Embed presentation

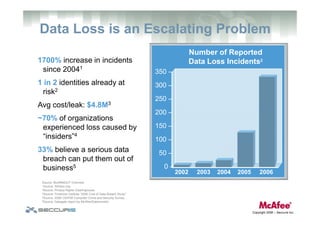
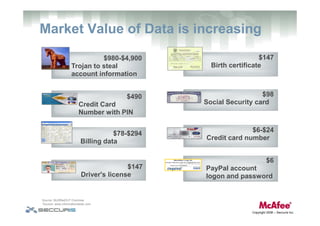
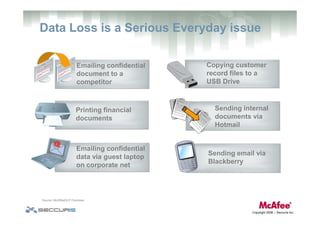


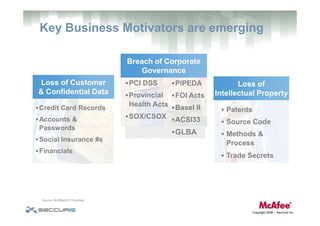

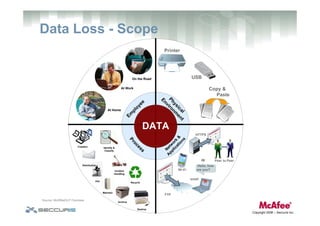
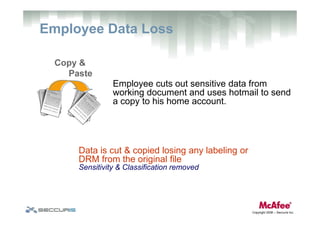
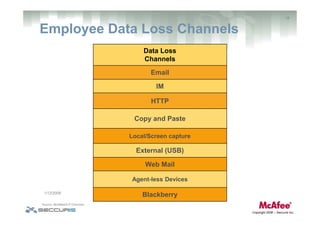
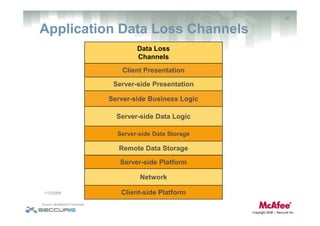
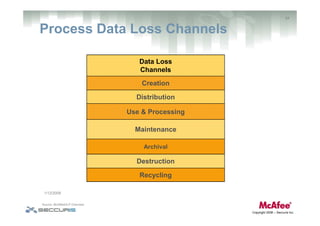

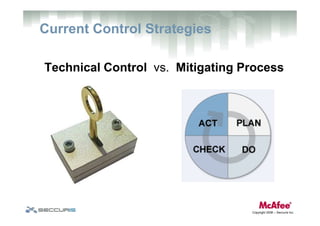
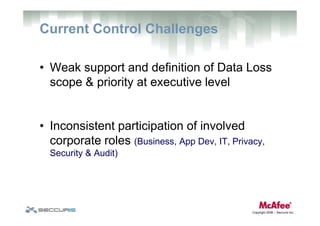
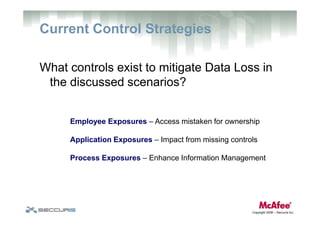
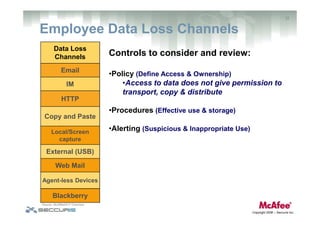
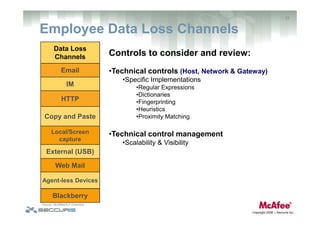
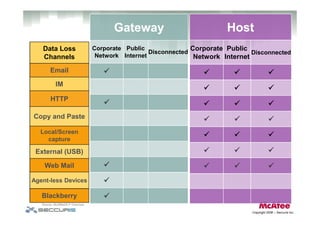
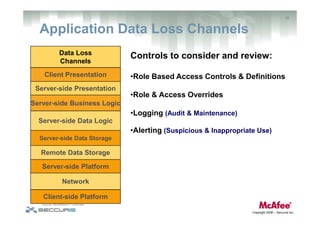
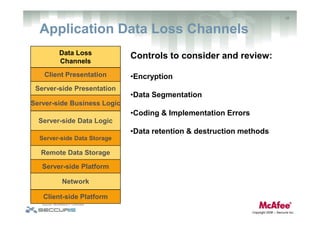
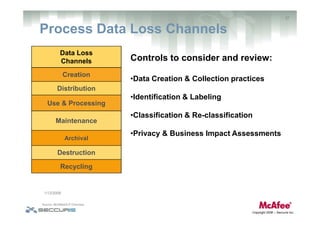
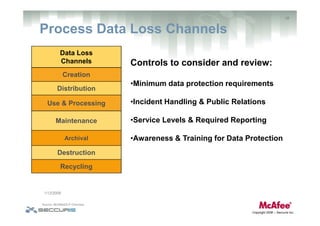
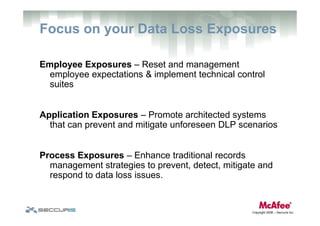


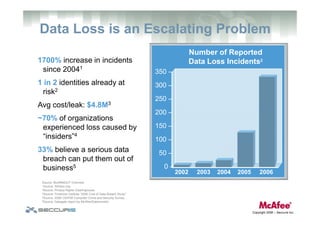
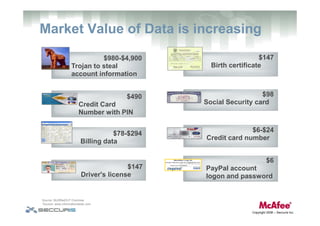
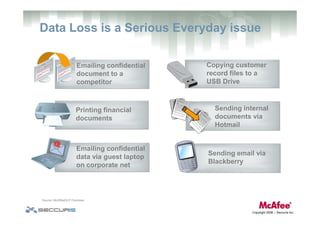
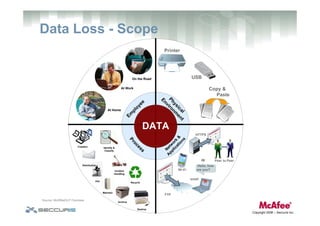
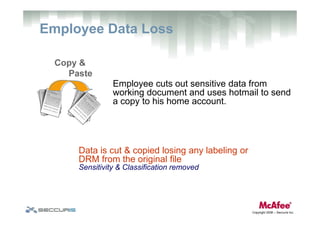
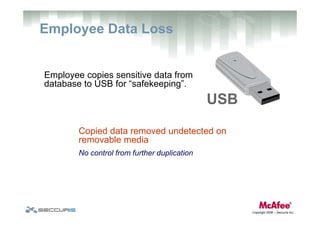
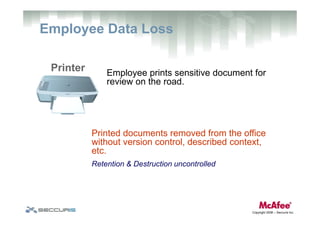
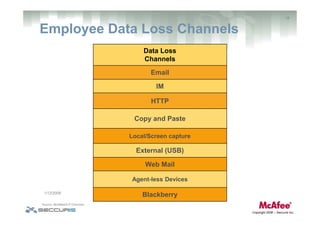
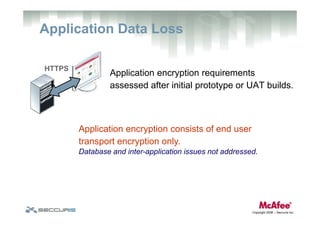
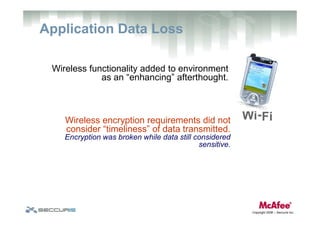
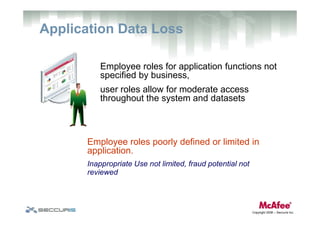
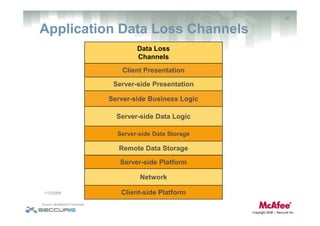
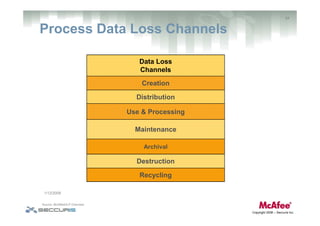
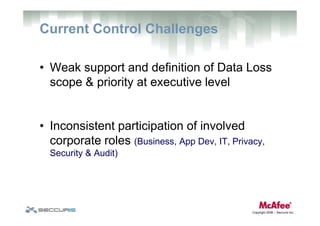
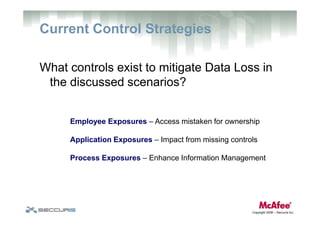
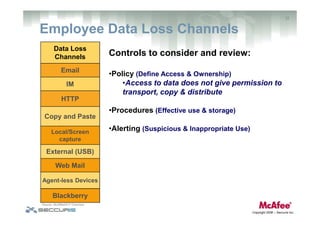
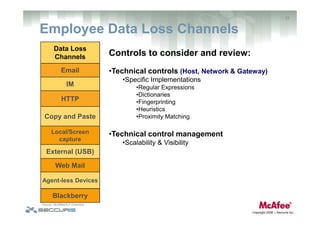
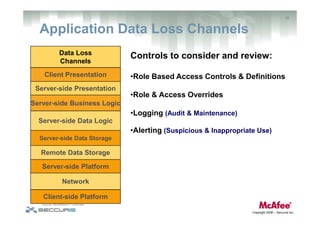
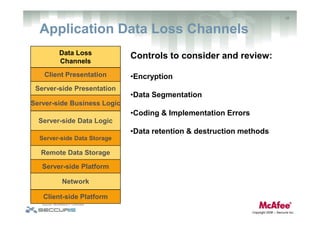
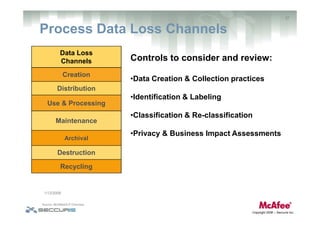
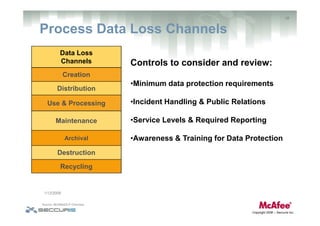
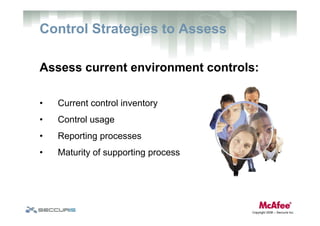
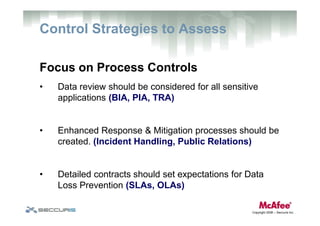
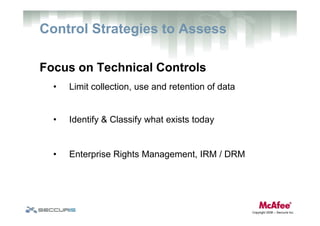
The document discusses data loss prevention challenges and strategies. It notes that data loss incidents have increased significantly in recent years and now cost organizations millions on average. Many data losses are caused by employees and insiders. The document outlines various types of employee, application, and process exposures that can lead to data loss and recommends assessing current controls and focusing on technical controls, access management, and process controls to better mitigate risks.