» »®·ż´ ďńđňîđ
Í»®·ż´ďńđňîđ · «° ř·şÁ˛«łľ»® ďč÷
ײ¬»®˛»¬ żĽĽ®» · ďëđňďňíďňíéńíđ
×ÝÓĐ ®»Ľ·®»˝¬ ż®» ż´©ż§ »˛¬
Đ»® °ż˝µ»¬ ´±żĽľż´ż˛˝·˛ą · Ľ·żľ´»Ľ
×Đ «˛·˝ż¬ ÎĐÚ ˝¸»˝µ · Ľ·żľ´»Ľ
ײľ±«˛Ľ ż˝˝» ´·¬ · ˛±¬ »¬
Ń«¬ľ±«˛Ľ ż˝˝» ´·¬ · ˛±¬ »¬
×Đ °±´·˝§ ®±«¬·˛ą · Ľ·żľ´»Ľ
ײ¬»®şż˝» · łż®µ»Ľ ż °±·˛¬ ¬± °±·˛¬ ·˛¬»®şż˝»
Řż®Ľ©ż®» ·Ľľ · Í»®·ż´ďńđ
Úż¬ ©·¬˝¸·˛ą ¬§°» ëô ·˛¬»®şż˝» ¬§°» ęě
×Đ ÝŰÚ ©·¬˝¸·˛ą »˛żľ´»Ľ
×Đ ÝŰÚ ĘĐŇ Úż¬ ©·¬˝¸·˛ą ¬«®ľ± Ş»˝¬±®
ĘĐŇ Ú±®©ż®Ľ·˛ą ¬żľ´» ţÍ·¬»ßîţ
ײ°«¬ şż¬ ş´żą đ¨ďđđđô Ń«¬°«¬ şż¬ ş´żą đ¨đ
·ş·˛Ľ»¨ íří÷
Í´±¬ ď Í´±¬ «˛·¬ đ ĘÝ óď
Ě®ż˛ł·¬ ´·ł·¬ ż˝˝«ł«´ż¬±® đ¨đ řđ¨đ÷
×Đ ÓĚË ďëđđ
Validating CEF Status:
show cef interface
show cef interface
To display detailed CEF information for all interfaces, use the show cef interface command in
EXEC mode.
show cef interface type number [statistics][detail].
This table describes the parameters for the show cef interface command.
Syntax Description
Parameter Description
¬§°» ˛«łľ»® Displays interface type and number for CEF information
¬ż¬·¬·˝ (Optional) Displays switching statistics for the line card
Ľ»¬ż·´ (Optional) Displays detailed CEF information for the specified
interface type and number
Usage Guidelines
This command is available on routers that have route processor (RP) cards and line cards.
The detail keyword displays more CEF information for the specified interface. You can use
this command to show the CEF state on an individual interface.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-482-2048.jpg)
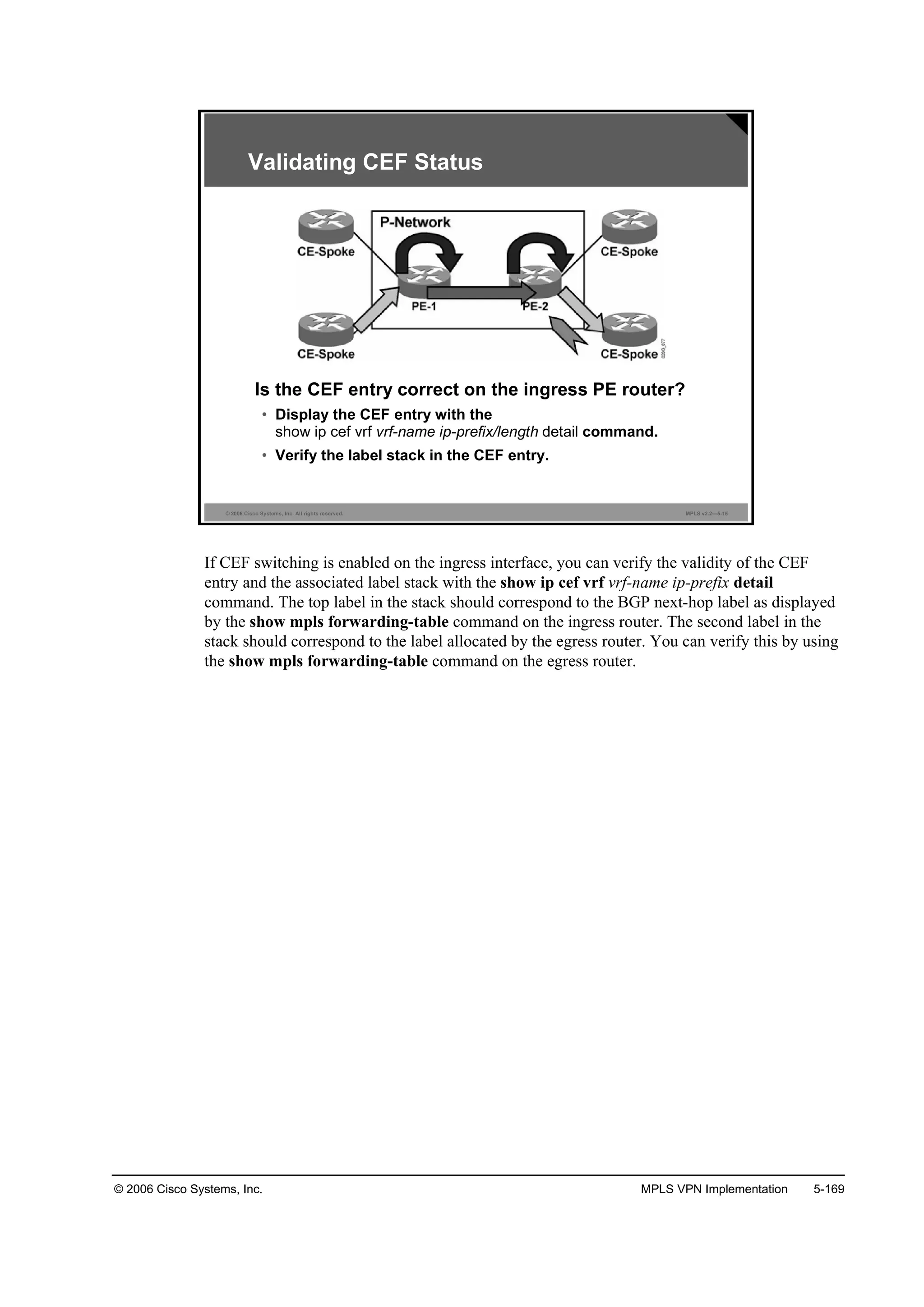
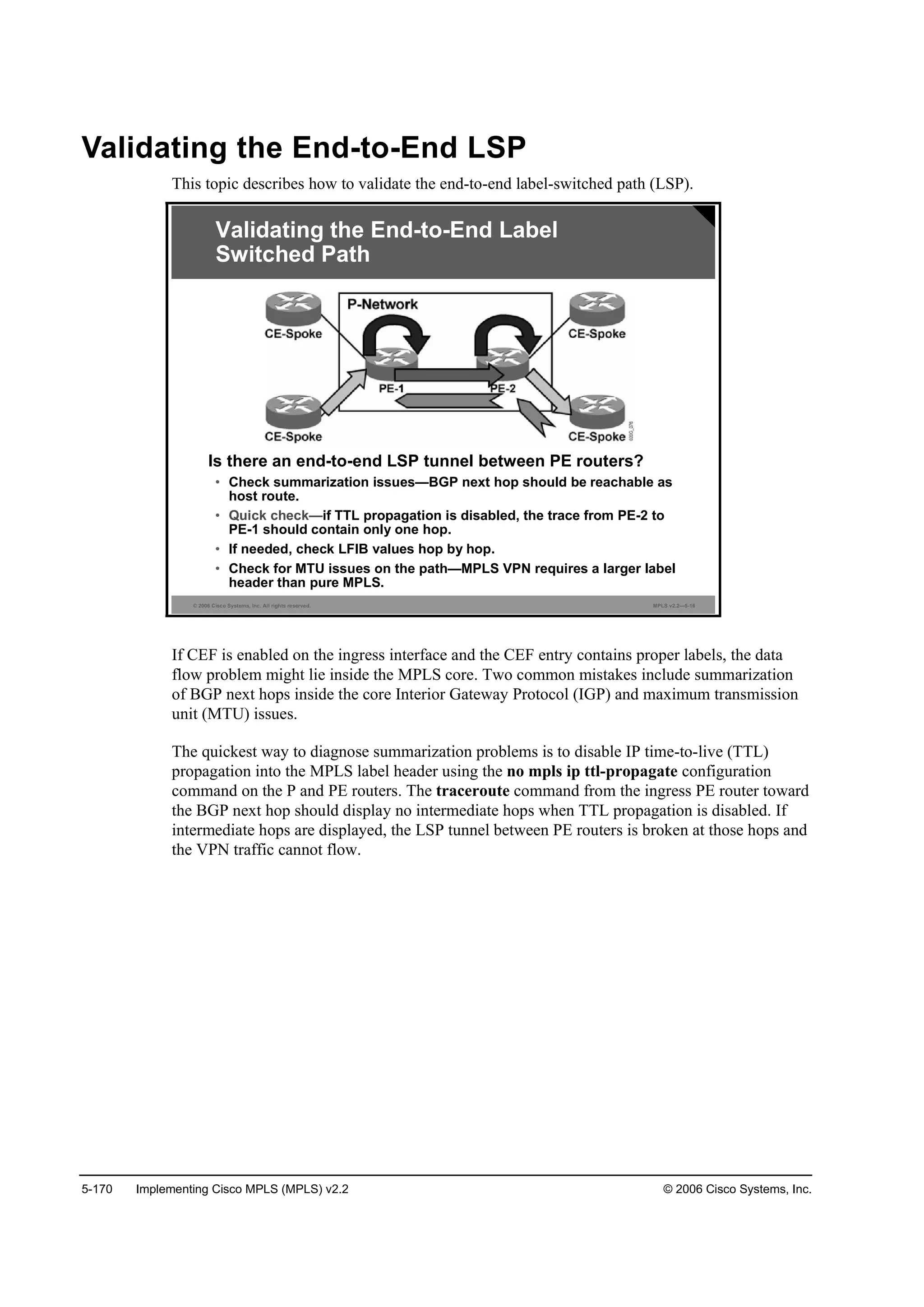

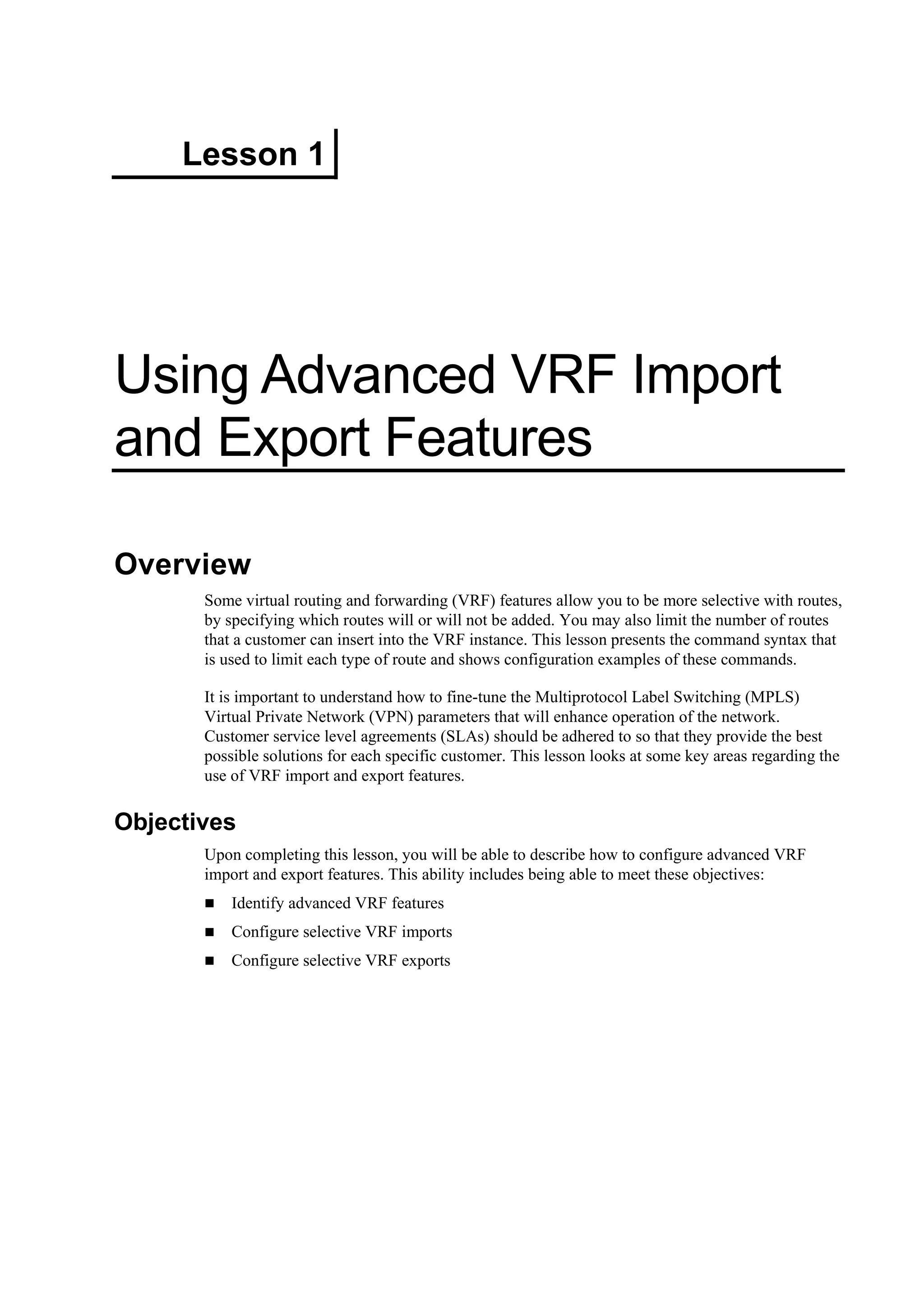
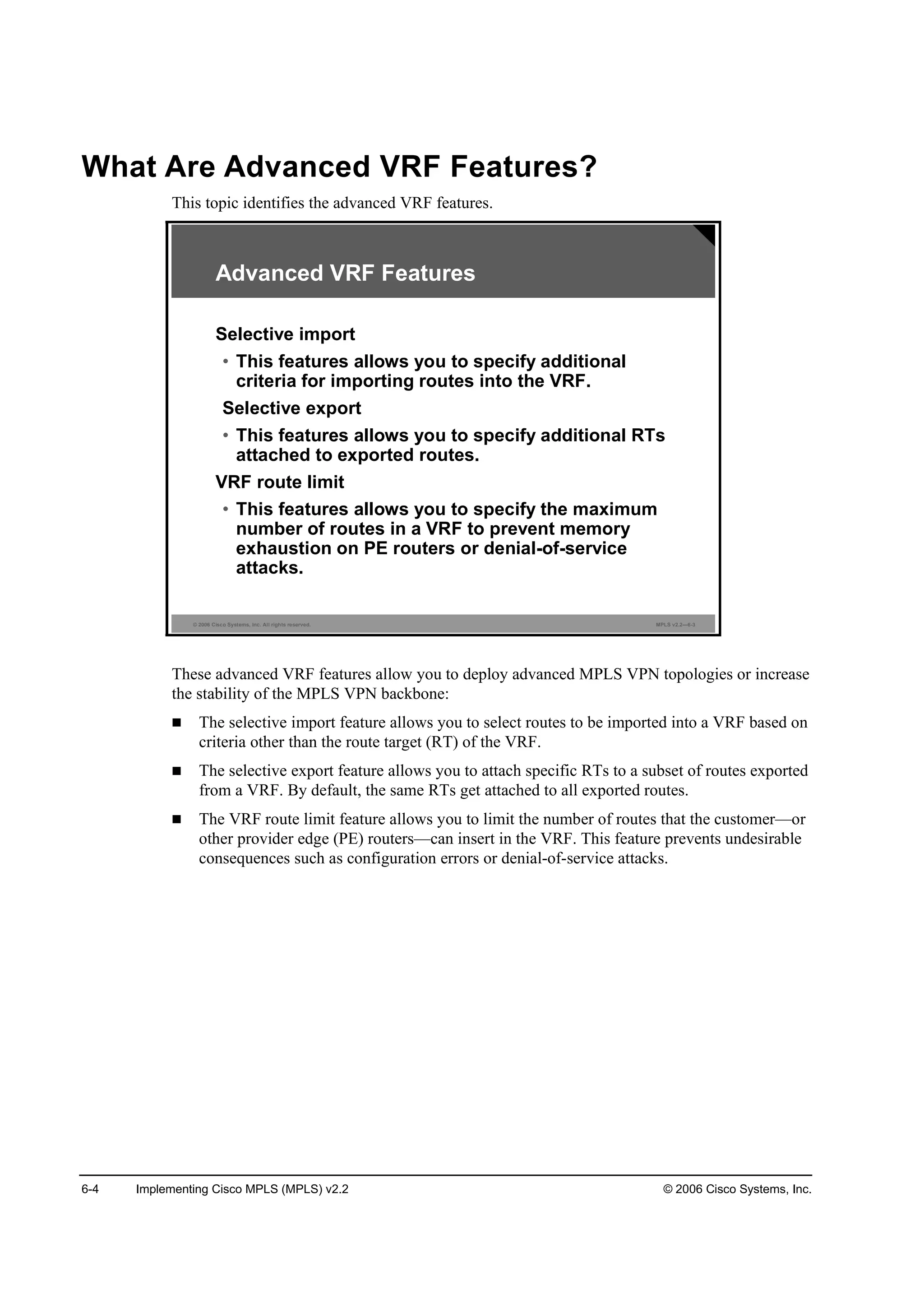
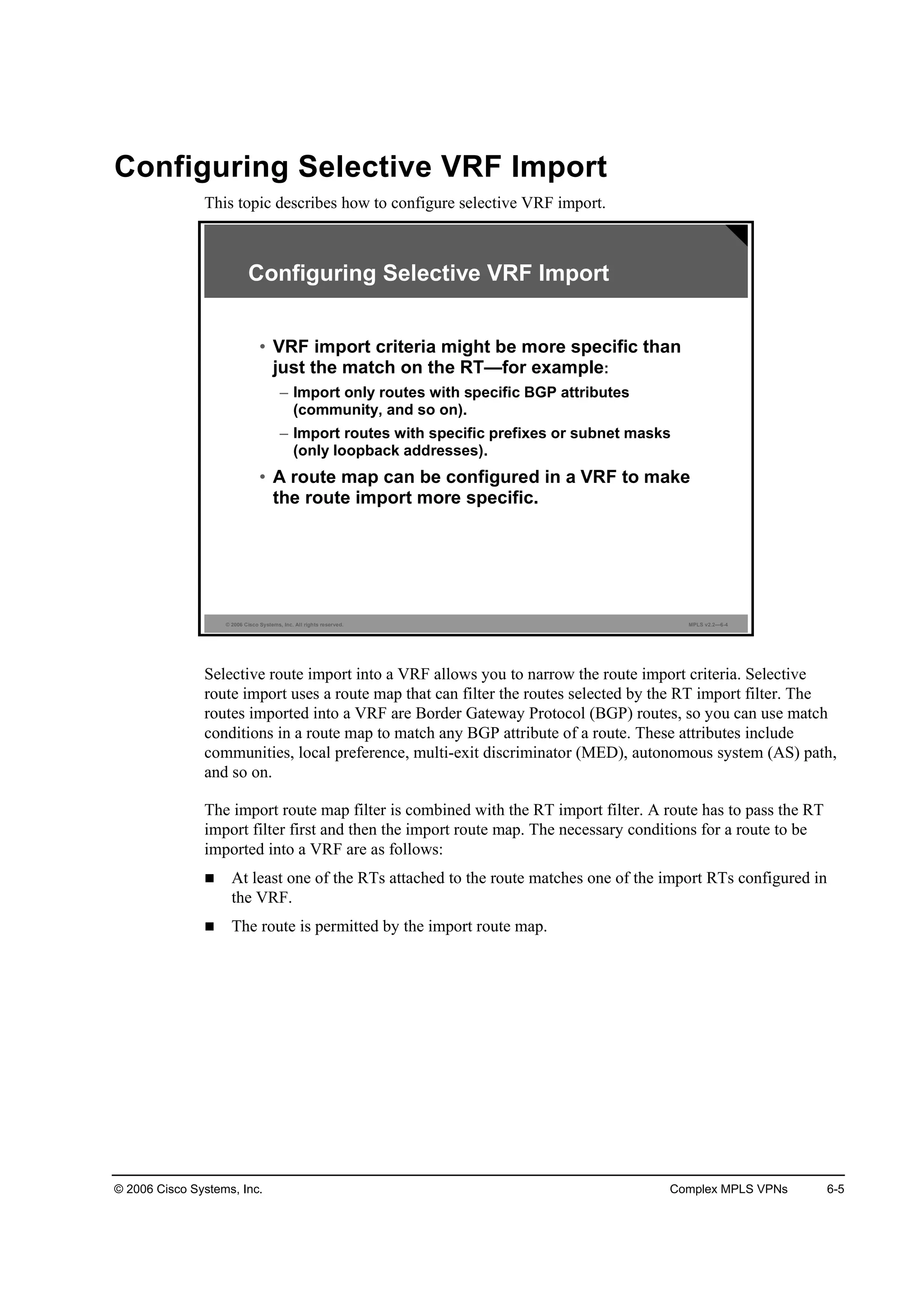
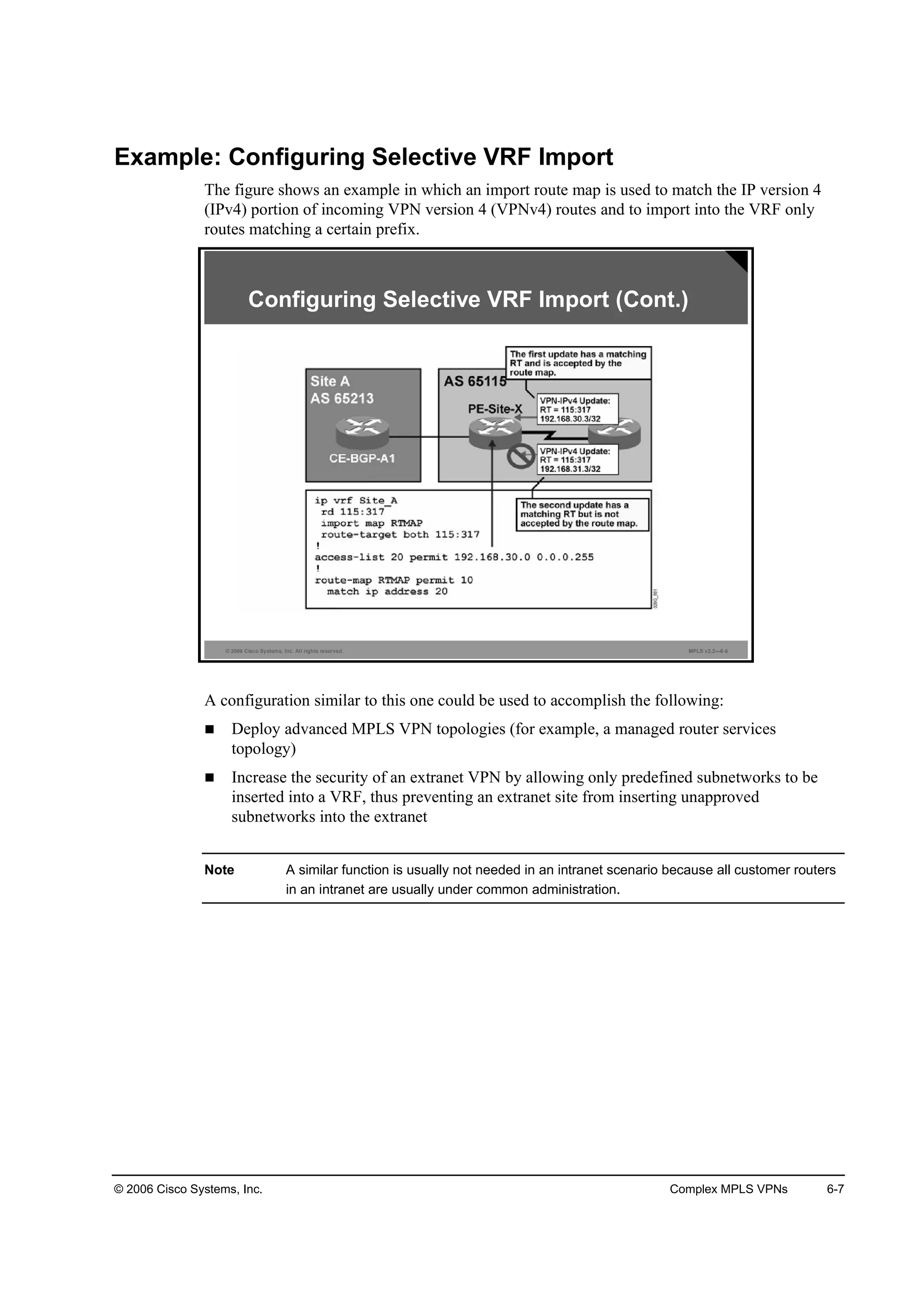
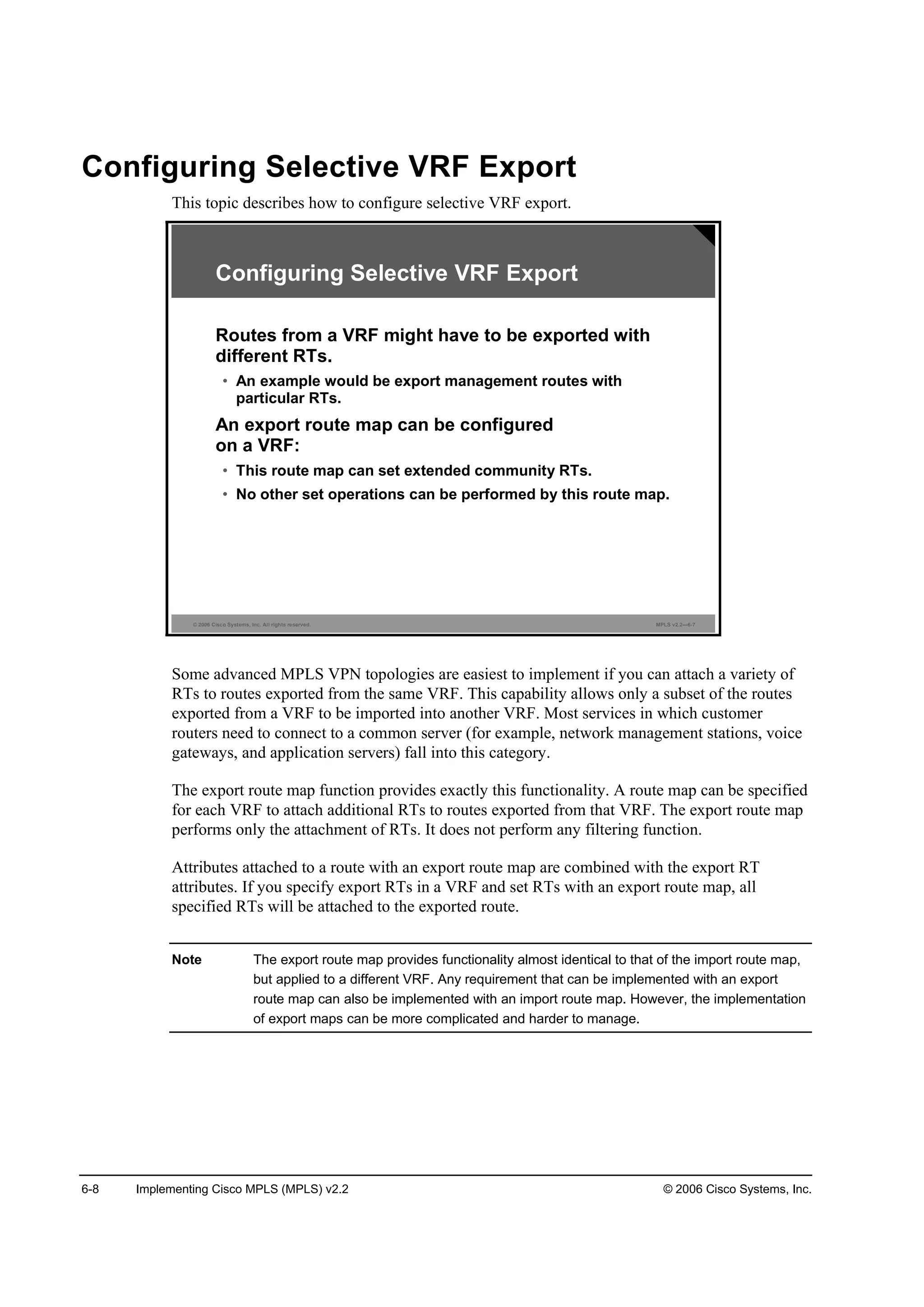
![© 2006 Cisco Systems, Inc. Complex MPLS VPNs 6-9
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—6-8
®±«¬»ółż° ˛żł» °»®ł·¬ »Ż
łż¬˝¸ ˝±˛Ľ·¬·±˛
»¬ »¨¬˝±łł«˛·¬§ ®¬ »¨¬»˛Ľ»Ľó˝±łł«˛·¬§óŞż´«» ĹżĽĽ·¬·Ş»Ă
᫬»®ř˝±˛ş·ą÷ý
• This command creates a route map that matches
routes based on any route map conditions and
sets RTs.
Configuring Selective VRF Export (Cont.)
set extcommunity
To set the BGP extended communities attribute, use the set extcommunity command in route-
map configuration mode. To delete the entry, use the no form of this command.
set extcommunity {rt extended-community-value [additive] | soo extended-community-
value}
no set extcommunity {rt extended-community-value [additive] | soo extended-community-
value}
This table describes the parameters for the set extcommunity command.
Syntax Description
Parameter Description
®¬ Specifies the RT extended community attribute.
±± Specifies the SOO extended community attribute.
»¨¬»˛Ľ»Ľó˝±łł«˛·¬§ó
Şż´«»
Specifies the value to be set. The value can be one of the
following combinations:
autonomous-system-number: network-number
ip-address: network-number
The colon is used to separate the AS number from the network
number or the IP address from the network number.
żĽĽ·¬·Ş» (Optional) Adds an RT to the existing RT list without replacing
any RTs.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-510-2048.jpg)
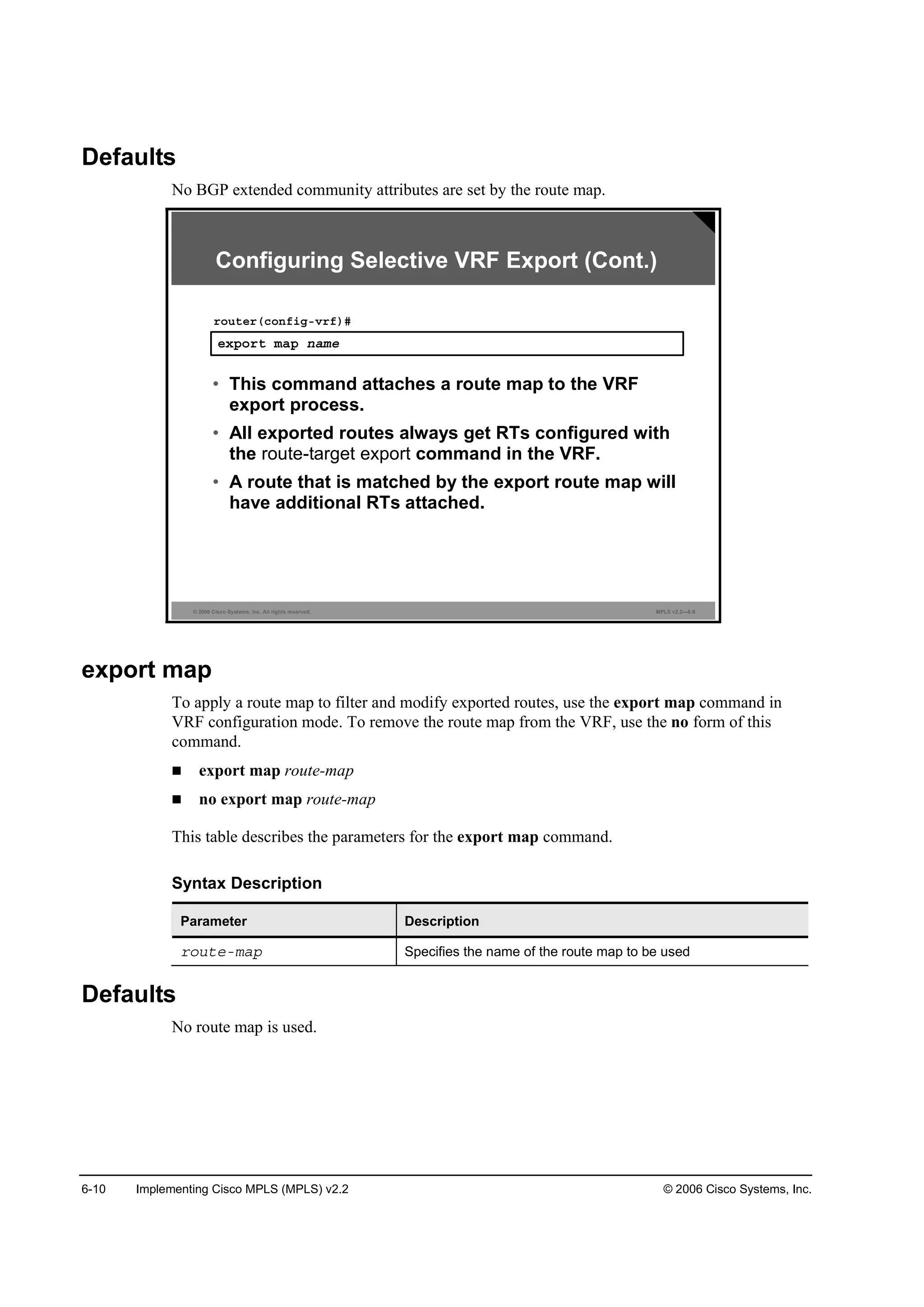
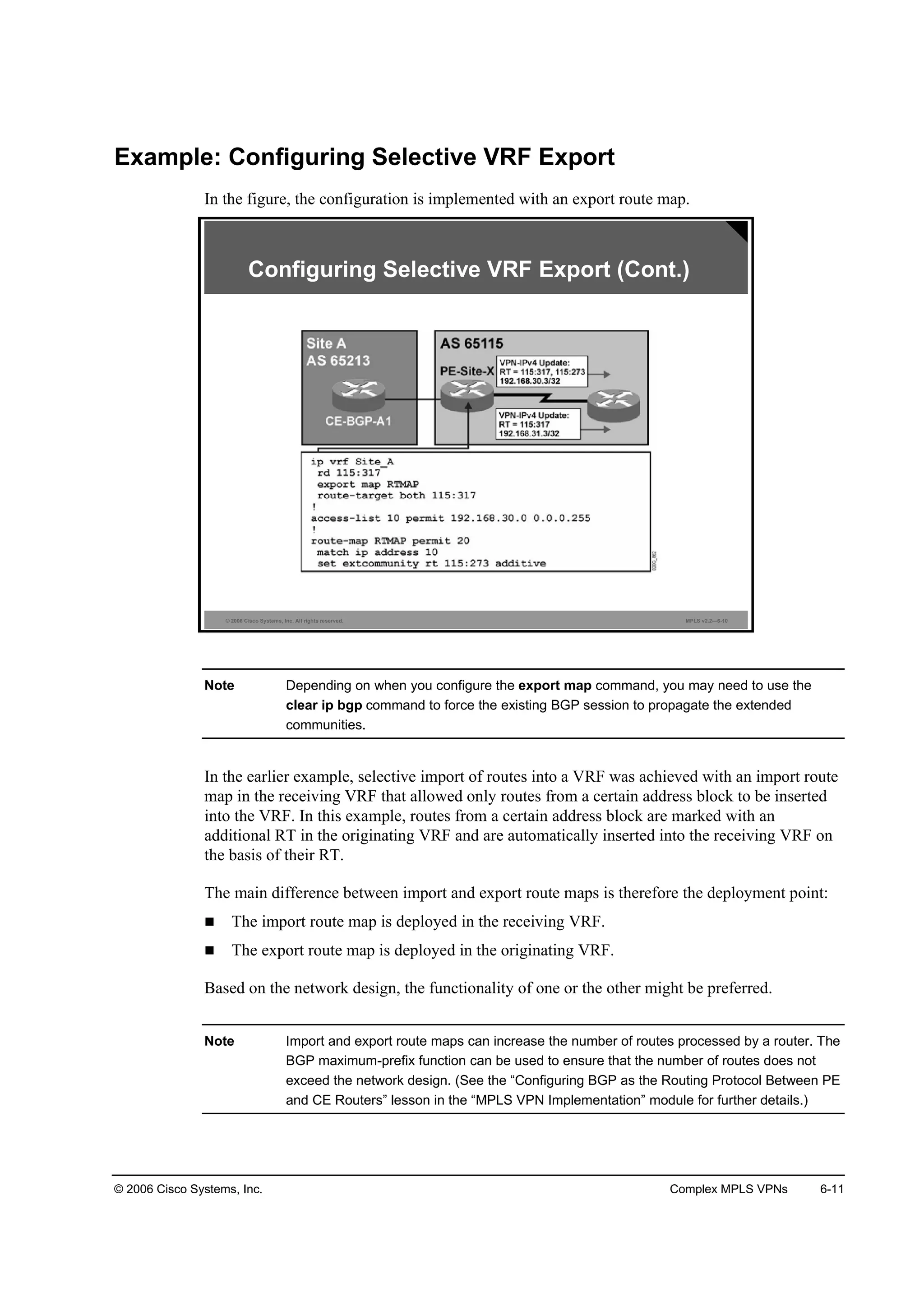
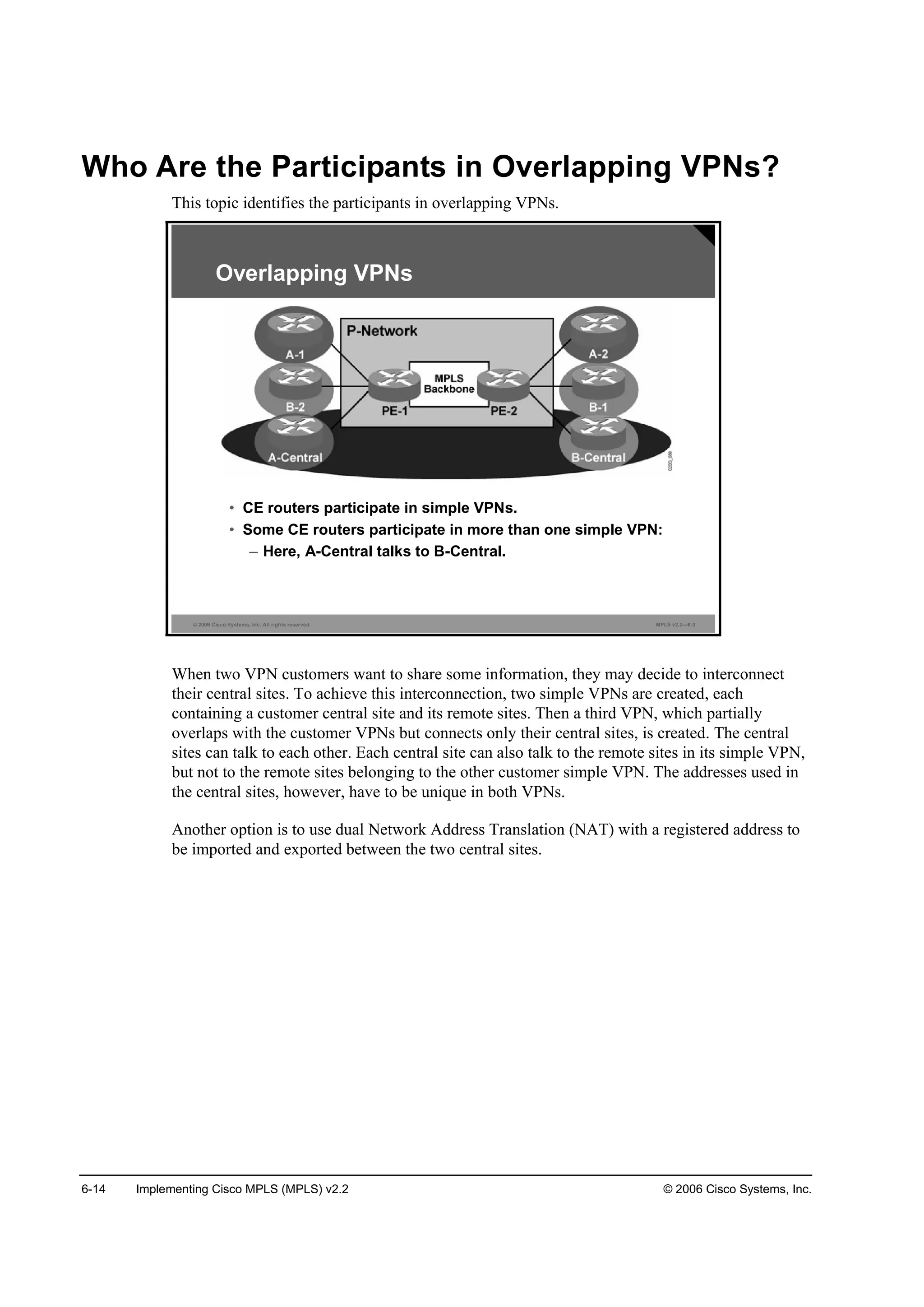
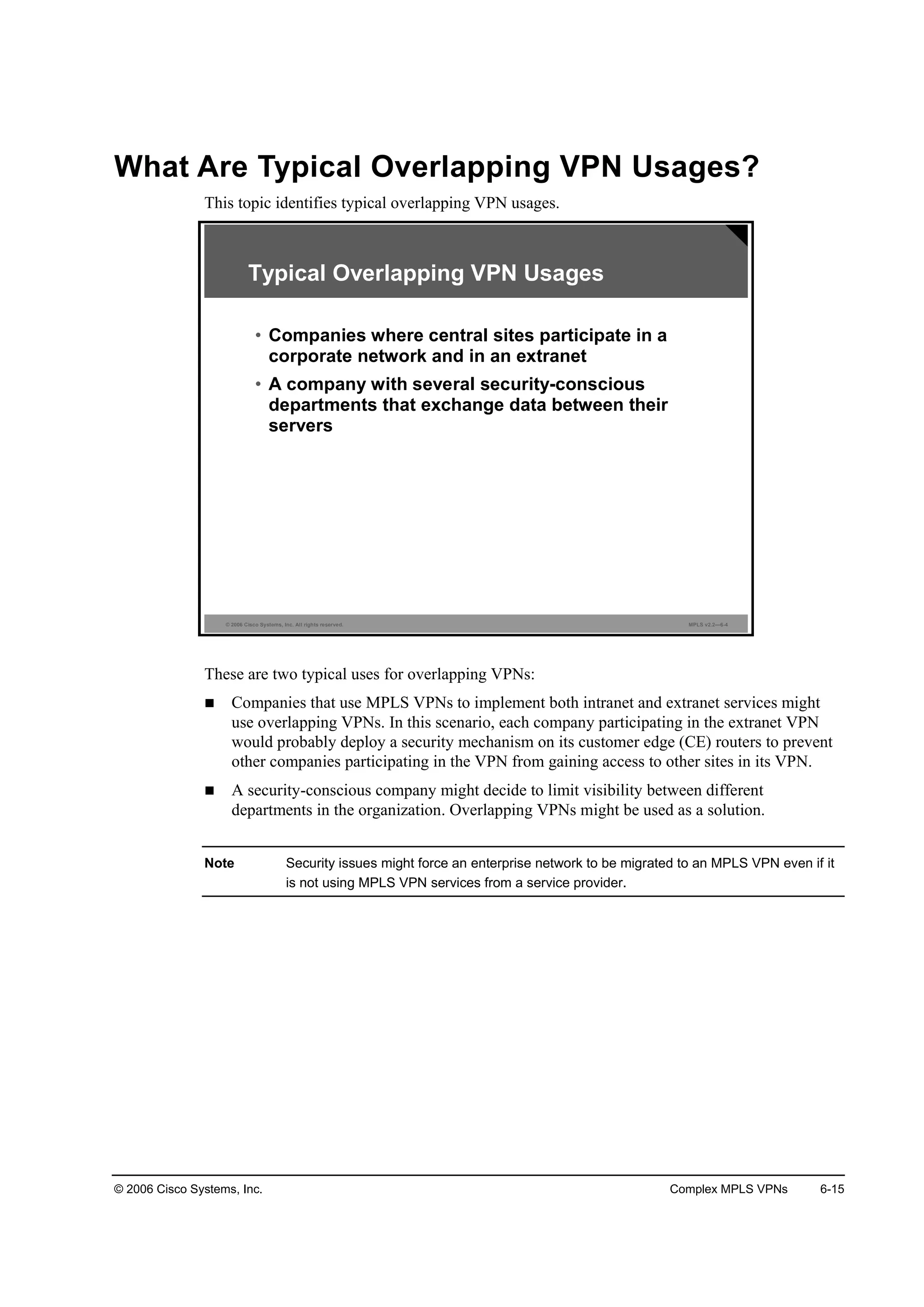
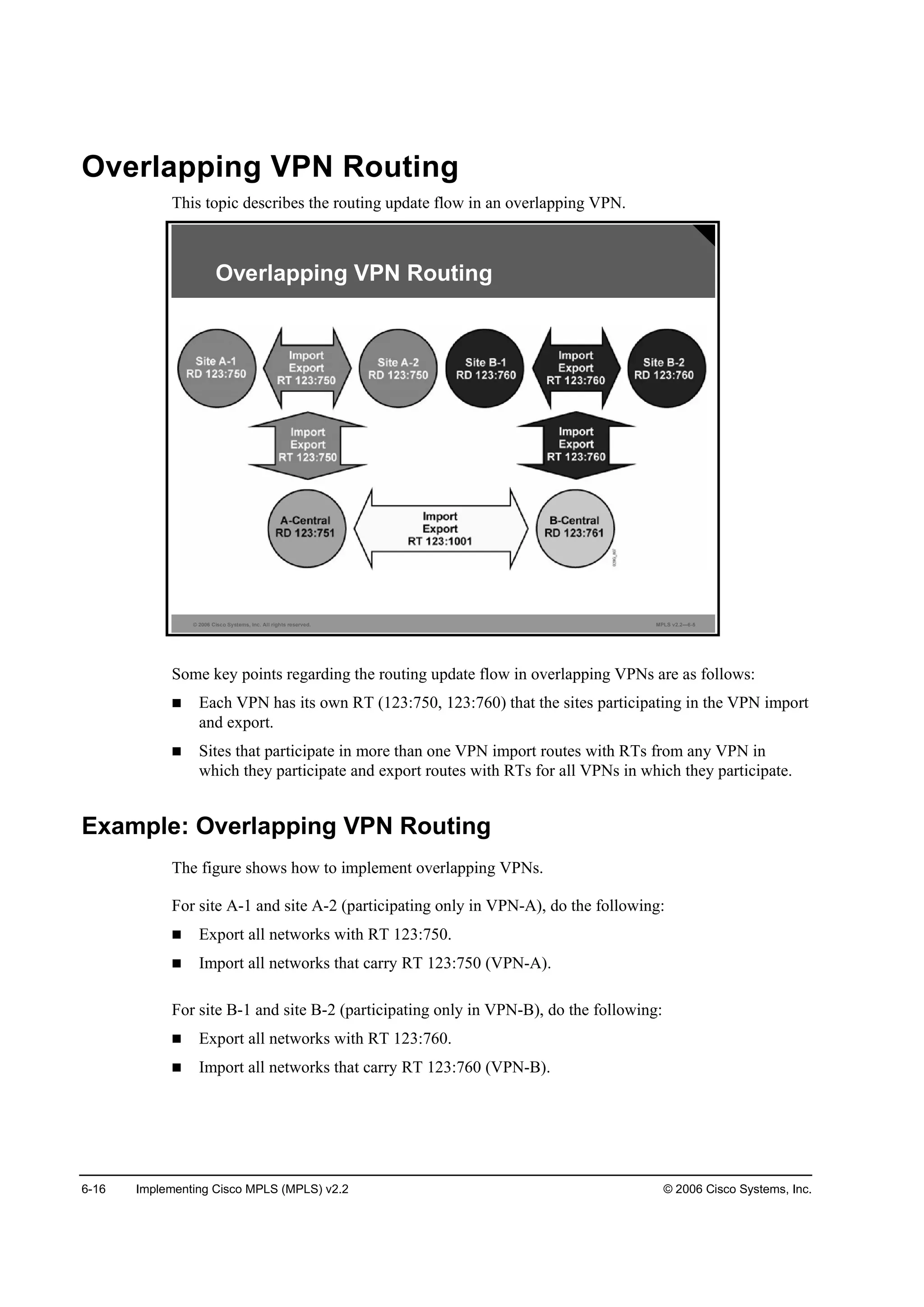
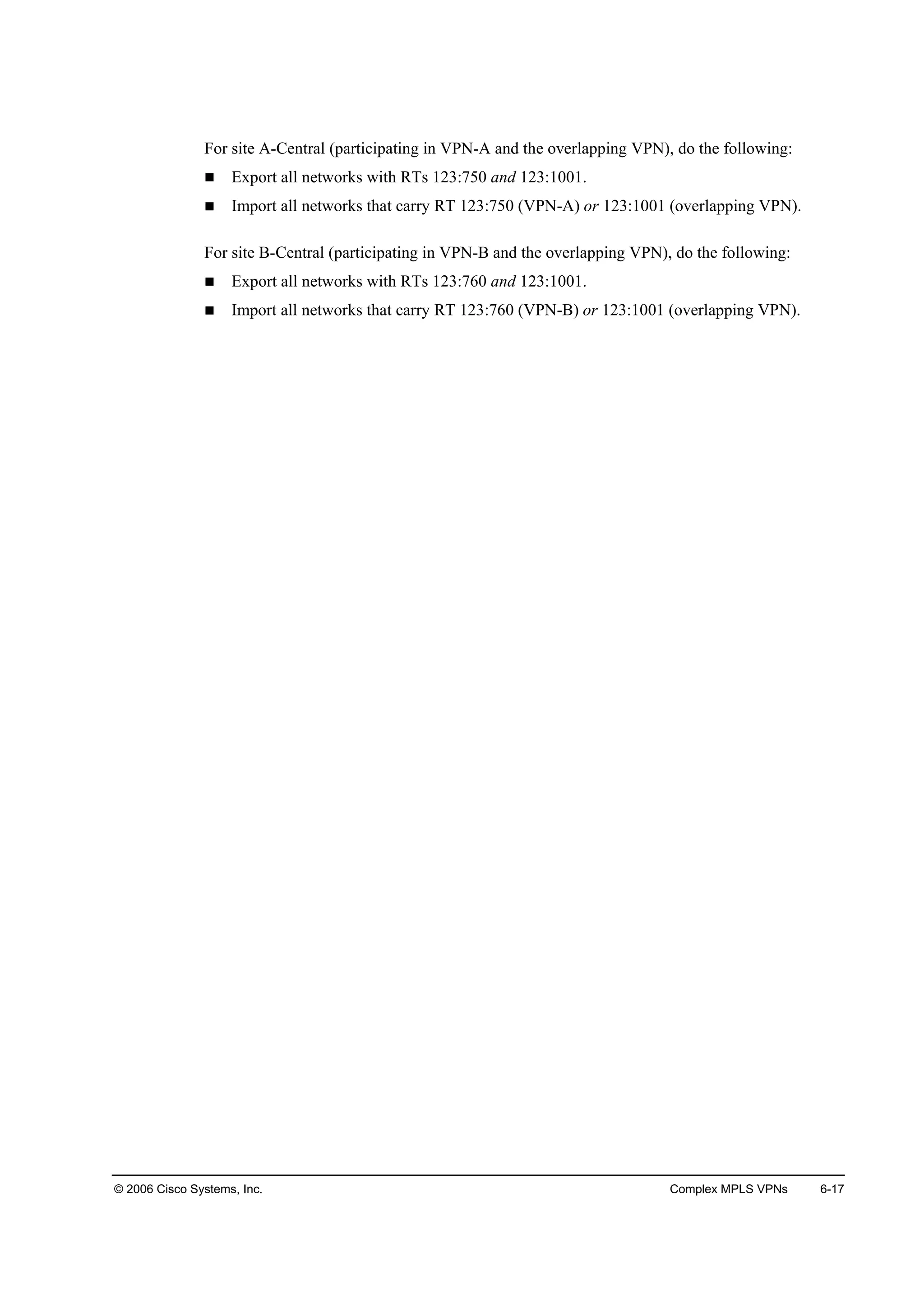
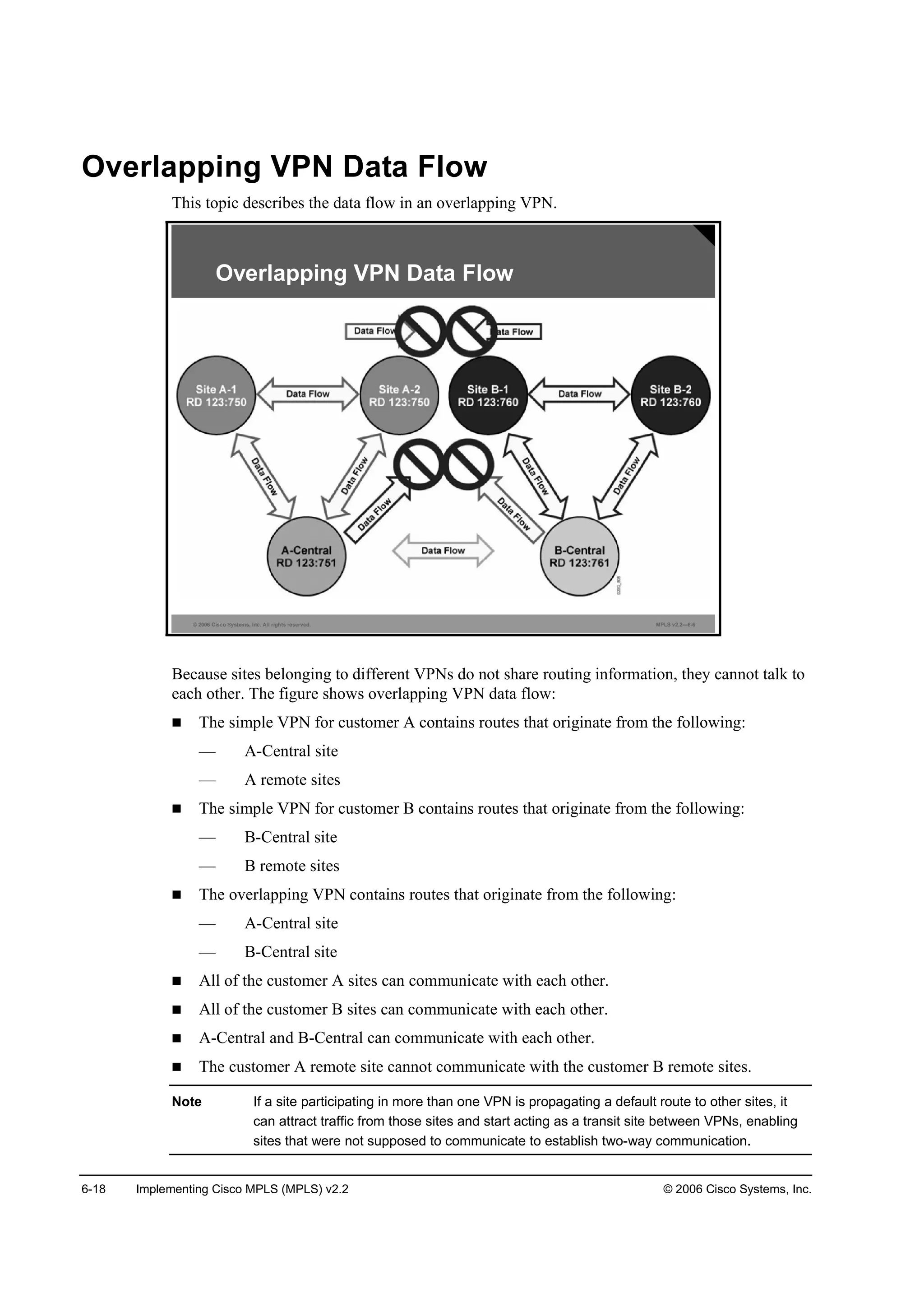
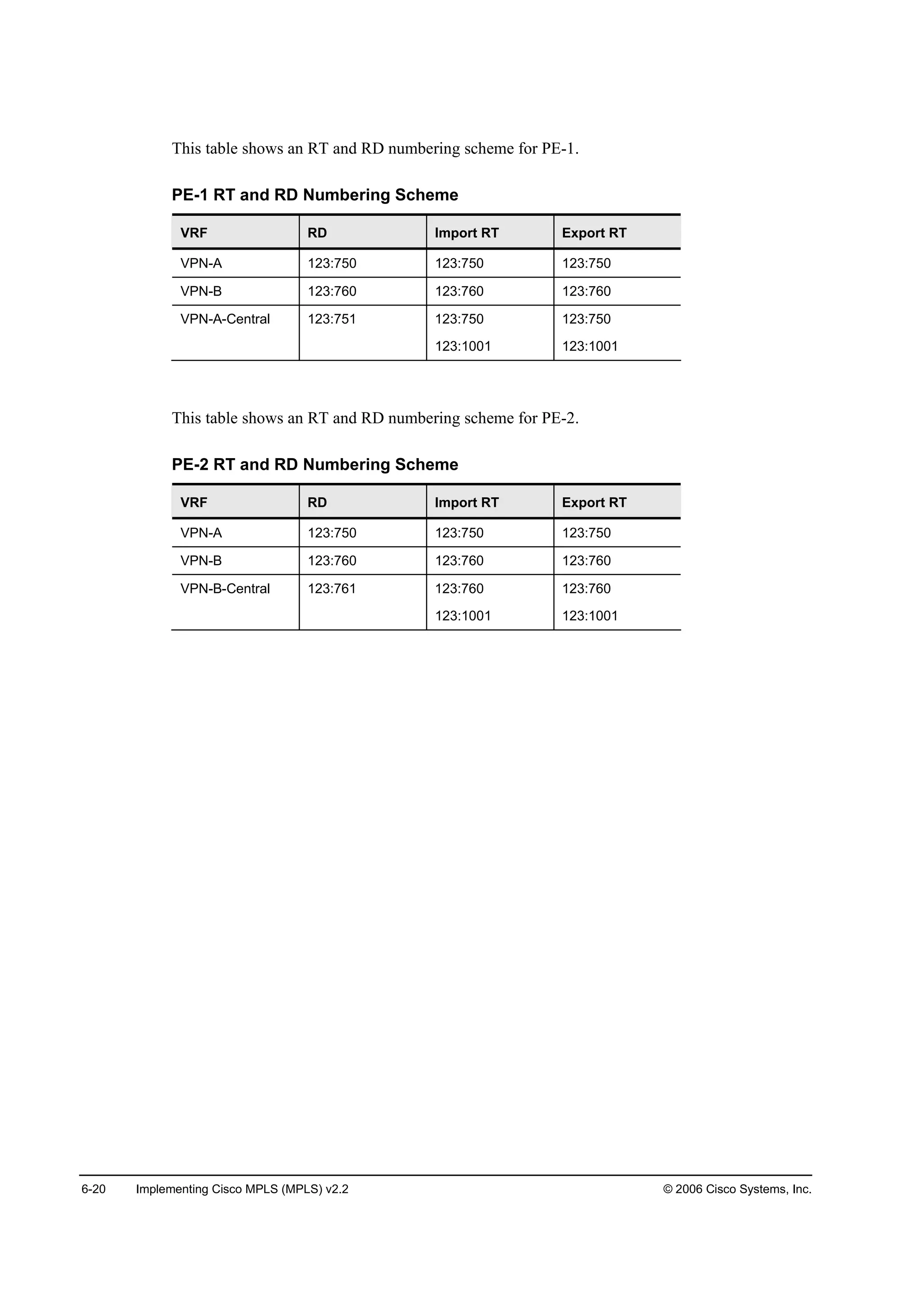
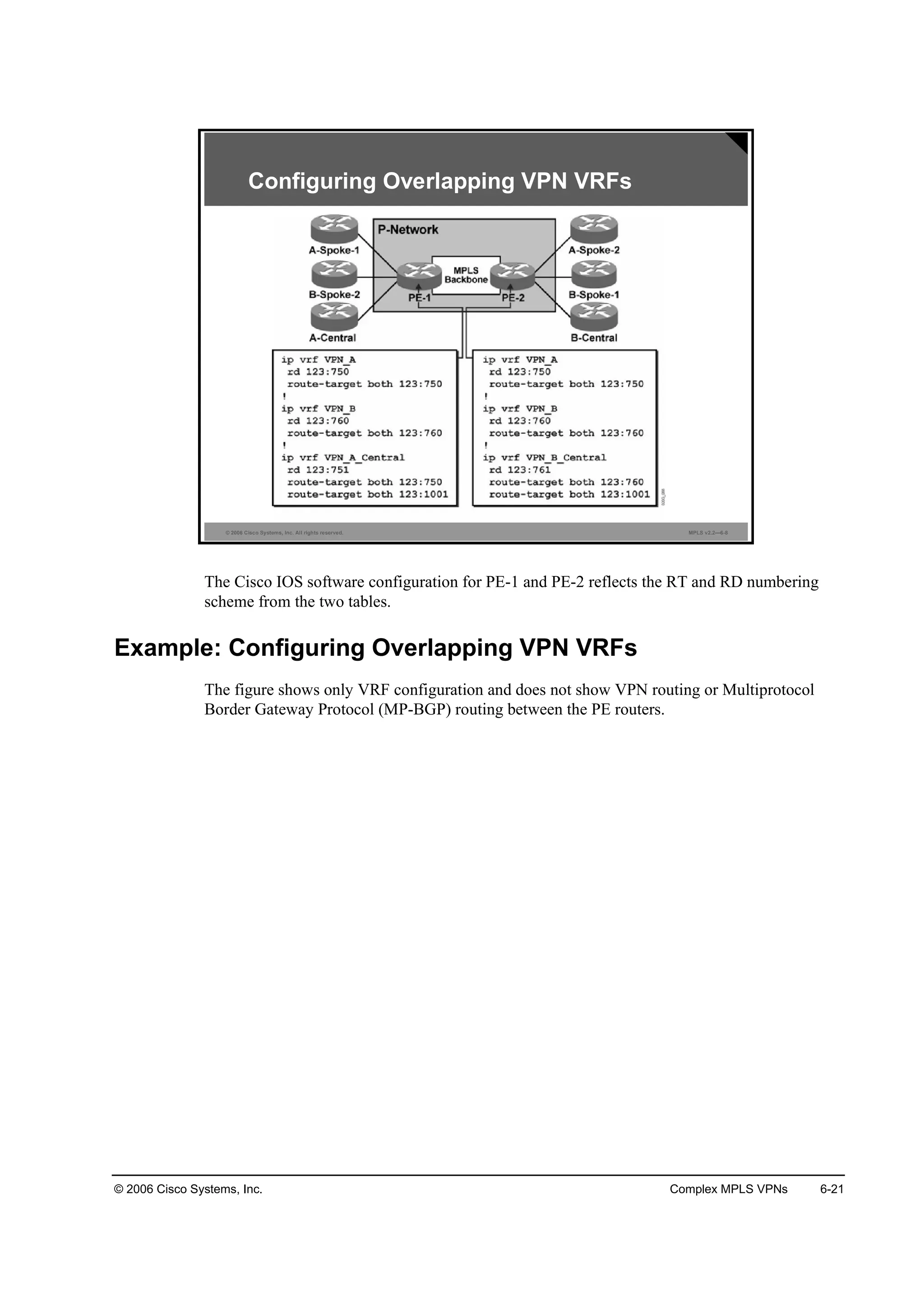
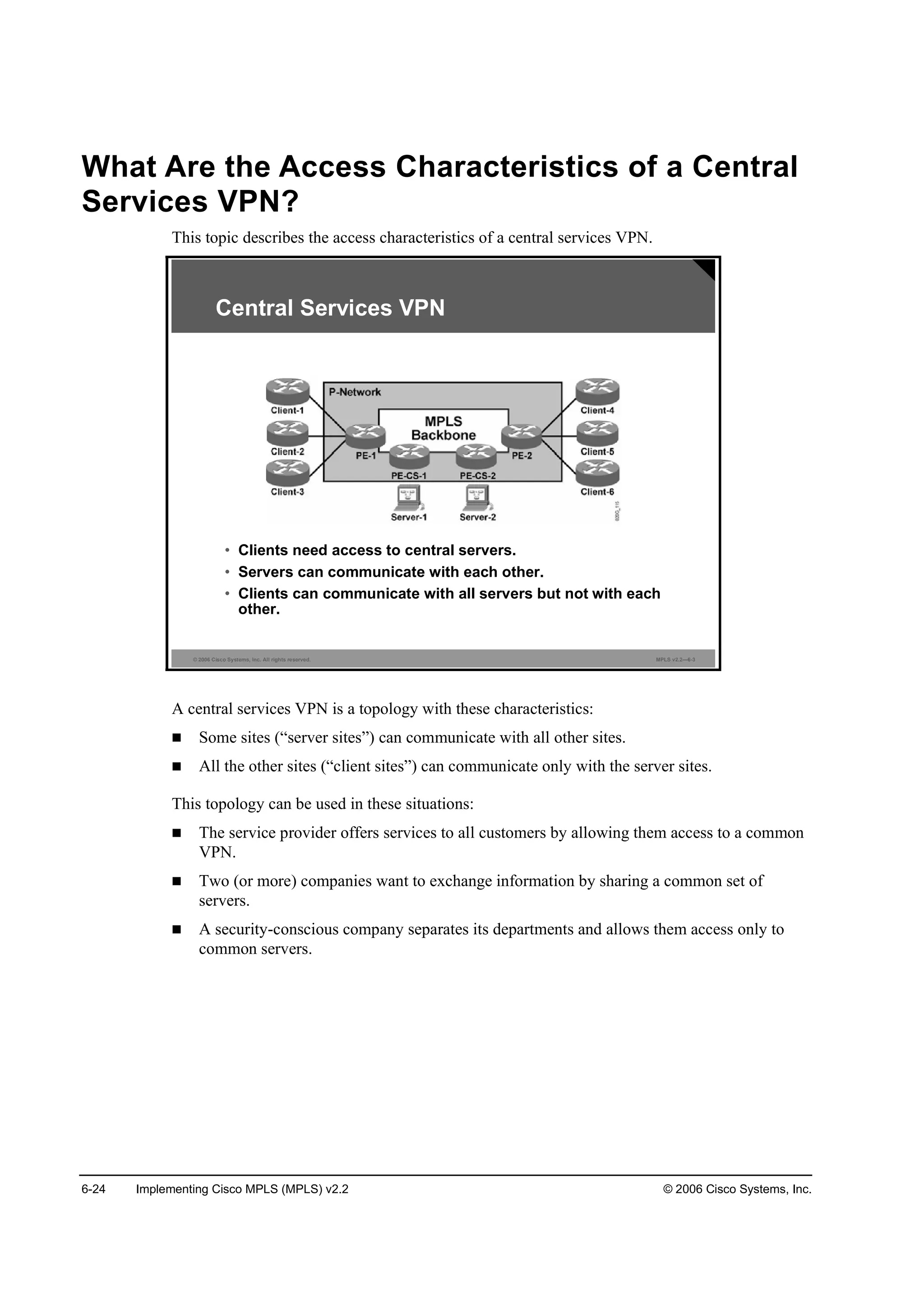
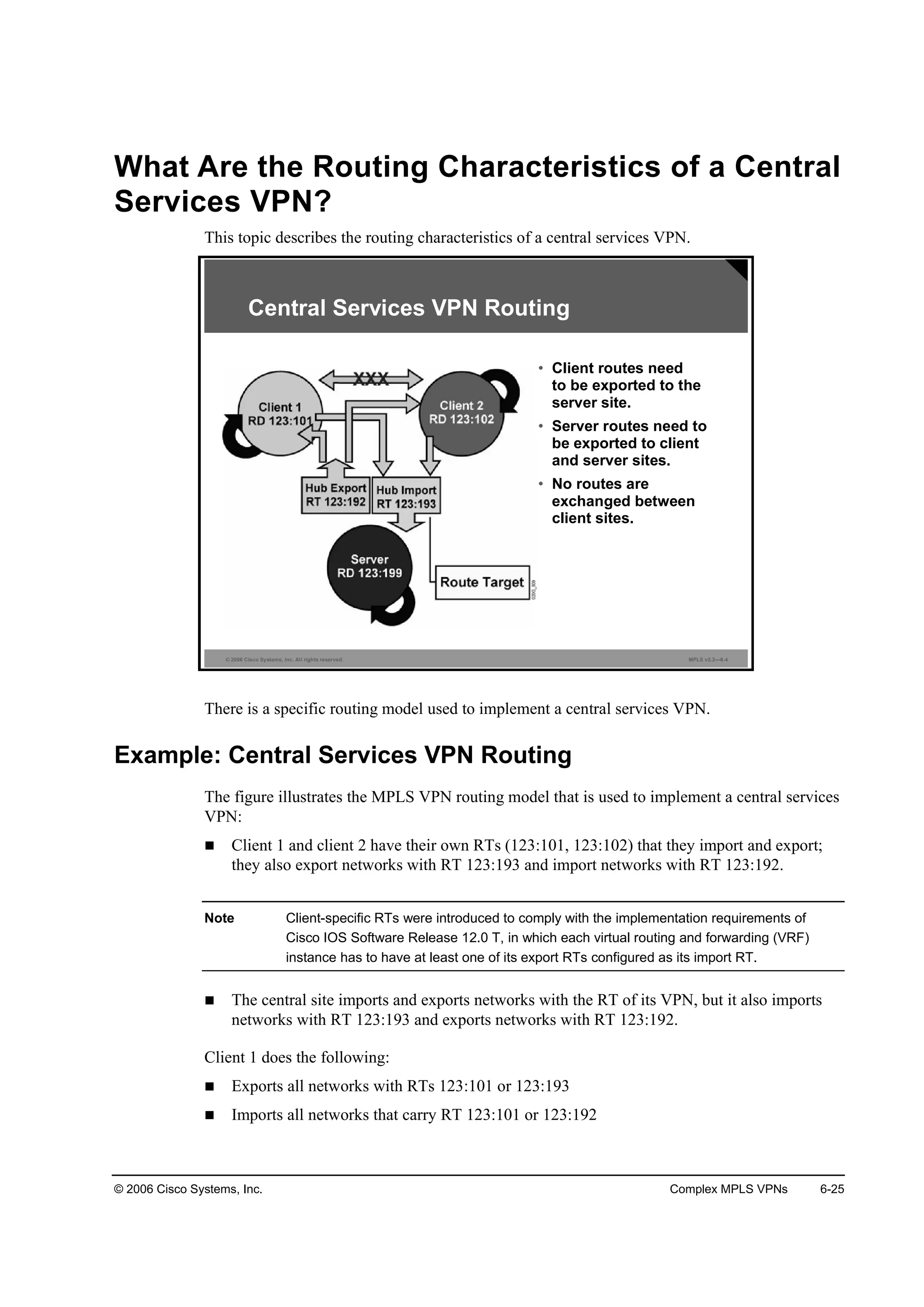
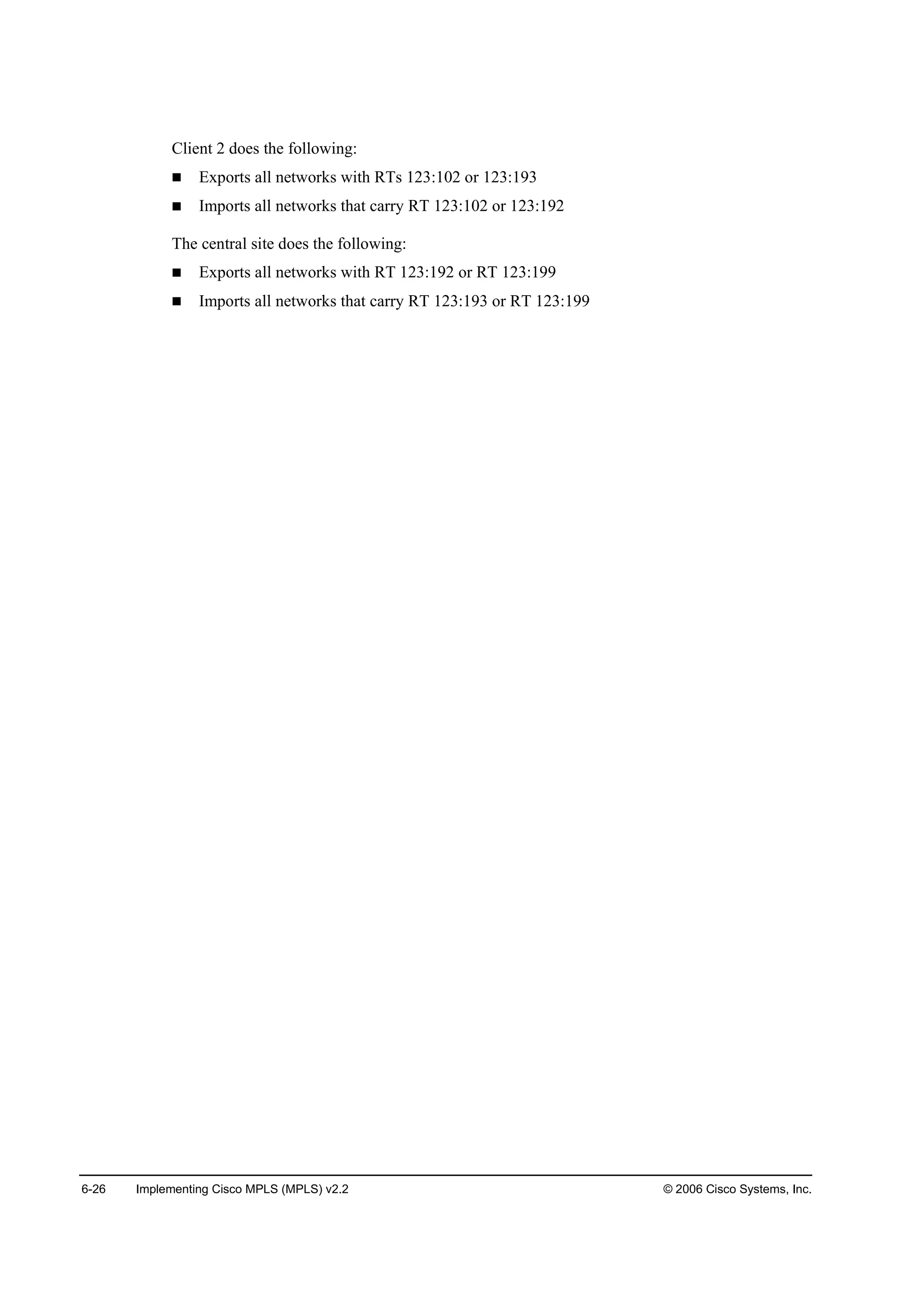
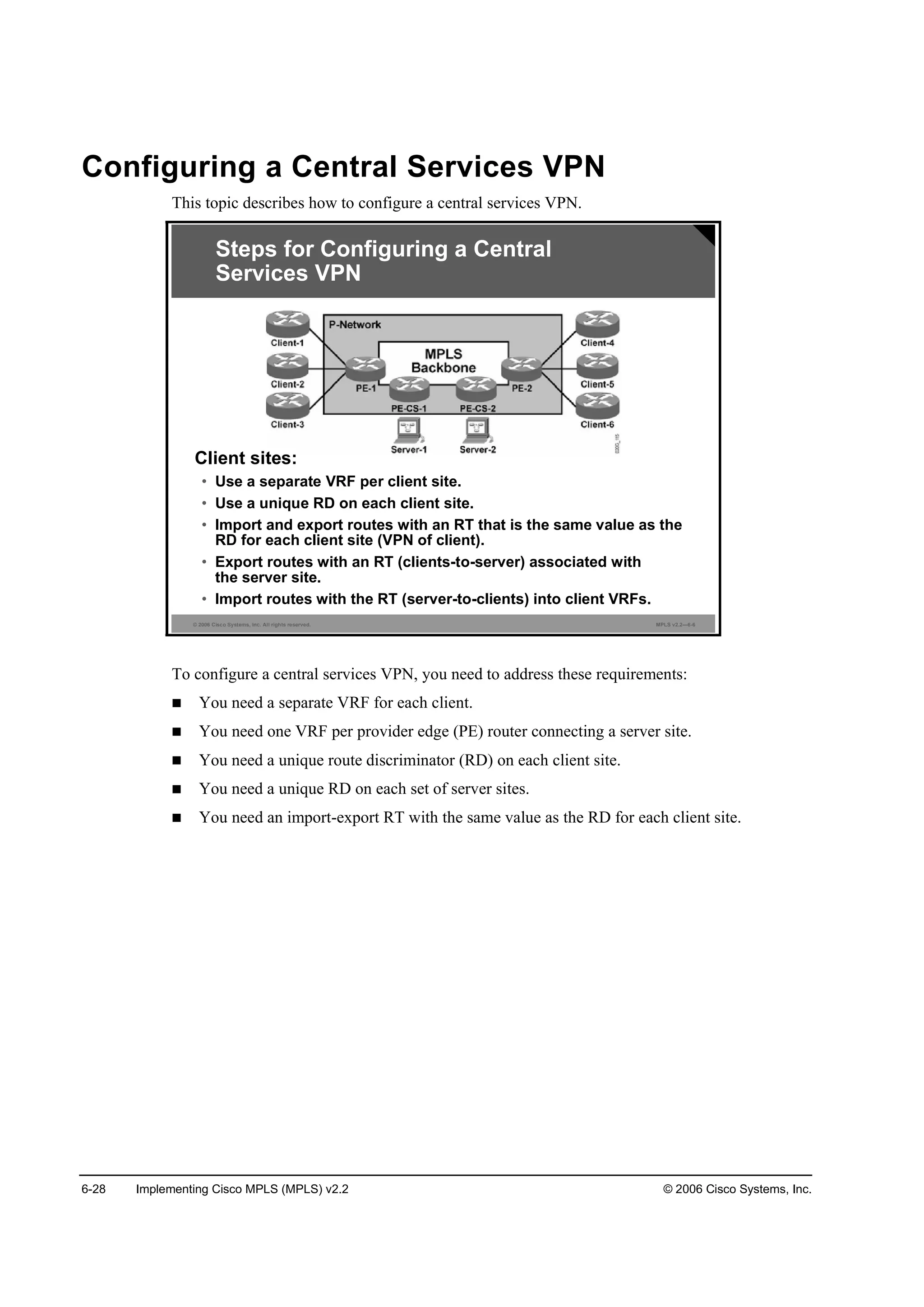
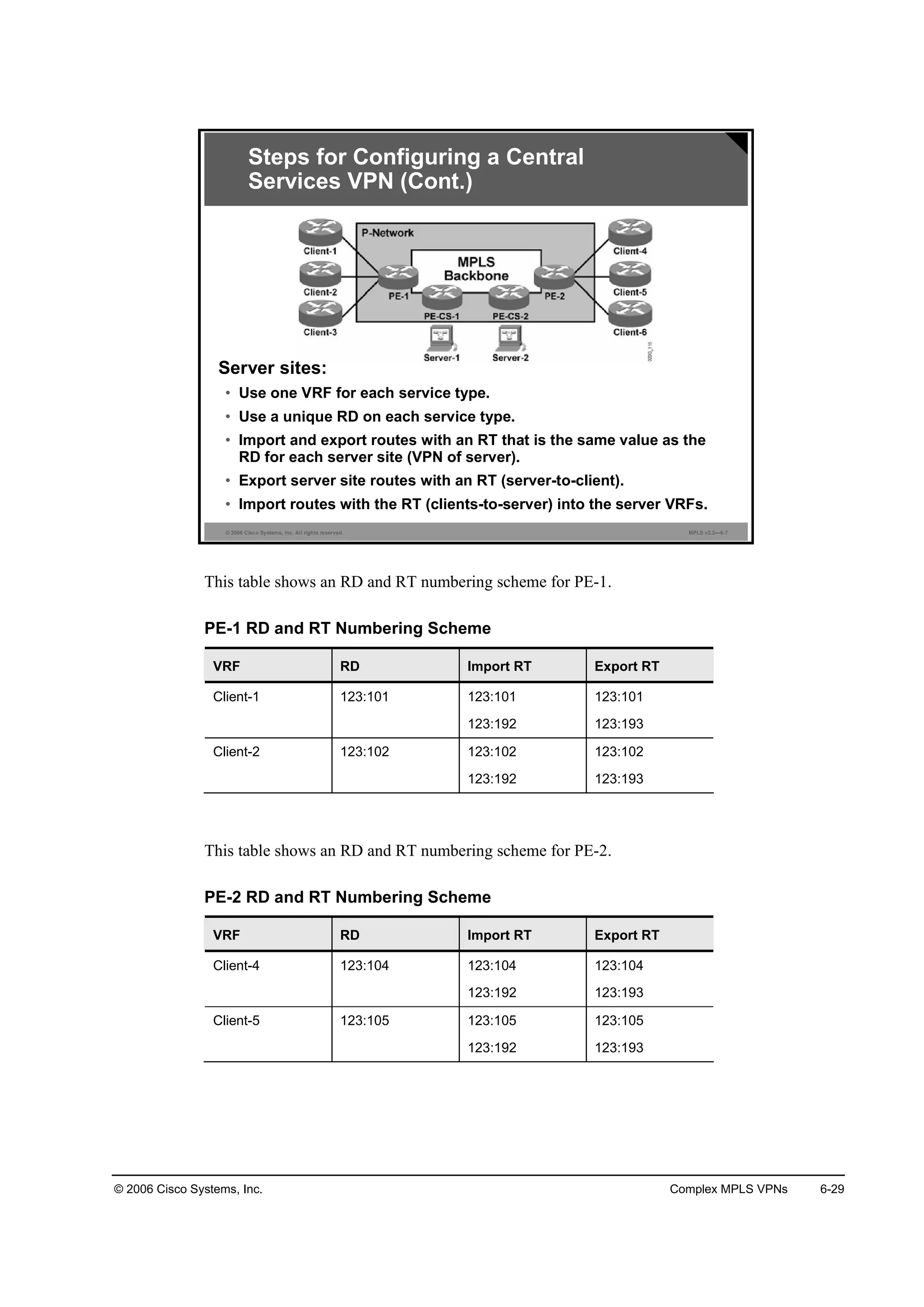
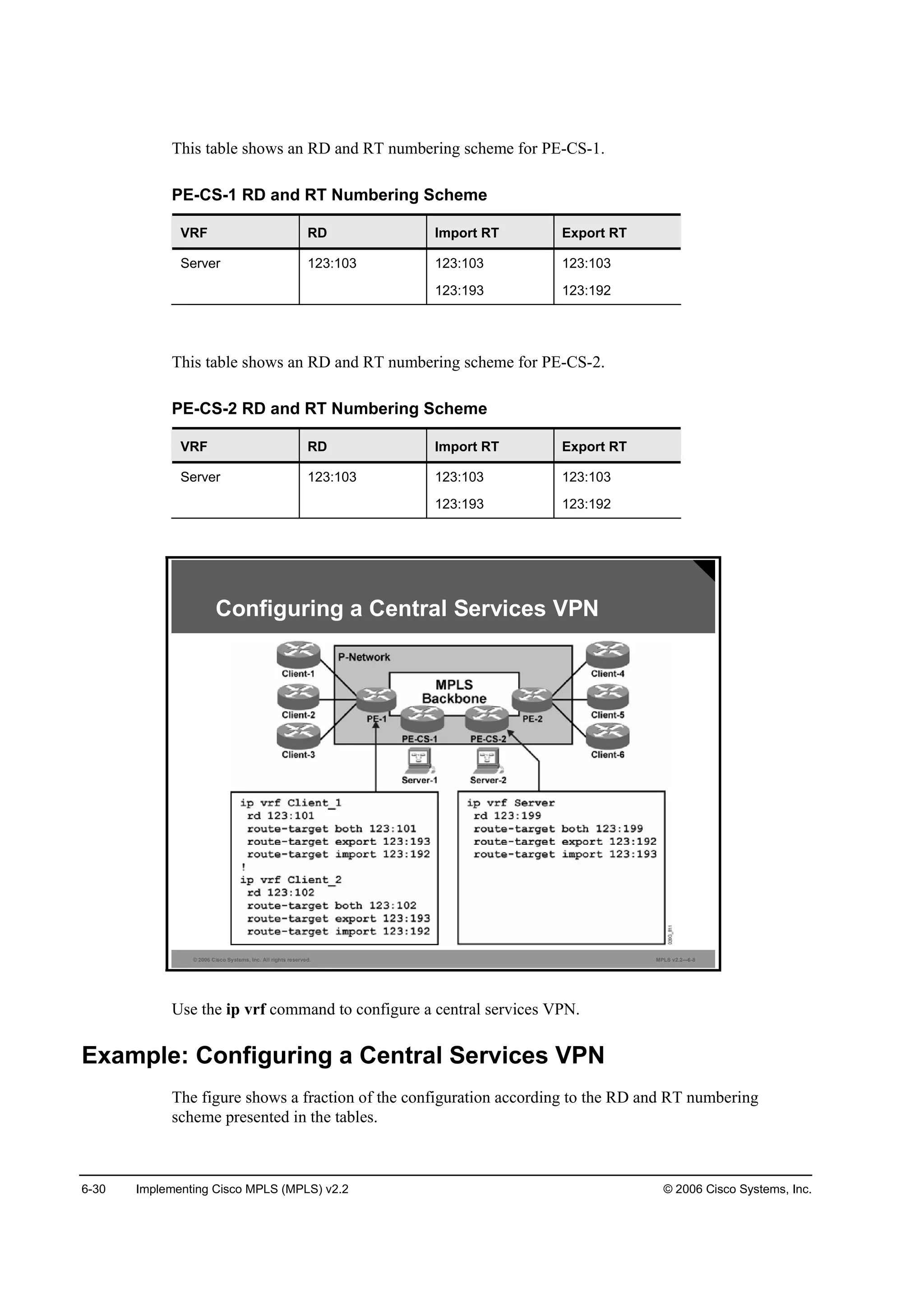
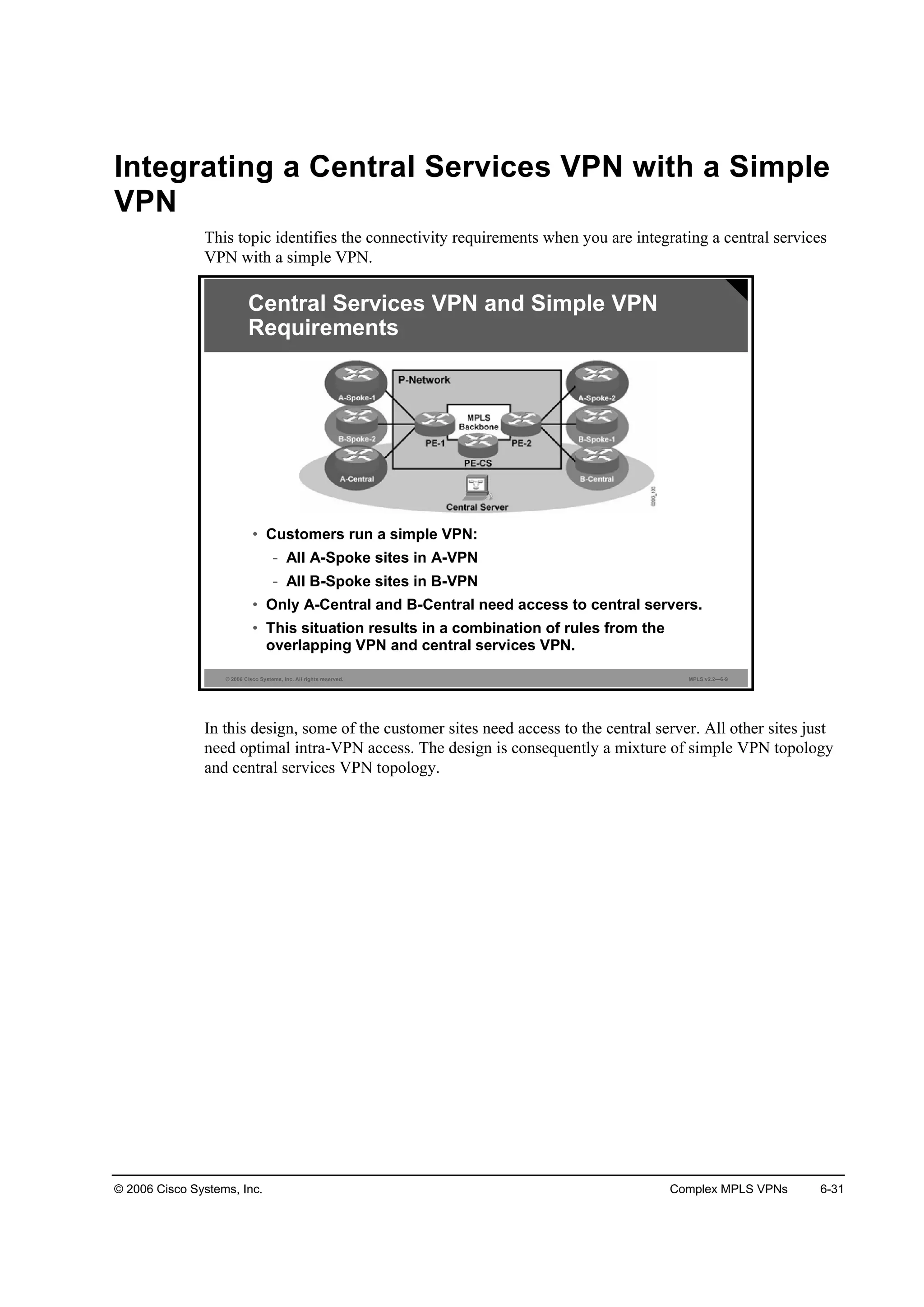
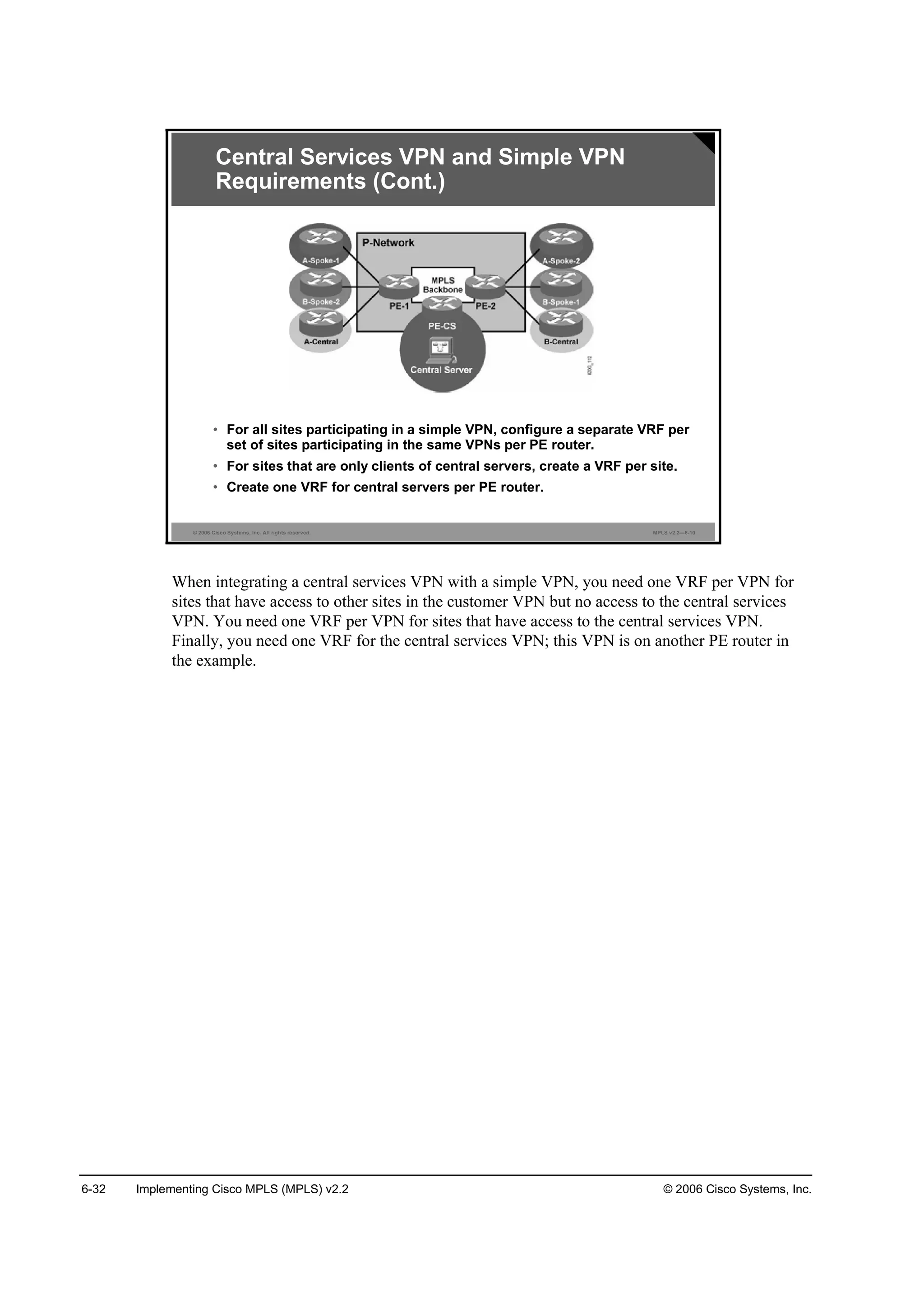
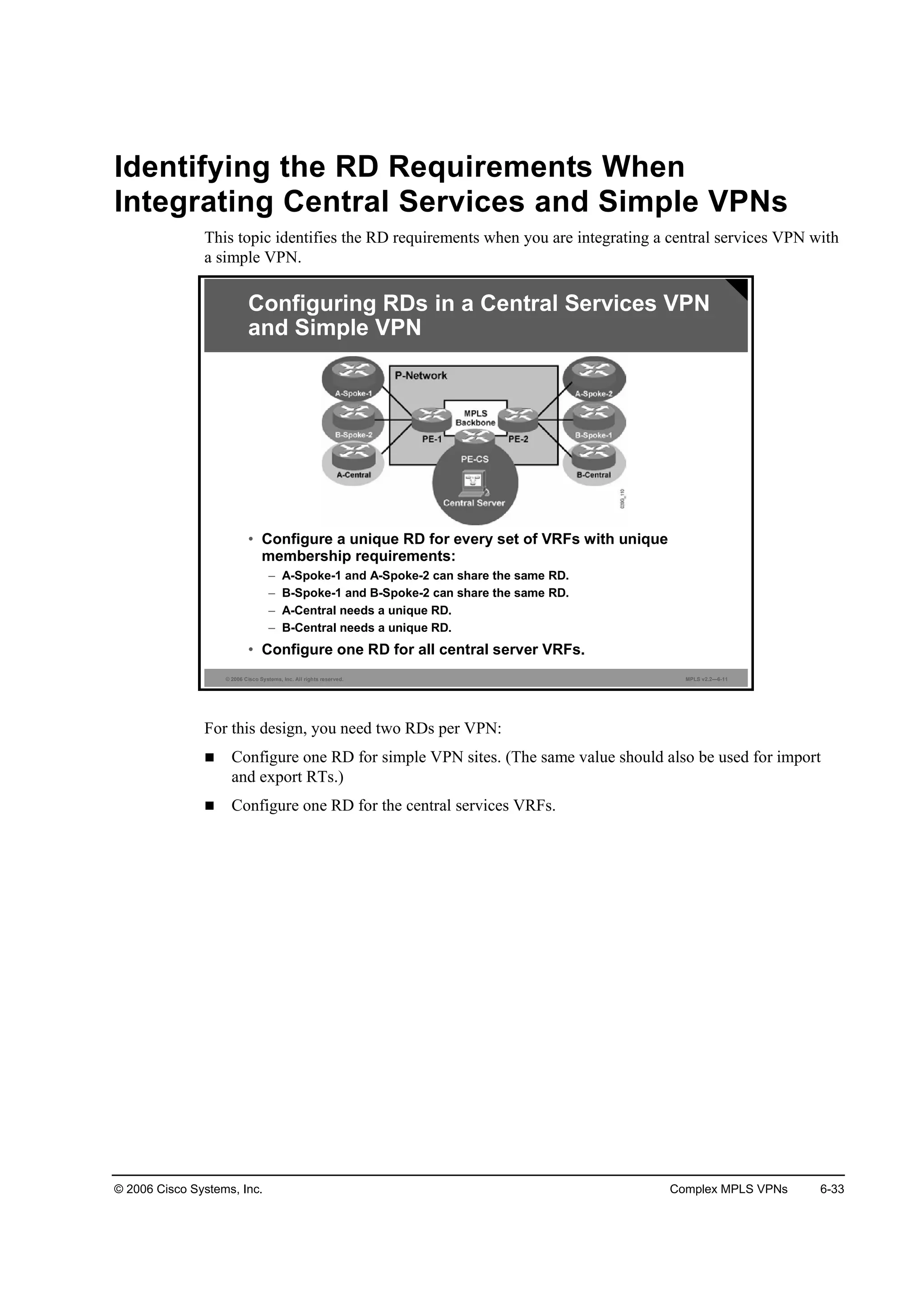
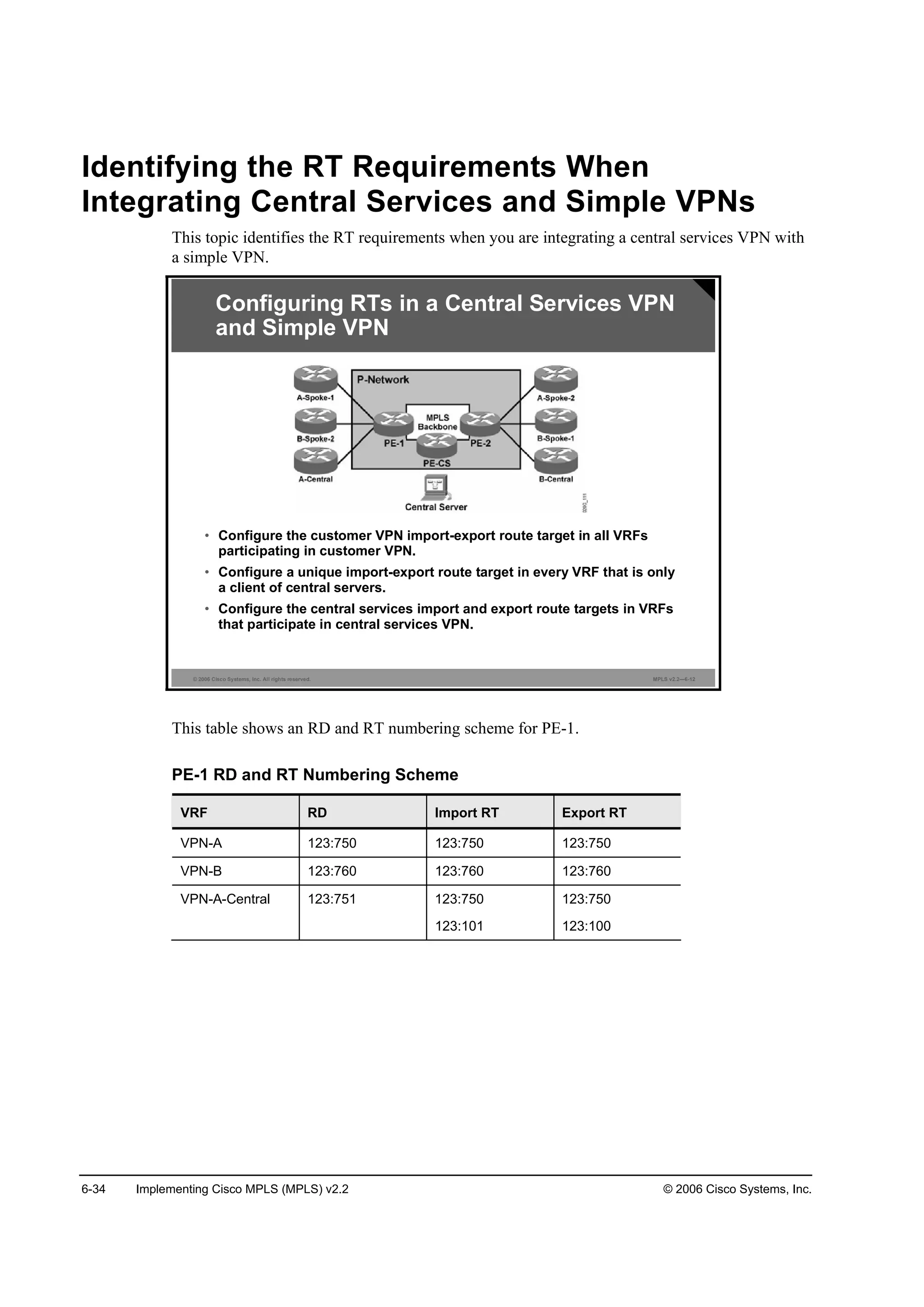
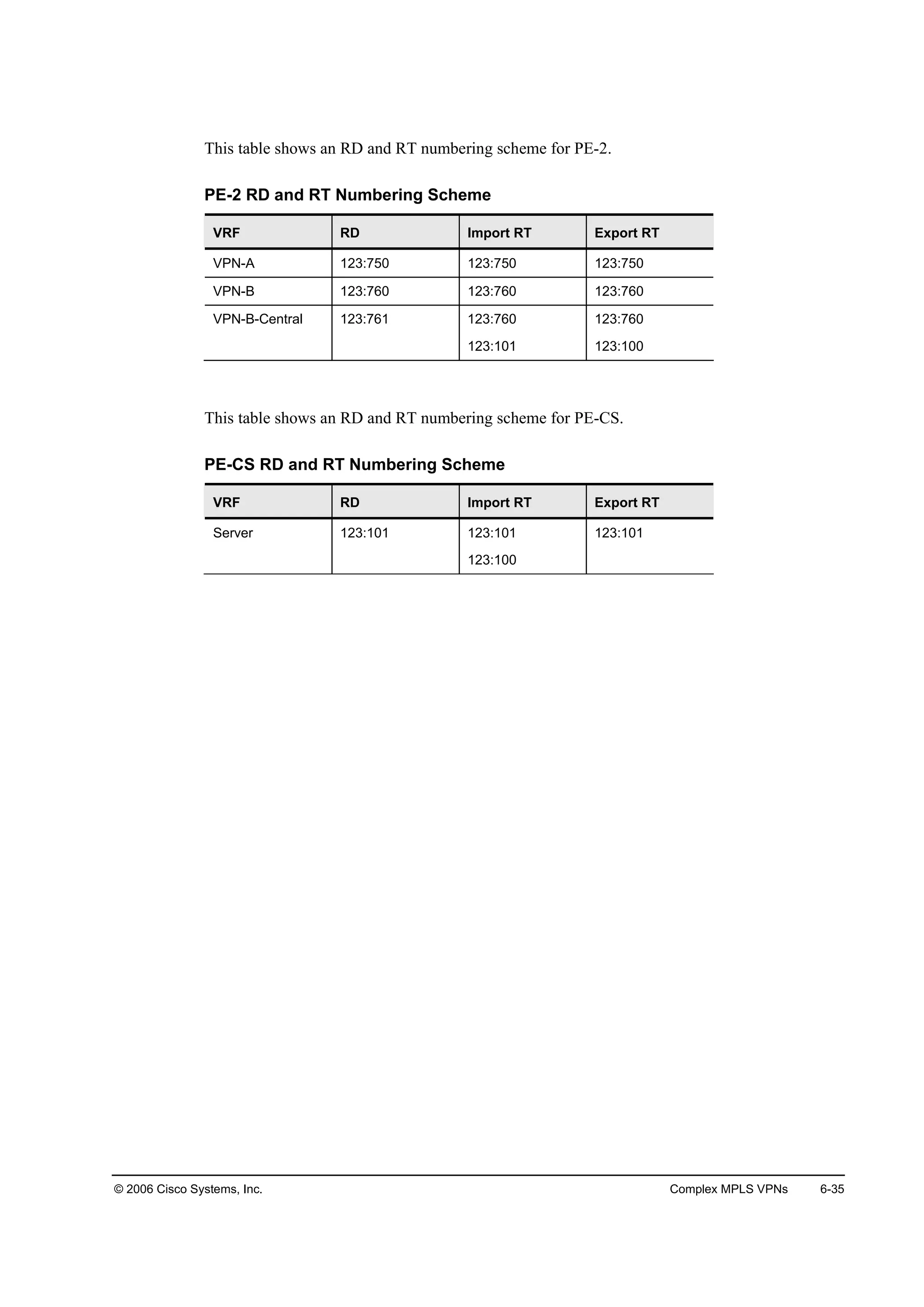
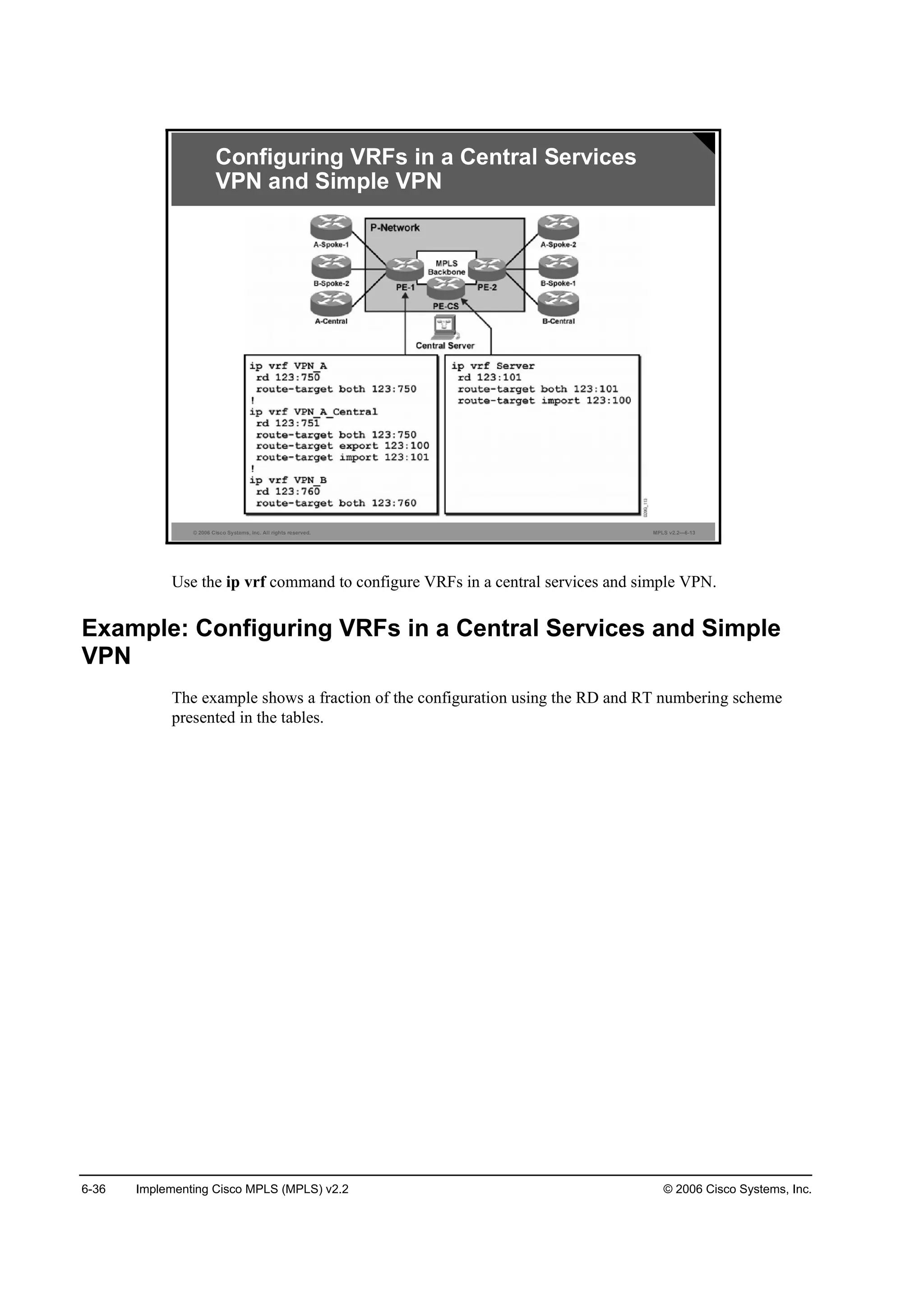
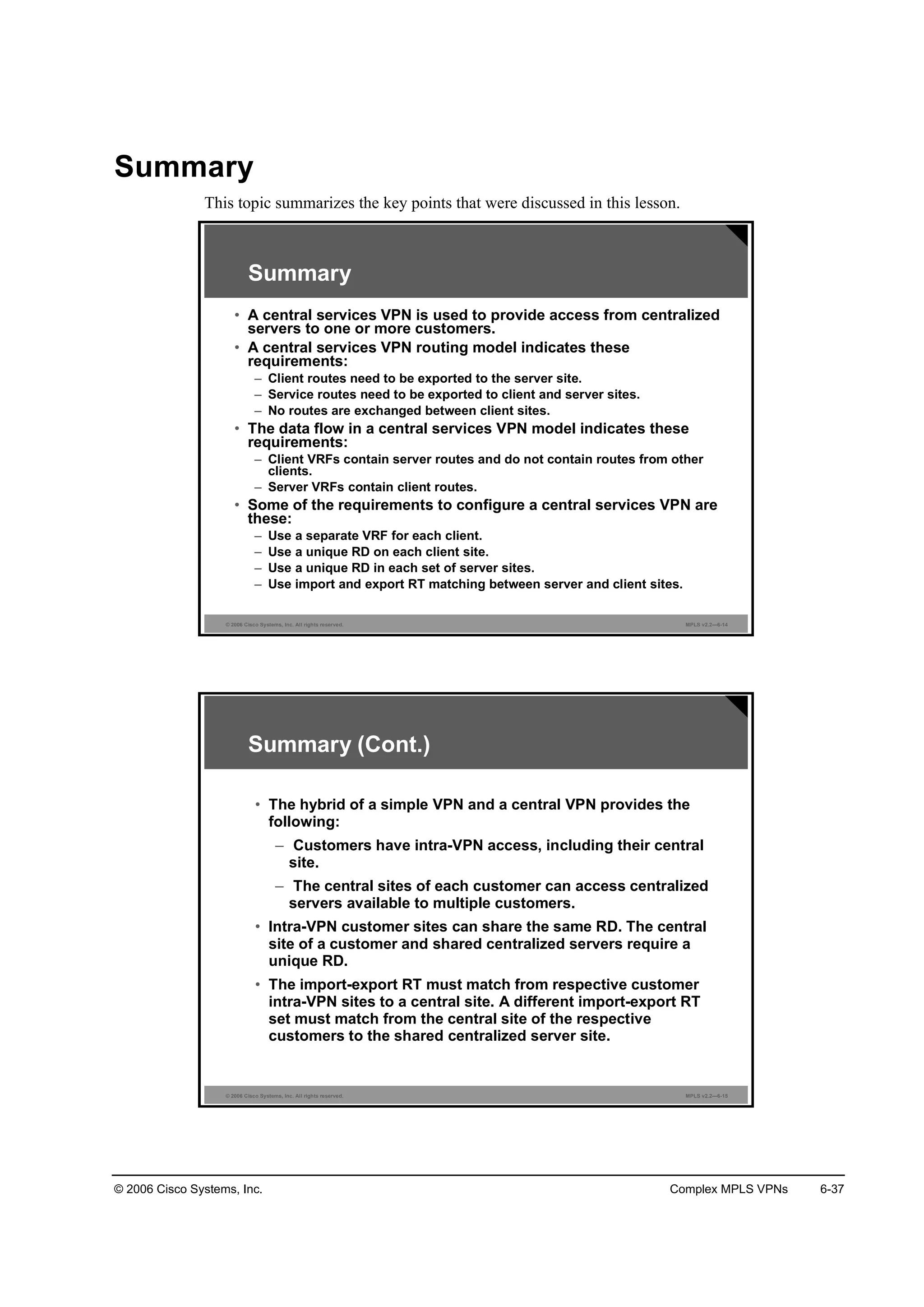

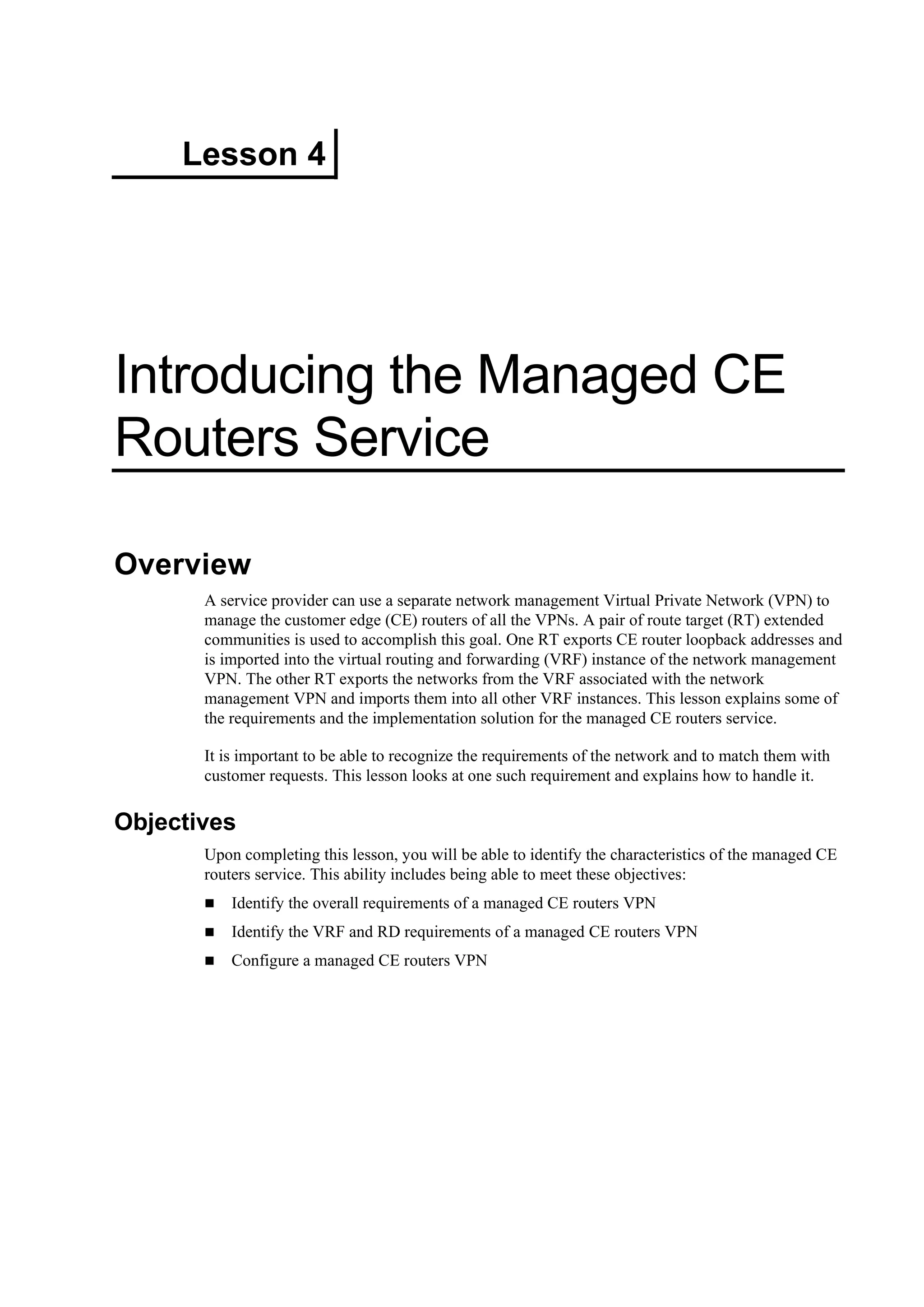
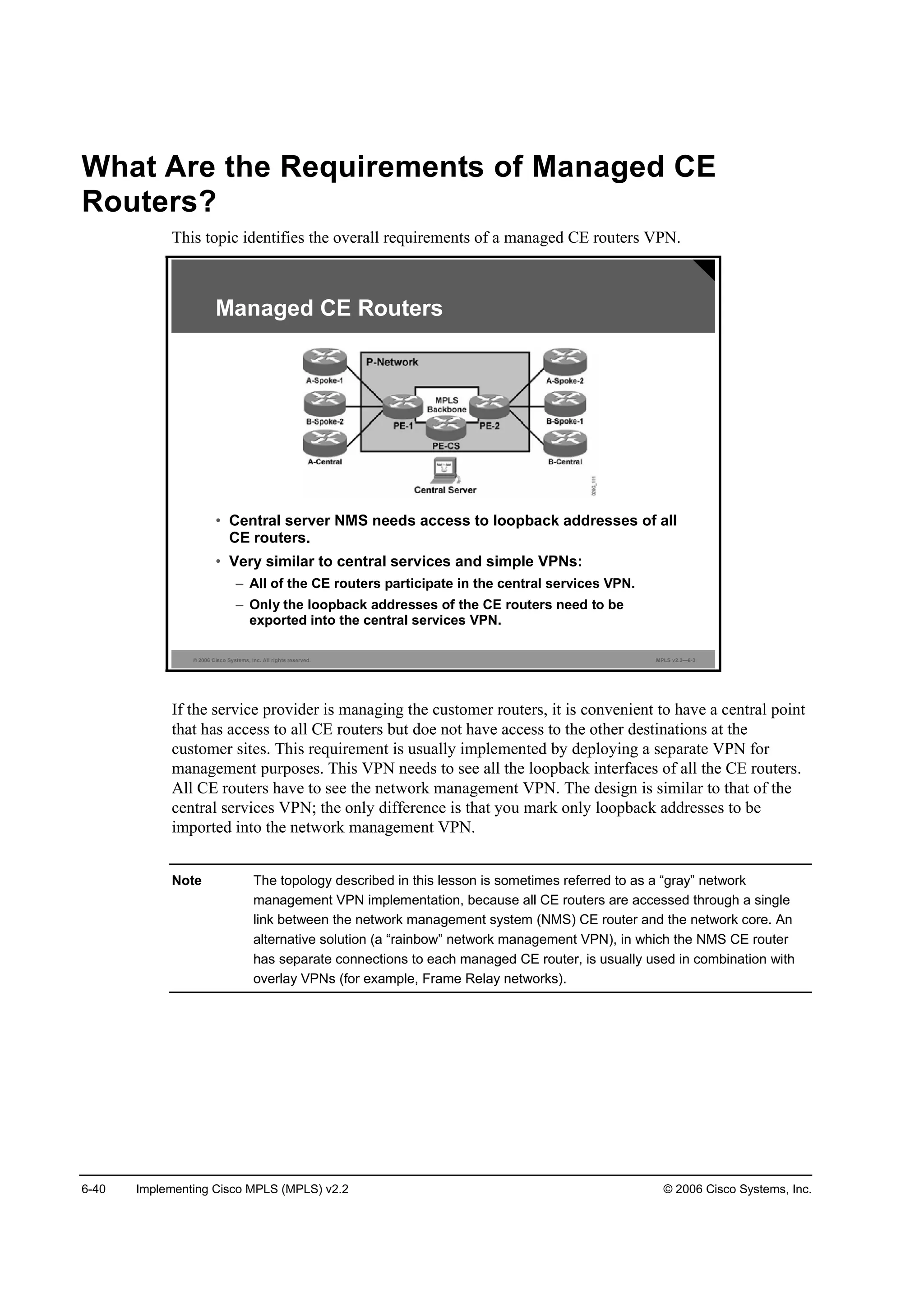
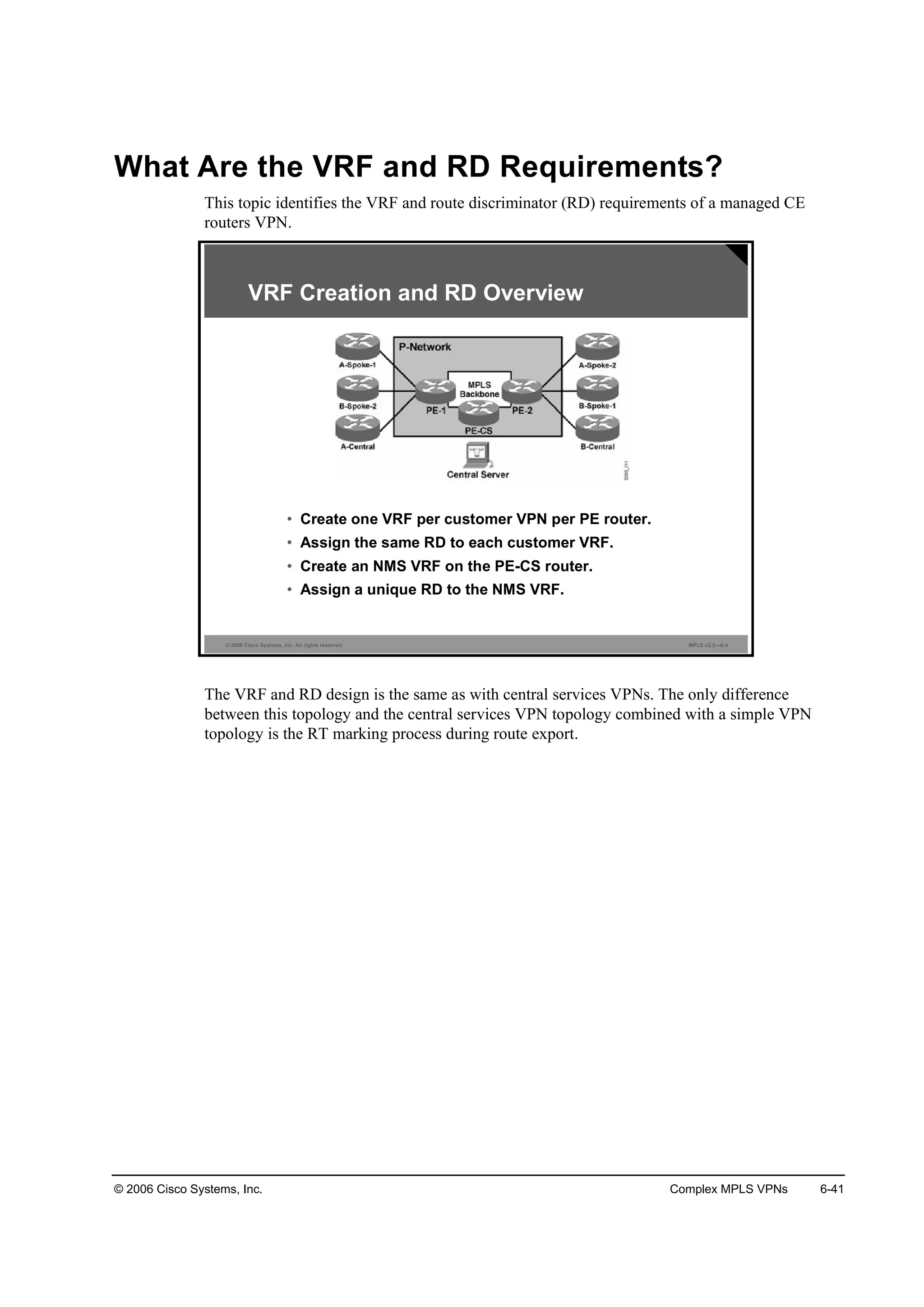
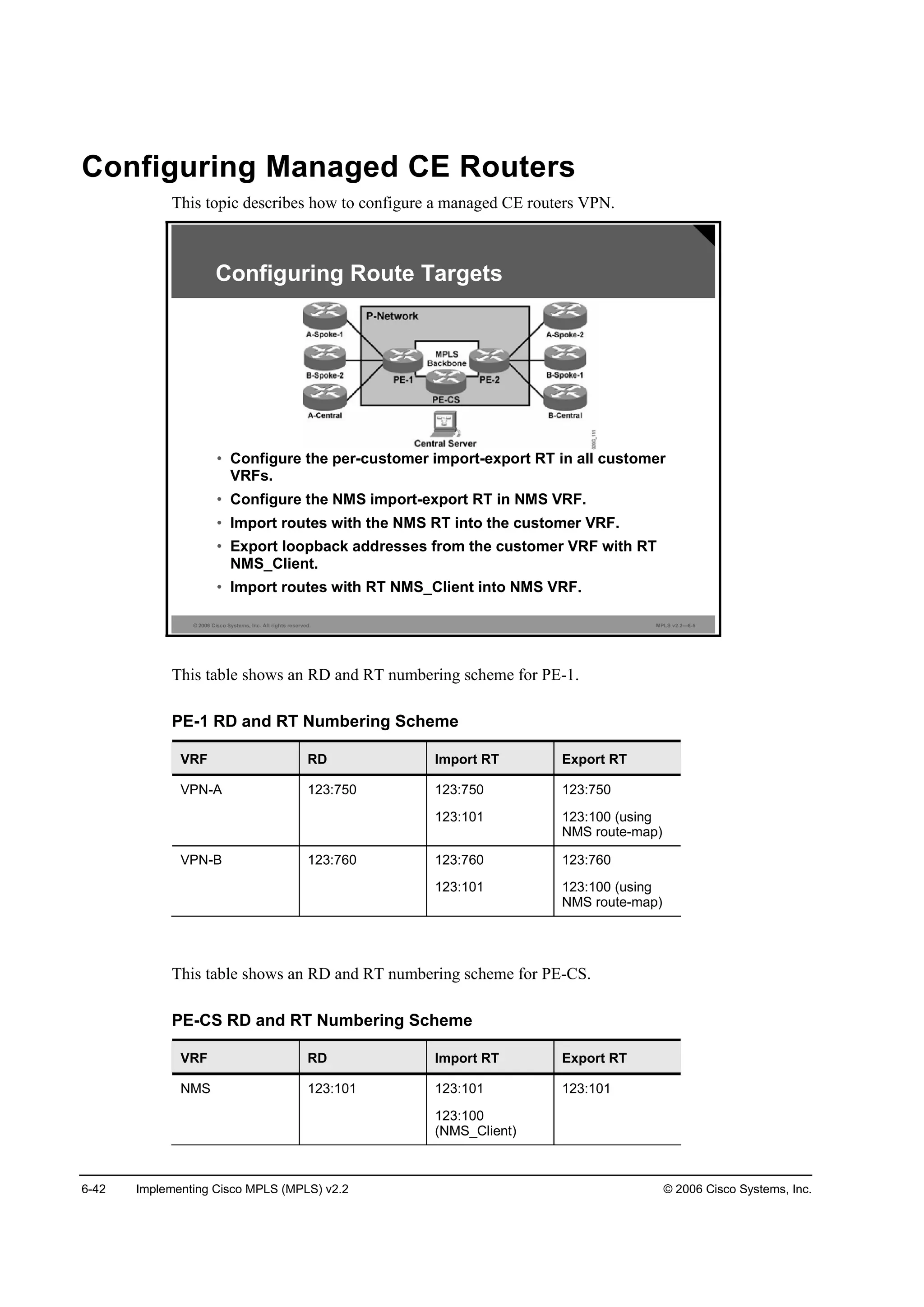
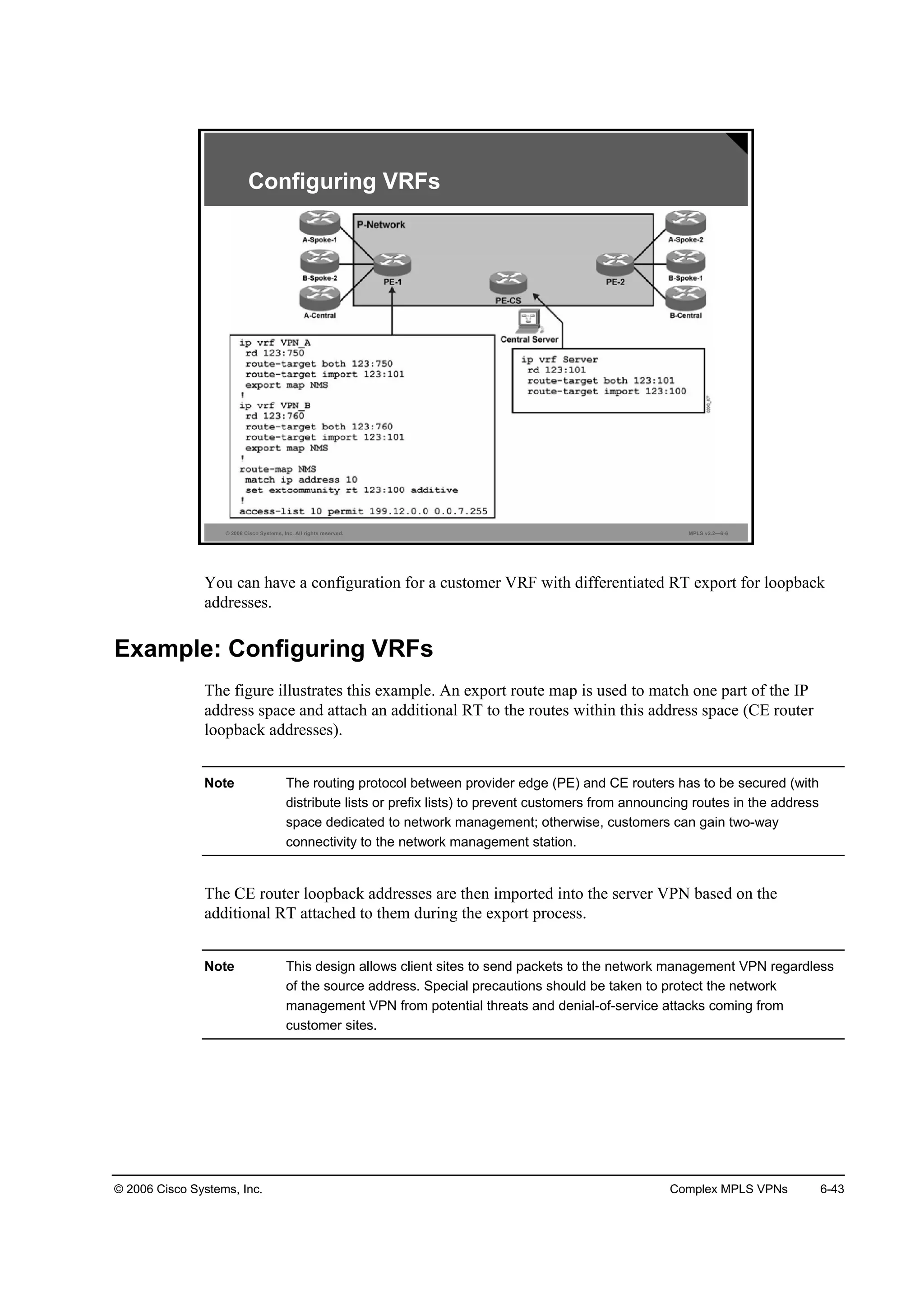
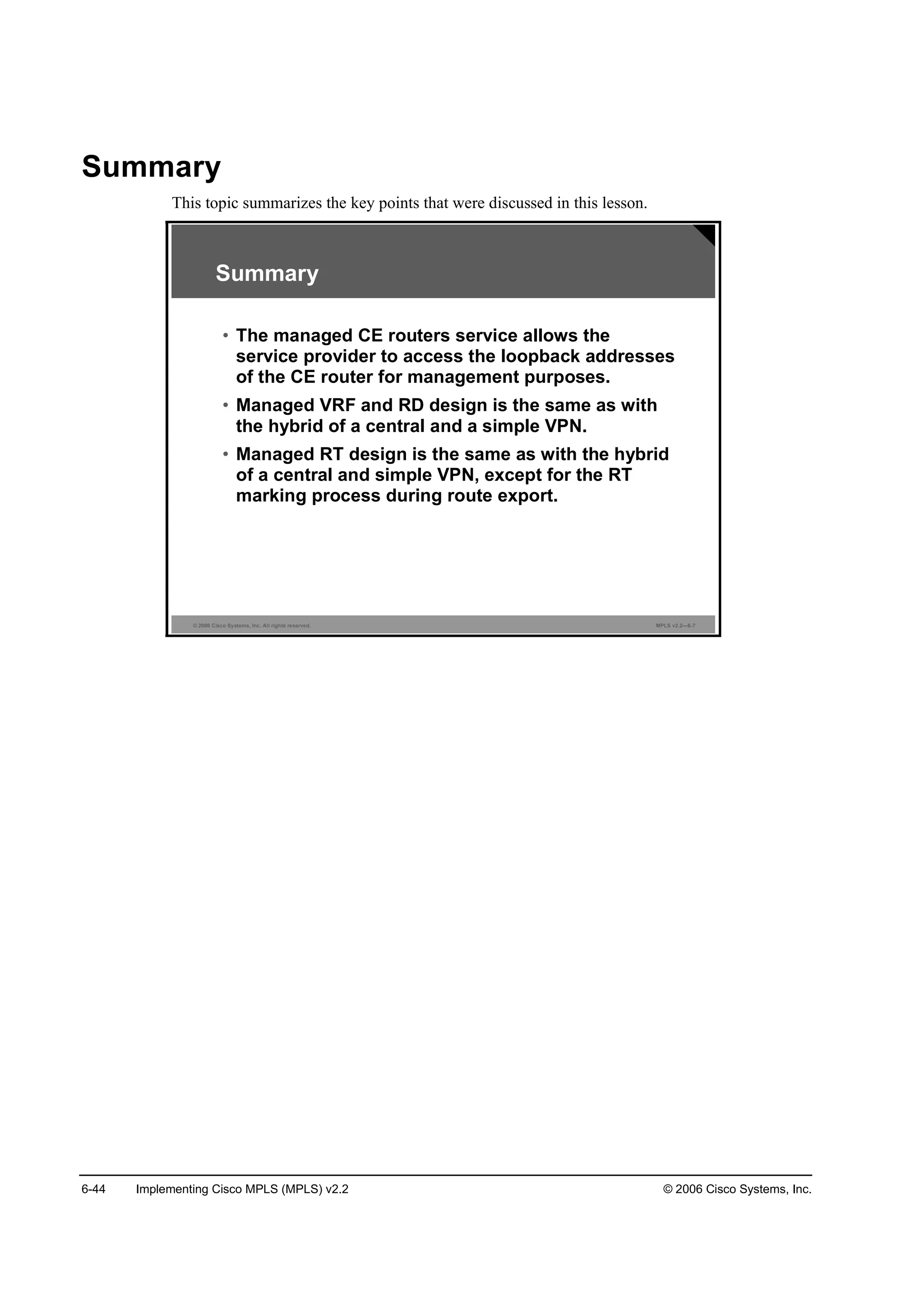
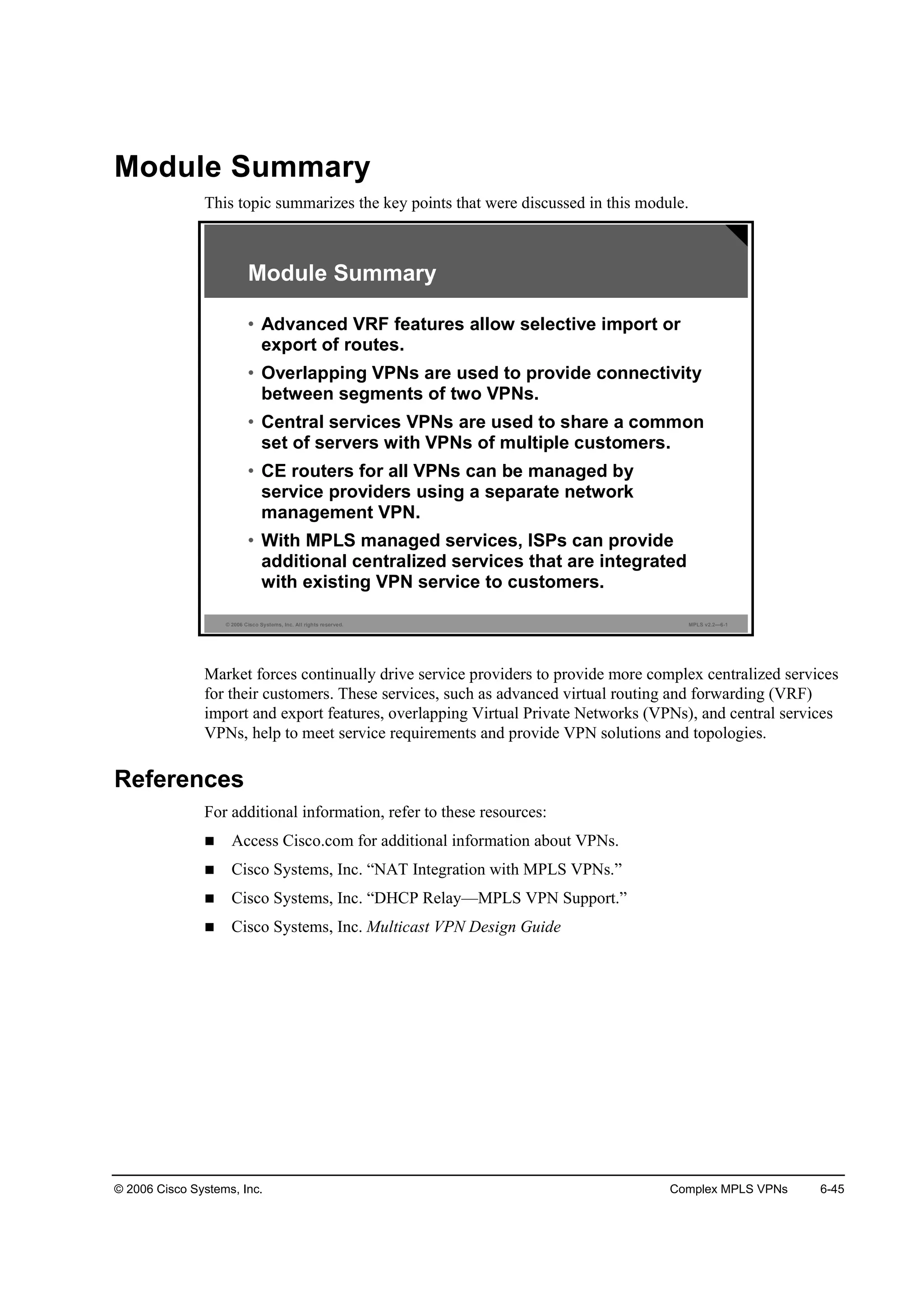



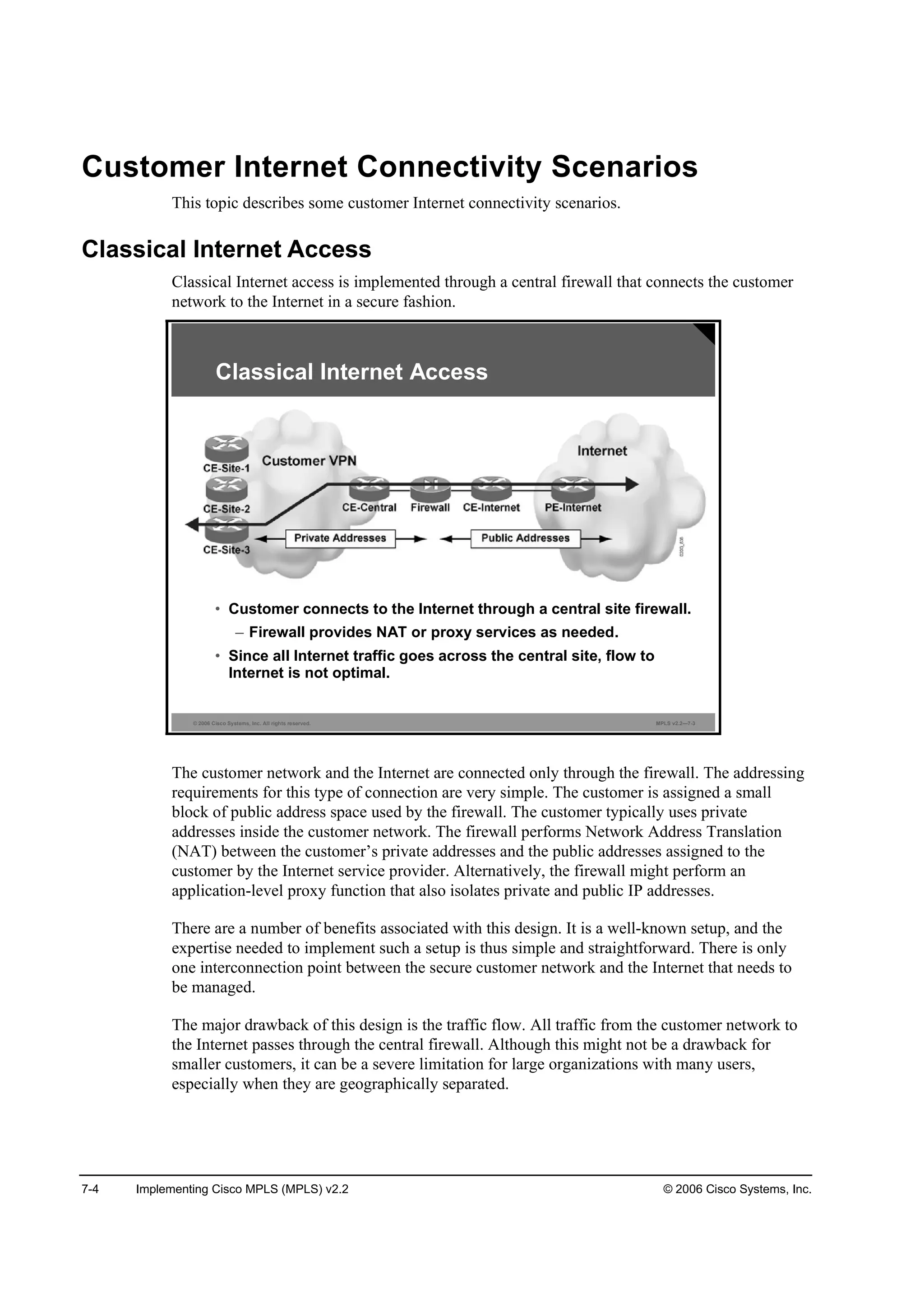
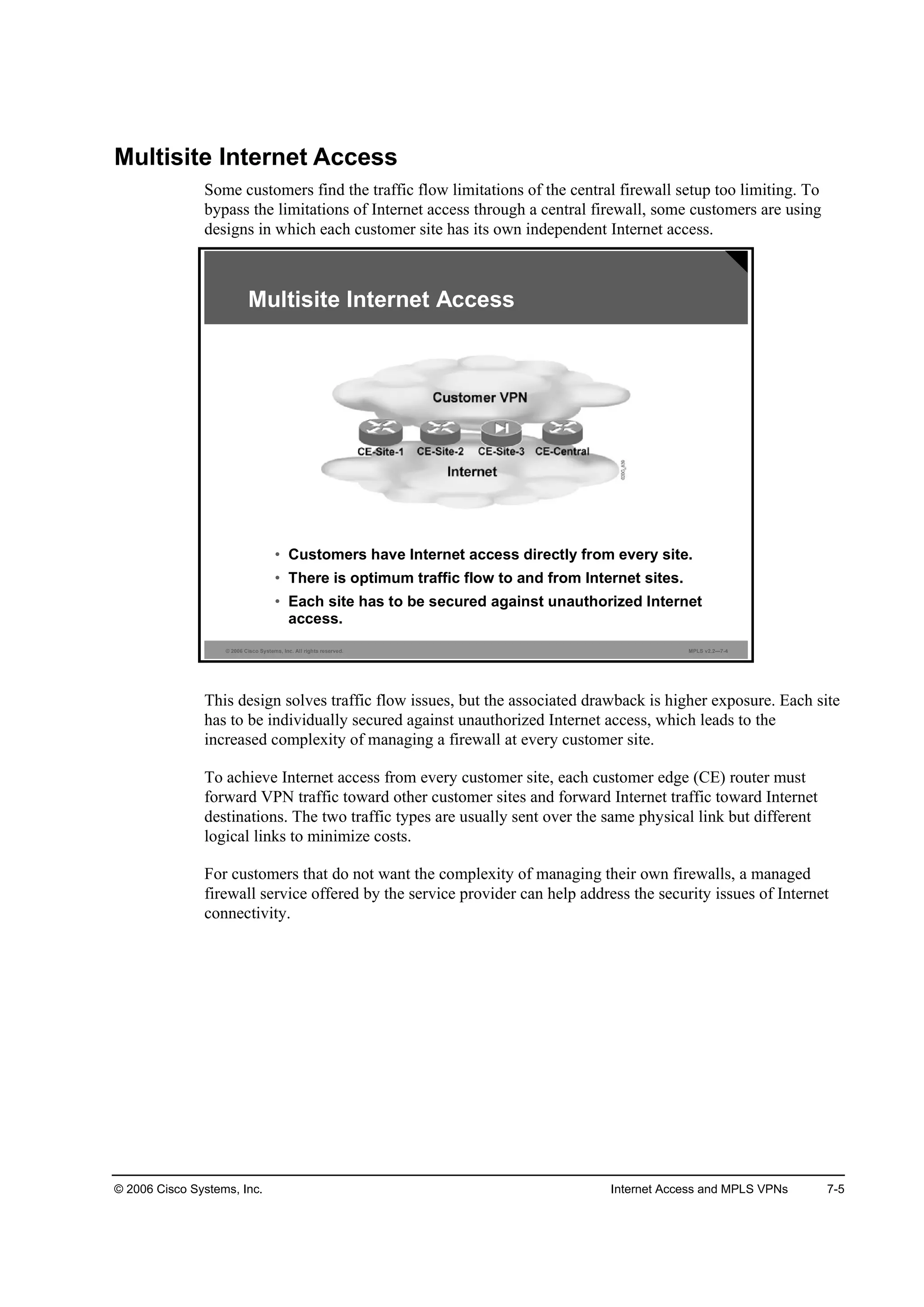
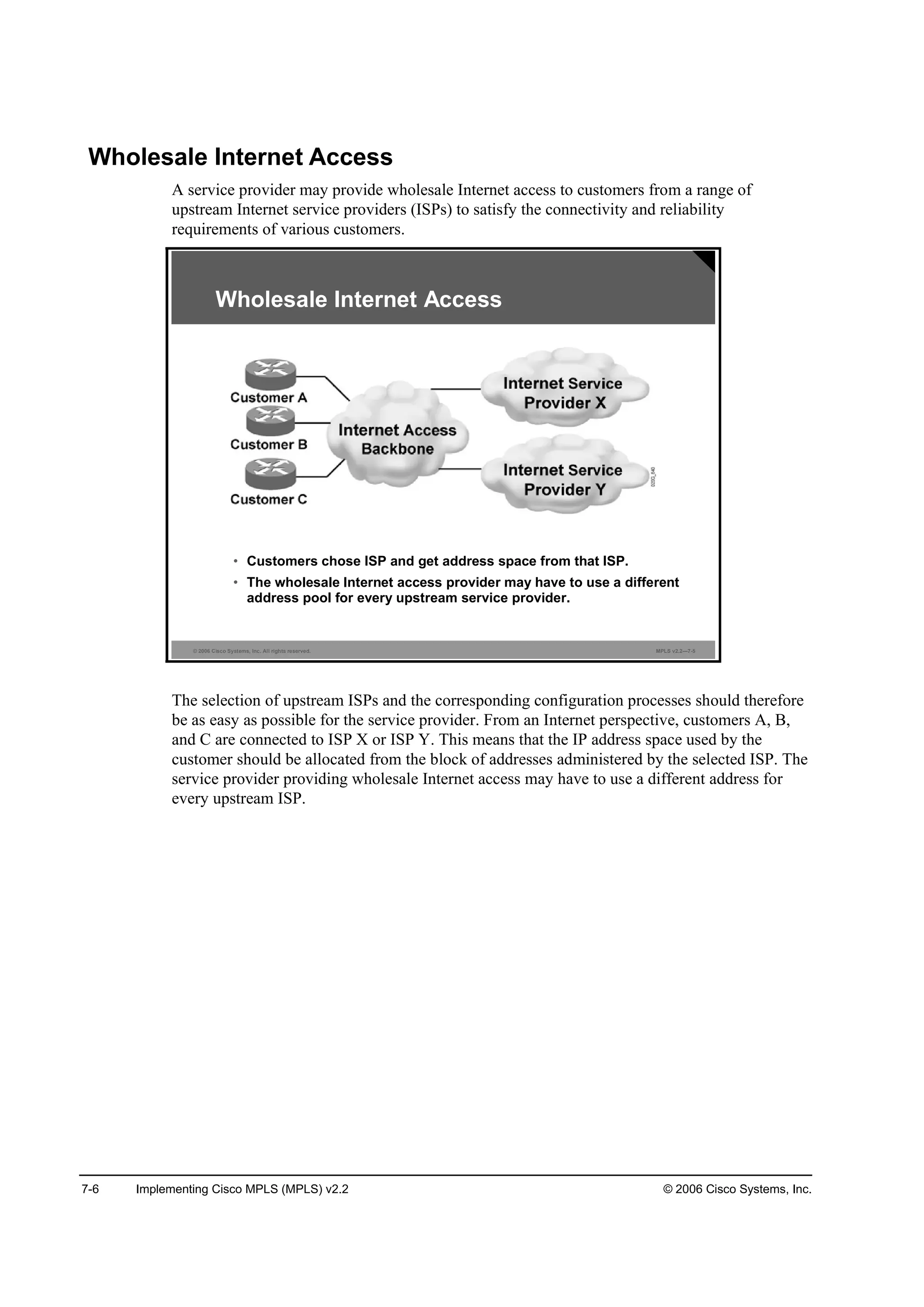
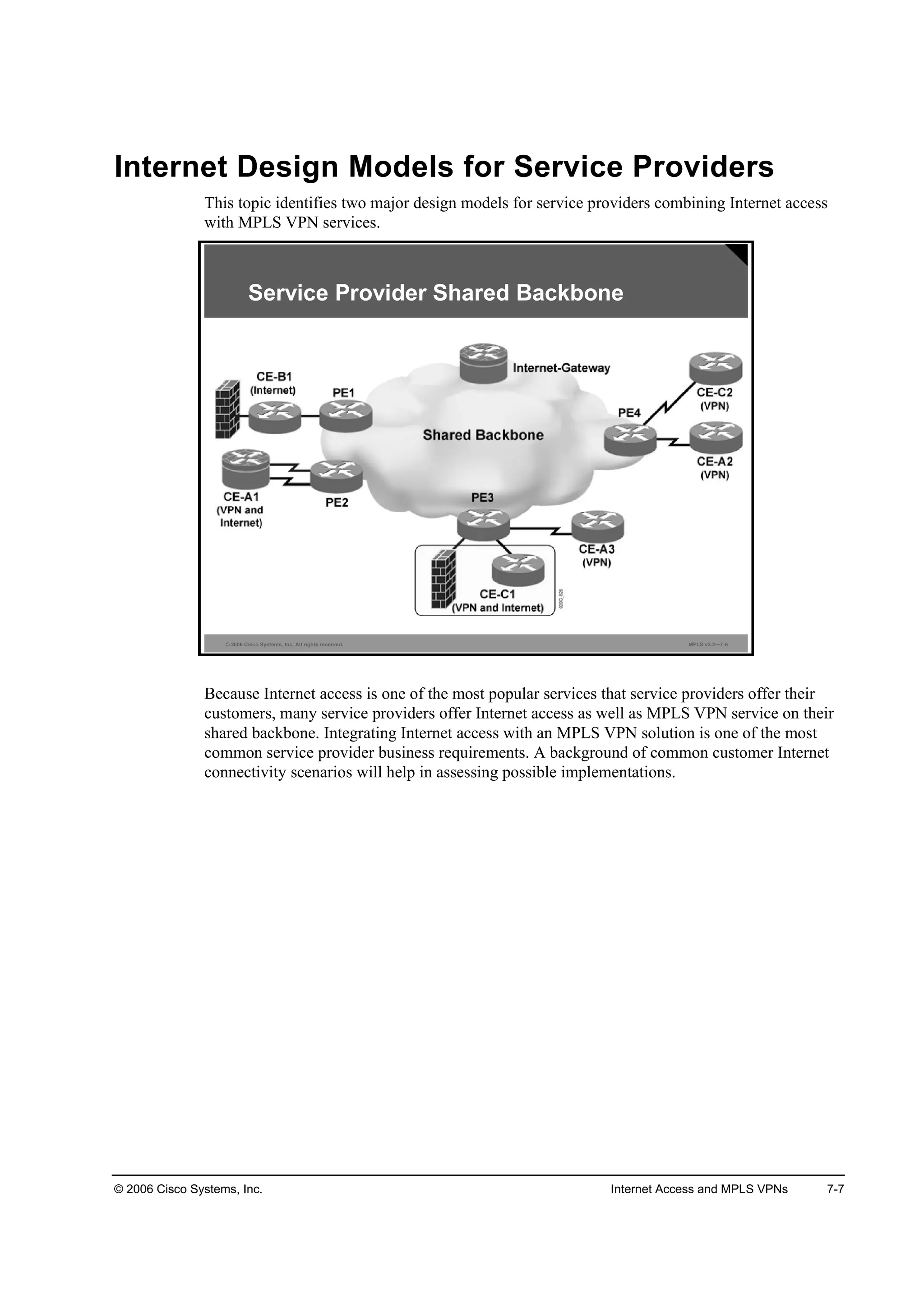

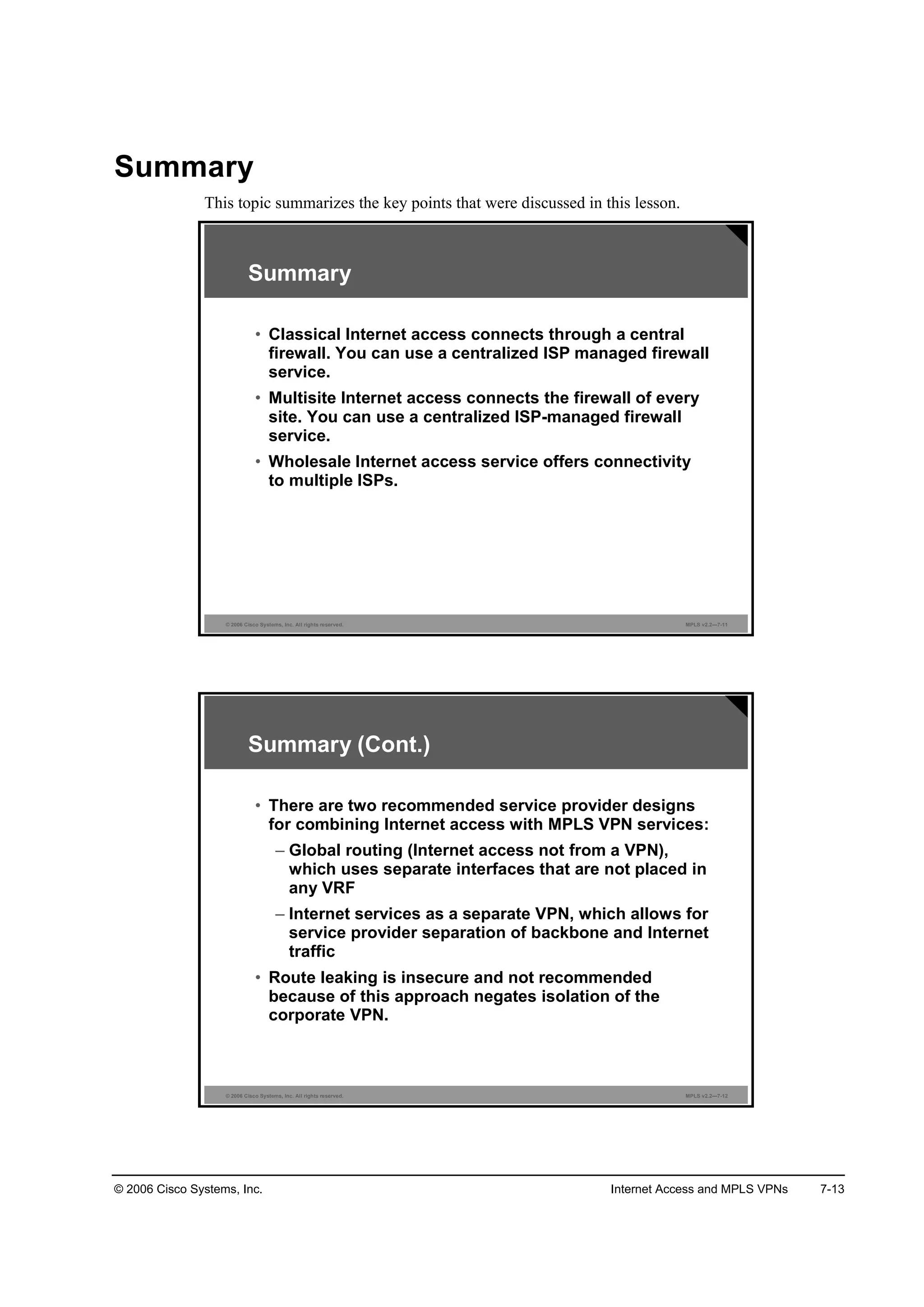

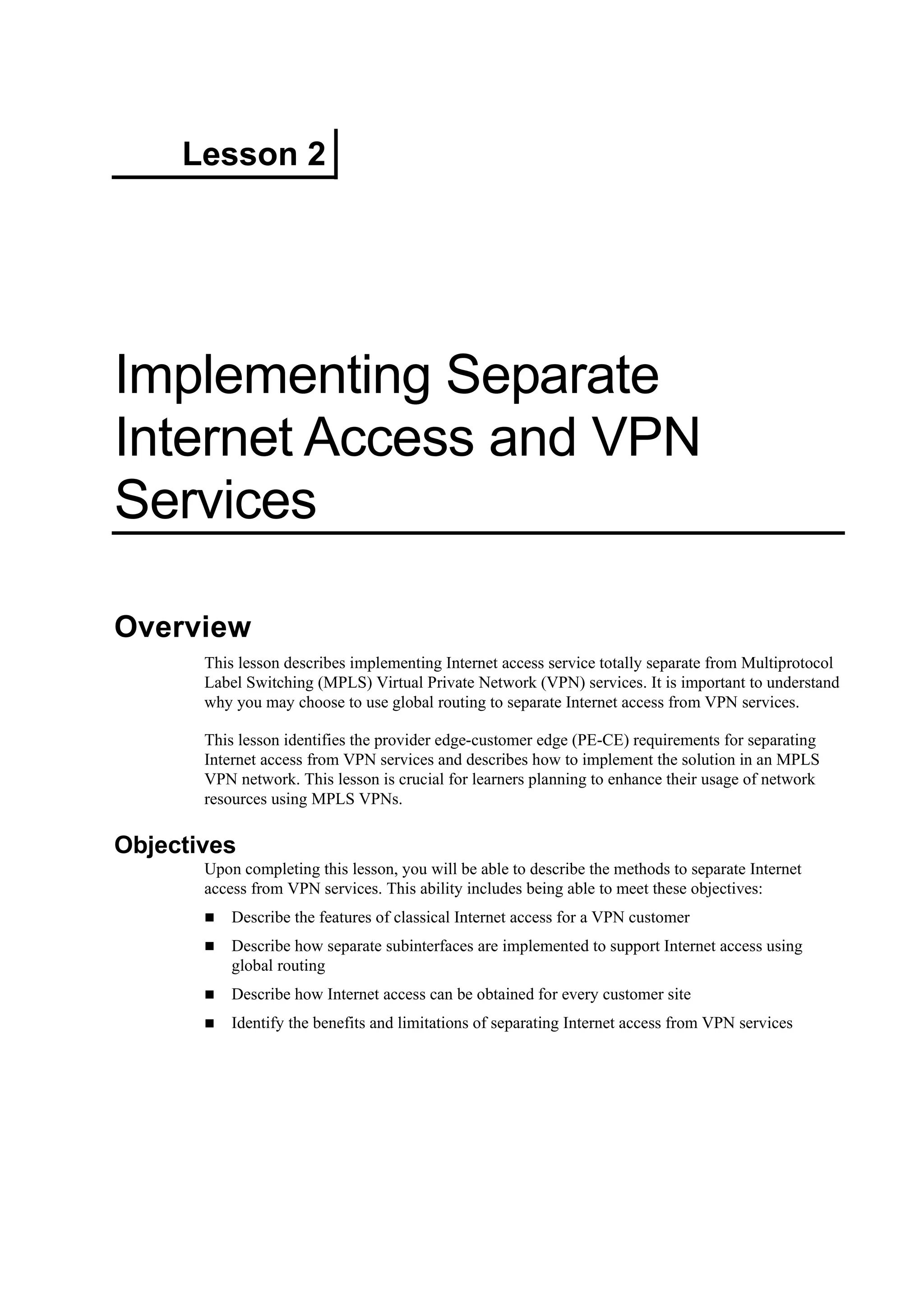
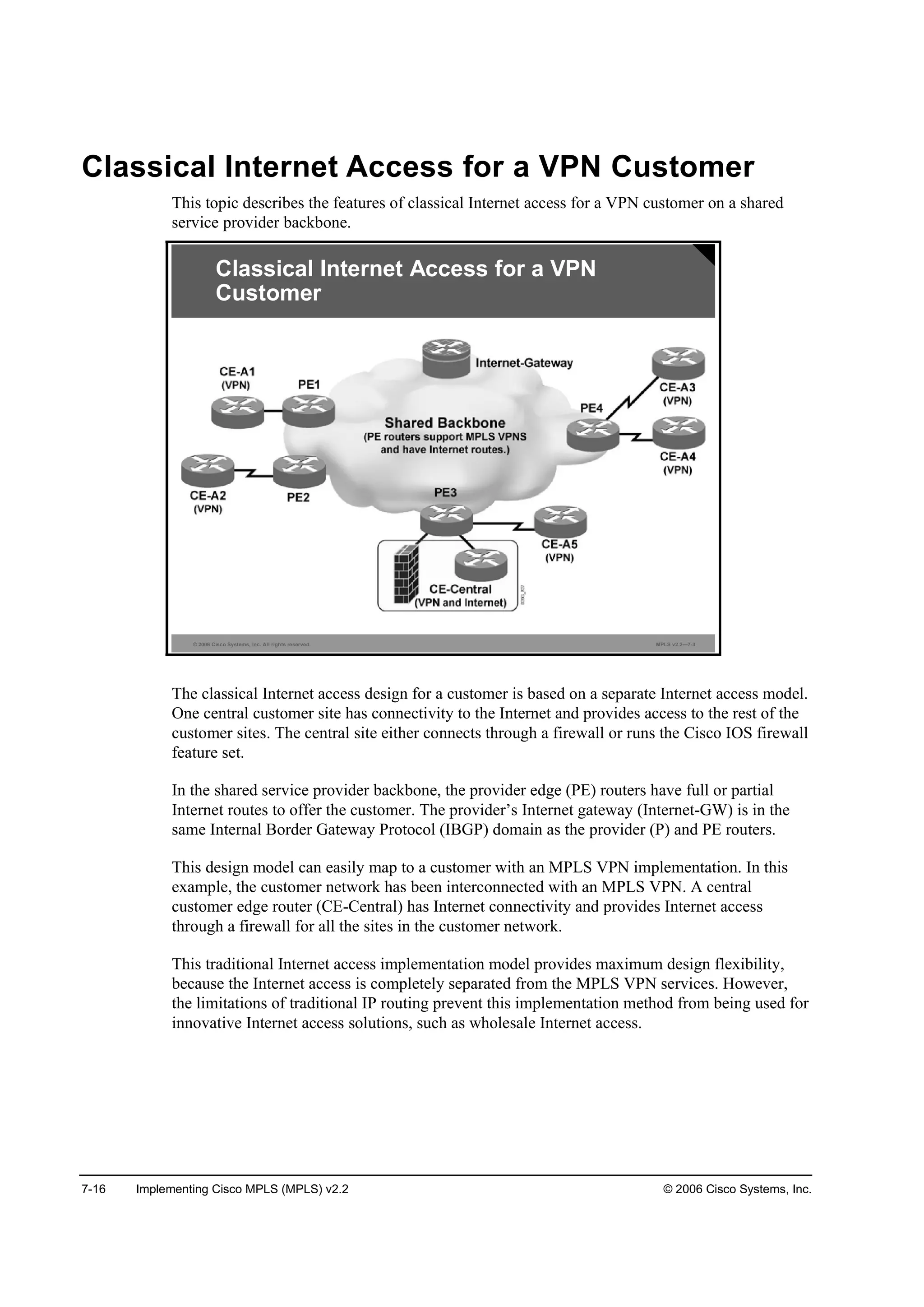
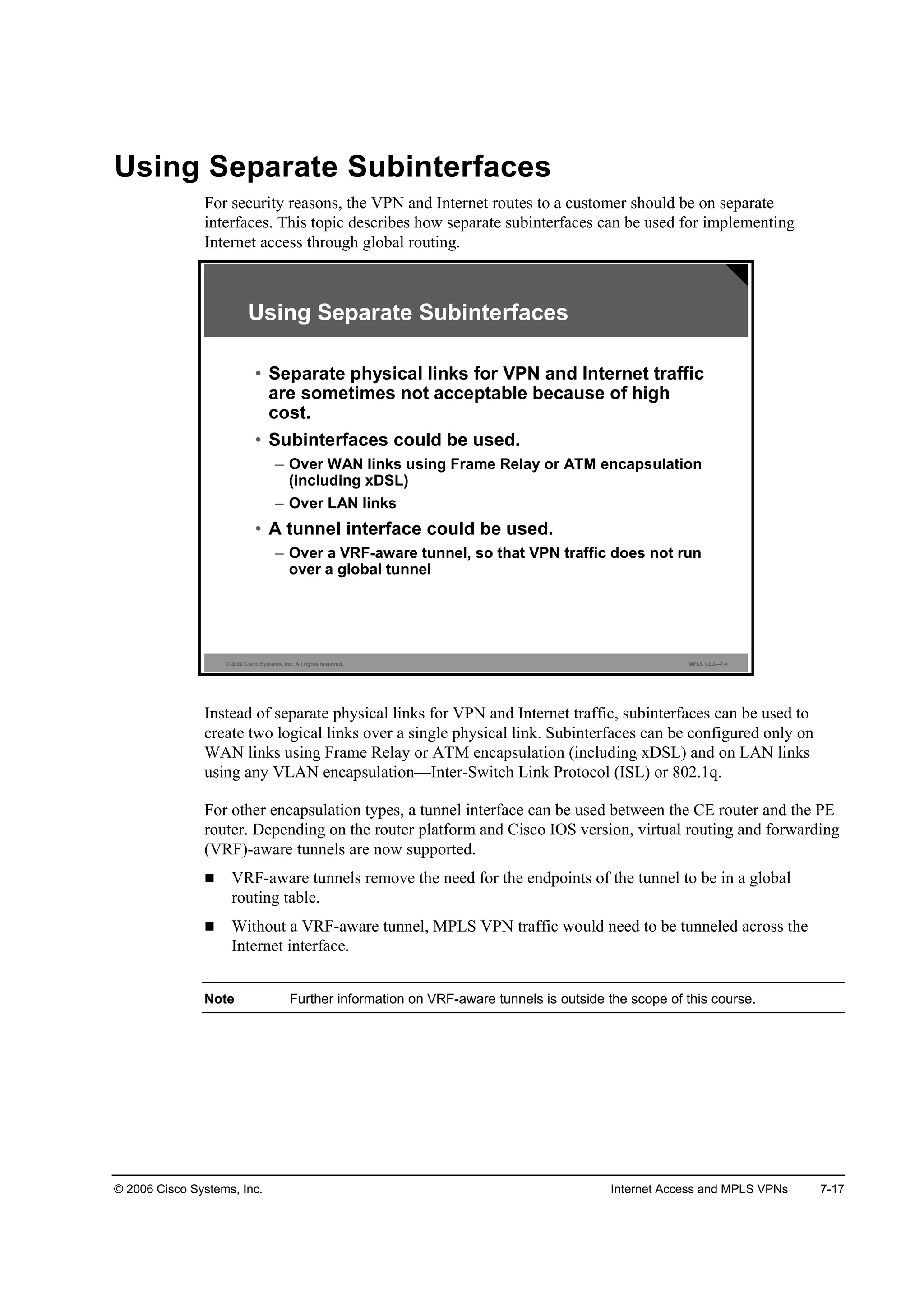
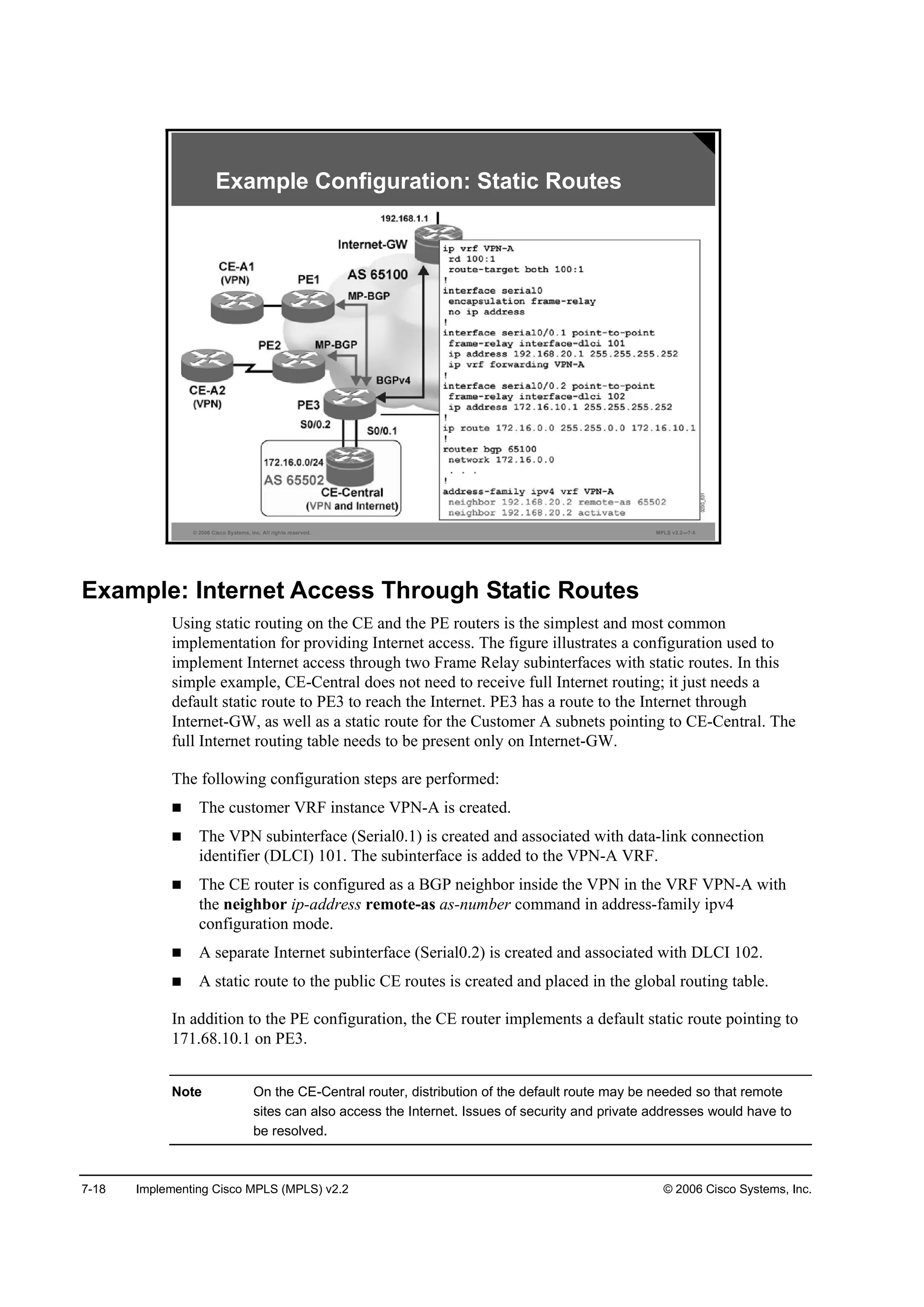
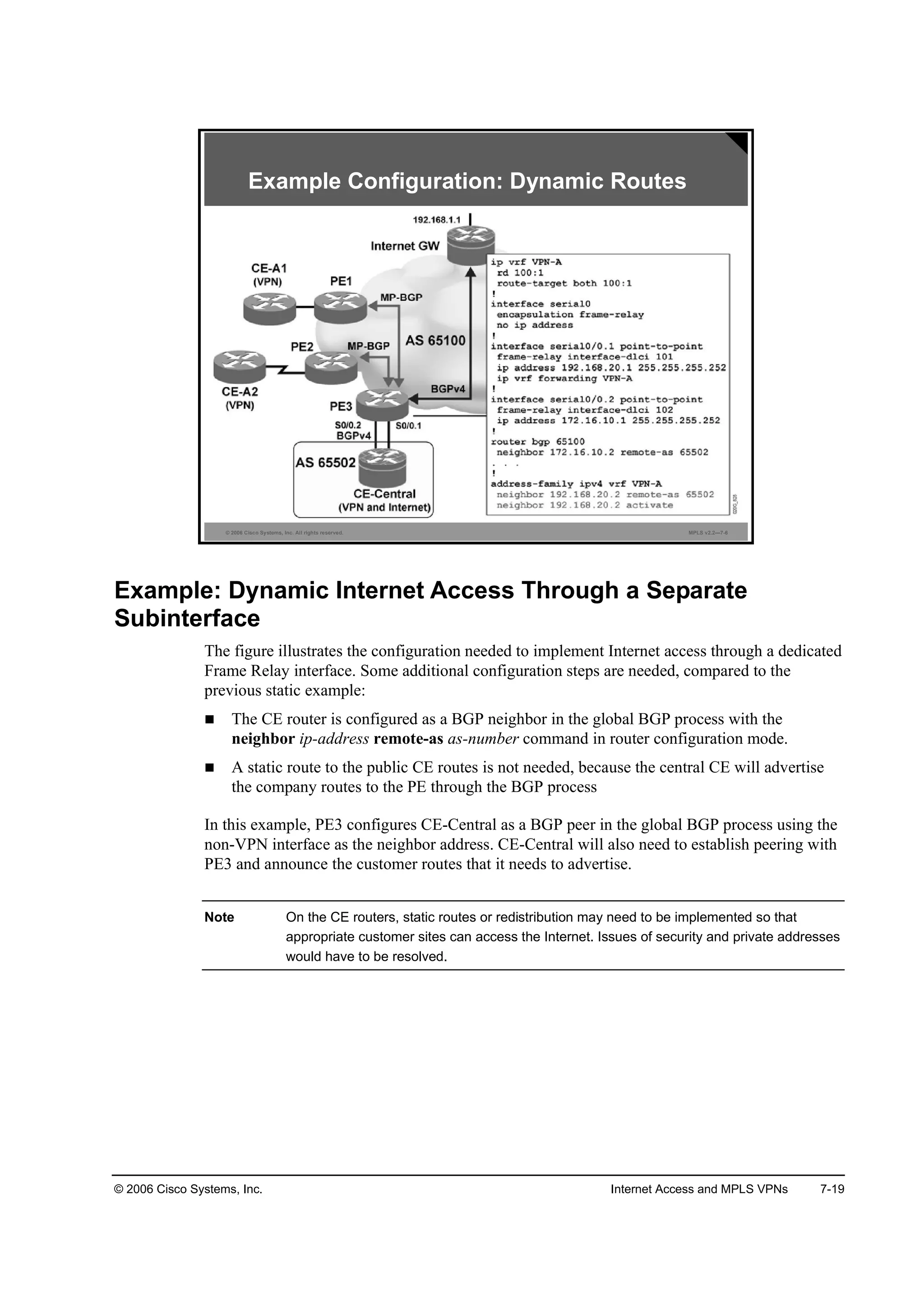
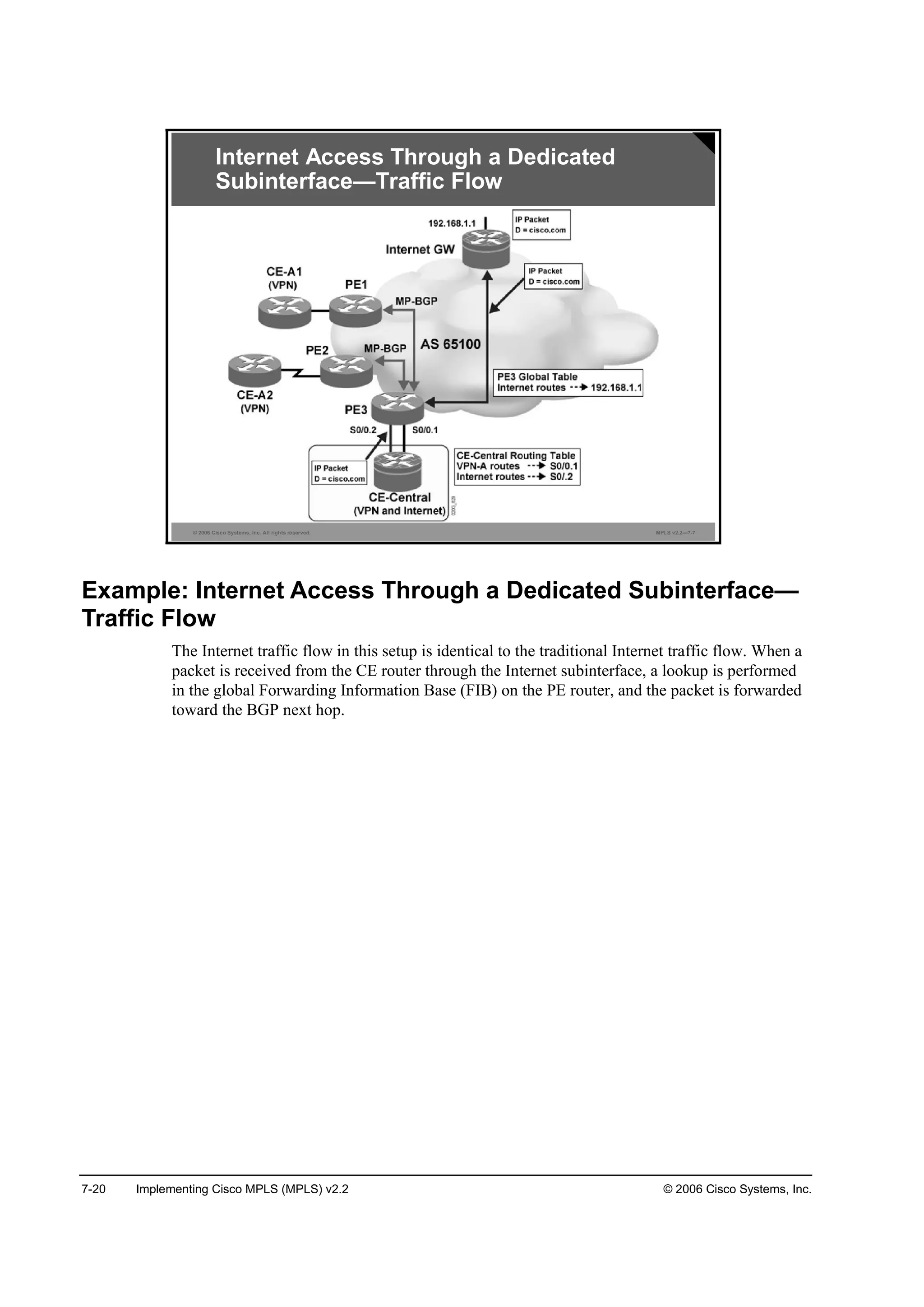
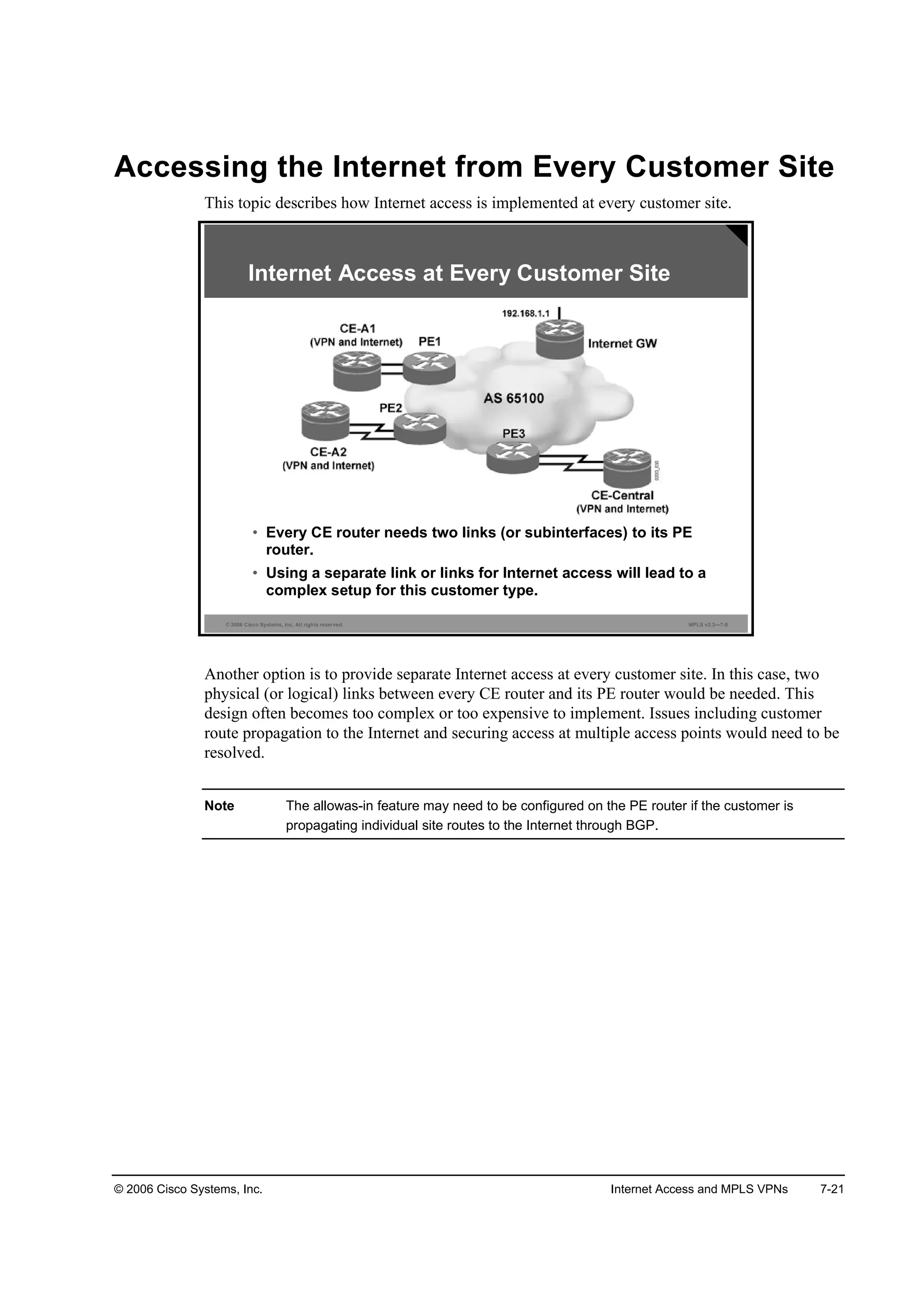

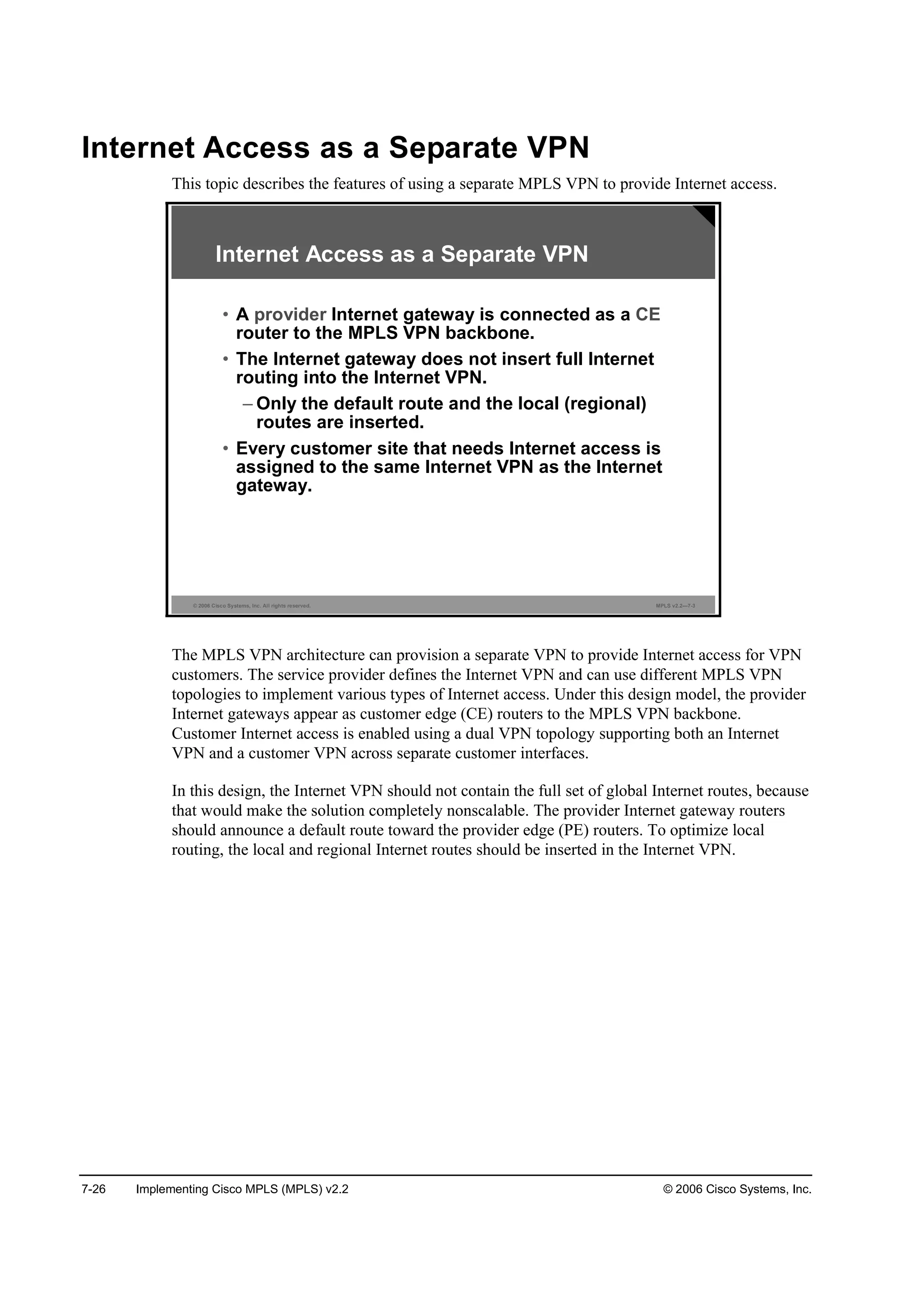
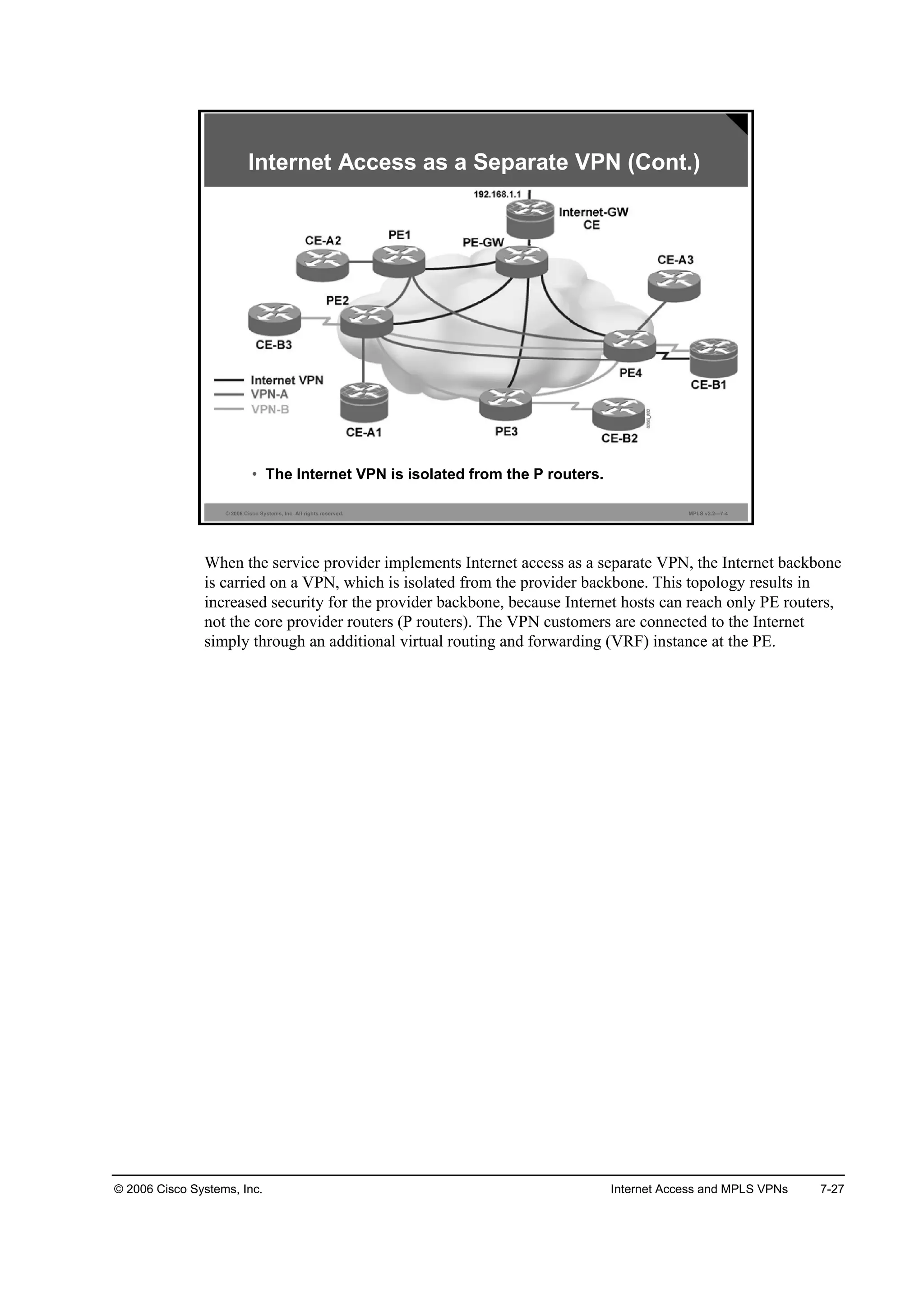
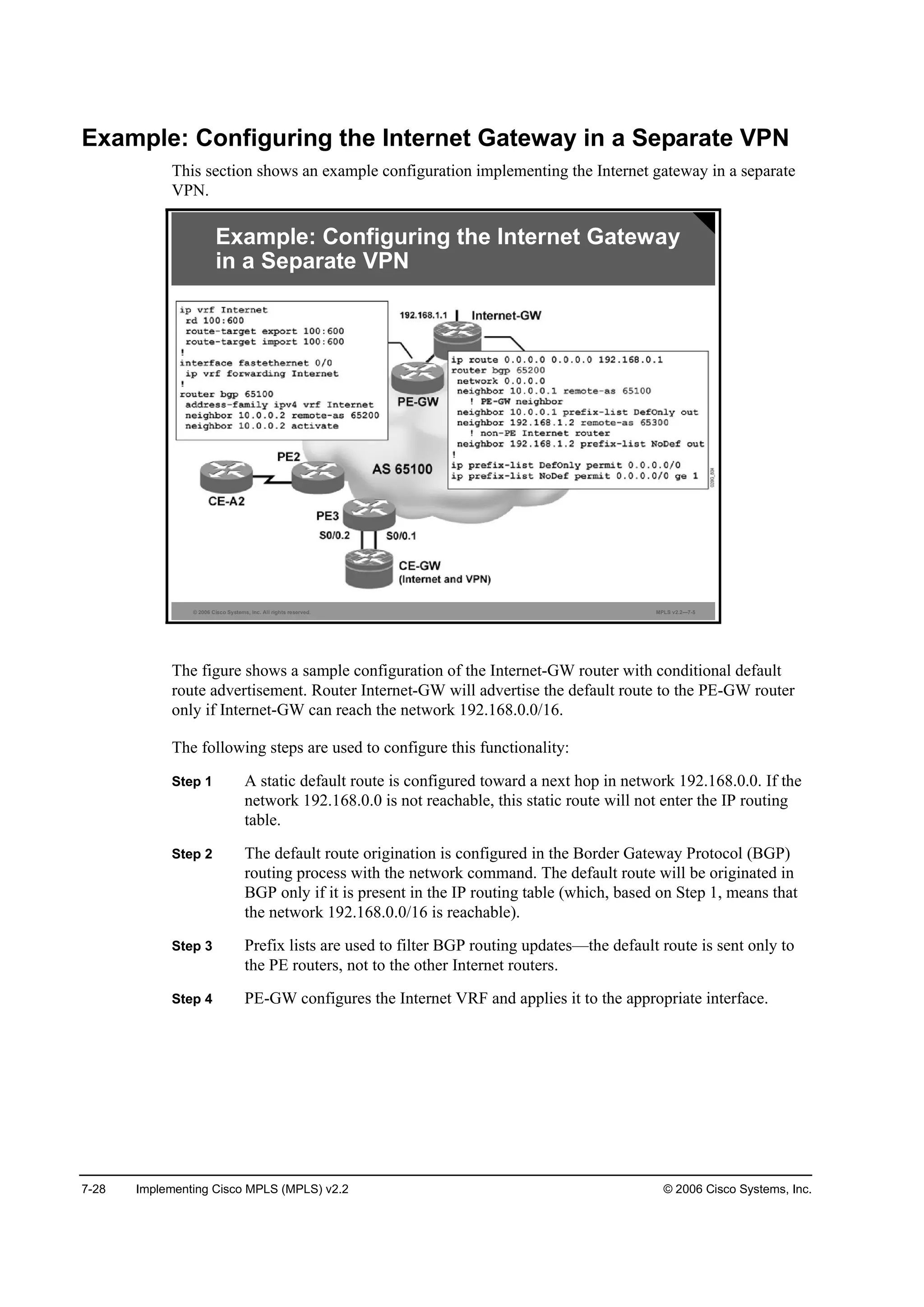
![© 2006 Cisco Systems, Inc. Internet Access and MPLS VPNs 7-29
Implementing Redundant Internet Access
This topic describes how to implement redundant Internet access.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—7-6
• The default route should be advertised by all Internet gateways
only if they can reach the upstream ISP core.
Redundant Internet Access
Redundant Internet access is easy to achieve when the Internet service is implemented as a
VPN in the MPLS VPN backbone:
Multiple Internet gateways (acting as CE routers) have to be connected to the MPLS VPN
backbone to ensure router and link redundancy.
All Internet gateways advertise the default route to the PE routers, resulting in routing
redundancy.
The Internet gateways also announce local Internet routes. Because these routes are
announced with different BGP attributes (most notably, multi-exit discriminator [MED]),
the PE routers select the proper Internet-GW router as the exit point toward those
destinations.
The MED attribute can also be used to indicate the preferred default route to the PE routers.
In this setup, one Internet-GW router acts as a primary Internet gateway, and the other
Internet-GW router acts as a backup.
The redundancy established so far covers the path between customer sites and the
Internet-GW routers. A failure in the Internet backbone might break the Internet
connectivity for the customers if the Internet-GW routers announce the default route
unconditionally. Conditional advertisement of the default route is therefore configured on
the Internet-GW routers—the Internet-GW routers announce the default route to the PE
routers only if the Internet-GW routers can reach an upstream destination.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-582-2048.jpg)
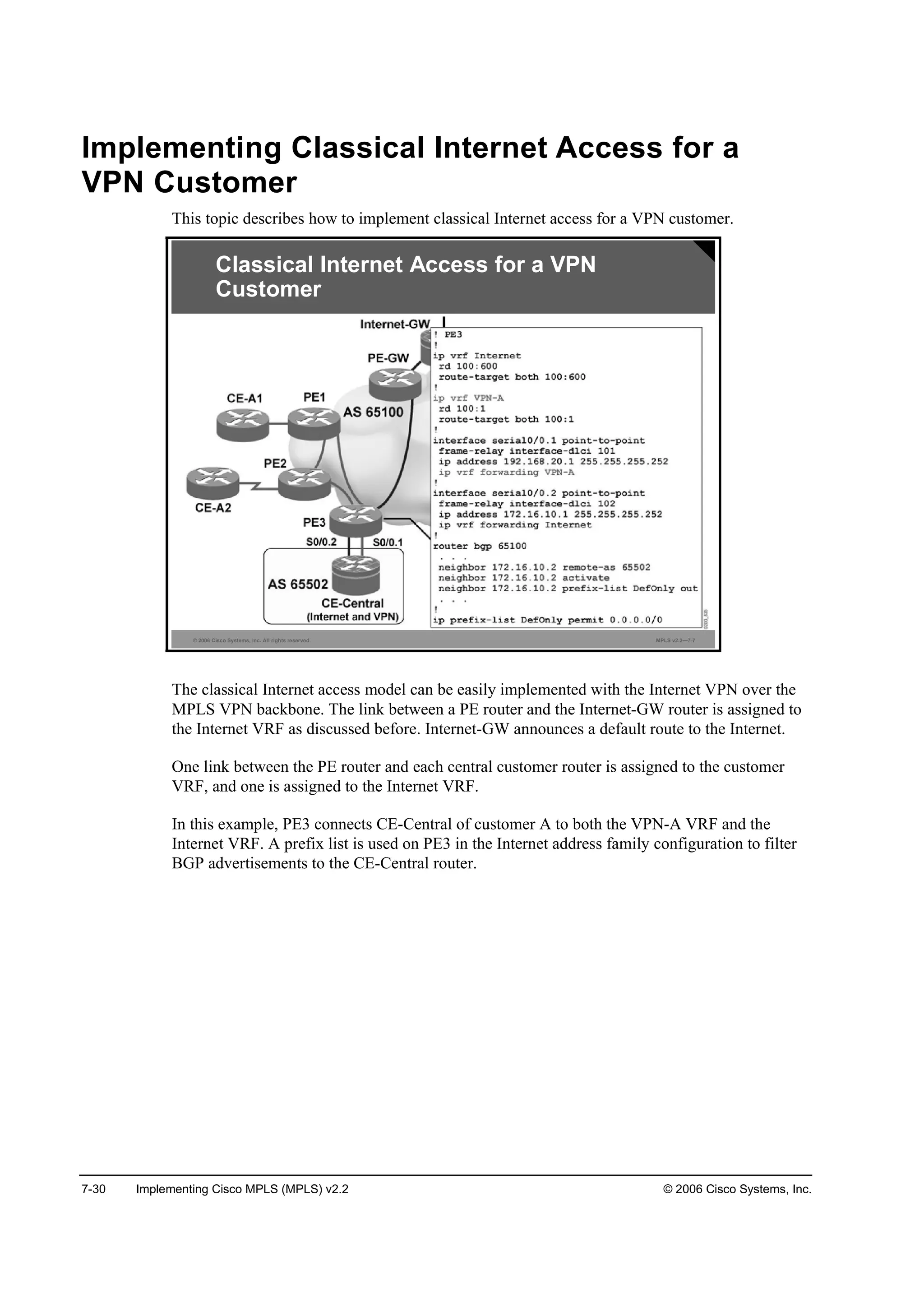
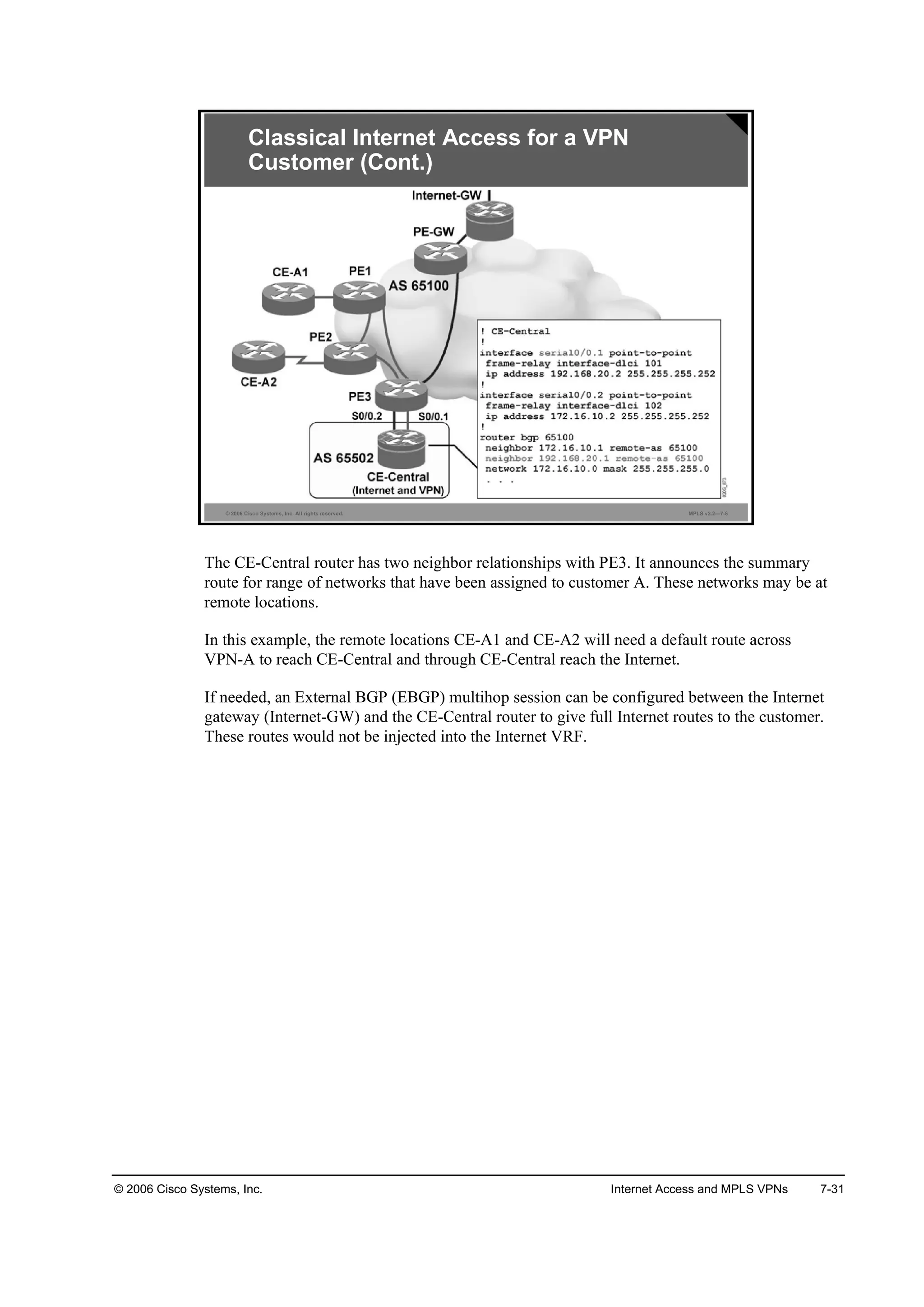
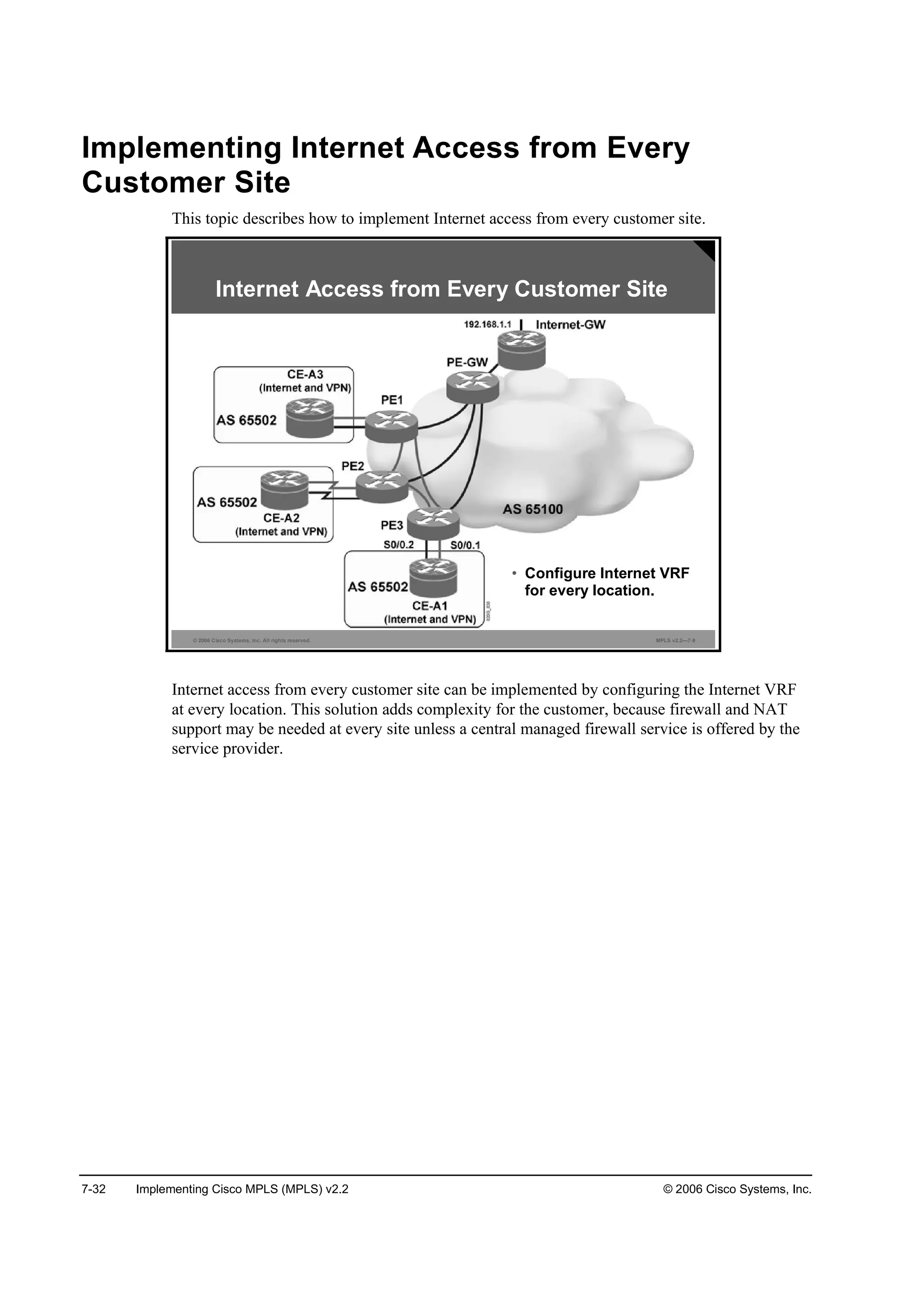
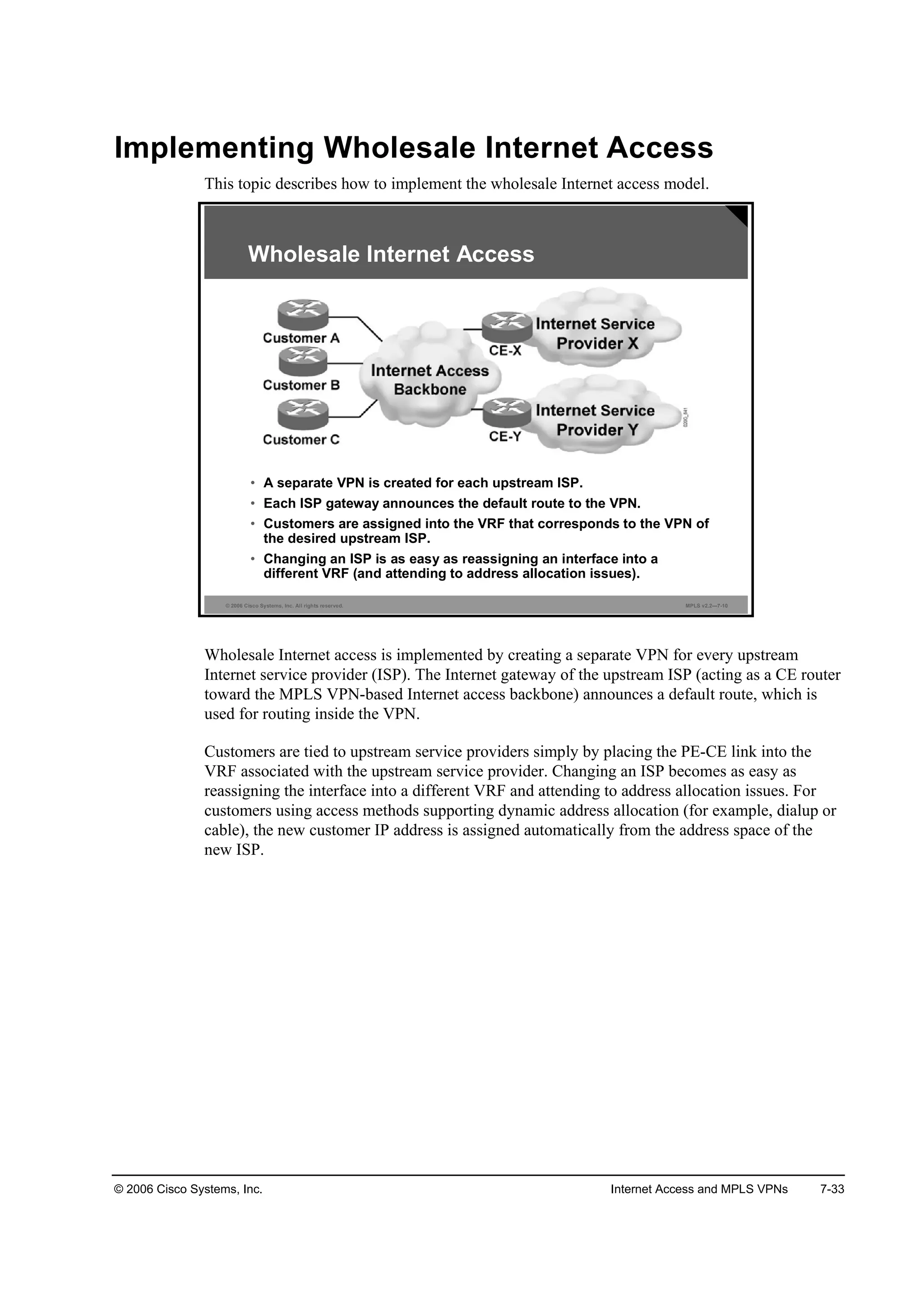
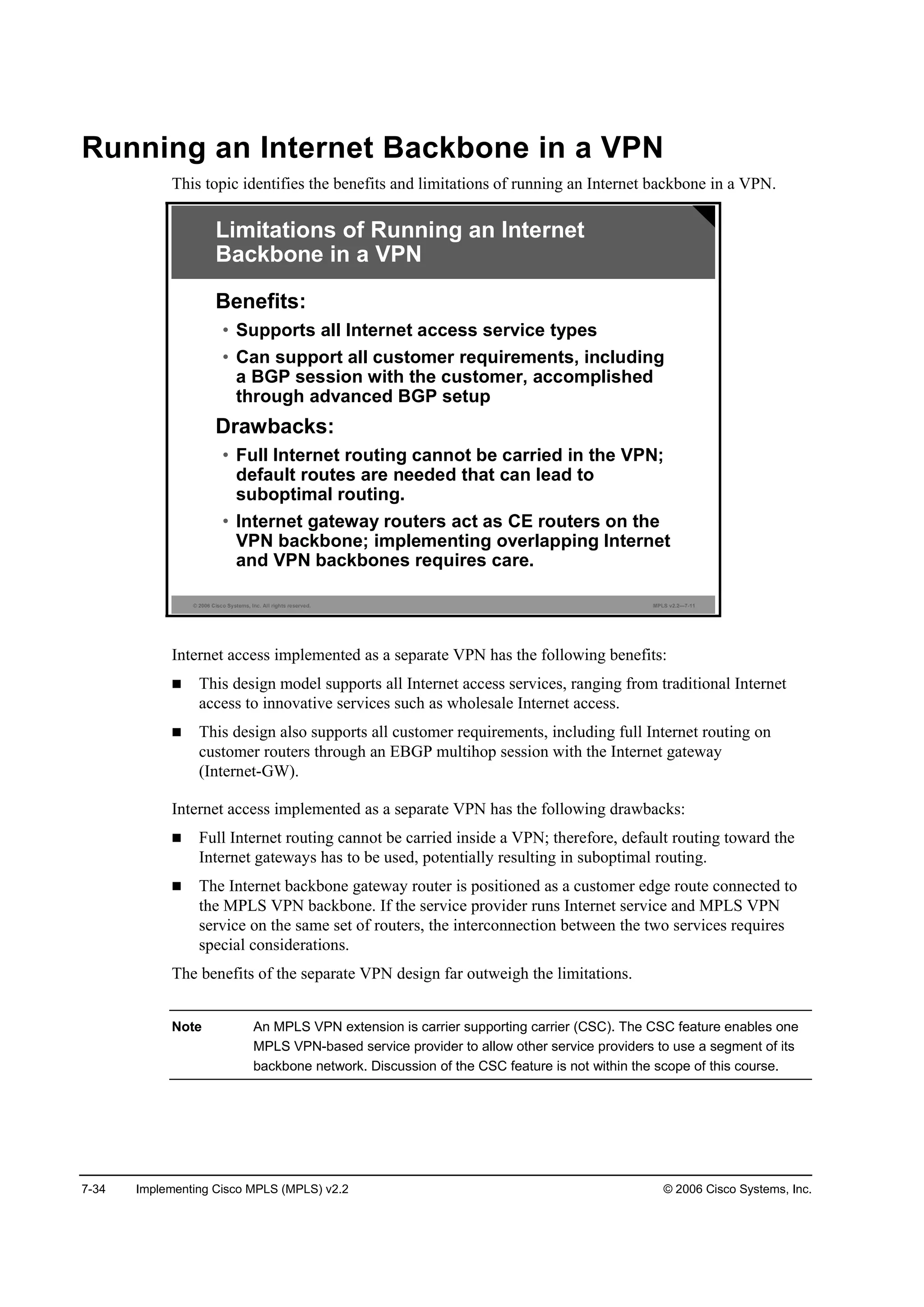

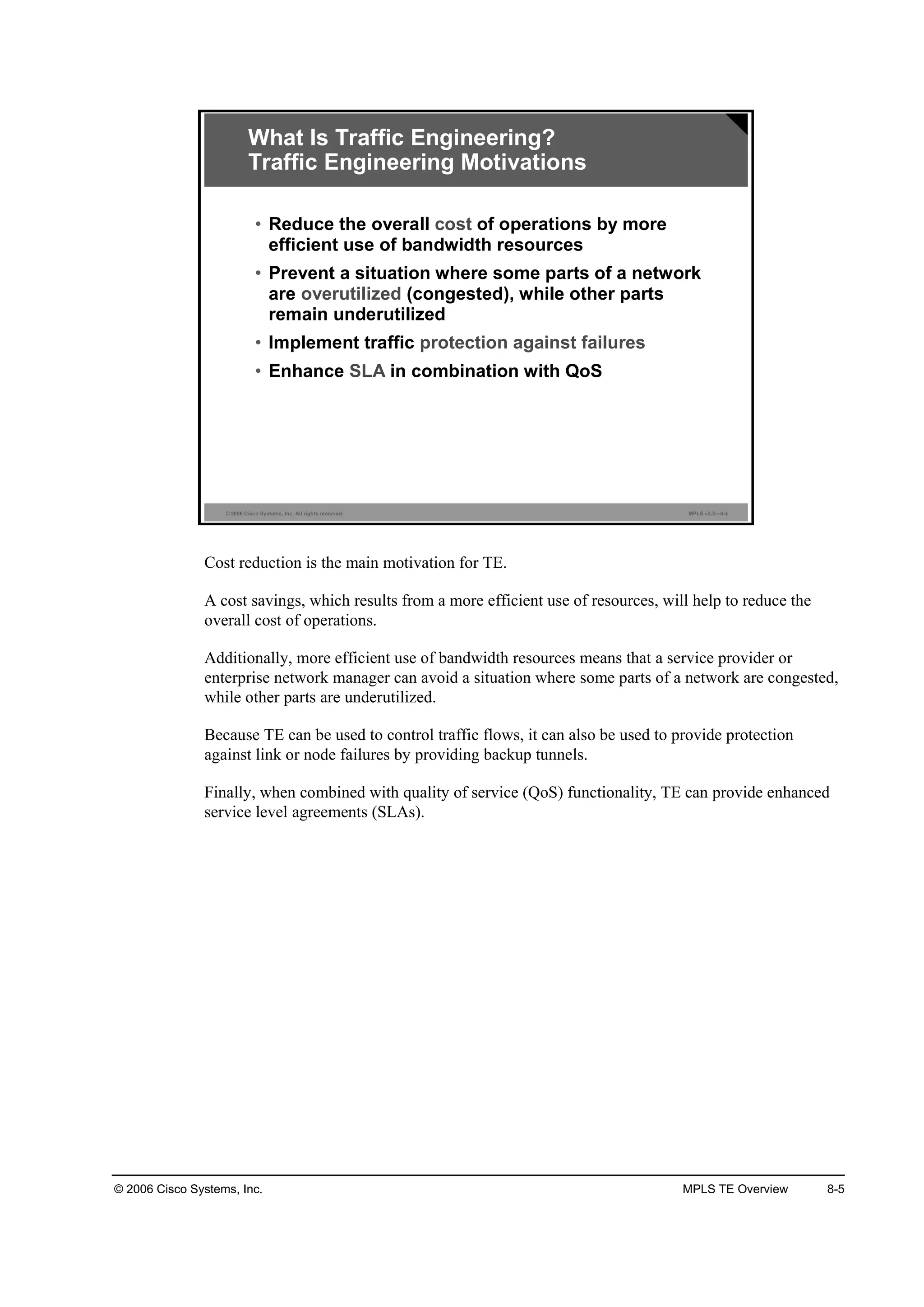
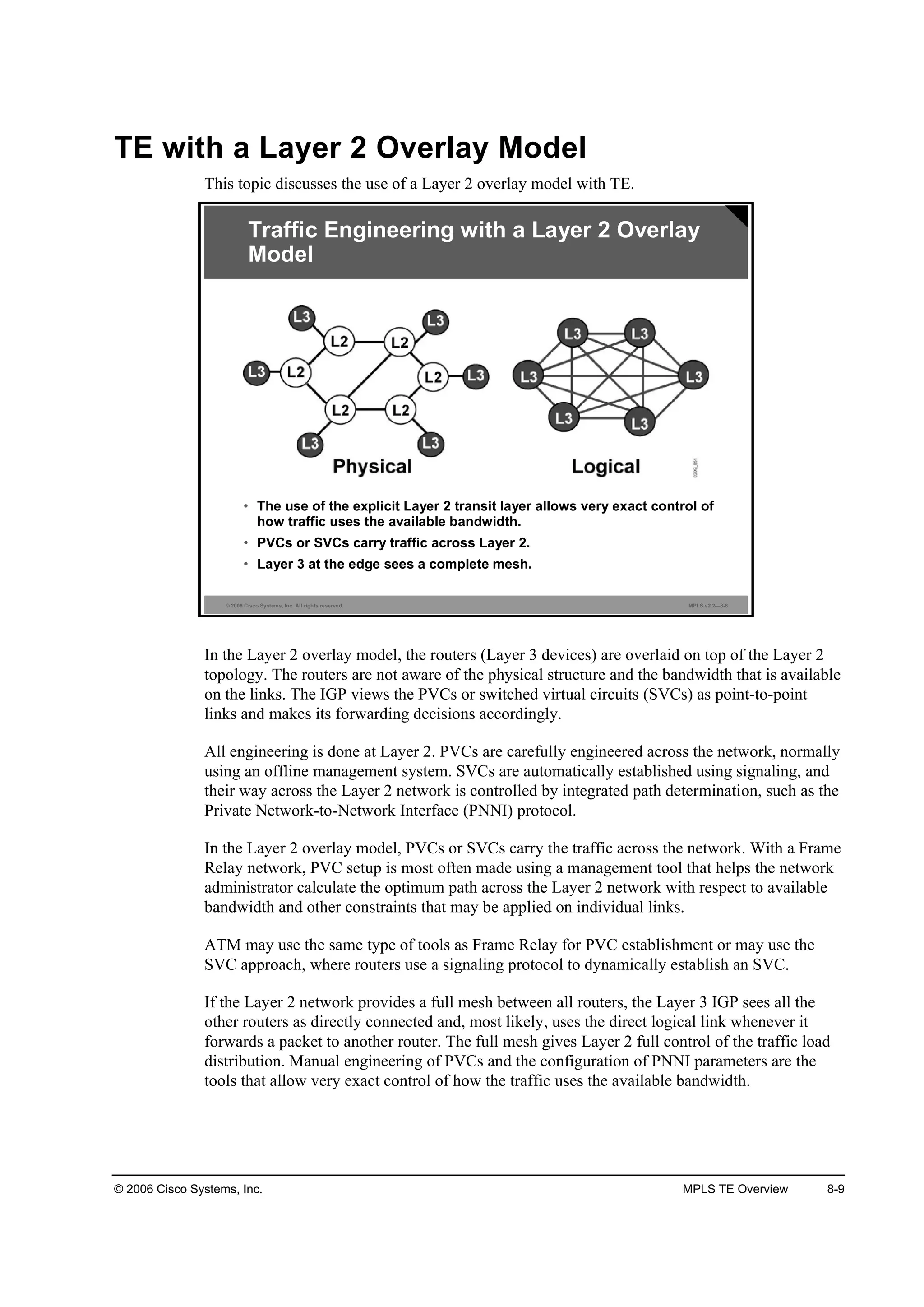
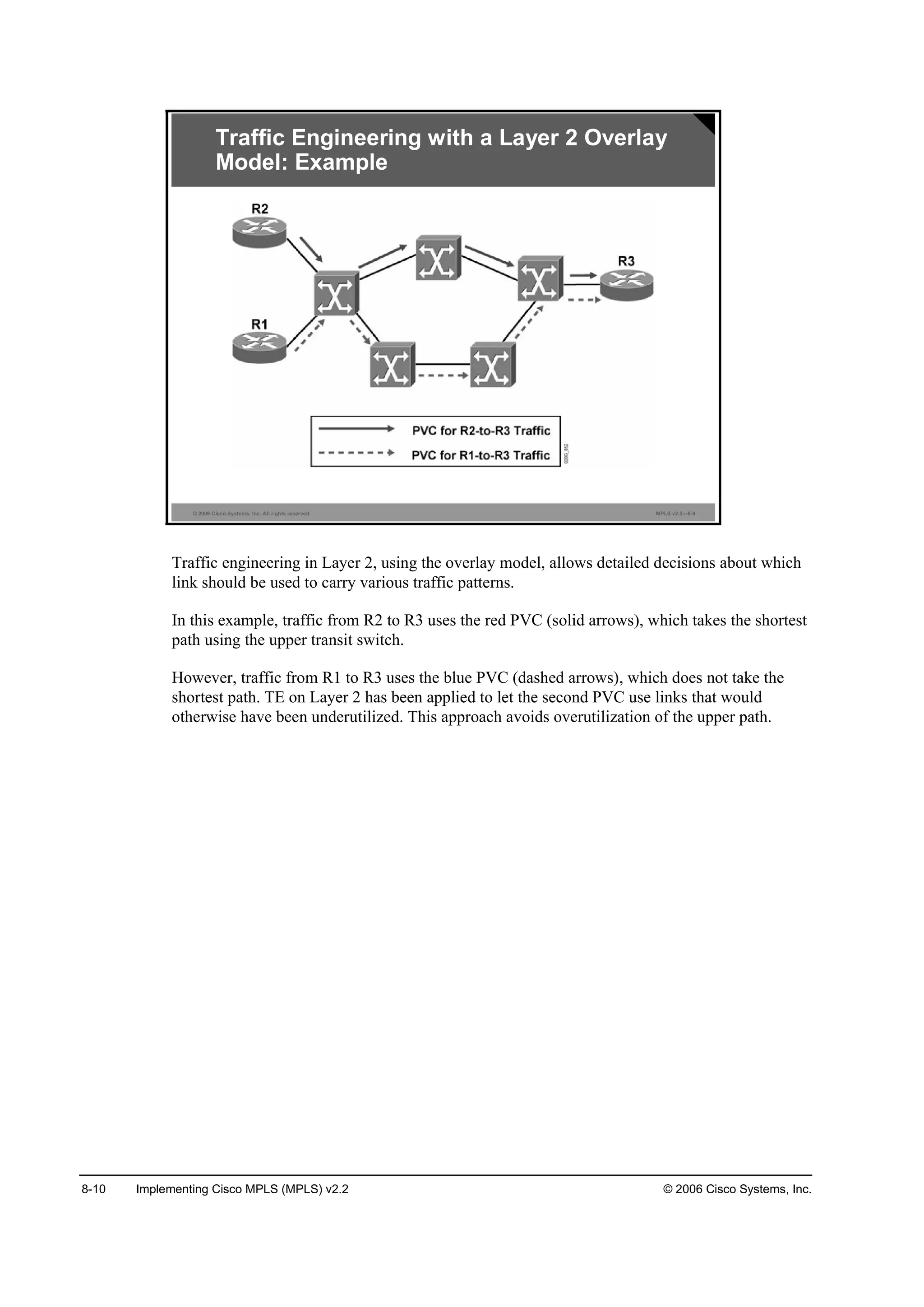
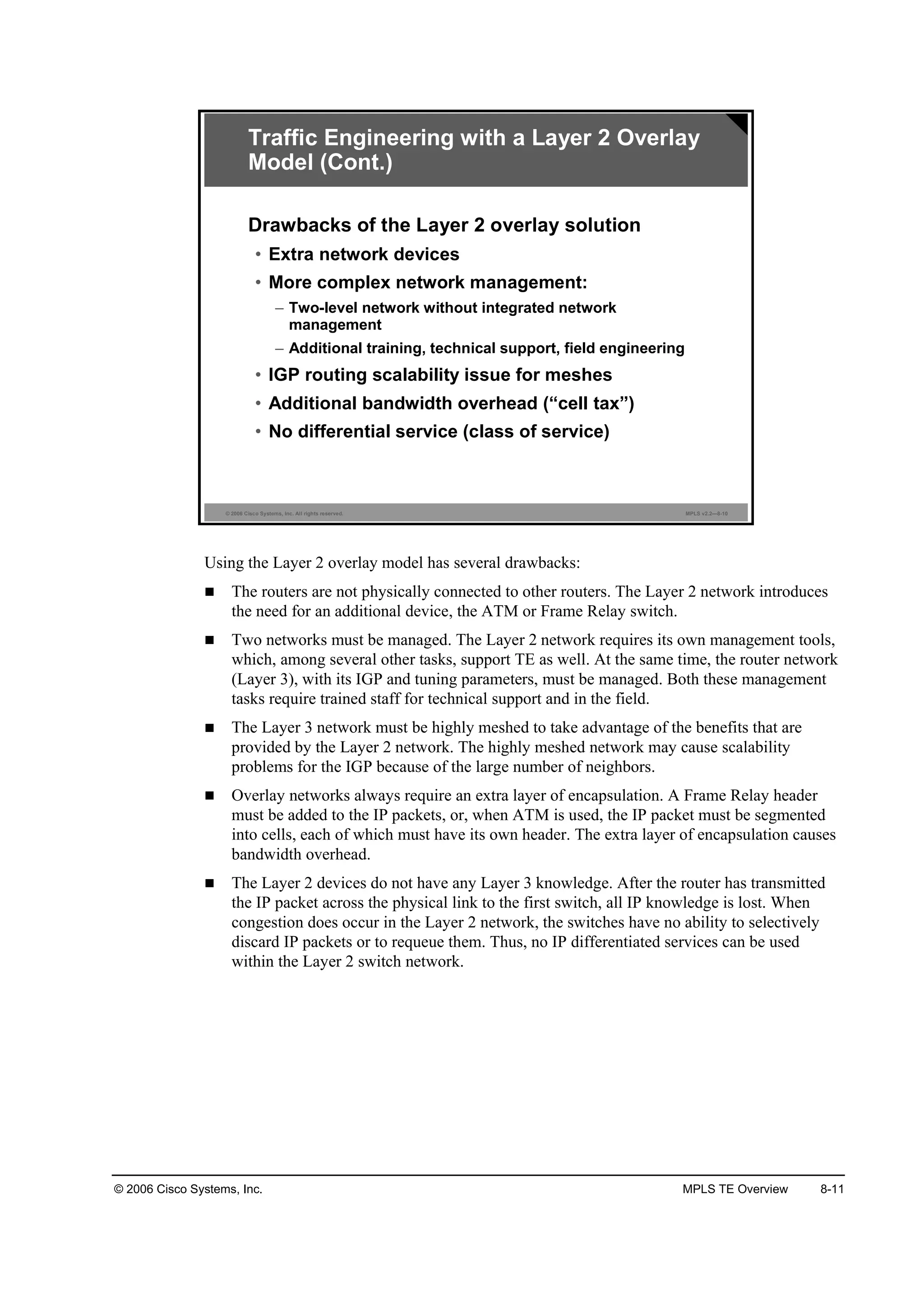
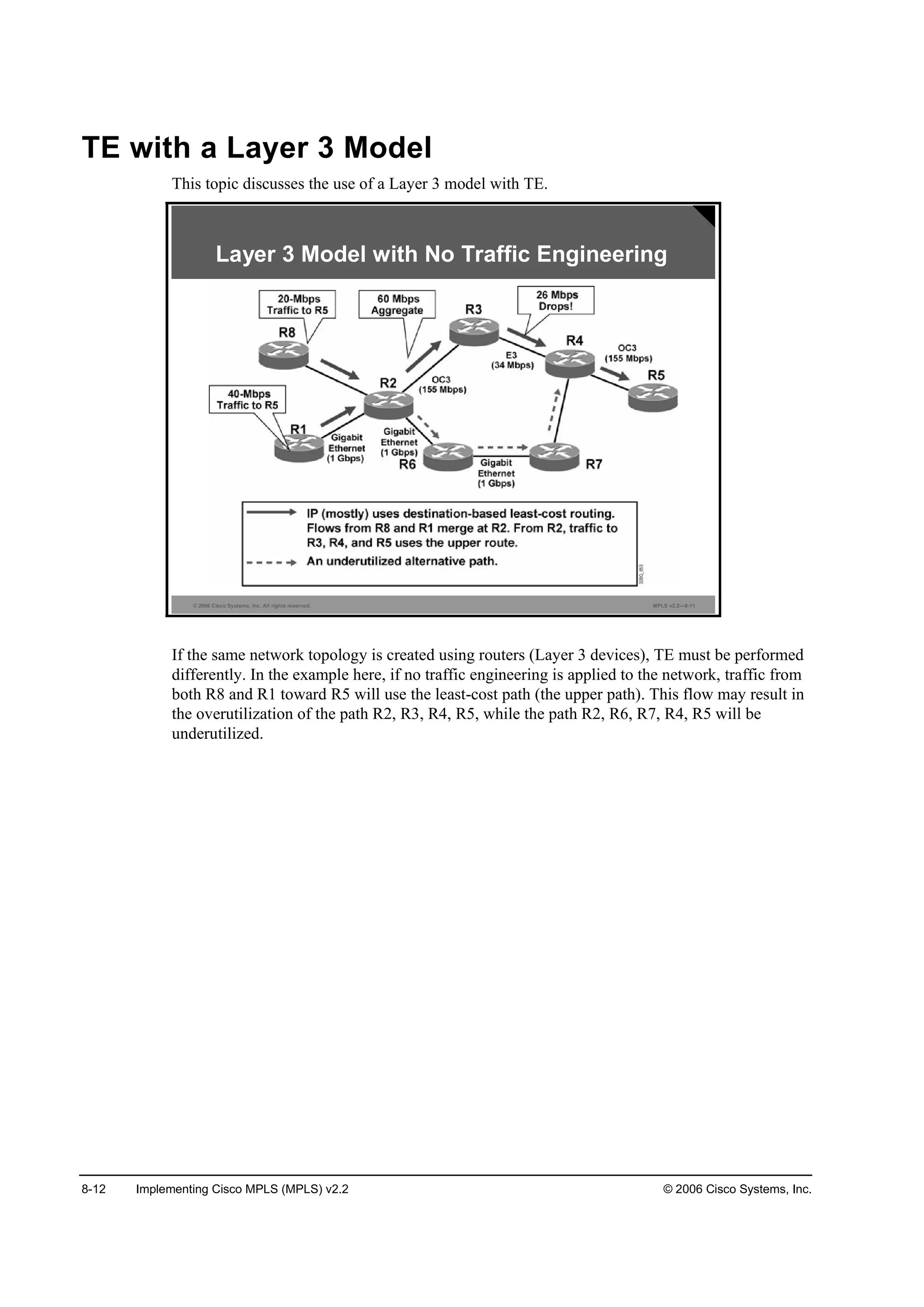
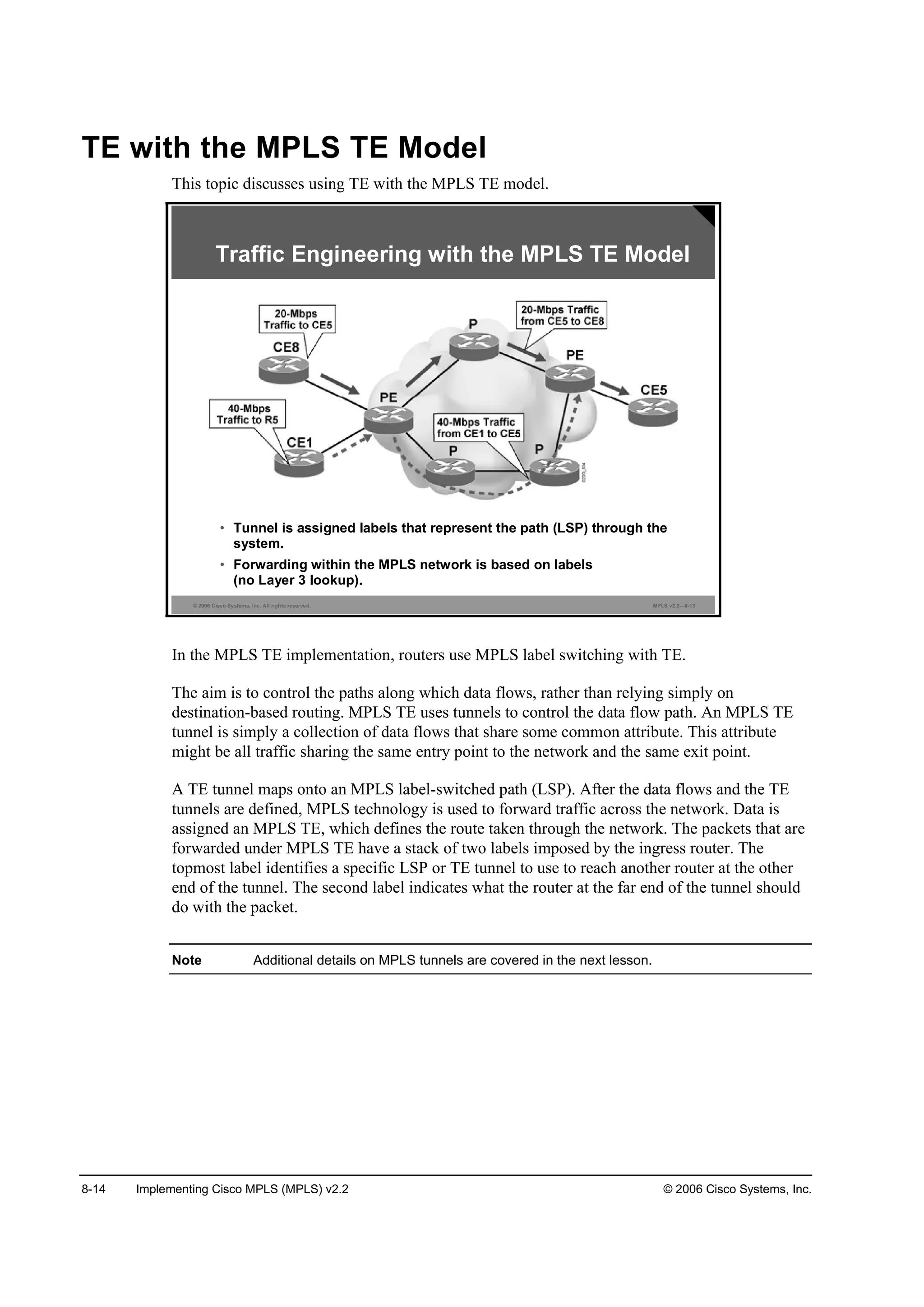
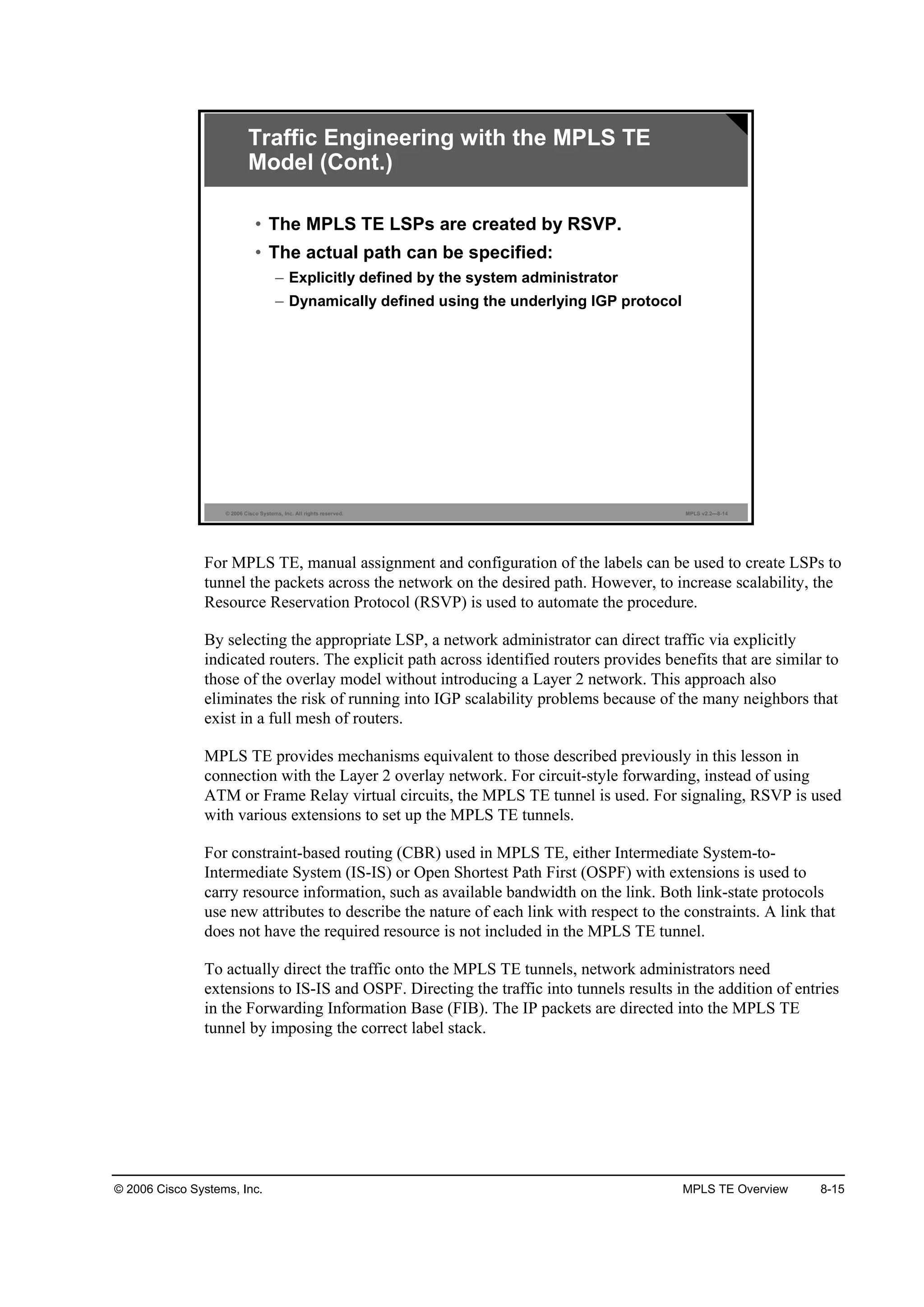
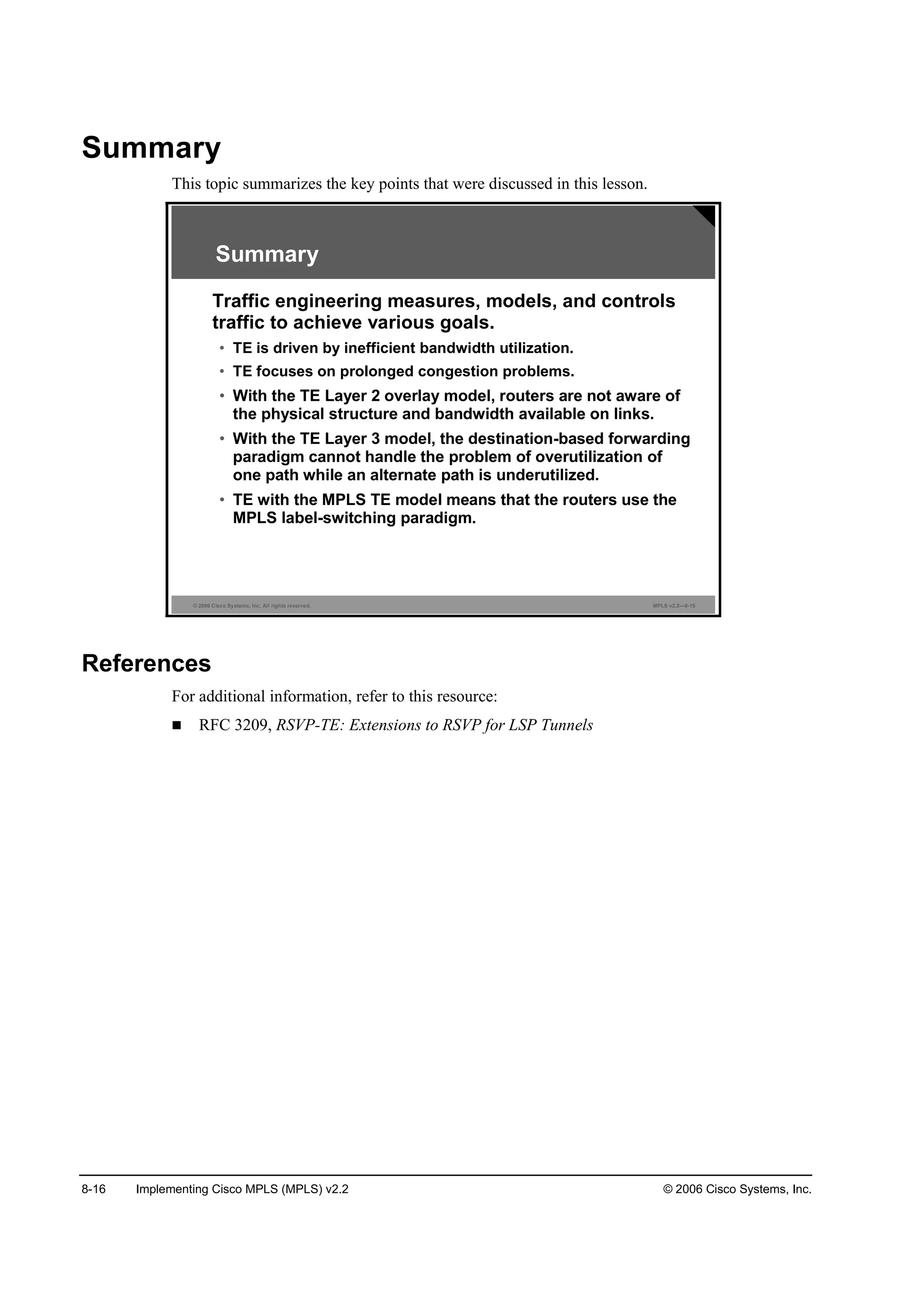
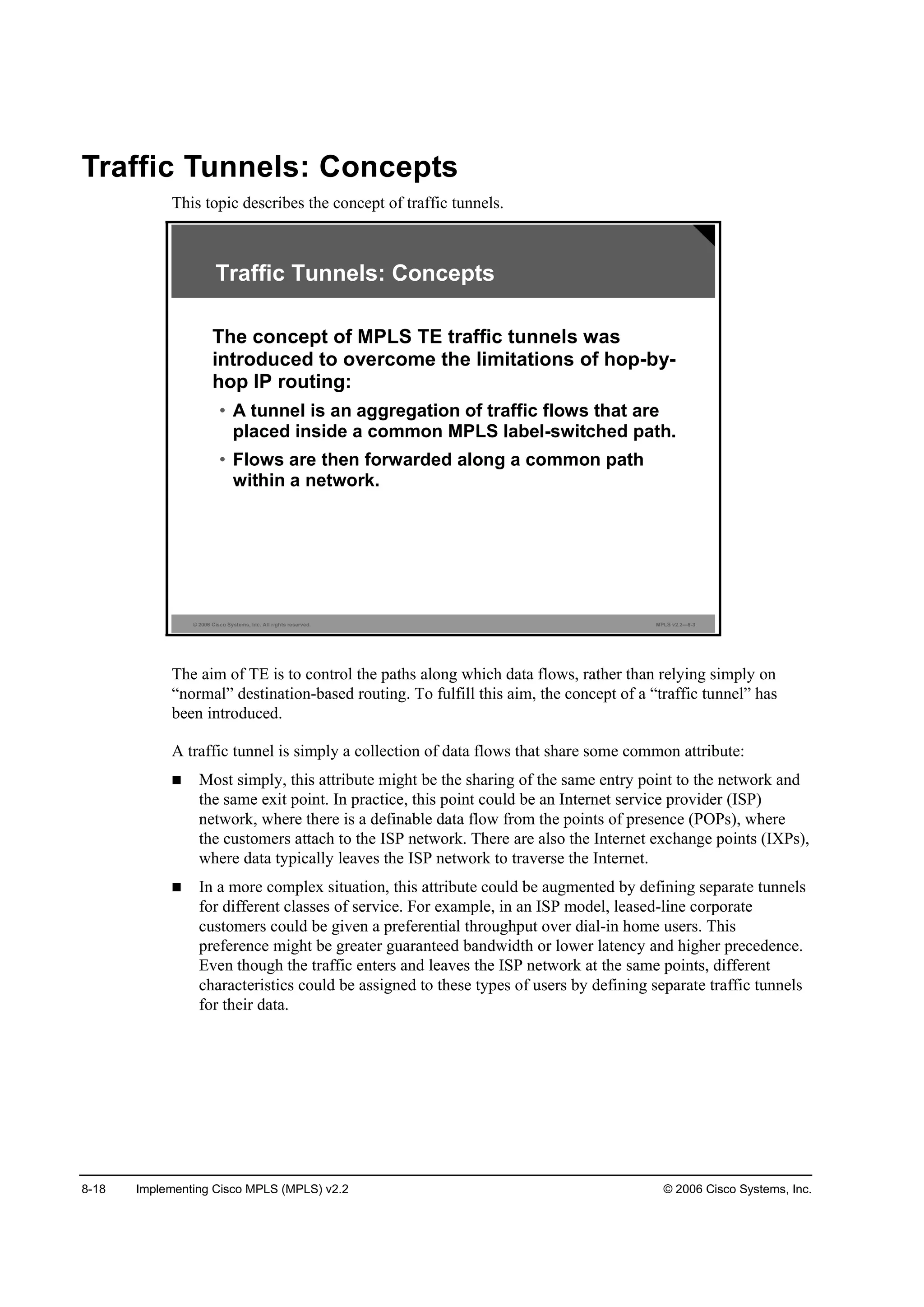
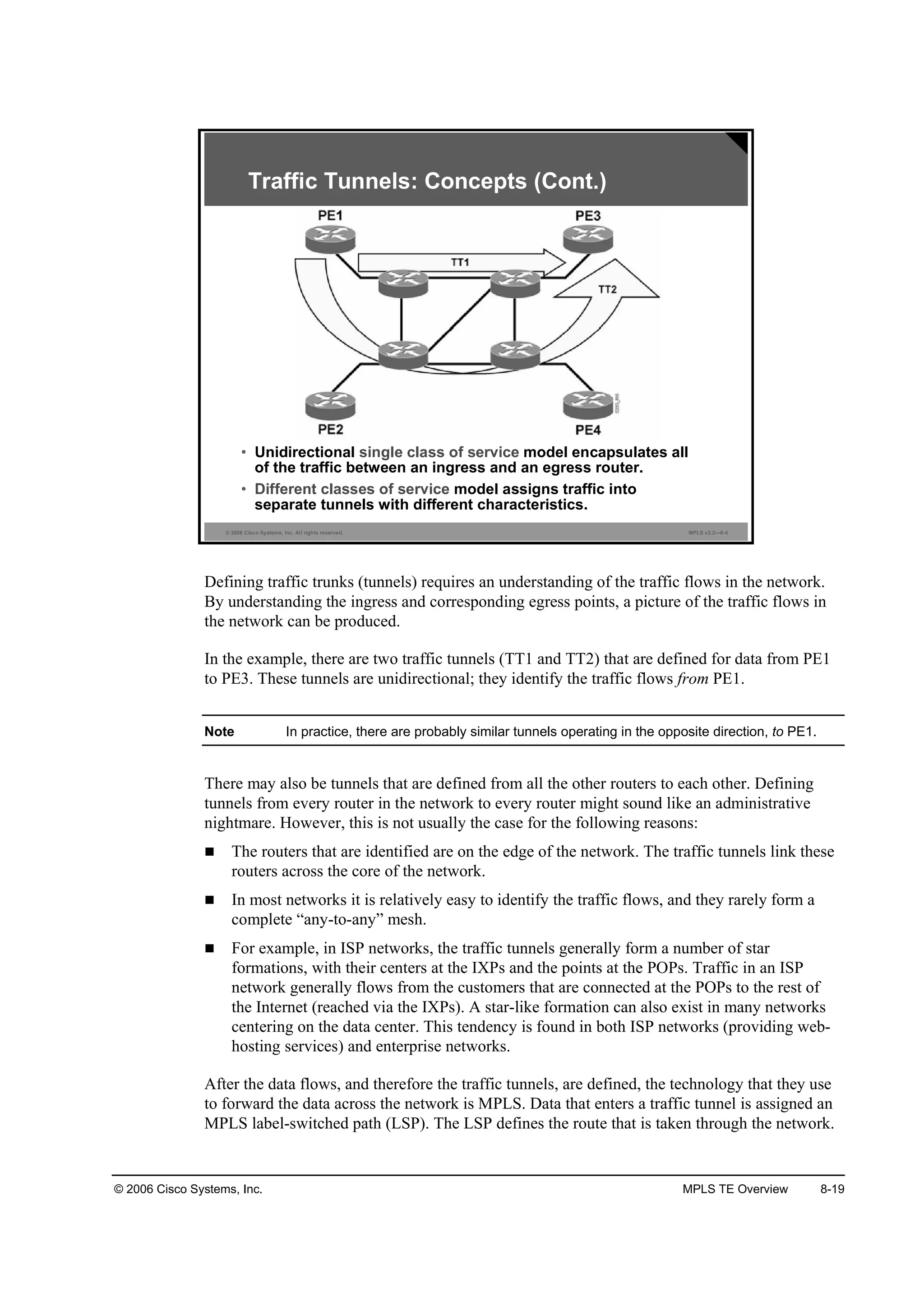
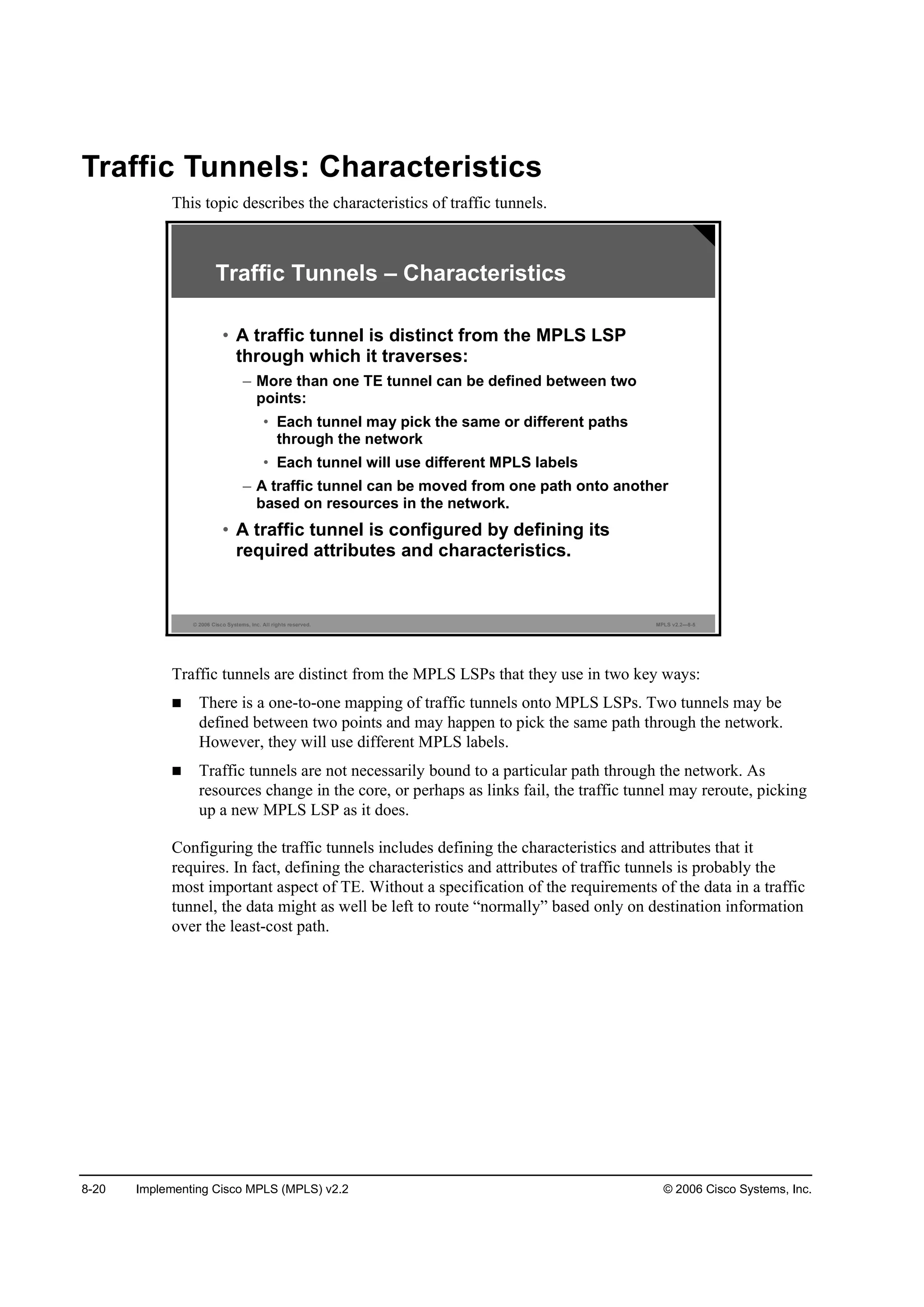
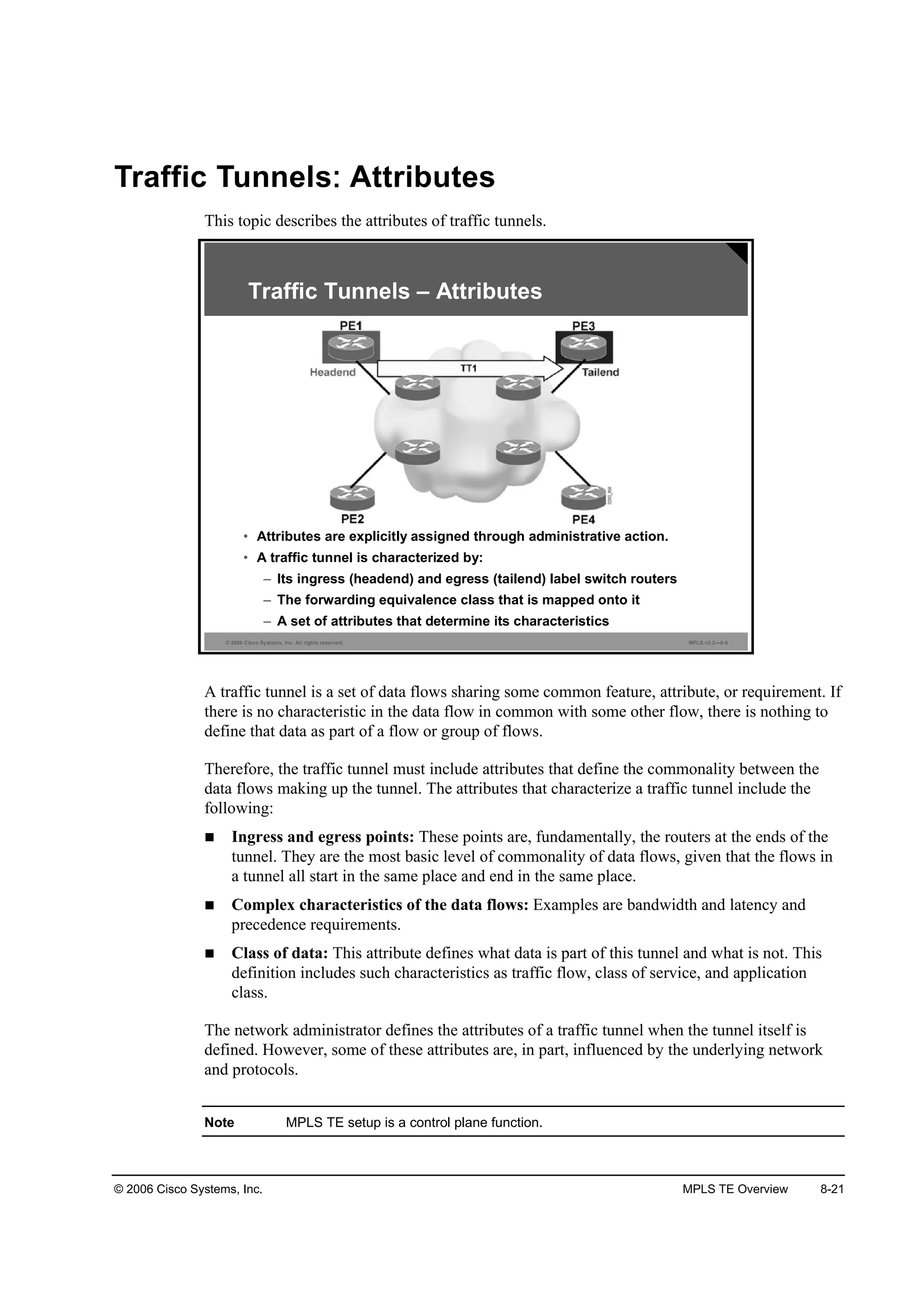
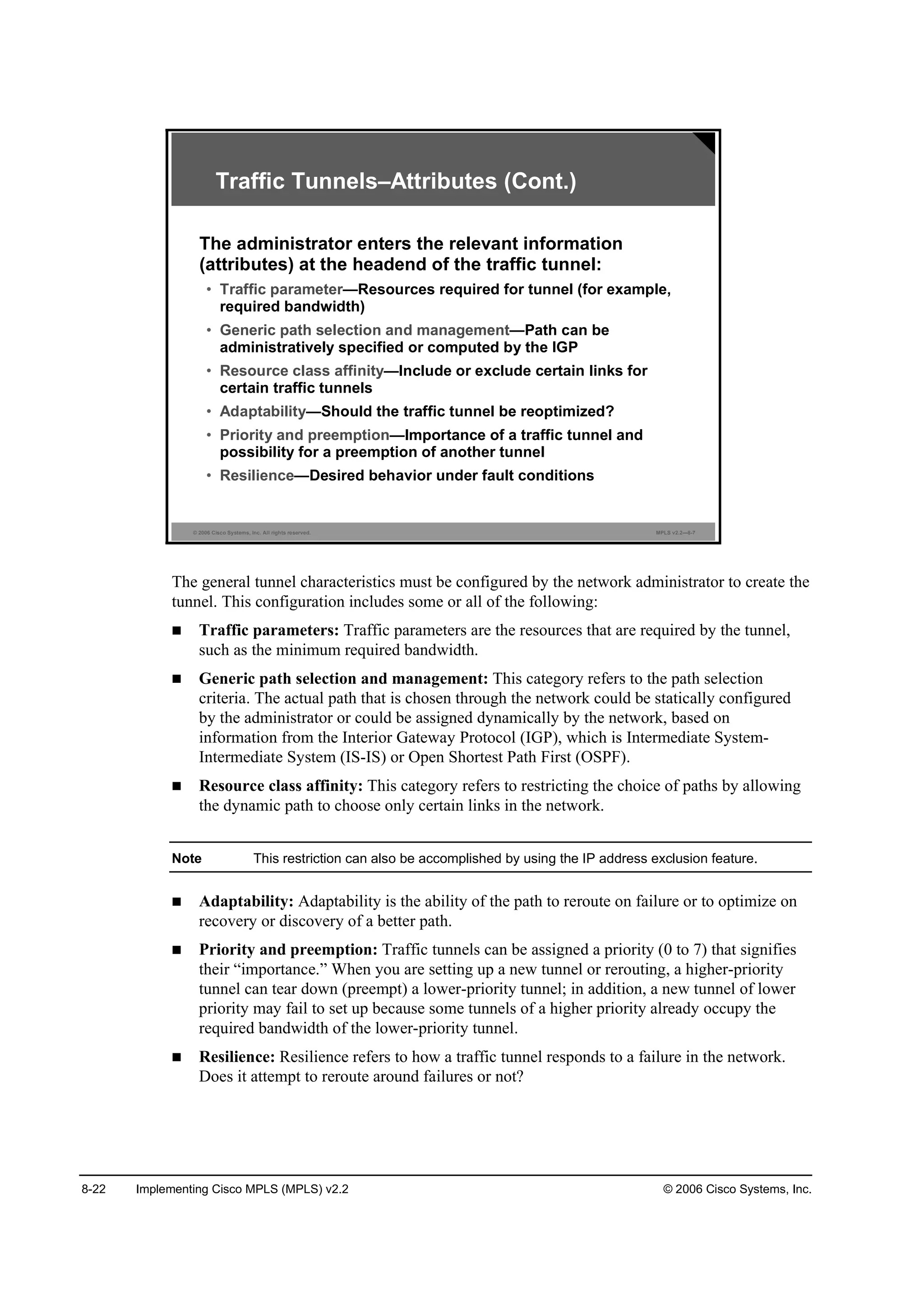
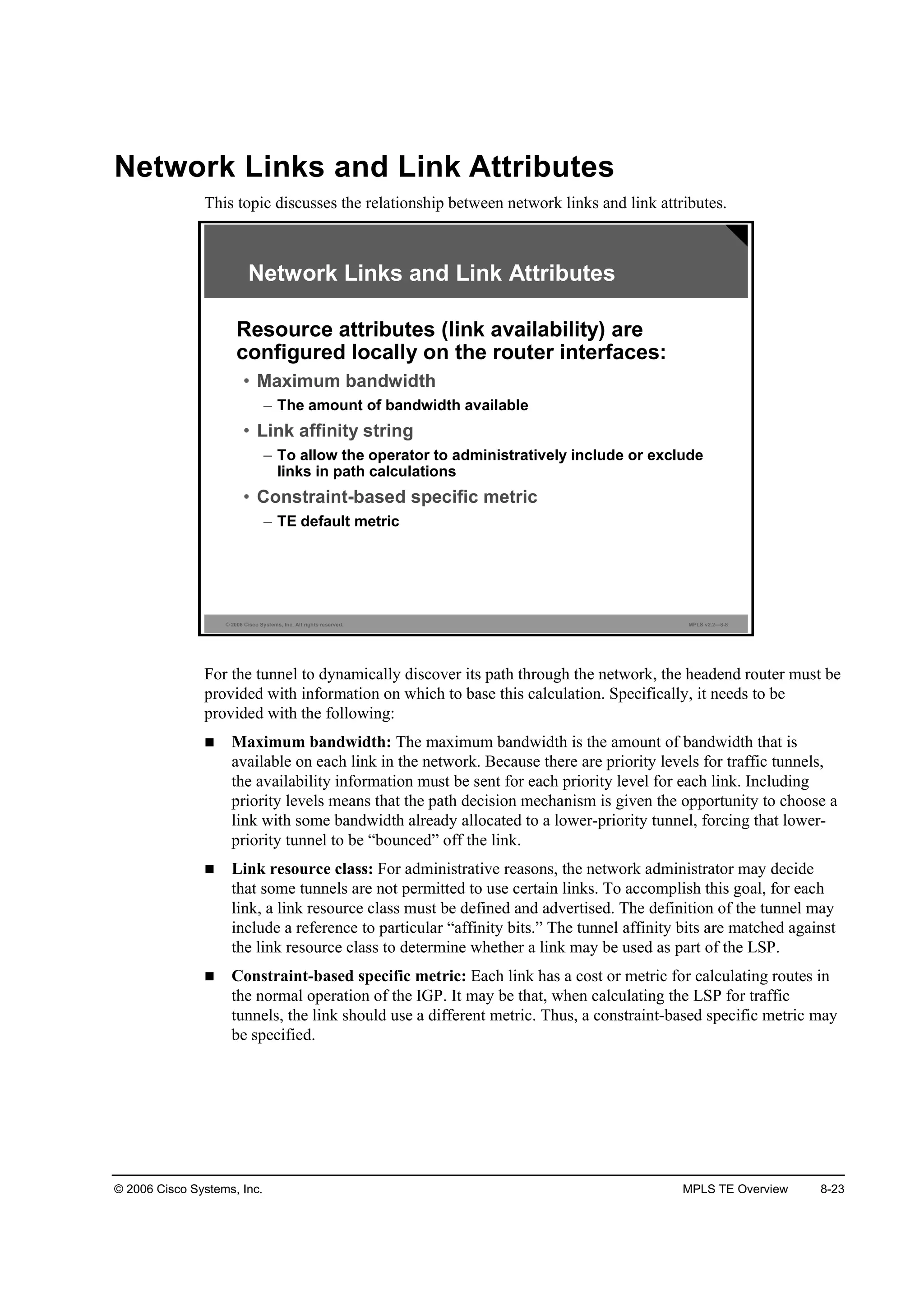
![8-24 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Constraint-Based Path Computation
This topic introduces constraint-based path computation.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—8-9
Constraint-Based Path Computation
• Constraint-based routing is demand-driven.
• Resource-reservation-aware routing paradigm:
– Based on criteria including, but not limited to,
network topology
– Calculated at the edge of a network:
• Modified Dijkstra’s algorithm at tunnel headend (CSPF
[Constraint-based SPF] or PCALC [path calculation]).
• Output is a sequence of IP interface addresses (next-
hop routers) between tunnel endpoints.
In traditional networks, the IGP calculates paths through the network based on the network
topology alone. Routing is destination-based, and all traffic to a given destination from a given
source uses the same path through the network. That path is based simply on what the IGP
regards as the “least cost” between the two points (source and destination).
“Constraint-based routing” (CBR) is the term that is used most often for this approach. In some
situations it is also referred to as a “constraint-based shortest path first” (CSPF) calculation or a
“path calculation” (PCALC).
CBR behaves in these ways:
It augments the use of link cost by also considering other factors, such as bandwidth
availability or link attributes, when choosing the path to a destination.
It tends to be carried out at the edge of the network, discovering a path across the core to
some destination elsewhere at the other edge of the network. Typically, this discovery uses
the CSPF calculation (a version of shortest path first [SPF] that is used by IS-IS and OSPF,
but considering other factors besides cost, such as bandwidth availability).
It produces a sequence of IP addresses that correspond to the routers that are used as the
path to the destination; these addresses are the next-hop addresses for each stage of the
path.
A consequence of CBR is that, from one source to one destination, many different paths can be
used through the network, depending on the requirements of those data flows.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-617-2048.jpg)
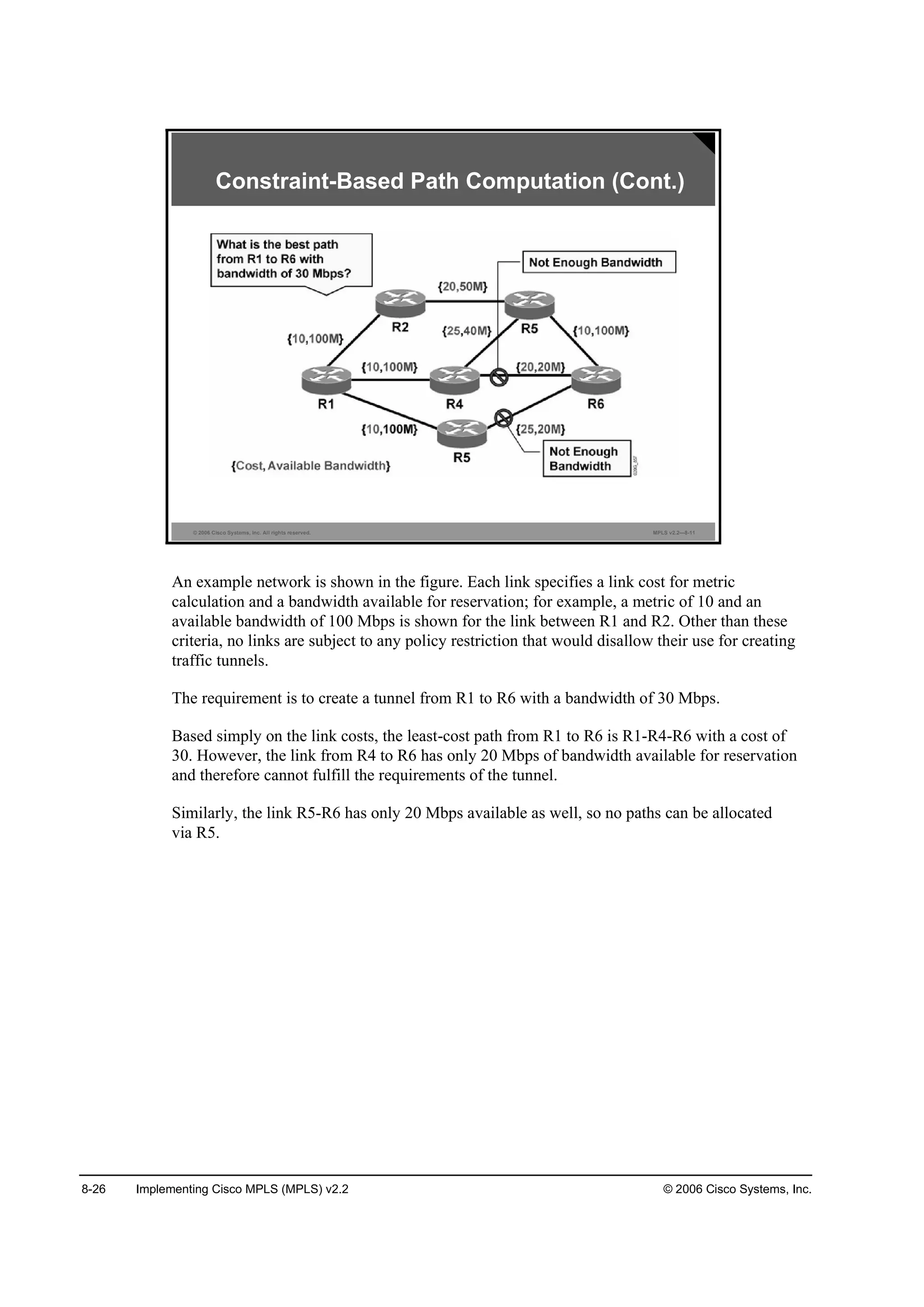
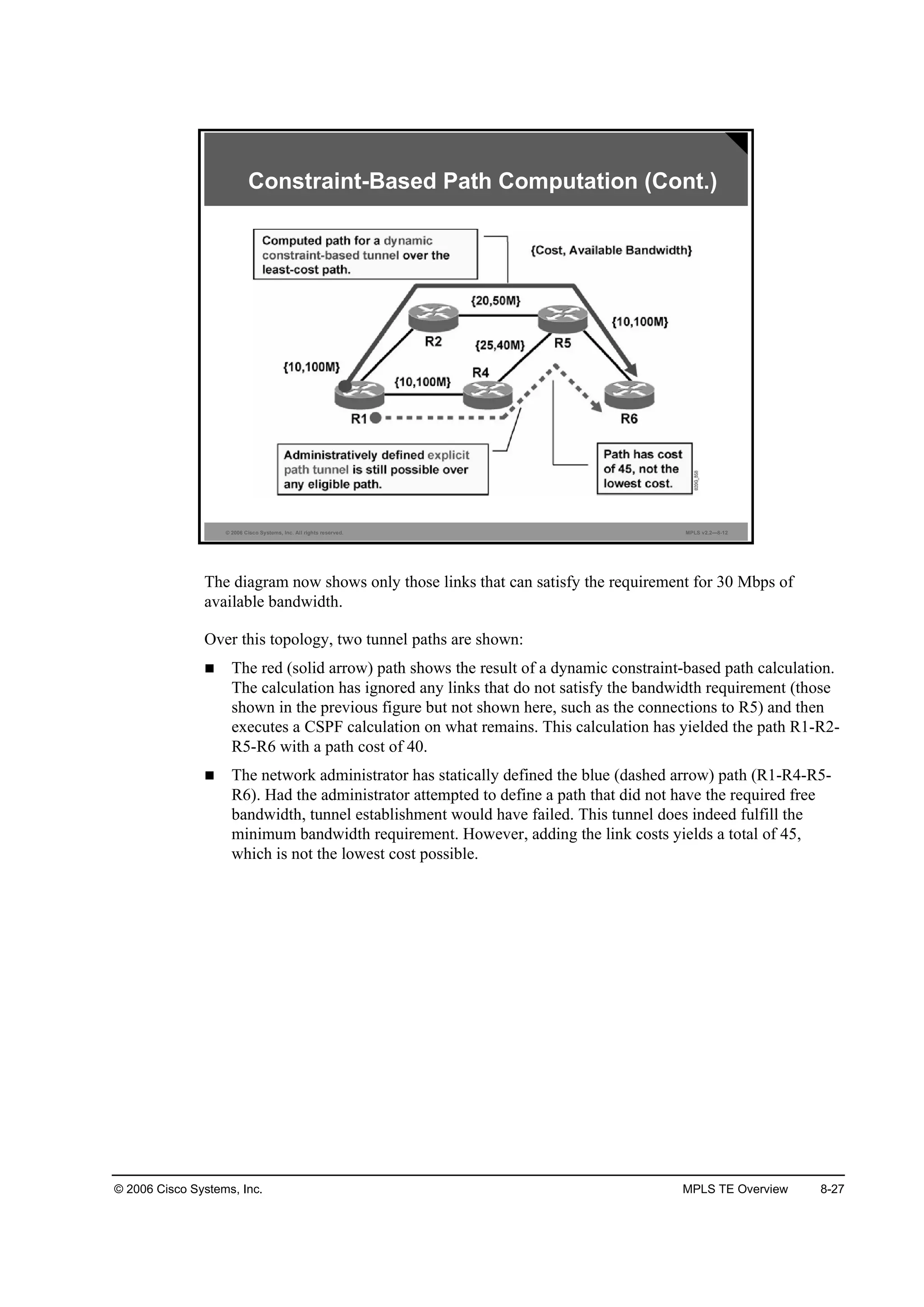
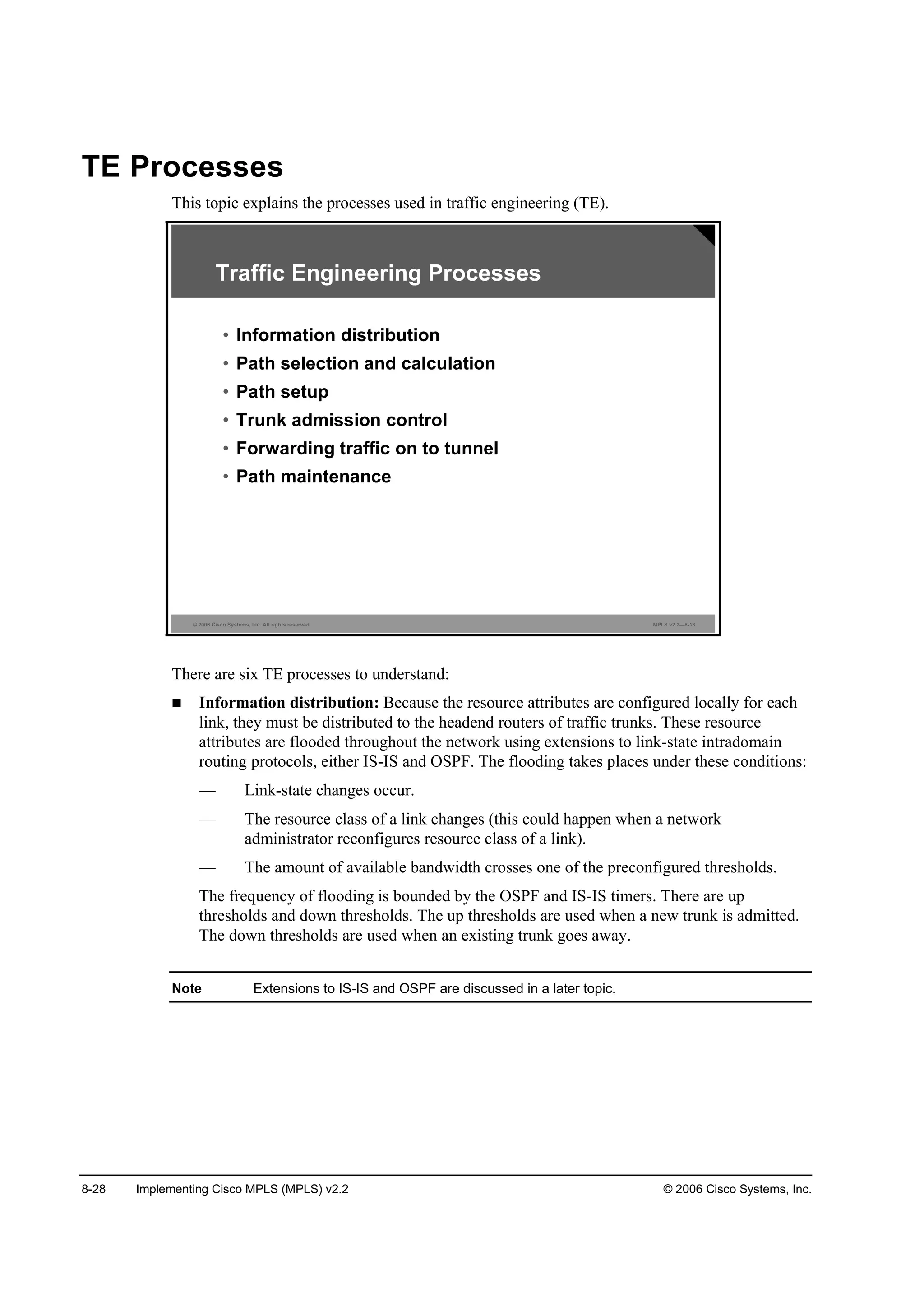
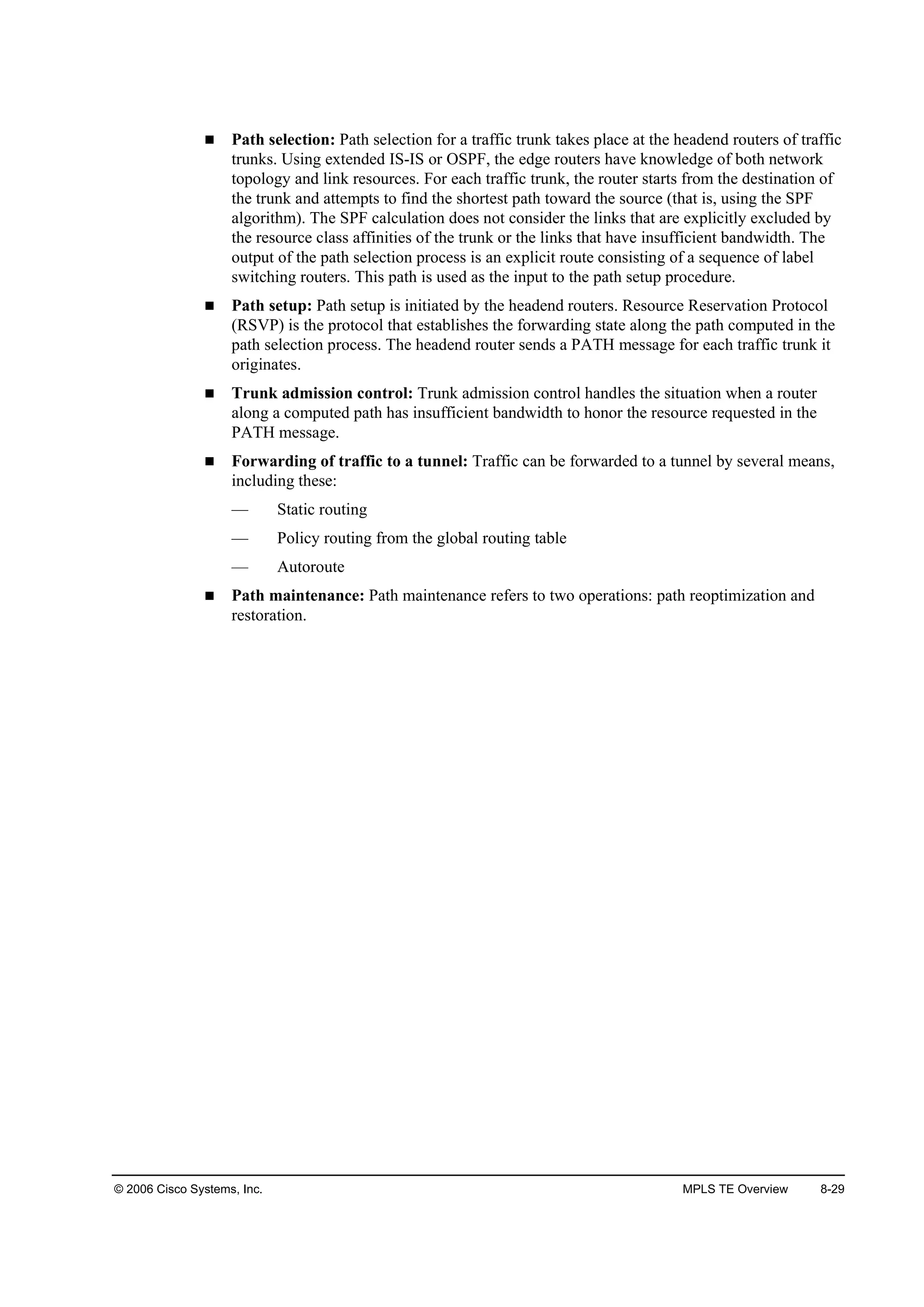
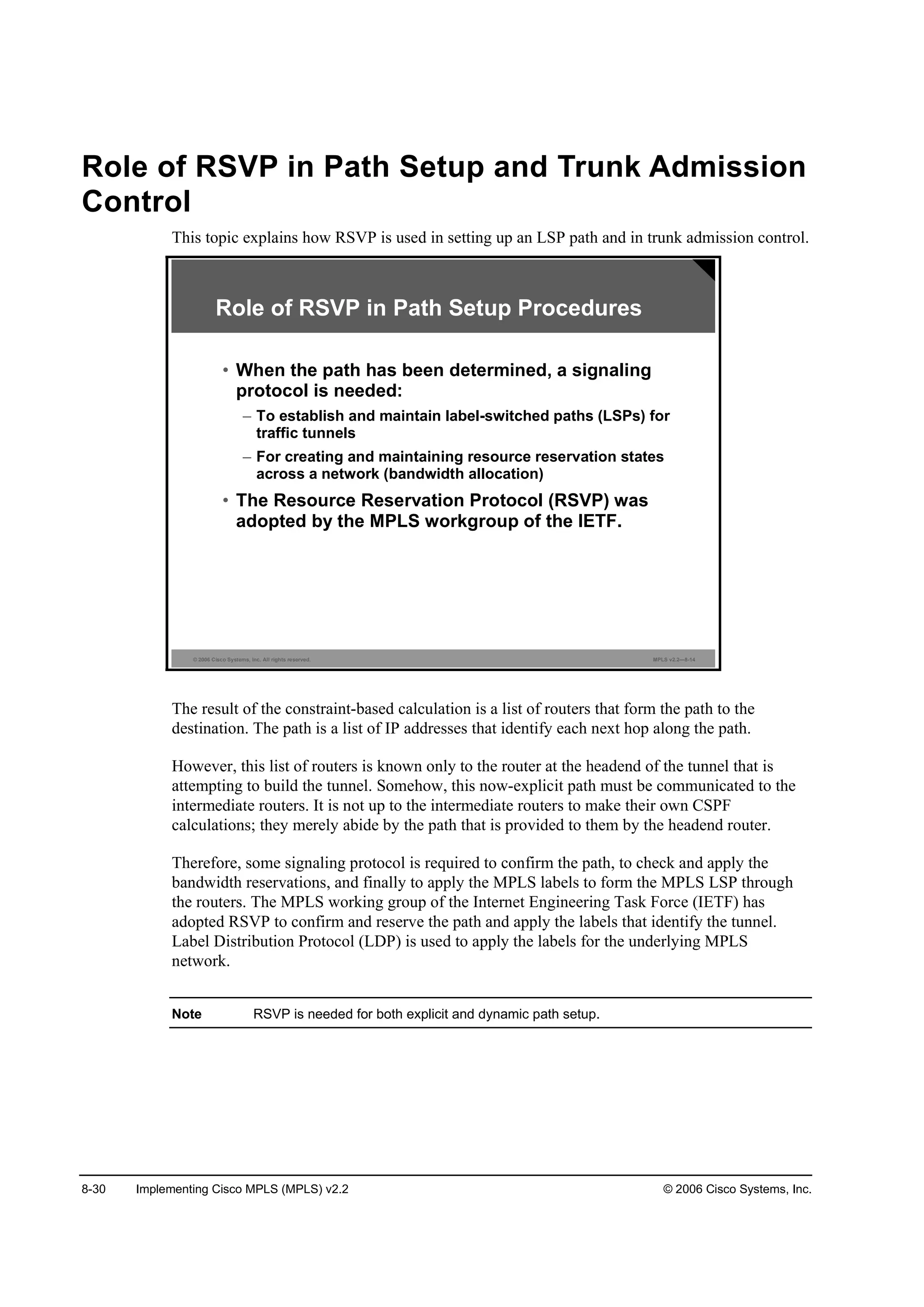
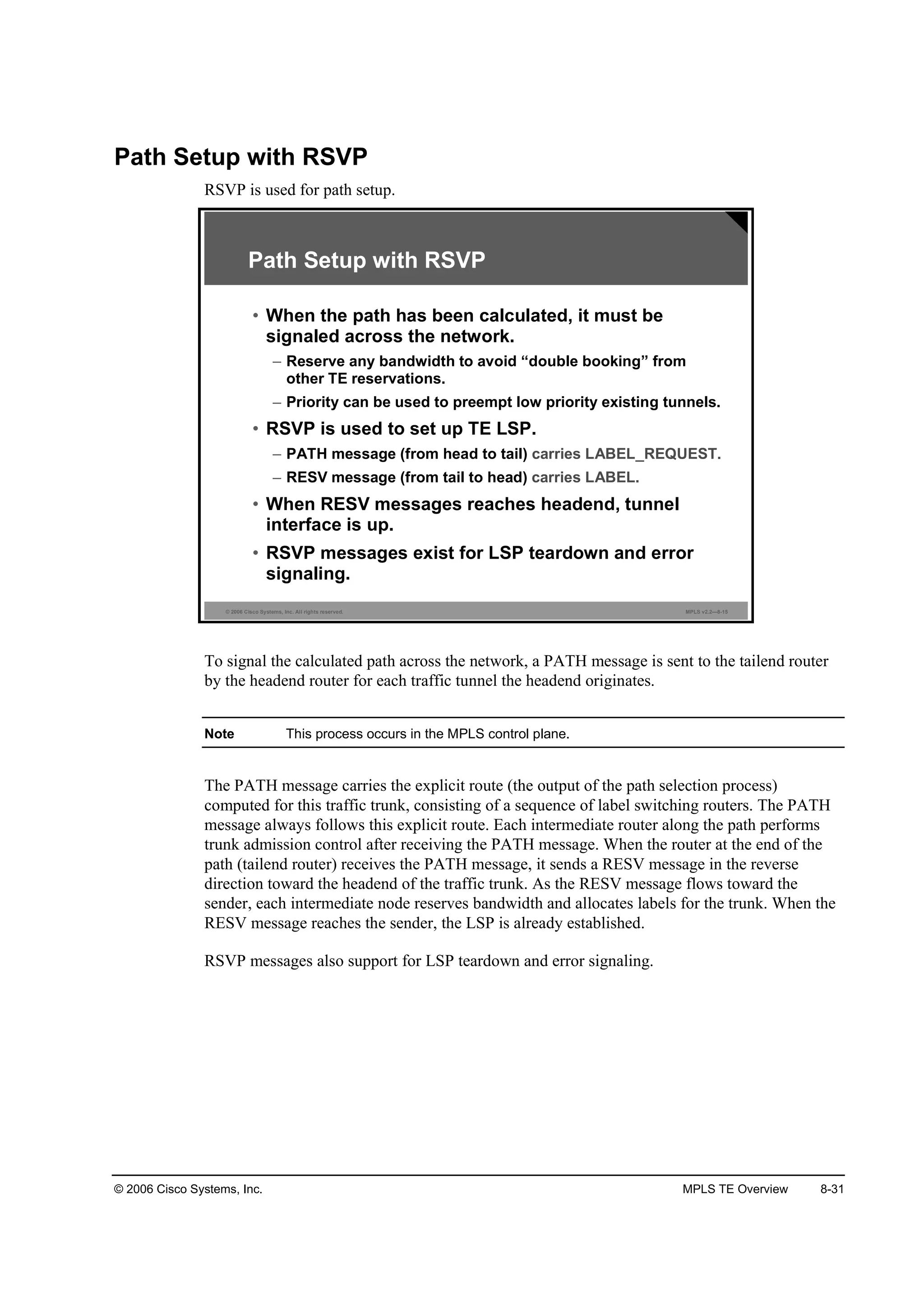
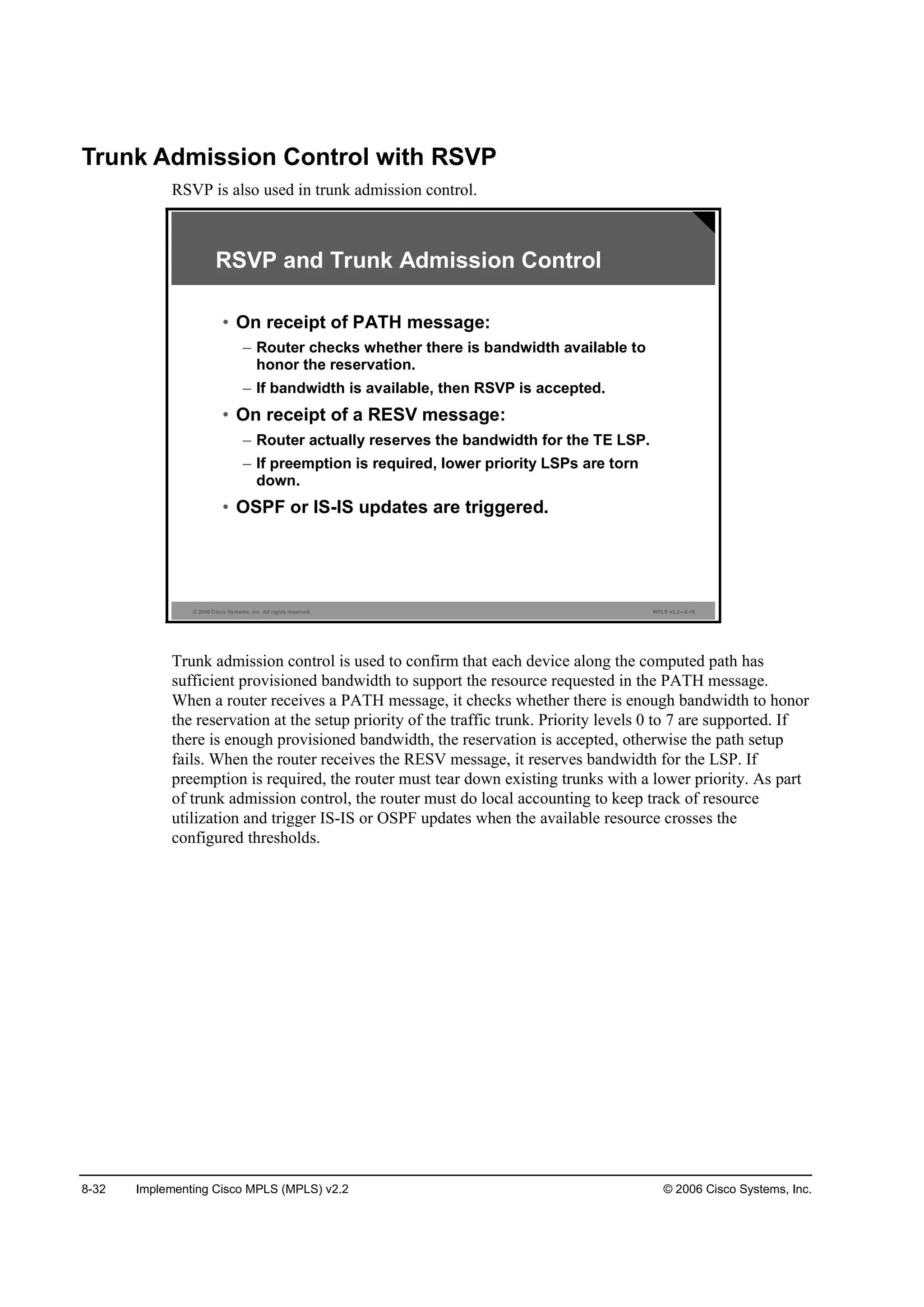
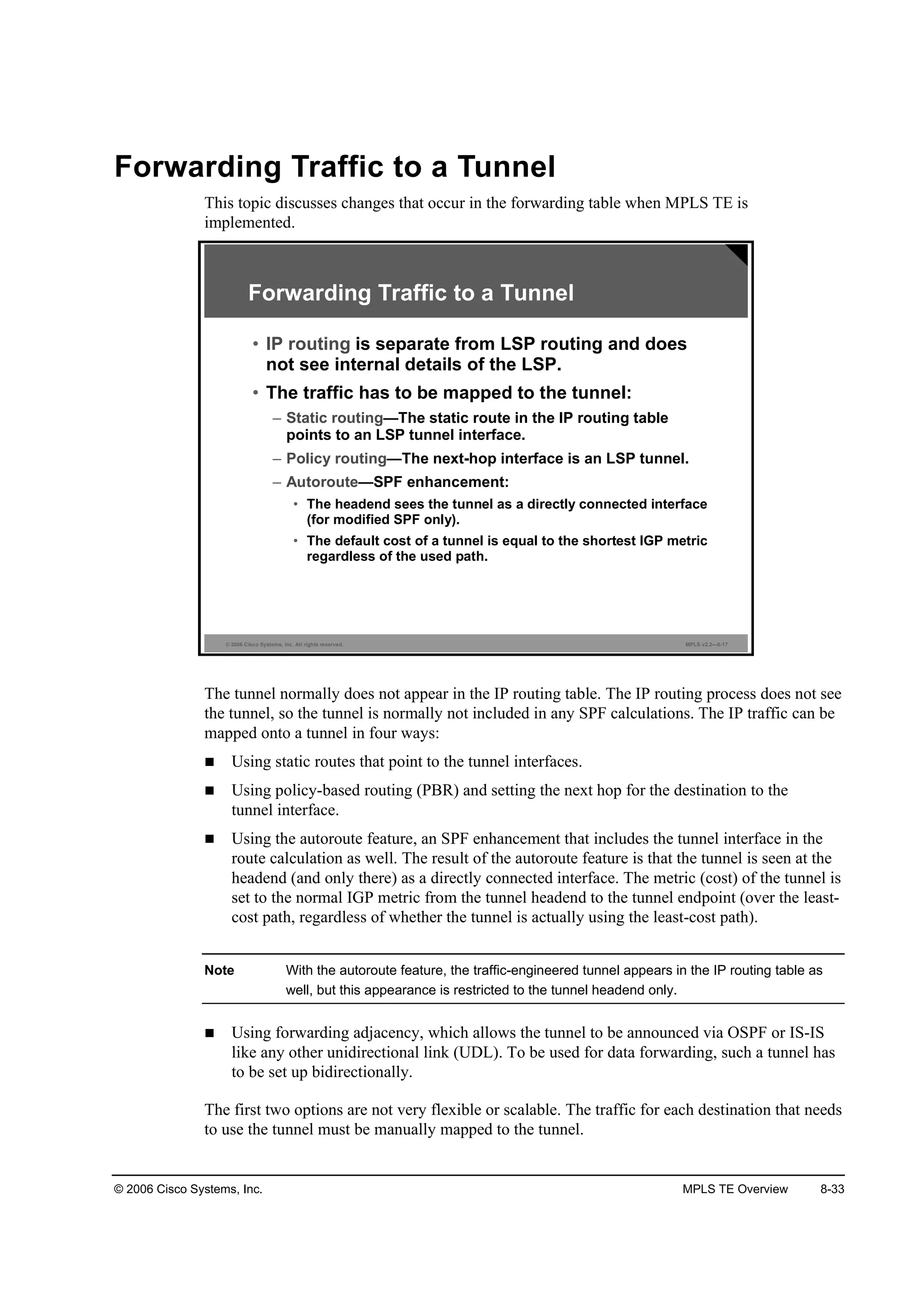
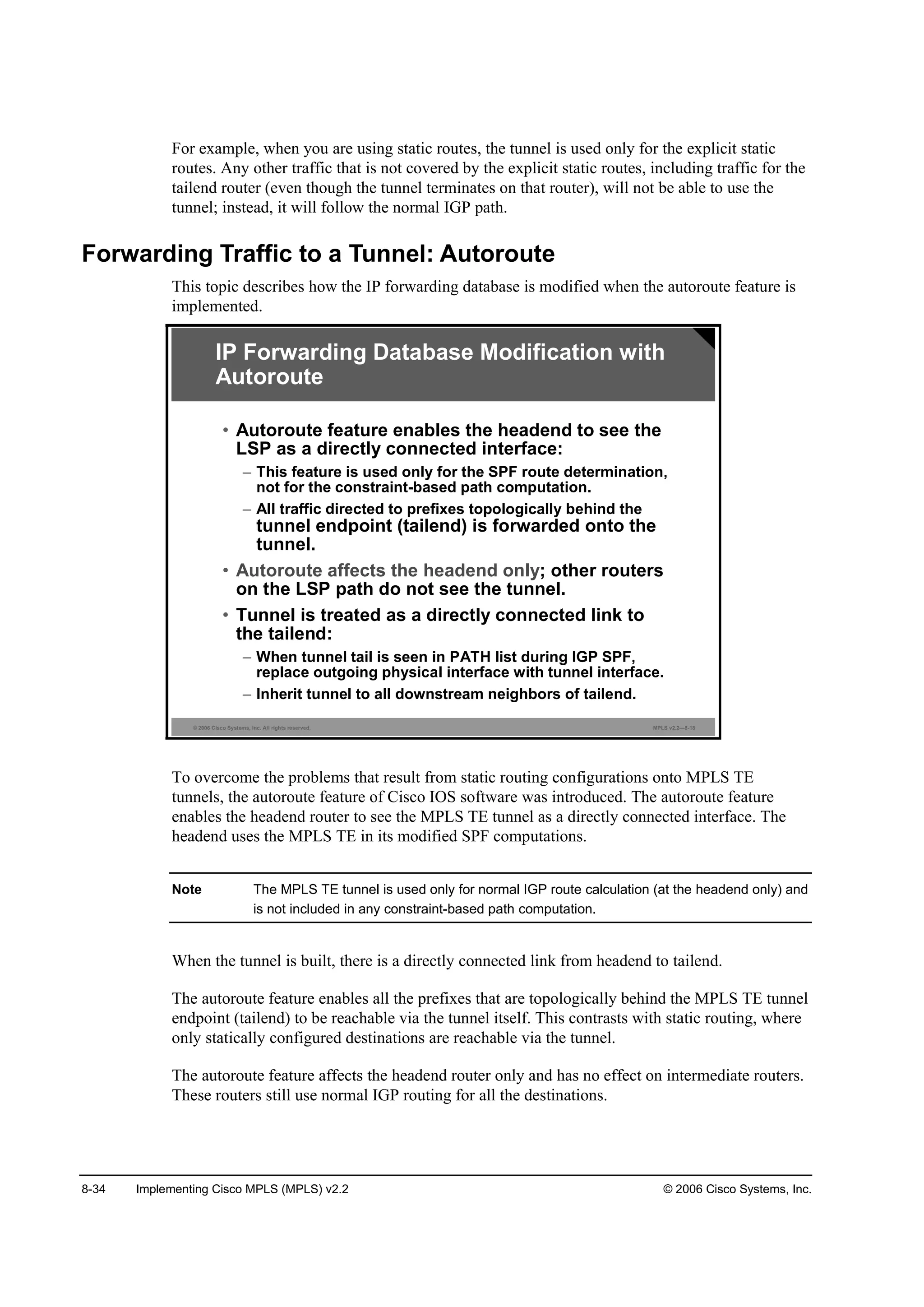
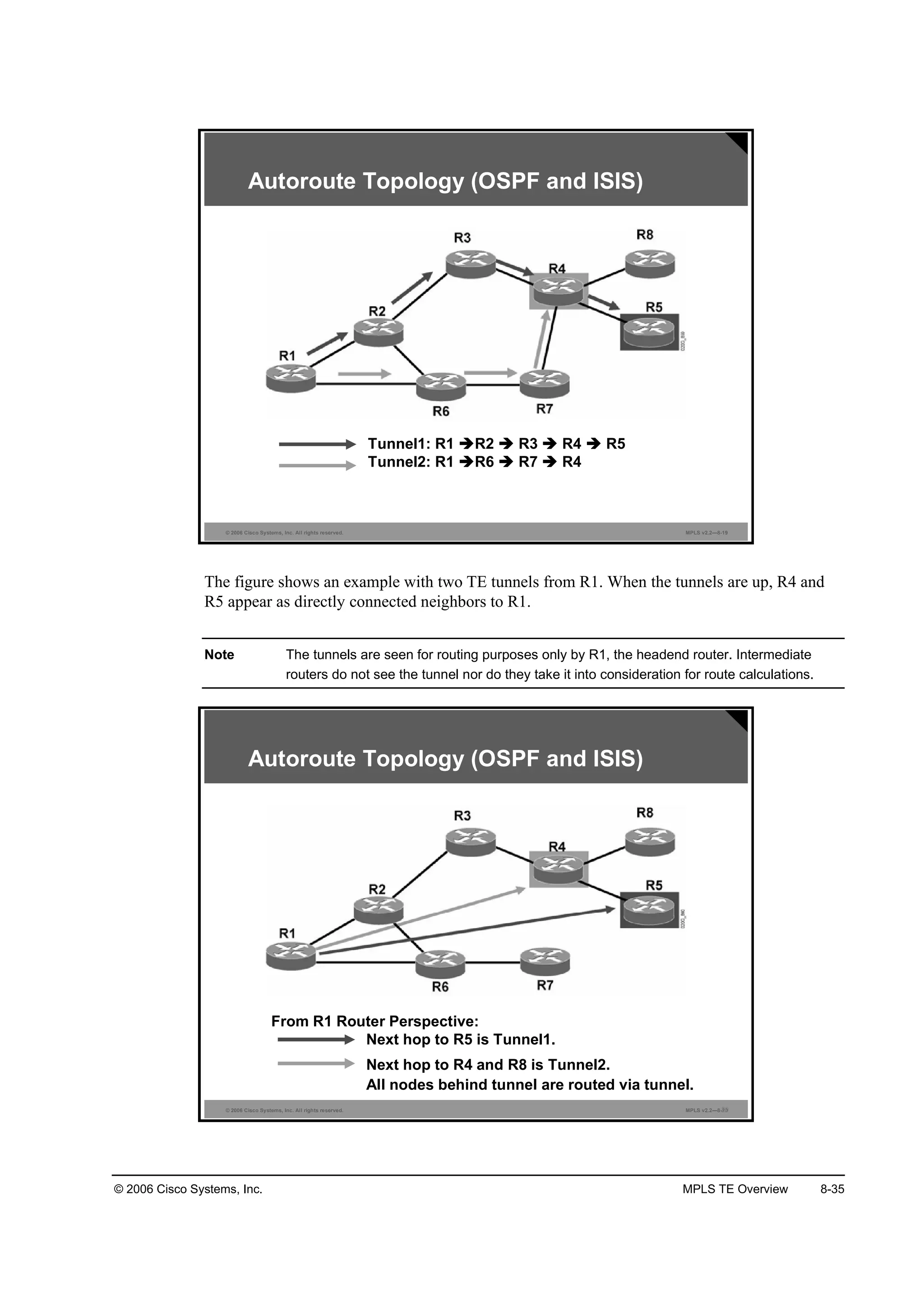
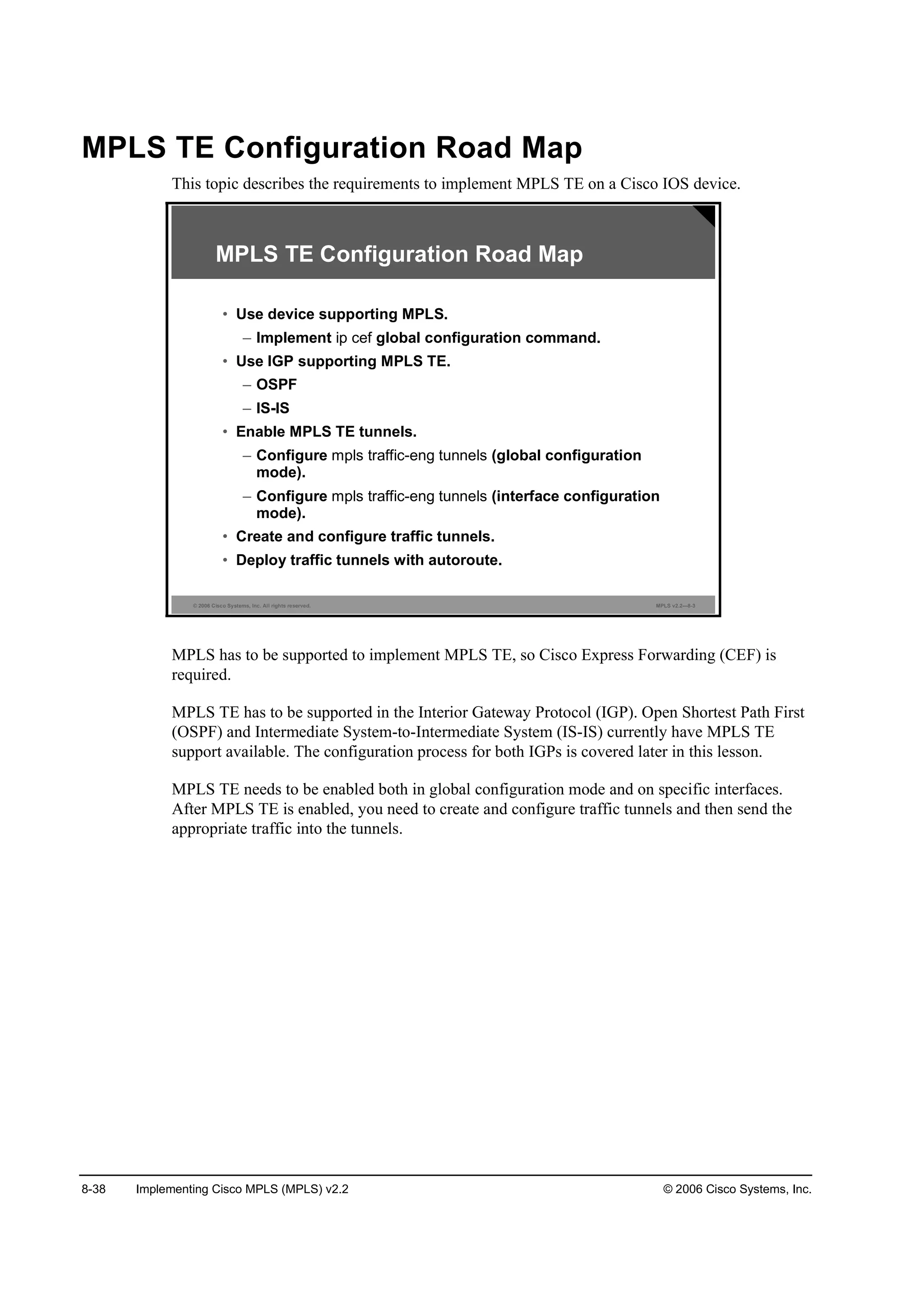
![© 2006 Cisco Systems, Inc. MPLS TE Overview 8-39
Enabling Device-Level MPLS TE Support
This topic describes the command syntax that is required to enable device-level MPLS TE
support on a Cisco IOS device.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—8-4
·° ˝»ş
®±«¬»®ř˝±˛ş·ą÷ý
• Enables IP CEF switching
Enabling Device-Level MPLS TE Support
ł°´ ¬®żşş·˝ó»˛ą ¬«˛˛»´
®±«¬»®ř˝±˛ş·ą÷ý
• Enables the MPLS TE tunnel feature on a device
ip cef
To enable CEF on the router, use the ip cef command in global configuration mode. To disable
CEF, use the no form of this command.
ip cef [distributed]
no ip cef [distributed]
Syntax Description
Parameter Description
Ľ·¬®·ľ«¬»Ľ (Optional) Enables distributed CEF (dCEF) operation. Distributes
CEF information to line cards. Line cards perform express
forwarding.
Usage Guidelines
CEF is an advanced Layer 3 IP switching technology. CEF optimizes network performance and
scalability for networks with dynamic, topologically dispersed traffic patterns, such as those
associated with web-based applications and interactive sessions.
Note CEF is a prerequisite for MPLS traffic engineering.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-632-2048.jpg)
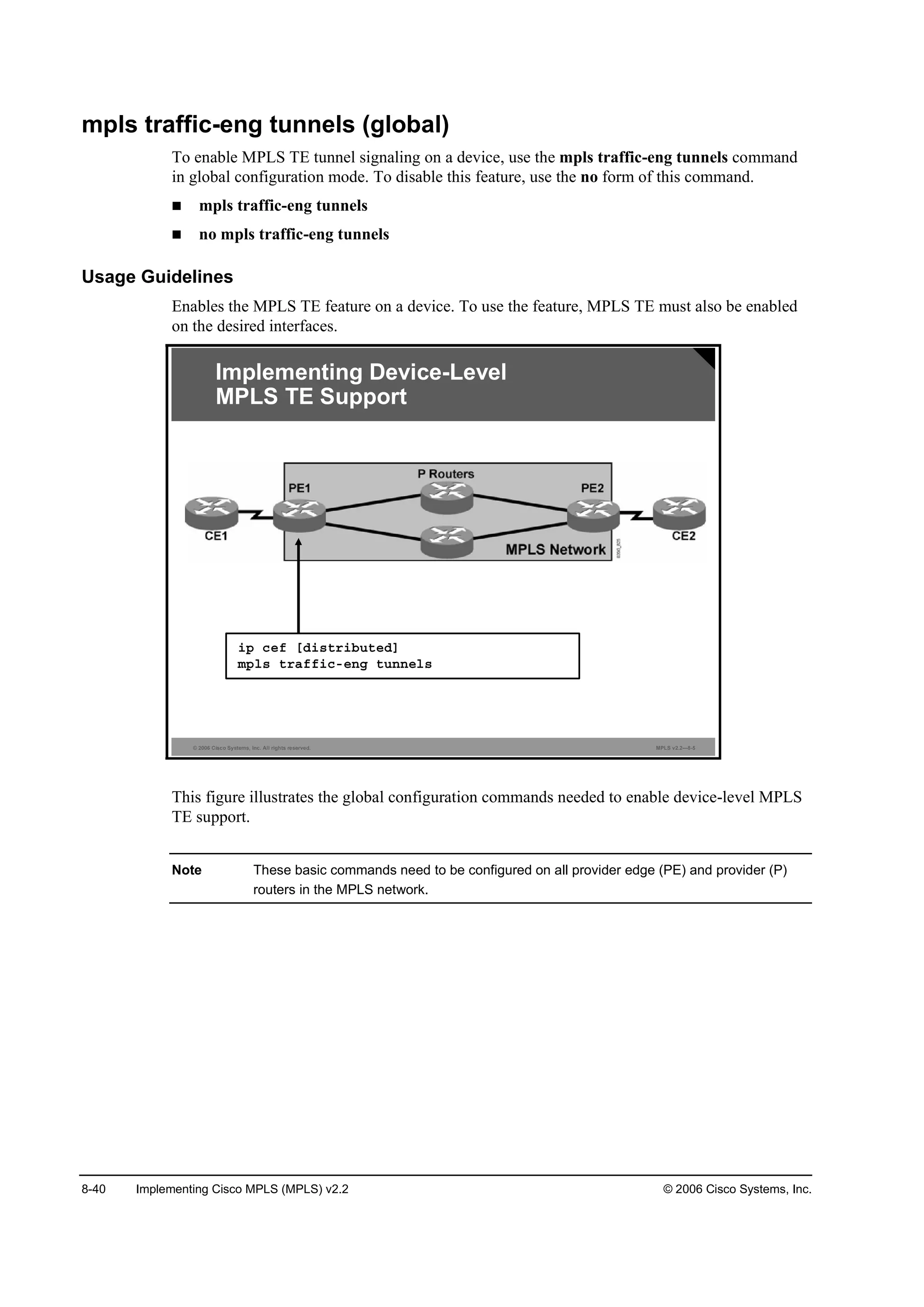
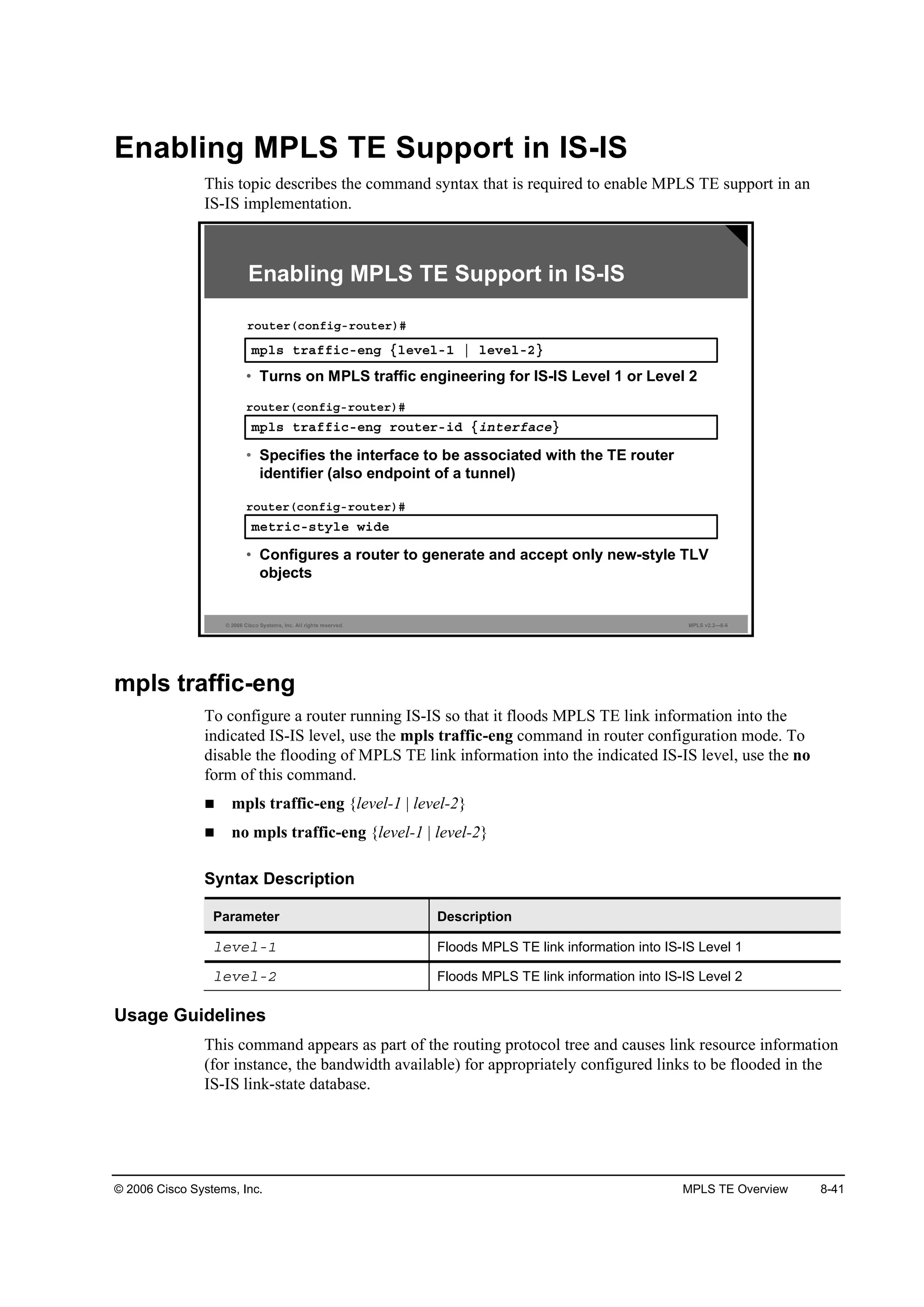
![8-42 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
mpls traffic-eng router-id
To specify the TE router identifier that is to be the IP address that is associated with the given
interface for the node, use the mpls traffic-eng router-id command in router configuration
mode. To disable this feature, use the no form of this command.
mpls traffic-eng router-id interface
no mpls traffic-eng router-id interface
Syntax Description
Parameter Description
·˛¬»®şż˝» The MPLS TE router identifier is taken from the IP address of the
supplied interface. This MPLS TE router identifier should be
configured as the tunnel destination for tunnels that originate at
other routers and terminate at this router. This interface should be
a stable interface that will not go up and down, such as a
loopback interface.
Usage Guidelines
The router identifier acts as a stable IP address for the TE configuration. This stable IP address
is flooded to all nodes. For all TE tunnels that originate at other nodes and end at this node, the
tunnel destination must be set to the TE router identifier of the destination node, because that
identifier is the address that the TE topology database at the tunnel head uses for its path
calculation.
Note The MPLS router ID has to be the same address as the IGP router ID. Typically a loopback
interface is used for the router ID.
It is a best practice to use the same loopback interface for MPLS TE, IGP, Border Gateway
Protocol (BGP), and Label Distribution Protocol (LDP) router identification.
metric-style wide
To configure a router running IS-IS so that it generates and accepts only new-style type, length,
and value (TLV) objects, use the metric-style wide command in router configuration mode. To
disable this function, use the no form of this command.
metric-style wide [transition] [level-1 | level-2 | level-1-2]
no metric-style wide [transition] [level-1 | level-2 | level-1-2]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-635-2048.jpg)
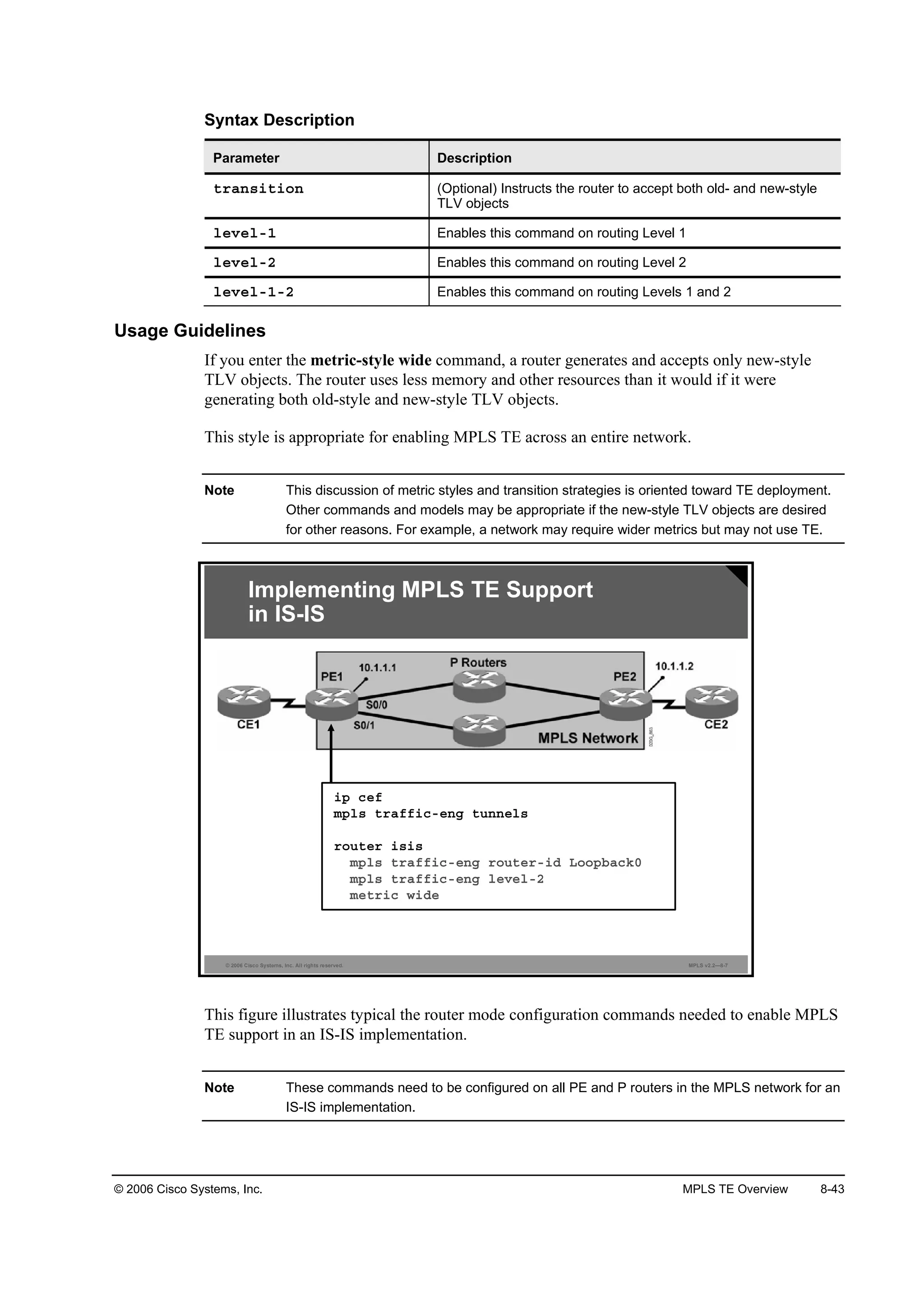
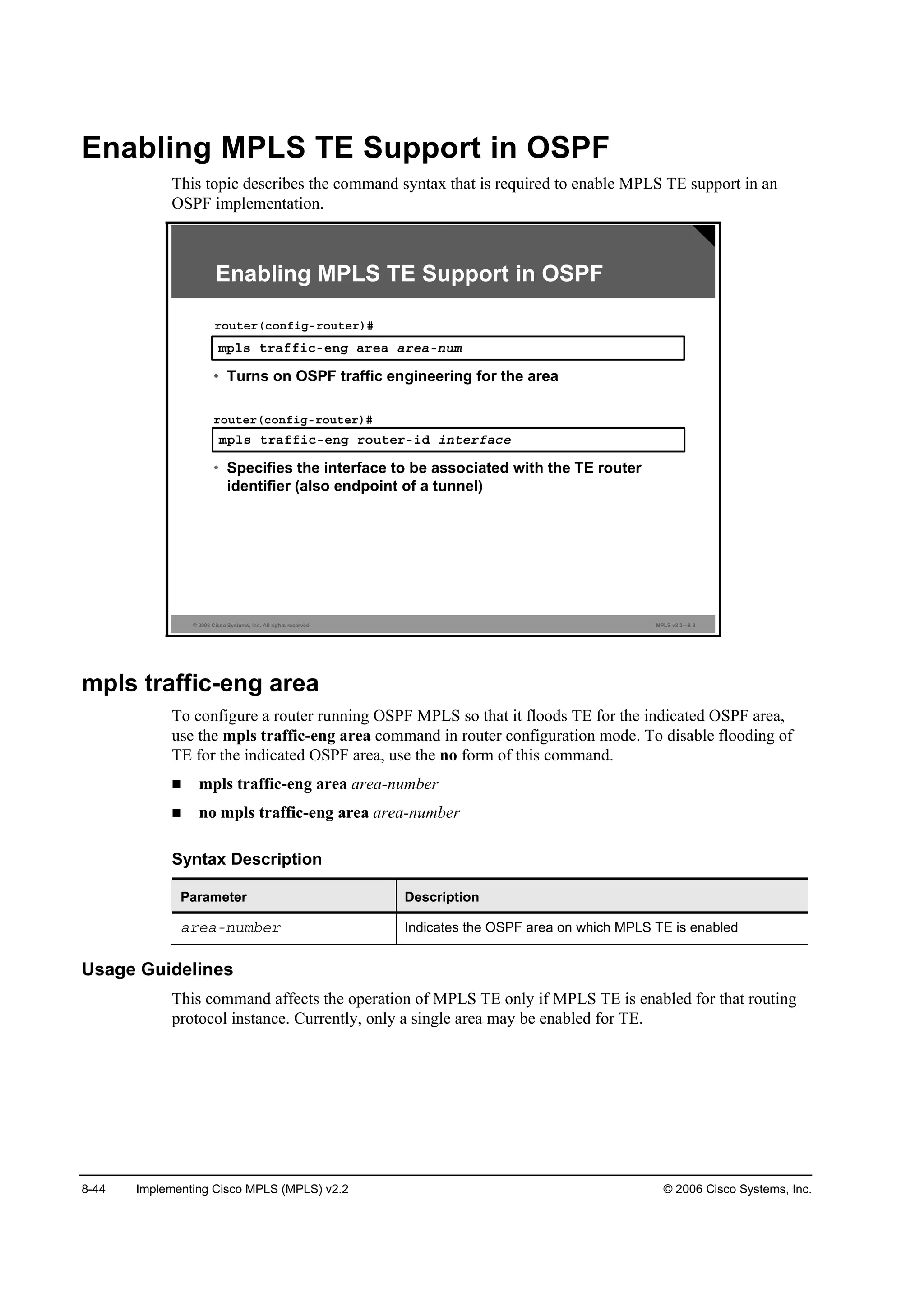
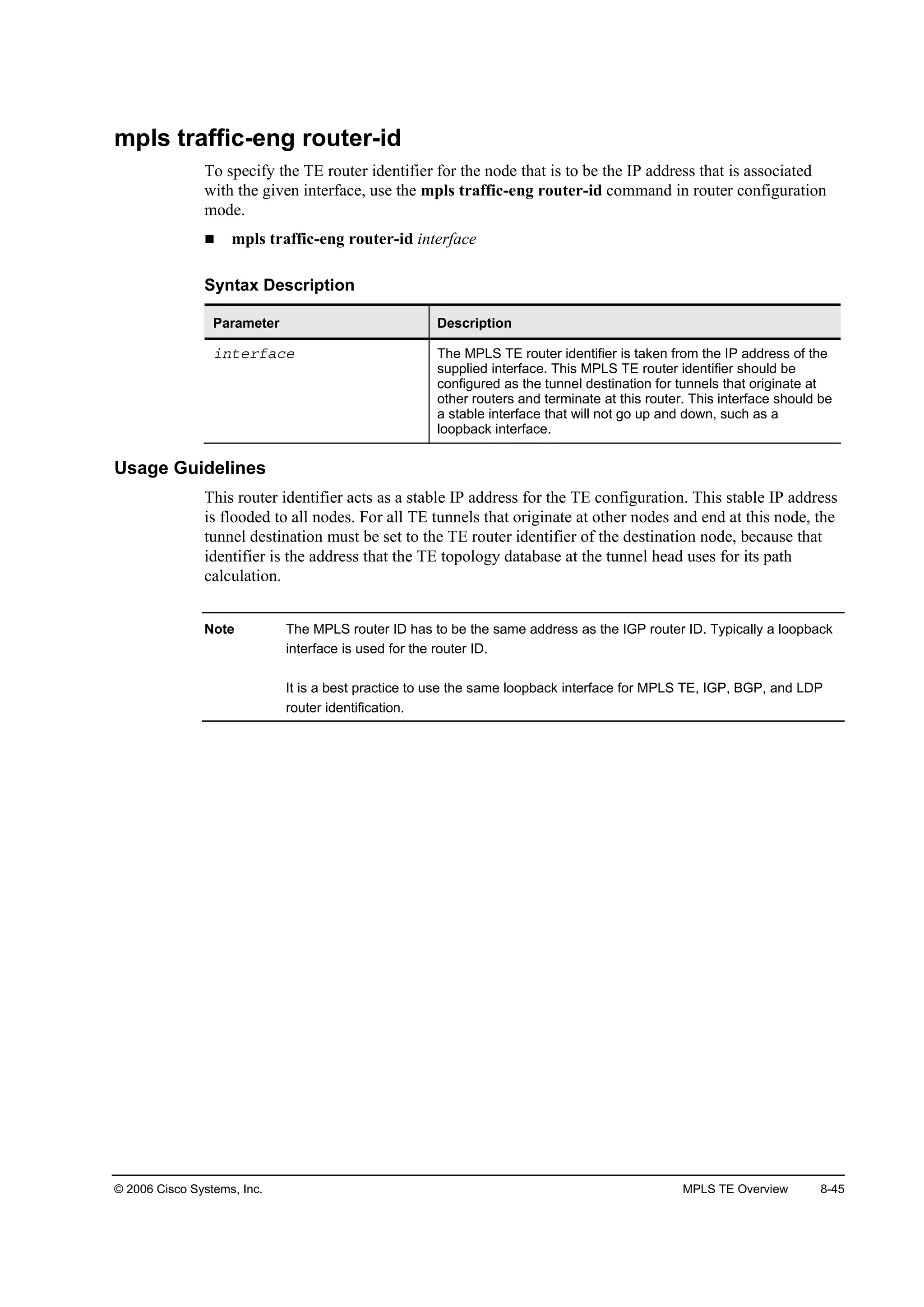
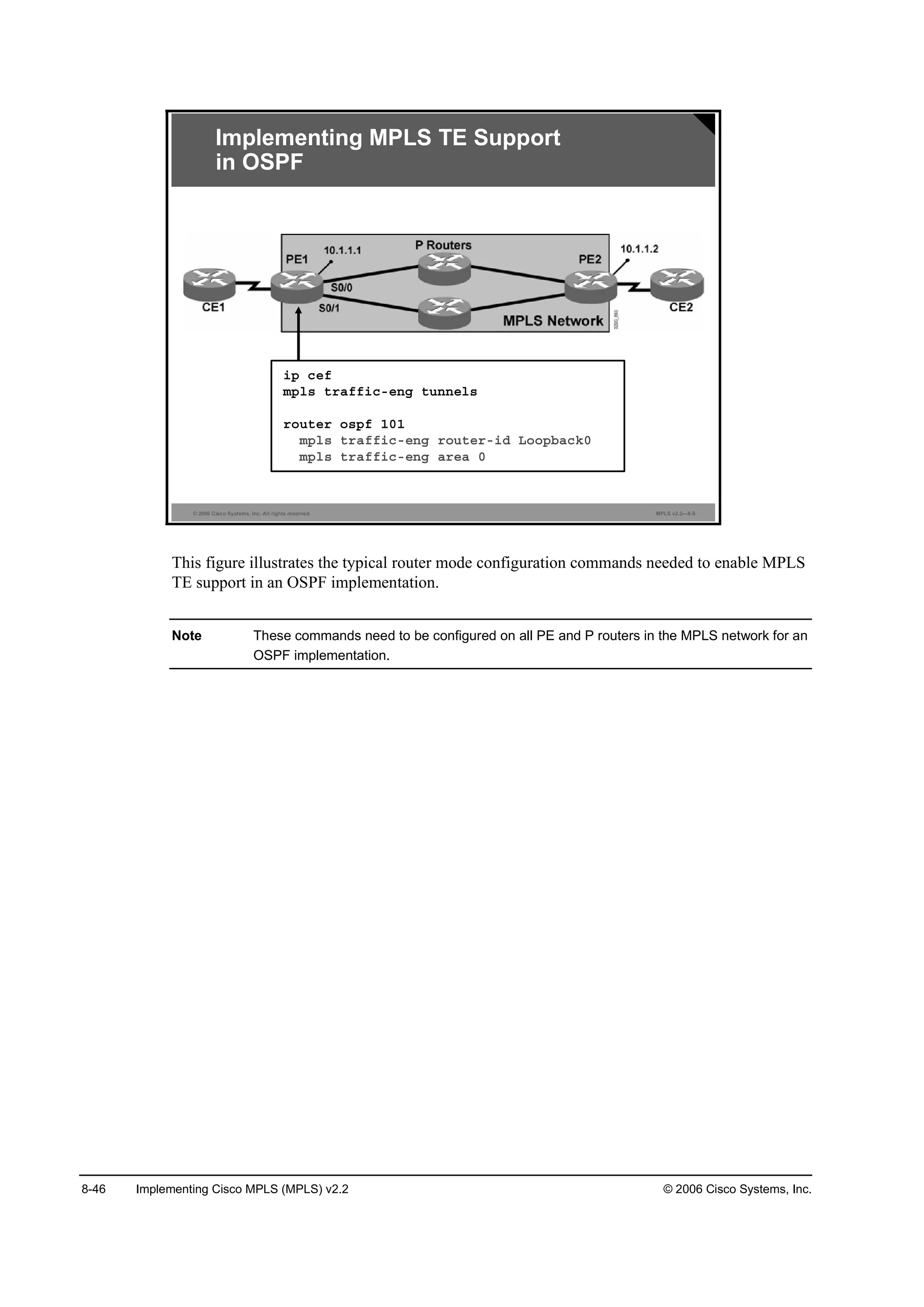
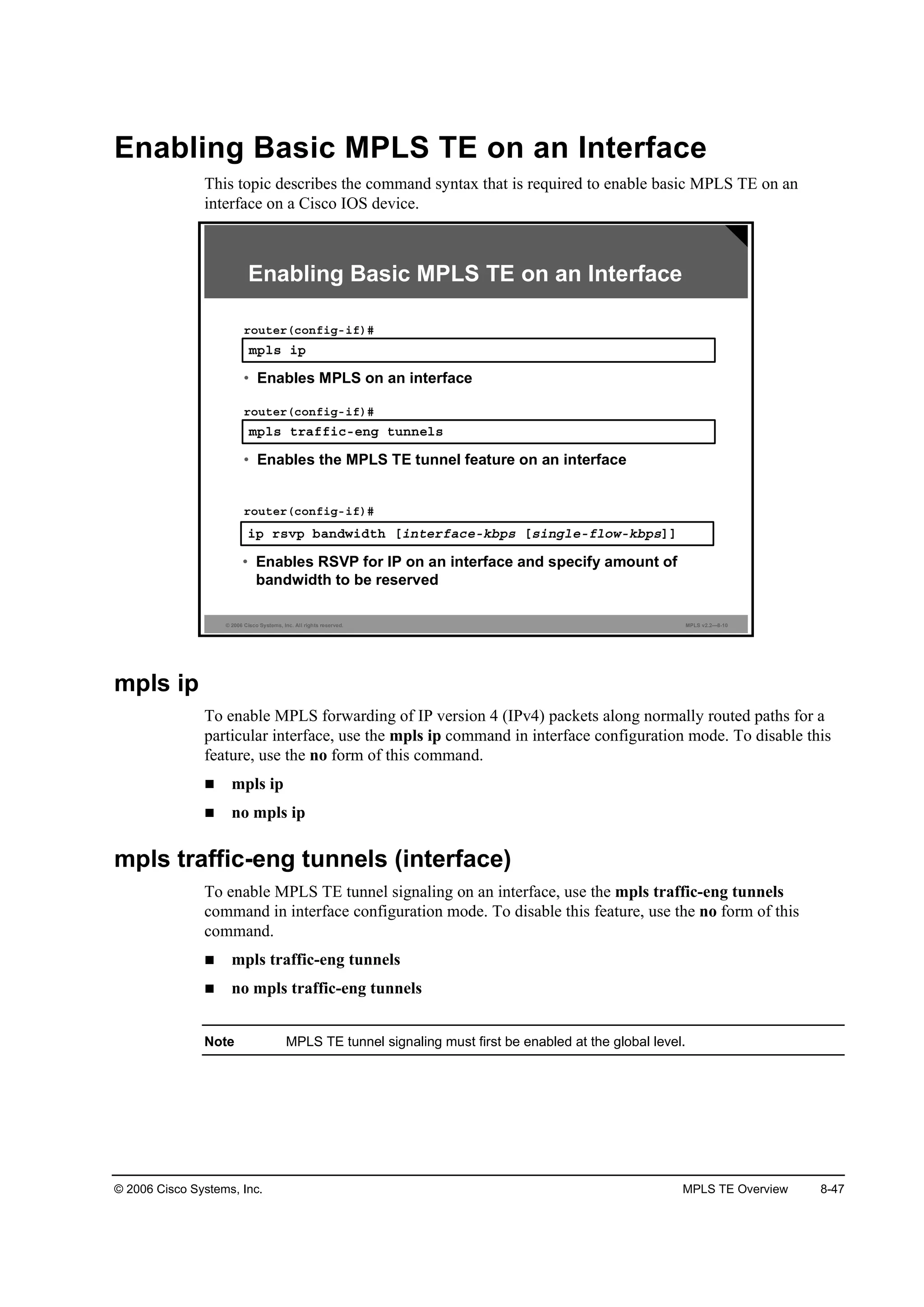
![8-48 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Usage Guidelines
This command enables the MPLS TE feature on the interface. To use the feature, MPLS TE
must also be enabled on the device globally. An enabled interface has its resource information
flooded into the appropriate IGP link-state database and accepts TE tunnel signaling requests.
ip rsvp bandwidth
To enable Resource Reservation Protocol (RSVP) for IP on an interface, use the ip rsvp
bandwidth interface configuration command. To disable RSVP, use the no form of this
command.
ip rsvp bandwidth [interface-kbps [single-flow-kbps]]
no ip rsvp bandwidth [interface-kbps [single-flow-kbps]]
Syntax Description
Parameter Description
·˛¬»®şż˝»óµľ° (Optional) Maximum amount of bandwidth, in kilobits per second,
that may be allocated by RSVP flows. The range is from 1 to
10,000,000.
·˛ą´»óş´±©óµľ° (Optional) Maximum amount of bandwidth, in kilobits per second,
that may be allocated to a single flow. The range is from 1 to
10,000,000.
Usage Guidelines
RSVP is disabled by default. If the ip rsvp bandwidth command is entered but no bandwidth
values are supplied (for example, if you enter ip rsvp bandwidth and then press the Enter key),
a default bandwidth value is assumed for both the interface-kbps and single-flow-kbps
arguments.
RSVP cannot be configured with Versatile Interface Processor (VIP) dCEF.
Note To make MPLS TE work over a subinterface, you must configure RSVP on the main
interface with the ip rsvp bandwidth command even if the main interface is not used for
MPLS TE.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-641-2048.jpg)
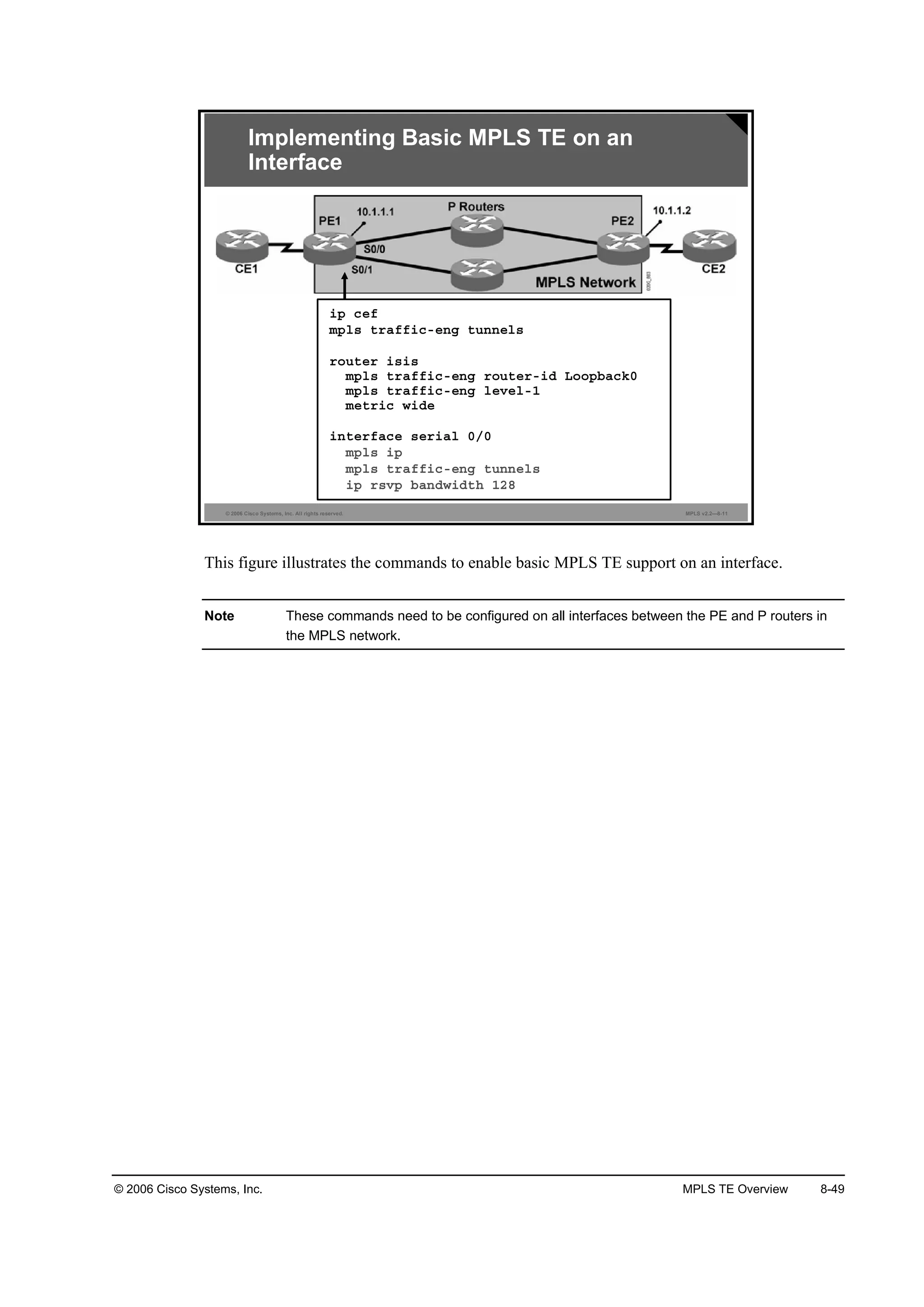
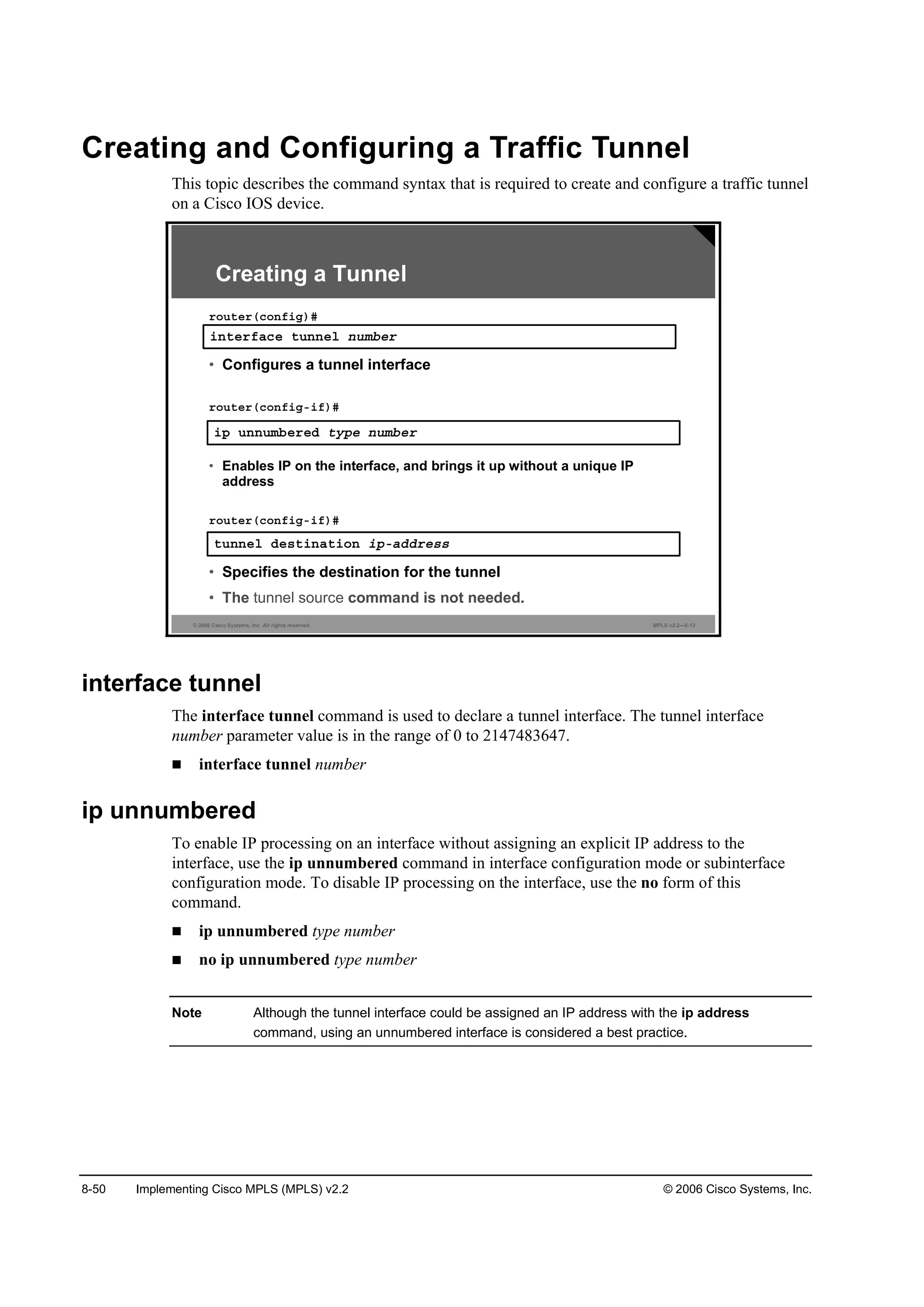
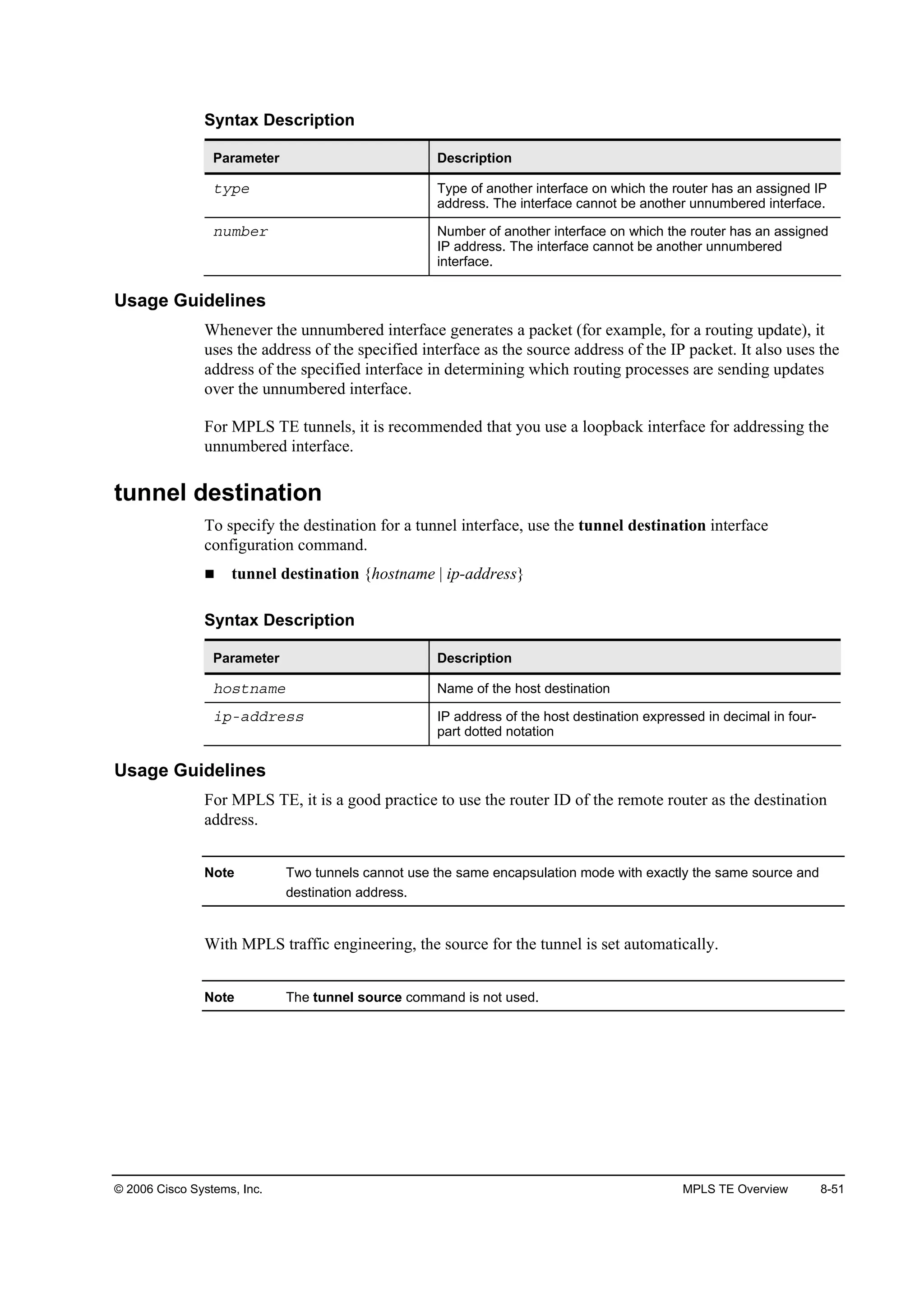
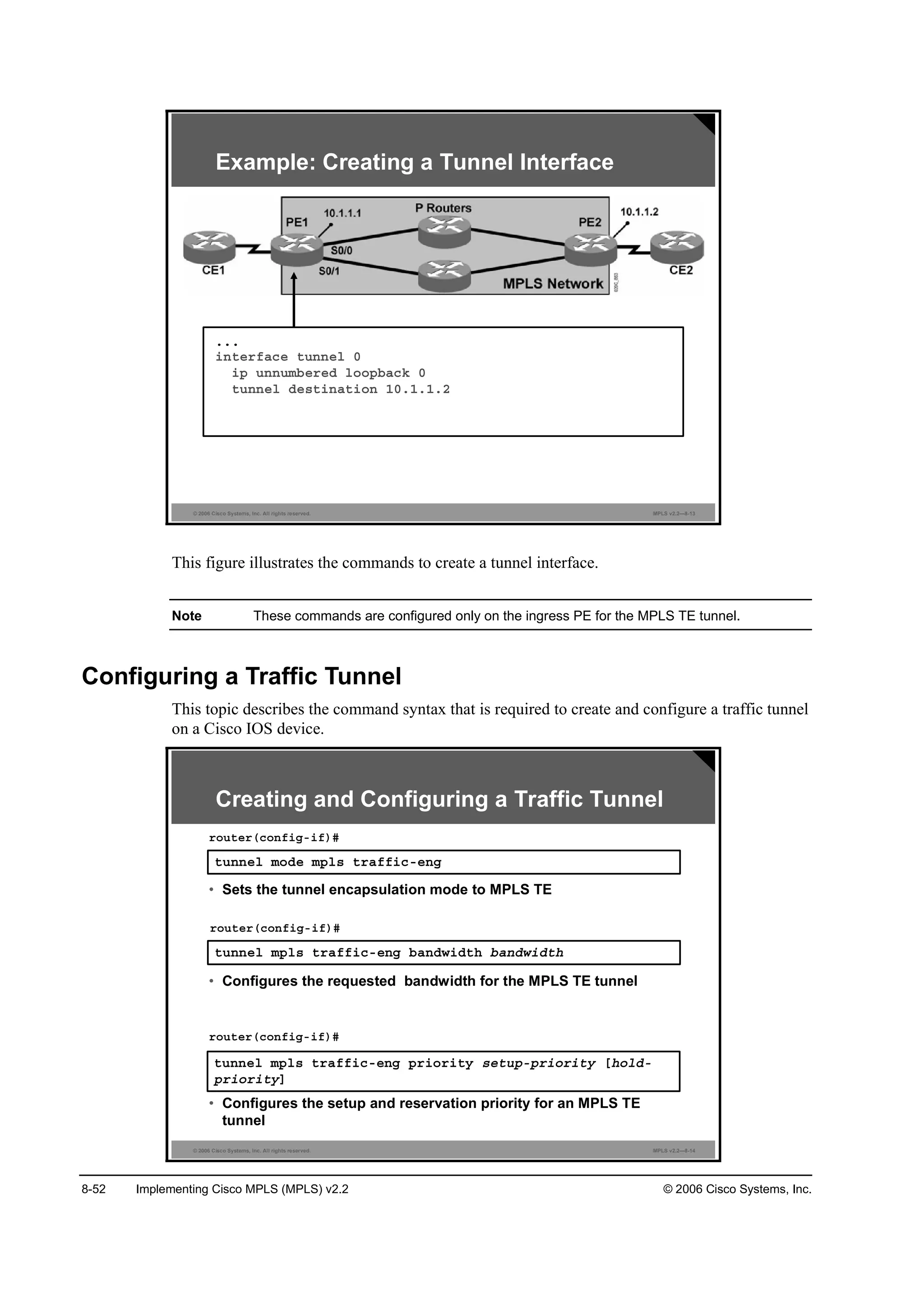
![© 2006 Cisco Systems, Inc. MPLS TE Overview 8-53
tunnel mode mpls traffic-eng
To set the mode of a tunnel to MPLS for TE, use the tunnel mode mpls traffic-eng command
in interface configuration mode.
tunnel mode mpls traffic-eng
Usage Guidelines
This command specifies that the tunnel interface is for an MPLS TE tunnel and enables the
various tunnel MPLS configuration options.
tunnel mpls traffic-eng bandwidth
To configure the bandwidth that is required for an MPLS TE tunnel, use the tunnel mpls
traffic-eng bandwidth command in the interface configuration mode. To disable this feature,
use the no form of this command.
tunnel mpls traffic-eng bandwidth [sub-pool | global] bandwidth
no tunnel mpls traffic-eng bandwidth [sub-pool | global] bandwidth
Syntax Description
Parameter Description
ľż˛Ľ©·Ľ¬¸ The bandwidth required for an MPLS TE tunnel. Bandwidth is
specified in kilobits per second. Bandwidth, in kilobits per second,
is set aside for the MPLS traffic engineering tunnel. The range is
between 1 and 4294967295.
sub-pool (Optional) Indicates a subpool tunnel.
global (Optional) Indicates a global pool tunnel. Entering this keyword is
not necessary, for all tunnels are global pool in the absence of
the sub-pool keyword. But if users of pre-DiffServ-aware TE
images enter this keyword, it is accepted.
Usage Guidelines
This command specifies that the tunnel bandwidth for an MPLS TE tunnel.
Default
The default bandwidth is 0.
tunnel mpls traffic-eng priority
To configure the setup and reservation priority for an MPLS TE tunnel, use the tunnel mpls
traffic-eng priority command in interface configuration mode. To remove the specified setup
and reservation priority, use the no form of this command.
tunnel mpls traffic-eng priority setup-priority [hold-priority]
no tunnel mpls traffic-eng priority setup-priority [hold-priority]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-646-2048.jpg)
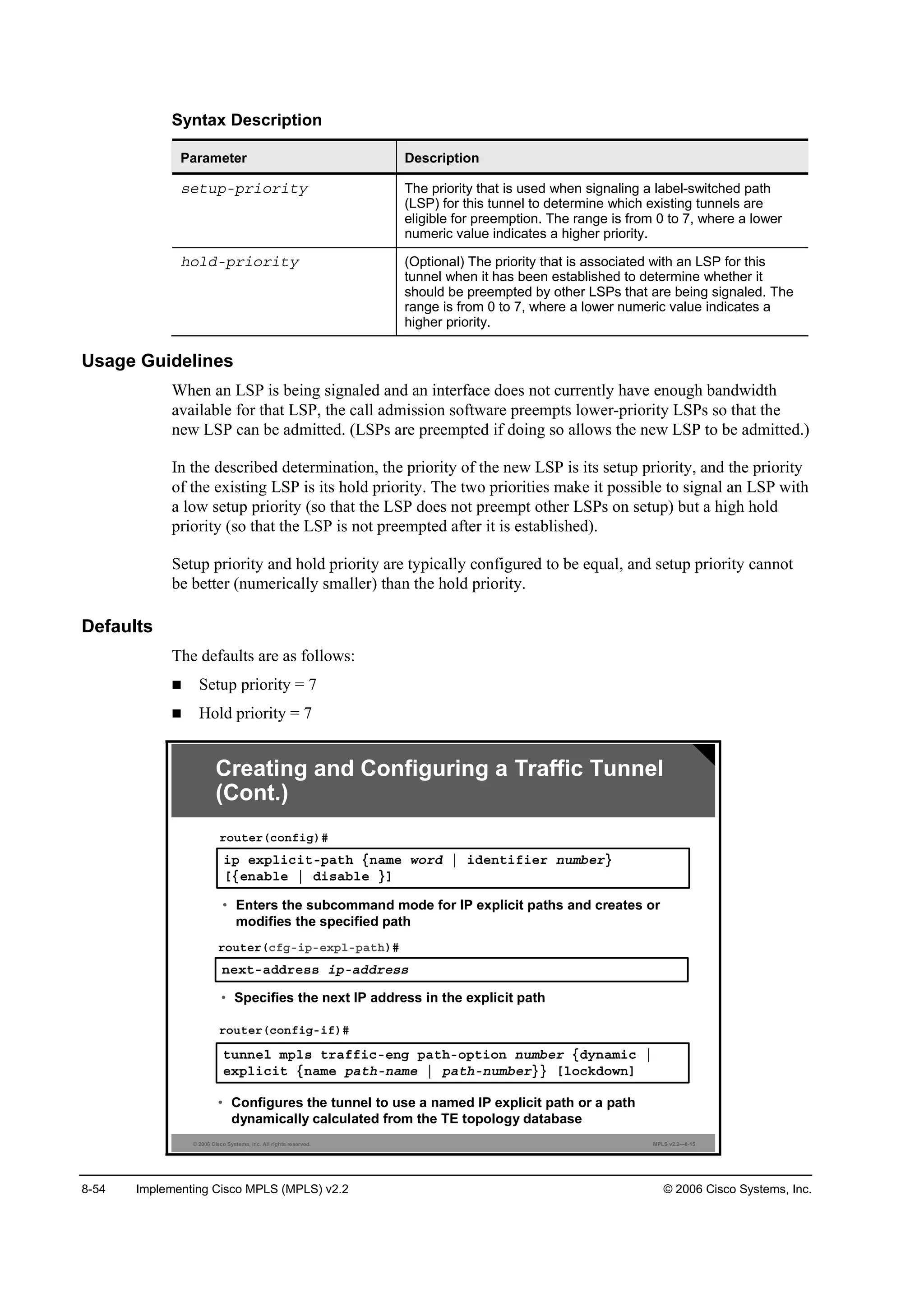
![© 2006 Cisco Systems, Inc. MPLS TE Overview 8-55
ip explicit-path
To enter the subcommand mode for IP explicit paths to create or modify the named path, use
the ip explicit-path command in global configuration mode. An IP explicit path is a list of IP
addresses, each representing a node or link in the explicit path.
ip explicit-path {name word | identifier number} [{enable | disable}]
Syntax Description
Parameter Description
˛żł» ©±®Ľ Specifies an explicit path by name.
·Ľ»˛¬·ş·»® ˛«łľ»® Specifies an explicit path by number. You can specify a number
from 1 to 65535.
»˛żľ´» (Optional) Sets the state of the path to be enabled.
Ľ·żľ´» (Optional) Prevents the path from being used for routing while it is
being configured.
next-address
To specify the next IP address in the explicit path, use the next-address command in IP explicit
path configuration mode. To remove the specified next IP address in the explicit path, use the
no form of this command.
next-address ip-address
no next-address ip-address
Default
The next IP address in the explicit path is not specified.
tunnel mpls traffic-eng path-option
To configure a path option for an MPLS-TE tunnel, use the tunnel mpls traffic-eng
path-option command in interface configuration mode. To disable the specified path option,
use the no form of this command.
tunnel mpls traffic-eng path-option number {dynamic | explicit {name path-name |
path-number}} [lockdown]
no tunnel mpls traffic-eng path-option number {dynamic | explicit {name path-name |
path-number}} [lockdown]](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-648-2048.jpg)

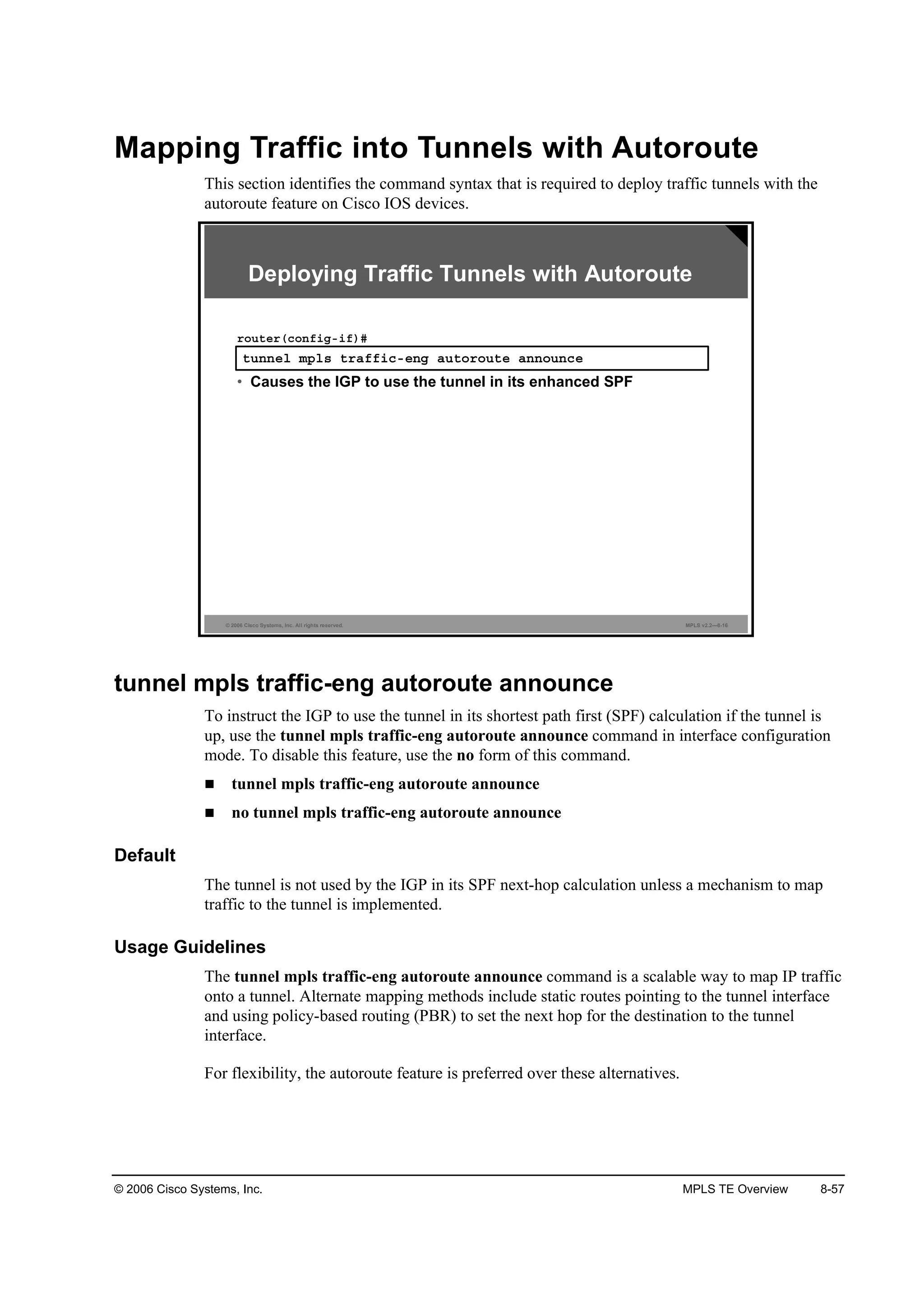
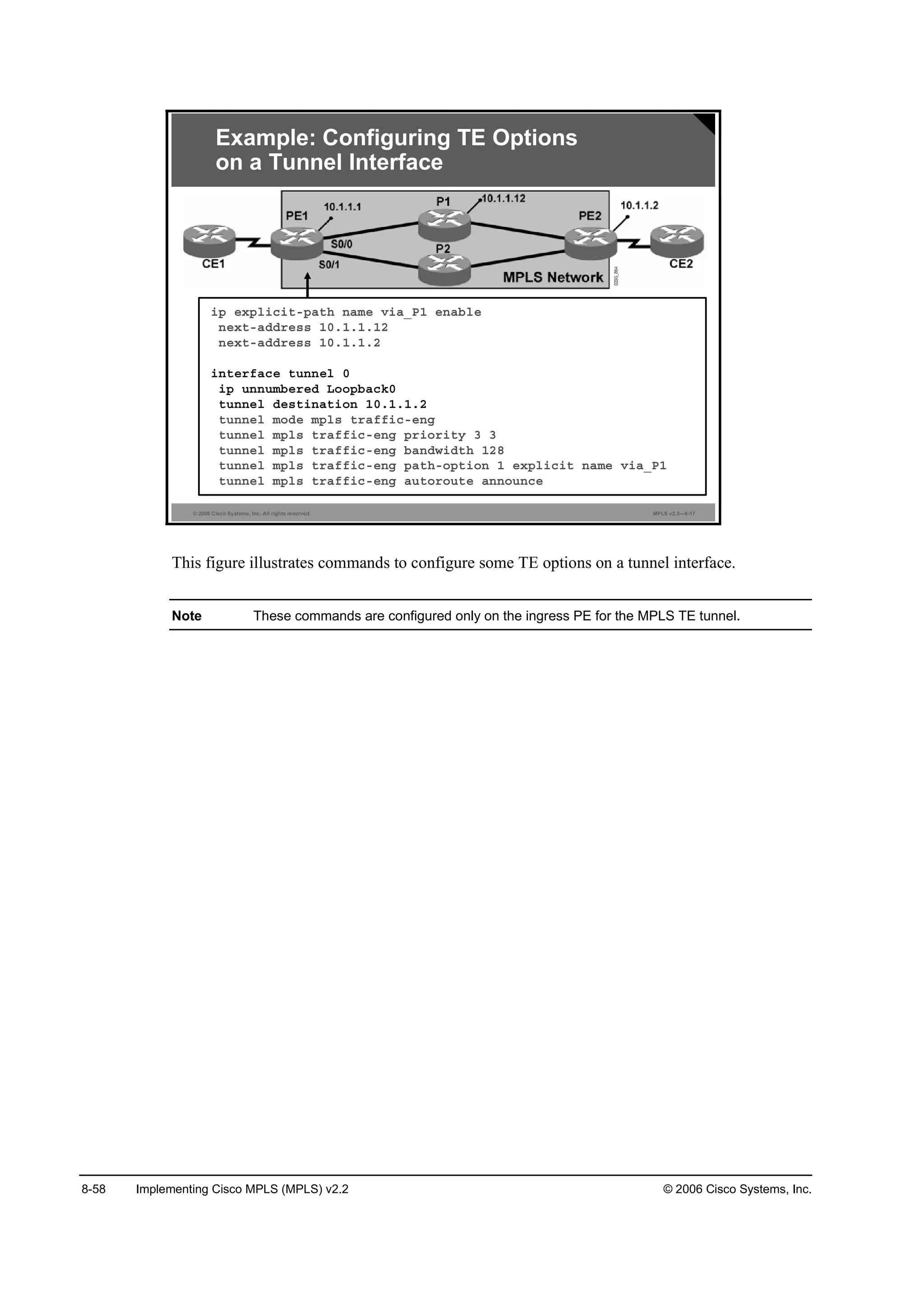

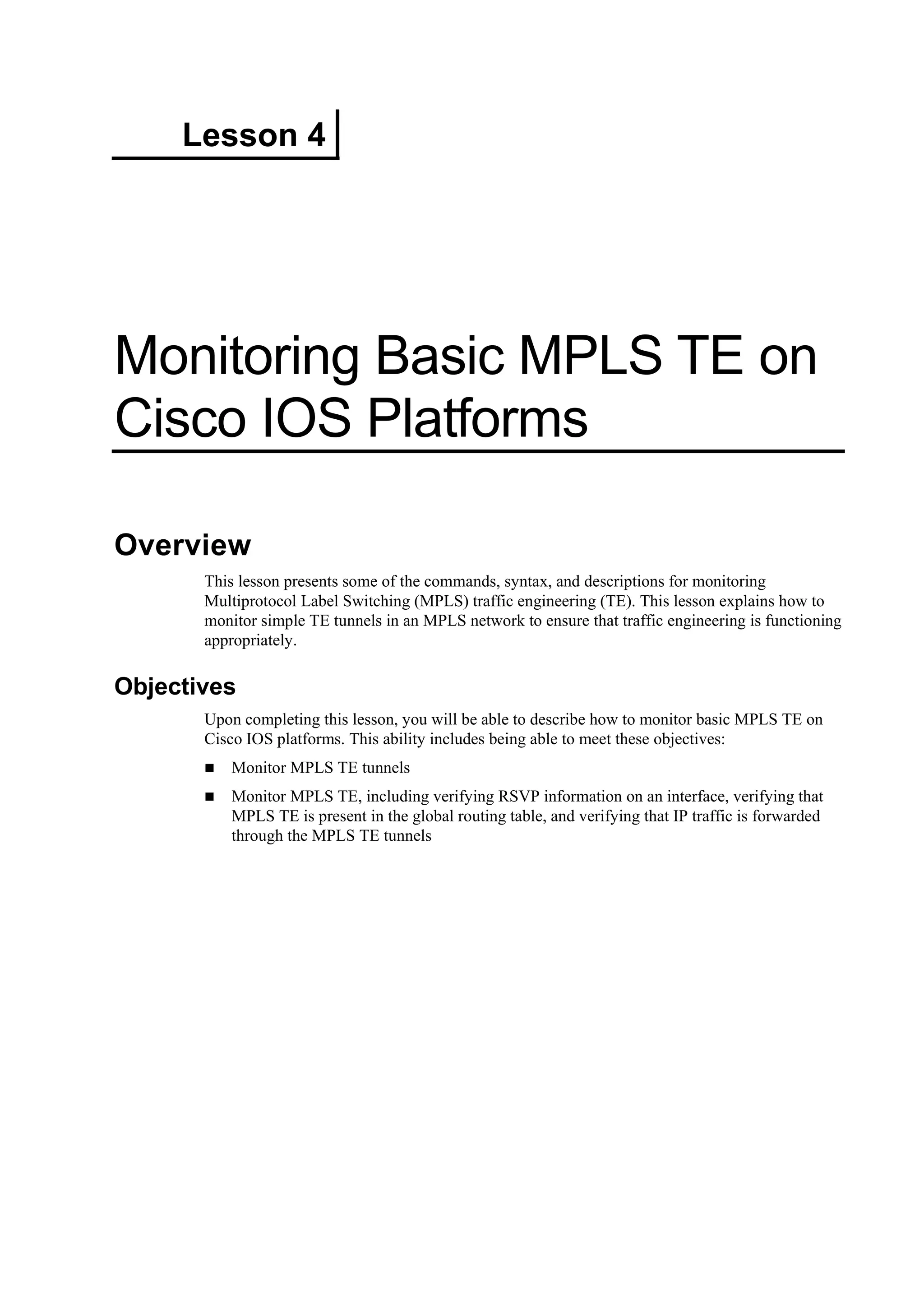
![8-62 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
Monitoring MPLS TE Tunnels
This topic describes how to monitor MPLS TE tunnels.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—7-3
¸±© ł°´ ¬®żşş·˝ó»˛ą ¬«˛˛»´ Ĺ°ż®żł»¬»®Ă
®±«¬»®ý
• Shows detailed information about a tunnel
Monitoring MPLS TE Tunnels
¸±© ł°´ ¬®żşş·˝ó»˛ą ¬«˛˛»´ ¬«˛˛»´Á·˛¬»®şż˝» Ĺľ®·»şĂ
®±«¬»®ý
• Shows summary information about a tunnel
¸±© ·° ®Ş° ·˛¬»®şż˝»
®±«¬»®ý
• Confirms which interfaces have RSVP information configured
show ip rsvp interface
To display Resource Reservation Protocol (RSVP)-related information, use the show ip rsvp
interface command in EXEC mode.
show ip rsvp interface [interface-type interface-number] [detail]
Syntax Description
Parameter Description
·˛¬»®şż˝»ó¬§°» (Optional) Type of interface
·˛¬»®şż˝»ó˛«łľ»® (Optional) Number of interface
Ľ»¬ż·´ (Optional) Displays additional information about interfaces](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-655-2048.jpg)
![© 2006 Cisco Systems, Inc. MPLS TE Overview 8-63
The example shows output from the show ip rsvp interface command.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—7-4
Monitoring MPLS TE Tunnels:
show ip rsvp interface
Đéîý¸±© ·° ®Ş° ·˛¬»®şż˝»
·˛¬»®şż˝» ż´´±˝ż¬»Ľ ·ńş łż¨ ş´±© łż¨ «ľ łż¨
Í»đńđ đ ďîčŐ ďîčŐ đ
Í»đńđňďďď đ ďîčŐ ďîčŐ đ
Í»đńđňďďî đ ďîčŐ ďîčŐ đ
Í»đńđňîéî đ ďîčŐ ďîčŐ đ
show mpls traffic-eng tunnels
To show information about MPLS TE tunnels, use the show mpls traffic-eng tunnels
command.
show mpls traffic-eng tunnels tunnel-interface [brief]
show mpls traffic-eng tunnels [destination address]
[source-id {number | ip-address | ip-address number}]
[role {all | head | middle | tail | remote}] [up | down] [name string]
[suboptimal constraints {none | current | max}] [[interface in physical-interface]
[interface out physical-interface] | [interface physical-interface] [brief]
The table describes the parameters available for the show mpls traffic-eng tunnels command.](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-656-2048.jpg)
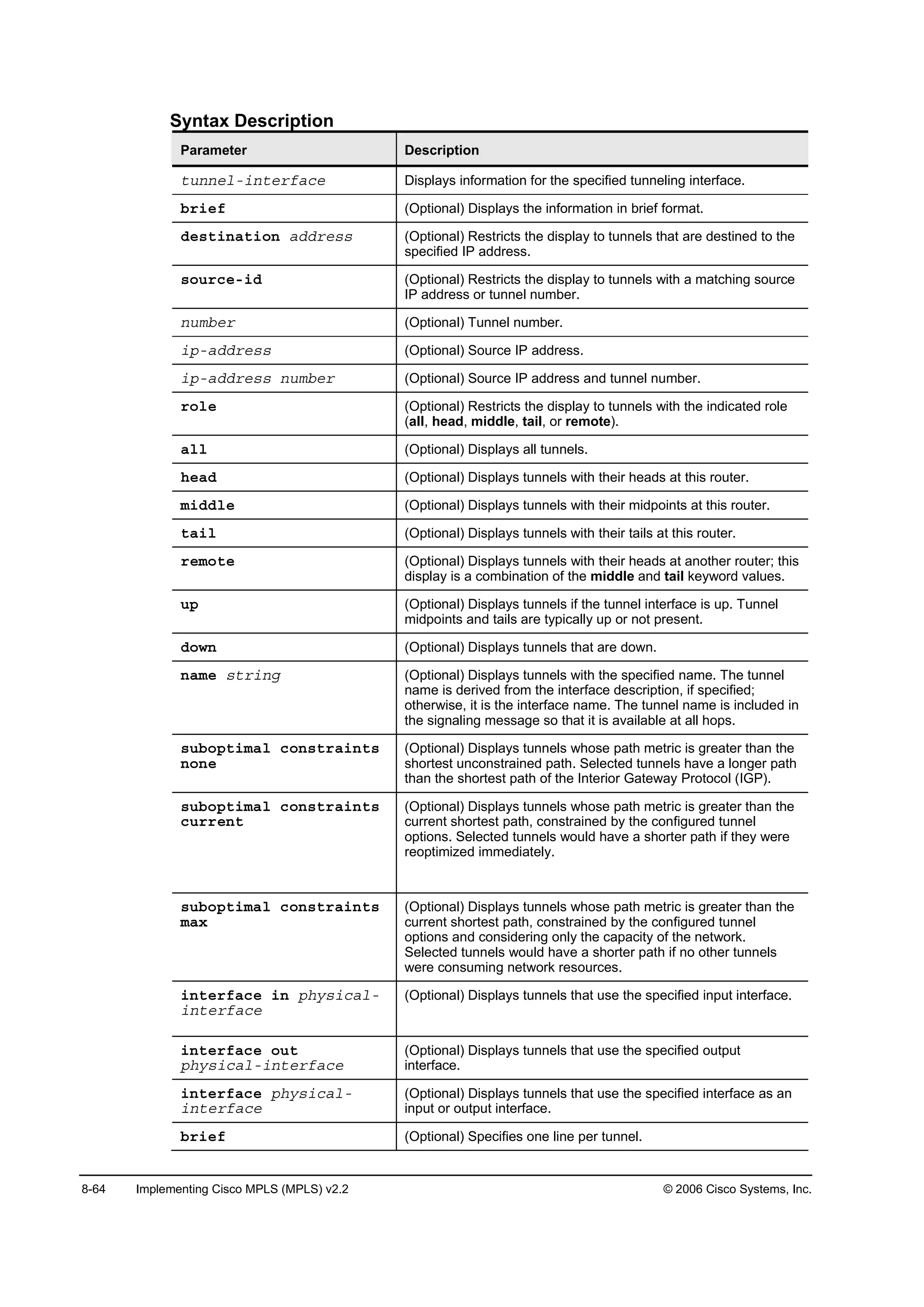
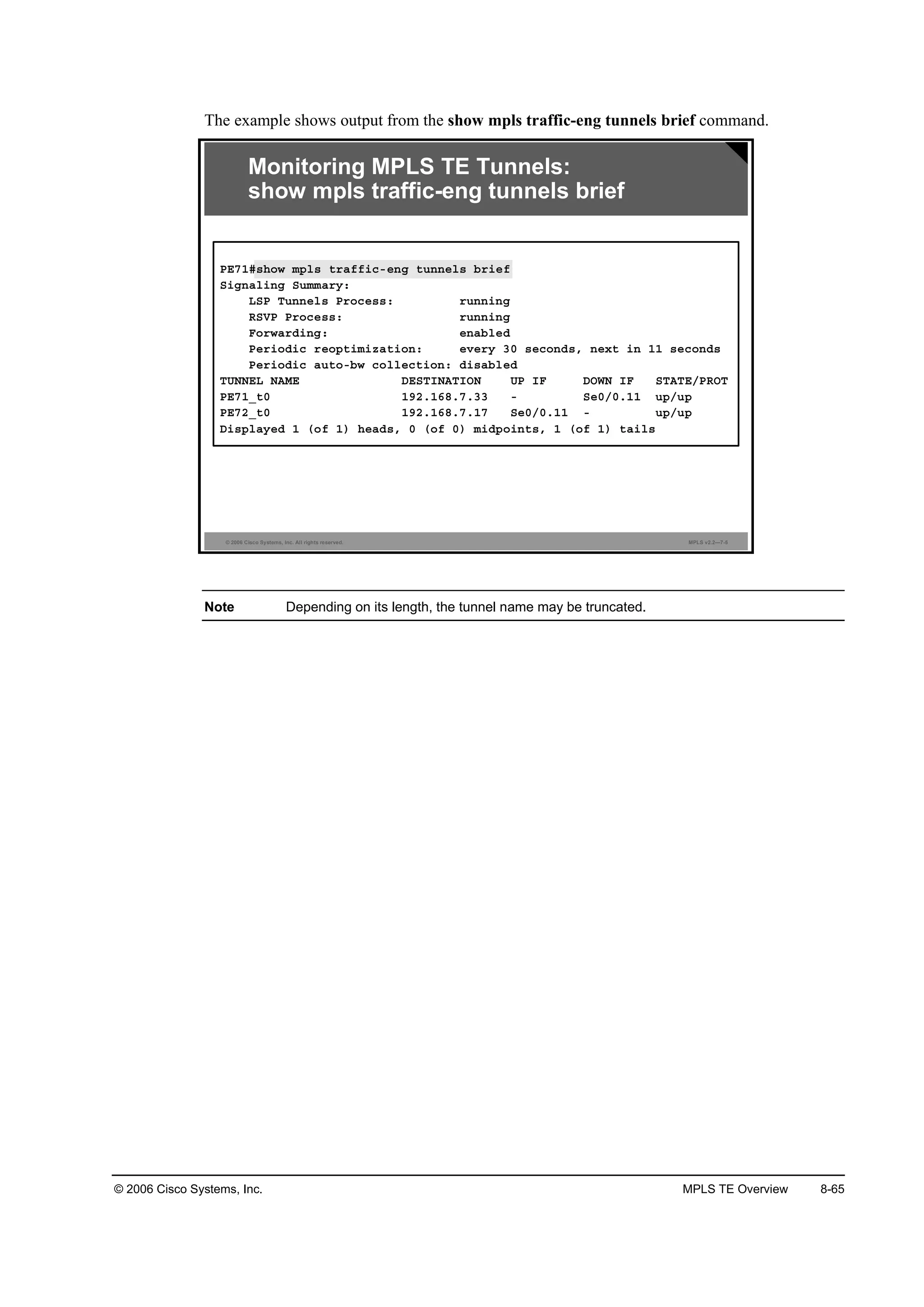
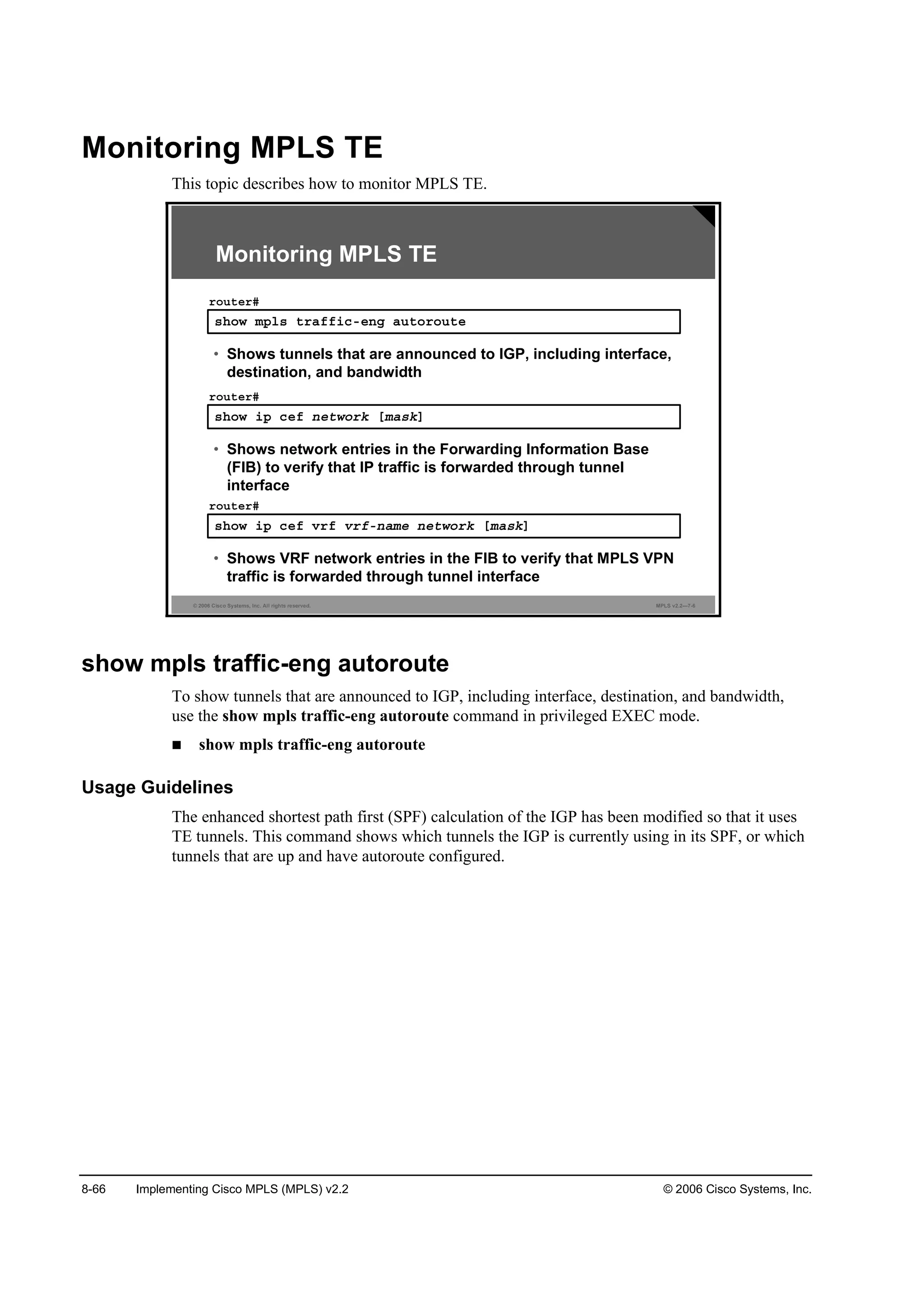
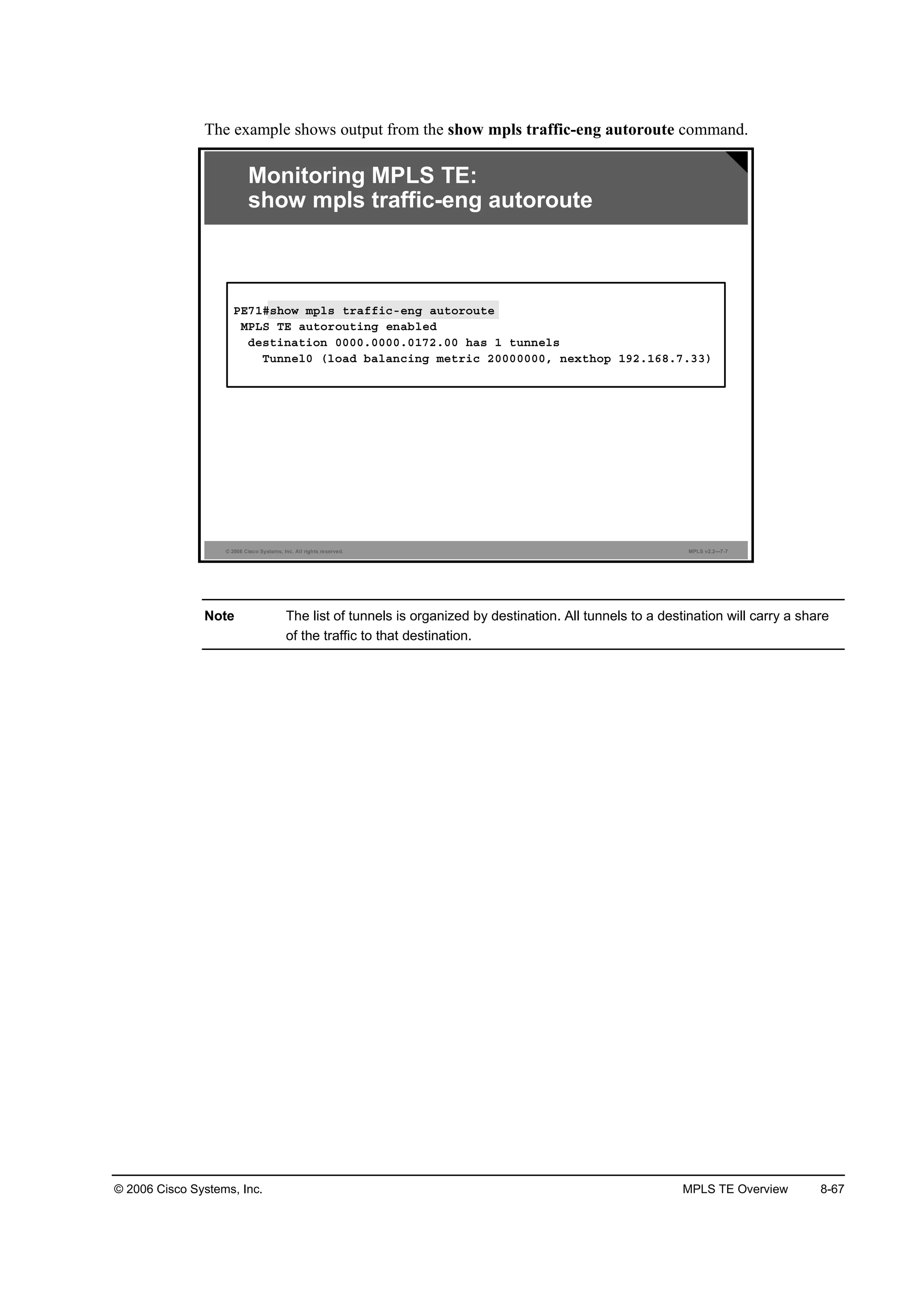
![8-68 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
show ip cef network
To verify that IP traffic is forwarded through a tunnel interface, use the show ip cef network
command in privileged EXEC mode.
show ip cef network [mask]
The example shows output from the show ip cef network command.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—7-8
Monitoring MPLS TE:
show ip cef network
ĐŰéďý¸±© ·° ˝»ş ďçîňďęčňéňíí
ďçîňďęčňéňííńíîô Ş»®·±˛ îëô »°±˝¸ đ
đ °ż˝µ»¬ô 𠾧¬»
¬żą ·˛ş±®łż¬·±˛ »¬ô ¸ż®»Ľ
´±˝ż´ ¬żąć íđ
şż¬ ¬żą ®»©®·¬» ©·¬¸ Ě«đô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄííŁ
Ş·ż ďçîňďęčňéňííô Ě«˛˛»´đô ďď Ľ»°»˛Ľ»˛˝·»
˛»¨¬ ¸±° ďçîňďęčňéňííô Ě«˛˛»´đ
Şż´·Ľ żĽ¶ż˝»˛˝§
¬żą ®»©®·¬» ©·¬¸ Ě«đô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć ĄííŁ](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-661-2048.jpg)
![© 2006 Cisco Systems, Inc. MPLS TE Overview 8-69
show ip cef vrf vrf-name network
To verify that Virtual Private Network (VPN) traffic is forwarded through a tunnel interface,
use the show ip cef vrf vrf-name network command in privileged EXEC mode.
show ip cef vrf vrf-name network [mask]
The example shows output from the show ip cef vrf vrf-name network command.
© 2006 Cisco Systems, Inc. All rights reserved. MPLS v2.2—7-9
Monitoring MPLS TE:
show ip cef vrf vrf-name network
ĐŰéďý¸±© ·° ˝»ş Ş®ş Ý«¬ß ďđňďňéîňěç
ďđňďňéîňěçńíîô Ş»®·±˛ îđô »°±˝¸ đ
đ °ż˝µ»¬ô 𠾧¬»
¬żą ·˛ş±®łż¬·±˛ »¬
´±˝ż´ ¬żąć ĘĐŇ󮱫¬»ó¸»żĽ
şż¬ ¬żą ®»©®·¬» ©·¬¸ Ě«đô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć Ąíí íěŁ
Ş·ż ďçîňďęčňéňííô đ Ľ»°»˛Ľ»˛˝·»ô ®»˝«®·Ş»
˛»¨¬ ¸±° ďçîňďęčňéňííô Ě«˛˛»´đ Ş·ż ďçîňďęčňéňííńíî
Şż´·Ľ żĽ¶ż˝»˛˝§
¬żą ®»©®·¬» ©·¬¸ Ě«đô °±·˛¬î°±·˛¬ô ¬żą ·ł°±»Ľć Ąíí íěŁ](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-662-2048.jpg)
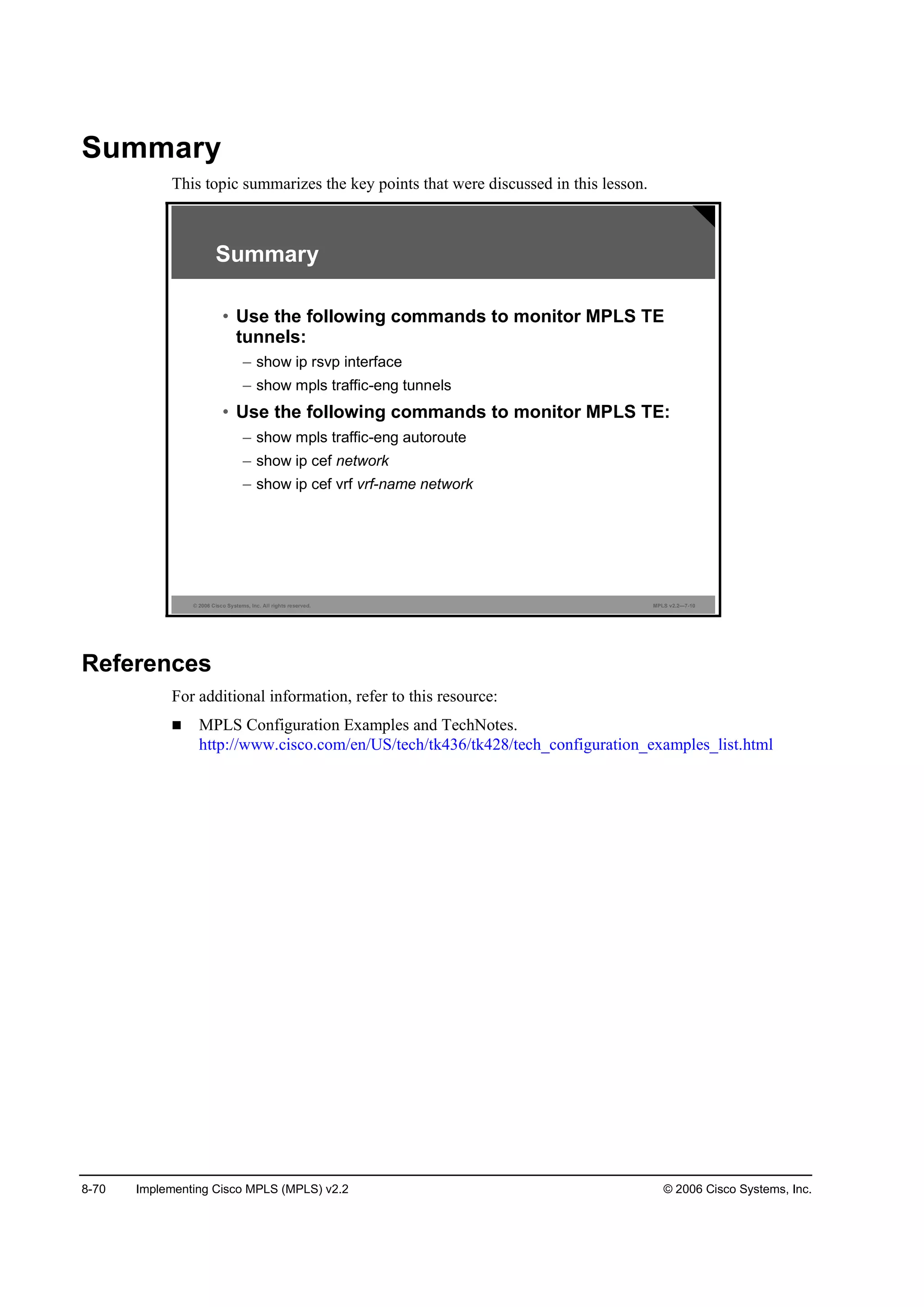
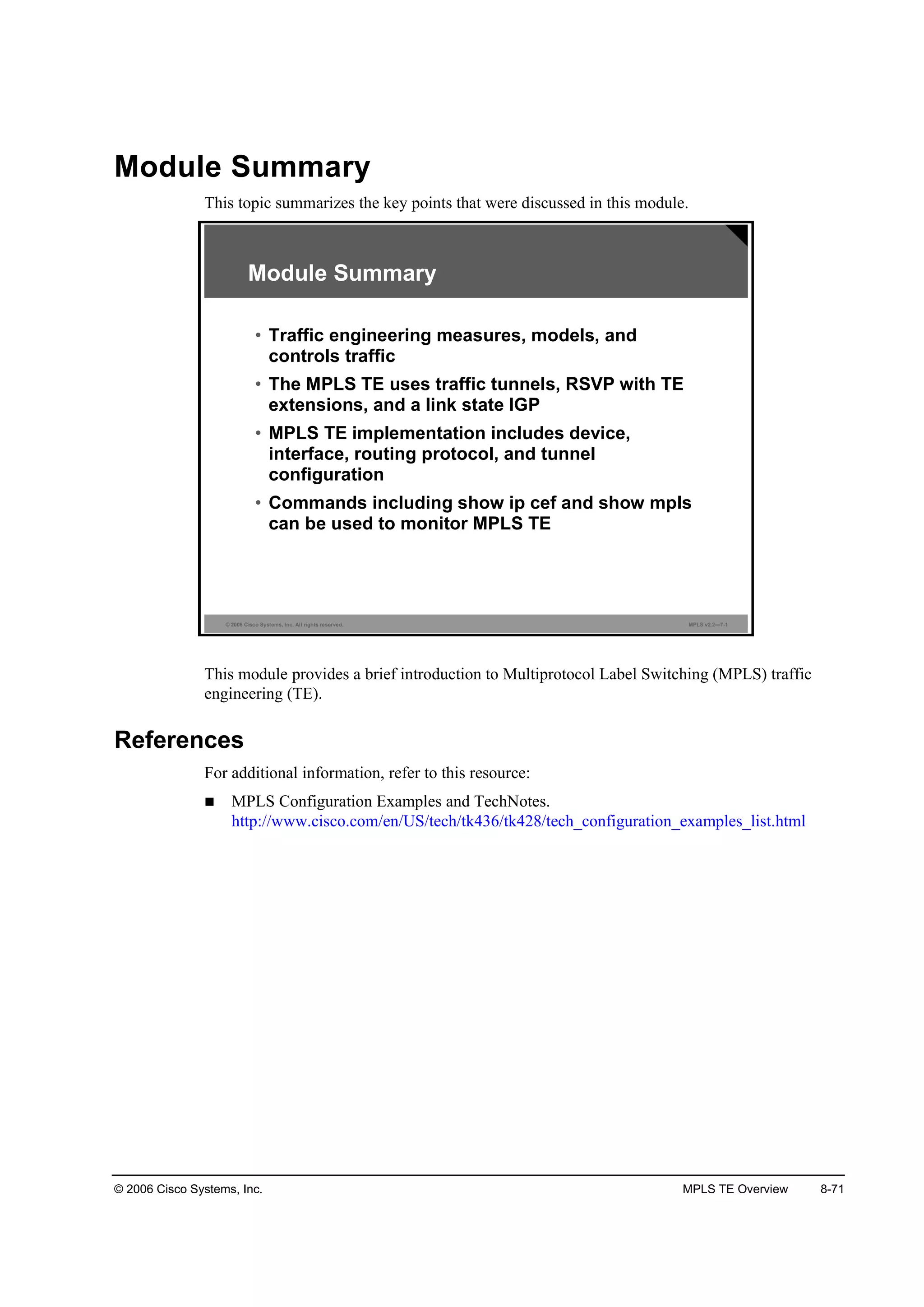

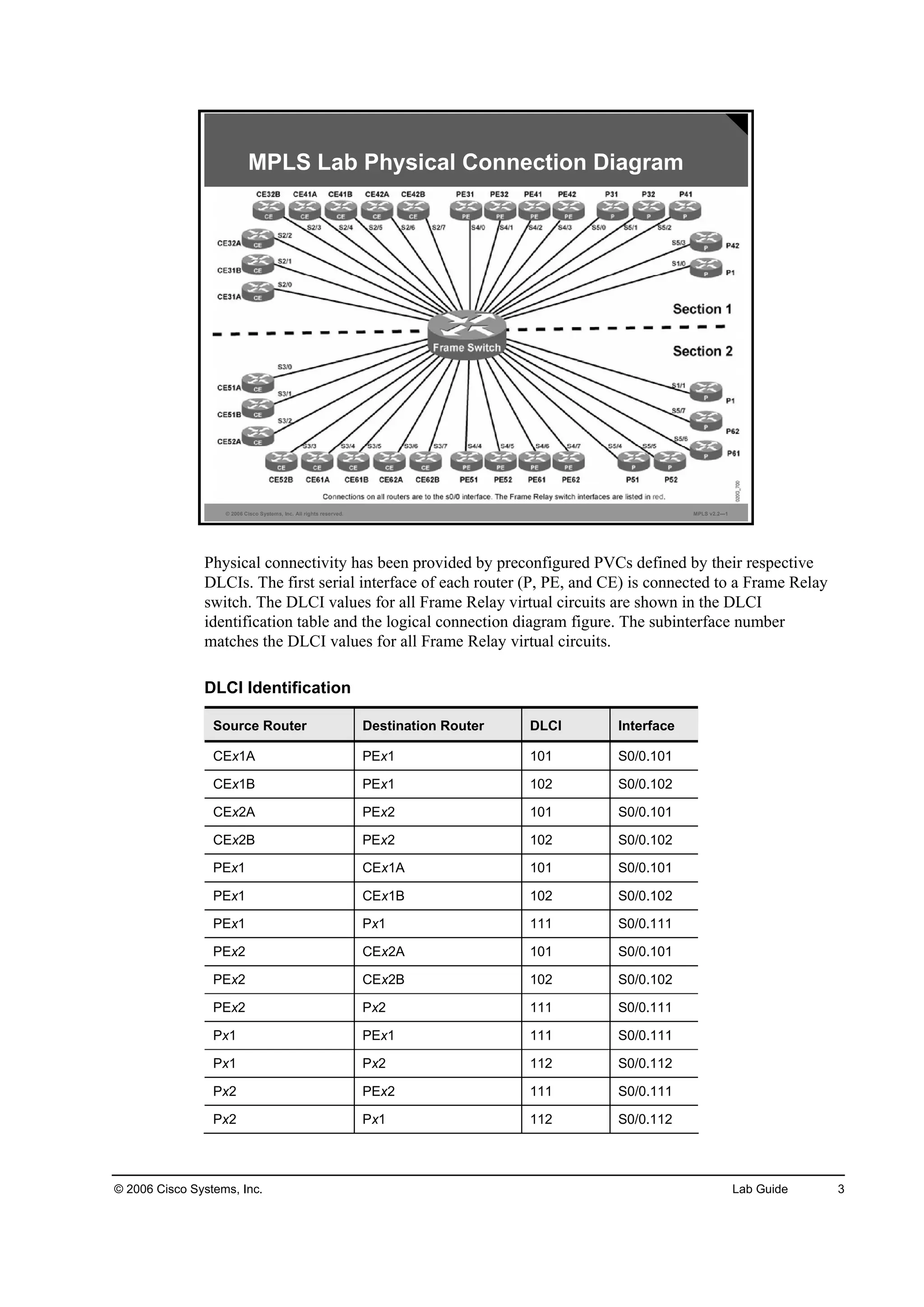
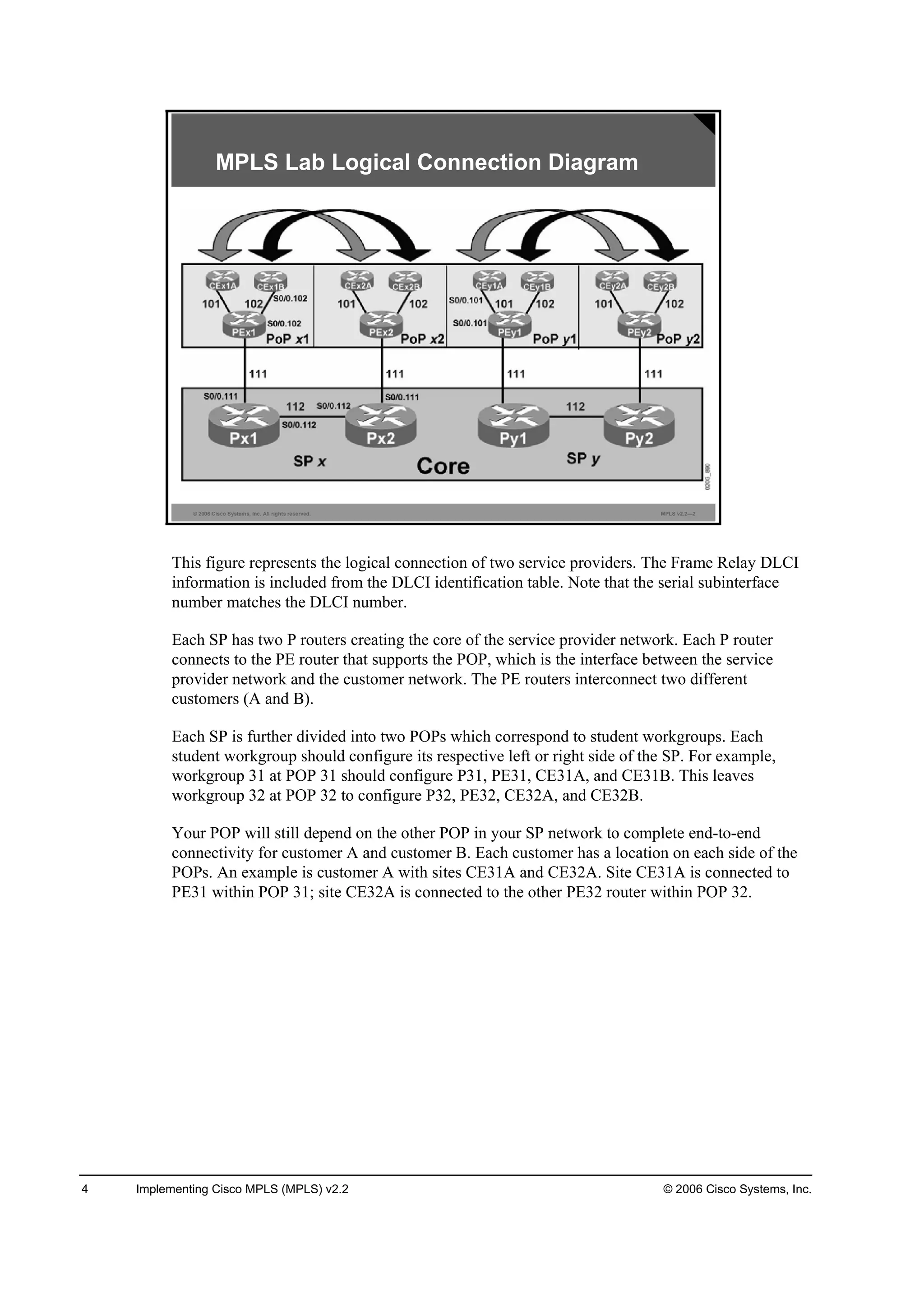
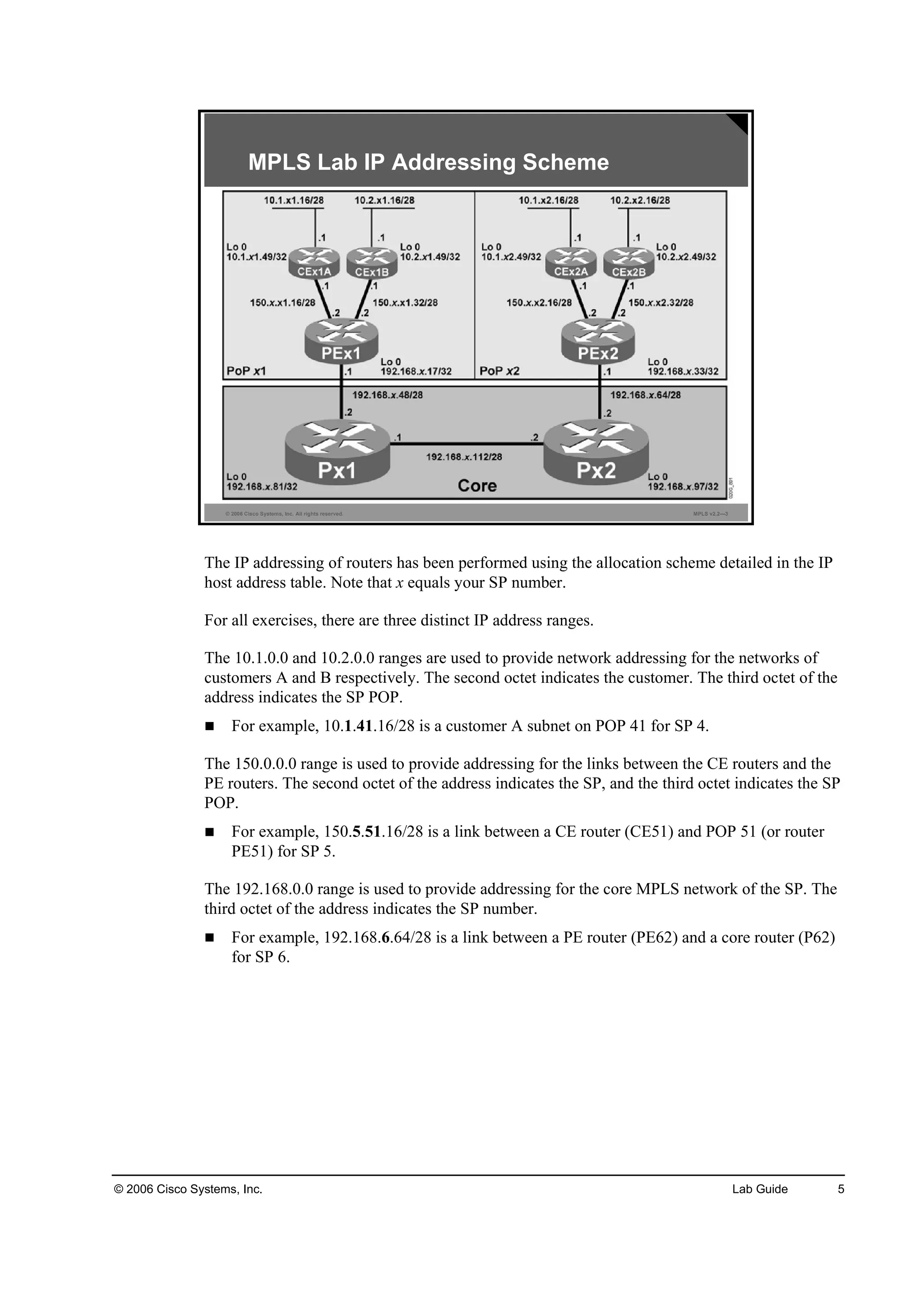
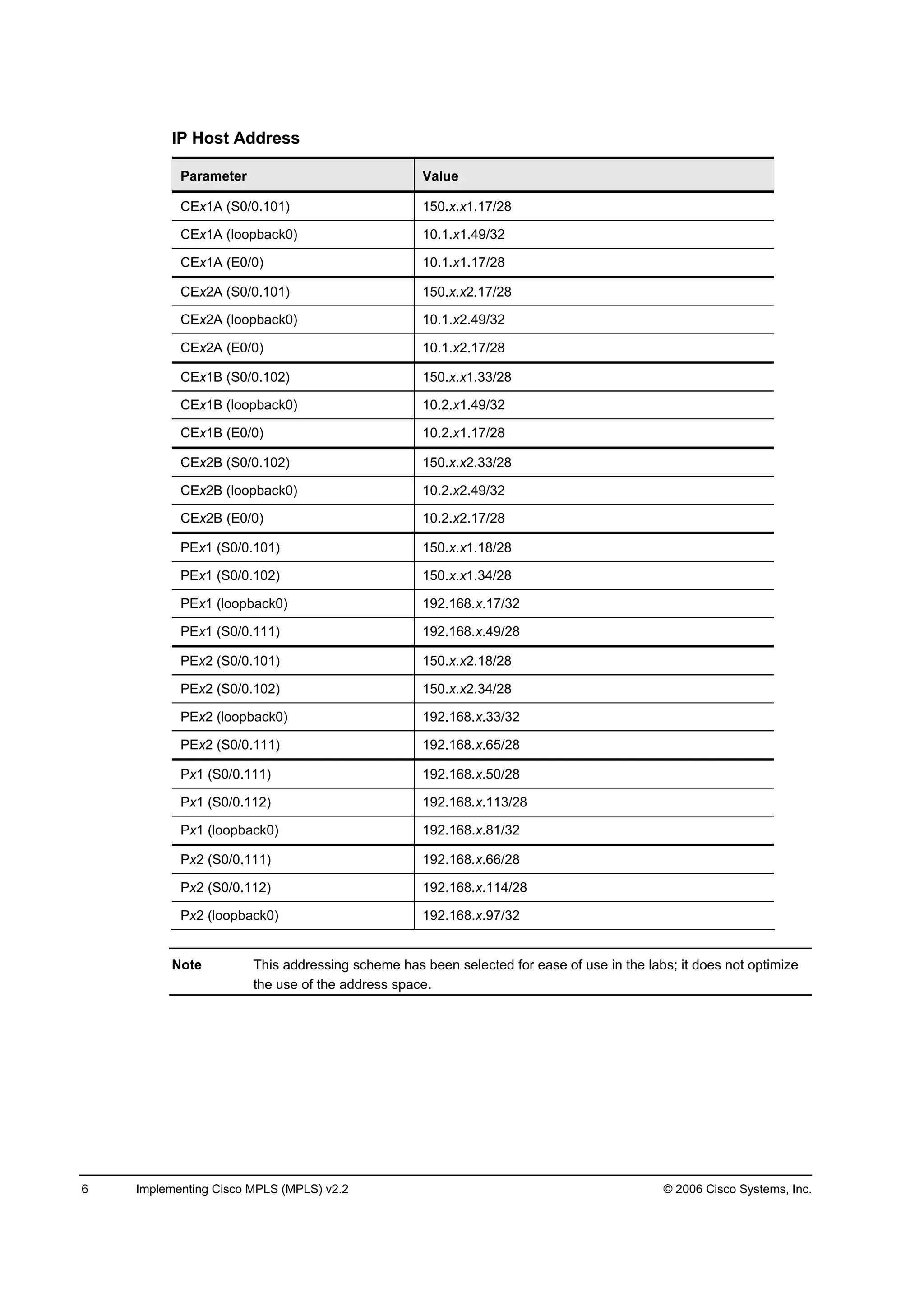
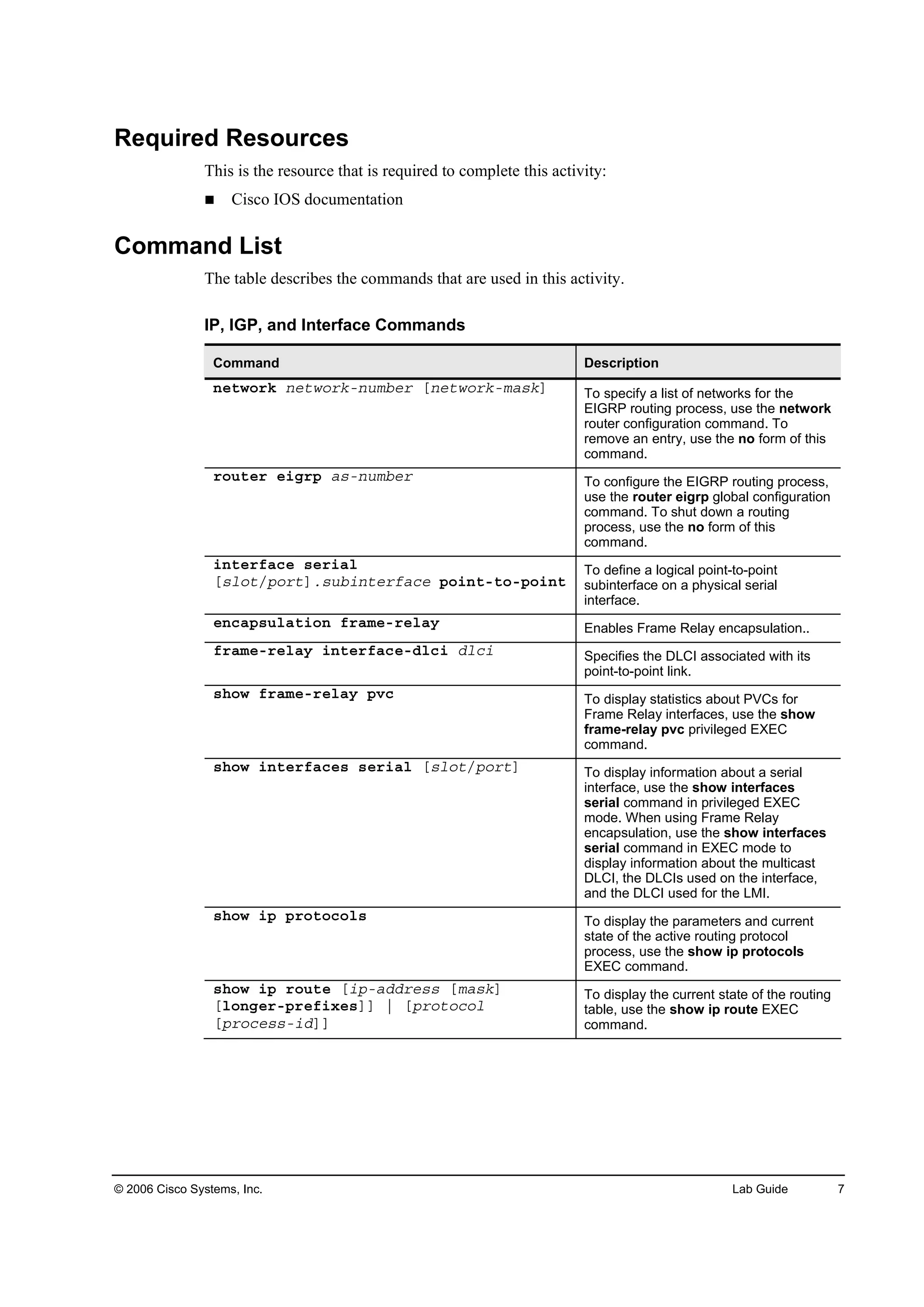
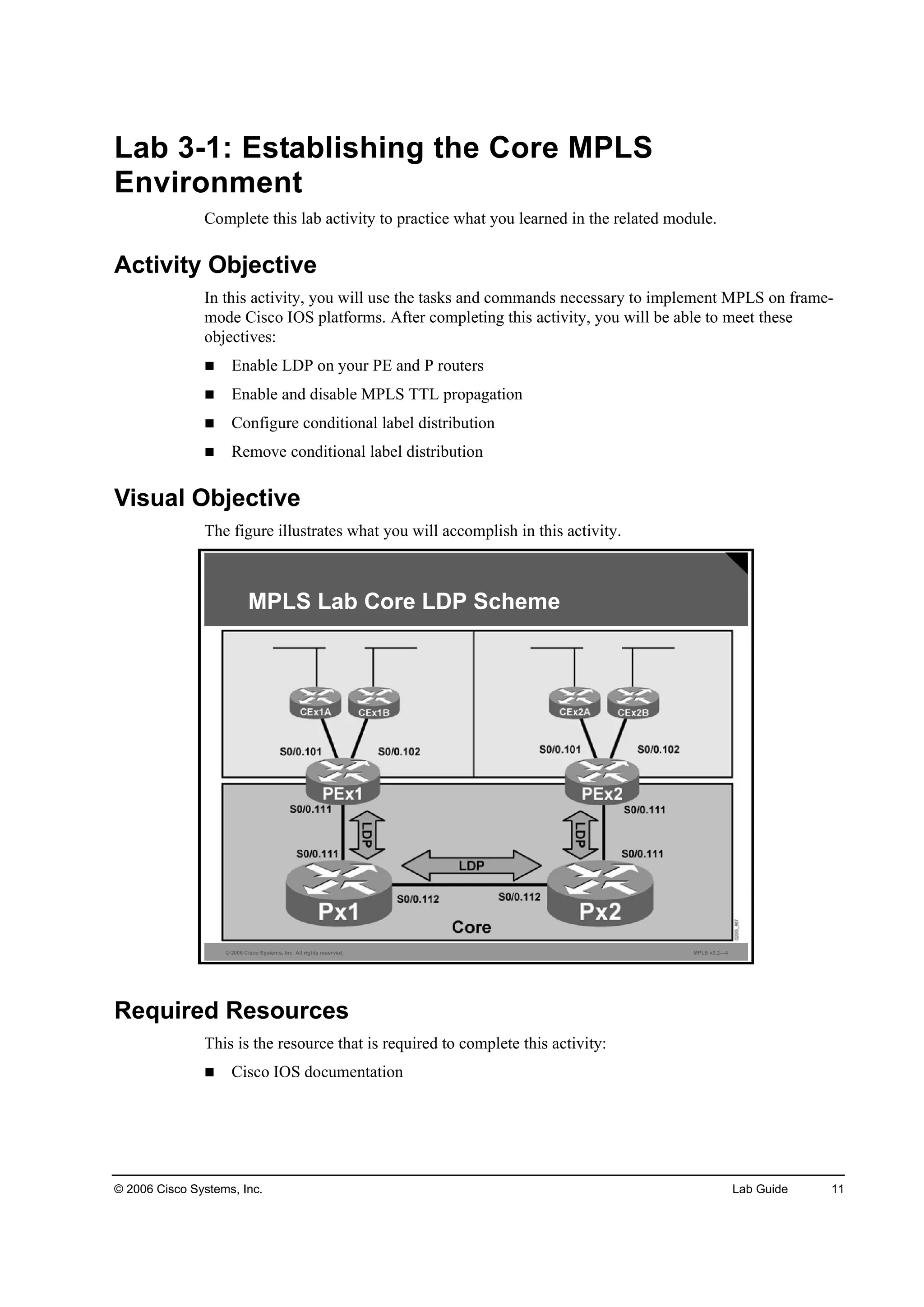
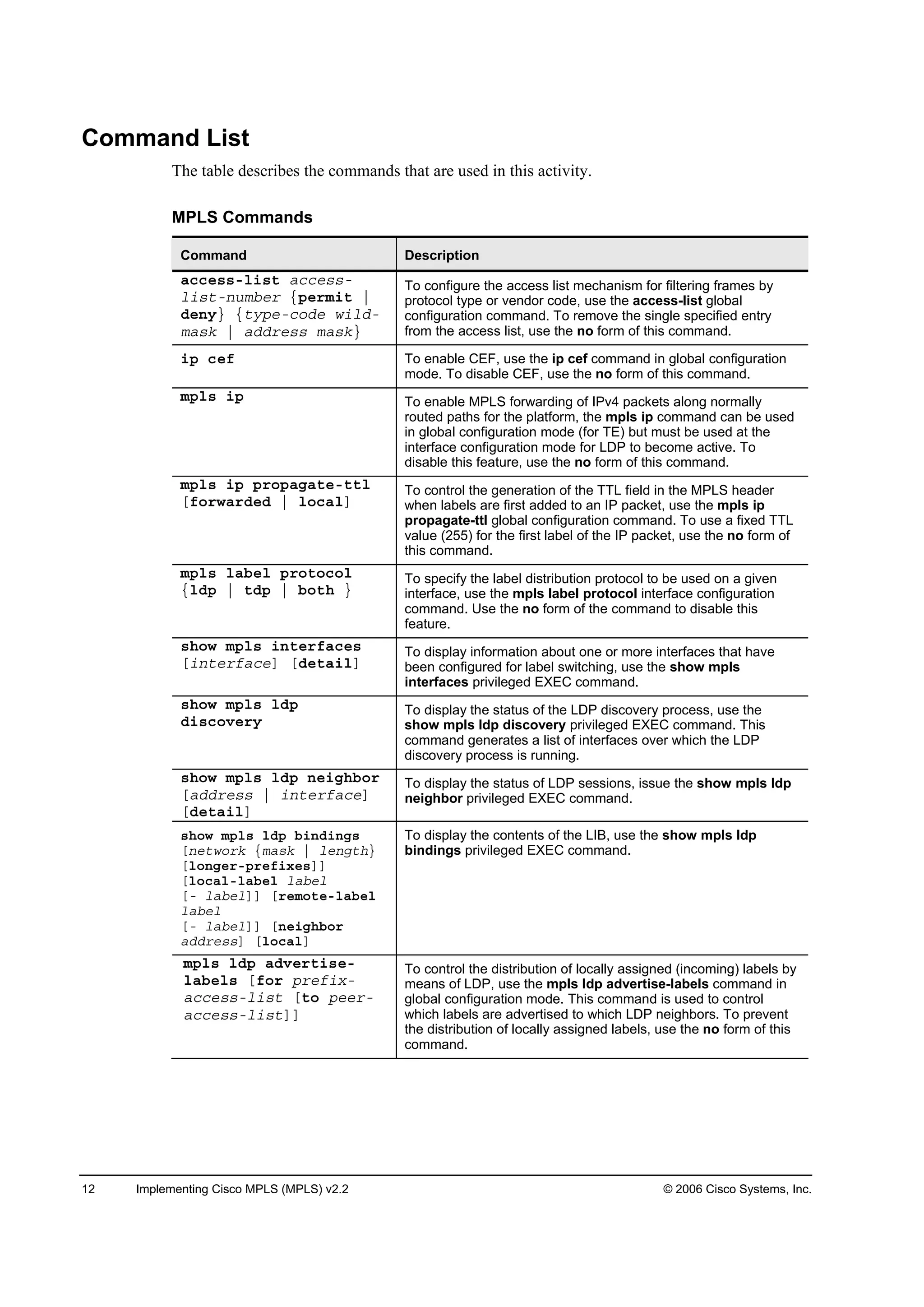
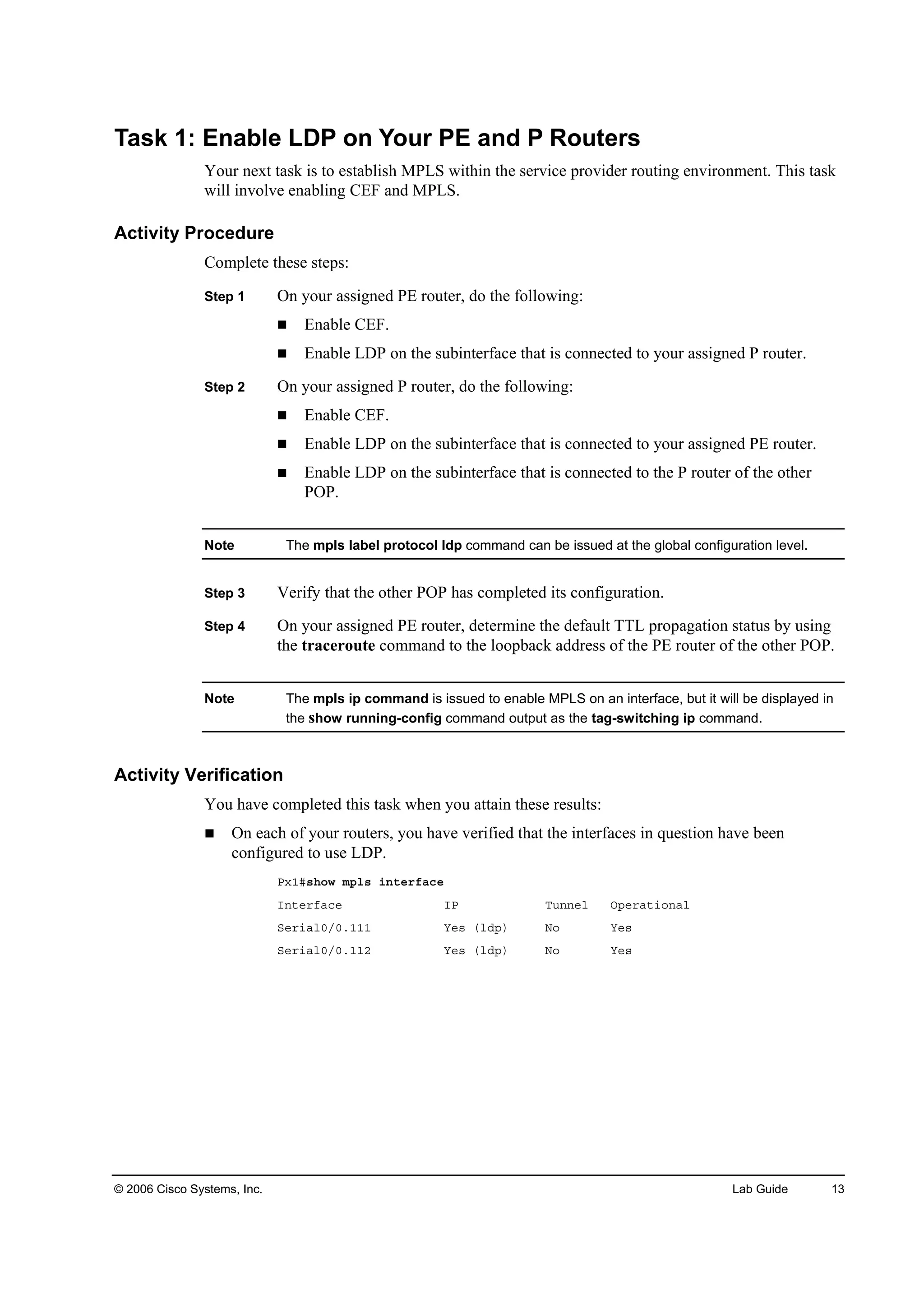
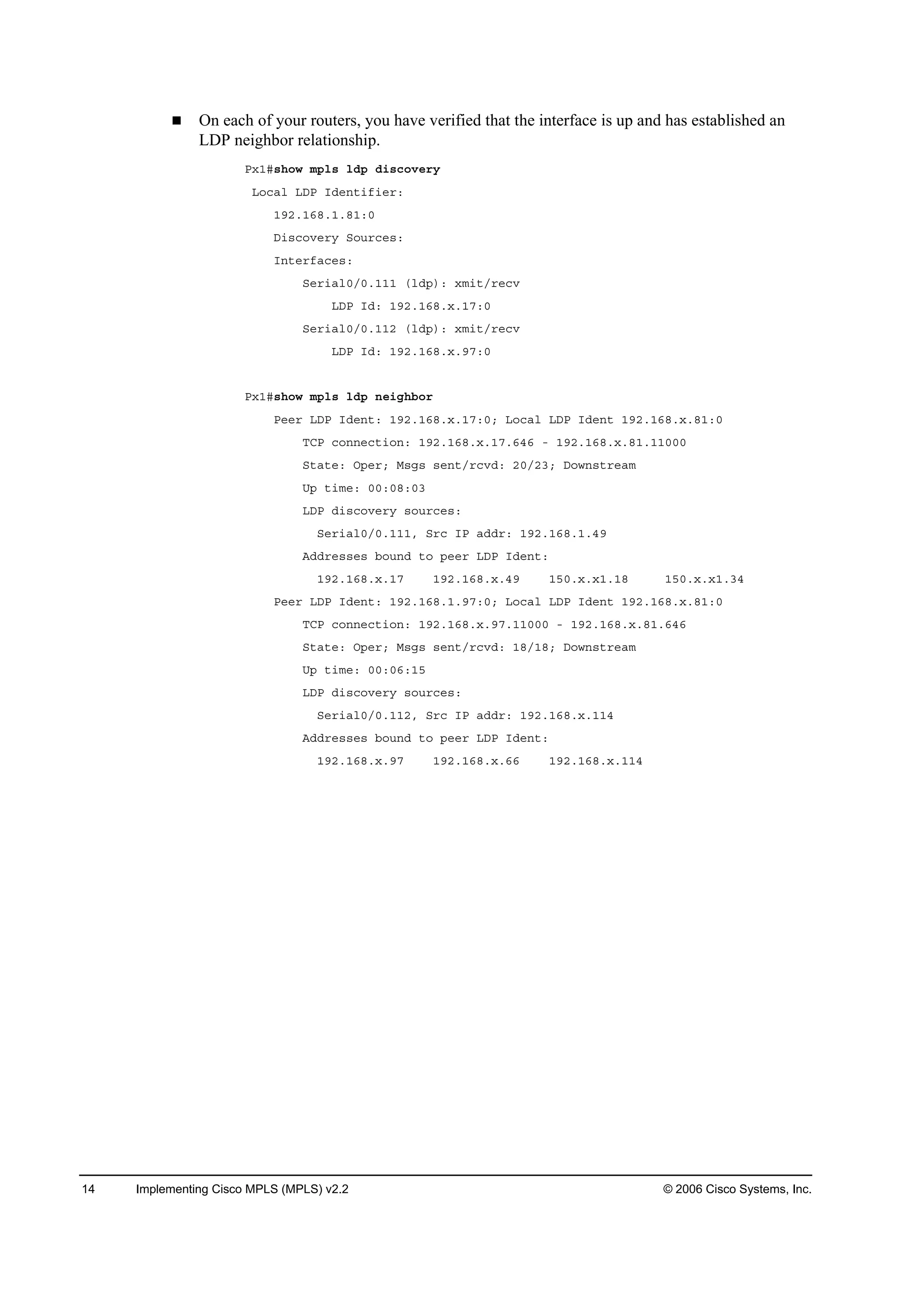
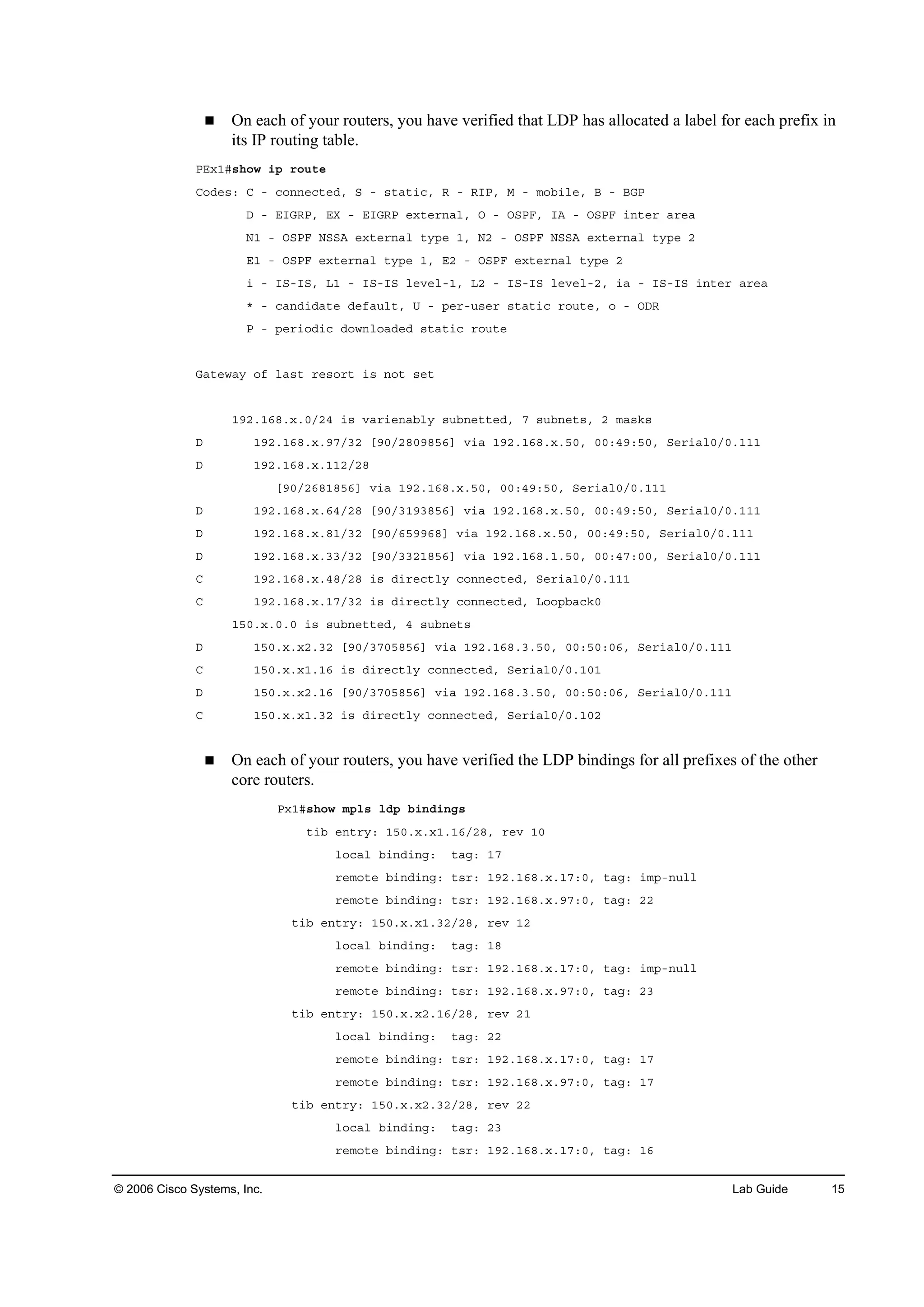
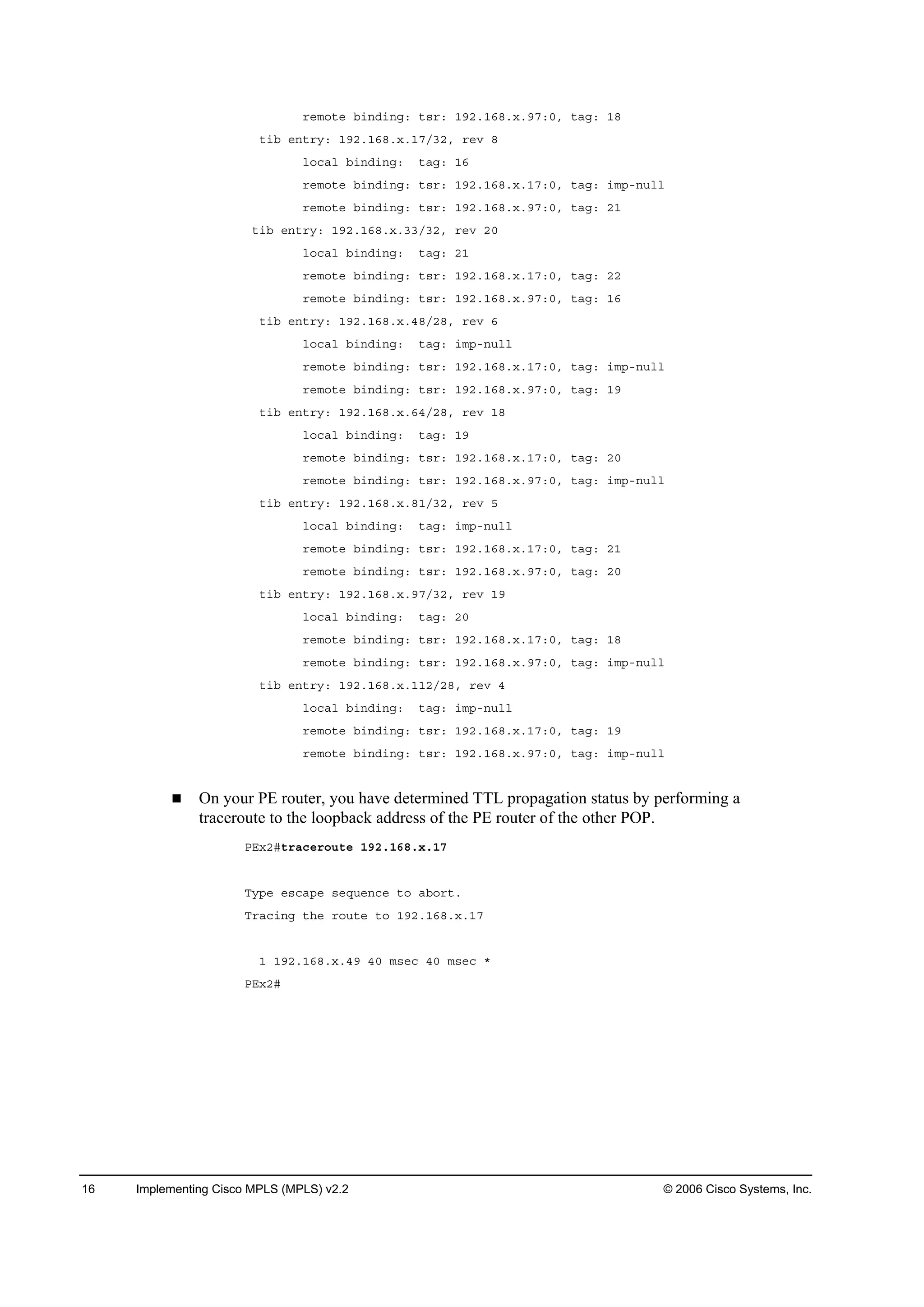
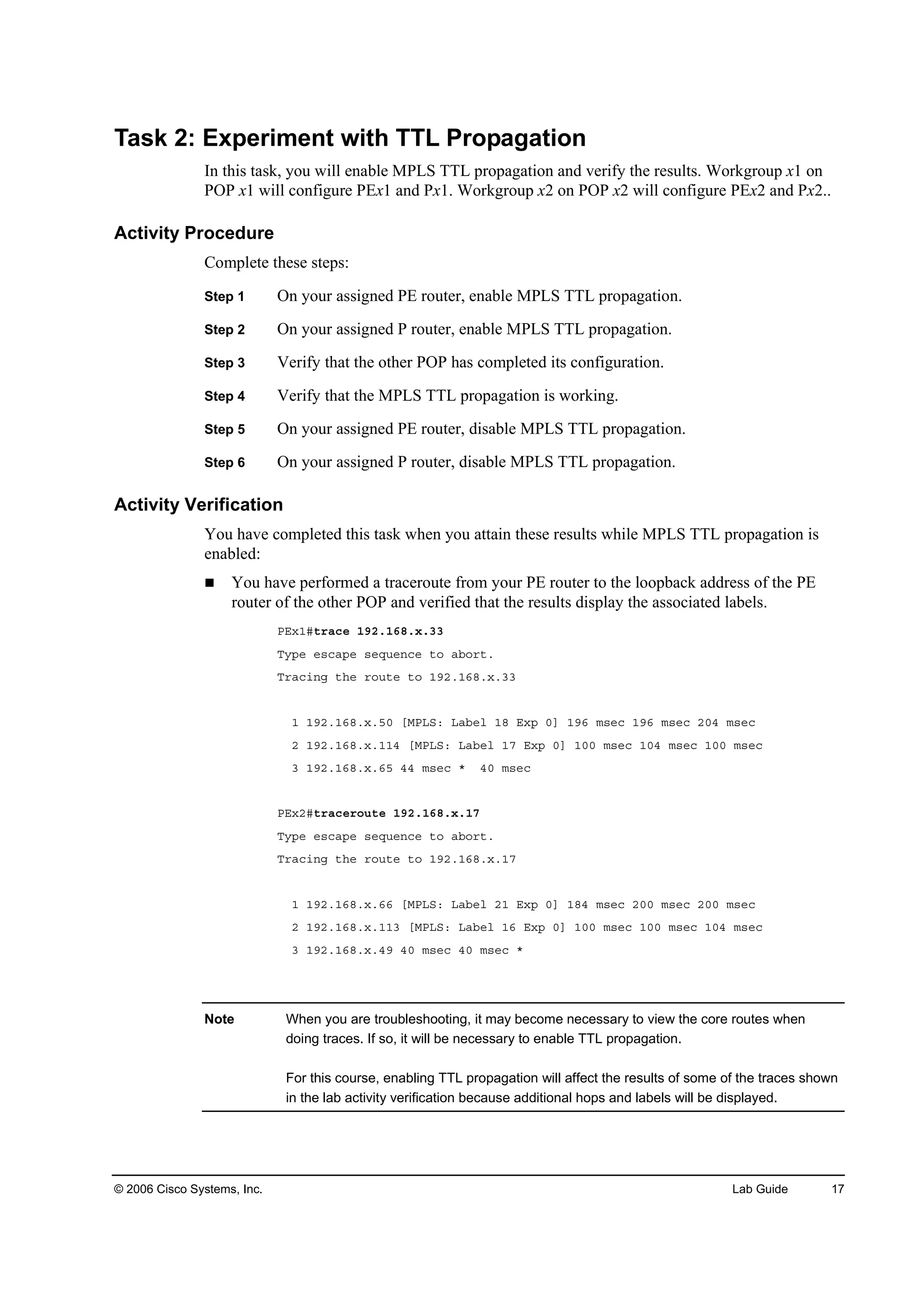
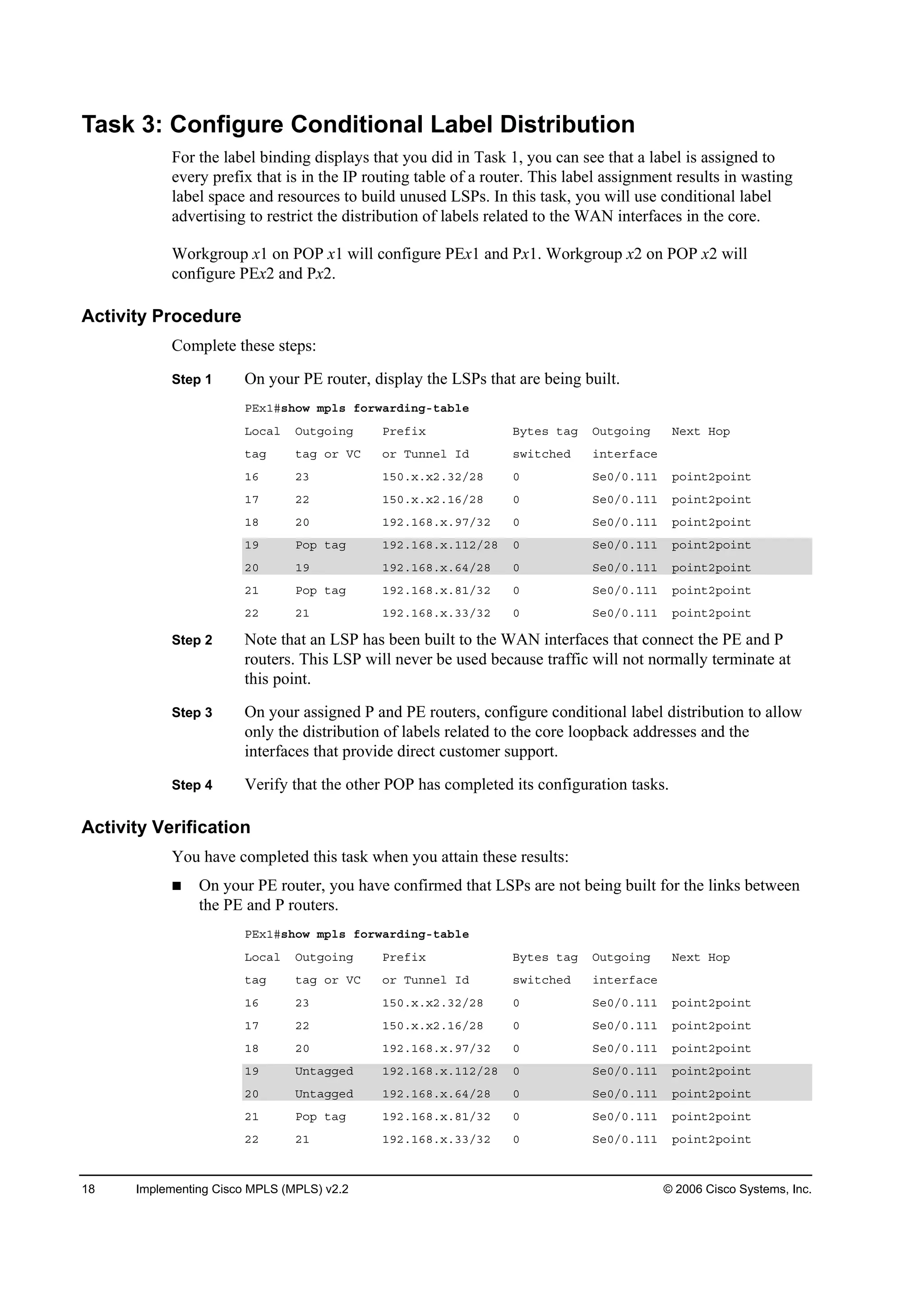
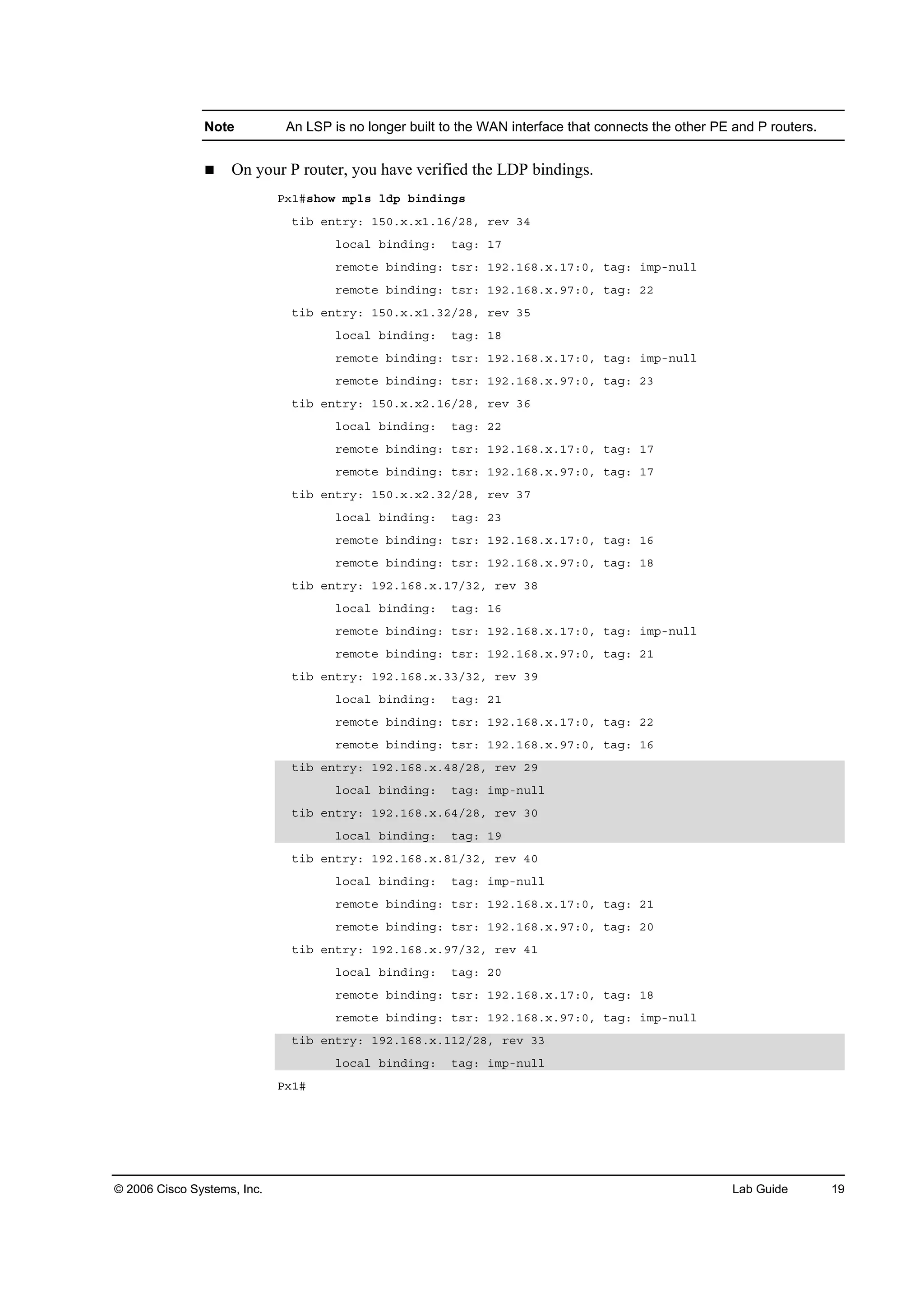
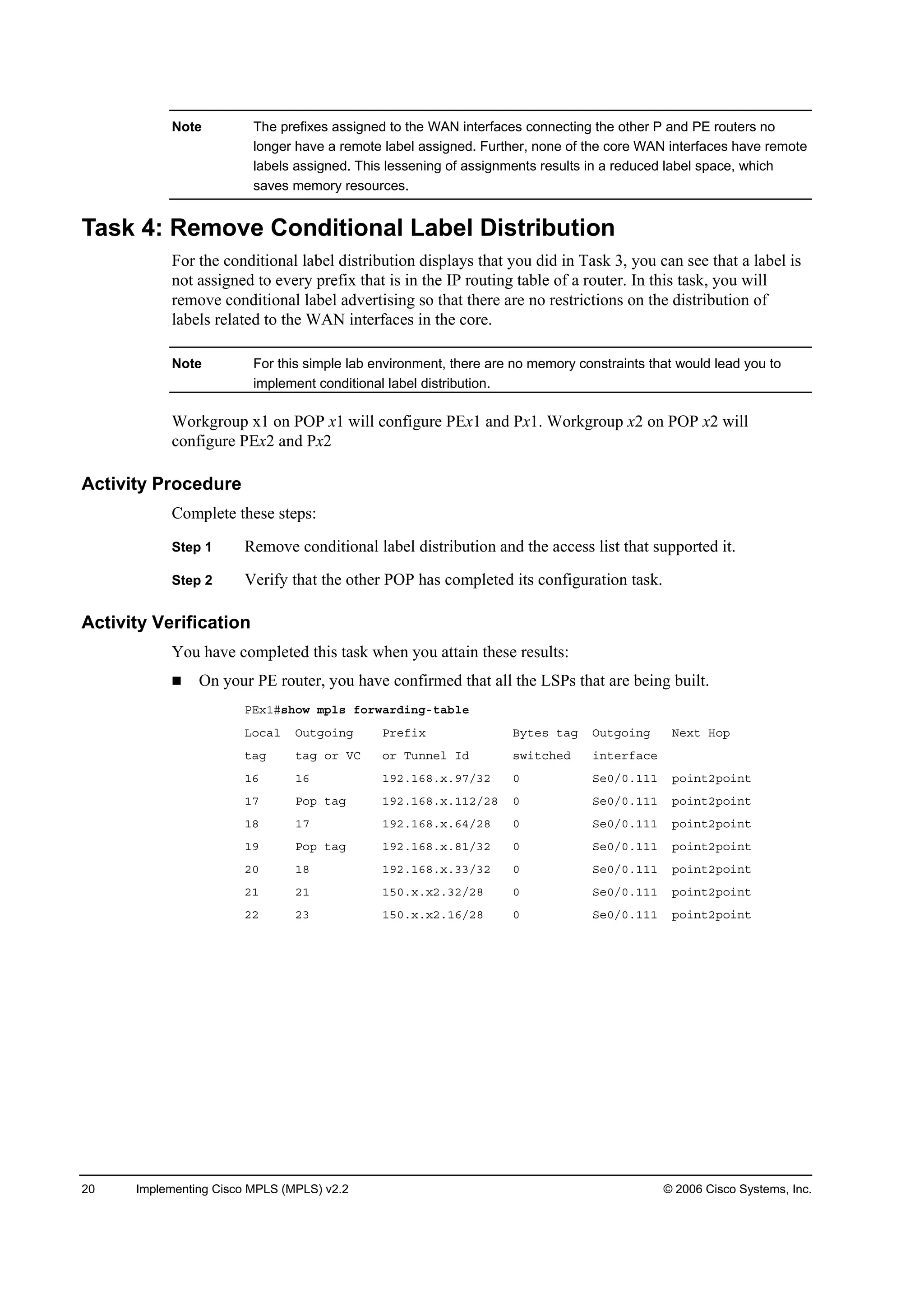
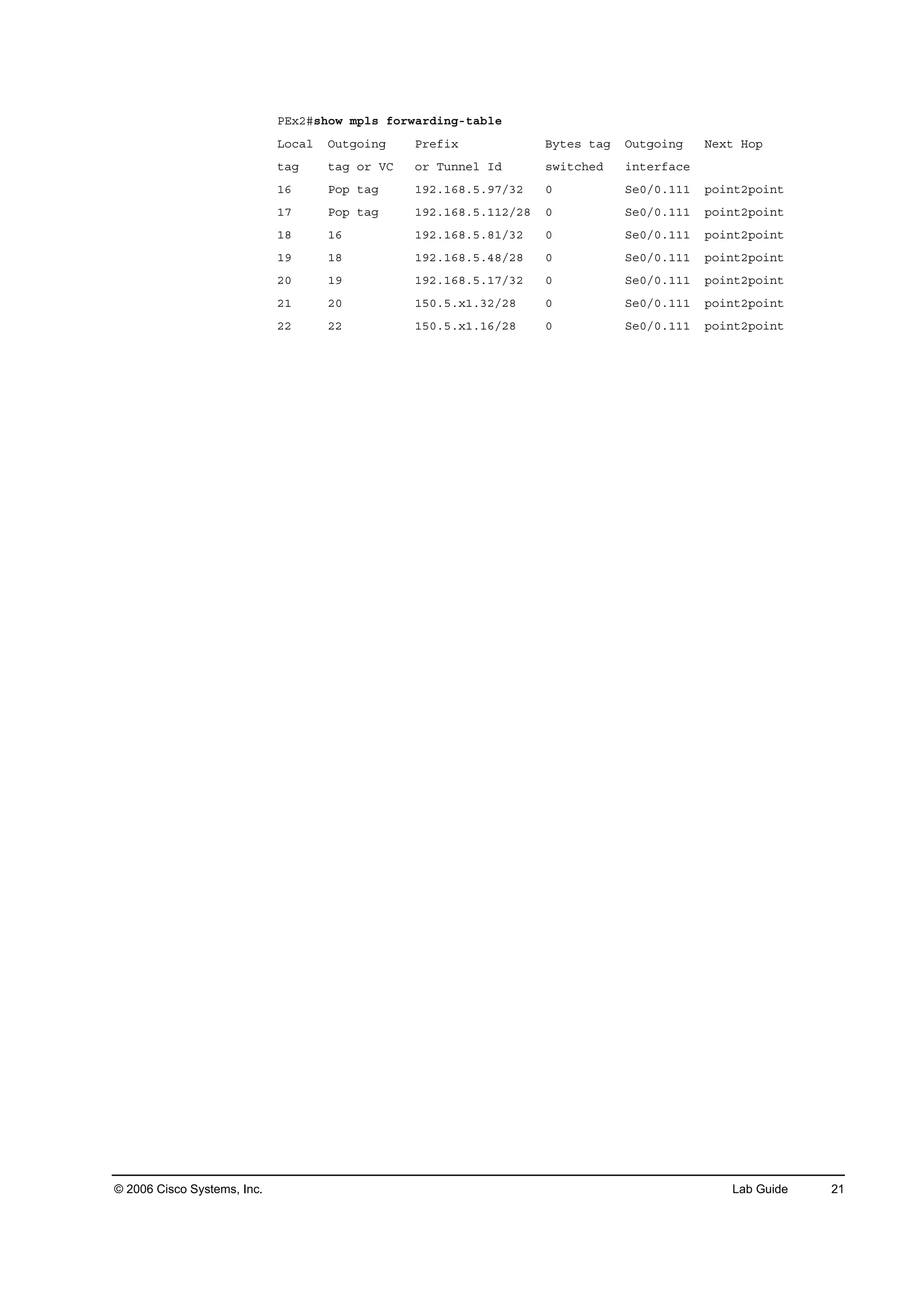
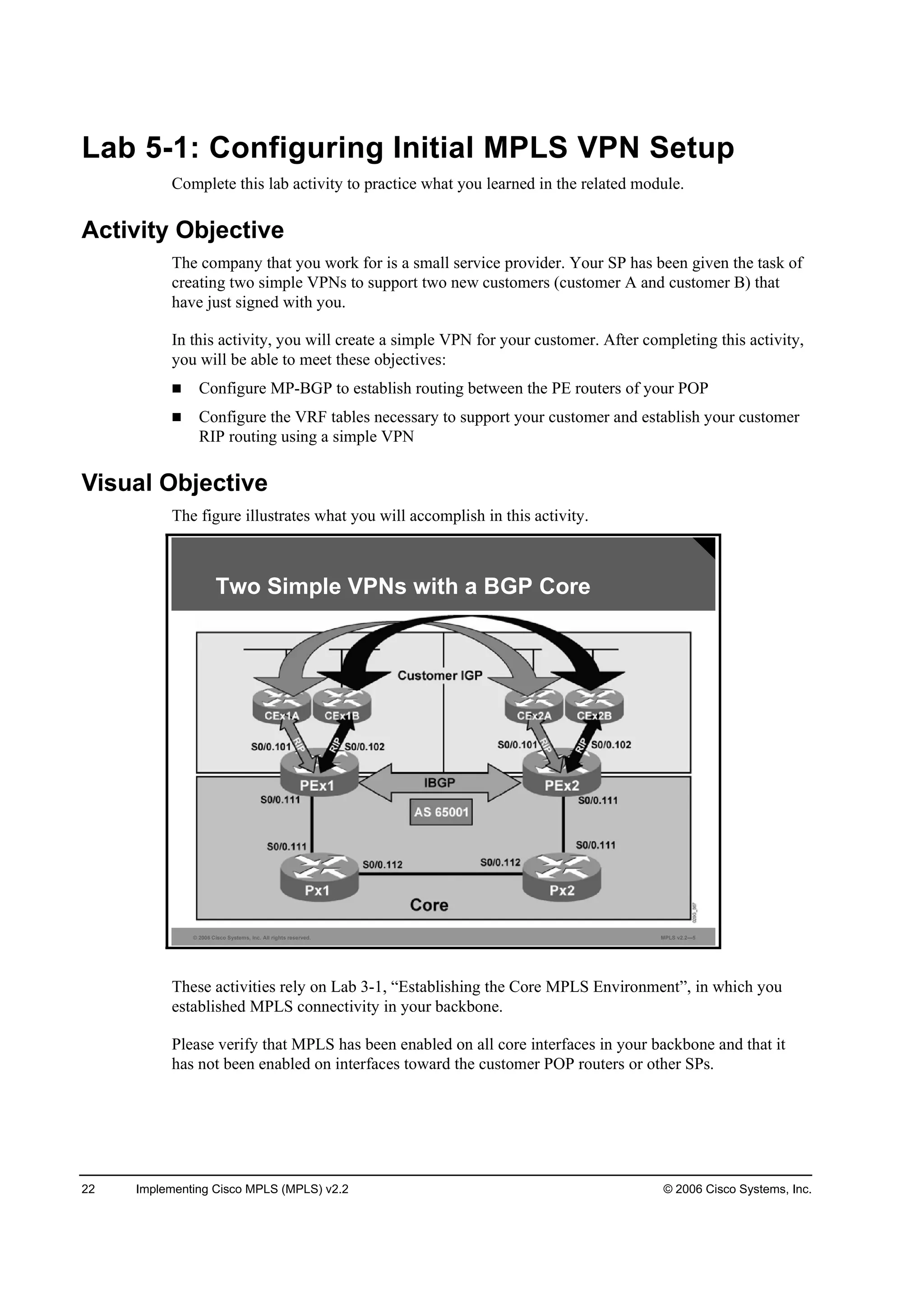
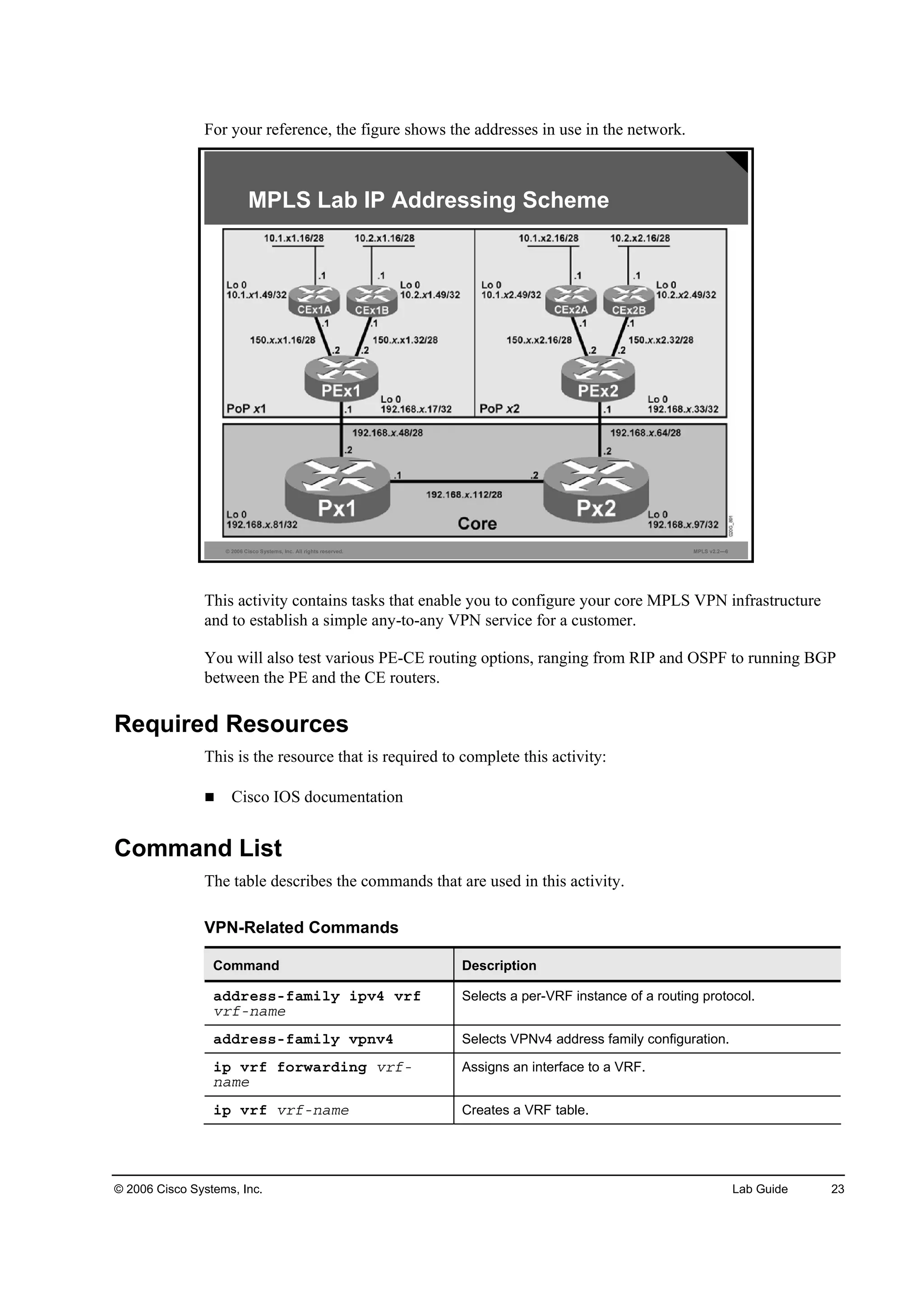
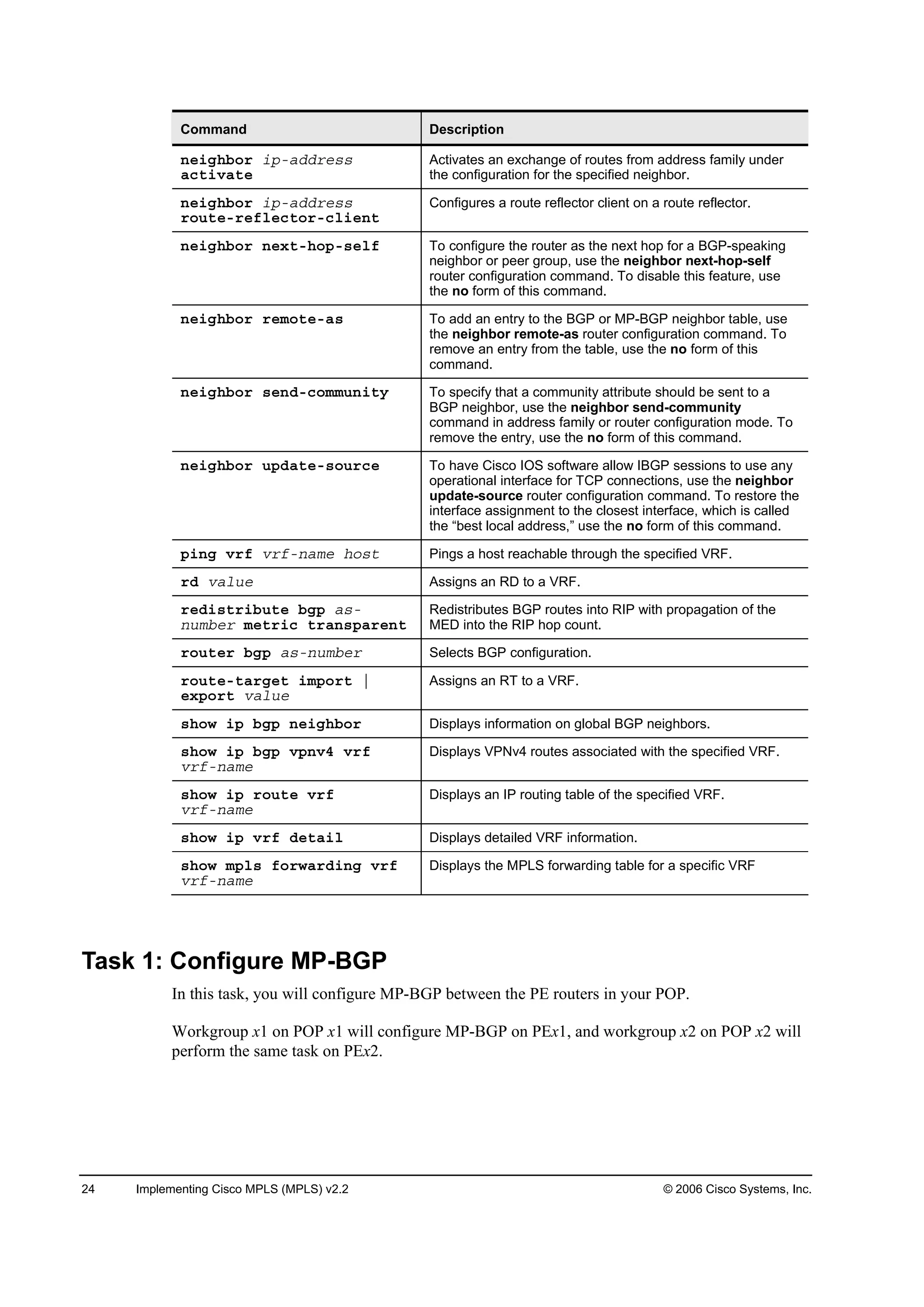
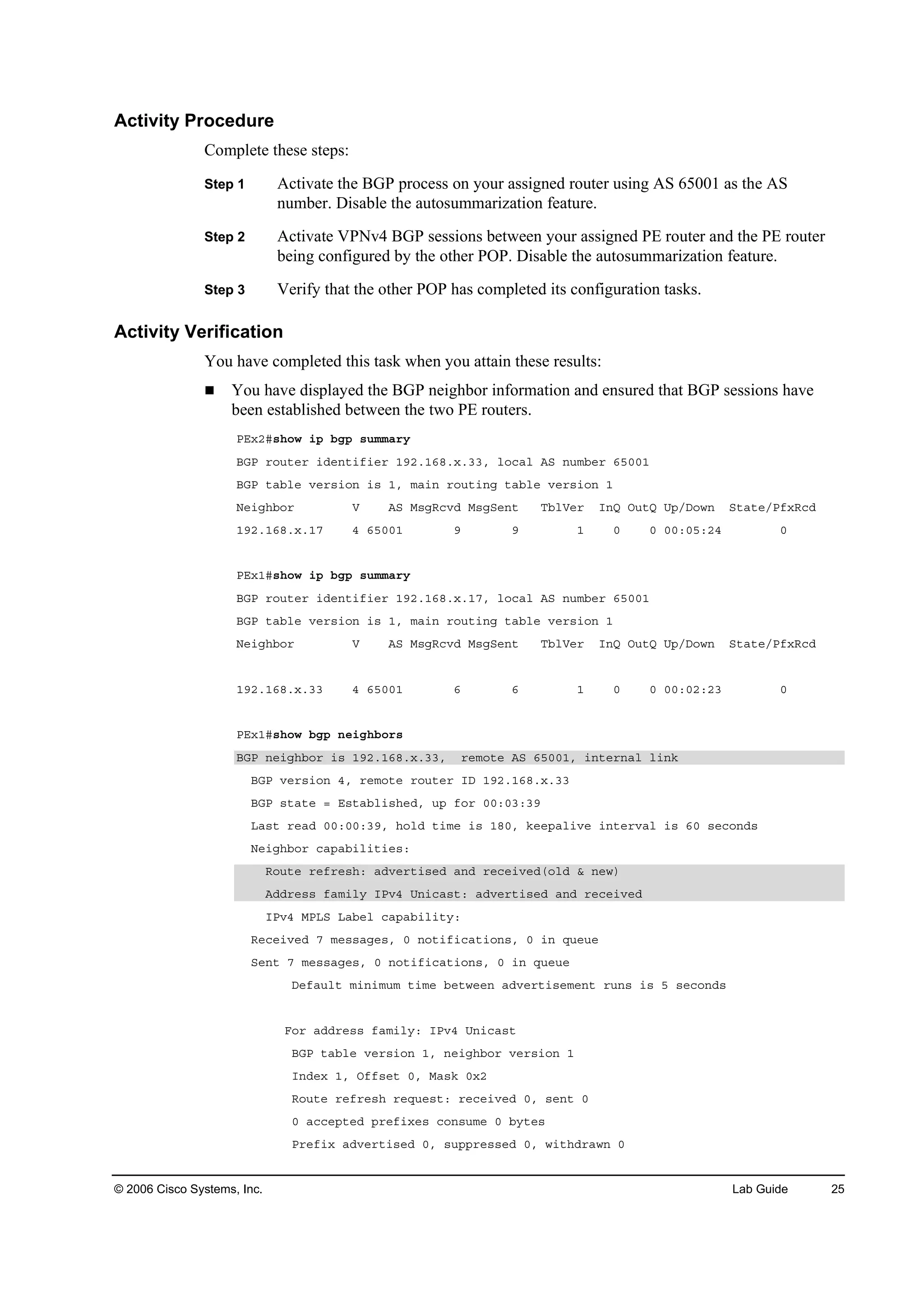
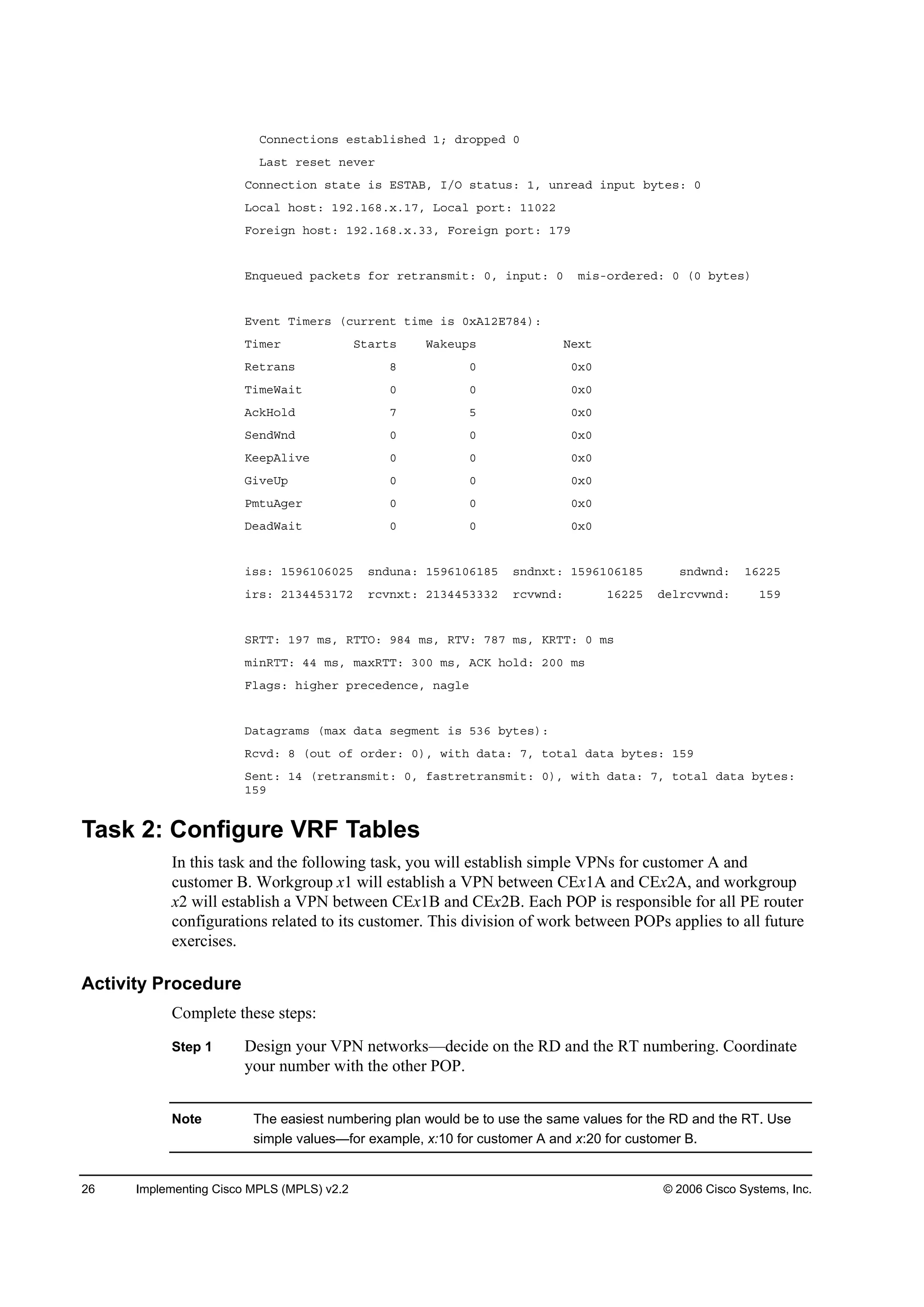
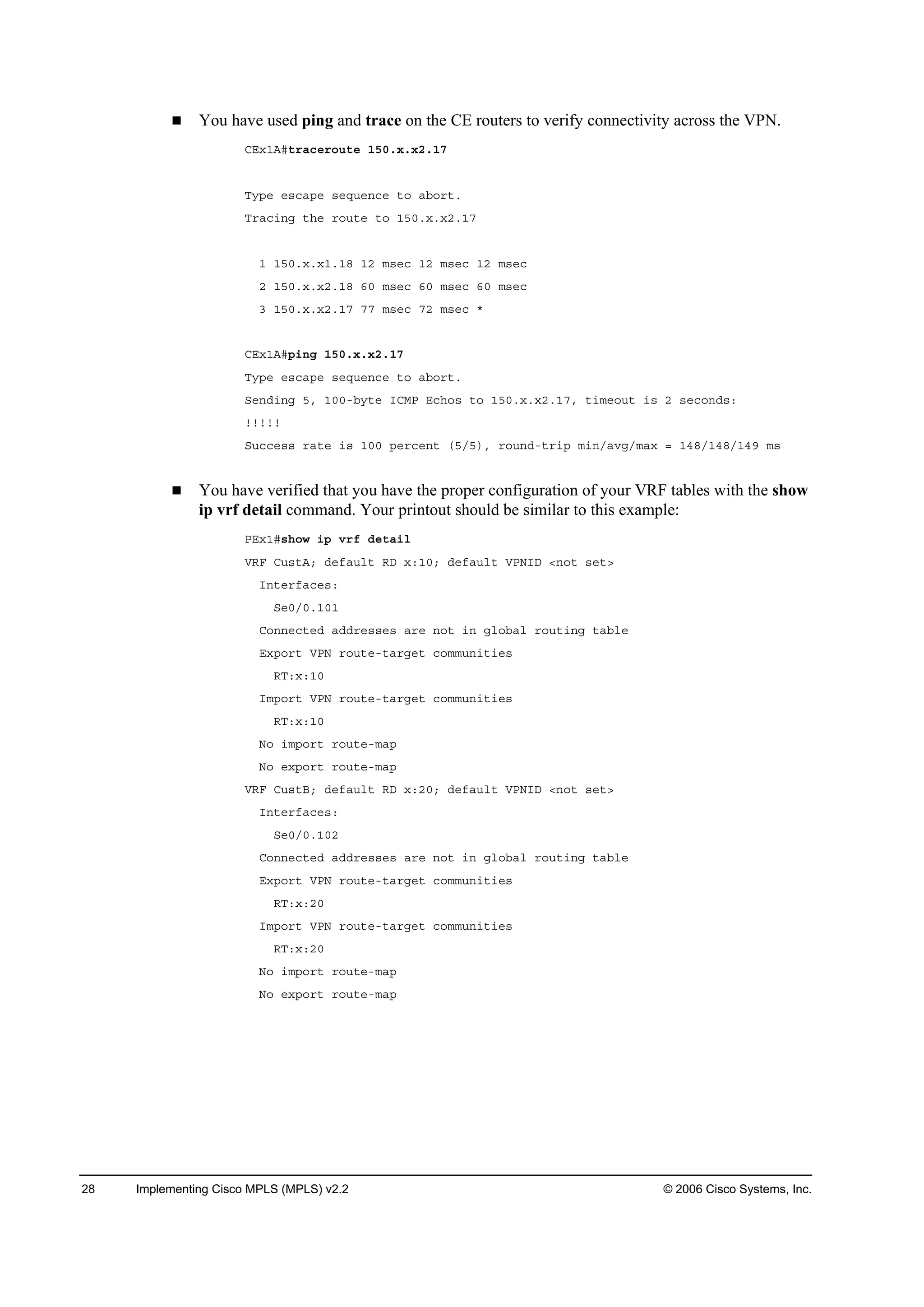
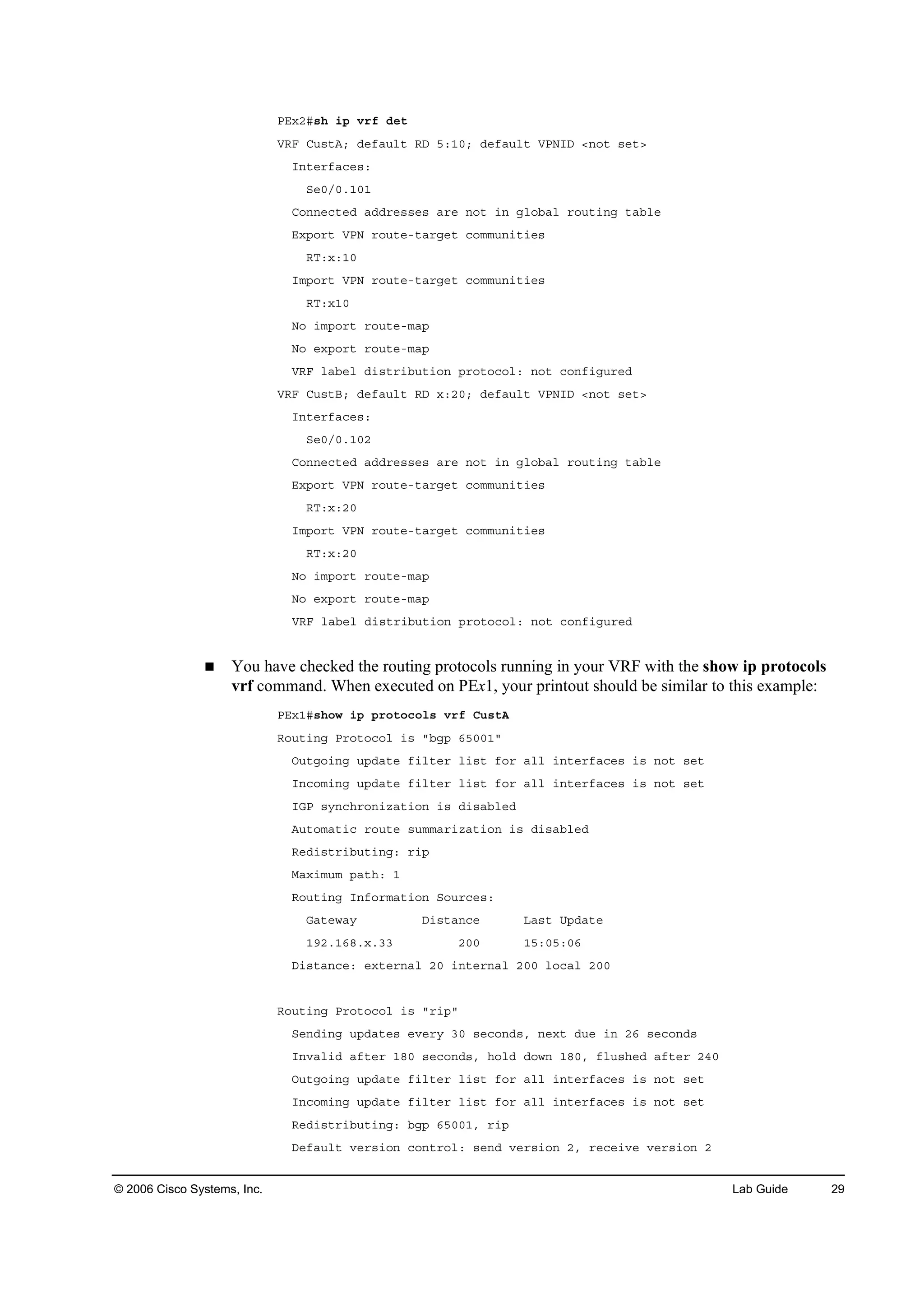
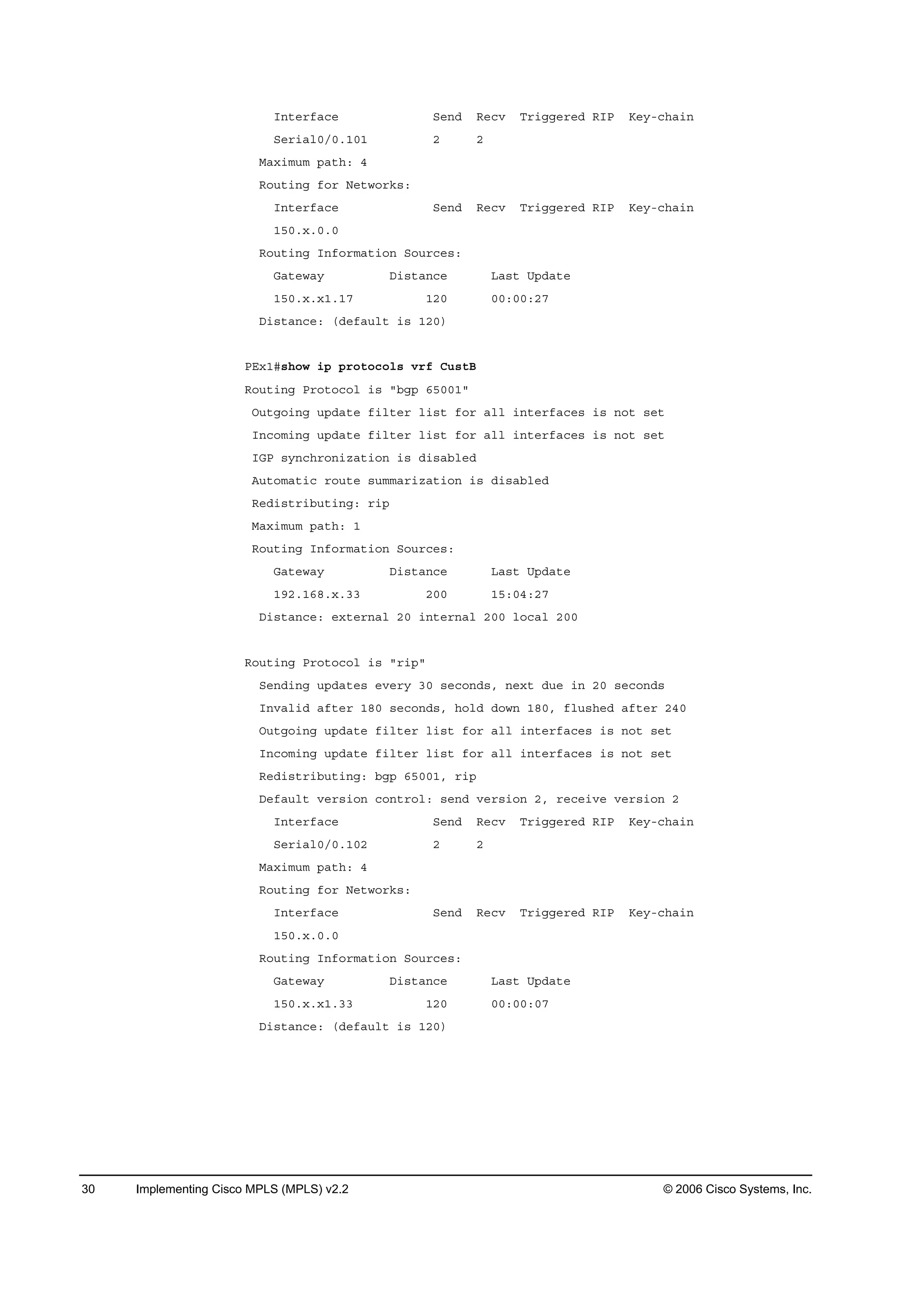
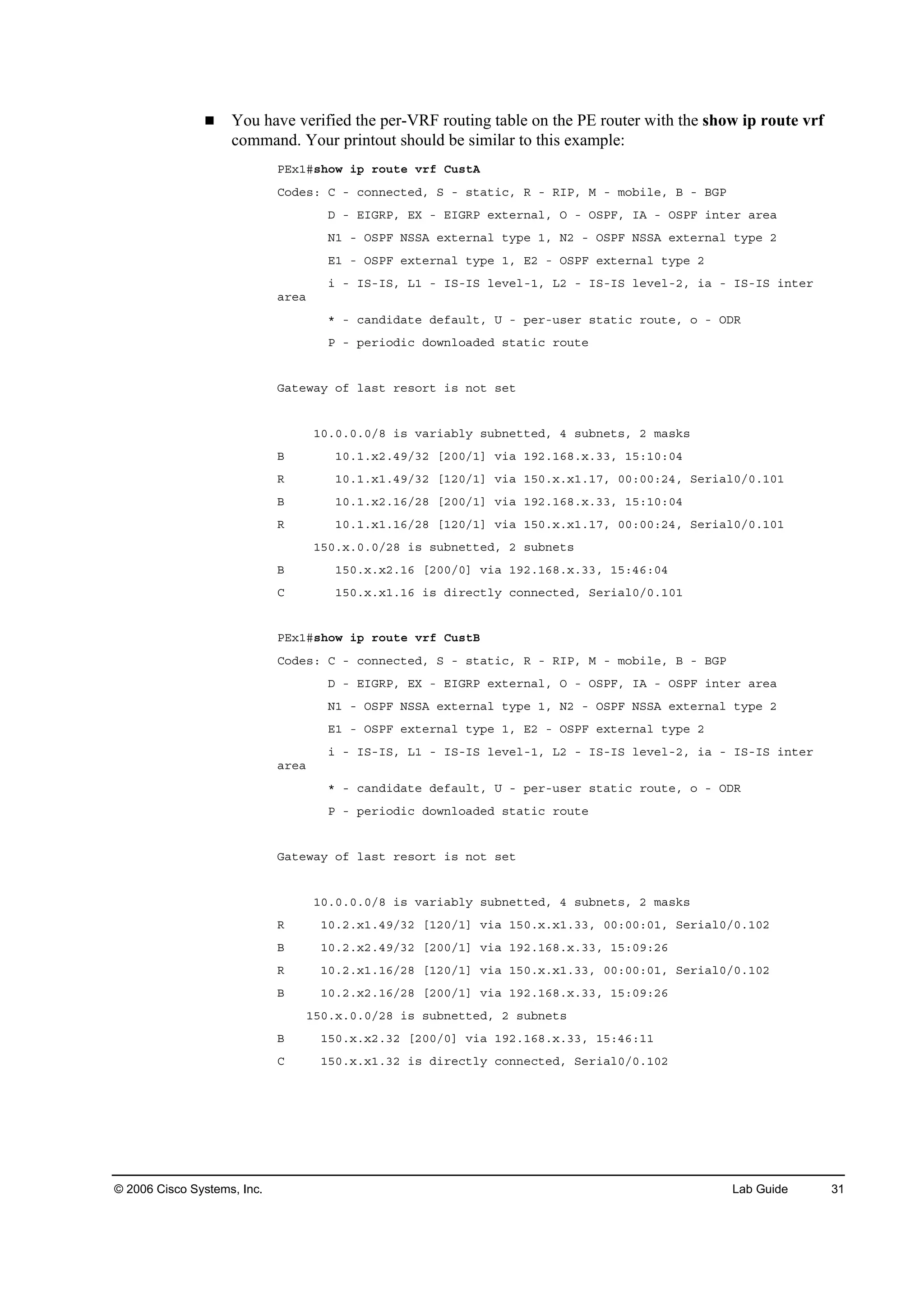
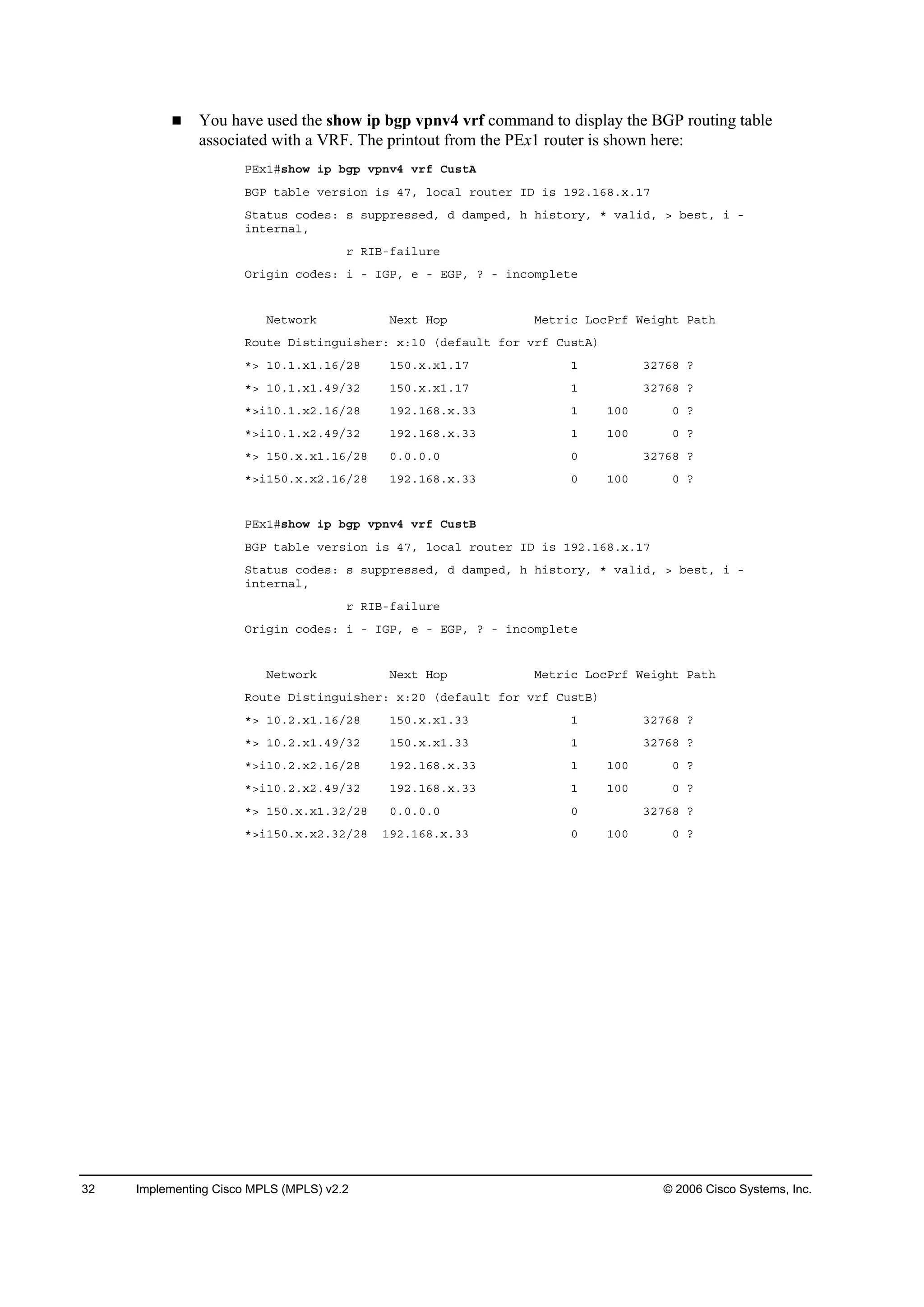
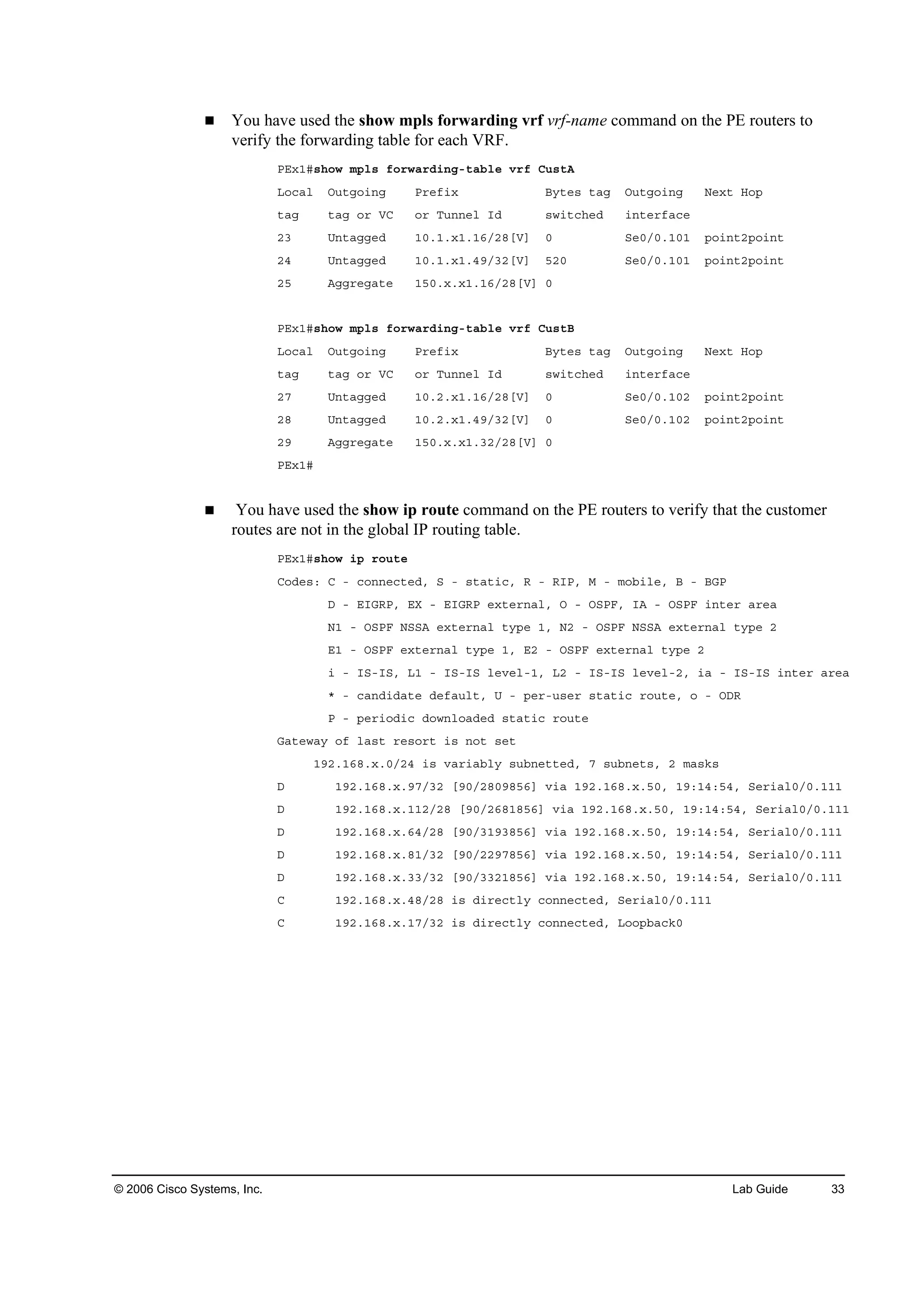
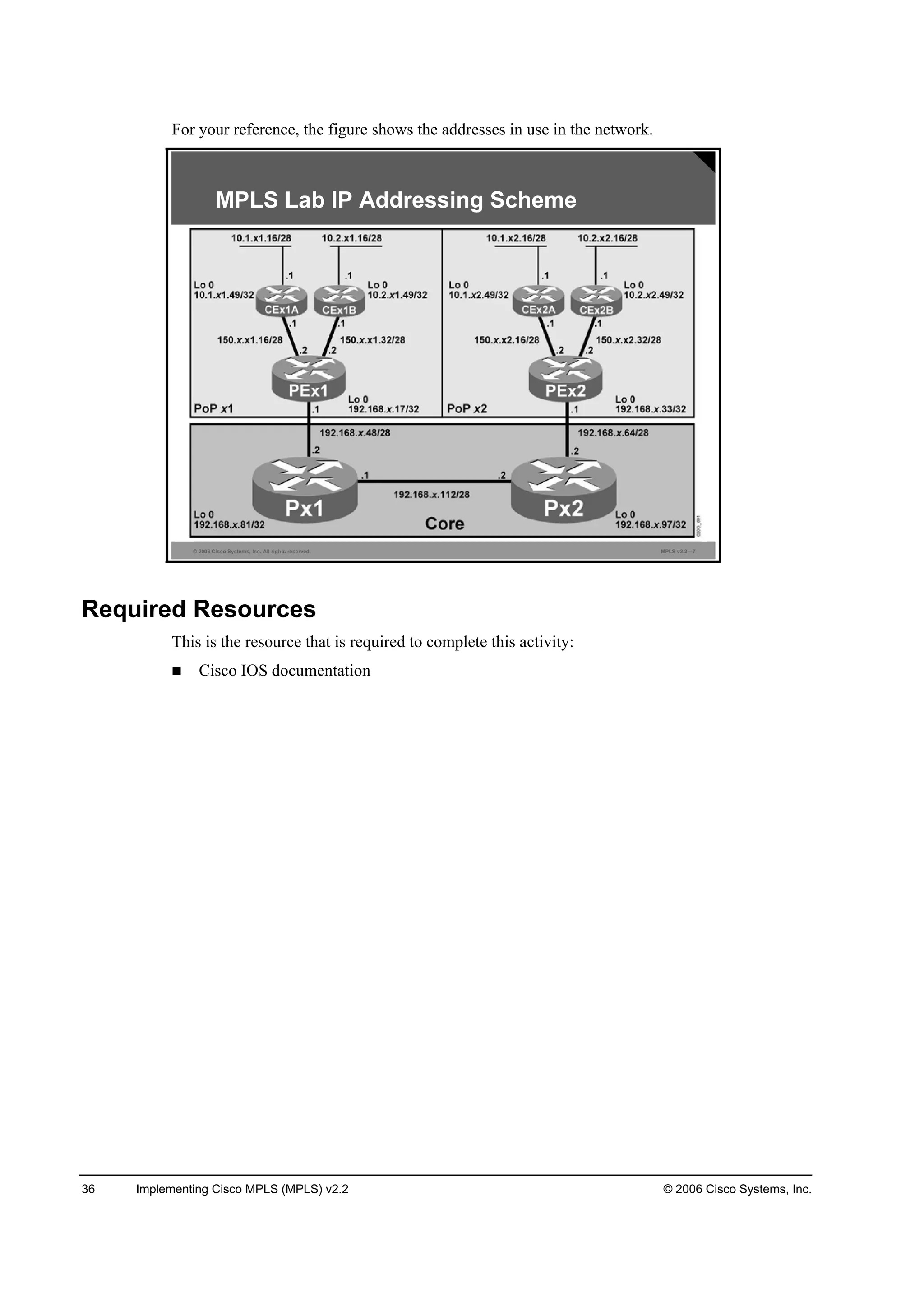
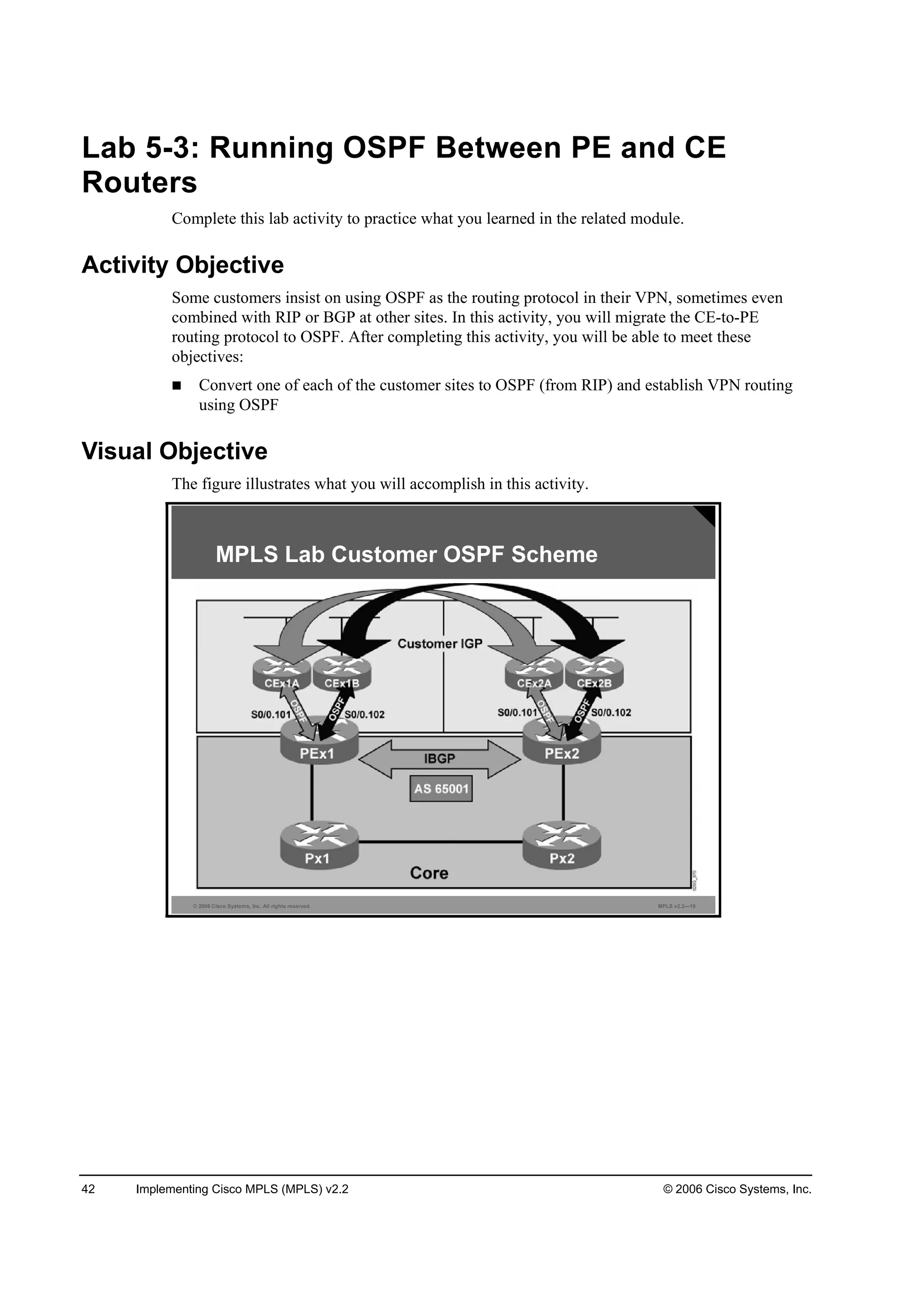
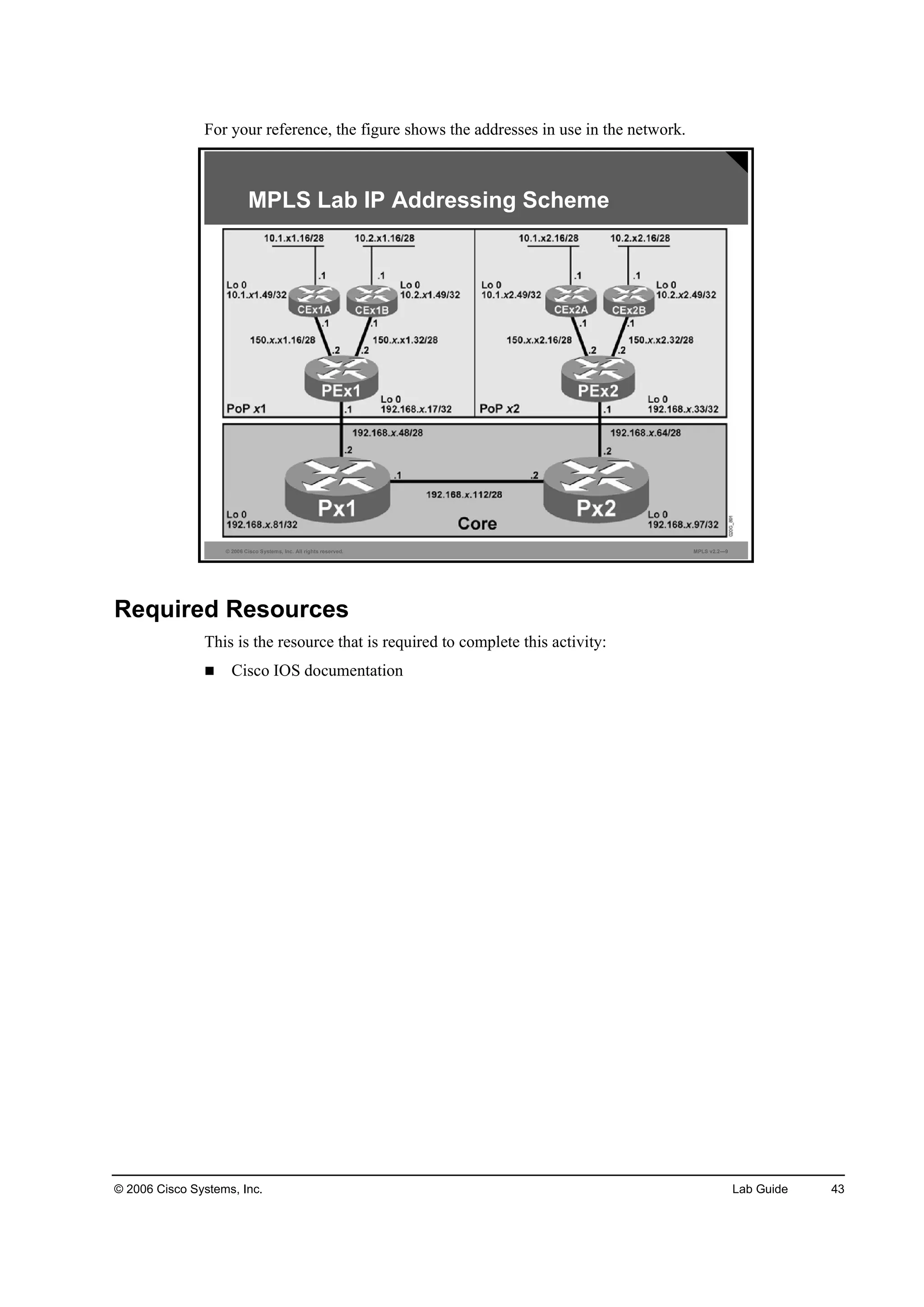
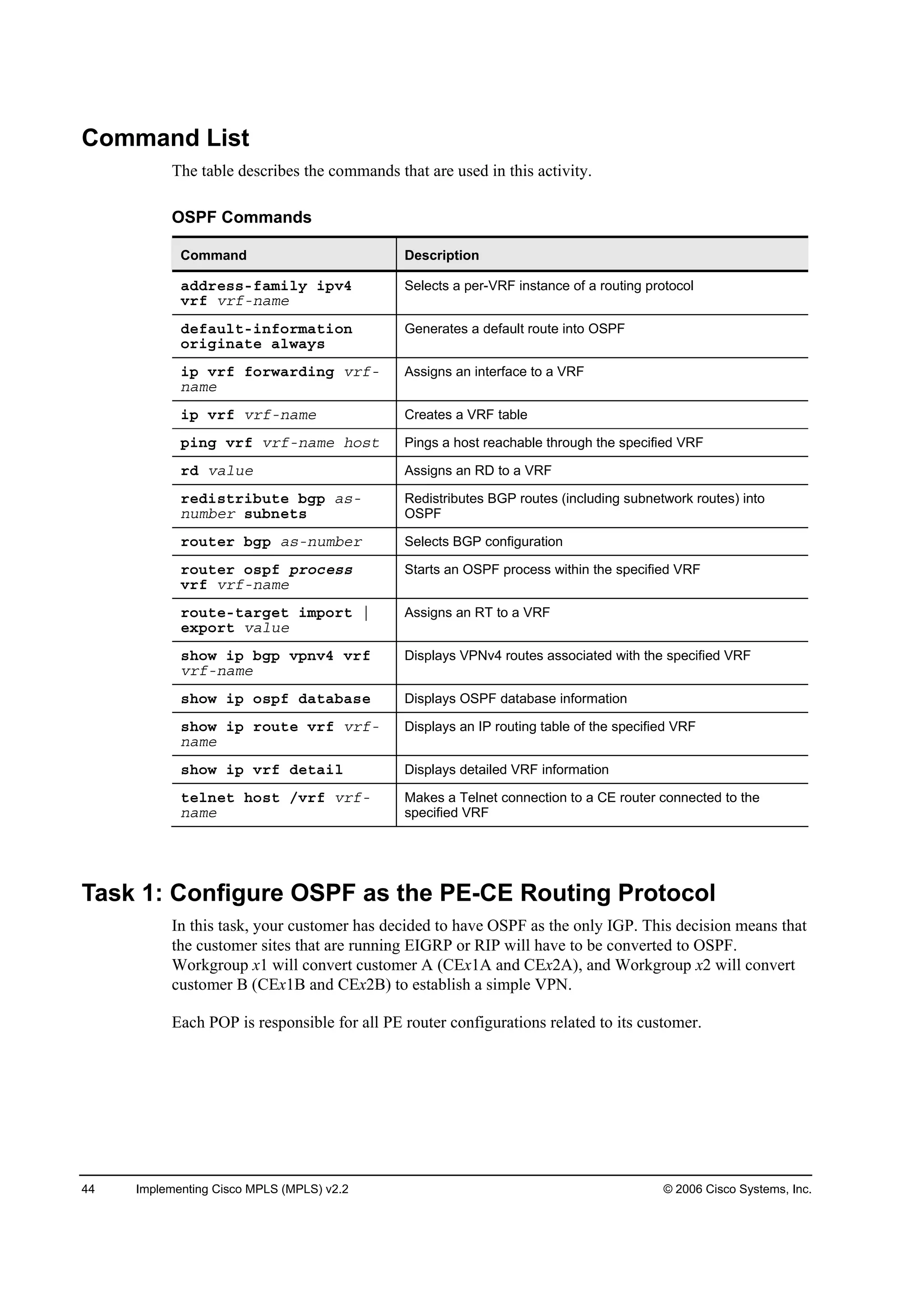
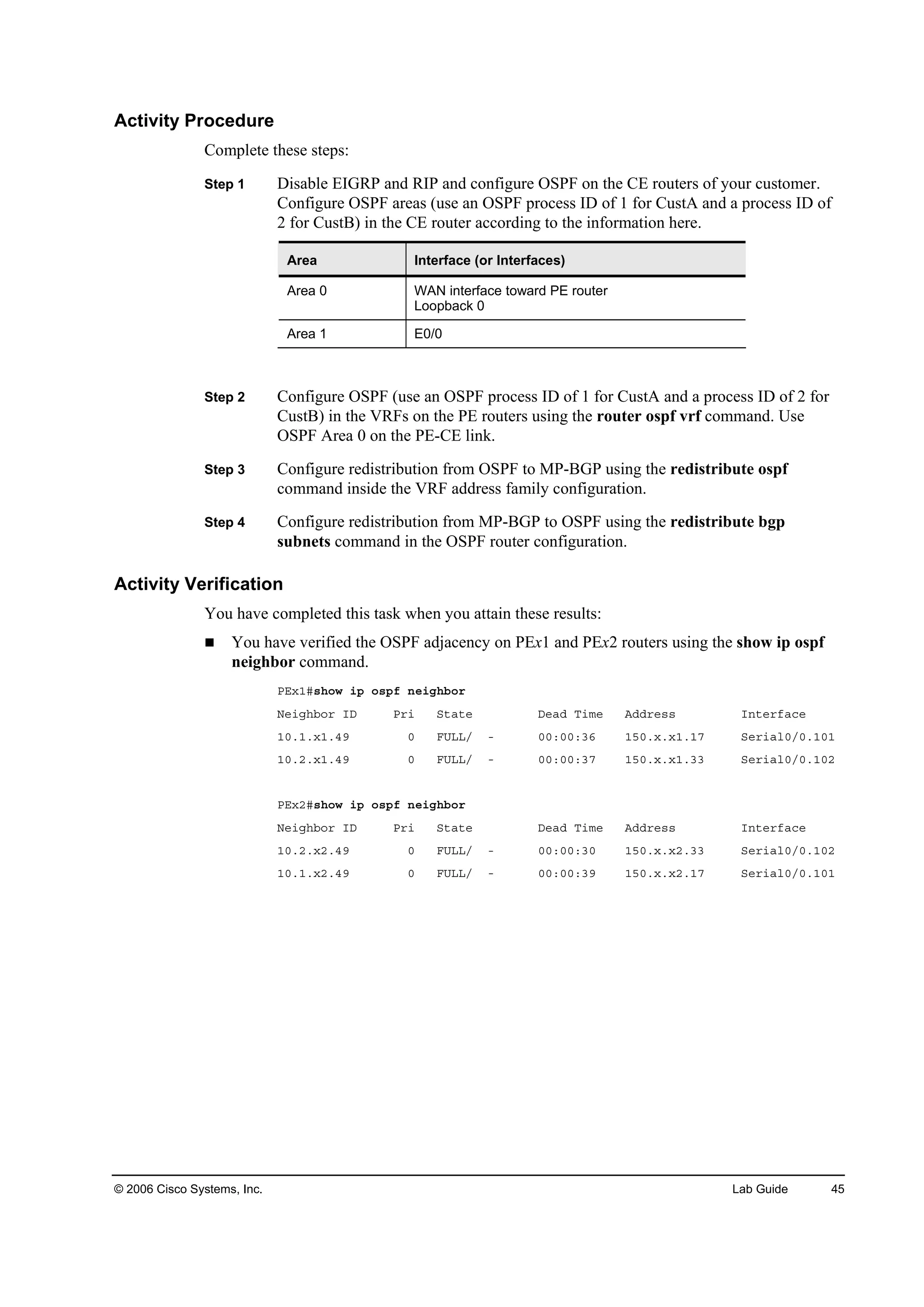
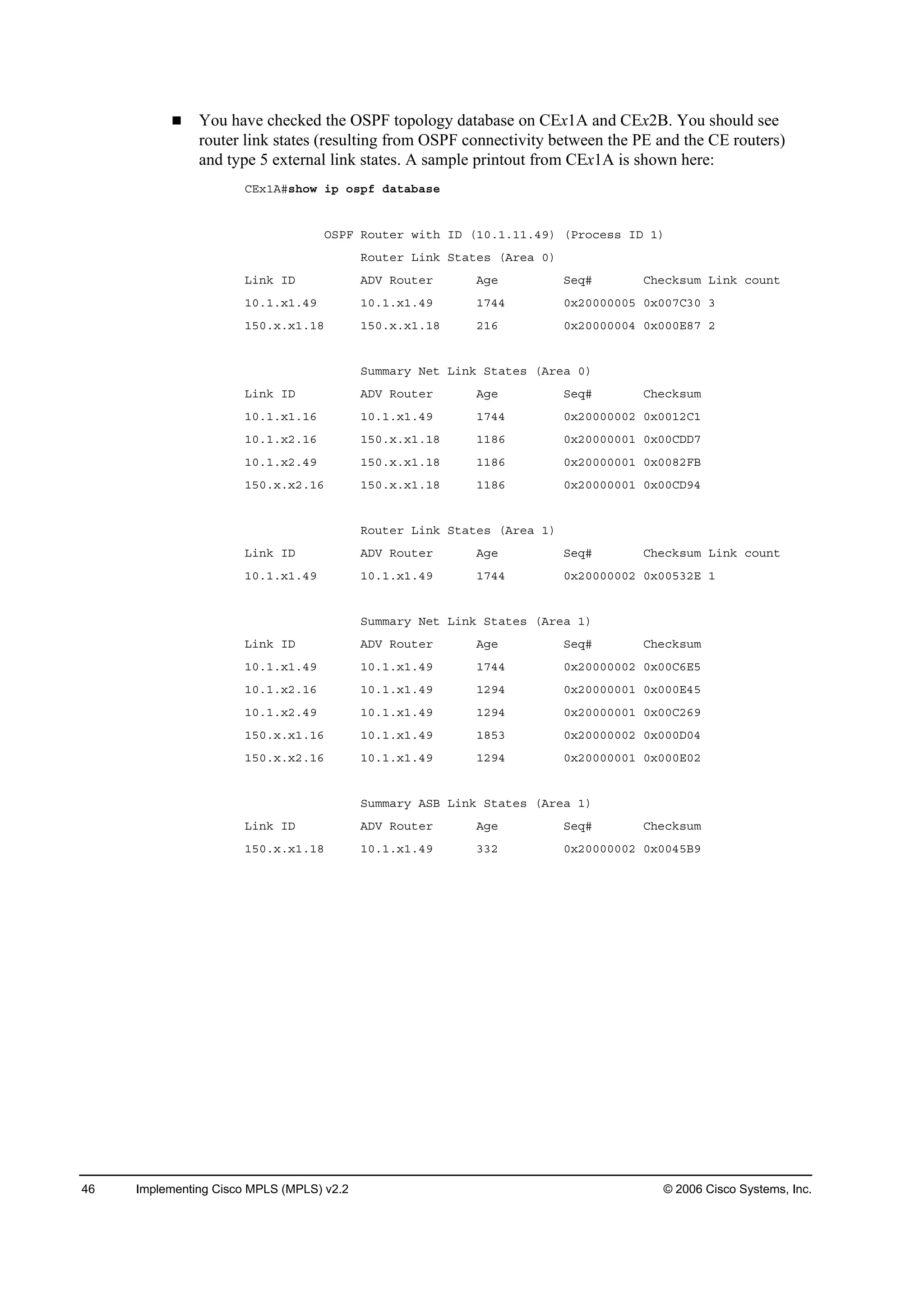
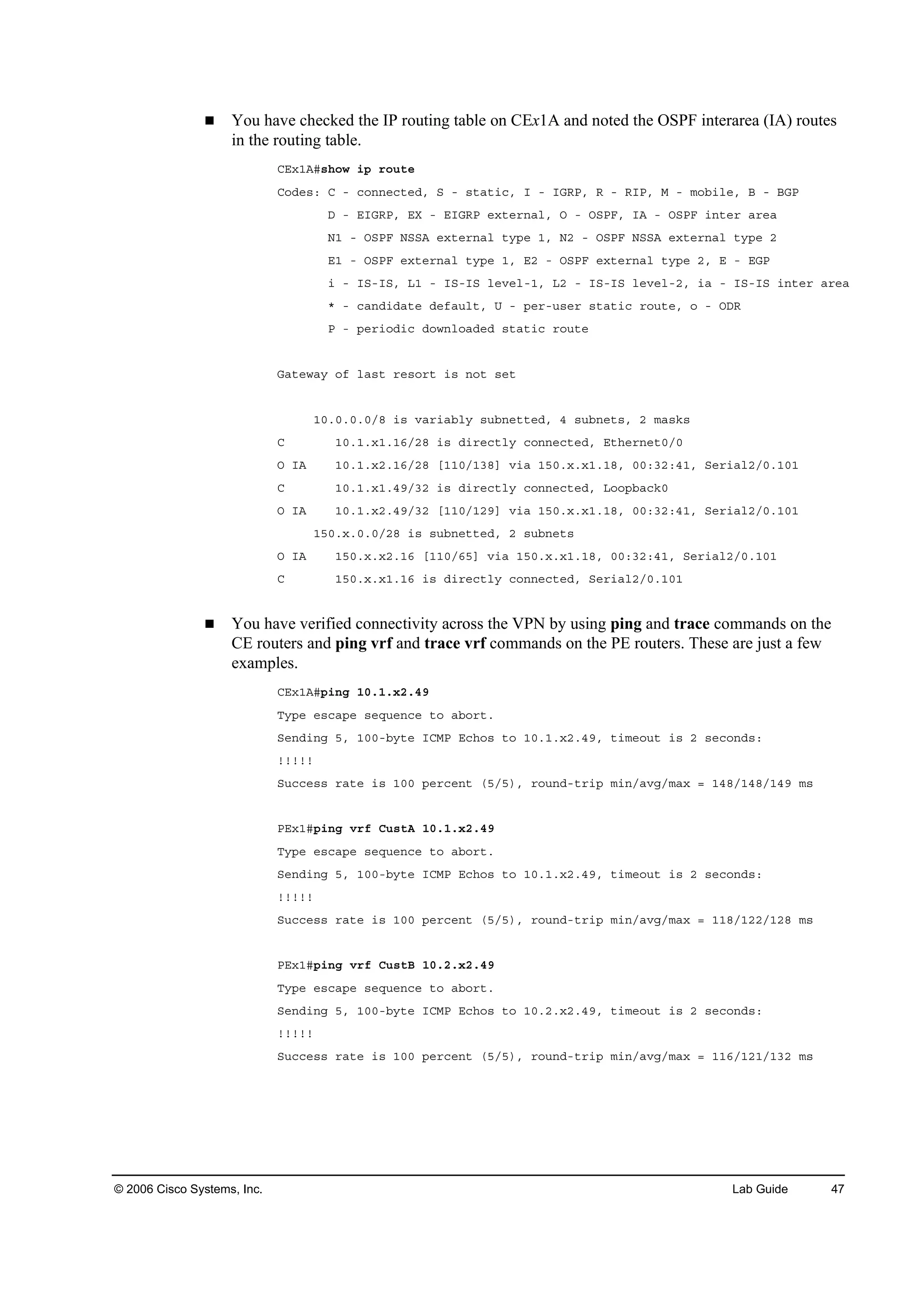
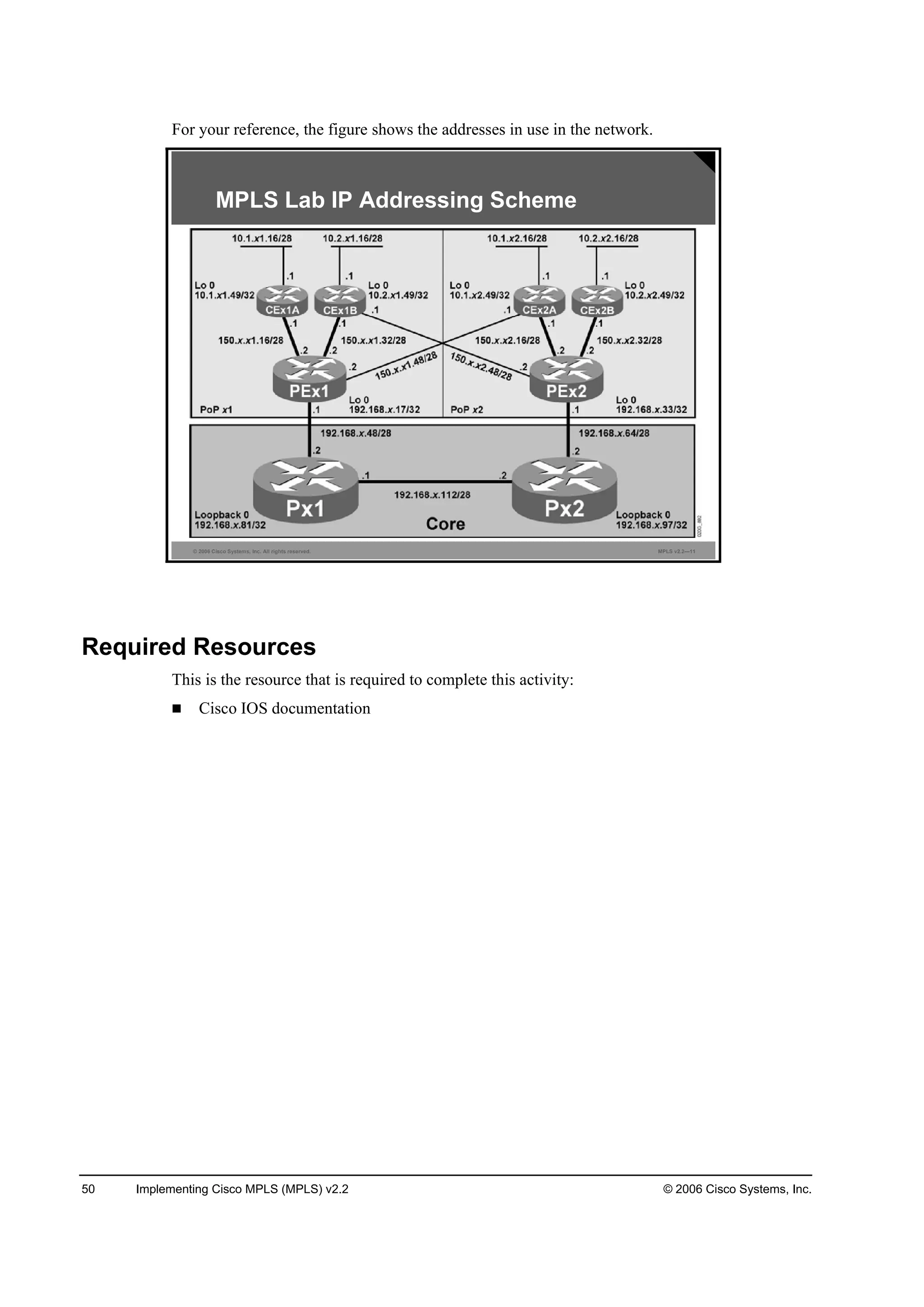
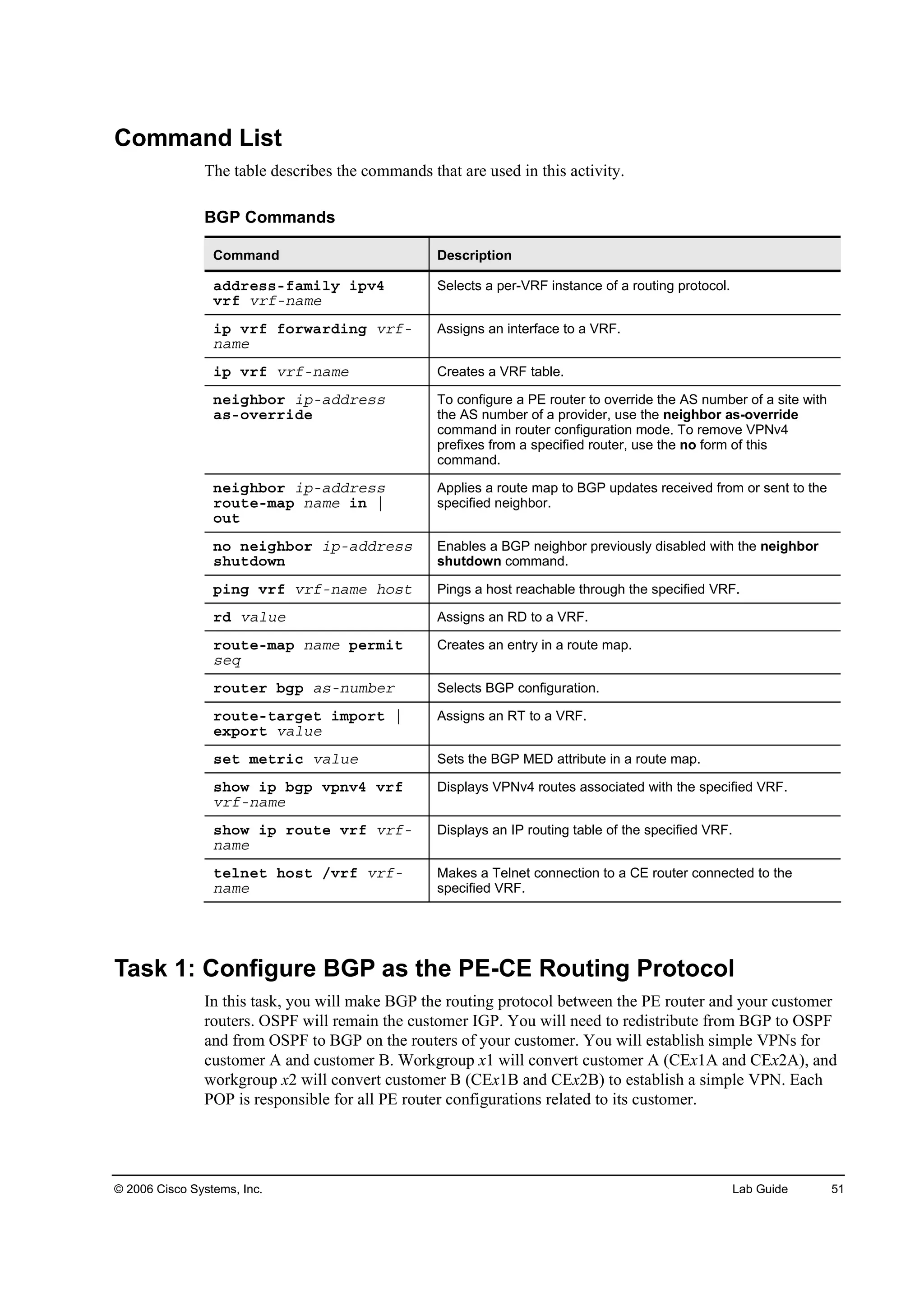

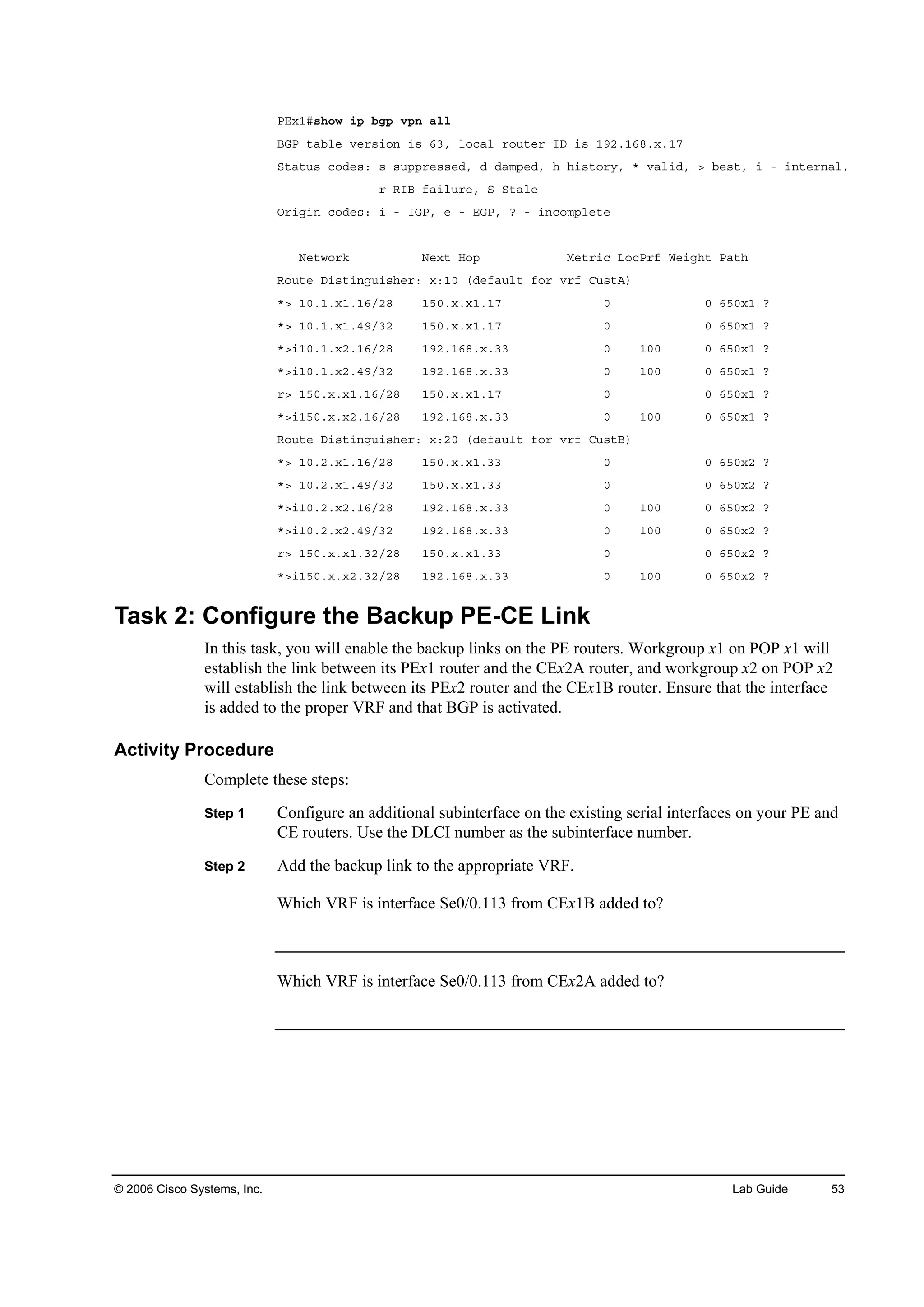
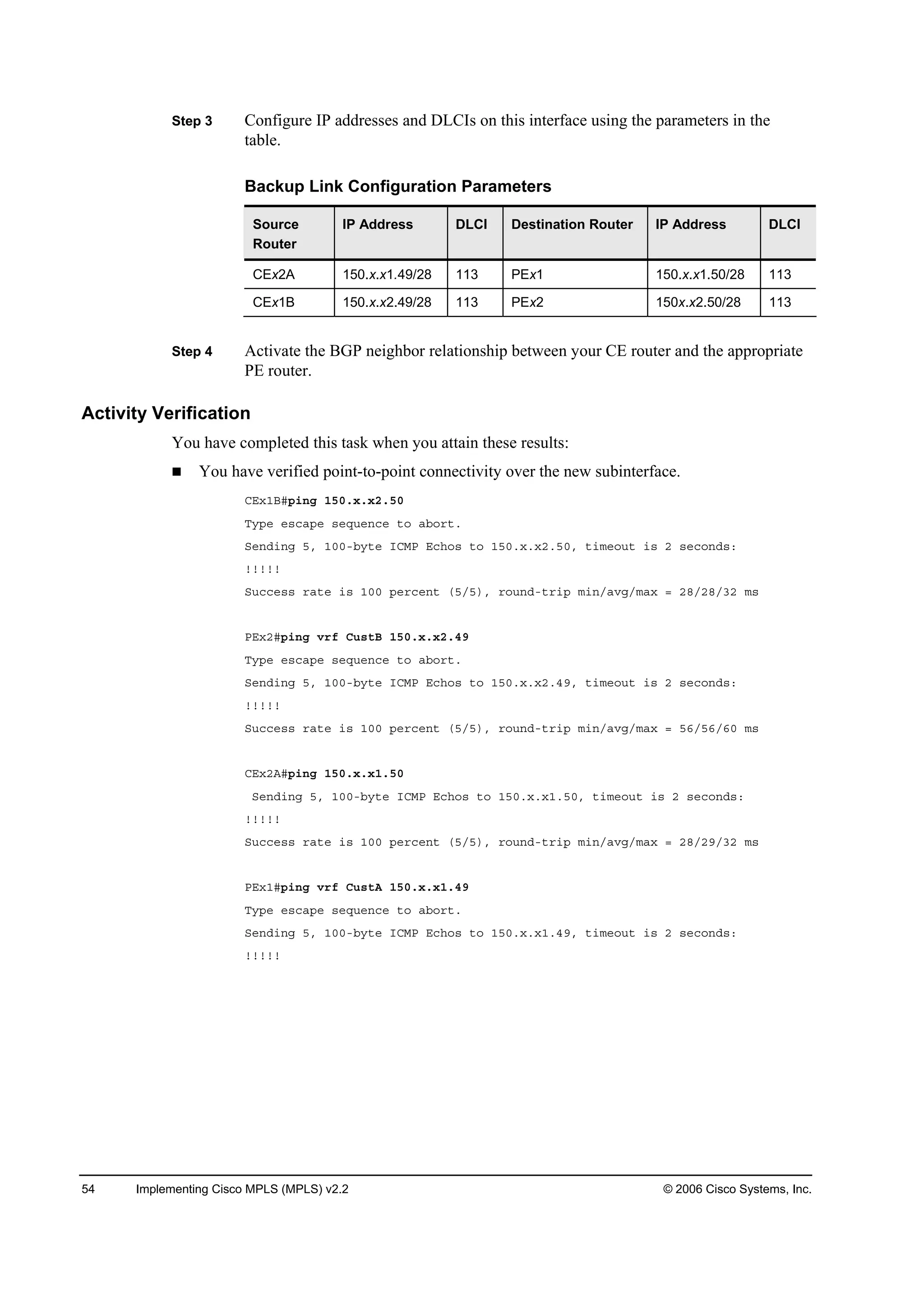
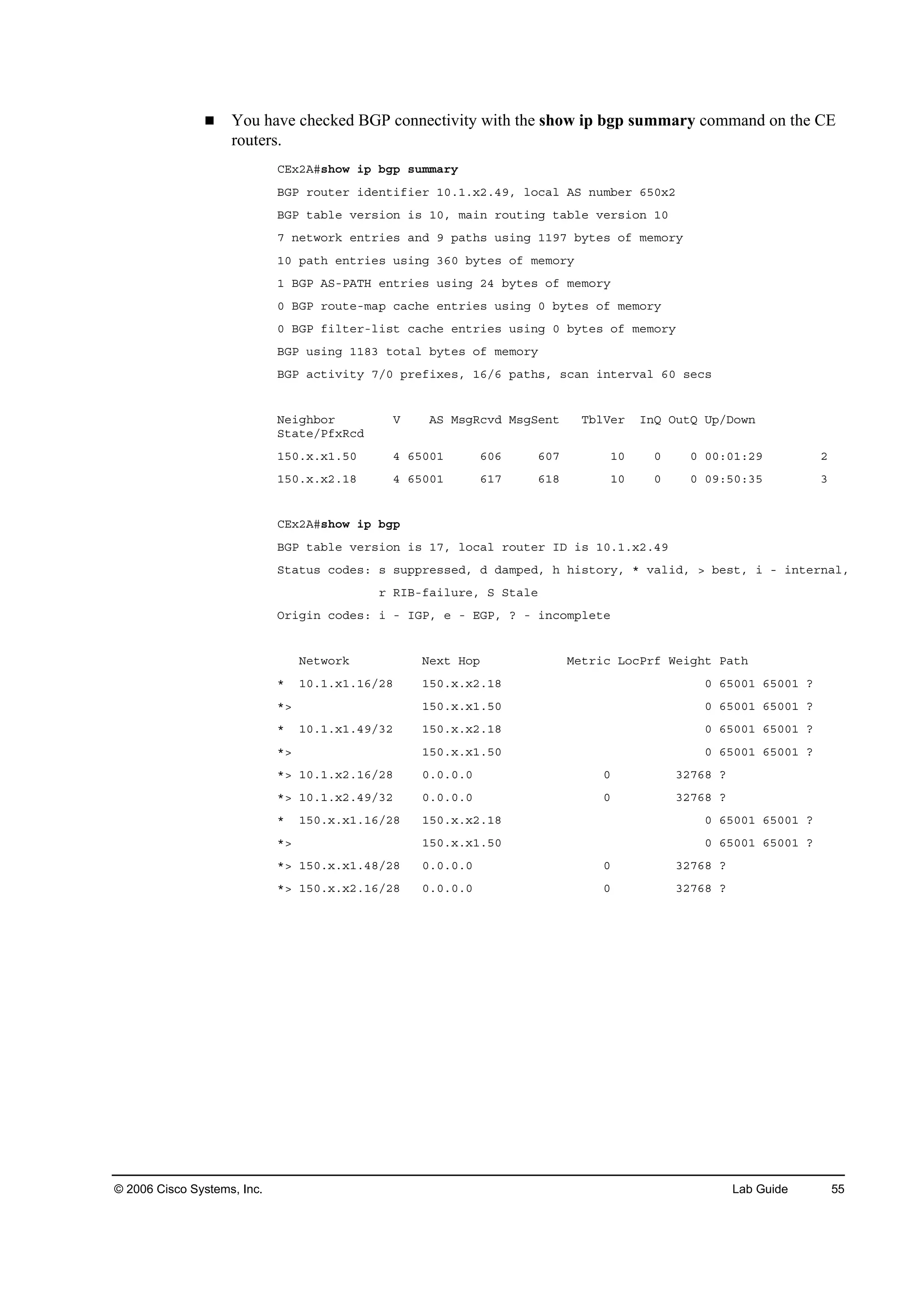
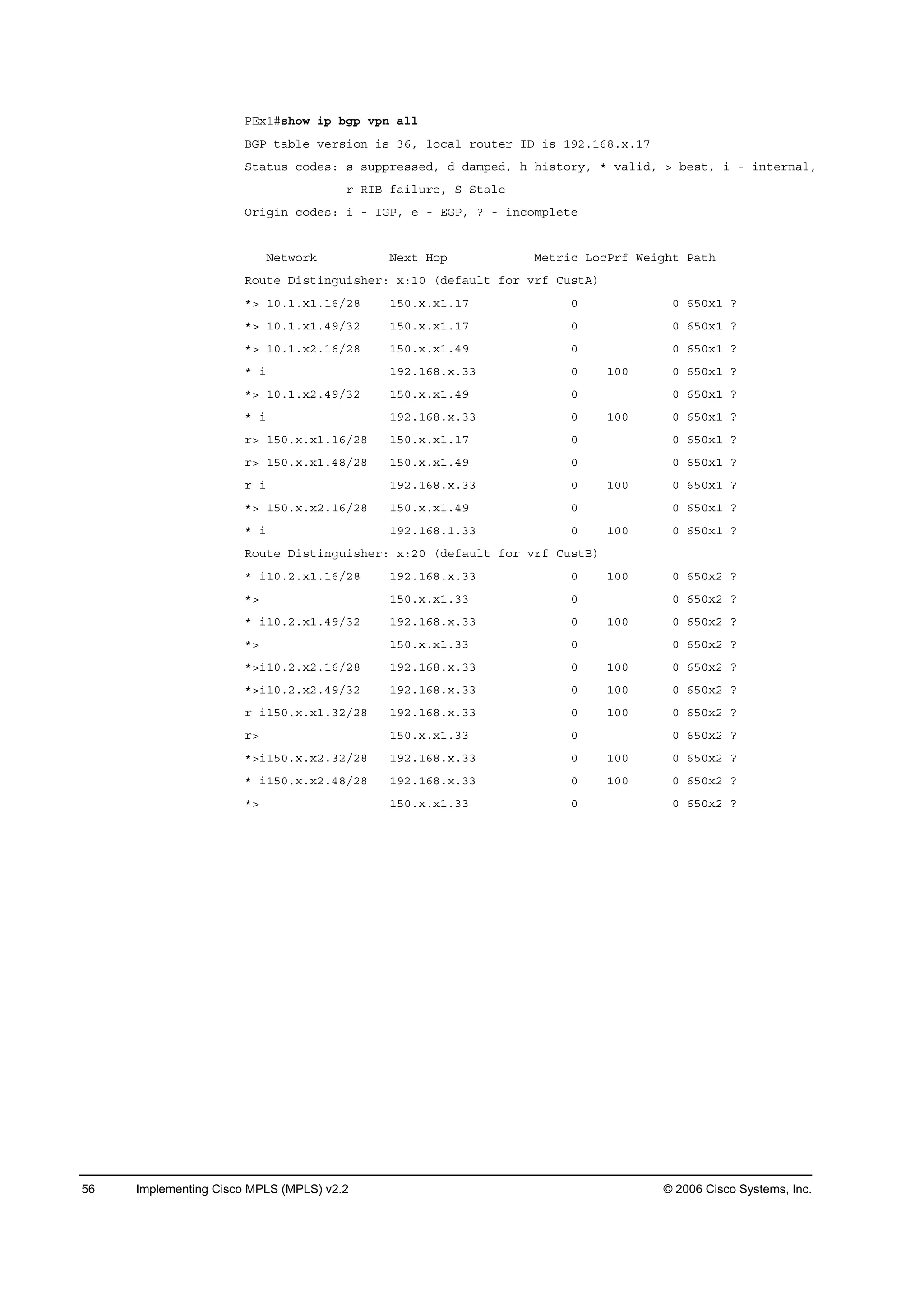
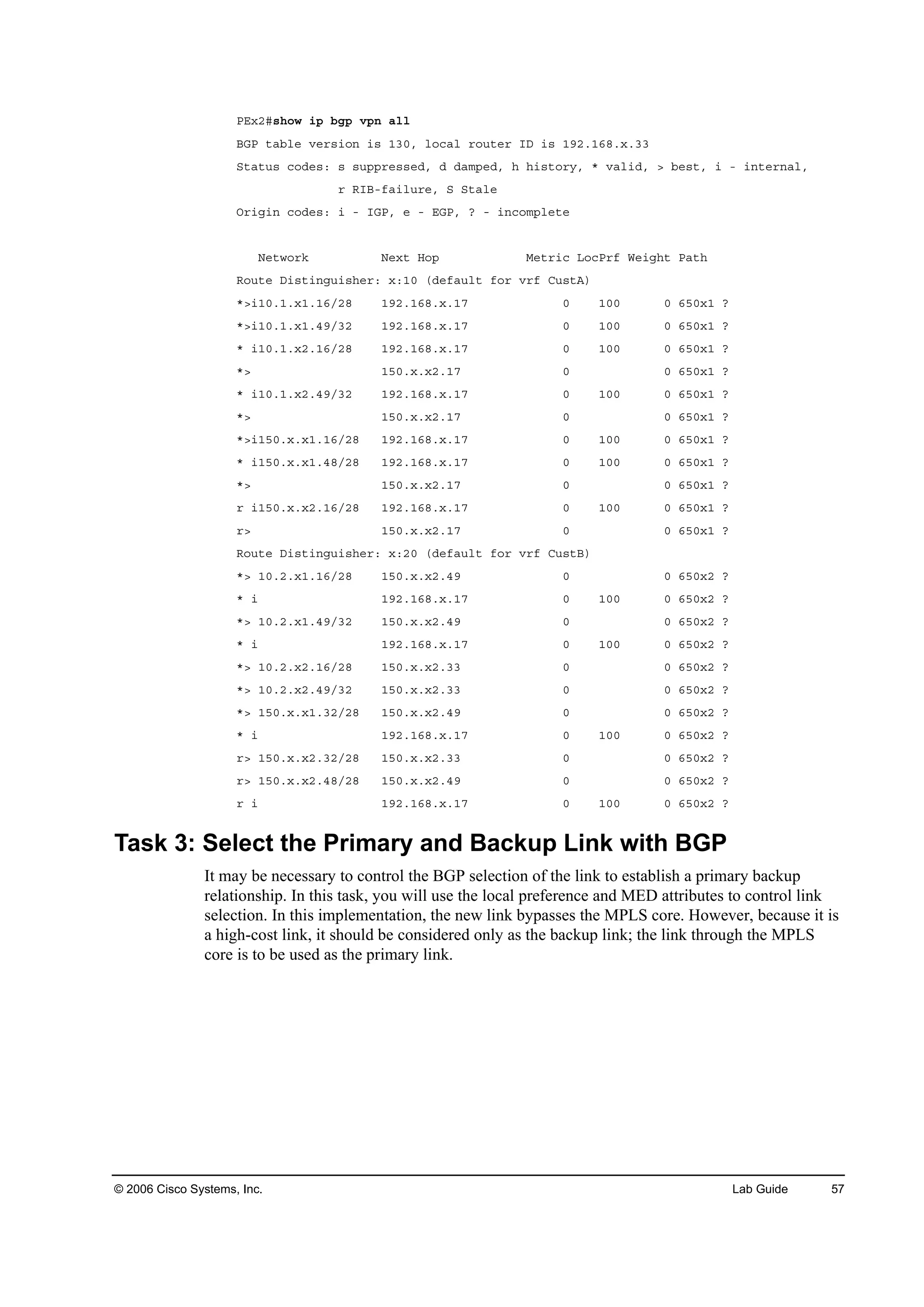
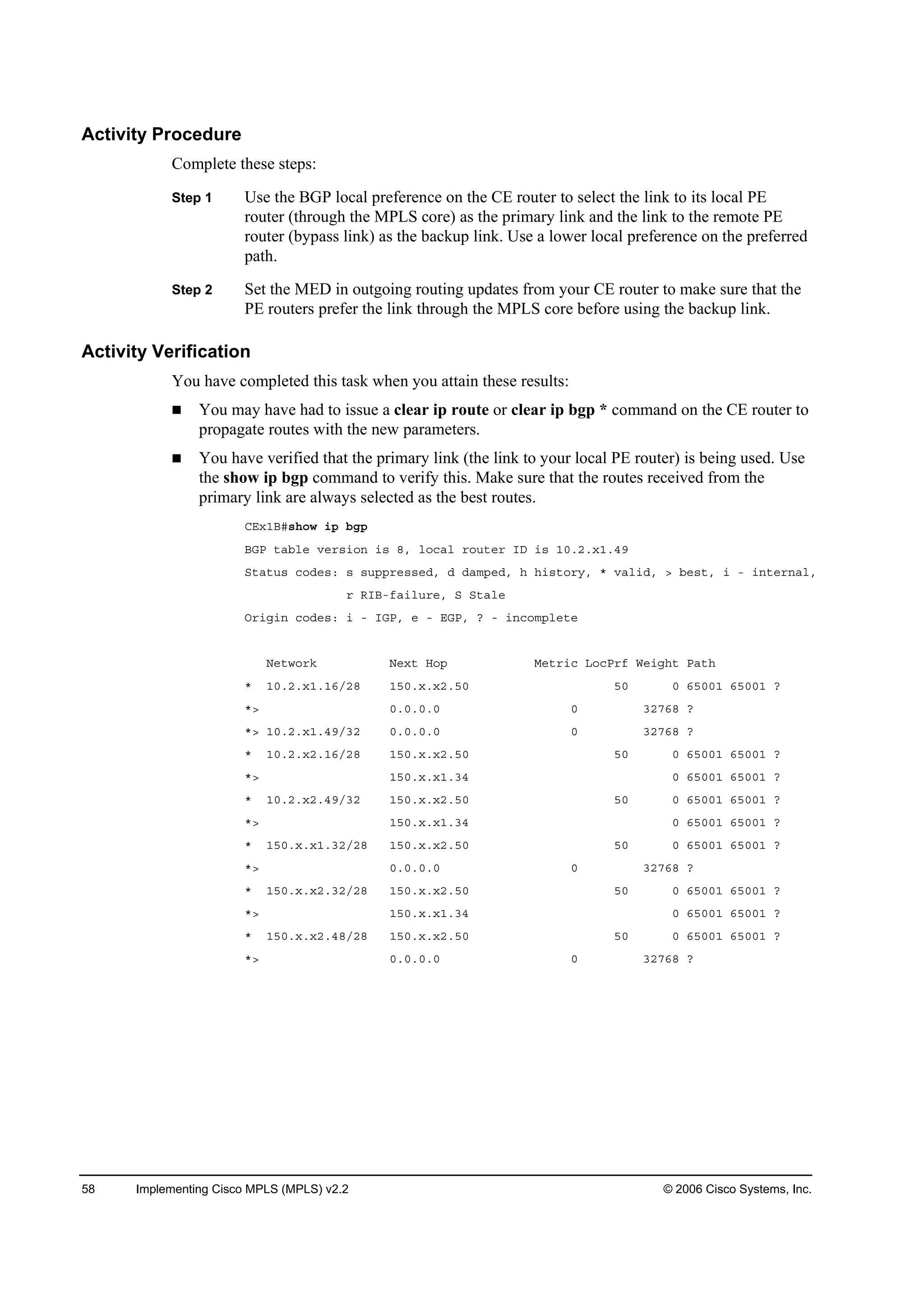
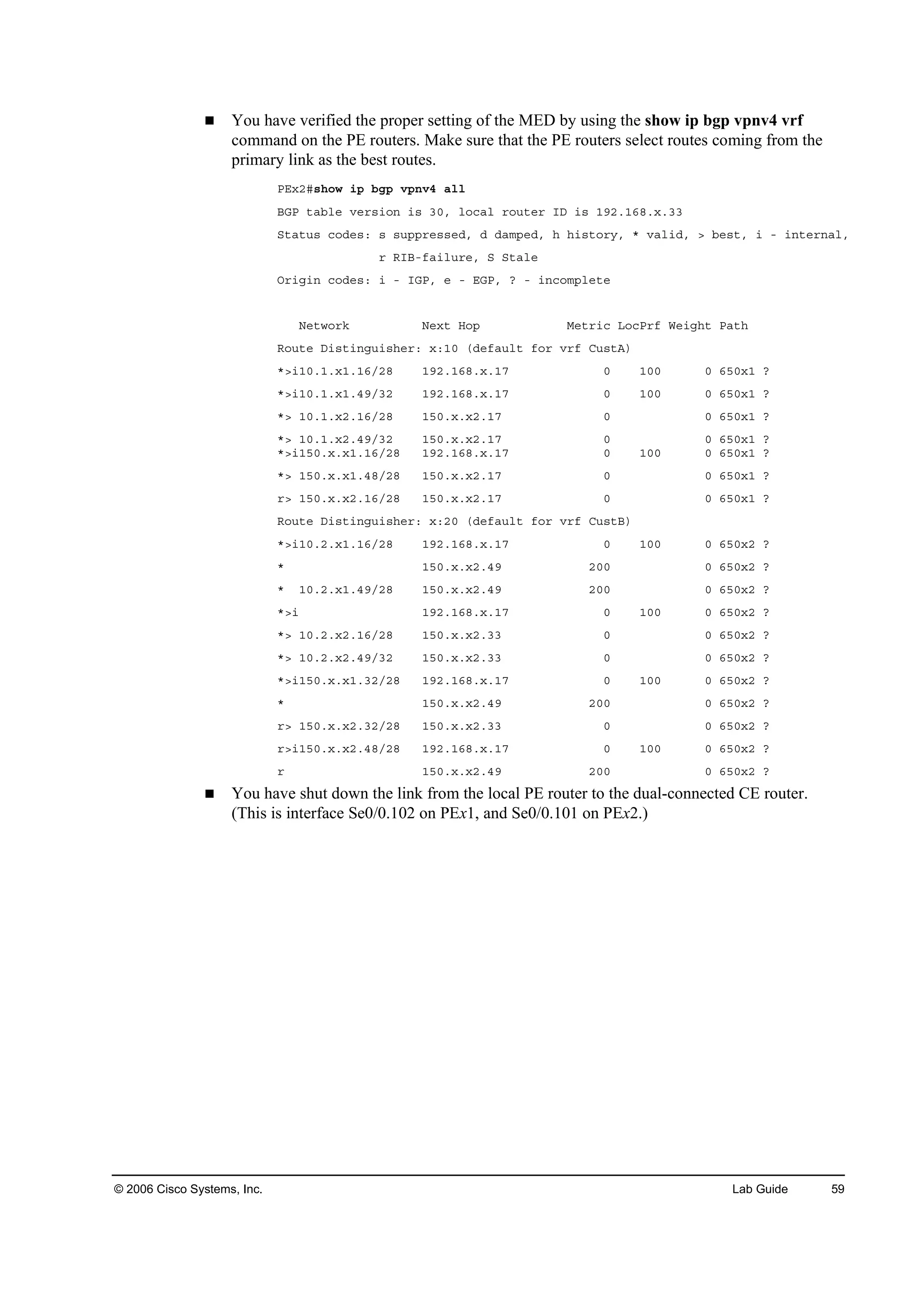
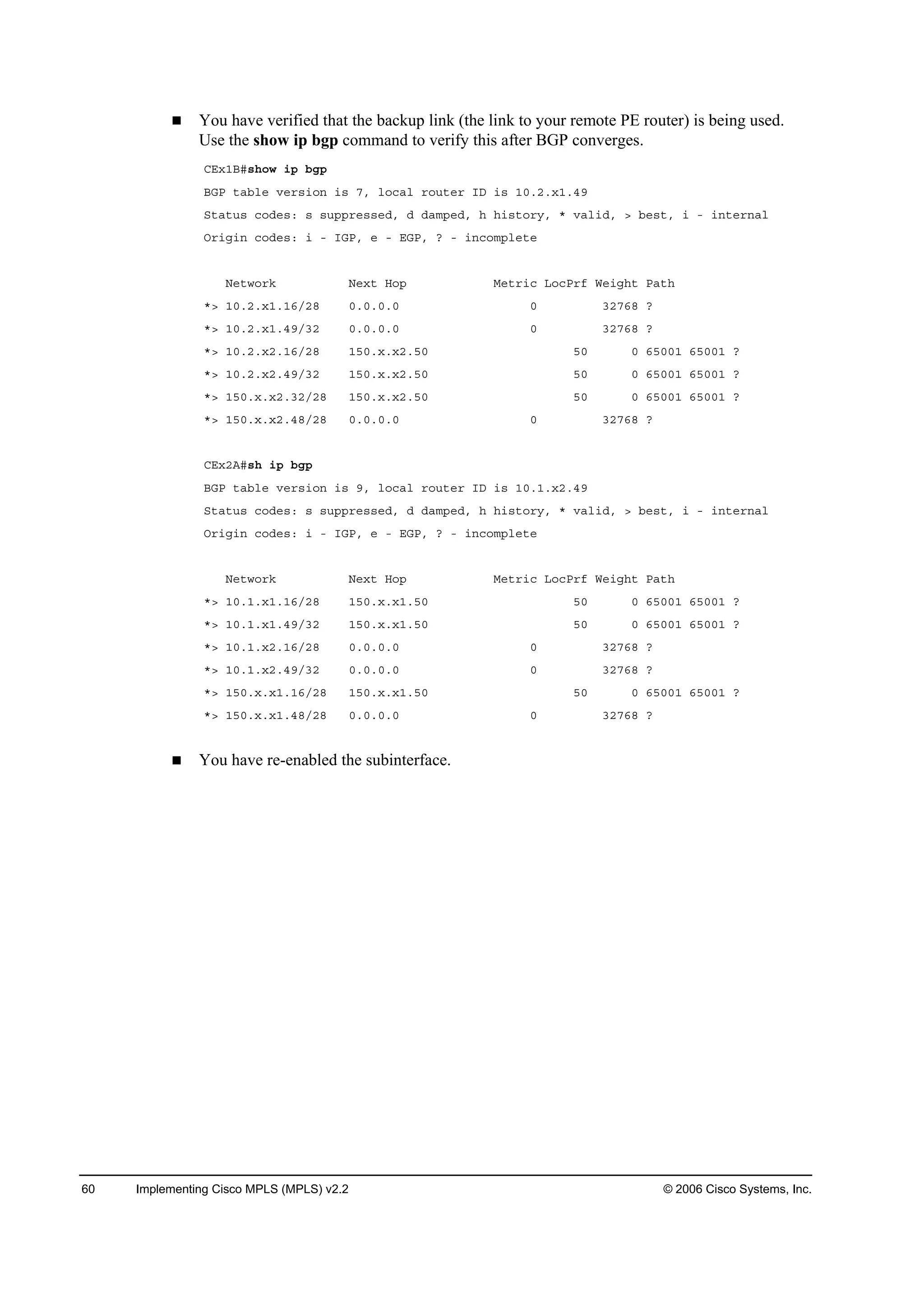
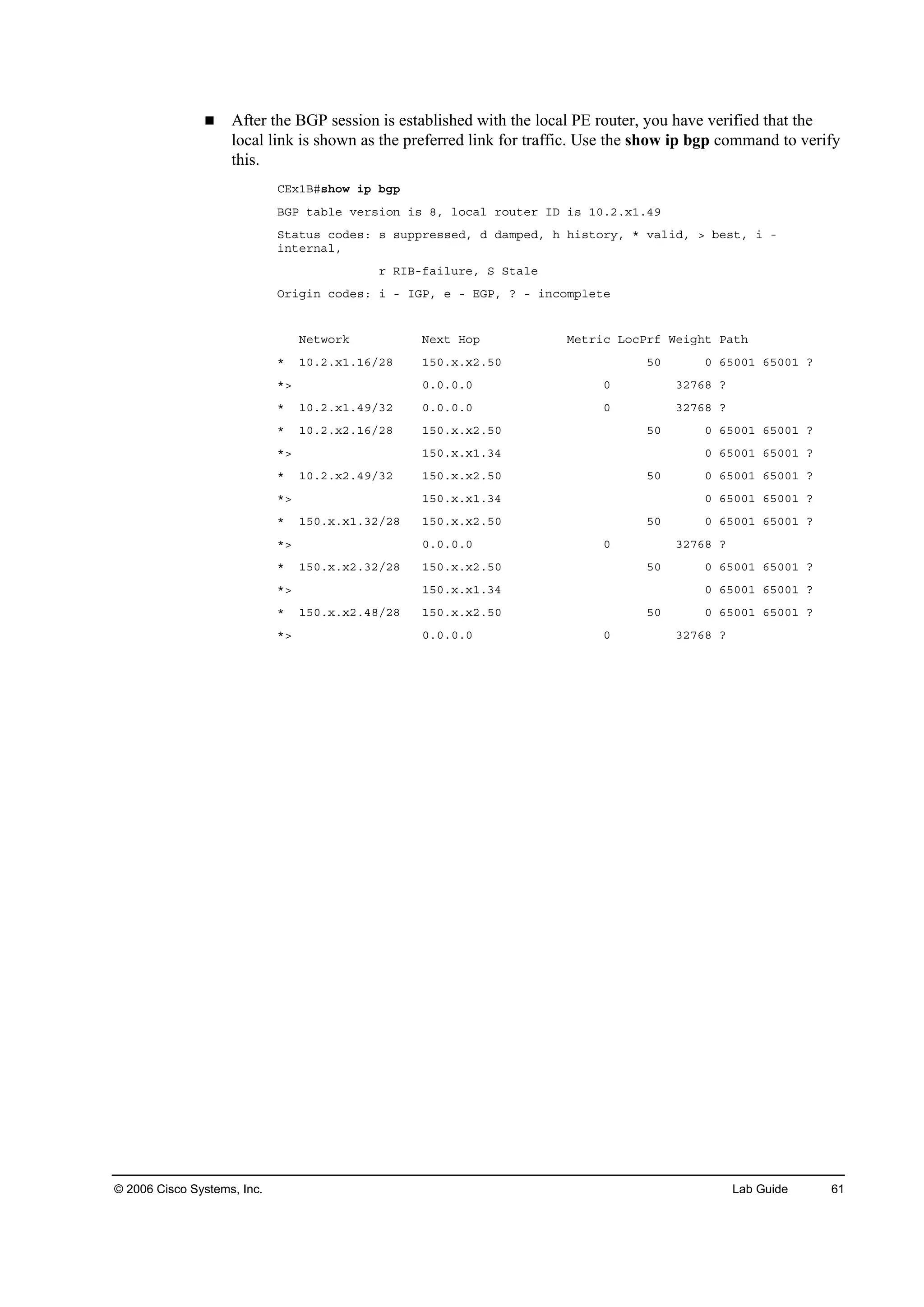
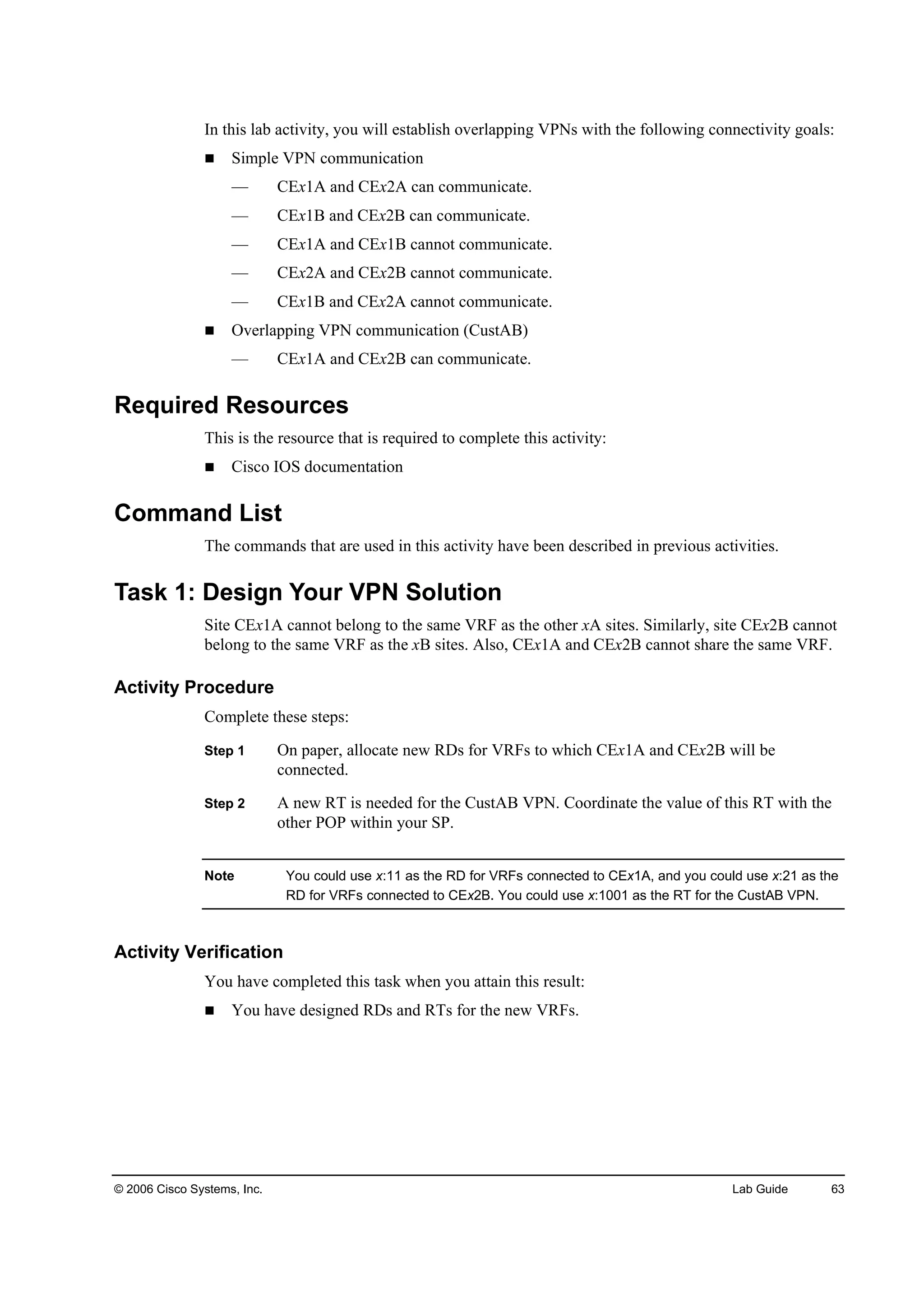
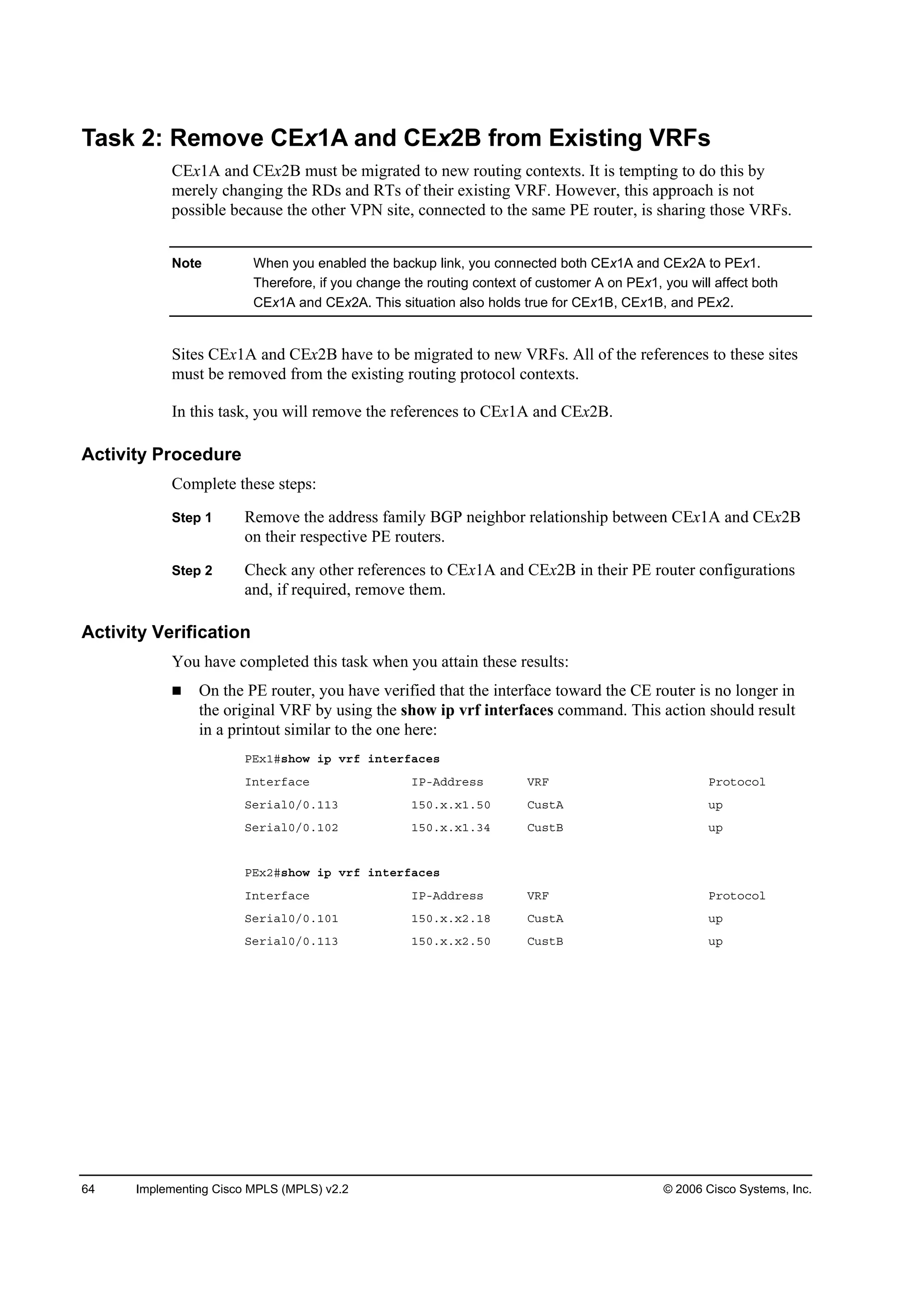
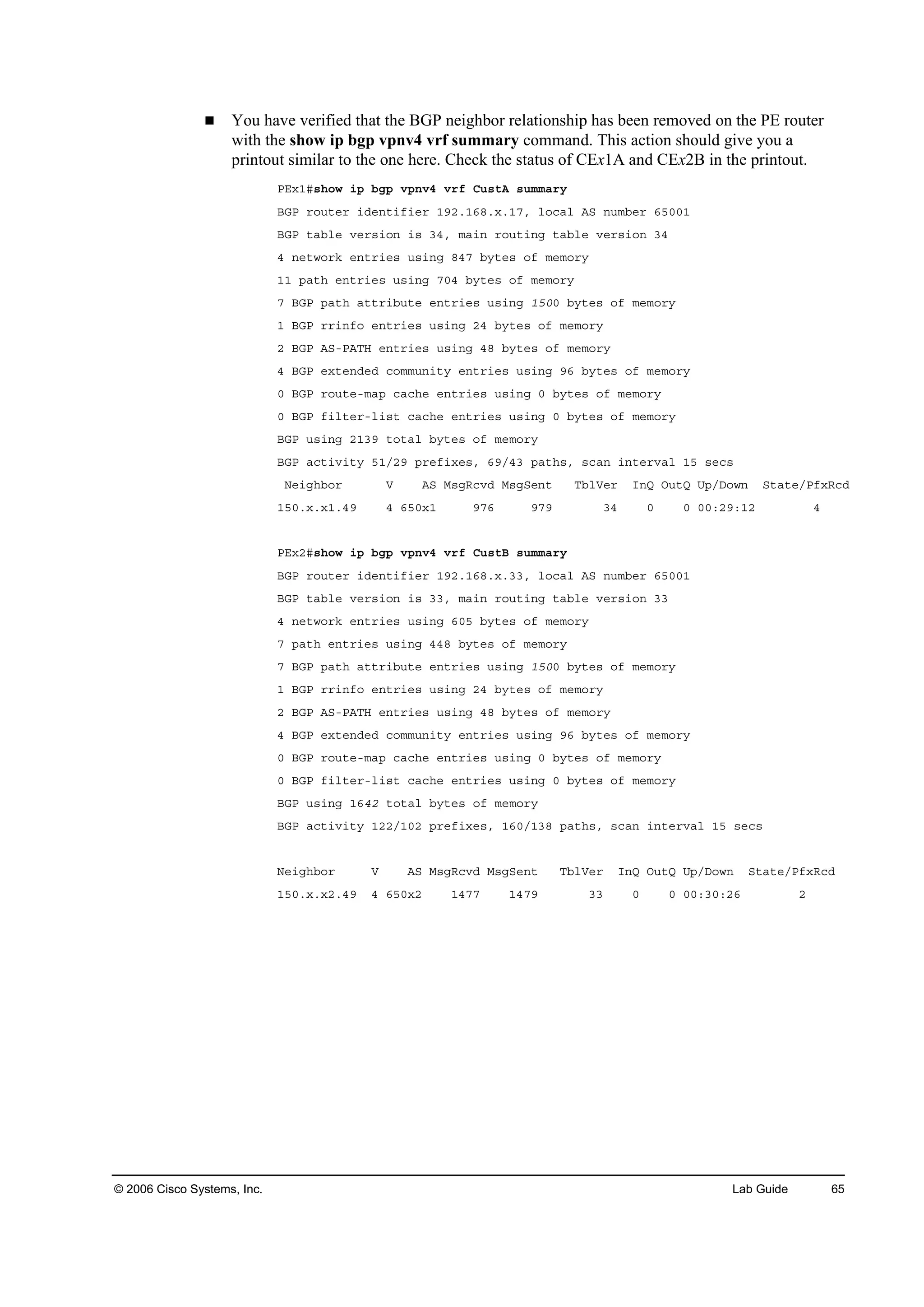
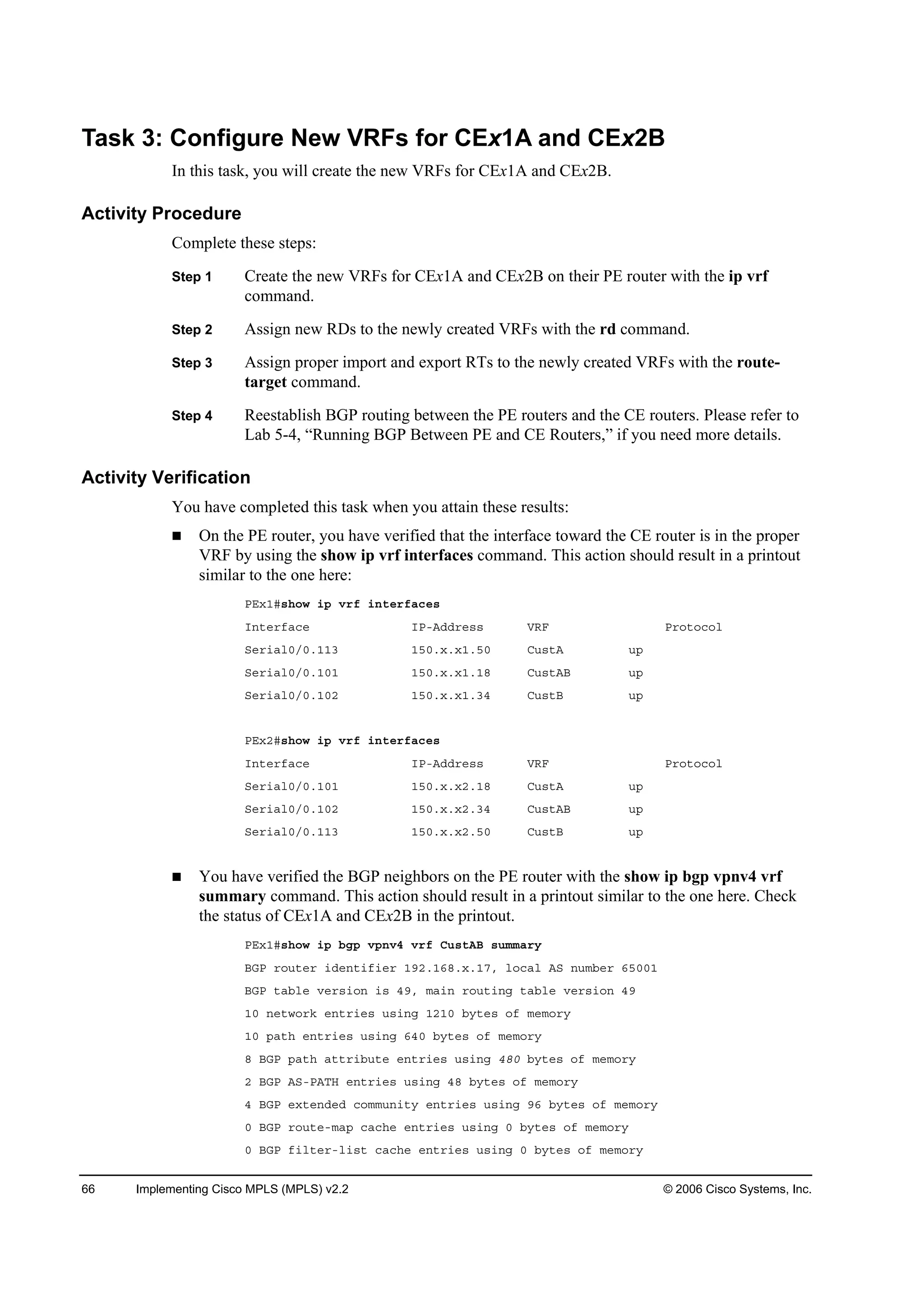
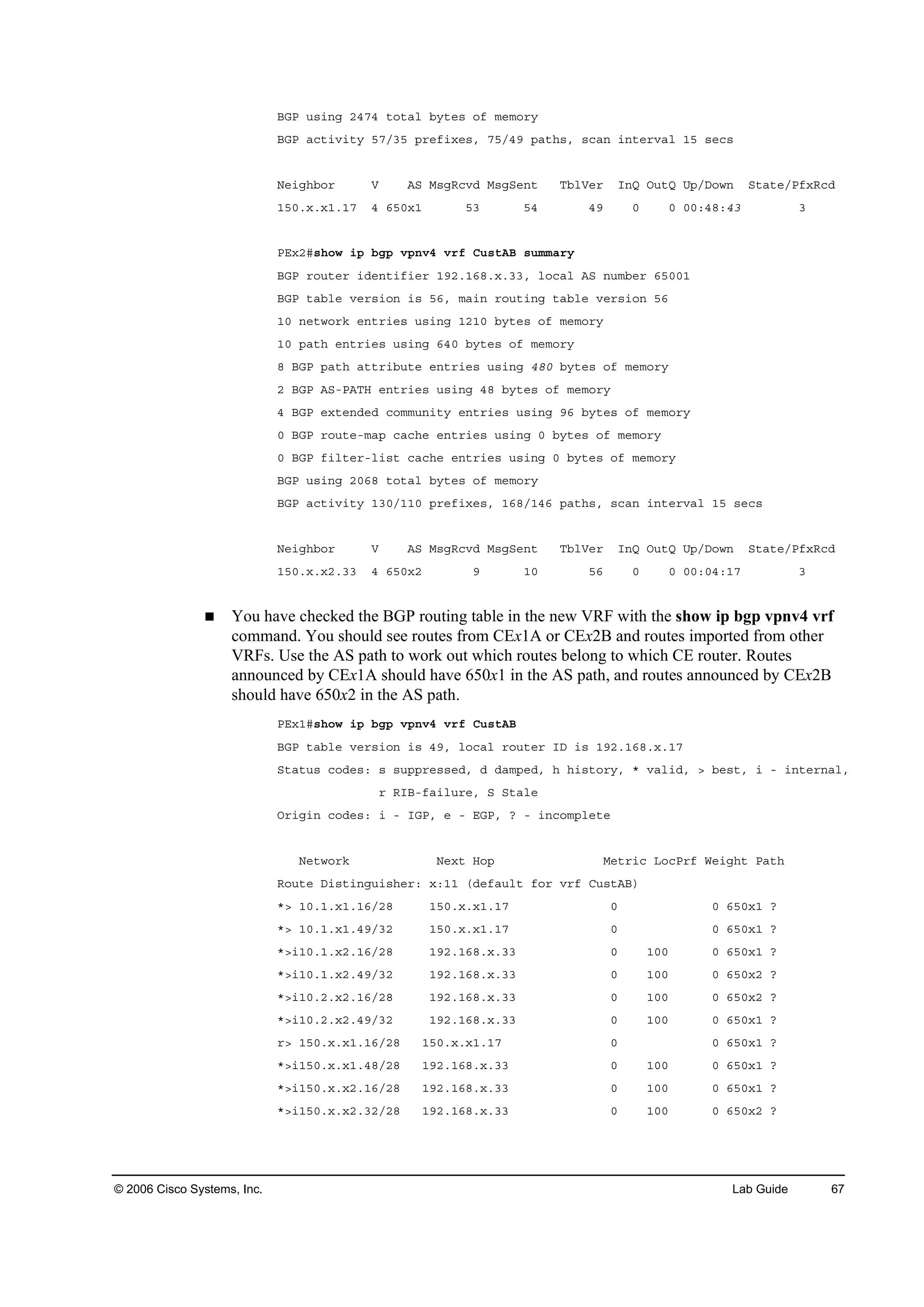
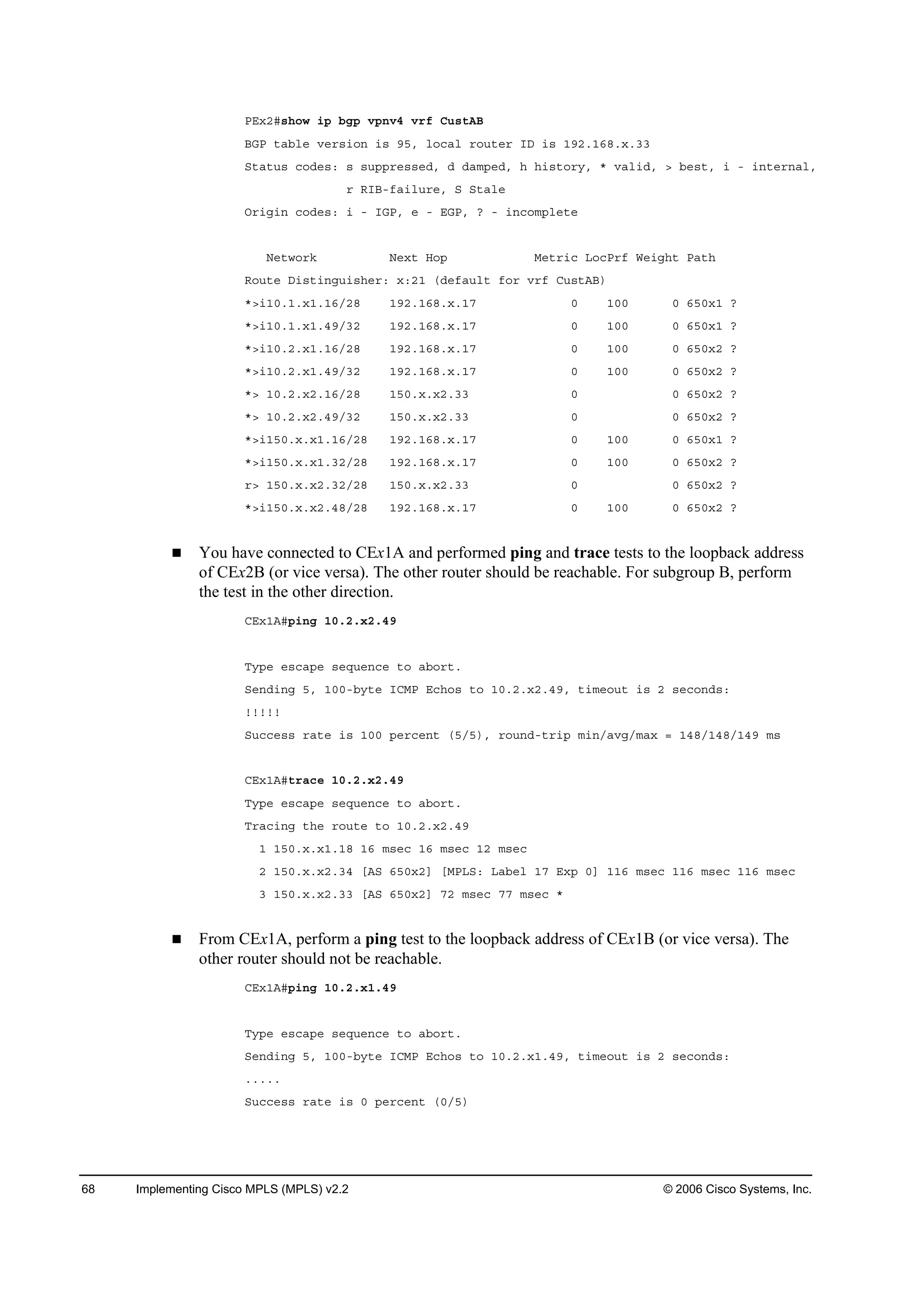
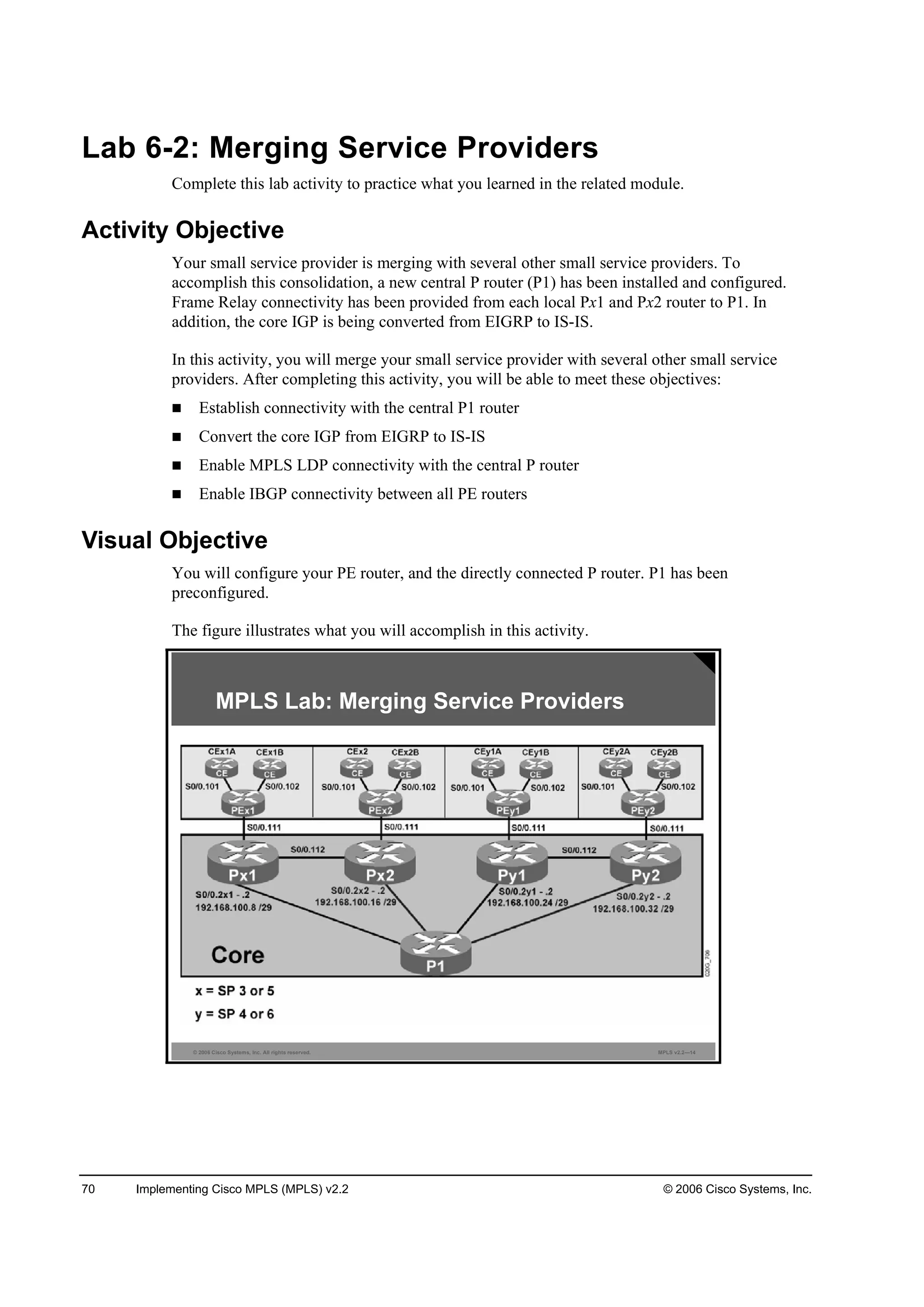
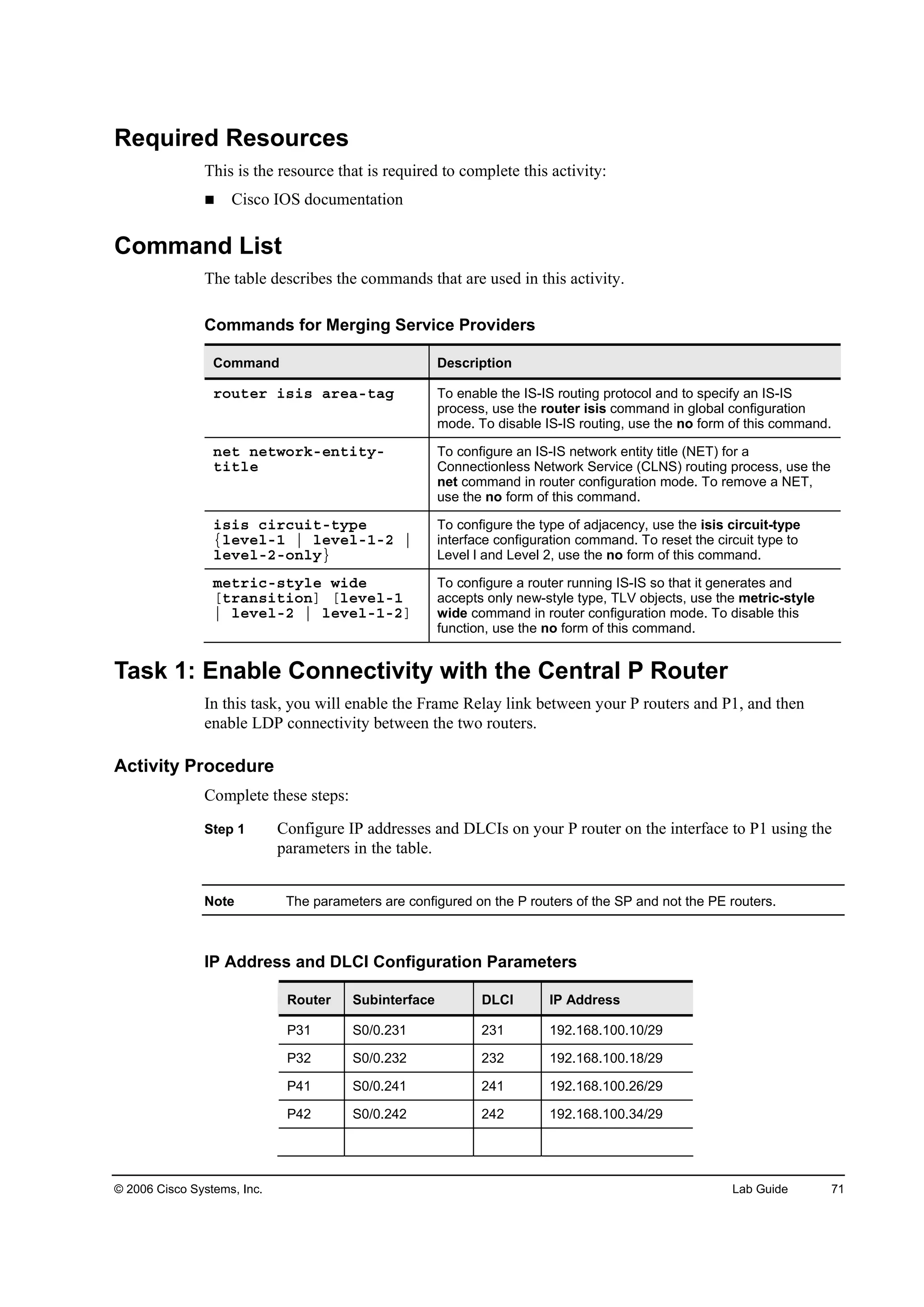
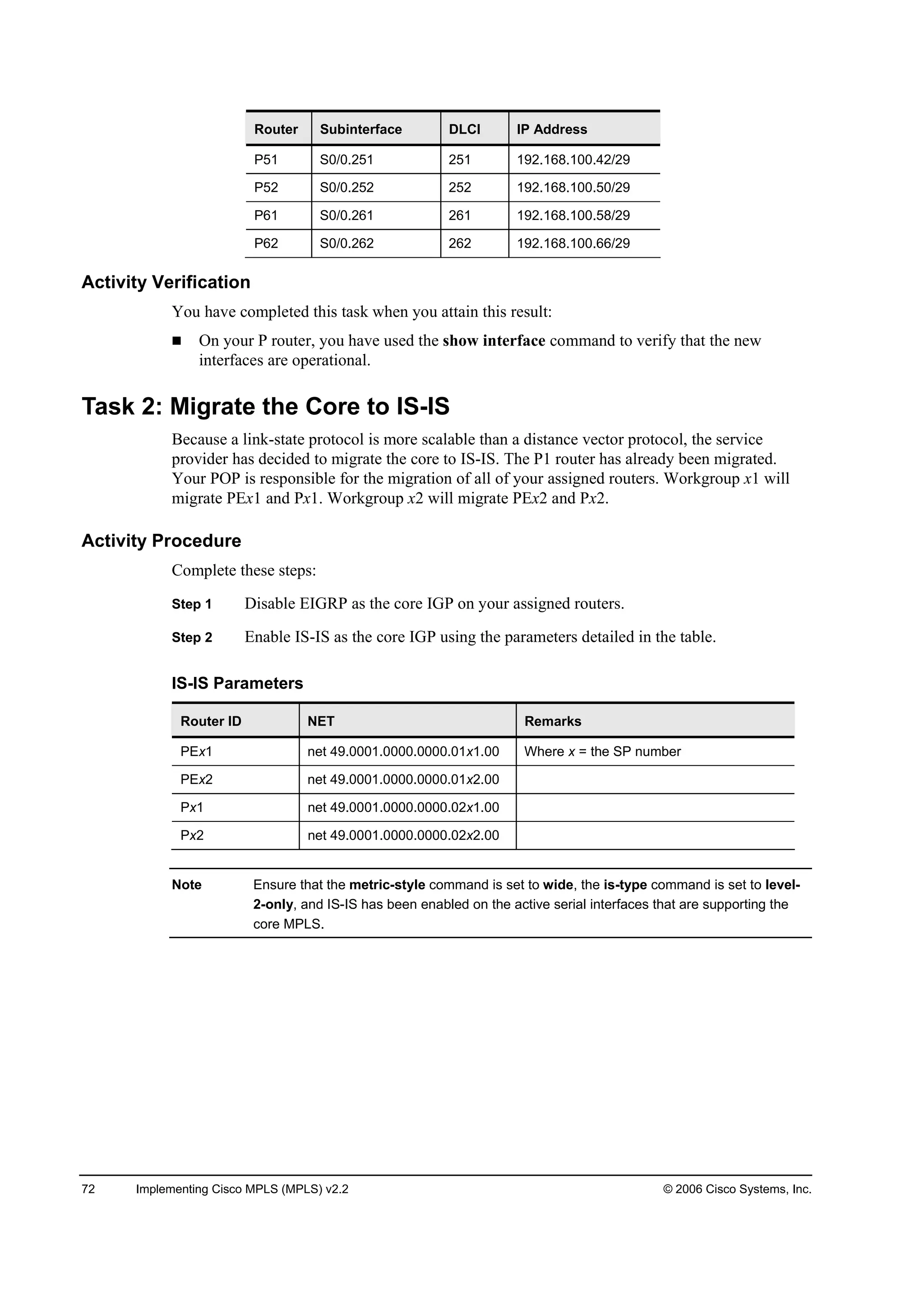
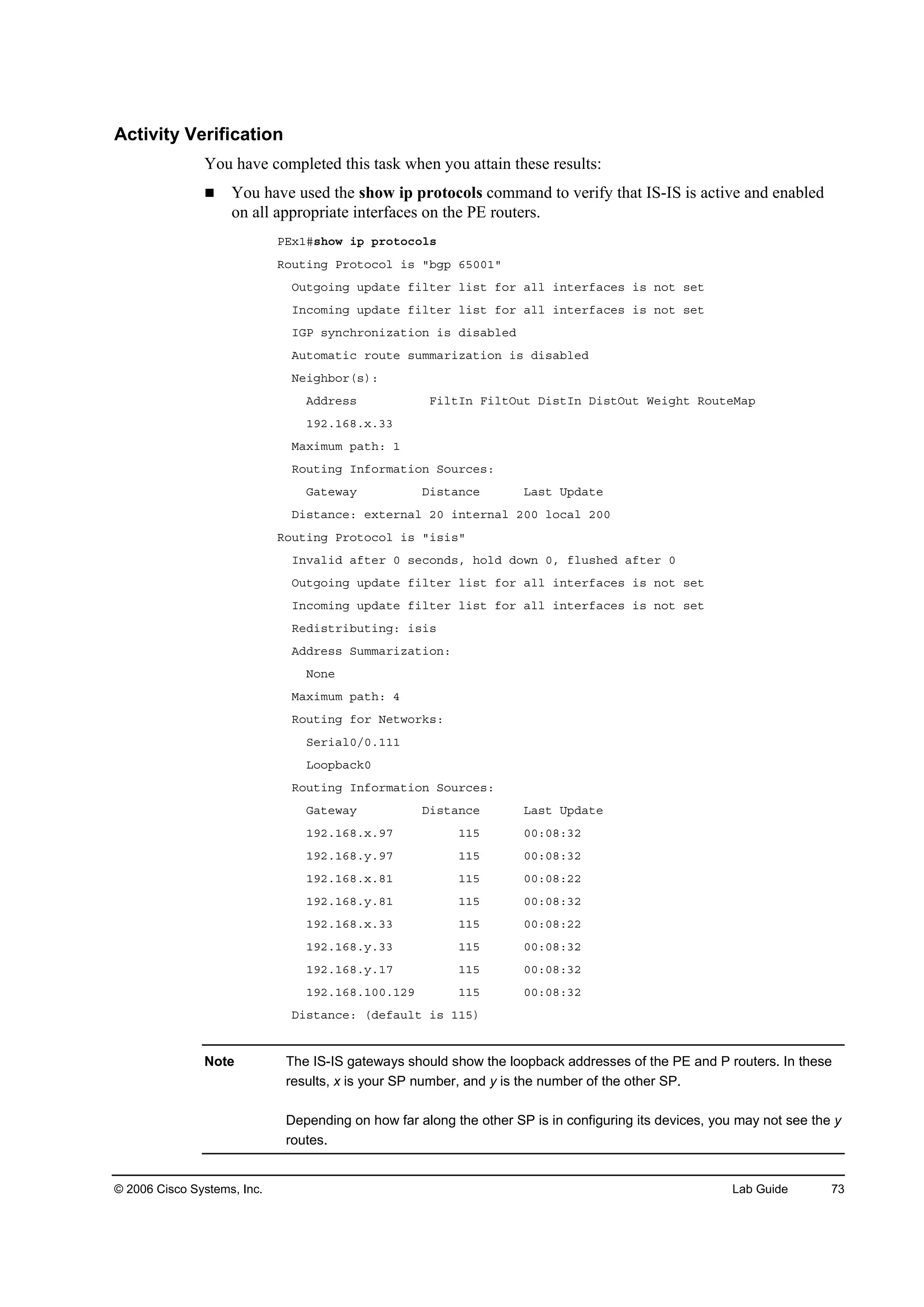
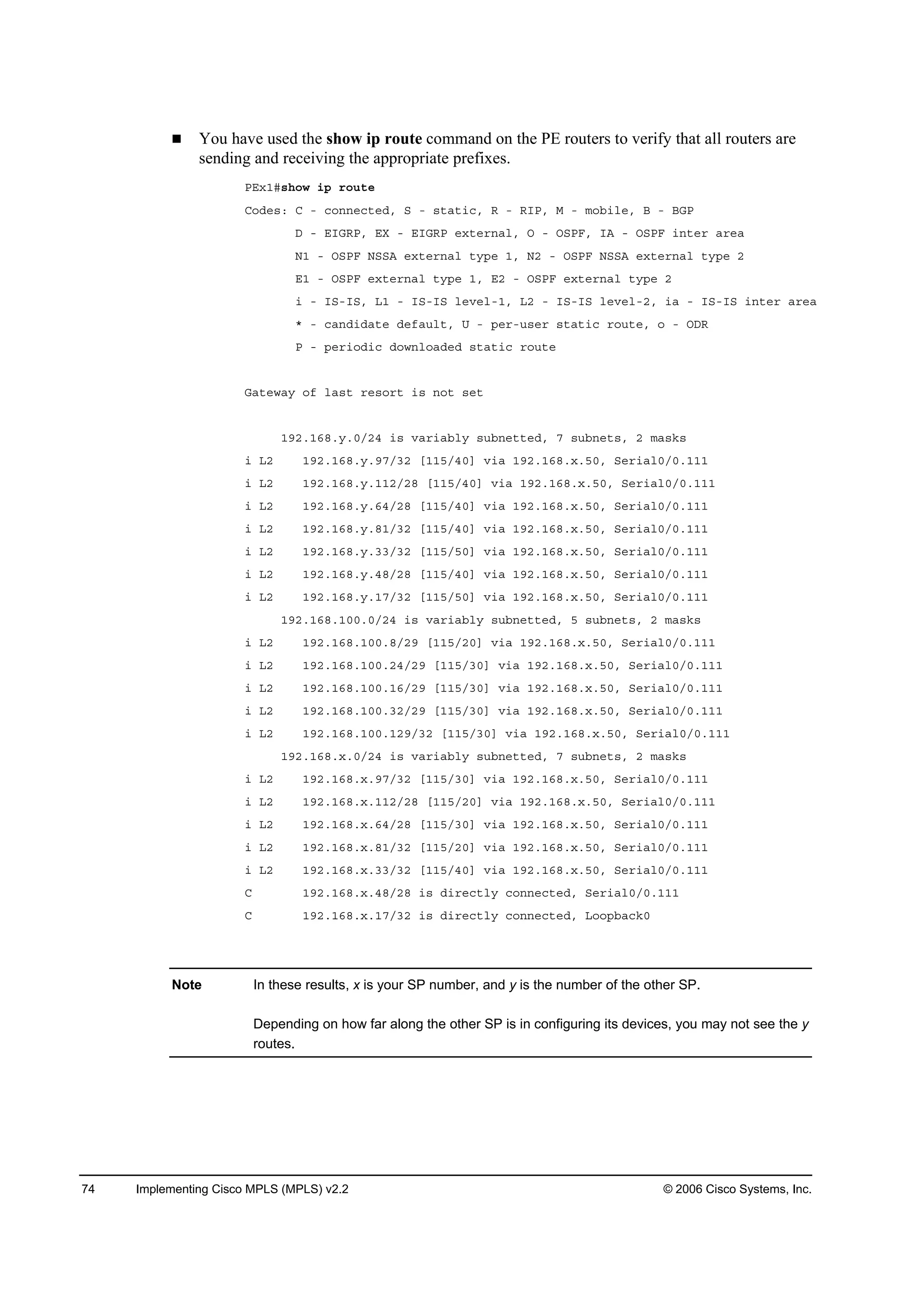
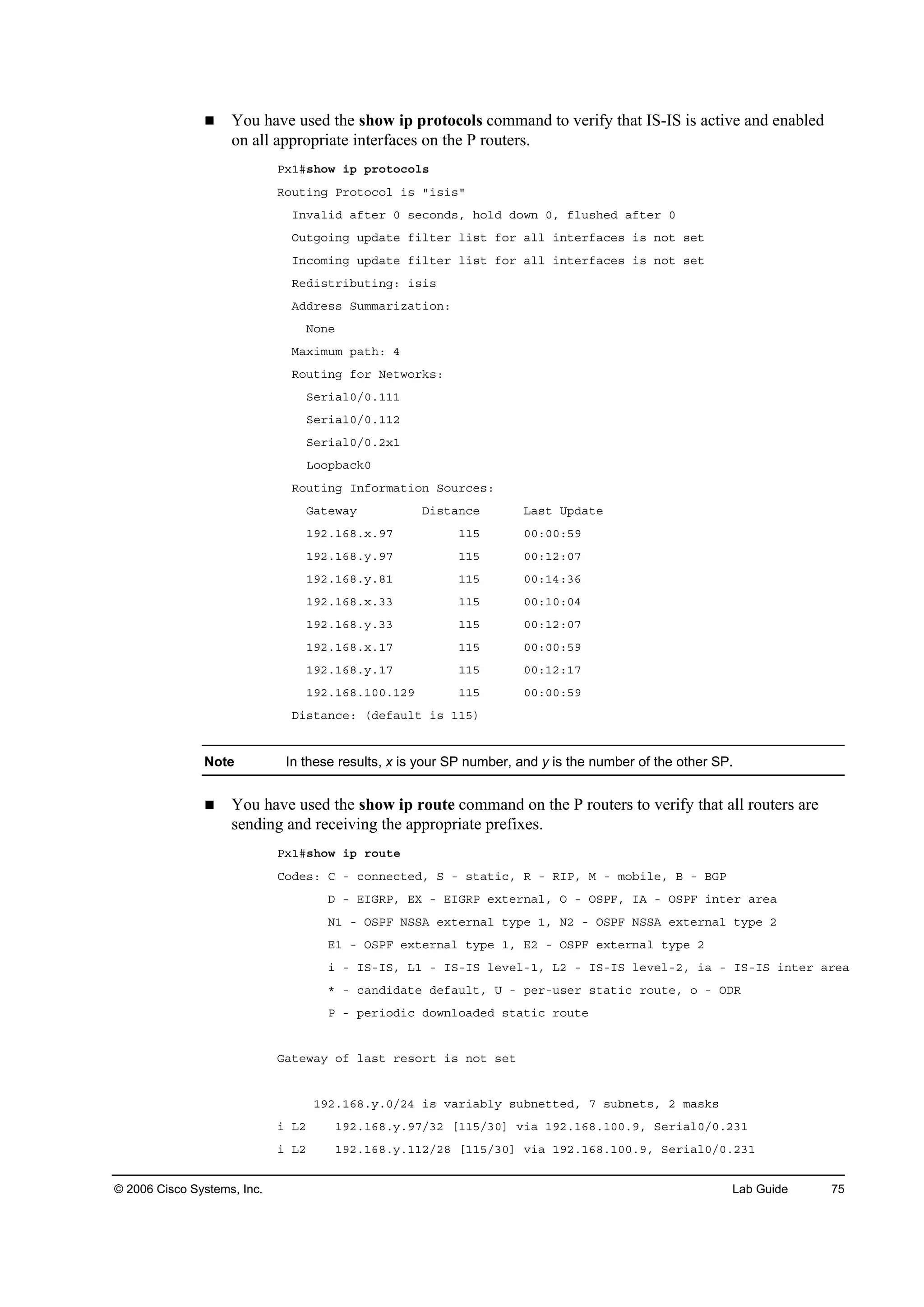
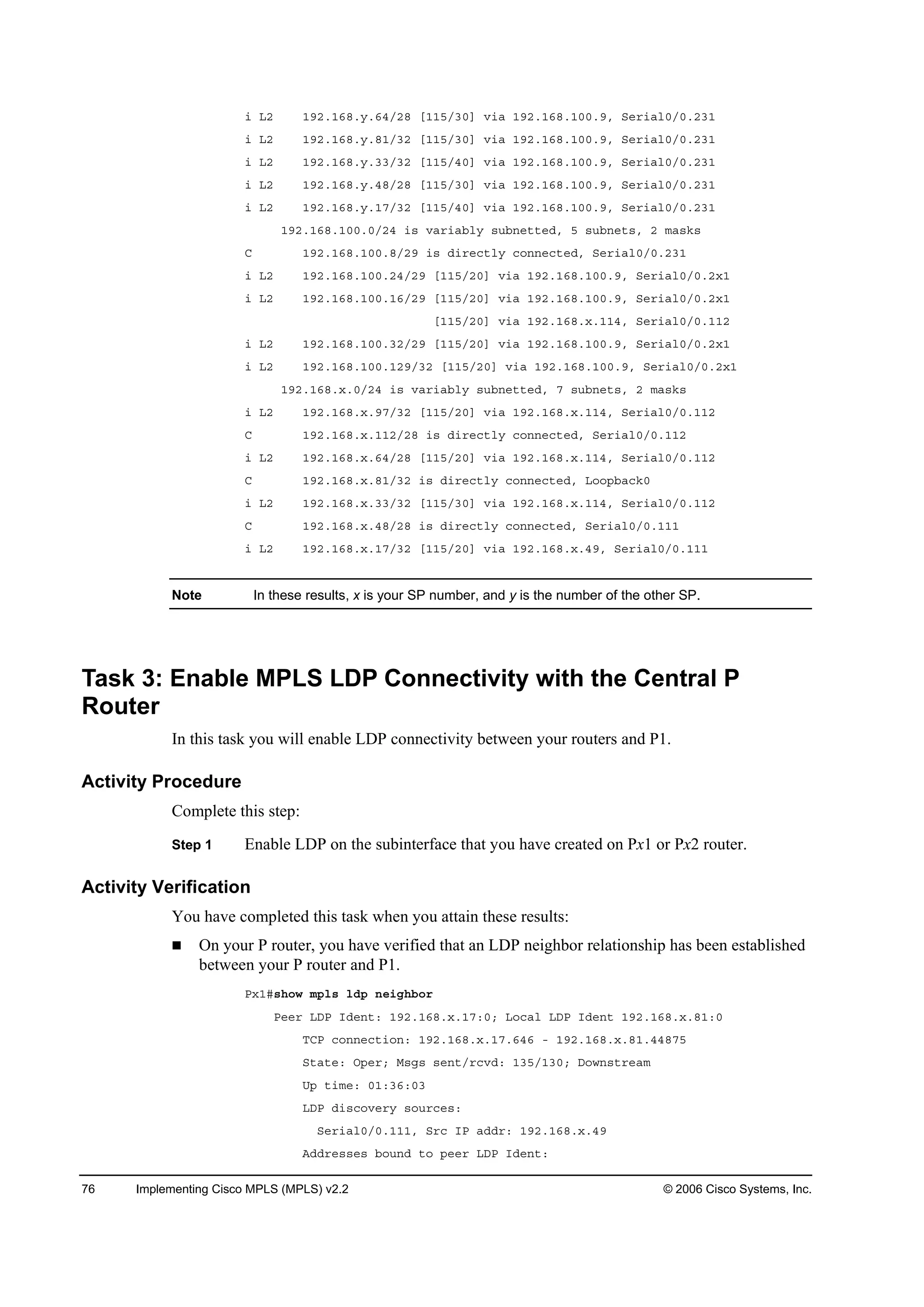
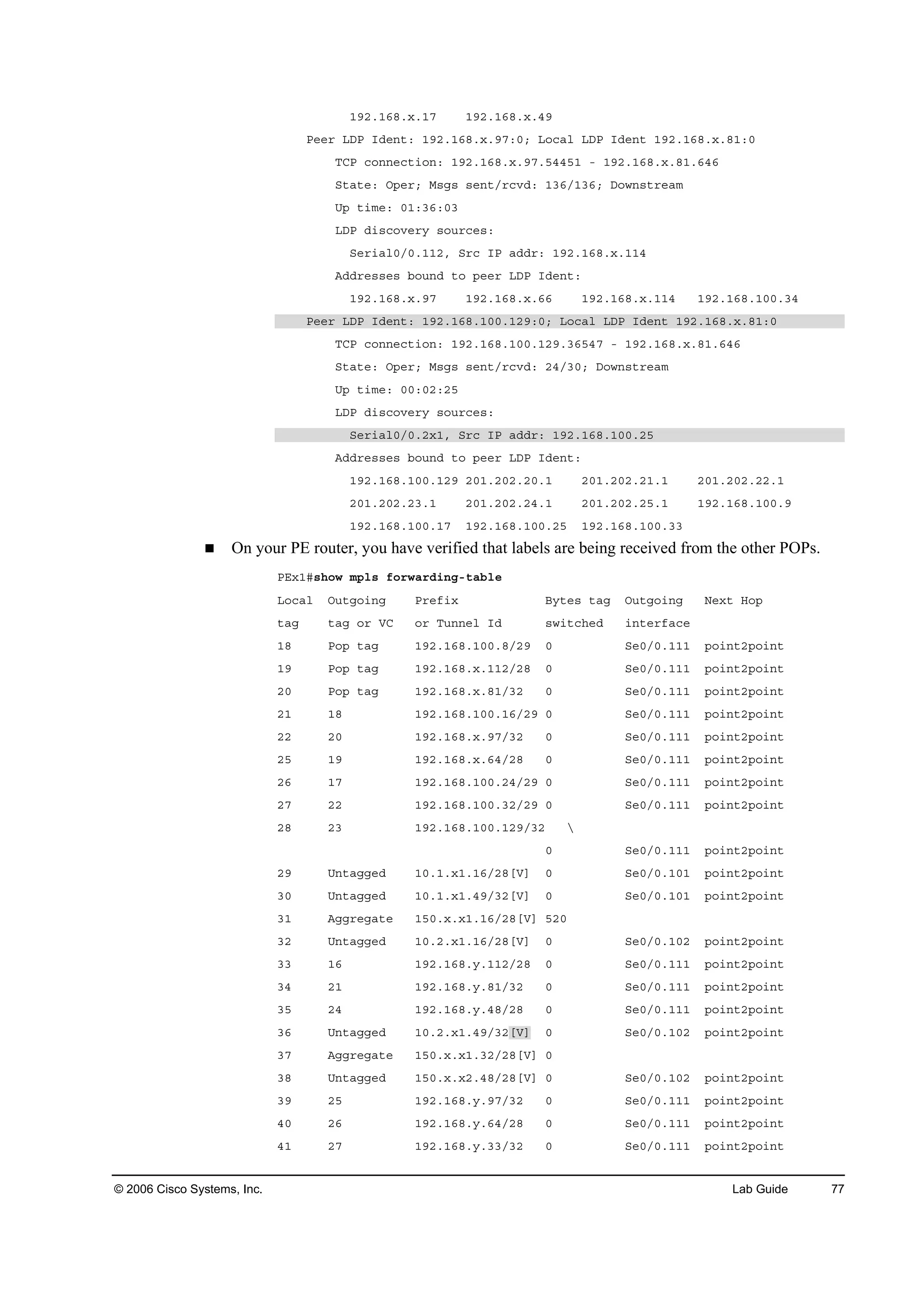
![78 Implementing Cisco MPLS (MPLS) v2.2 © 2006 Cisco Systems, Inc.
ěî îč ďçîňďęčň§ňďéńíî đ Í»đńđňďďď °±·˛¬î°±·˛¬
ěí íđ ďçîňďęčň¨ňííńíî đ Í»đńđňďďď °±·˛¬î°±·˛¬
Note In these results, x is your SP number, and y is the number of the other SP. The “[V]”
indicates a VPN prefix.
Task 4: Enable IBGP Connectivity for All PE Routers
At this point, you have established LDP connectivity for all of the PE and P routers in your new
service provider environment, but you have not yet established BGP connectivity. You now
need to establish IBGP connectivity for your PE routers.
There are two methods that you can implement. The first is to use the bgp neighbor command
to add a neighbor relationship between each of the routers, but this approach would entail a
substantial configuration effort.
The second method is to implement route reflectors. To this end, P1 has been configured as a
BGP route reflector. However, to take advantage of this fact, you will need to remove the
neighbor relationship between your two PE routers and make them neighbors of P1.
Note The loopback address for P1 is 192.168.100.129 with AS 65001. Ensure that your update
source is also your loopback interface.
Workgroup x1 will configure PEx1, and Workgroup x2 will configure PEx2.
Activity Procedure
Complete these steps:
Step 1 Remove the neighbor relationship between your PE router and the PE router in your
remote POP.
Step 2 Configure your PE router as a neighbor of P1.
What routes do you expect to see in VRF CustA?
What routes do you expect to see in VRF CustB?
What routes do you expect to see in VRF CustAB?
Activity Verification
You have completed this task when you attain these results:](https://image.slidesharecdn.com/implementingciscompls-140803084228-phpapp01/75/Implementing-cisco-mpls-749-2048.jpg)