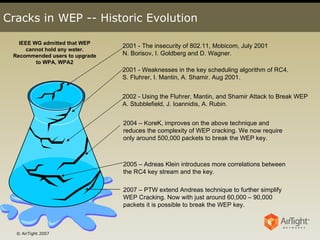
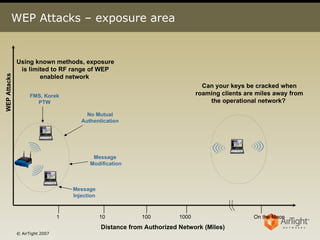
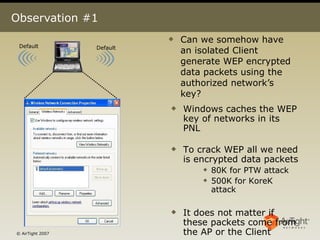
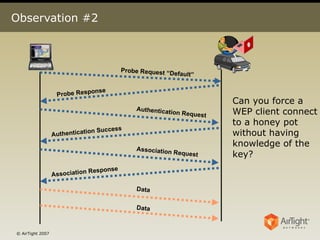
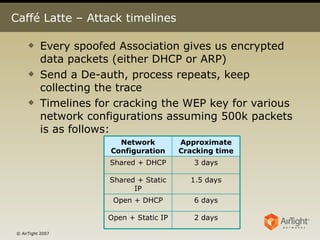
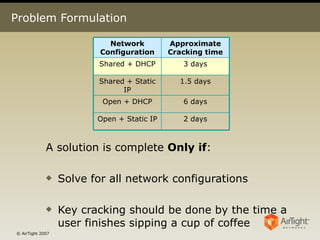
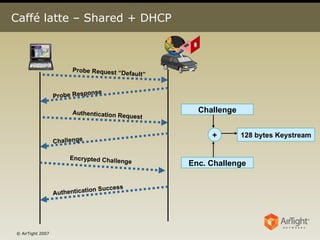
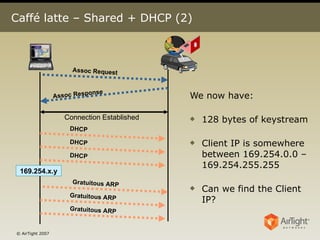
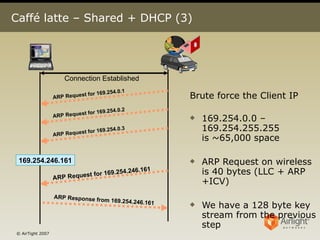
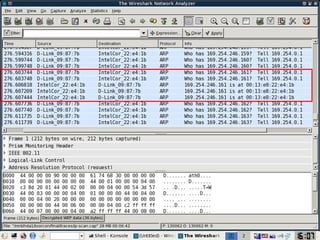
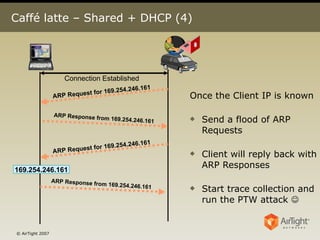
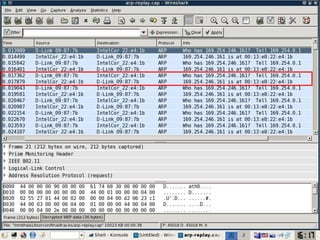
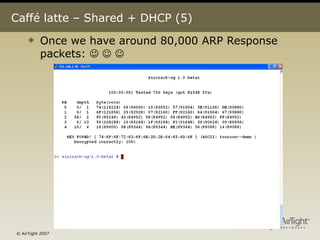
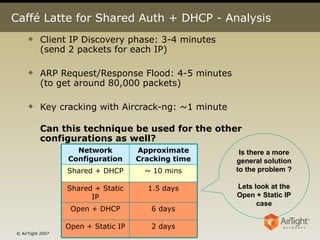
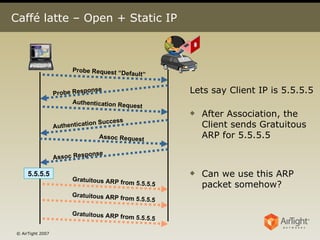
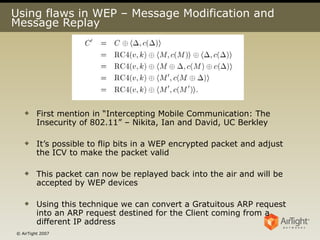
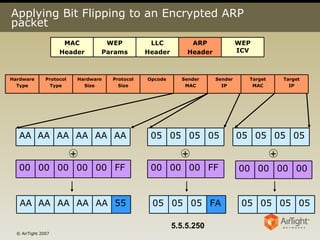
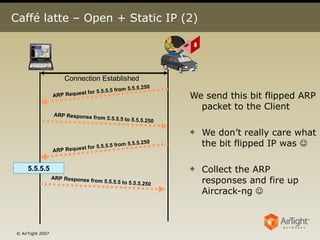
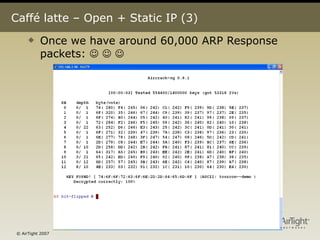
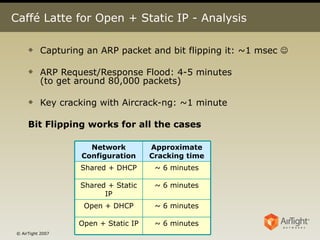
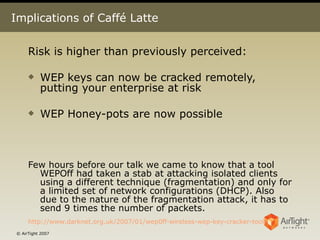
The document details the vulnerabilities in WEP encryption and methods for cracking WEP keys, highlighting techniques developed from 2001 to 2007 that can easily compromise WEP security. It discusses specific attack strategies, such as capturing ARP packets and using methods like PTW and Korek attacks to expedite key retrieval, demonstrating that WEP can be cracked within hours or even minutes under certain configurations. The authors emphasize the need for users to upgrade from WEP to more secure protocols like WPA/WPA2 and to exercise caution when using public wireless networks.
![Questions? [email_address] Md.Ahmad@airtightnetworks.net Airtight Networks www.AirTightNetworks.net Acknowledgements: Amit Vartak (amit.vartak@airtightnetworks.net)](https://image.slidesharecdn.com/toorconcaffelatteattack-090918052912-phpapp01/85/Caffe-Latte-Attack-26-320.jpg)