Embed presentation
Downloaded 22 times

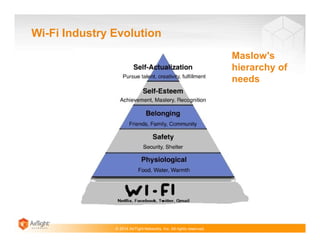
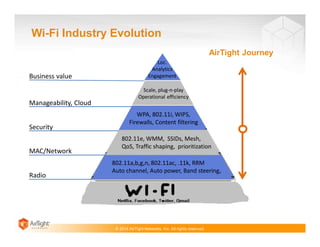

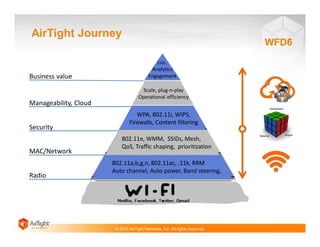
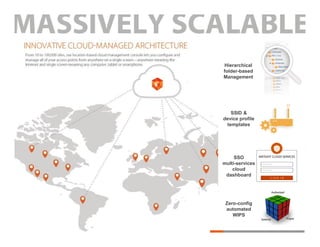


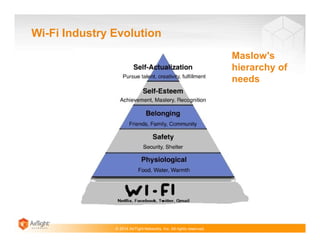
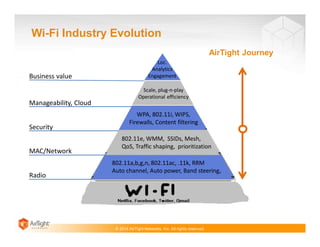
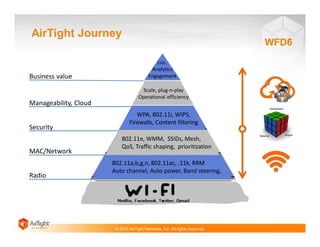
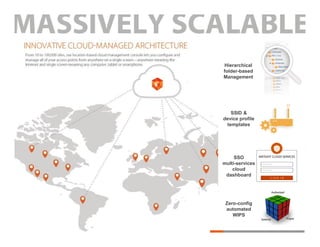
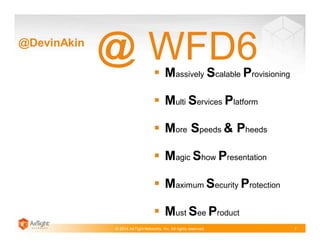
The document discusses AirTight Networks, a provider of cloud-managed Wi-Fi solutions. It highlights AirTight's chief evangelist Devin Akin and CTO Pravin Bhagwat, and notes technologies like WIPS, 802.11ac, and the evolution of Wi-Fi industry needs around manageability, security, and analytics. Diagrams show AirTight's journey and focus on more distributed environments, and new features in the WFD6 product line including massively scalable provisioning and a multi-service cloud platform.