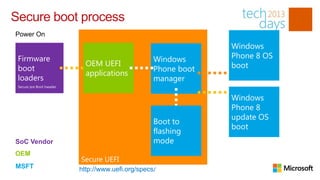
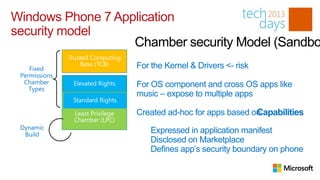
Windows Phone 8 provides several security features to protect devices and data, including secure boot to prevent malware installation, device encryption, and application sandboxing. It also supports enterprise management of apps and policies through Exchange ActiveSync or System Center Mobile Device Management for features like remote wiping, password policies, and app distribution controls.