Embed presentation





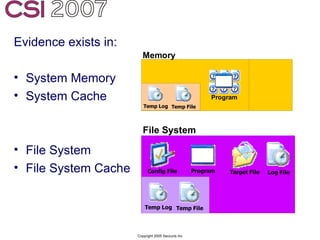
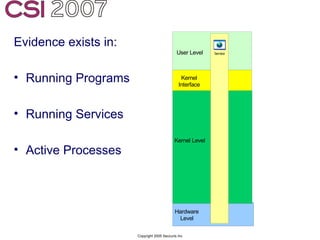

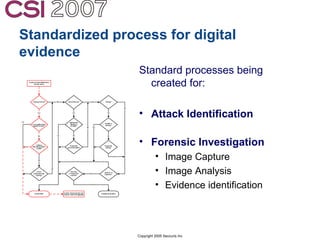

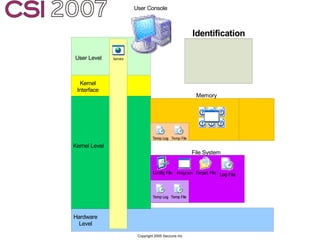




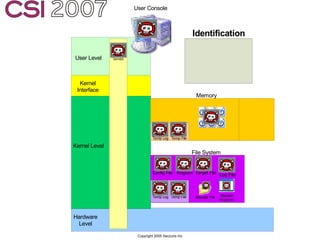

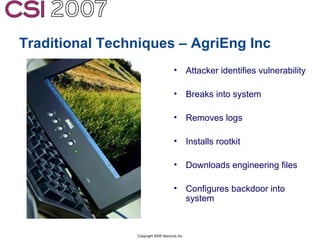
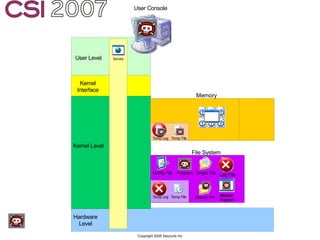
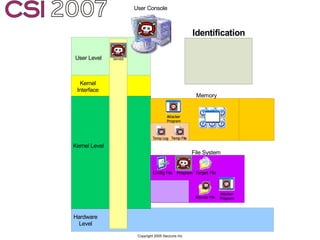


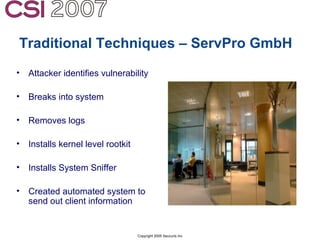


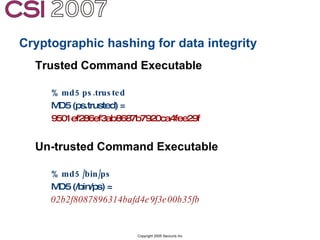
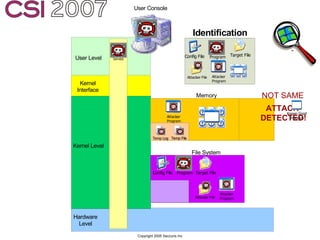
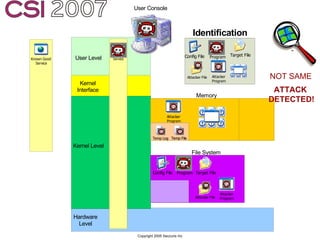
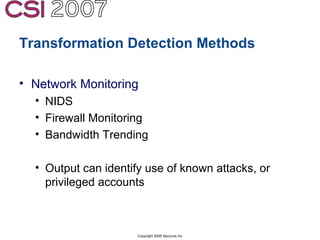
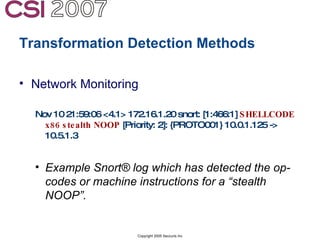

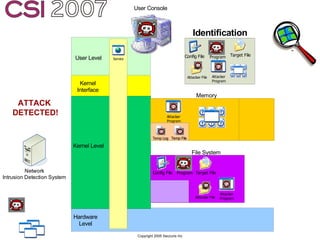
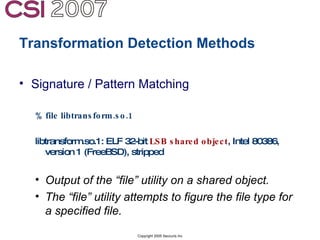
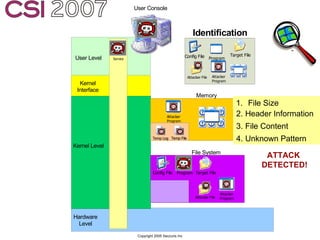
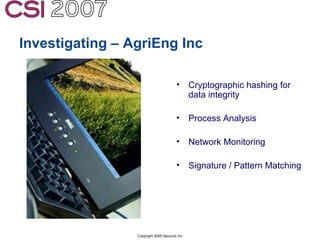



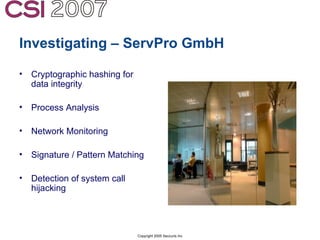
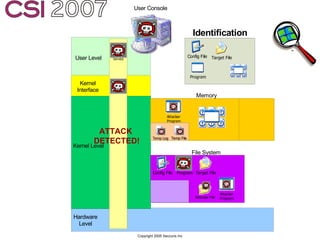
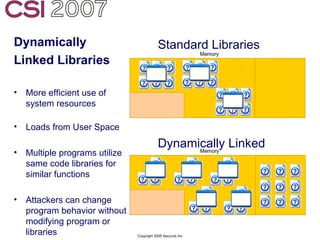
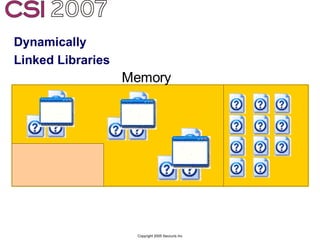
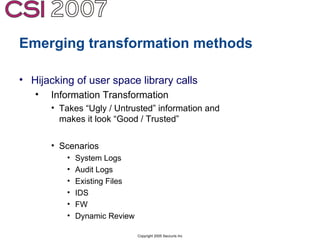
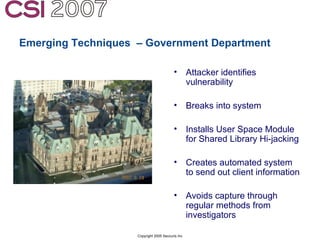
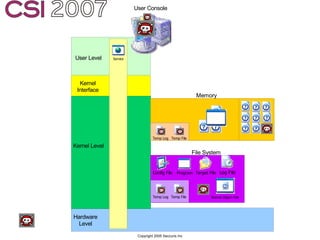
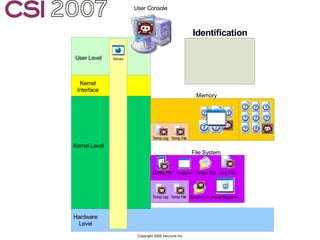
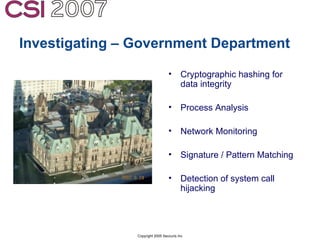
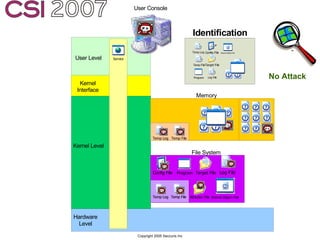

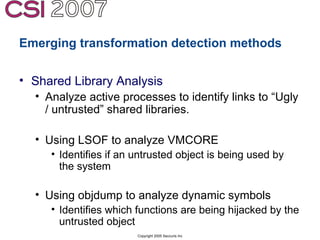
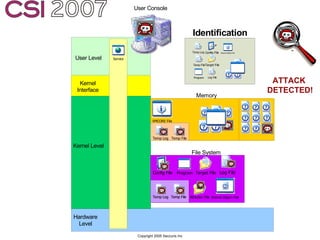


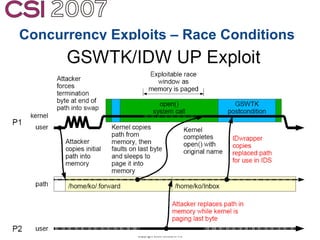




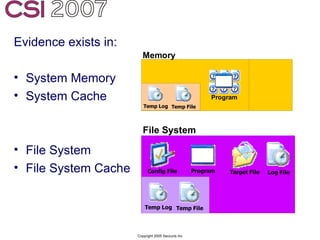
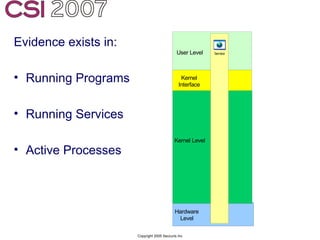
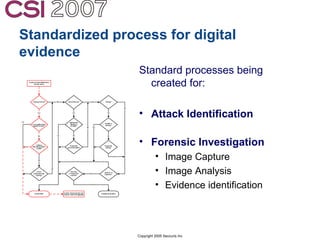
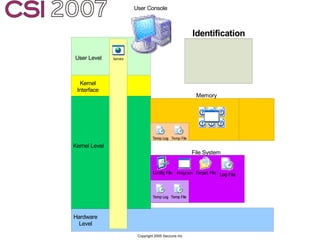
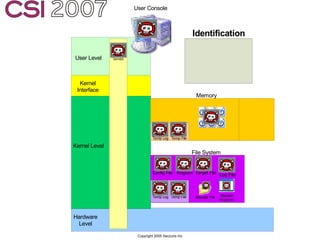
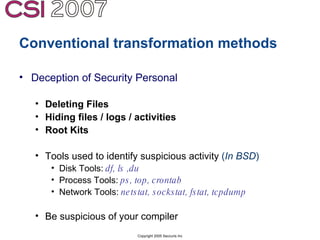
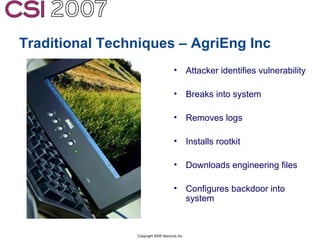
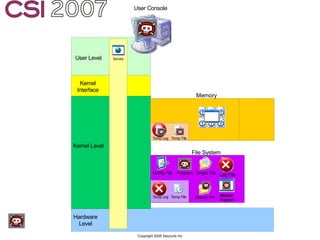
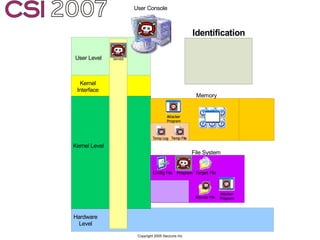
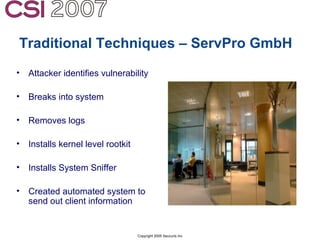
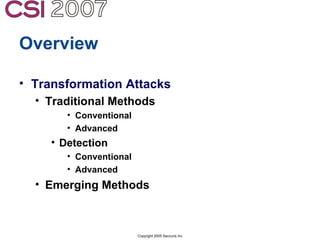
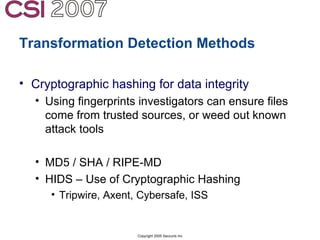
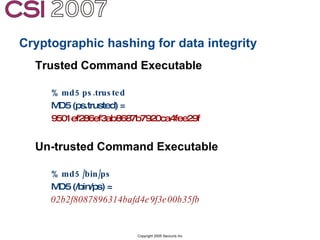
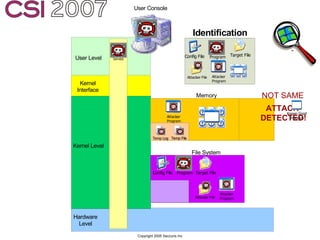
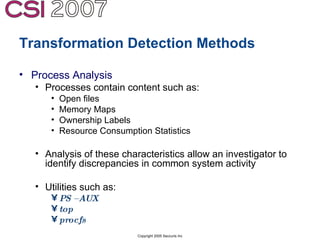
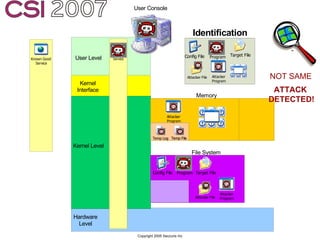
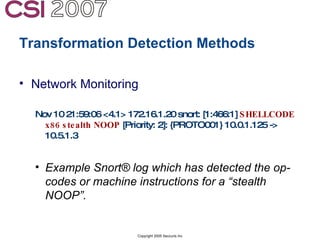
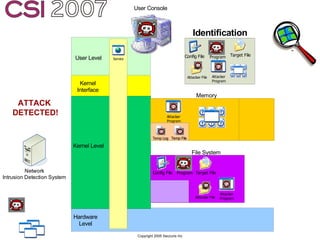
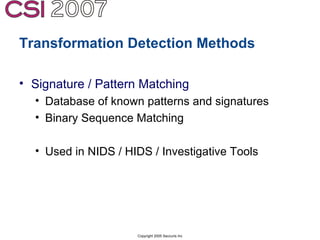
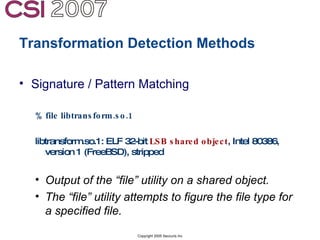
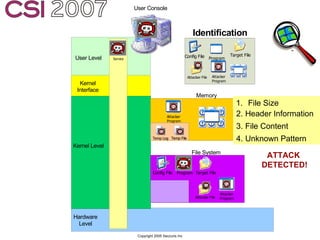
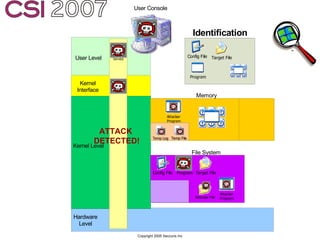
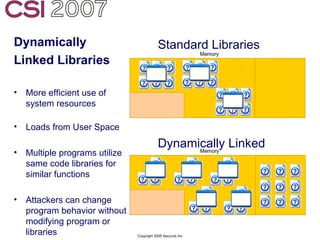
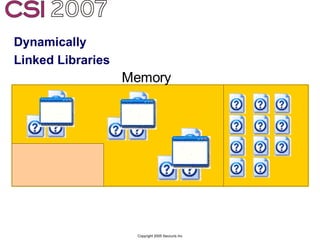
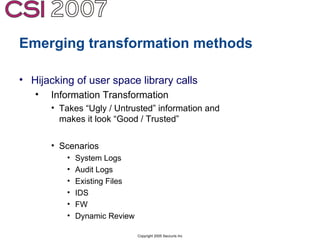
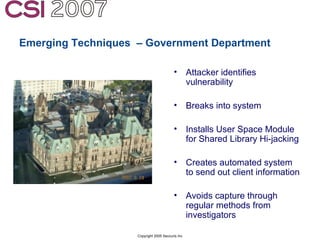
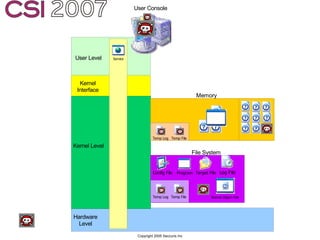
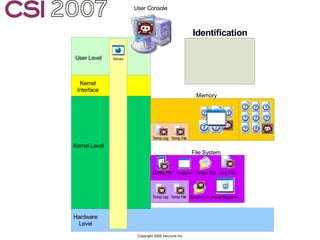
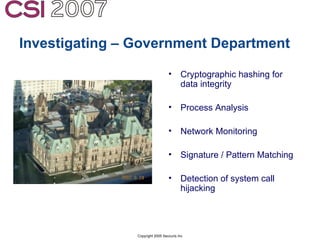
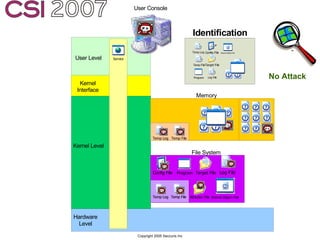
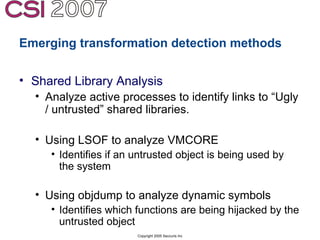
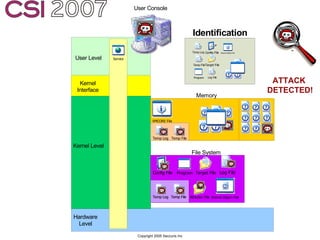
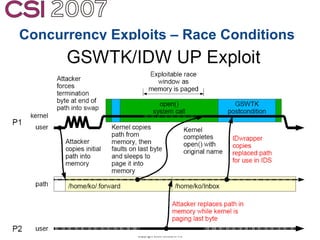
The document discusses digital anti-forensics, focusing on methods used to obscure and manipulate evidence in investigations, as well as the implications for forensic analysis. It highlights various methods of preventing detection, including data destruction, hiding, and transformation techniques, and addresses the challenges investigators face in identifying compromised systems. Additionally, it outlines current trends, preventive measures, and standardized processes for enhancing digital evidence collection and analysis.