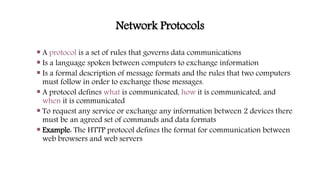
The document discusses network protocols and protocol layering. It describes the seven layers of the OSI model and four layers of the TCP/IP model. It explains the functions of each layer, including physical addressing at layer 2, logical addressing and routing at layer 3, transport functions like segmentation and error checking at layer 4, and application functions at layer 7. Common protocols are assigned to each layer, such as IP, TCP, UDP, HTTP, and FTP. Protocol layering allows dividing network designs into functional layers and assigning protocols to perform each layer's tasks.