This document provides an overview of computer networking concepts including:
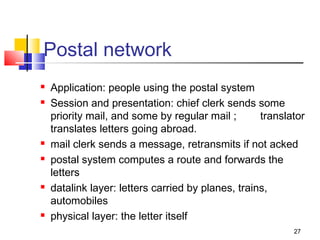
1. Networks are complex systems consisting of hosts, routers, links, applications, protocols, and hardware/software.
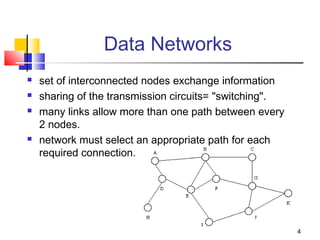
2. Early telephone networks used point-to-point links to directly connect users, while modern data networks allow indirect connections through interconnected nodes using packet switching.
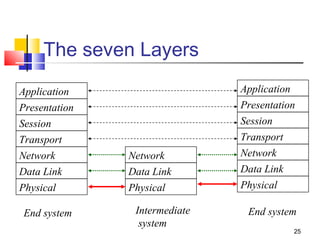
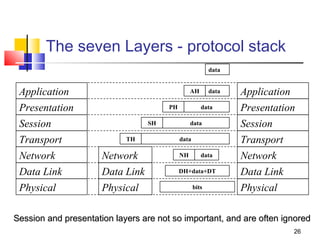
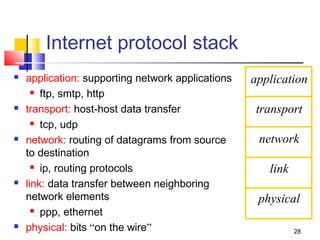
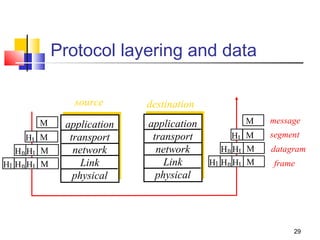
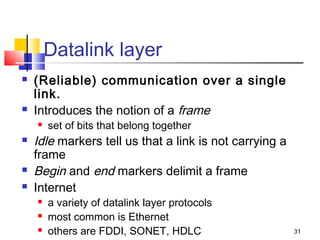
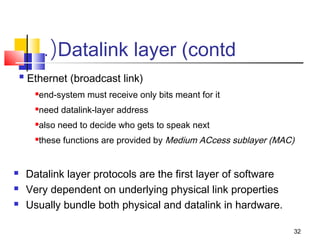
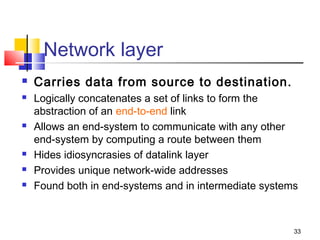
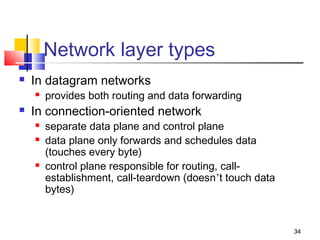
3. The Internet protocol stack includes layers for applications, transport, network, link, and physical, with TCP/IP being the dominant protocols.
![12
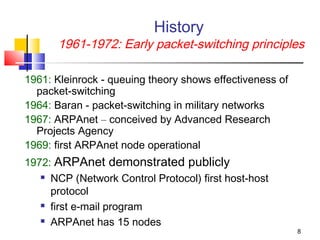
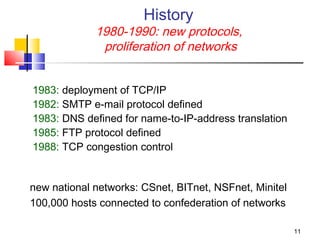
History
1990 - : commercialization and WWW
early 1990’s: ARPAnet decomissioned
1991: NSF lifts restrictions on commercial use of
NSFnet (decommissioned, 1995)
early 1990s: WWW
hypertext [Bush 1945, Nelson 1960’s]
HTML, http: Berners-Lee
1994: Mosaic, later Netscape
late 1990’s: commercialization of WWW
2004-2005: Web 2.0 (O’Reilly)](https://image.slidesharecdn.com/computer-networks-networks-141001004554-phpapp02/85/Computer-networks-networks-12-320.jpg)