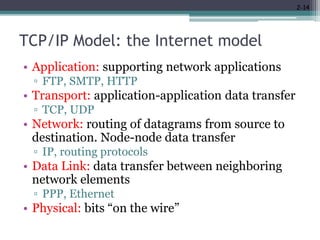
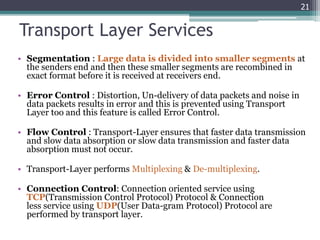
The document discusses network models and protocol layering. It describes the TCP/IP model which consists of five layers - application, transport, network, data link, and physical. It also mentions the OSI model. Each layer in the TCP/IP model has specific responsibilities like the application layer supporting network applications, the transport layer handling end-to-end data transfer, the network layer routing data, the data link layer transferring data between neighboring elements, and the physical layer dealing with transmission of raw bits. Layering allows for modularity and abstraction which helps manage network complexity.