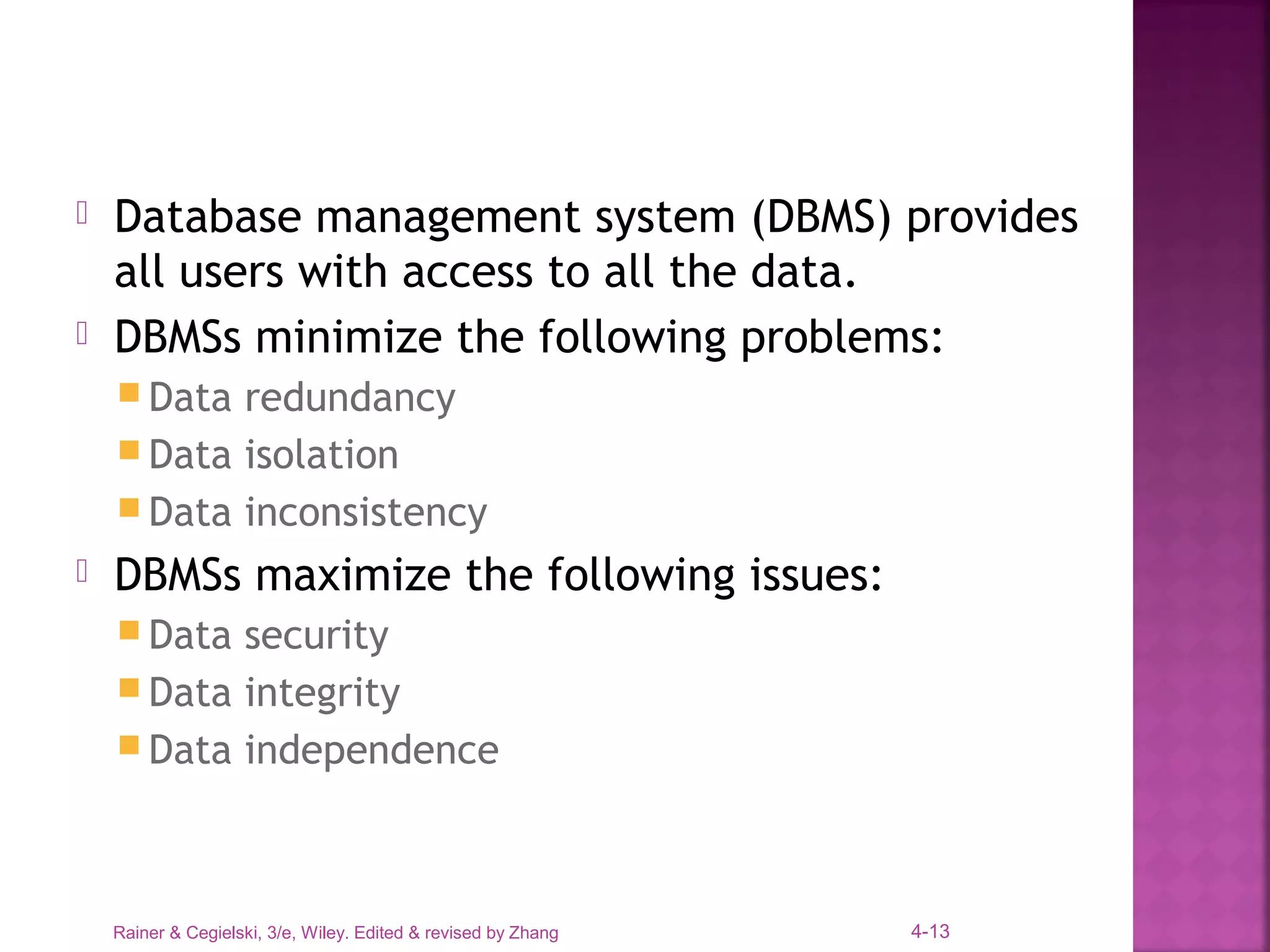
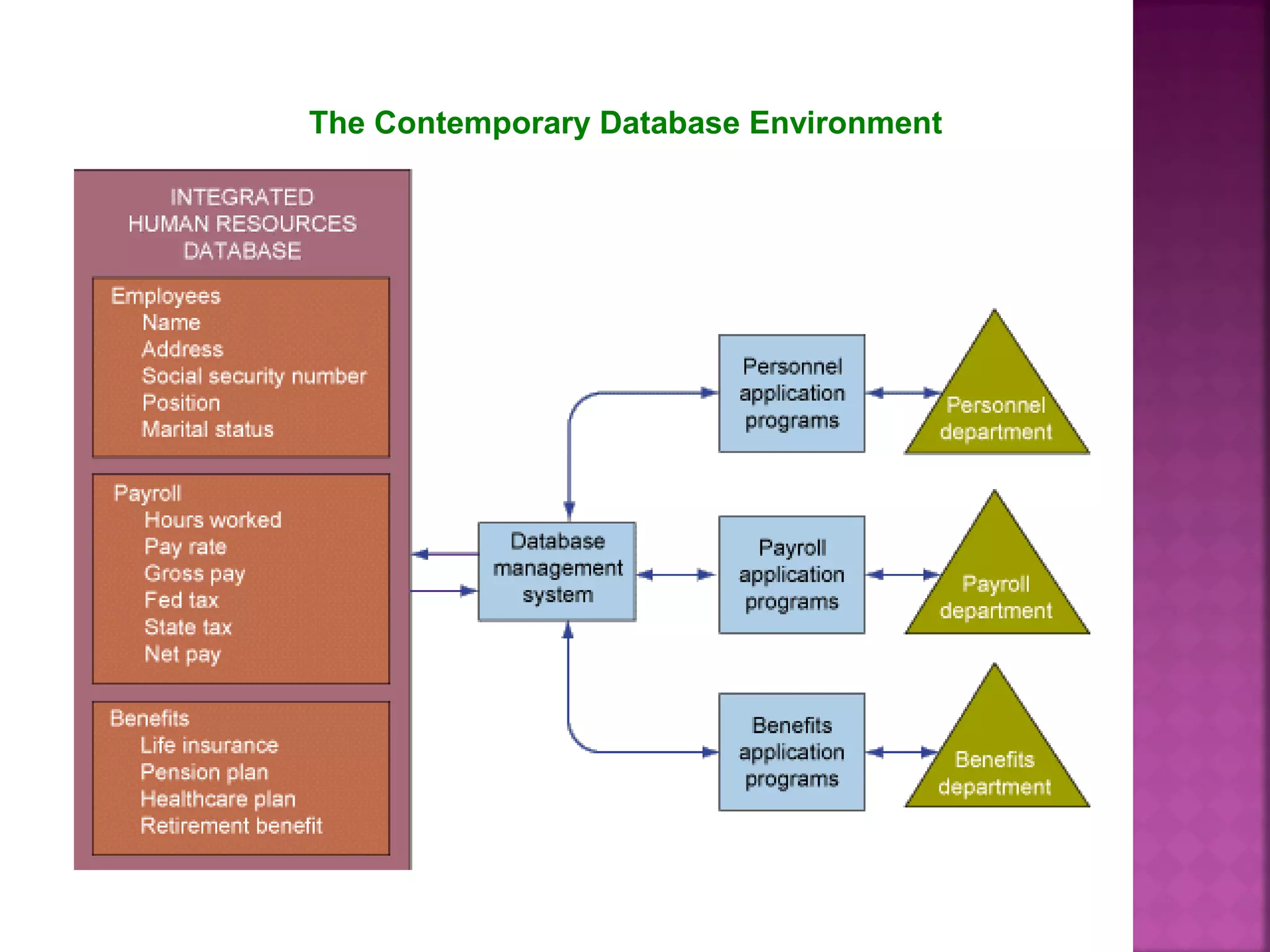
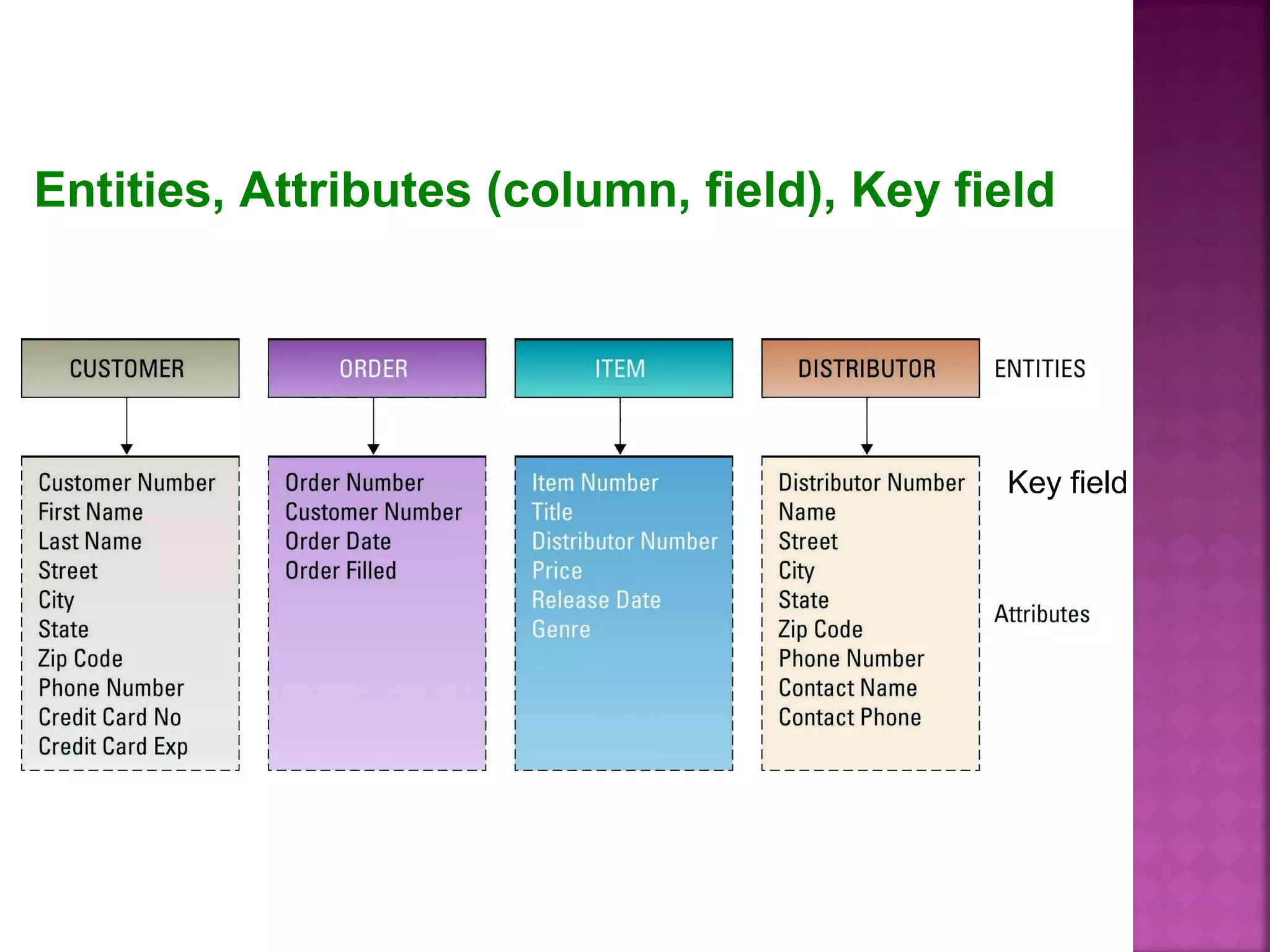
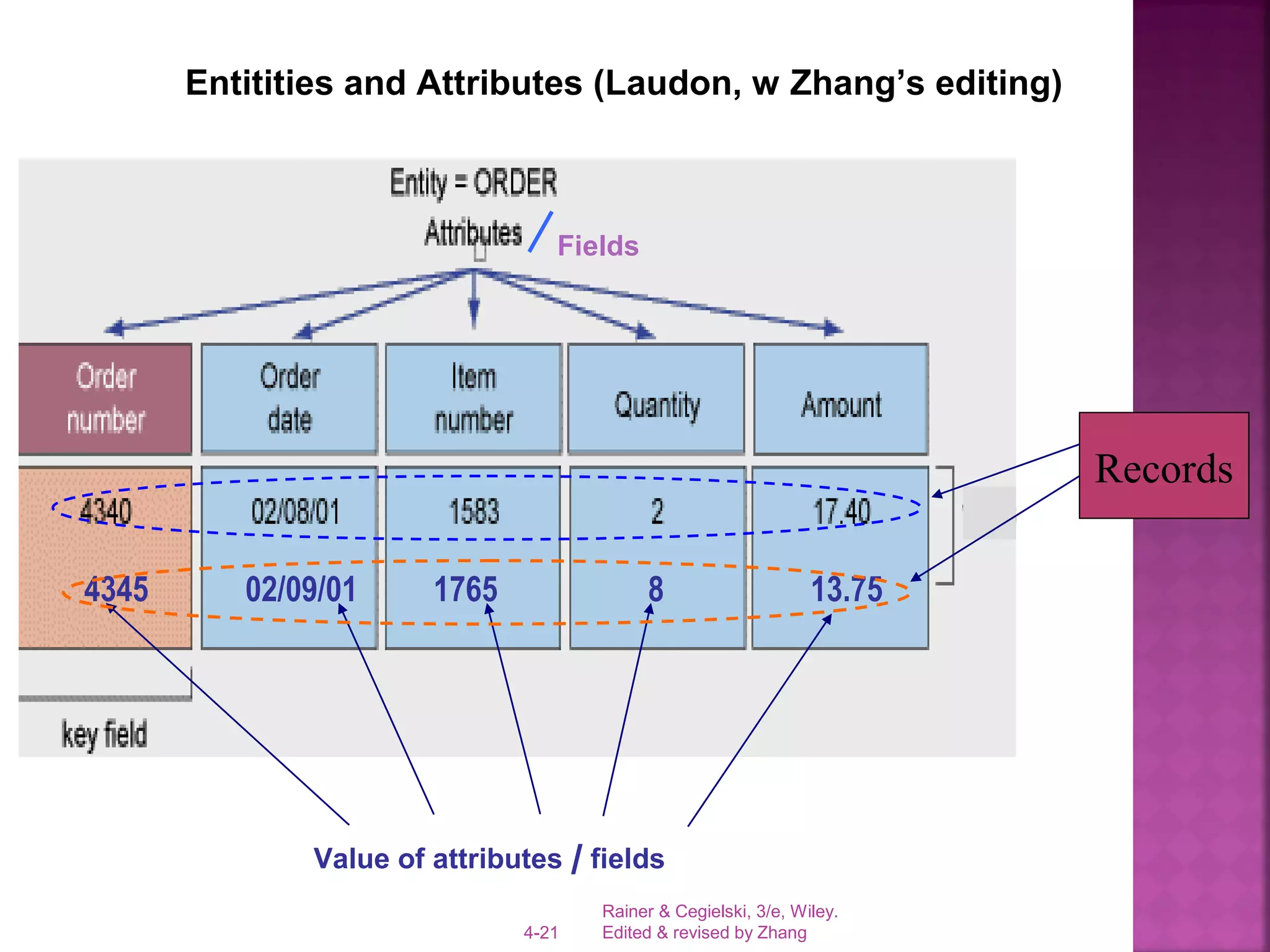
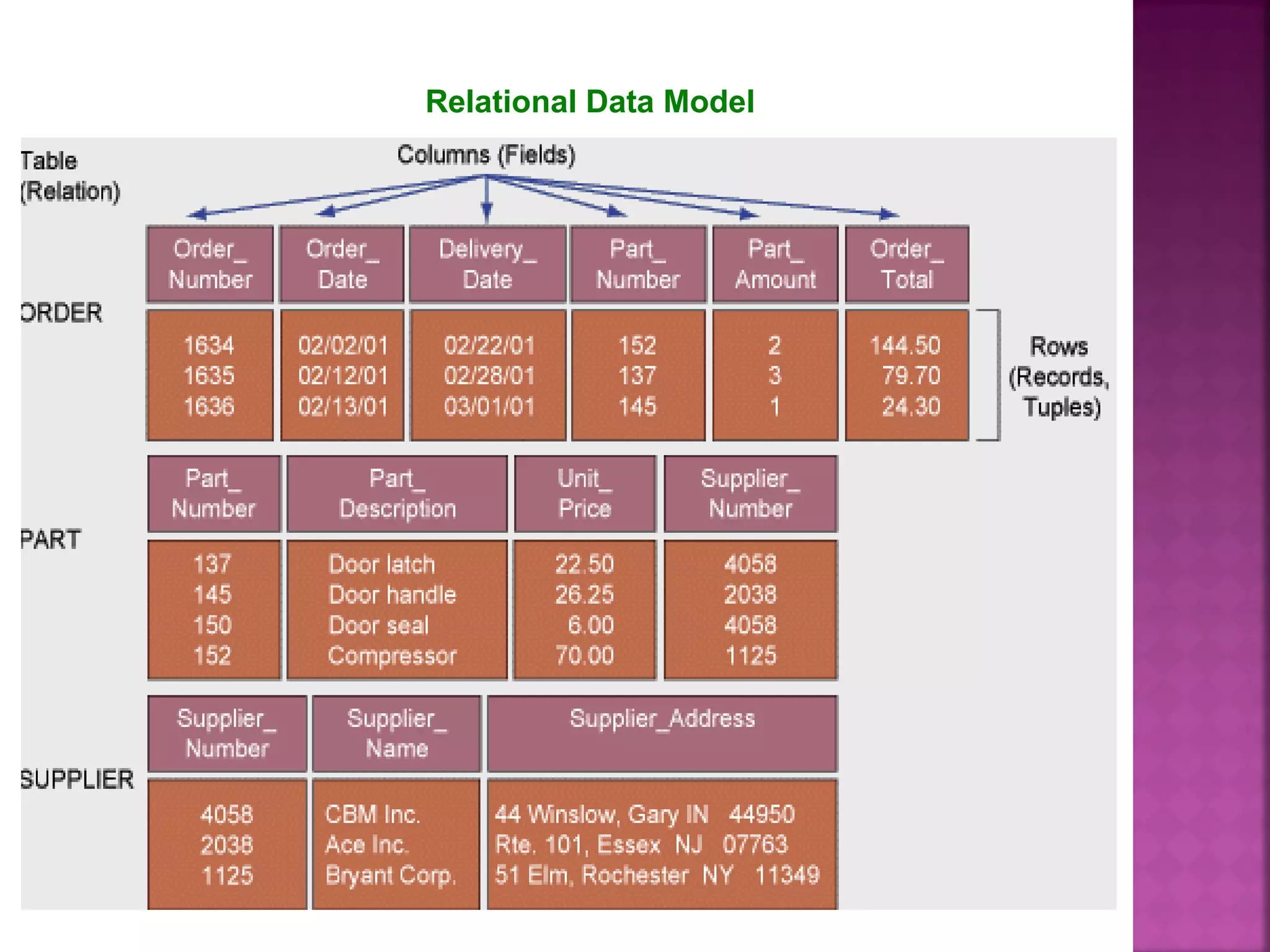
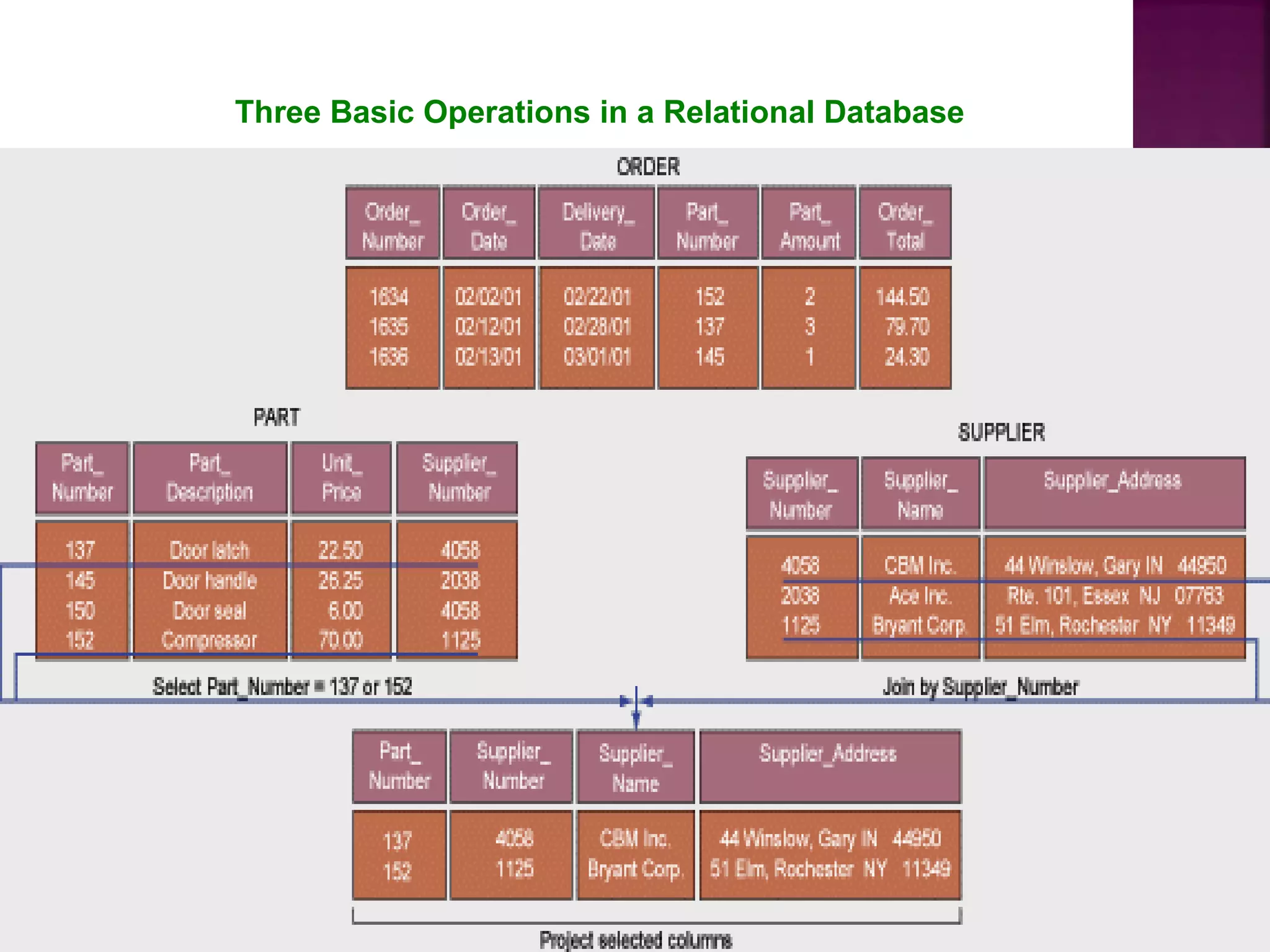
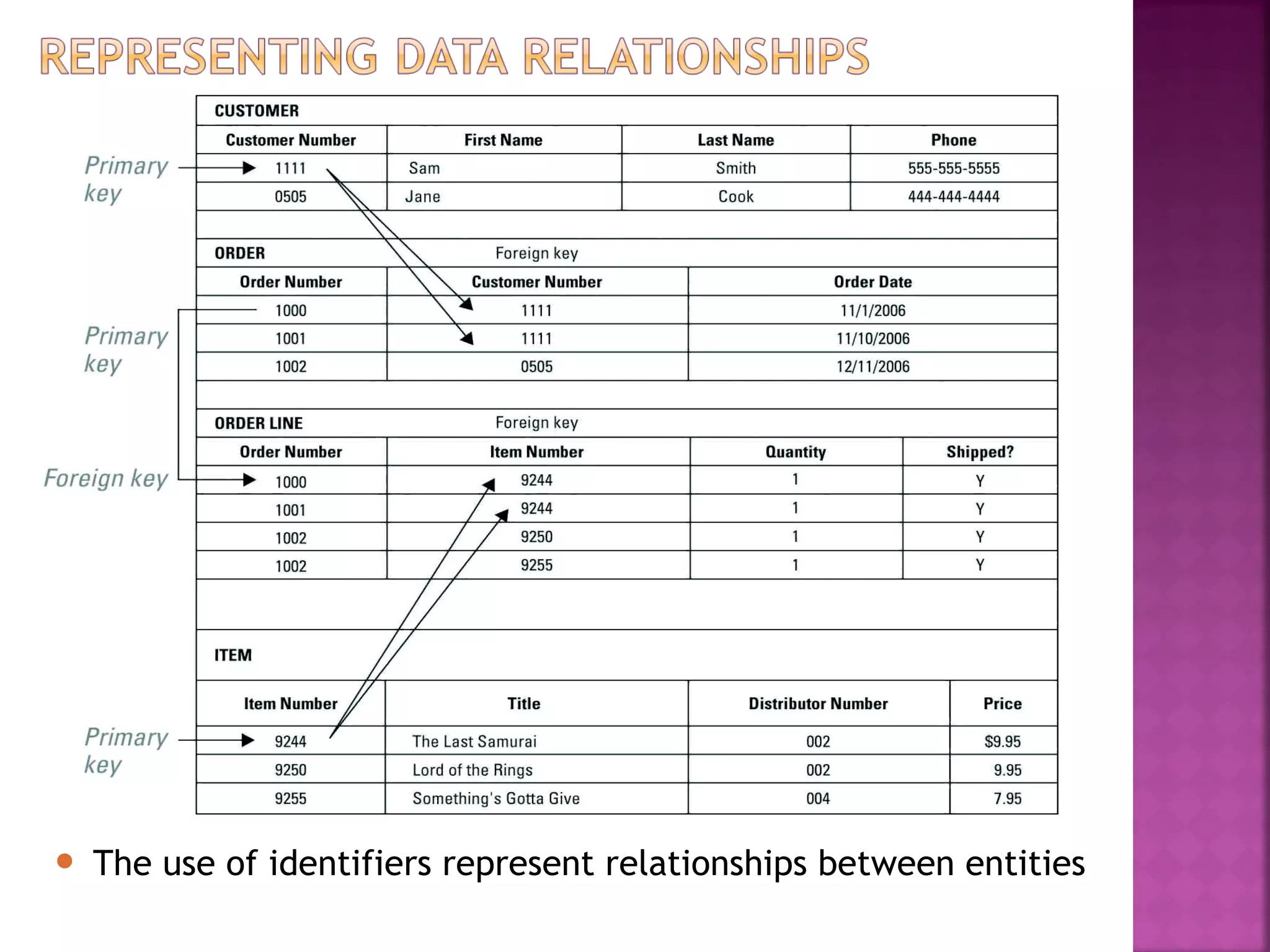
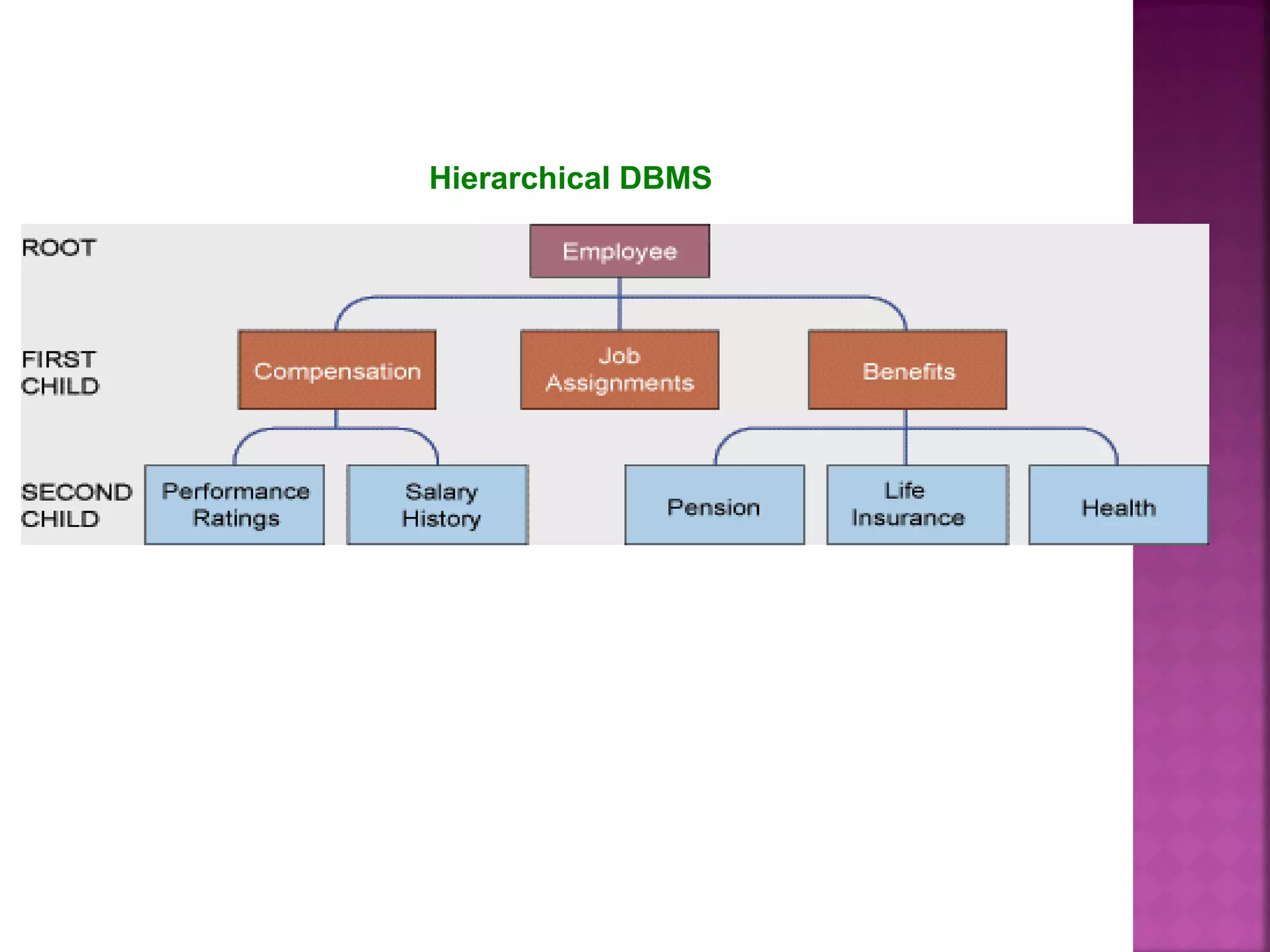
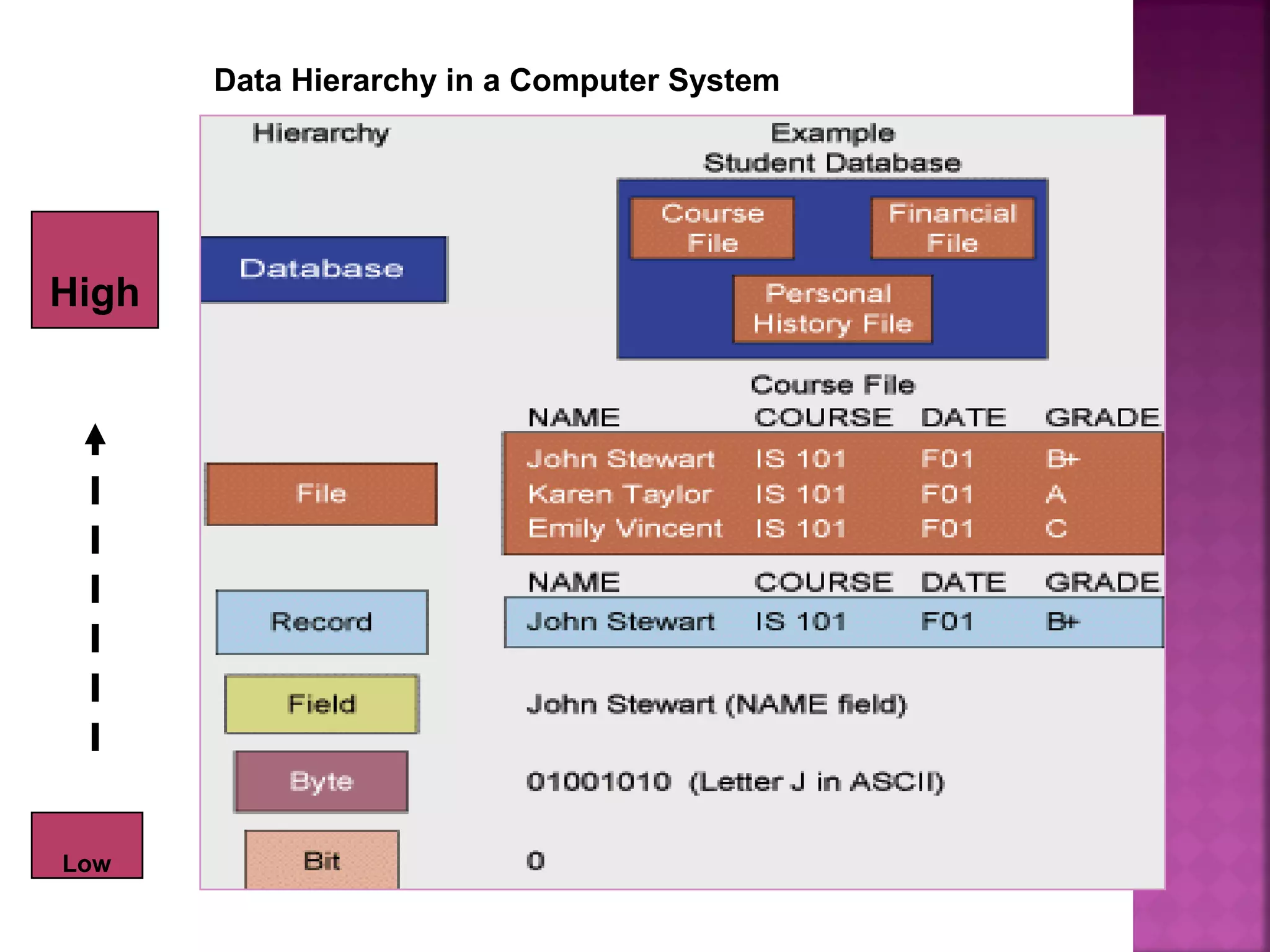
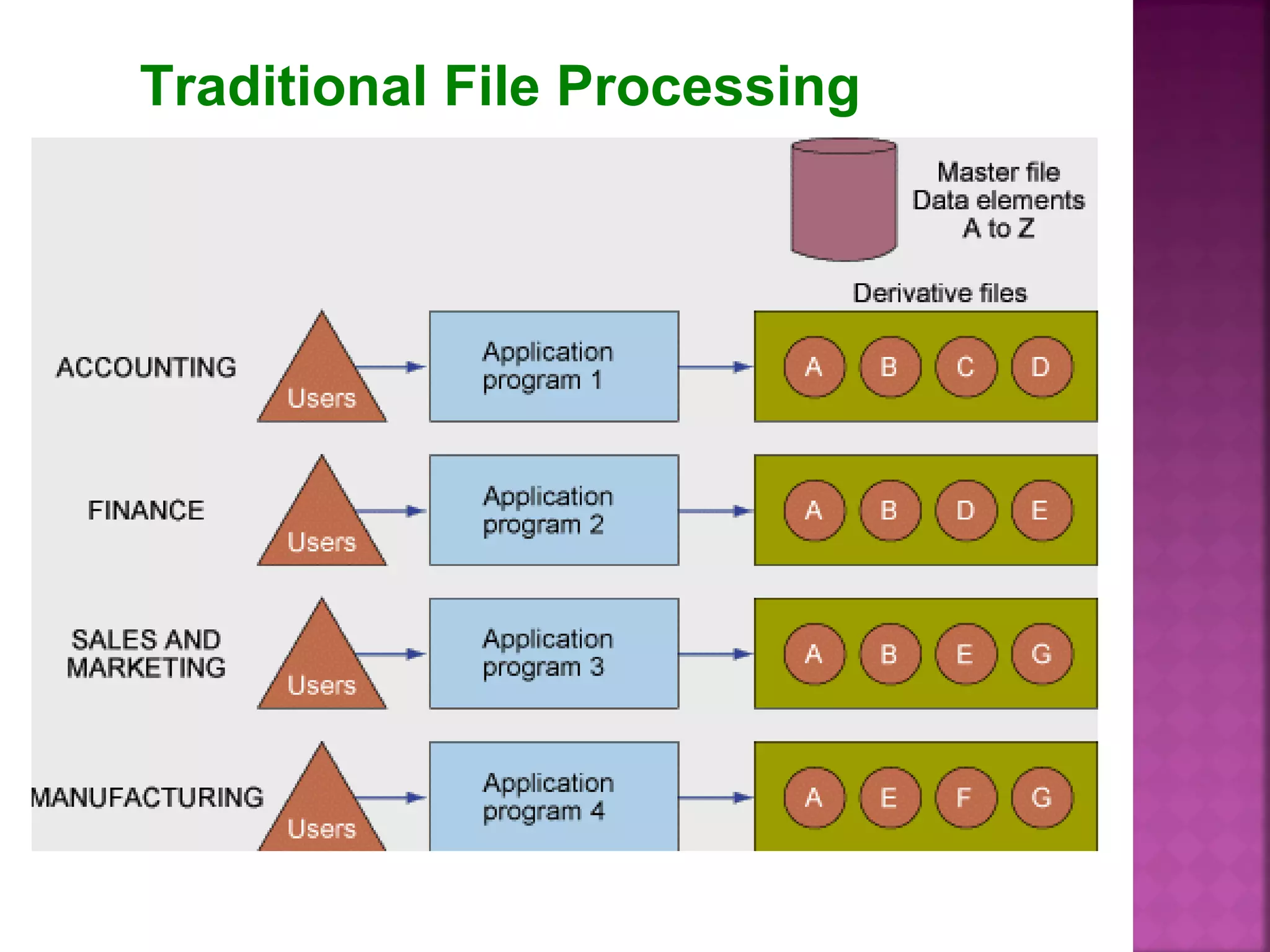
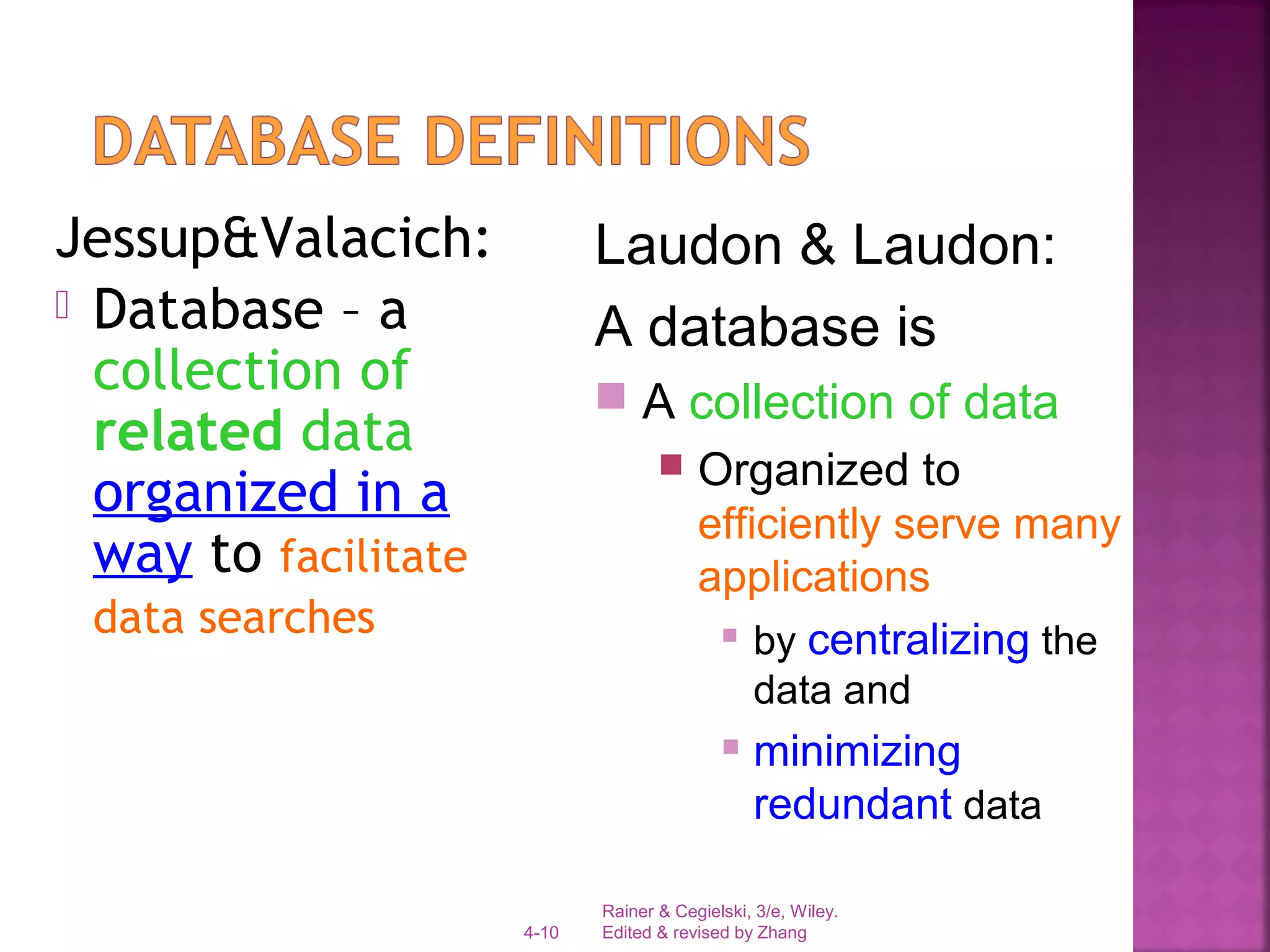
The document defines key concepts related to file organization and database management systems. It discusses the hierarchy of data from bits to files and databases. Issues with traditional file processing like data redundancy, poor security, and lack of data sharing are covered. The benefits of a database management system in centralizing data, minimizing redundancy, and improving security and data sharing are summarized. Relational database concepts like entities, attributes, keys, records, and tables are defined. Common database operations like select, join, and project are also outlined.
![Rainer & Cegielski, 3/e, Wiley.
Edited & revised by Zhang4-11
DBMS – Database Management Systems
It is a software used to
1. create,
2. store,
3. organize,
4. update, and
5. retrieve
data, from a single database or several
databases
[in a desirable arrangement/format, that
can be specified by the users in an easy
way]](https://image.slidesharecdn.com/08sipdatabase-130925120846-phpapp02/75/08-sip-database-11-2048.jpg)