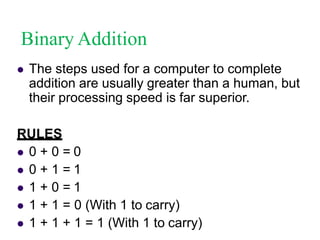
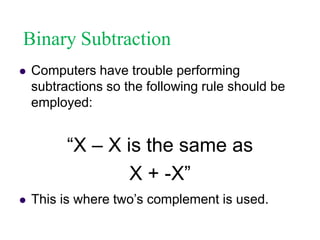
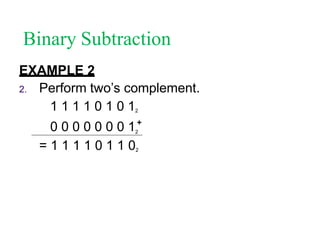
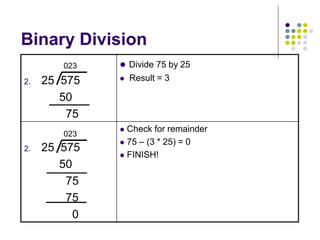
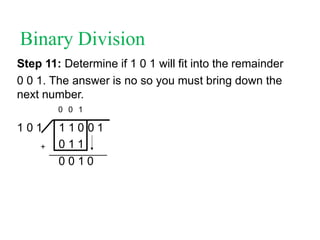
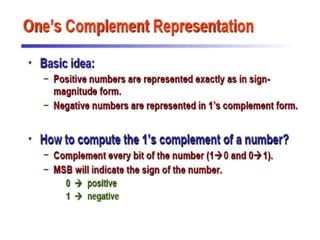
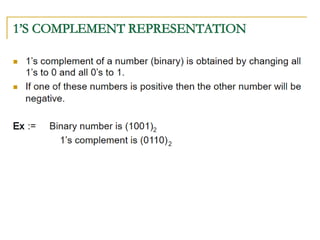
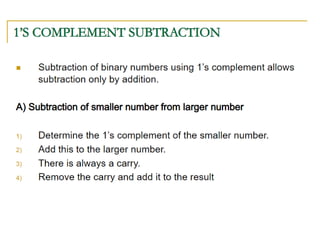
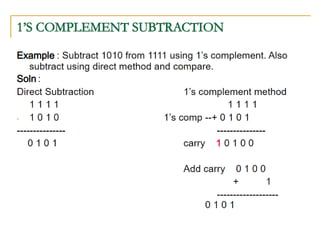
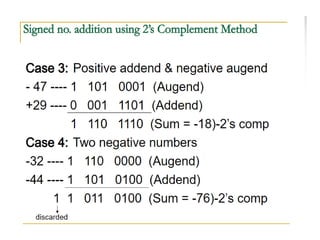
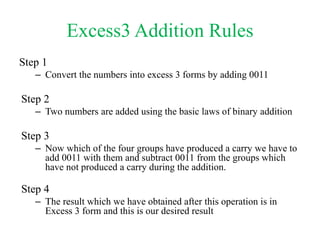
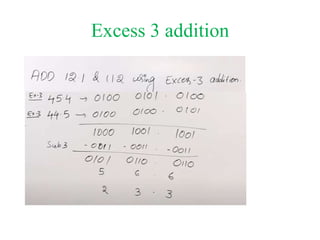
The document provides an in-depth overview of binary arithmetic, detailing operations such as addition, subtraction, multiplication, and division, all performed using binary representations. It explains methods such as two’s complement for subtraction and the shift-and-add technique for multiplication and division. Additionally, it touches on octal and hexadecimal arithmetic, showing how these systems convert to binary for operations.