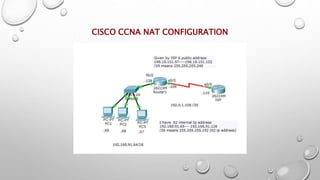
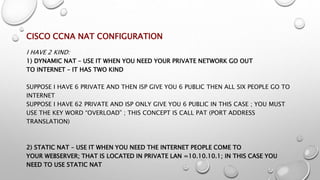
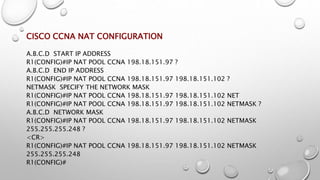
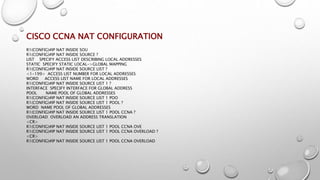
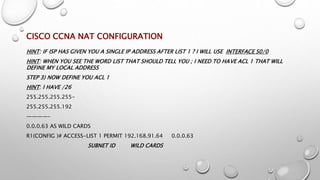
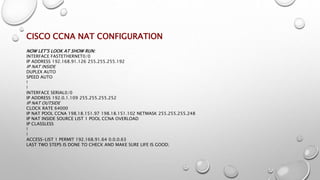
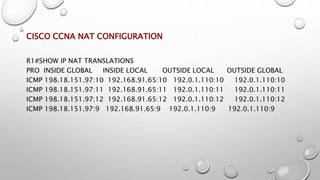
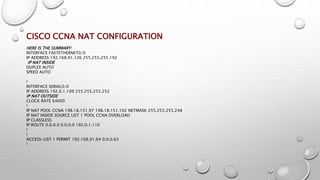
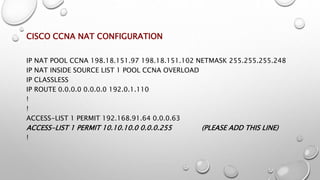
The document provides a detailed guide on Cisco CCNA Network Address Translation (NAT) configuration, explaining both dynamic and static NAT. It includes step-by-step instructions to configure a NAT with examples of commands and IP addresses, emphasizing the setup of access lists and defining inside and outside interfaces. Additional notes clarify when to use NAT pools and the importance of ensuring the ISP is aware of the network's public address.