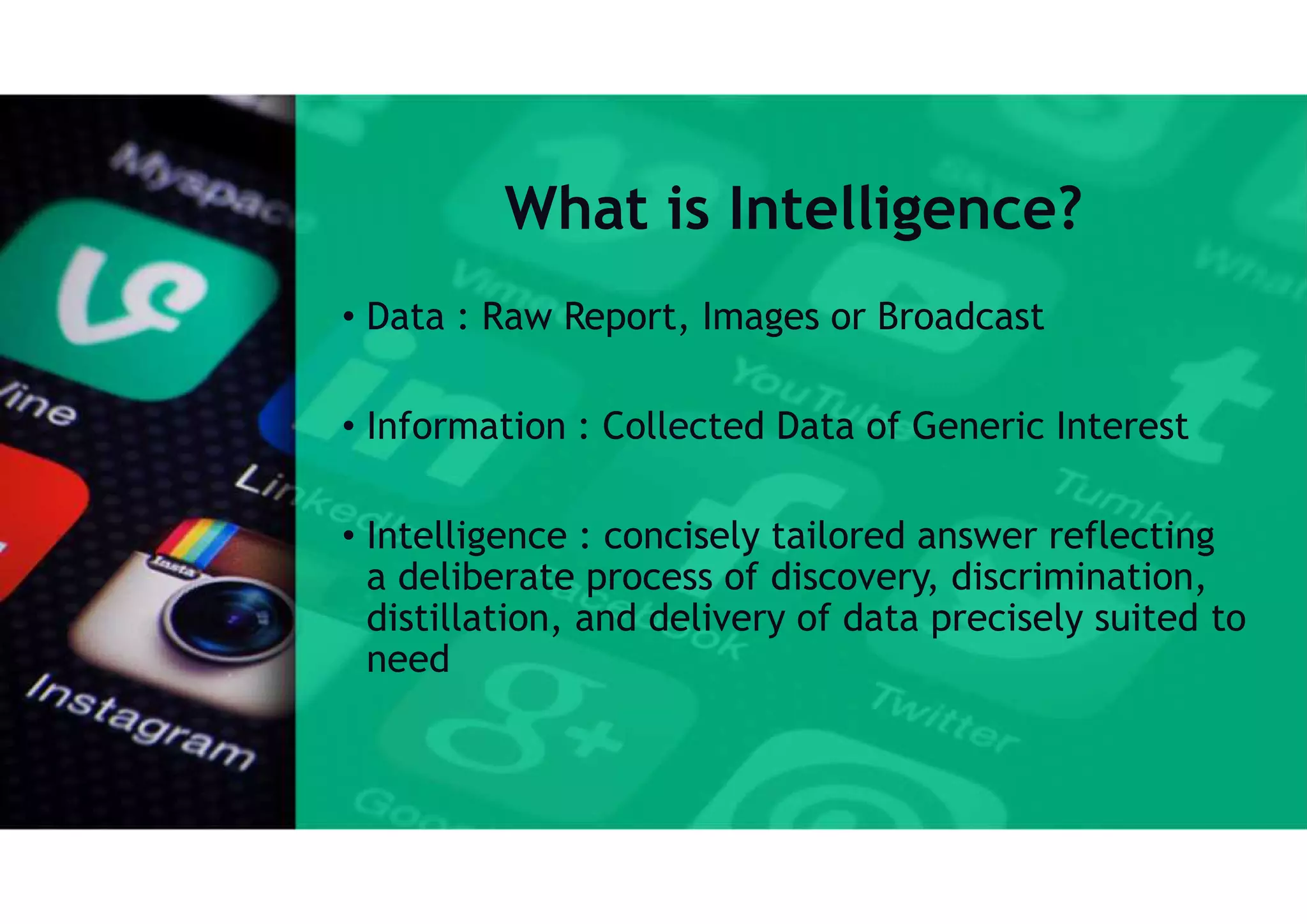
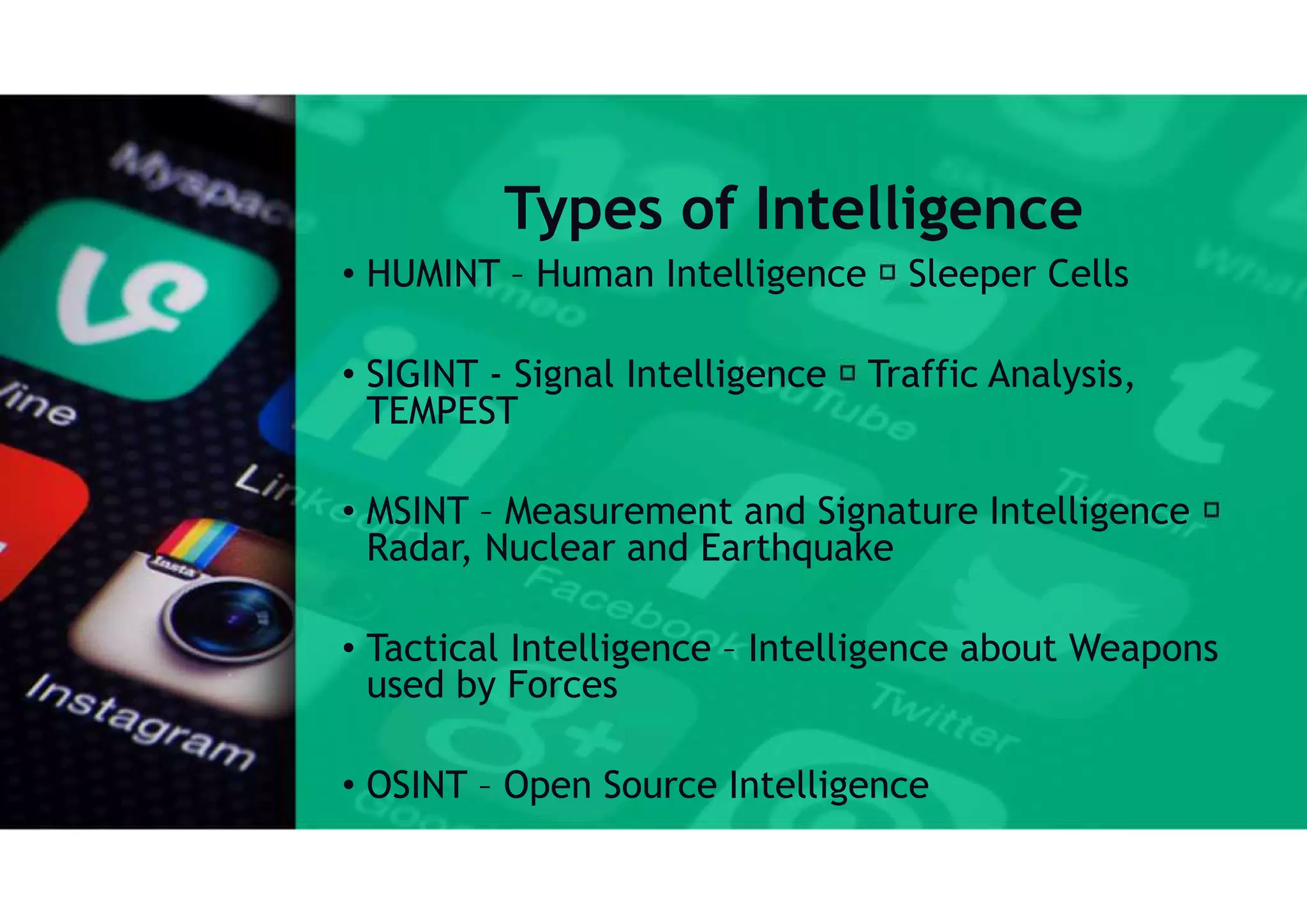
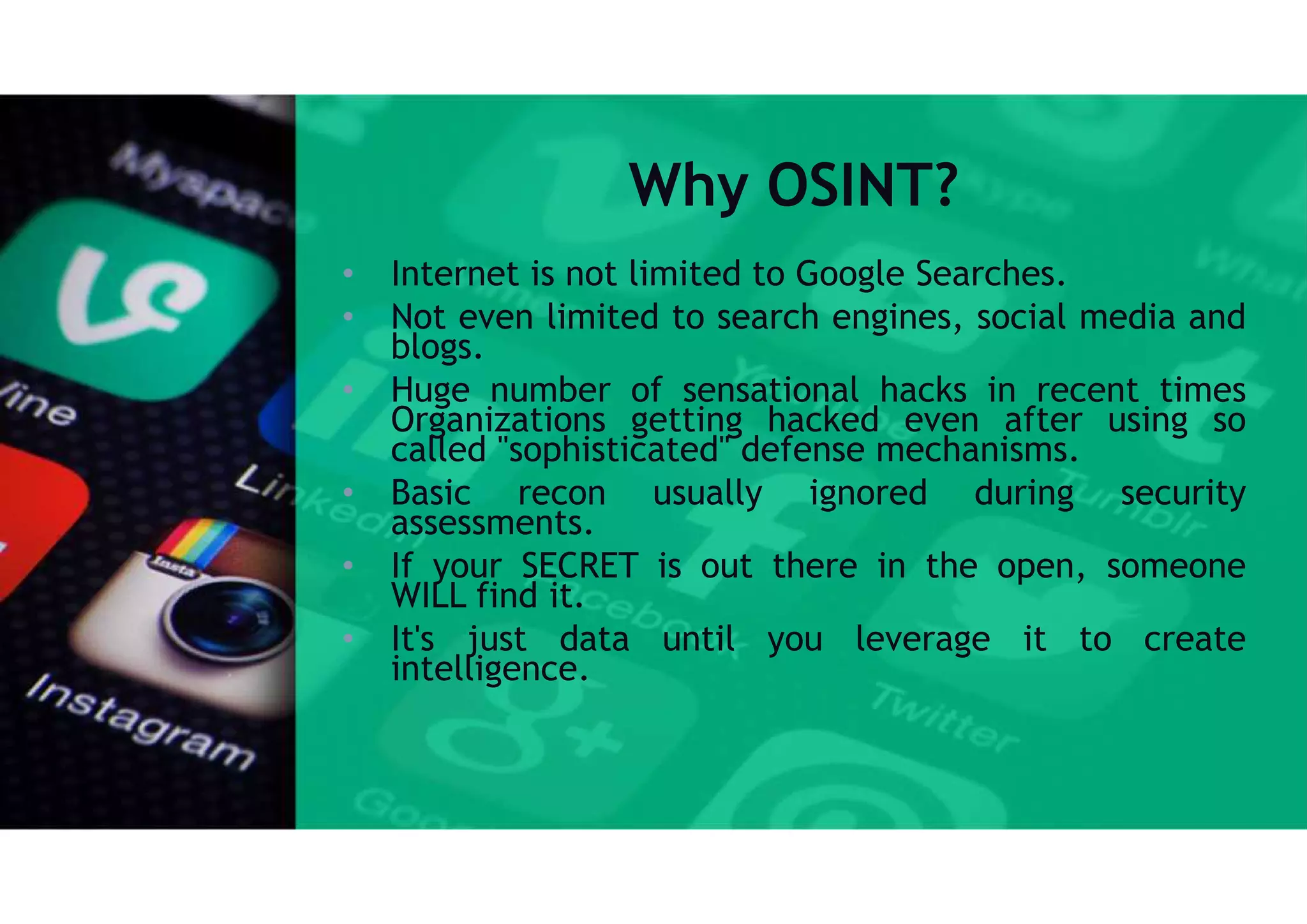
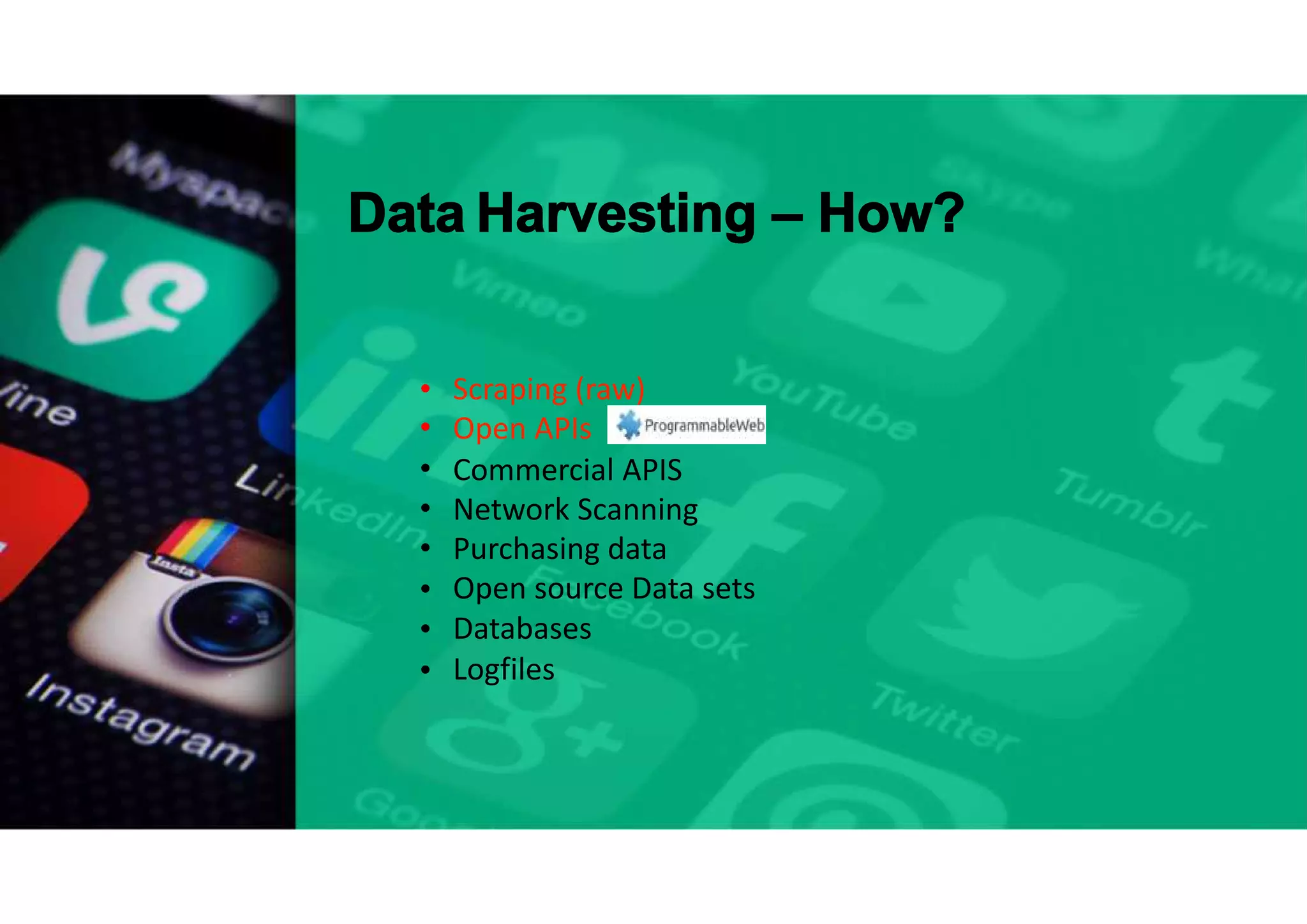
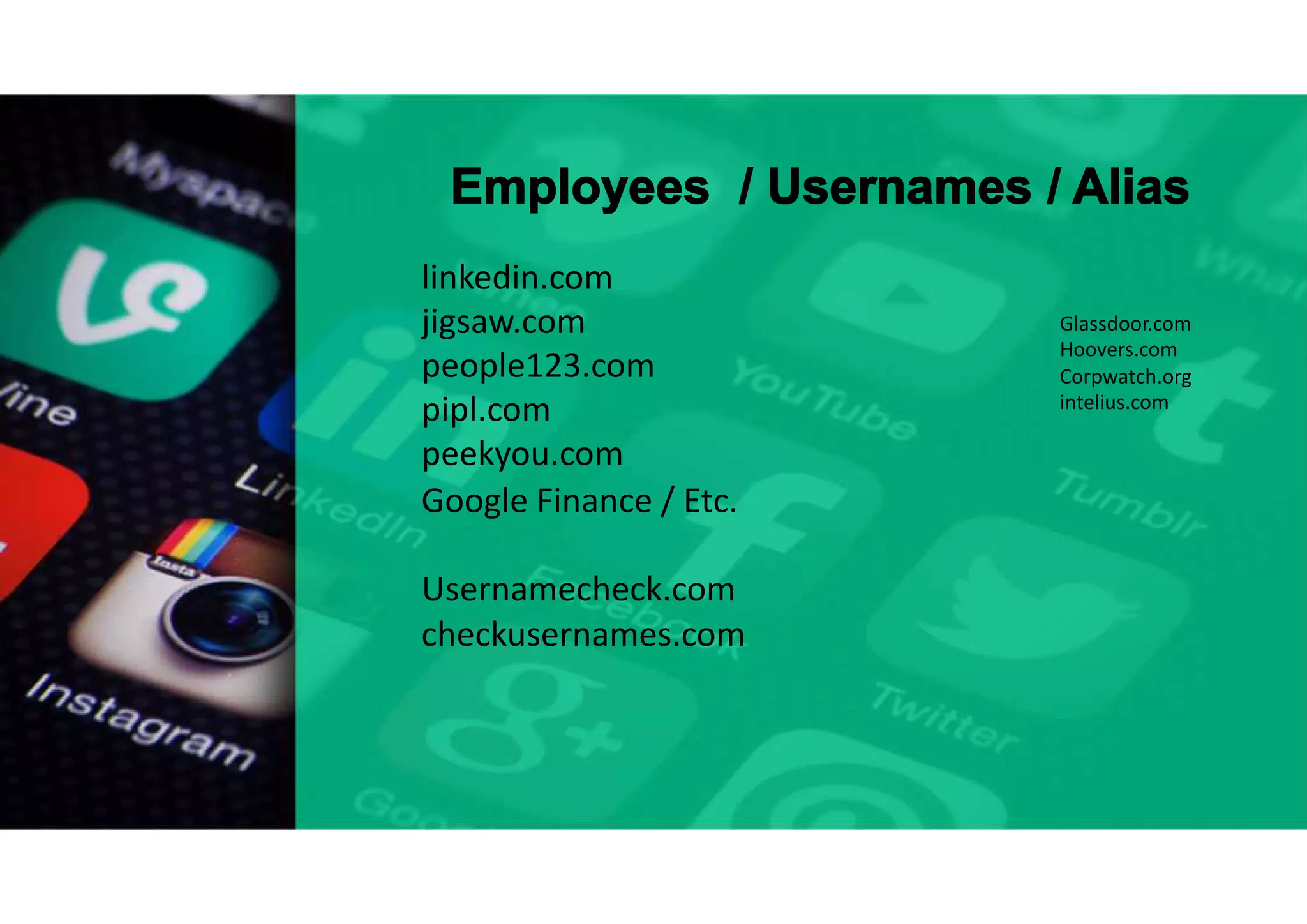
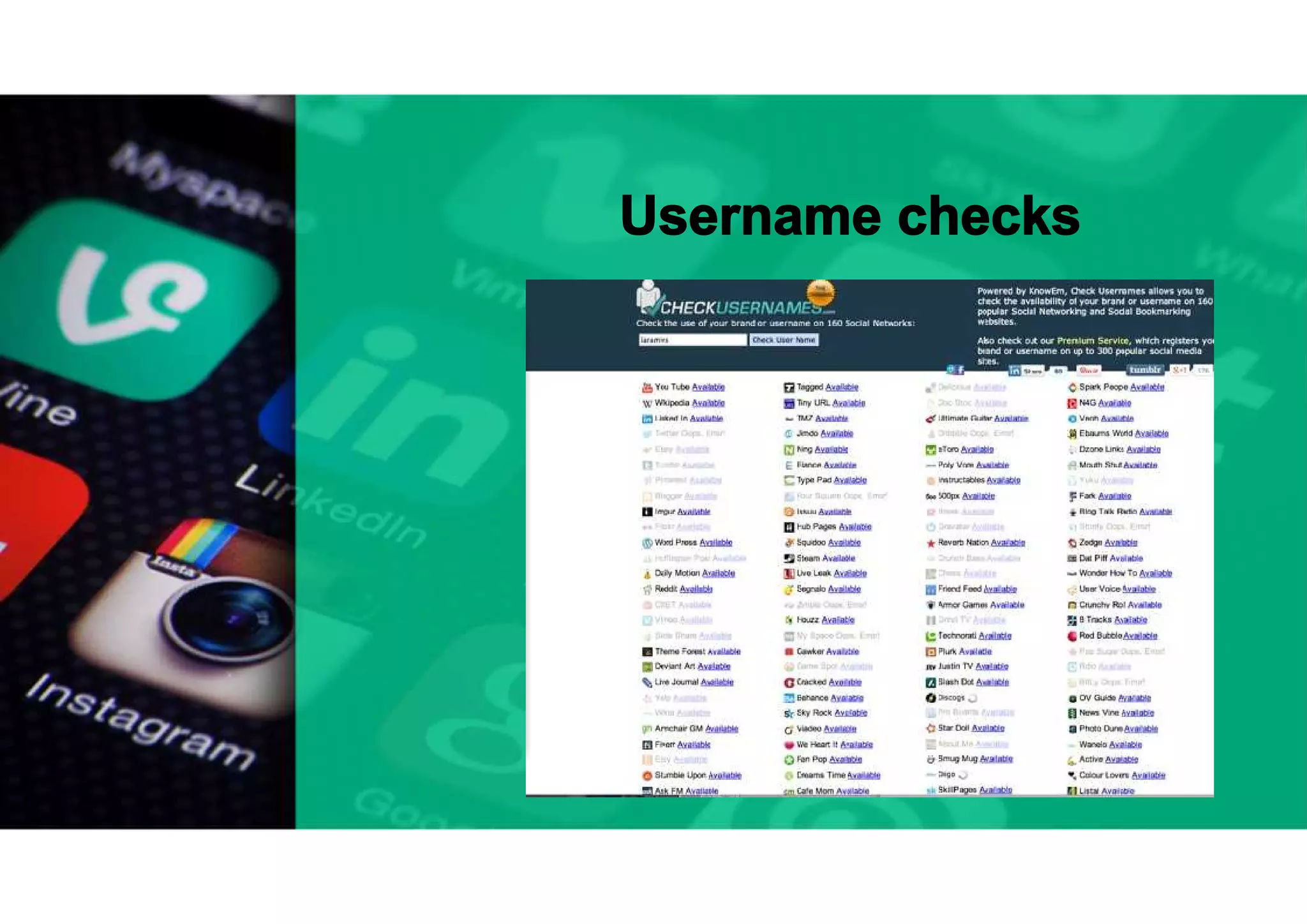
The document discusses open source intelligence (OSINT), defining it as intelligence gathered from publicly available data, and highlights its importance in the context of recent hacking incidents. It outlines various types of intelligence, OSINT processes, data sources, and methods for data harvesting. Additionally, it addresses current challenges in OSINT and mentions notable tools that can be used for intelligence gathering.