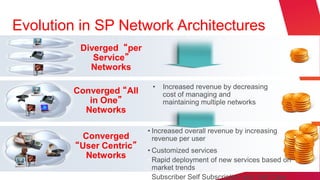
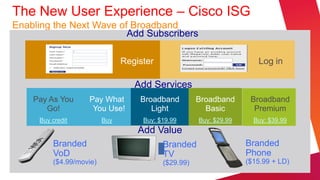
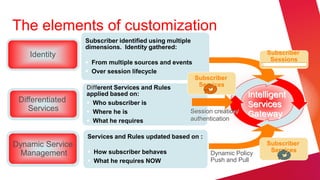
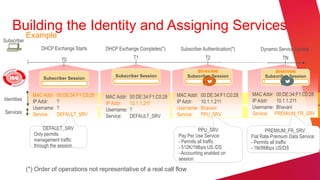
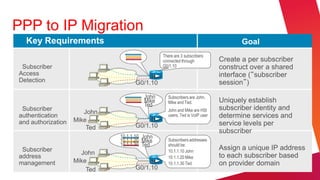
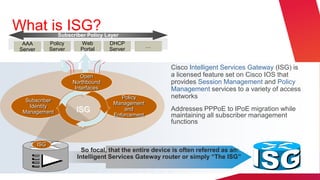
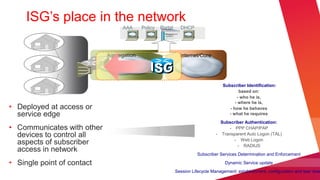
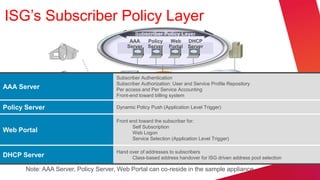
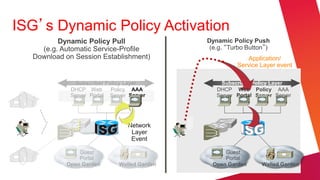
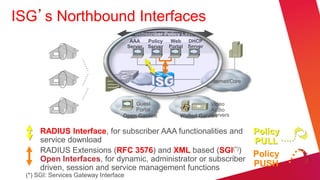
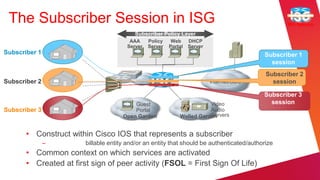
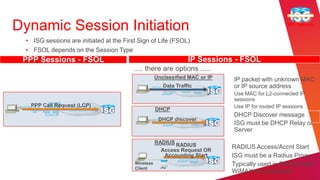
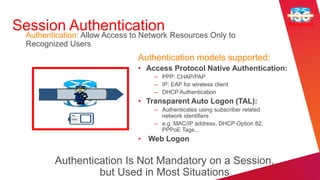
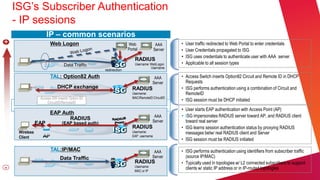
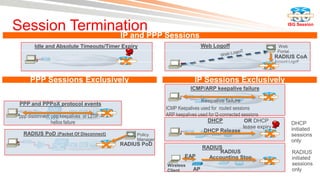
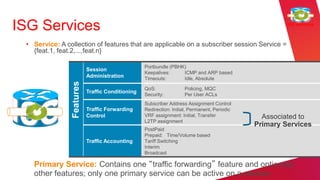
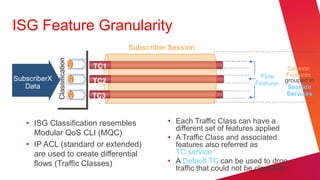
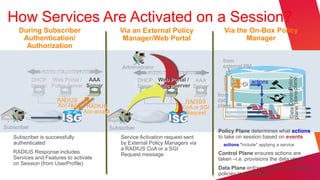
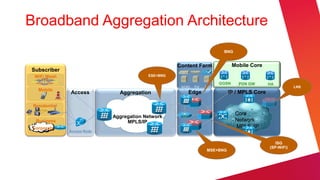
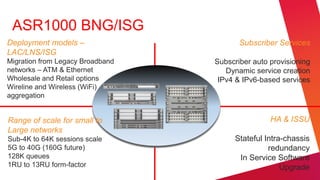
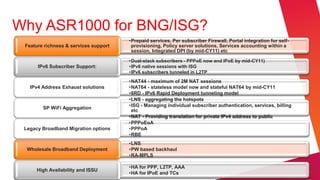
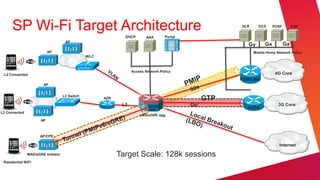
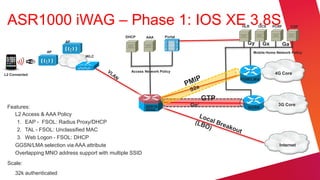
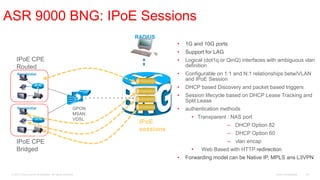
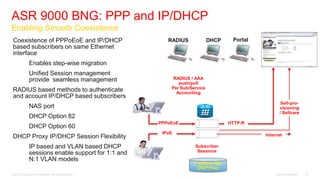
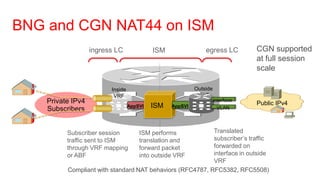
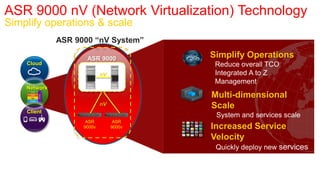
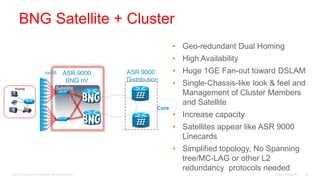
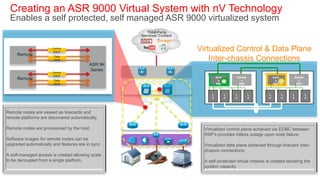
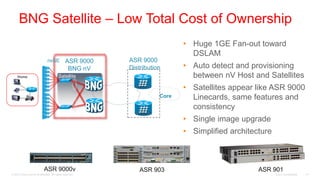
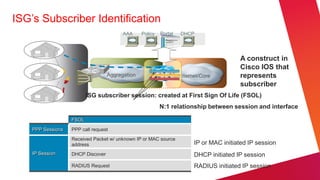
The document discusses subscriber traffic and policy management on Cisco's ASR9000 and ASR1000 systems, emphasizing the evolution of broadband architectures and user-centric services. It outlines key features such as dynamic service updates, subscriber identification, and management functionalities enabled by Cisco's Intelligent Services Gateway (ISG). The document also highlights deployment models, scalability options, and specific technical capabilities for optimizing broadband delivery and subscriber experiences.